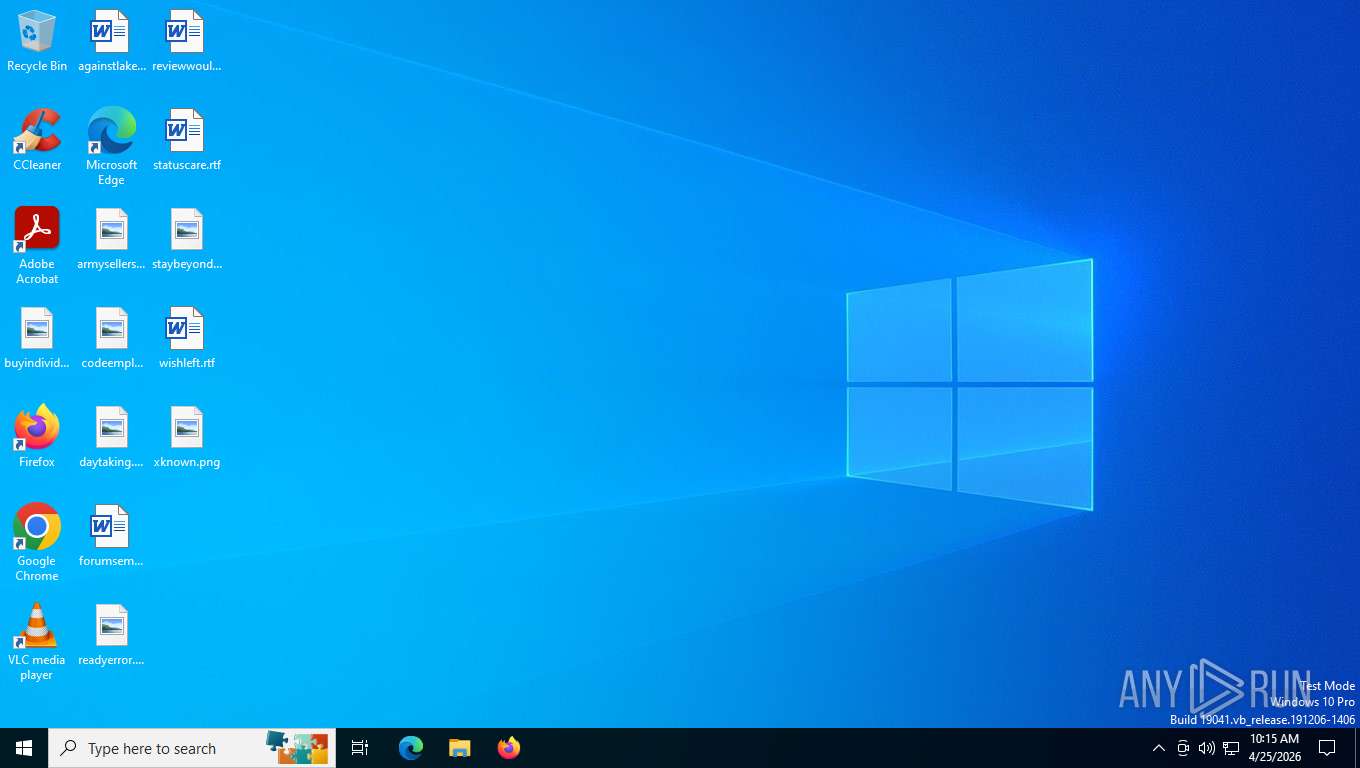
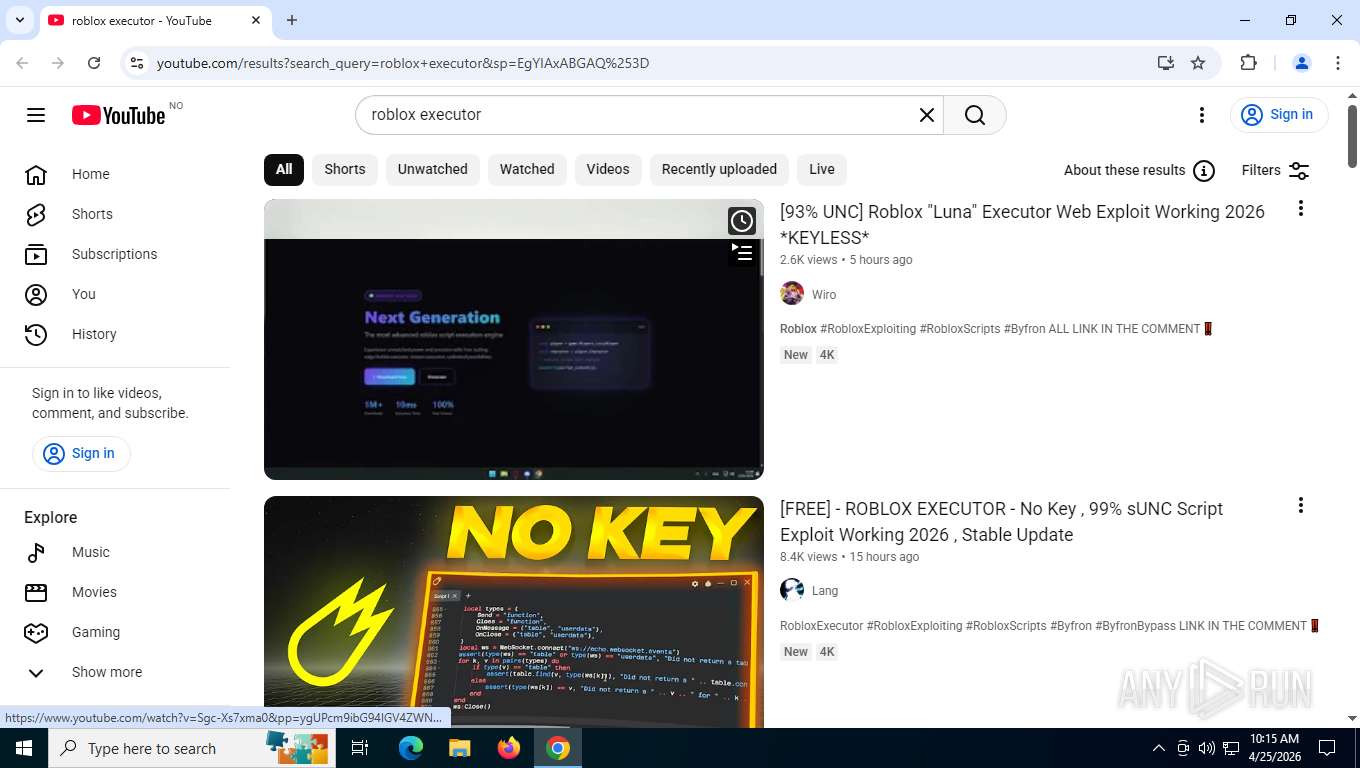
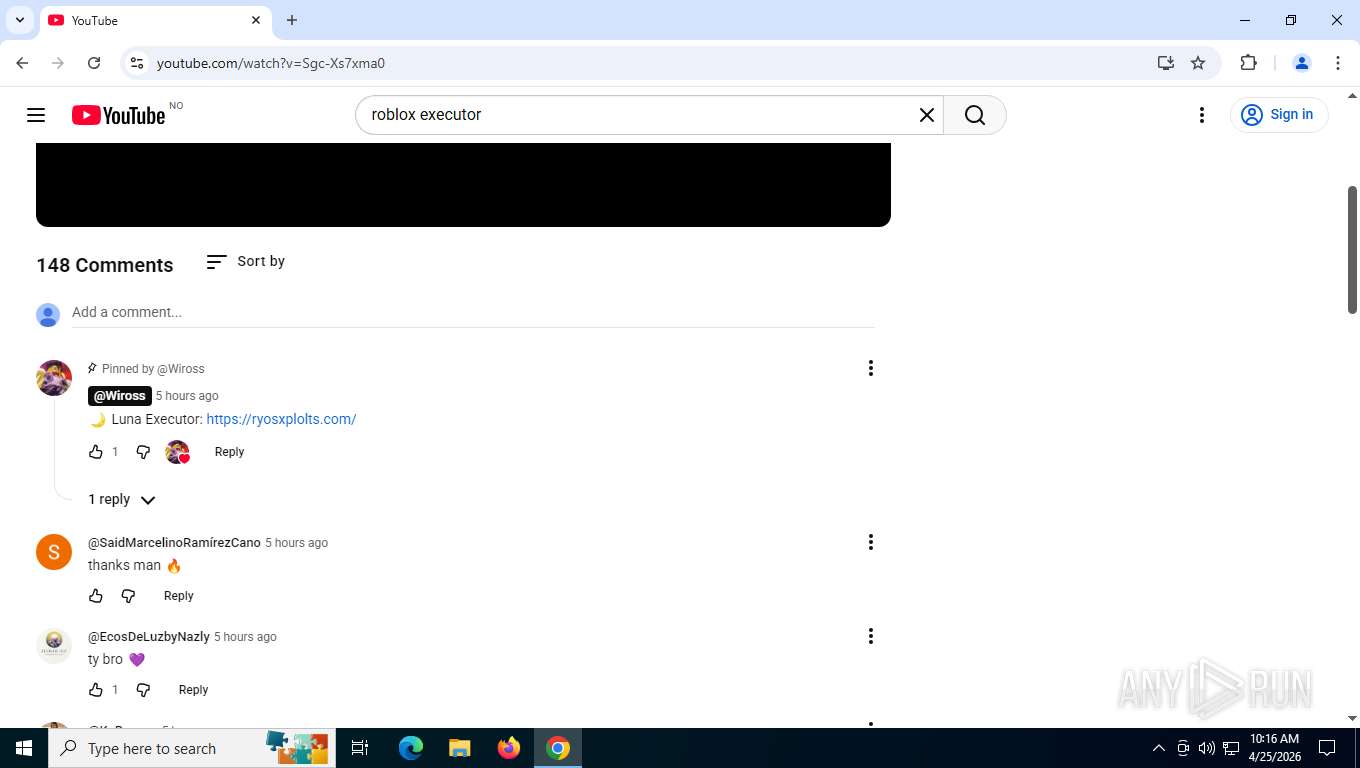
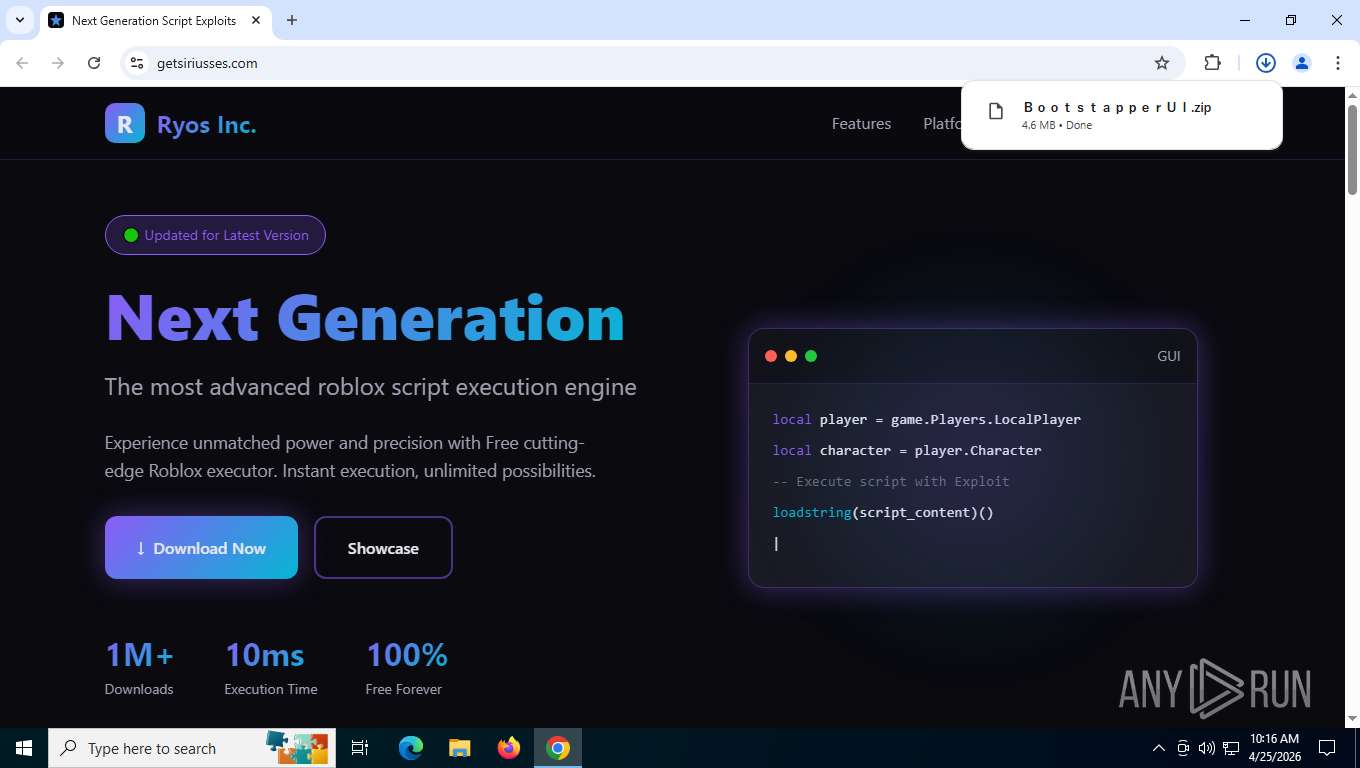
| URL: | https://www.youtube.com/results?search_query=roblox+executor&sp=EgYIAxABGAQ%253D |
| Full analysis: | https://app.any.run/tasks/7f92e6cc-c373-41c3-9ab4-094604b35787 |
| Verdict: | Malicious activity |
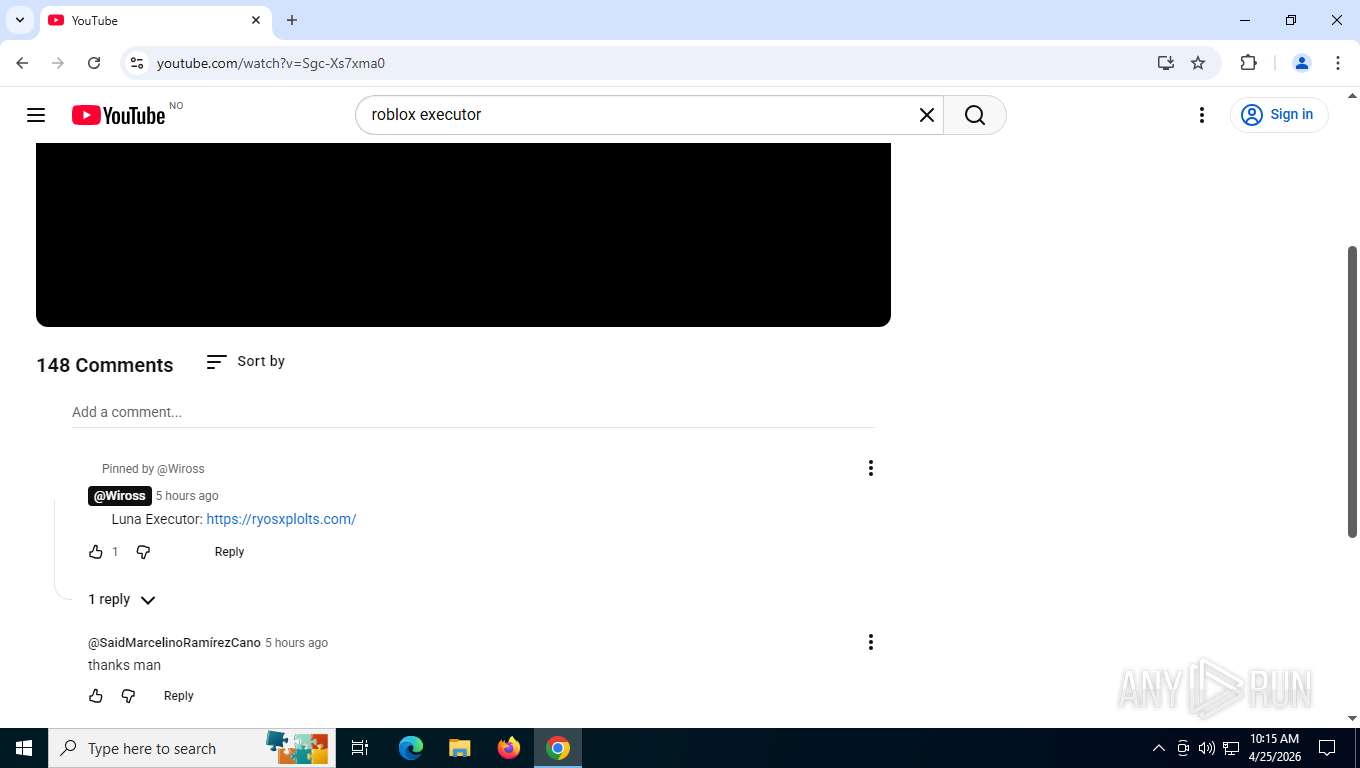
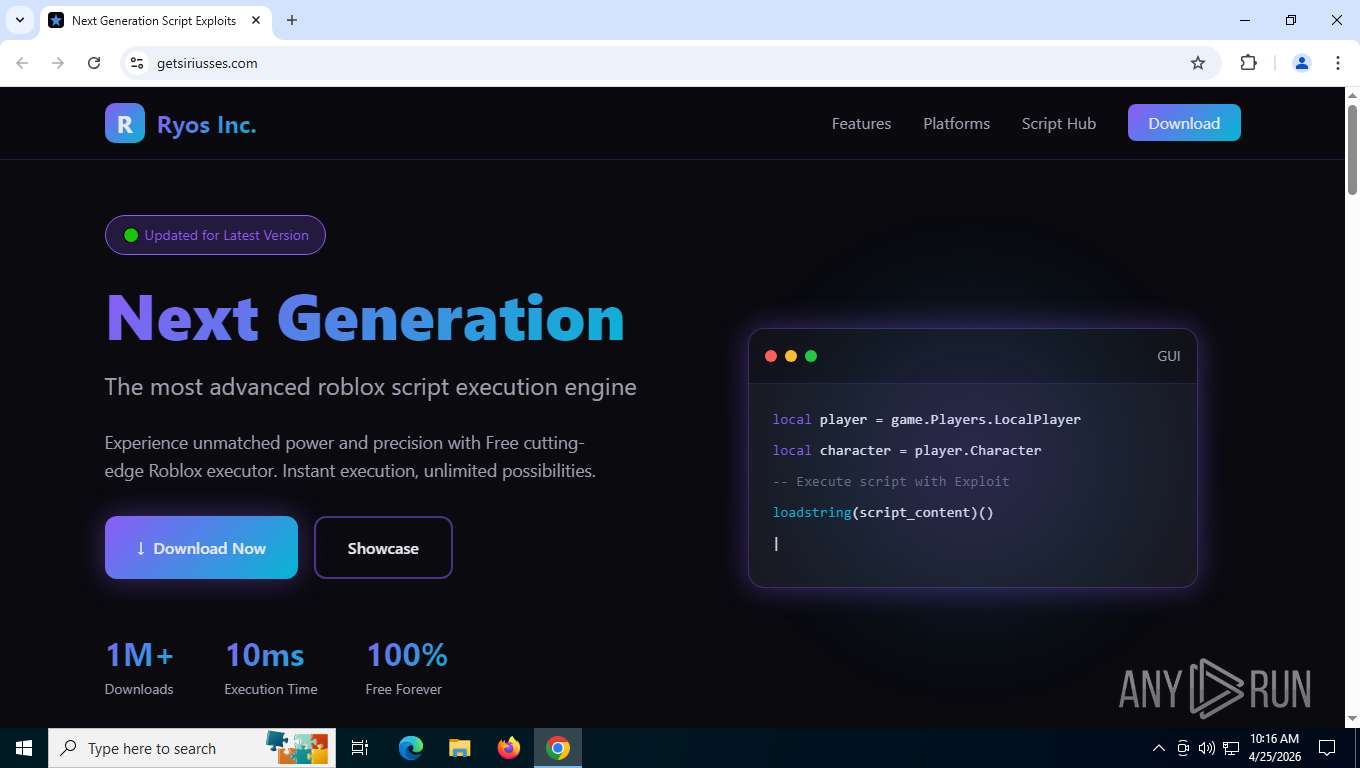
