| File name: | chrome_elf.dll |
| Full analysis: | https://app.any.run/tasks/79ca79c6-ec73-4c07-946f-fa3e12b7ce79 |
| Verdict: | No threats detected |
| Analysis date: | November 22, 2019, 00:45:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 3F9C18E3B8ACA6564F2E718CD2C4236D |
| SHA1: | FF2BF050F6C8DC46F72D9B0608777920C6B67823 |
| SHA256: | 152BD996D71A1C12726509EE88B0F1E170A0272C2D2B83C9B94496B1BDAED04D |
| SSDEEP: | 12288:yNyHLoSMbjVMJ2oMcKidLlJZhJuTmrAUTlD5RH9P0OUxl+ntsCU:qyHkLbjVQ2eUTIROvfX |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Loads main object executable
- rundll32.exe (PID: 2428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:05 07:00:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 578560 |
| InitializedDataSize: | 141312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x69112 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 76.0.3809.12 |
| ProductVersionNumber: | 76.0.3809.12 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | The Chromium Authors |
| FileDescription: | Chromium |
| FileVersion: | 76.0.3809.12 |
| InternalName: | chrome_elf_dll |
| LegalCopyright: | Copyright 2019 The Chromium Authors. All rights reserved. |
| OriginalFileName: | chrome_elf.dll |
| ProductName: | Chromium |
| ProductVersion: | 76.0.3809.12 |
| CompanyShortName: | The Chromium Authors |
| ProductShortName: | Chromium |
| LastChange: | 220b19a666554bdcac56dff9ffd44c300842c933-refs/branch-heads/3809@{#83} |
| OfficialBuild: | 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Jun-2019 05:00:00 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | The Chromium Authors |
| FileDescription: | Chromium |
| FileVersion: | 76.0.3809.12 |
| InternalName: | chrome_elf_dll |
| LegalCopyright: | Copyright 2019 The Chromium Authors. All rights reserved. |
| OriginalFilename: | chrome_elf.dll |
| ProductName: | Chromium |
| ProductVersion: | 76.0.3809.12 |
| CompanyShortName: | The Chromium Authors |
| ProductShortName: | Chromium |
| LastChange: | 220b19a666554bdcac56dff9ffd44c300842c933-refs/branch-heads/3809@{#83} |
| Official Build: | 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0078 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0x0000 |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x0000 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000078 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 05-Jun-2019 05:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008D3C9 | 0x0008D400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.80684 |
.rdata | 0x0008F000 | 0x00018A80 | 0x00018C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.46418 |
.data | 0x000A8000 | 0x0000716C | 0x00002E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.36214 |
.00cfg | 0x000B0000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0815394 |
.crthunk@ | 0x000B1000 | 0x00000040 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.tls | 0x000B2000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.voltbl | 0x000B3000 | 0x000002B9 | 0x00000400 | 4.87726 | |
CPADinfo( | 0x000B4000 | 0x00000028 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.122276 |
.rsrc | 0x000B5000 | 0x000006A0 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.55449 |
.reloc | 0x000B6000 | 0x00005D94 | 0x00005E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65377 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.53756 | 1172 | UNKNOWN | English - United States | RT_VERSION |
2 | 4.93822 | 358 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
KERNEL32.dll |
VERSION.dll |
WINMM.dll (delay-loaded) |
Exports
Title | Ordinal | Address |
|---|---|---|
0 | 0x00000000 | |
AddDllToBlacklist | 1 | 0x0001ACCA |
ClearReportsBetween_ExportThunk | 2 | 0x00001325 |
CrashForException_ExportThunk | 3 | 0x000012E7 |
DisableHook | 4 | 0x000277D3 |
DrainLog | 5 | 0x0002669B |
DumpHungProcessWithPtype_ExportThunk | 6 | 0x0000132A |
DumpProcessWithoutCrash | 7 | 0x00001173 |
GetApplyHookResult | 8 | 0x000277DB |
GetBlockedModulesCount | 9 | 0x00026C10 |
Total processes
34
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
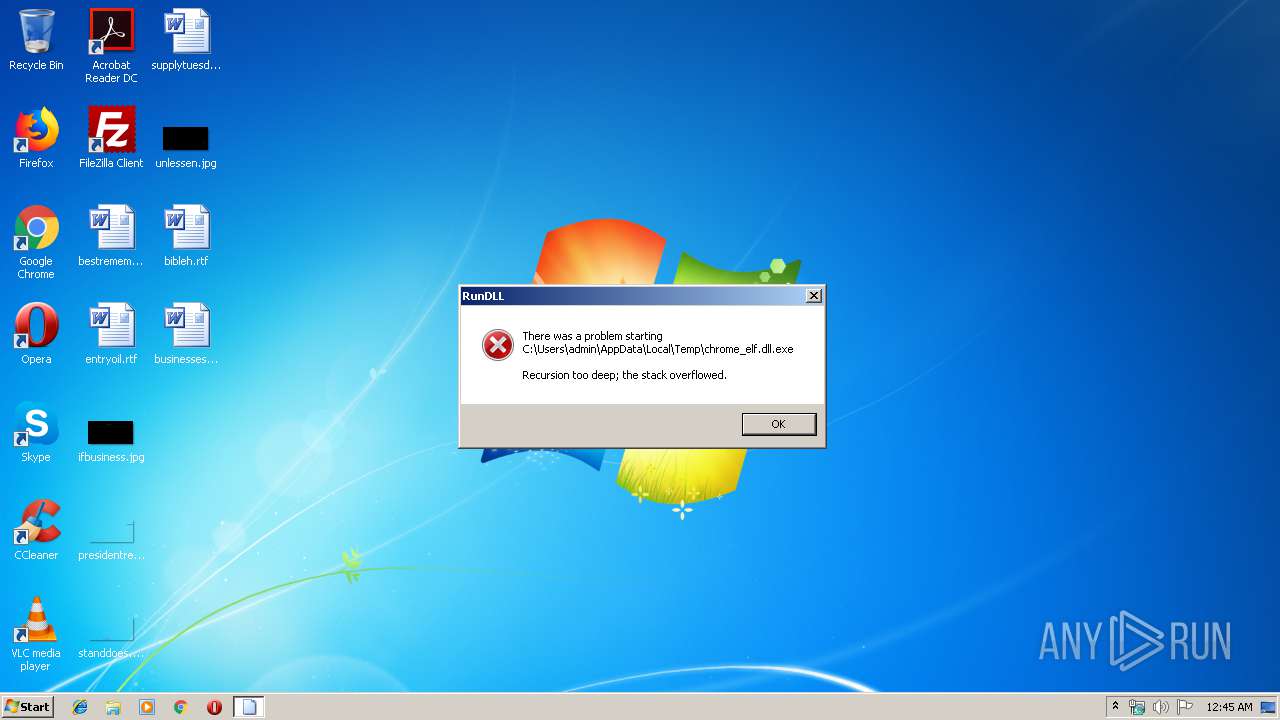
| 2428 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\chrome_elf.dll.exe", AddDllToBlacklist | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report