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | April 25, 2026, 14:15:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1305A64936C8797FDA5FC141472B0DB0 |
| SHA1: | 90E5C63543FDC3A5052B9DB39D5006AE920F277C |
| SHA256: | 1526615DCEFACCD60F44A16A09ADAE1EAC36E03D8A74FBE110A47762B51A2C0A |
| SSDEEP: | 3:N8DSLUxGTKXYwdBSQ6dvdjEQgkUuHJQm:2OLUxGvwdBWdvdjE1kUu+m |
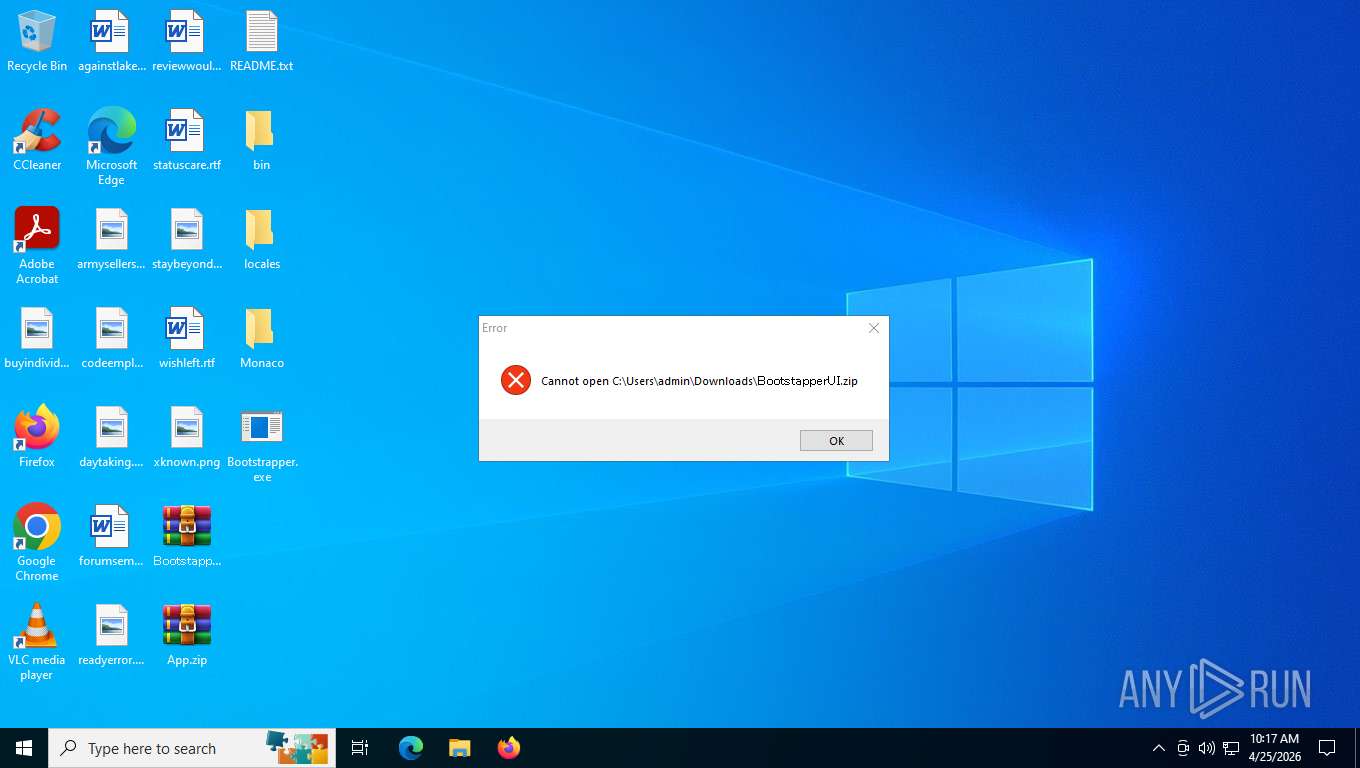
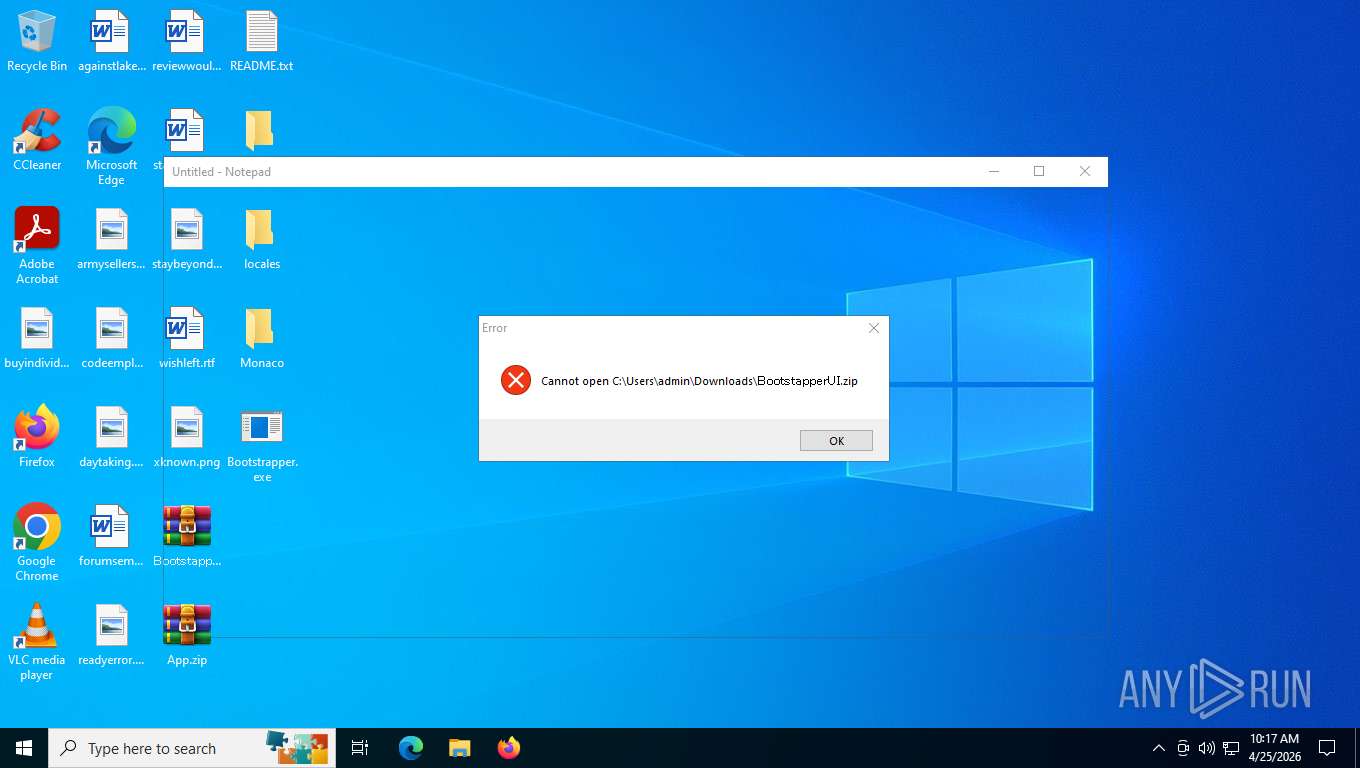
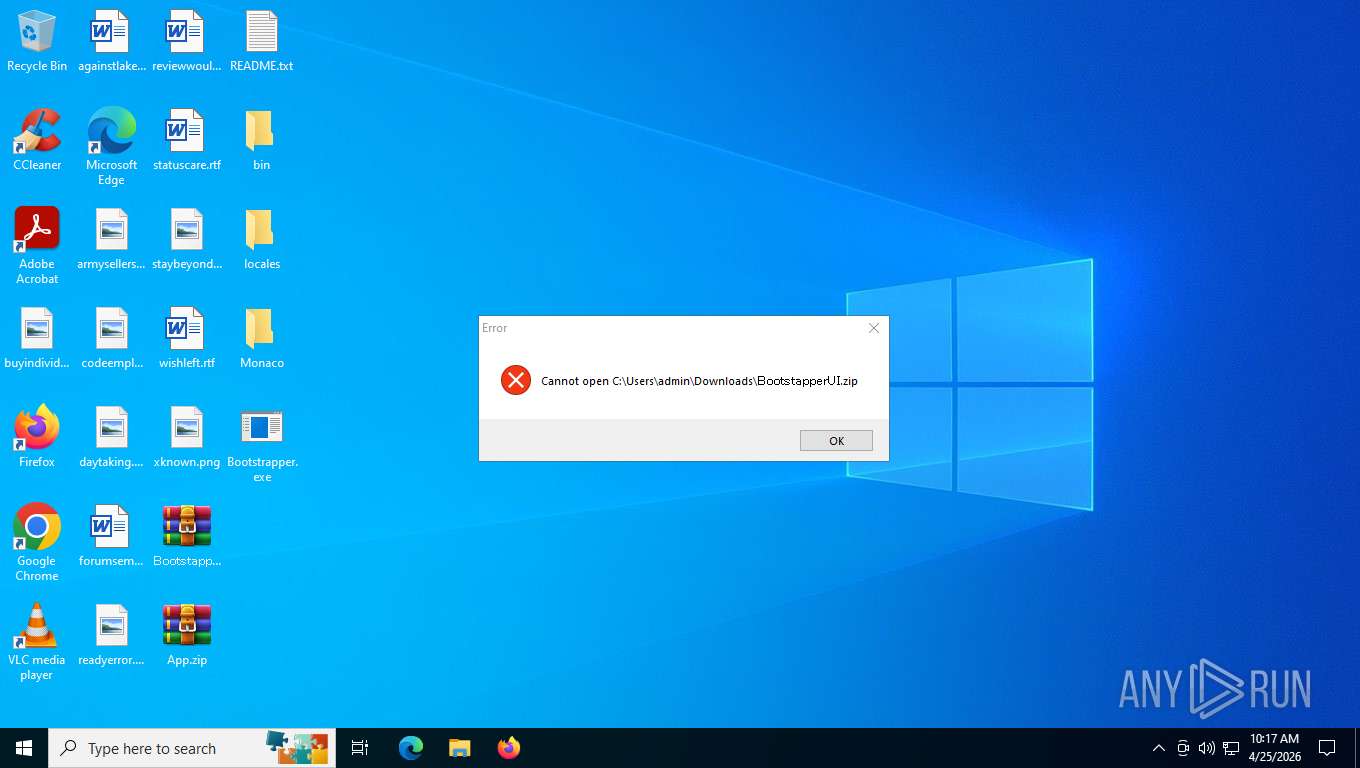
MALICIOUS
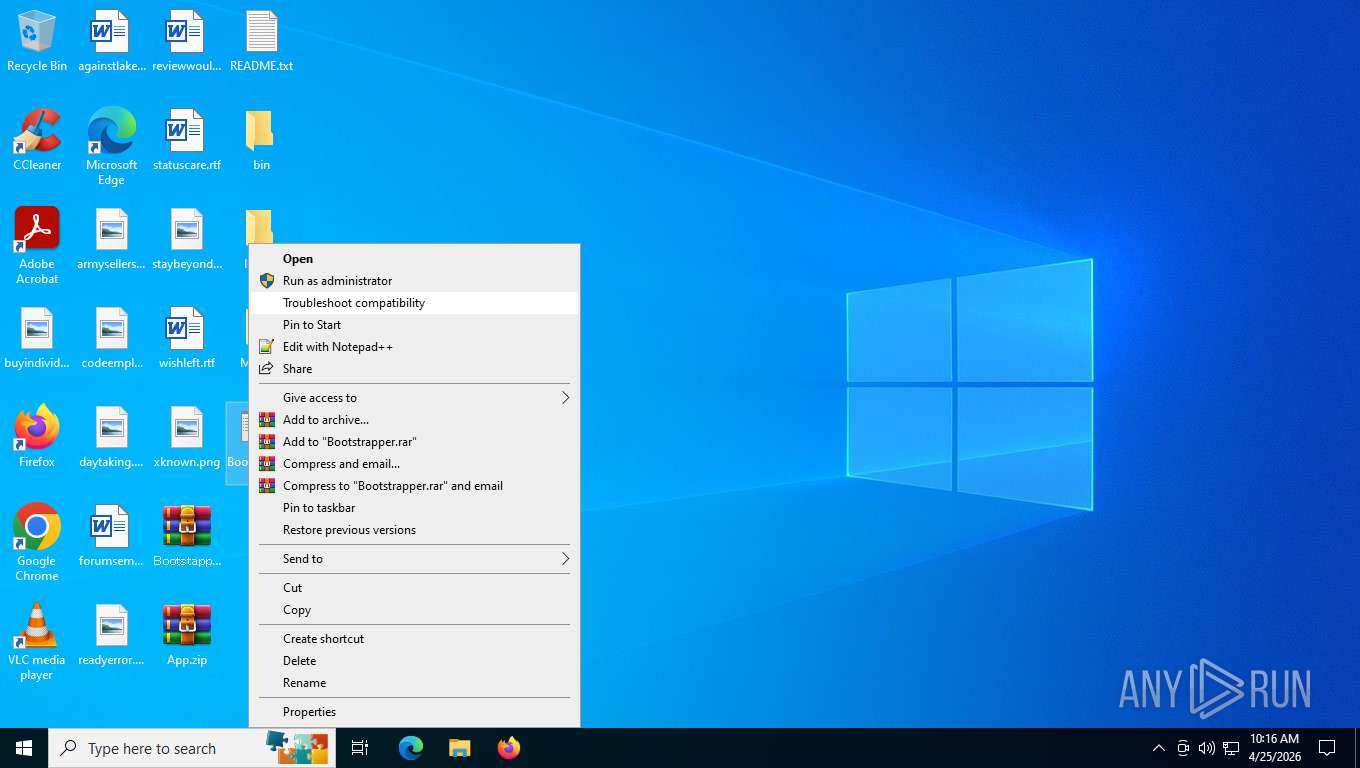
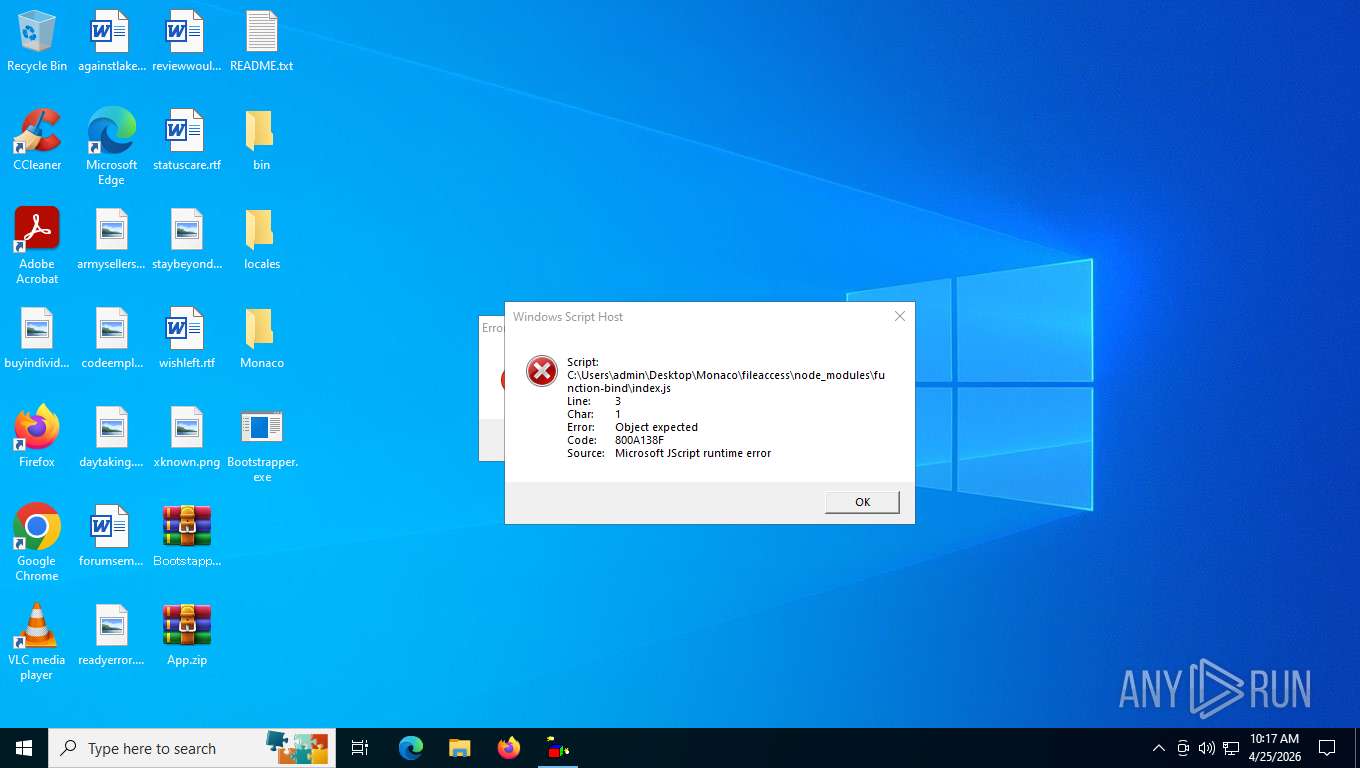
Executing a file with an untrusted certificate
- Bootstrapper.exe (PID: 8852)
Generic malicious agent network activity observed
- Bootstrapper.exe (PID: 8852)
SUSPICIOUS
Possible stealing from crypto wallets
- Bootstrapper.exe (PID: 8852)
Possible stealing from 2fa
- Bootstrapper.exe (PID: 8852)
Possible stealing of cloud data
- Bootstrapper.exe (PID: 8852)
Possible stealing of VPN data
- Bootstrapper.exe (PID: 8852)
Possible stealing of messenger data
- Bootstrapper.exe (PID: 8852)
Possible stealing from password managers
- Bootstrapper.exe (PID: 8852)
Possible stealing from notes
- Bootstrapper.exe (PID: 8852)
Possible stealing of FTP data
- Bootstrapper.exe (PID: 8852)
INFO
Application launched itself
- chrome.exe (PID: 5196)
- chrome.exe (PID: 4272)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 9016)
- msedge.exe (PID: 8324)
- msedge.exe (PID: 9040)
- msedge.exe (PID: 8664)
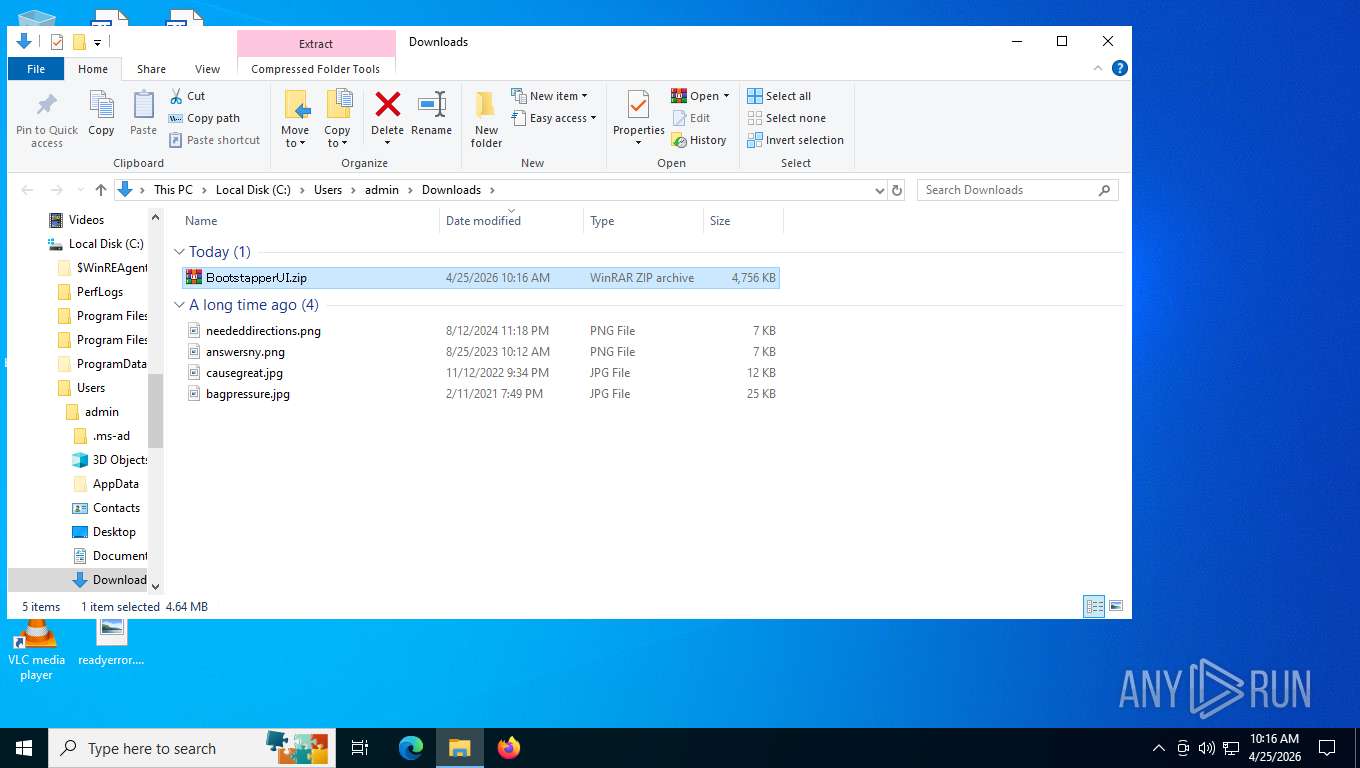
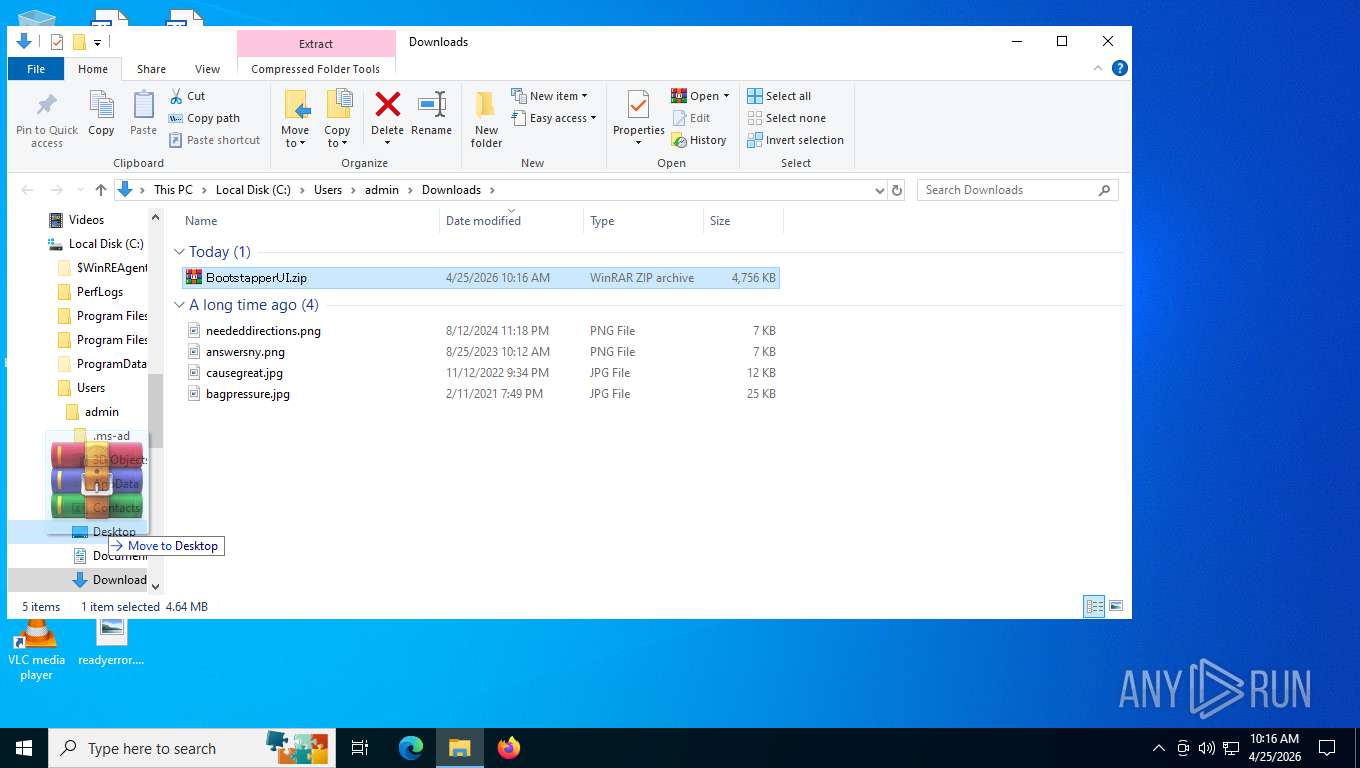
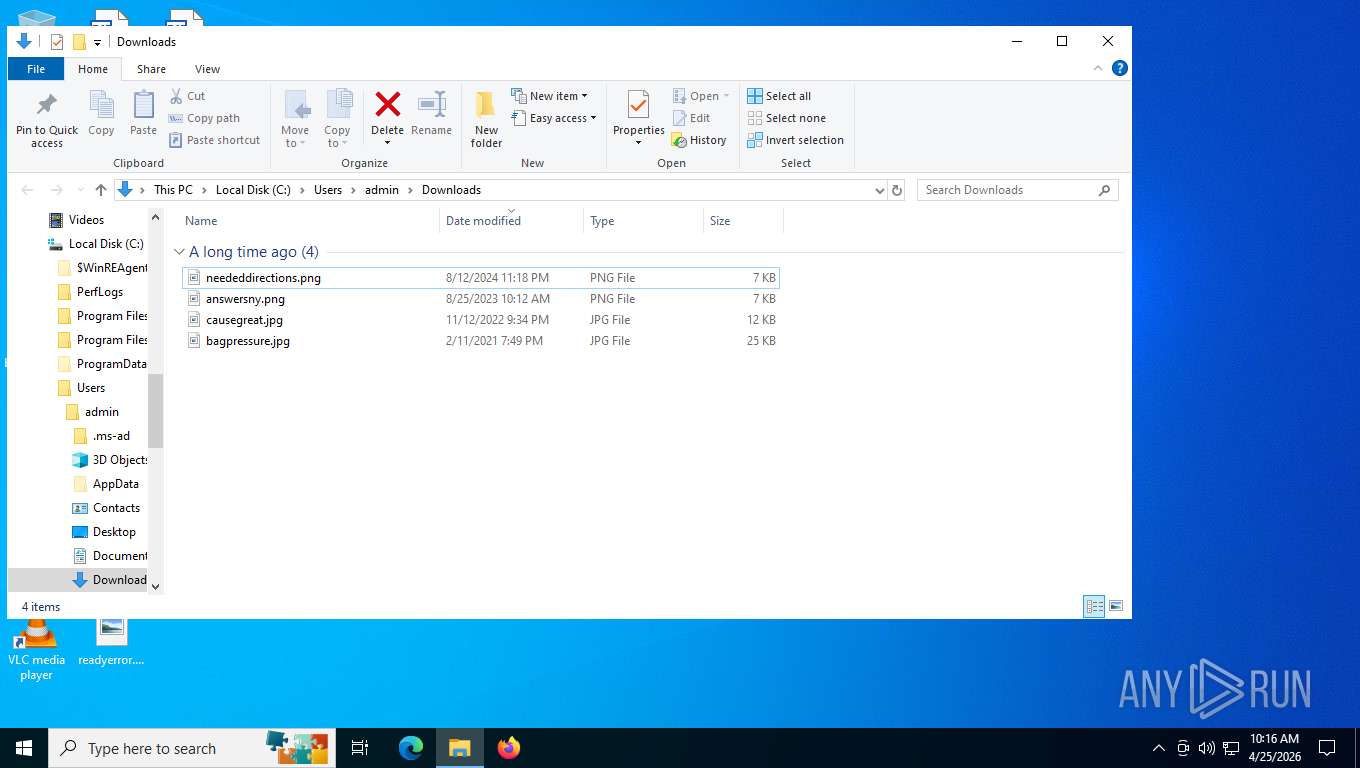
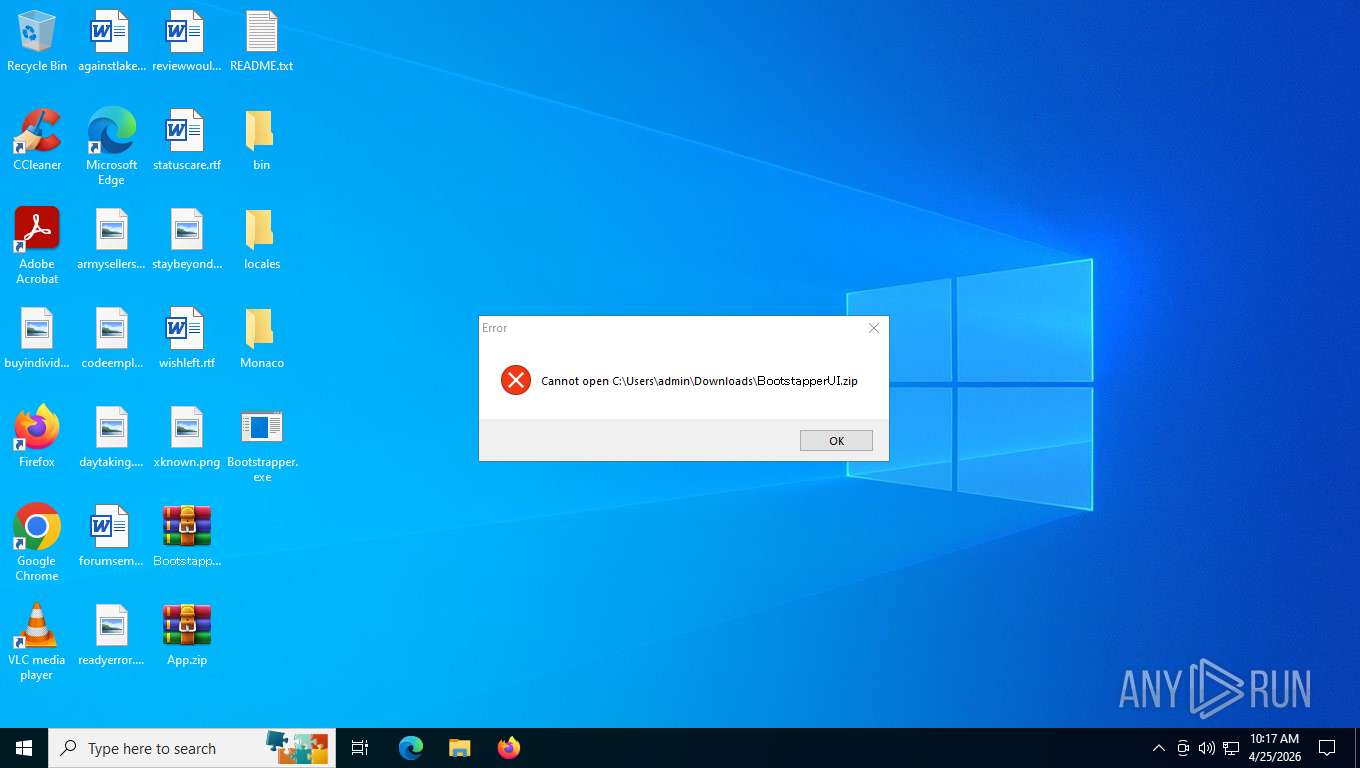
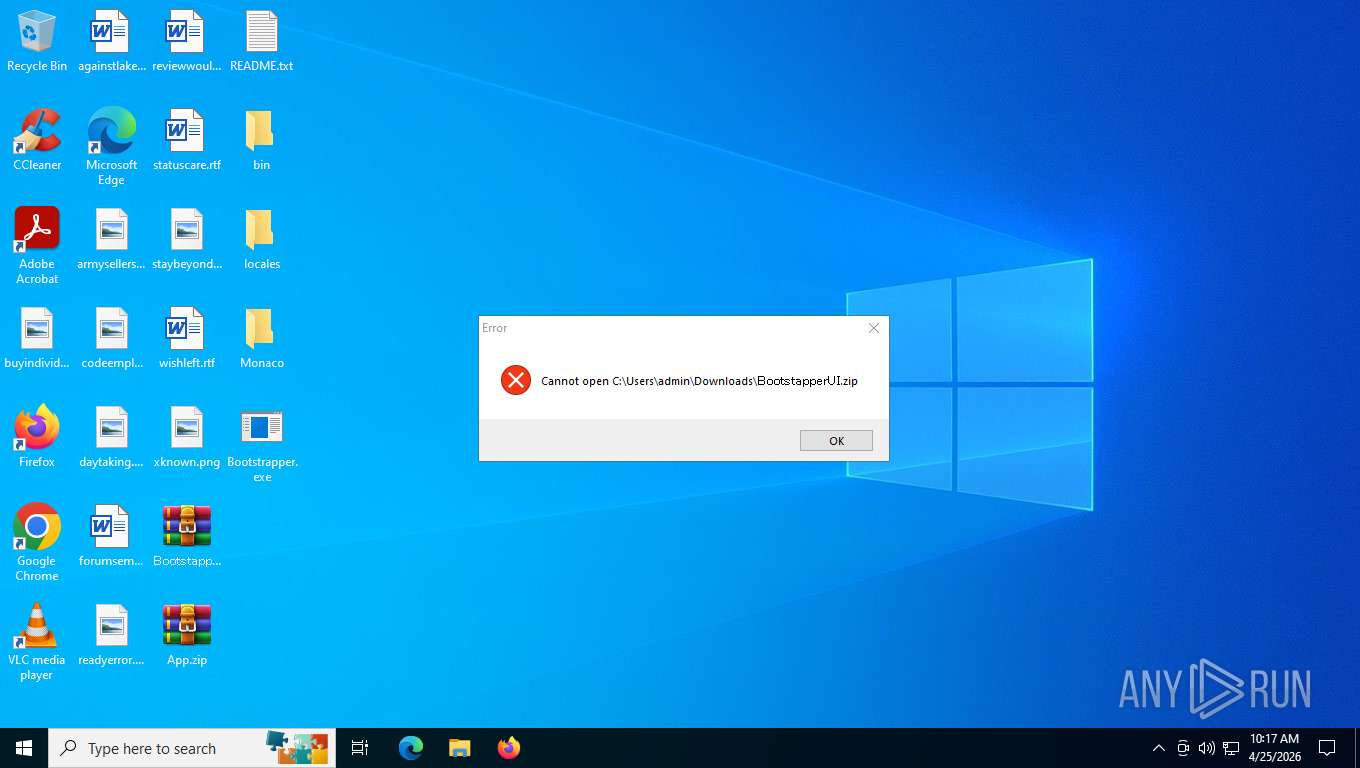
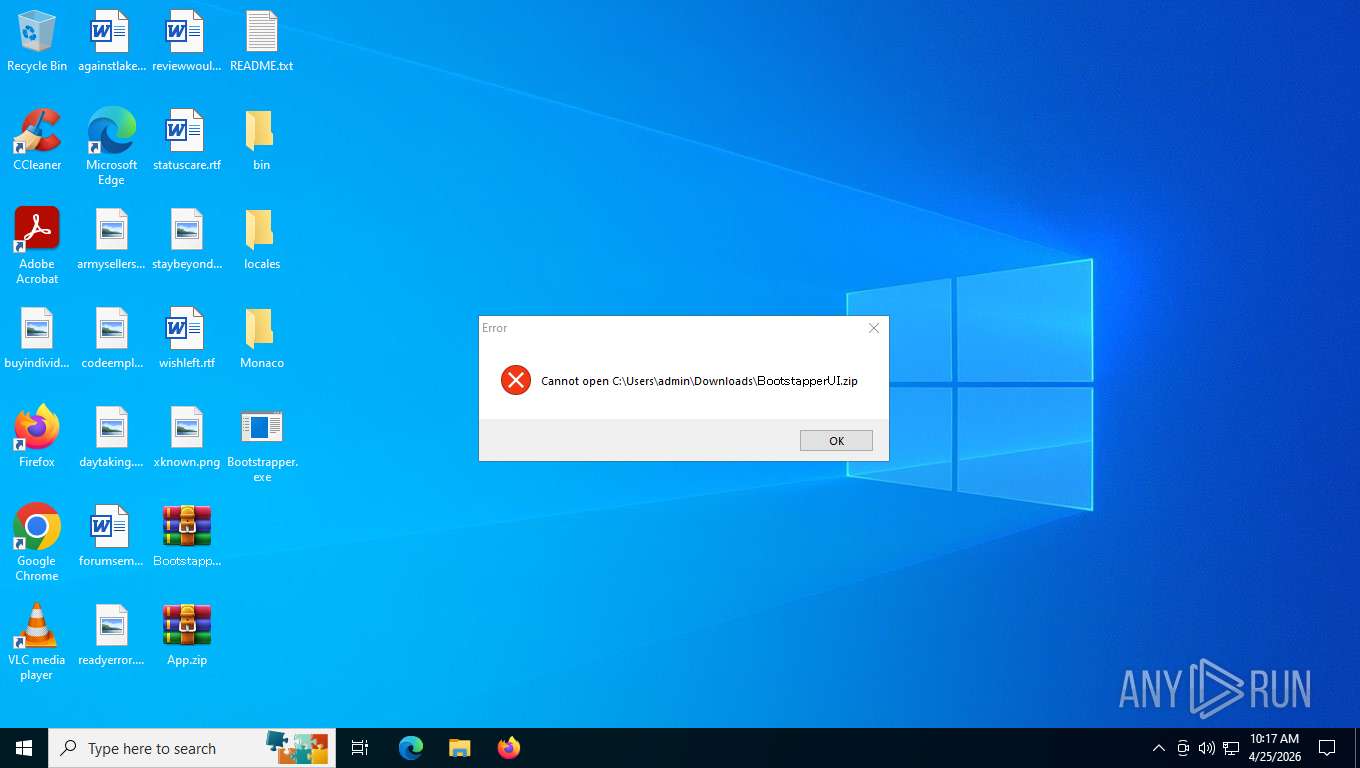
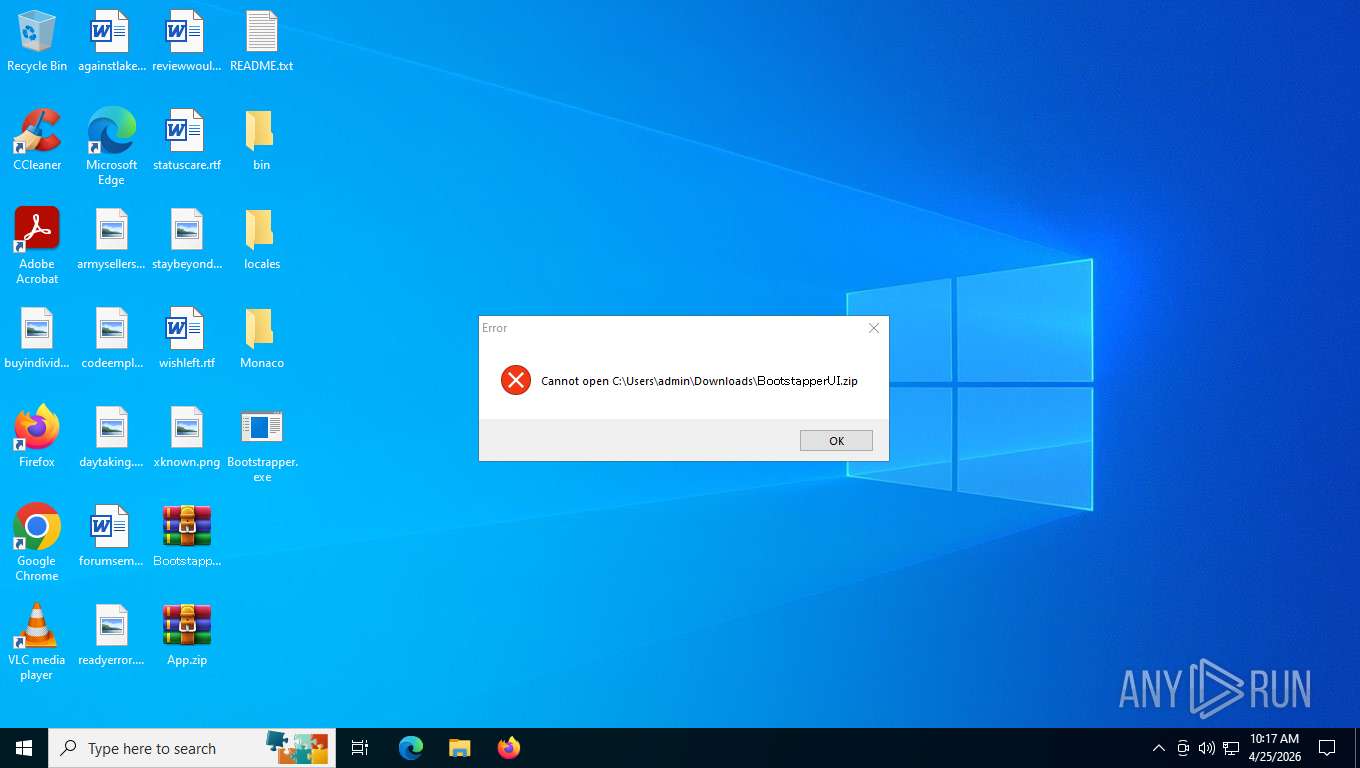
Launching a file from the Downloads directory
- chrome.exe (PID: 5196)
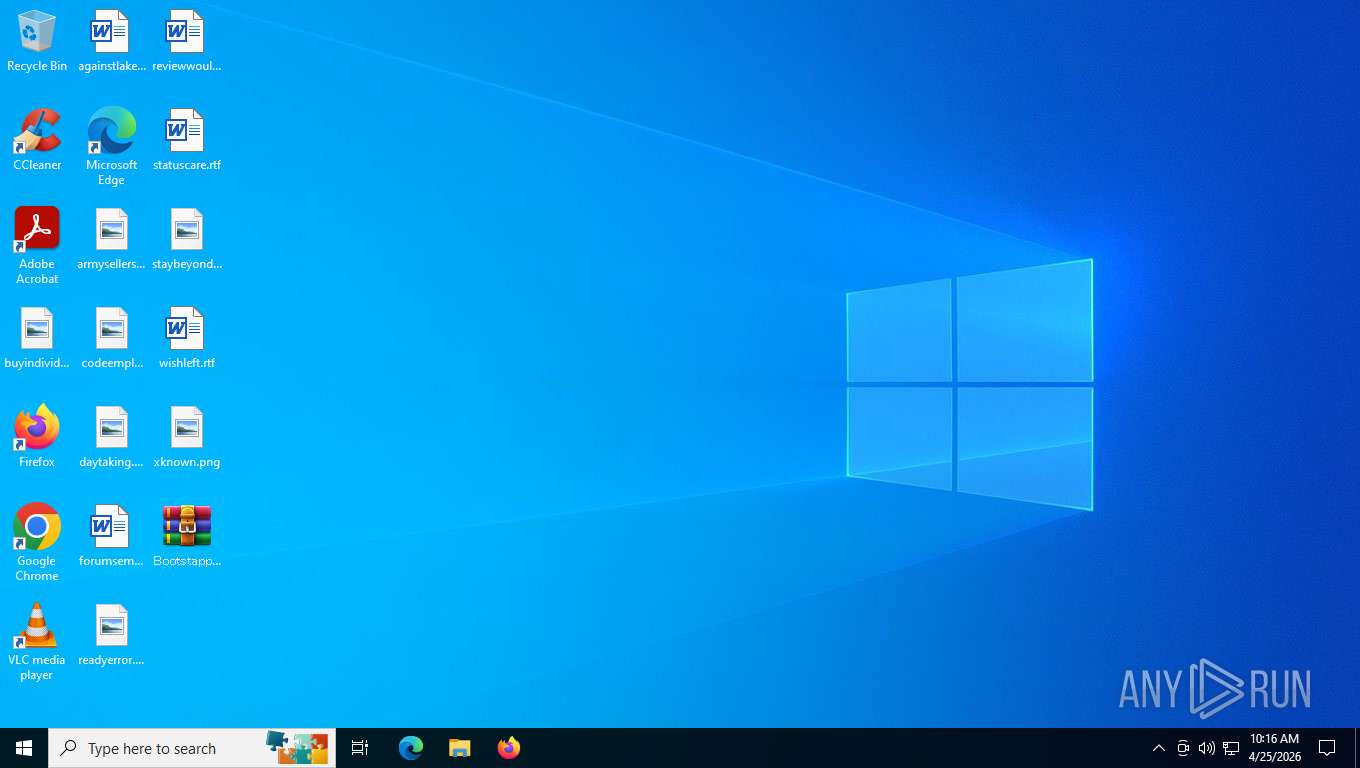
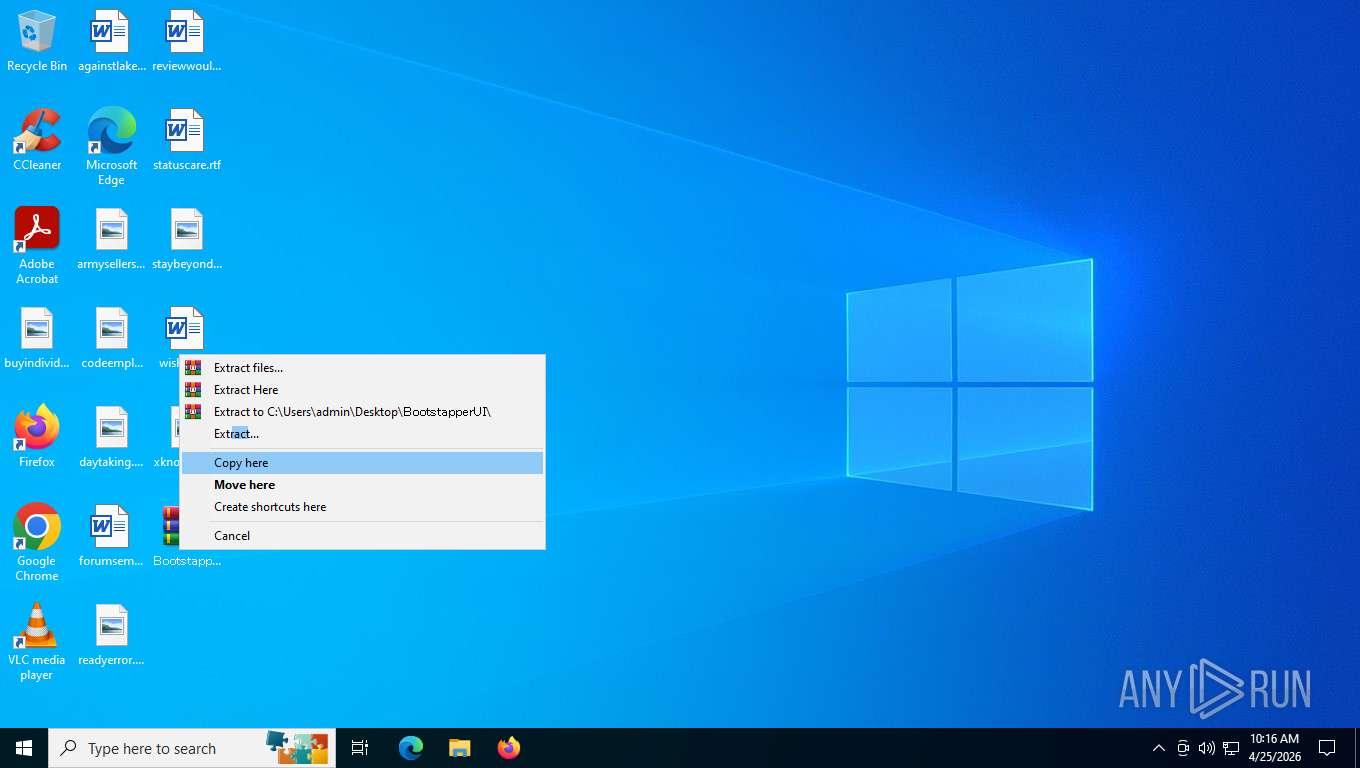
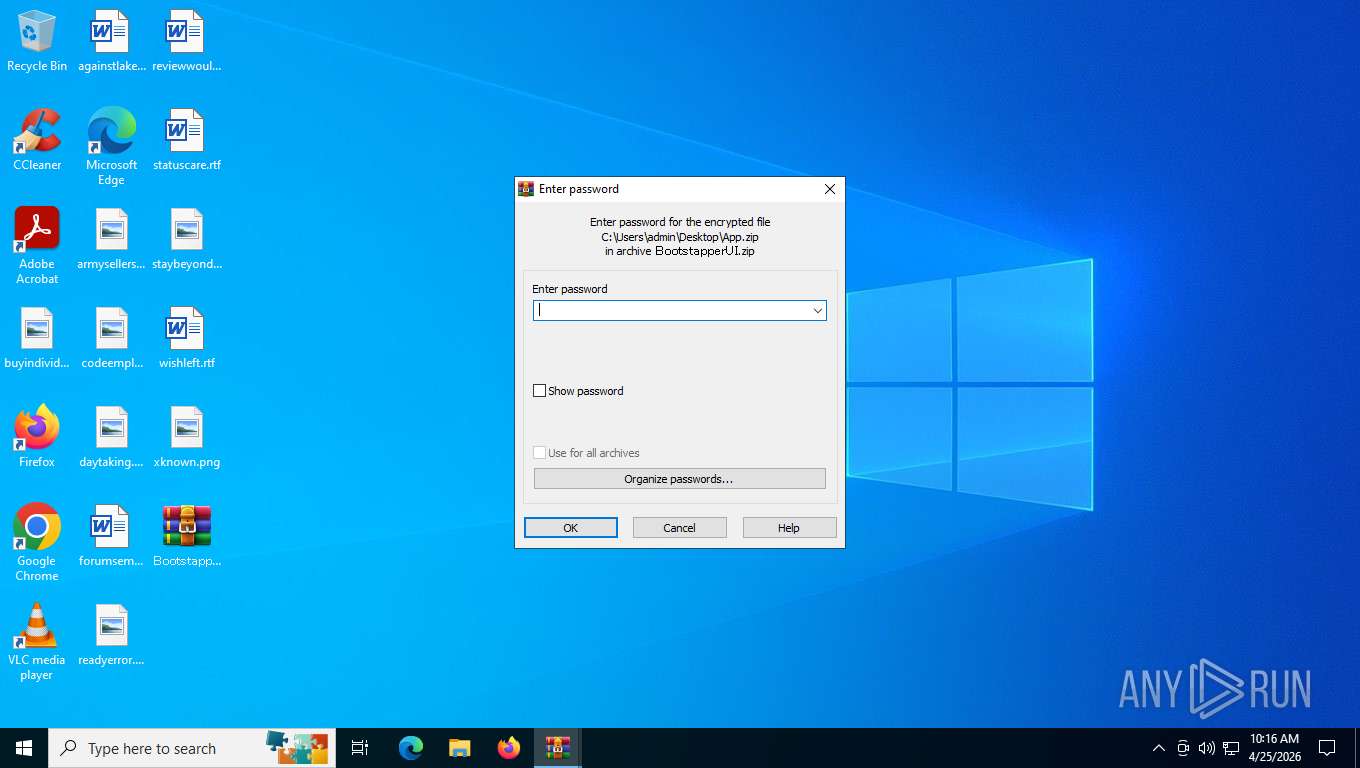
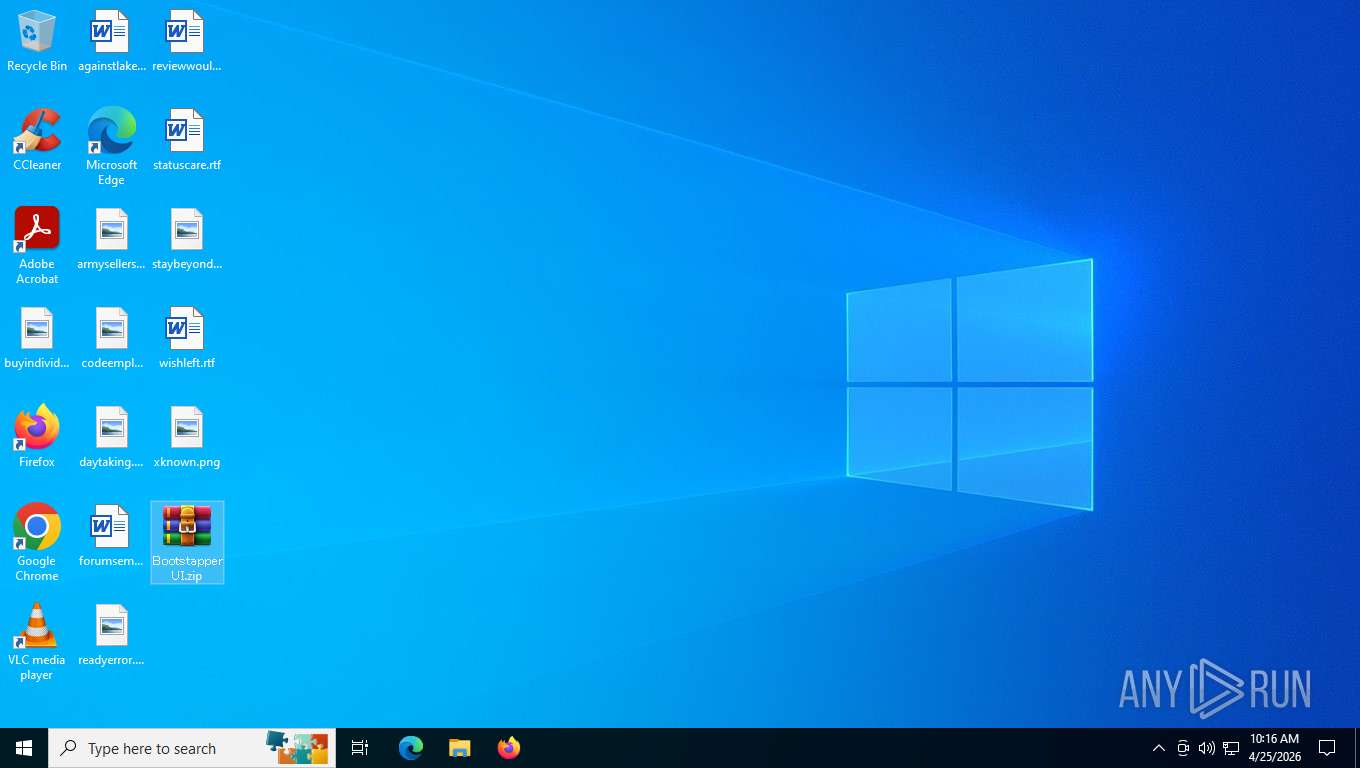
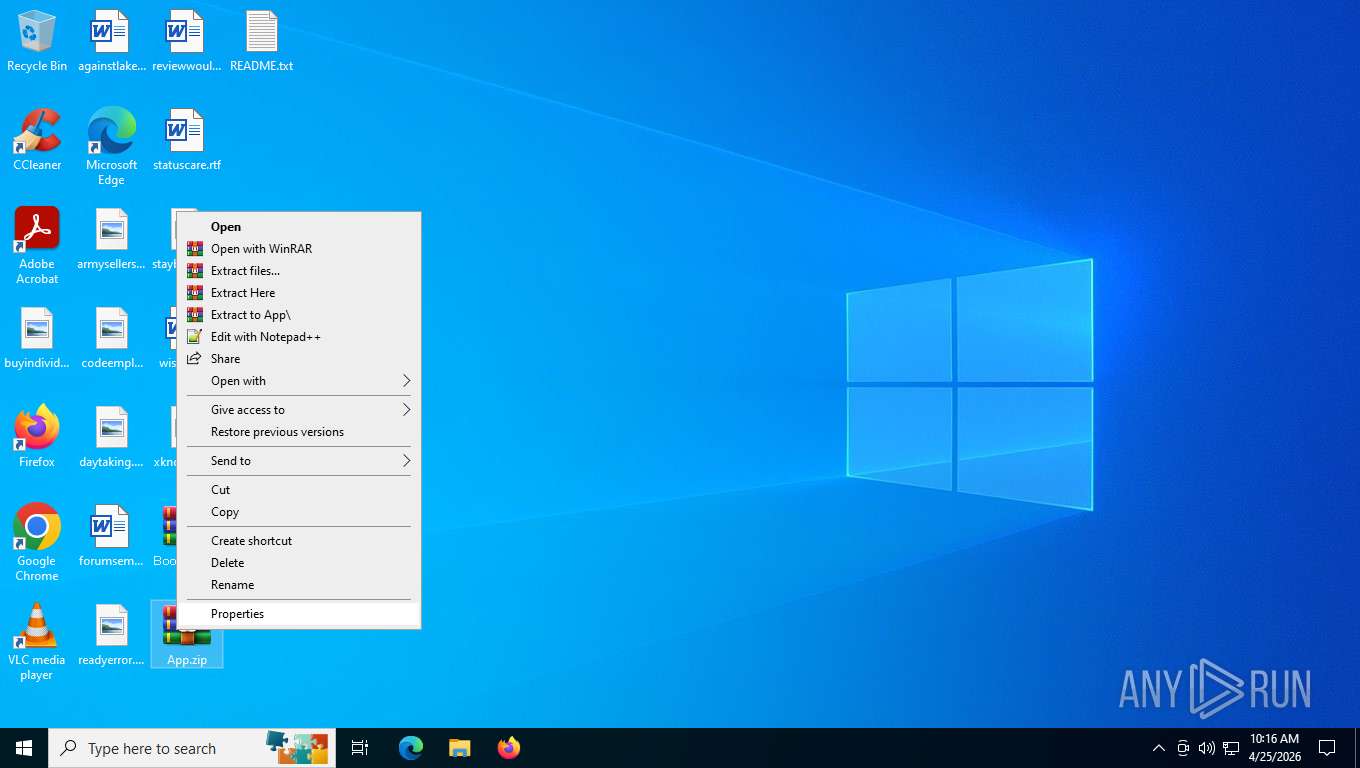
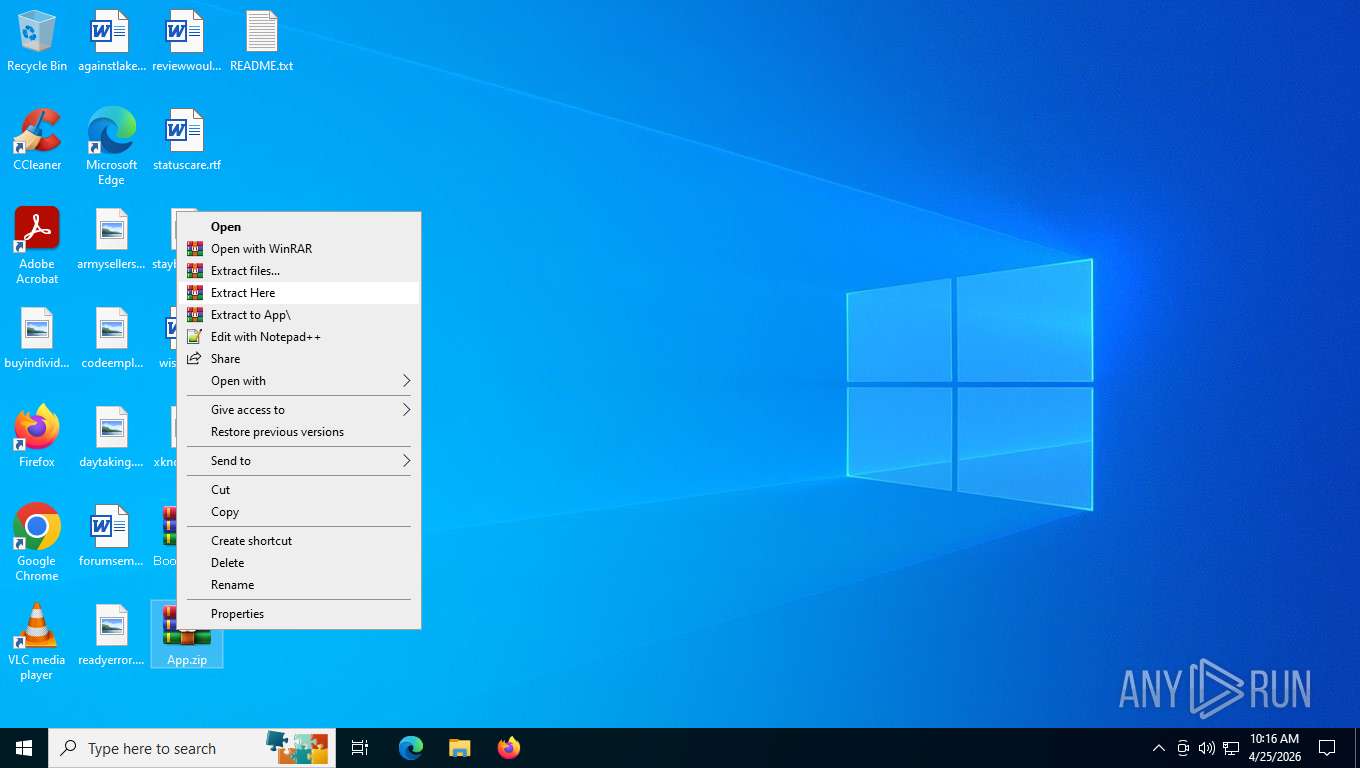
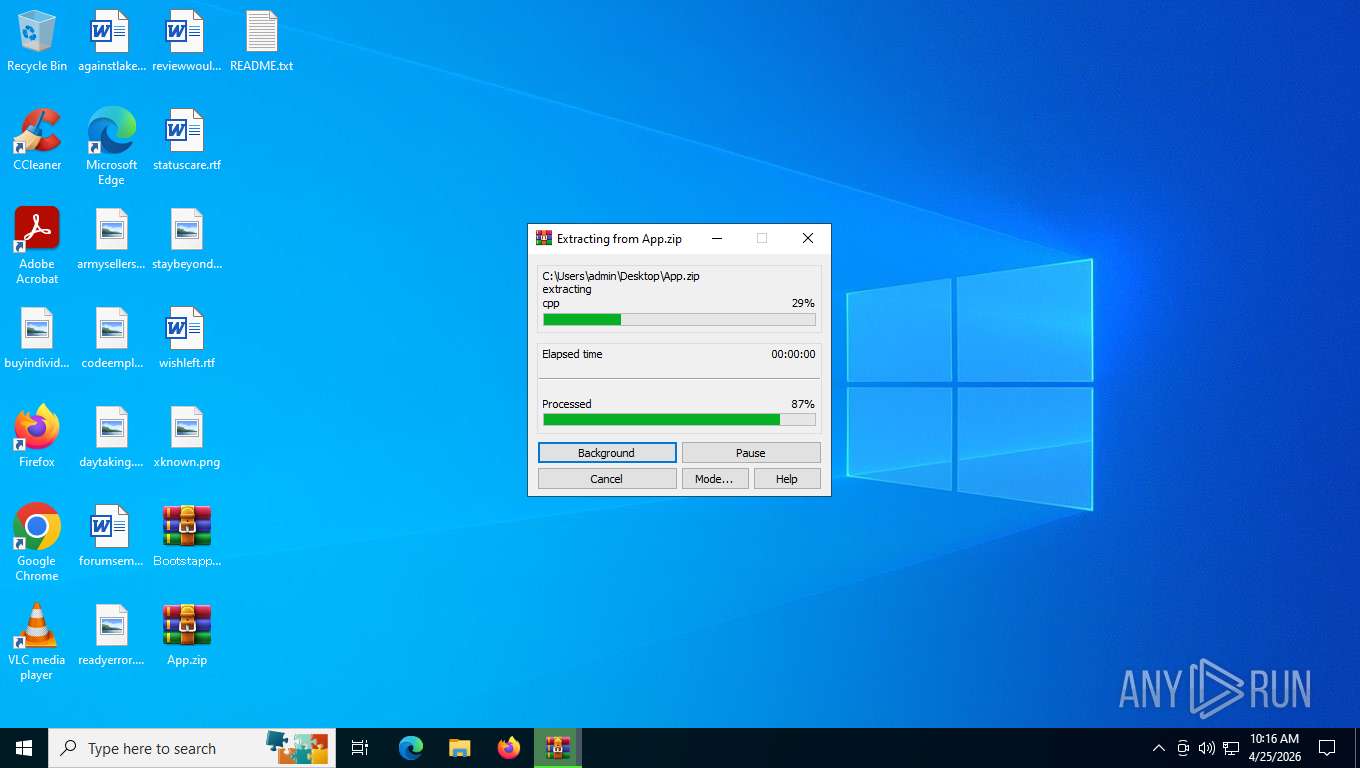
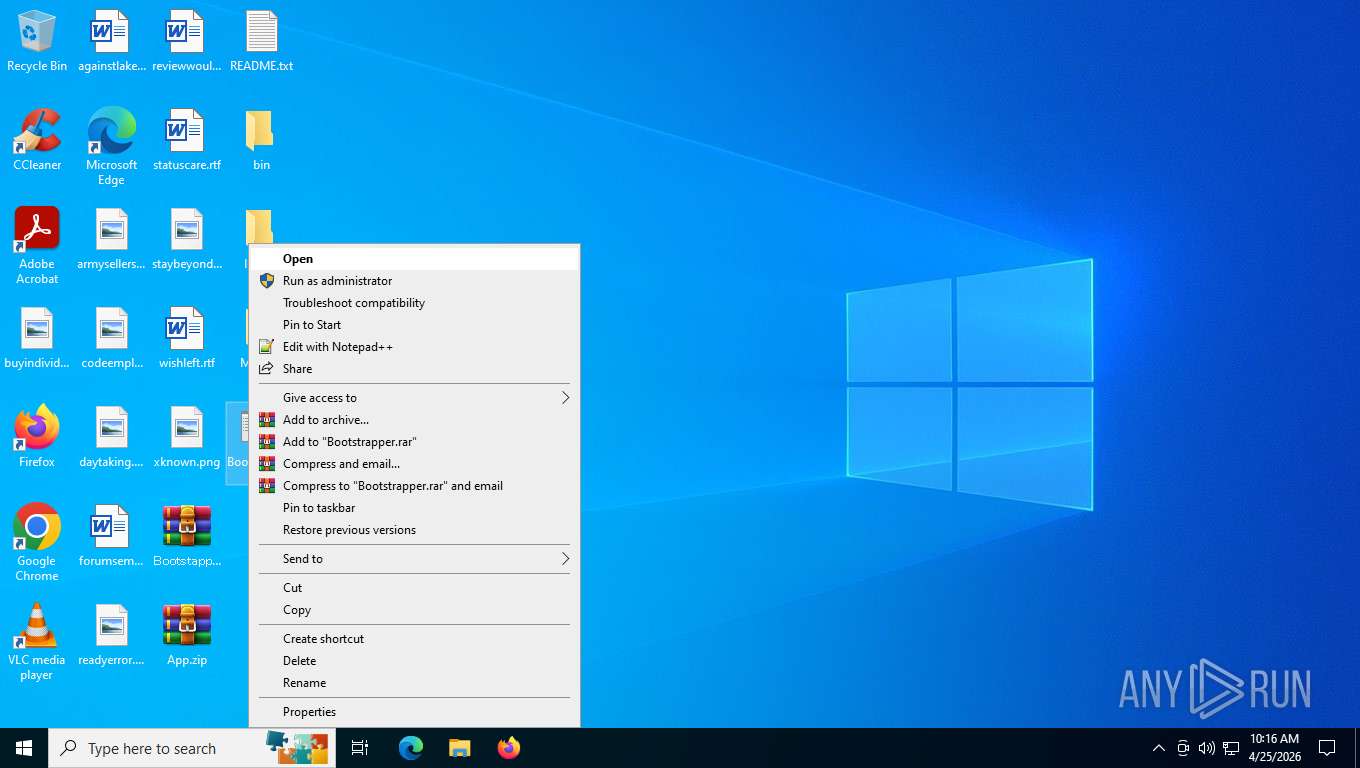
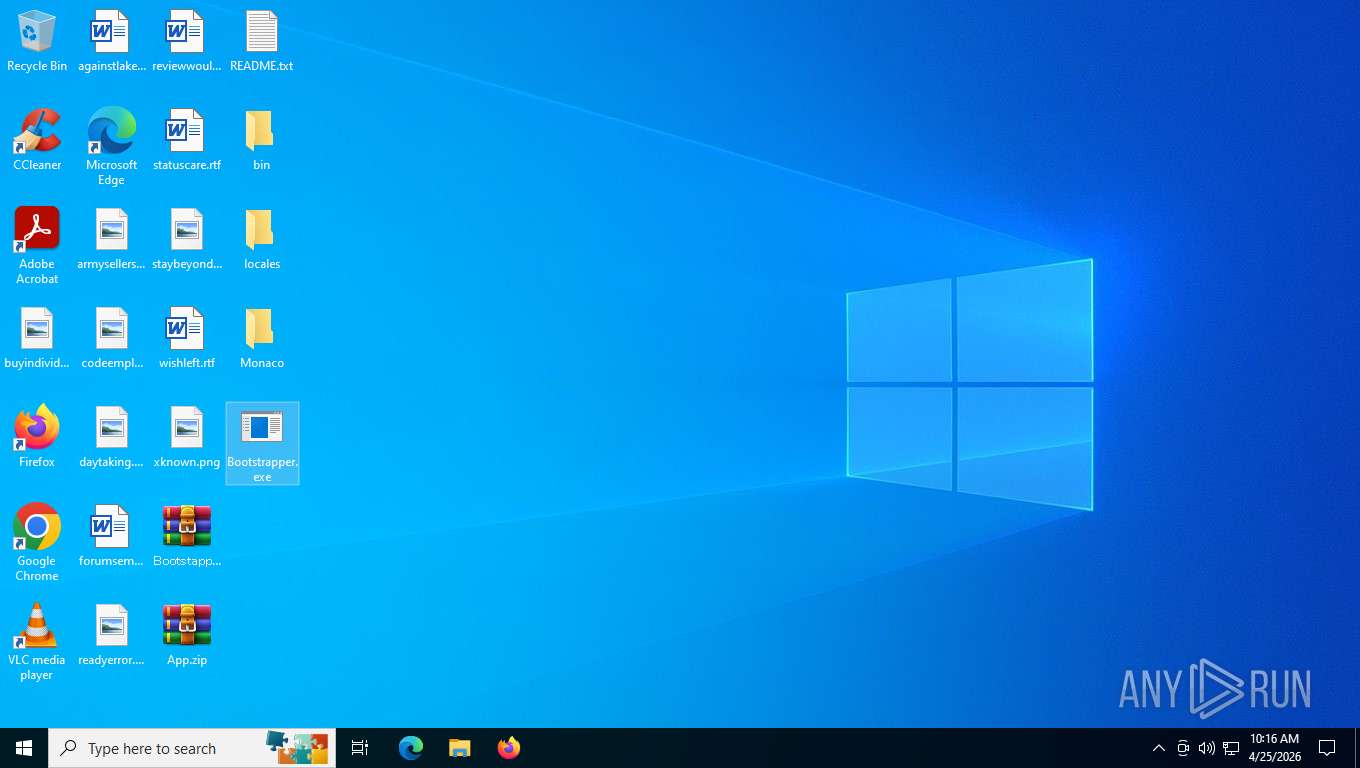
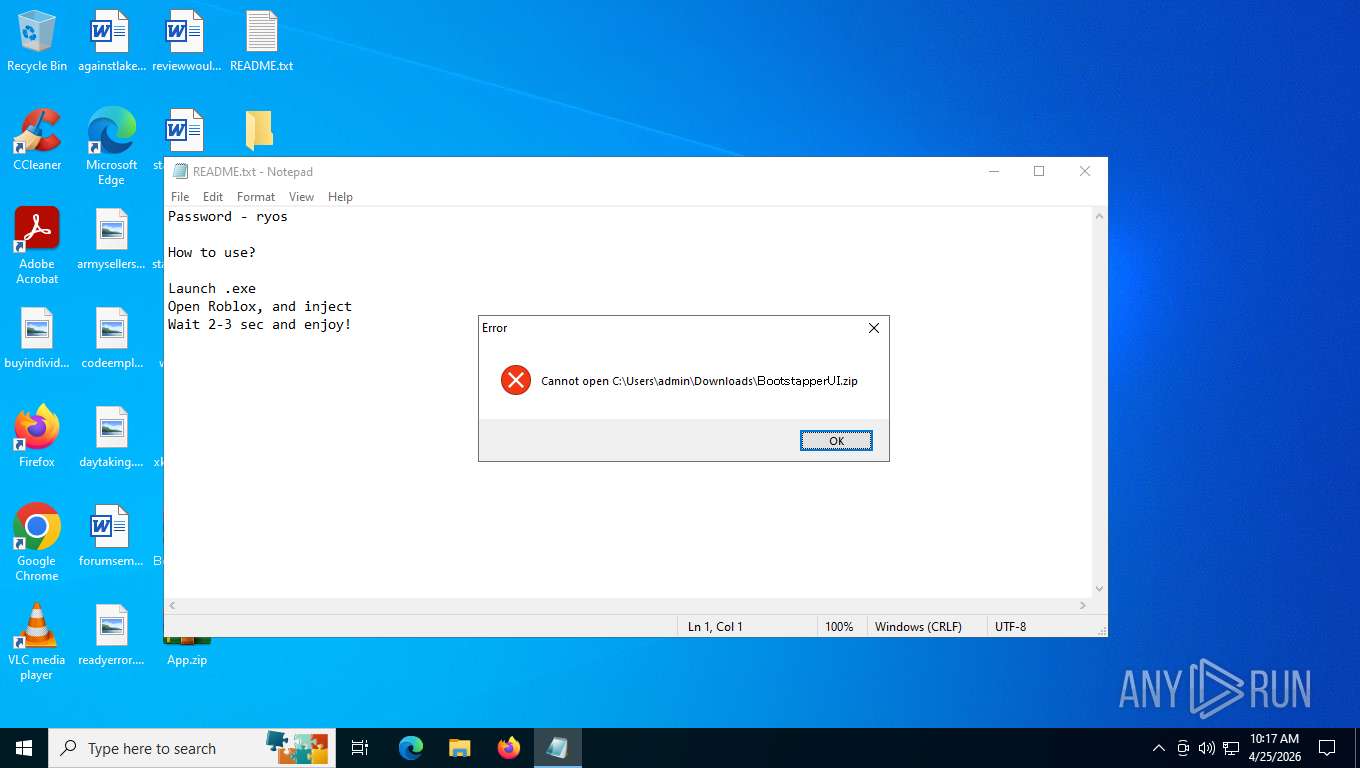
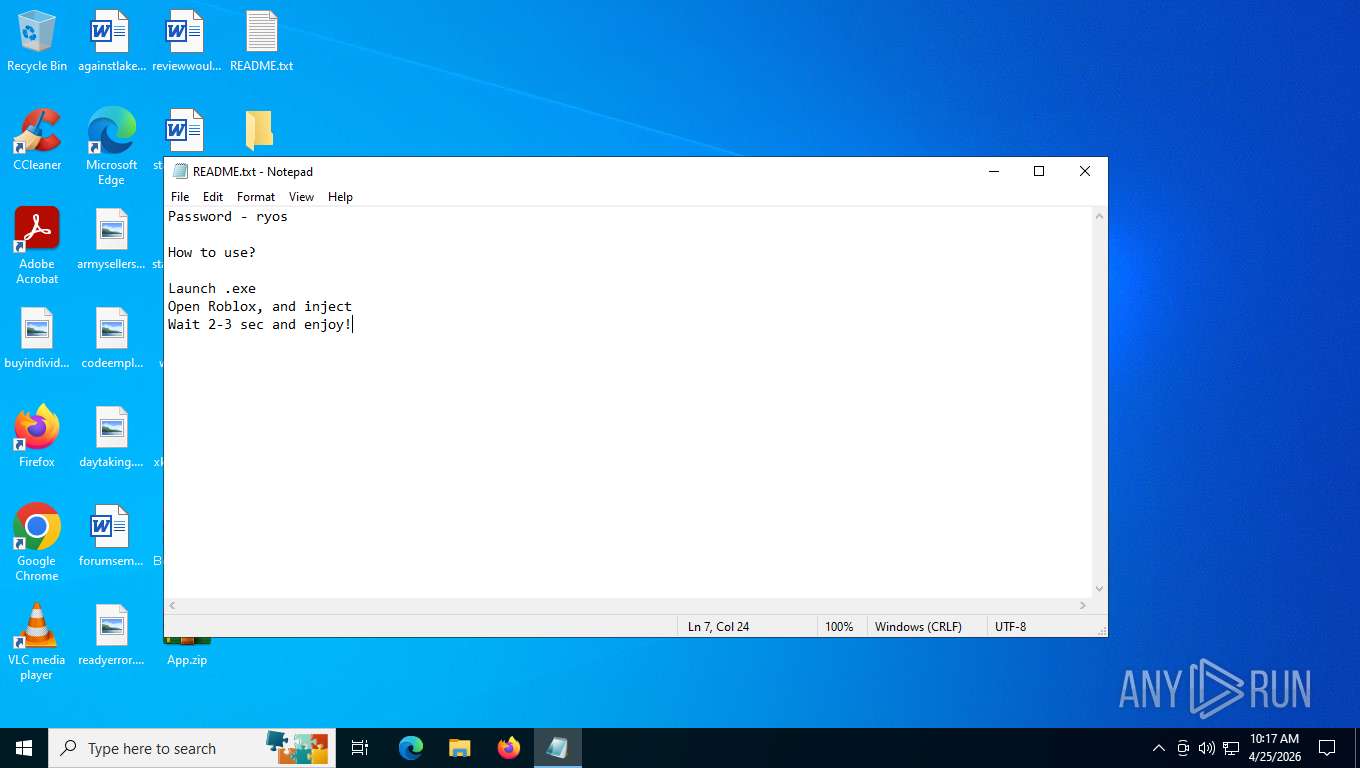
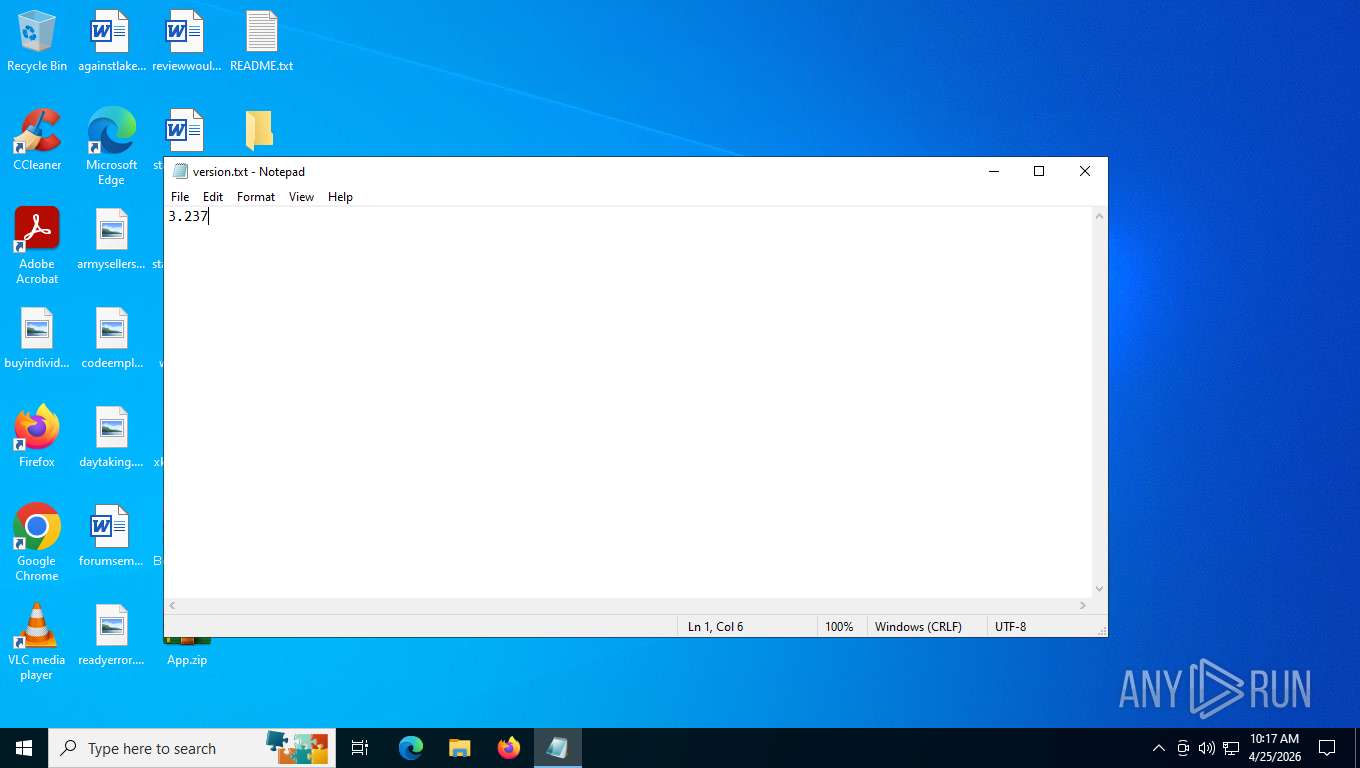
Manual execution by a user
- Bootstrapper.exe (PID: 8852)
- WinRAR.exe (PID: 8620)
- WinRAR.exe (PID: 8804)
- notepad.exe (PID: 9132)
- WinRAR.exe (PID: 5412)
- wscript.exe (PID: 8388)
- wscript.exe (PID: 9180)
- wscript.exe (PID: 4348)
- wscript.exe (PID: 5524)
- wscript.exe (PID: 7880)
- wscript.exe (PID: 9148)
- wscript.exe (PID: 9140)
- wscript.exe (PID: 8988)
- wscript.exe (PID: 6504)
- wscript.exe (PID: 3104)
- wscript.exe (PID: 7116)
- wscript.exe (PID: 5304)
- wscript.exe (PID: 8296)
- wscript.exe (PID: 6108)
- wscript.exe (PID: 7992)
- wscript.exe (PID: 9012)
- wscript.exe (PID: 8400)
- wscript.exe (PID: 8208)
- wscript.exe (PID: 1864)
- wscript.exe (PID: 4712)
- wscript.exe (PID: 6672)
- wscript.exe (PID: 5672)
- wscript.exe (PID: 3996)
- wscript.exe (PID: 7964)
- wscript.exe (PID: 8028)
- wscript.exe (PID: 6532)
- notepad.exe (PID: 5200)
- wscript.exe (PID: 3200)
- wscript.exe (PID: 4328)
Checks supported languages
- Bootstrapper.exe (PID: 8852)
- identity_helper.exe (PID: 4308)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8804)
Reads the computer name
- Bootstrapper.exe (PID: 8852)
- identity_helper.exe (PID: 4308)
Application based on Golang
- Bootstrapper.exe (PID: 8852)
There is functionality for taking screenshot (YARA)
- Bootstrapper.exe (PID: 8852)
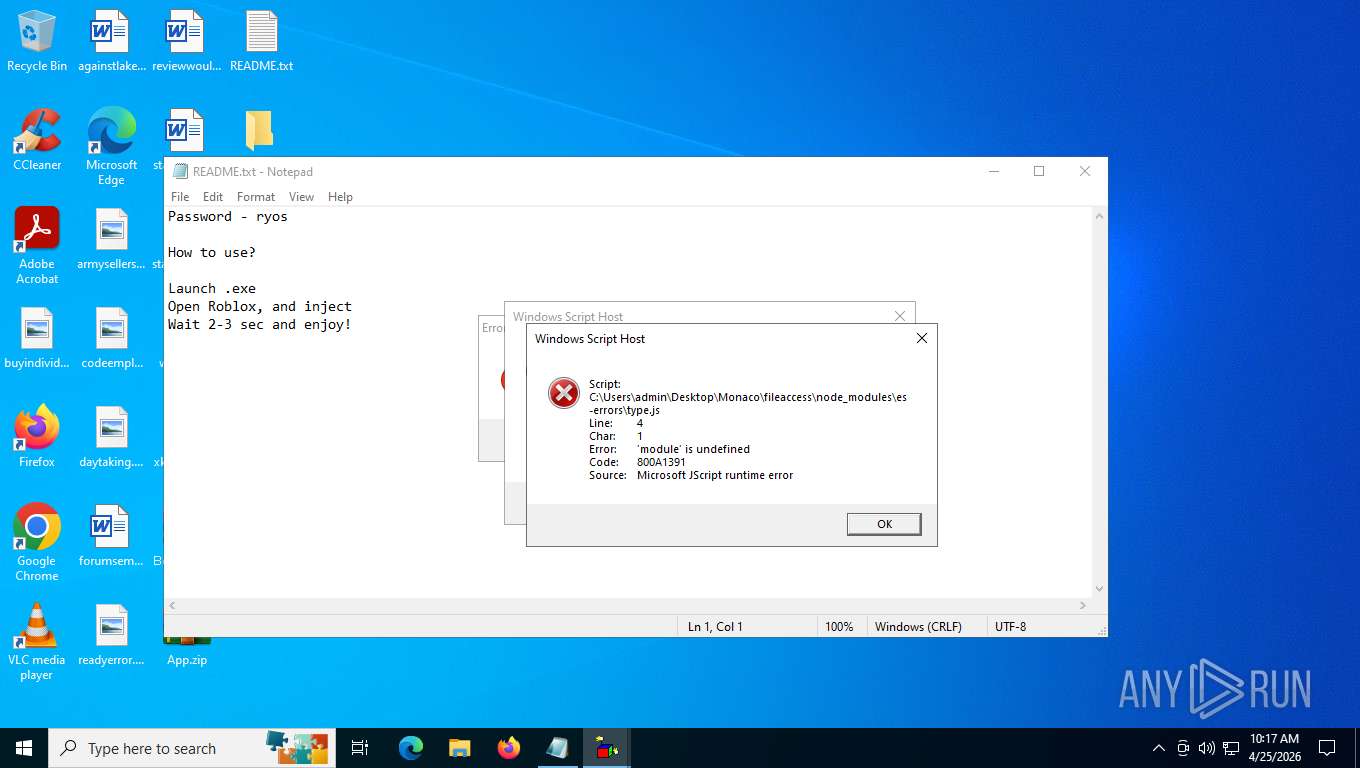
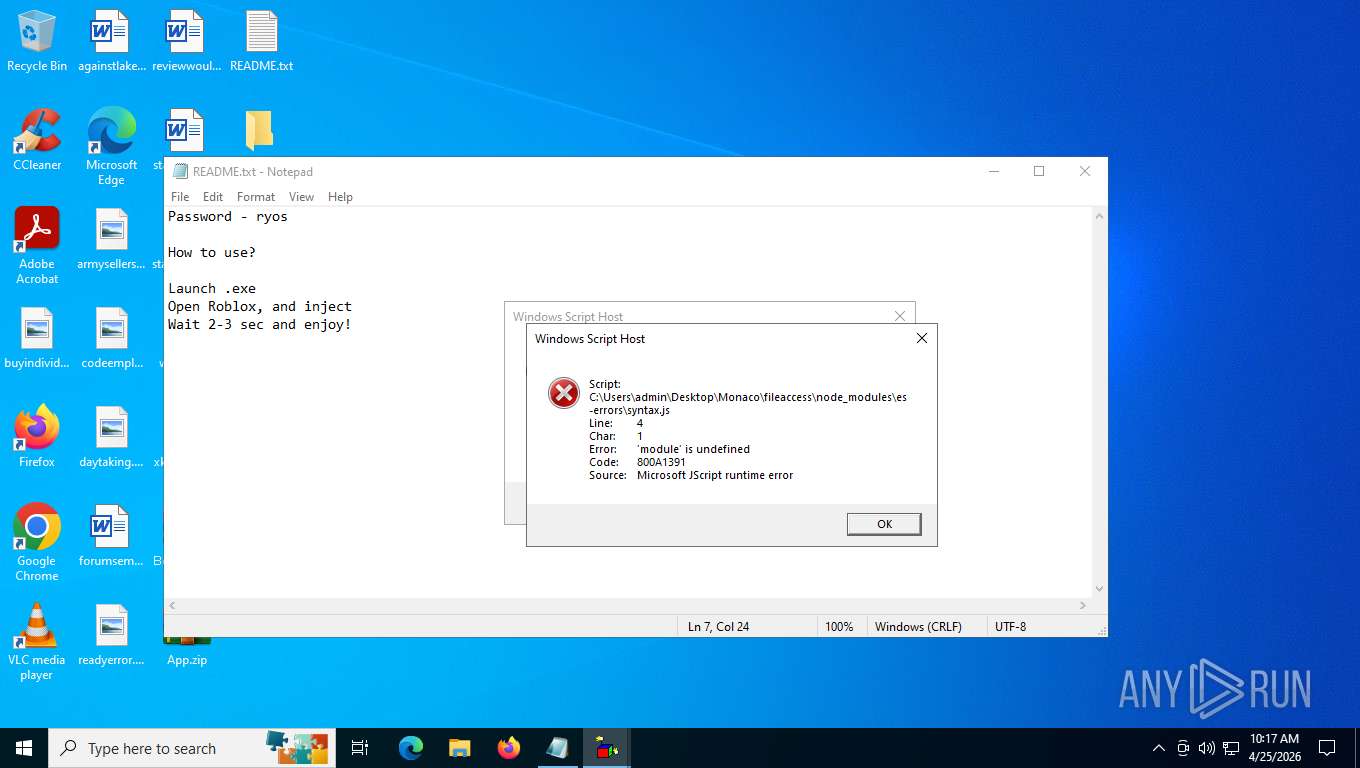
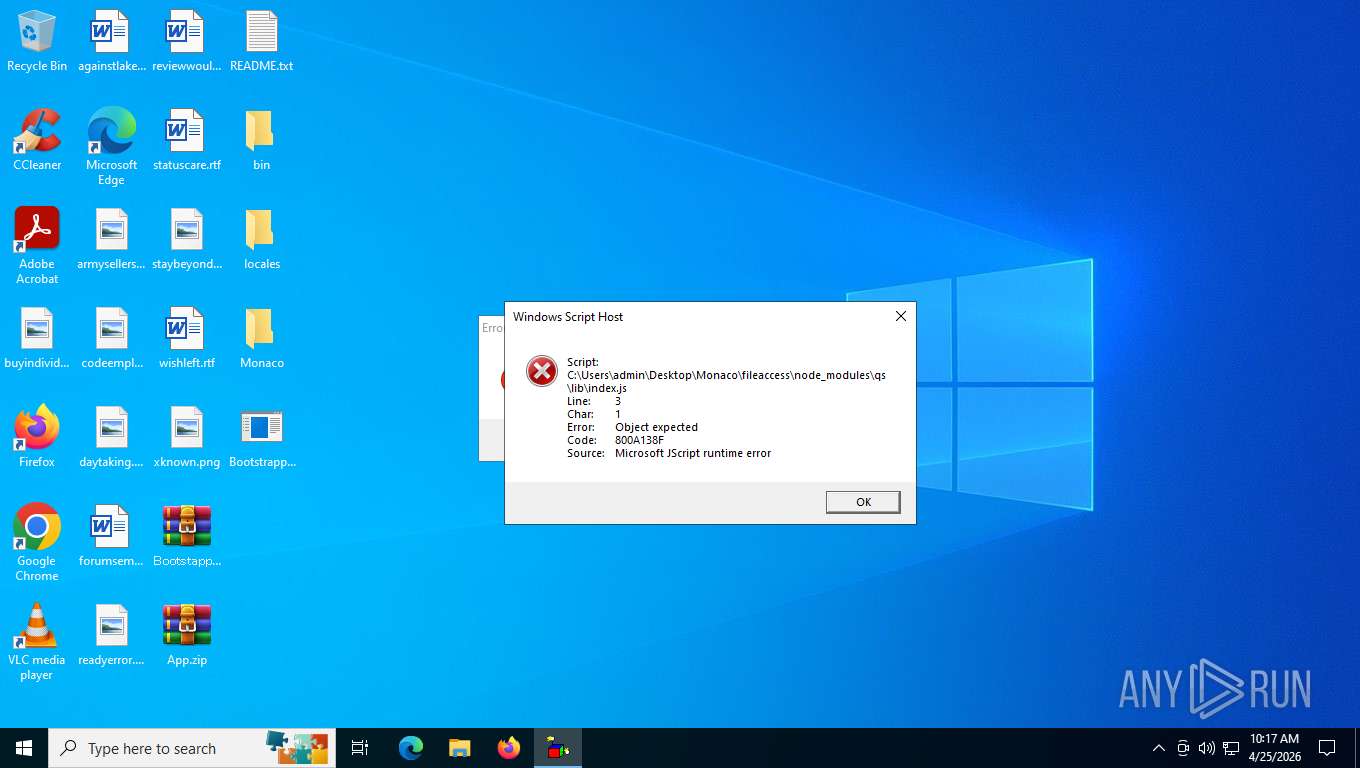
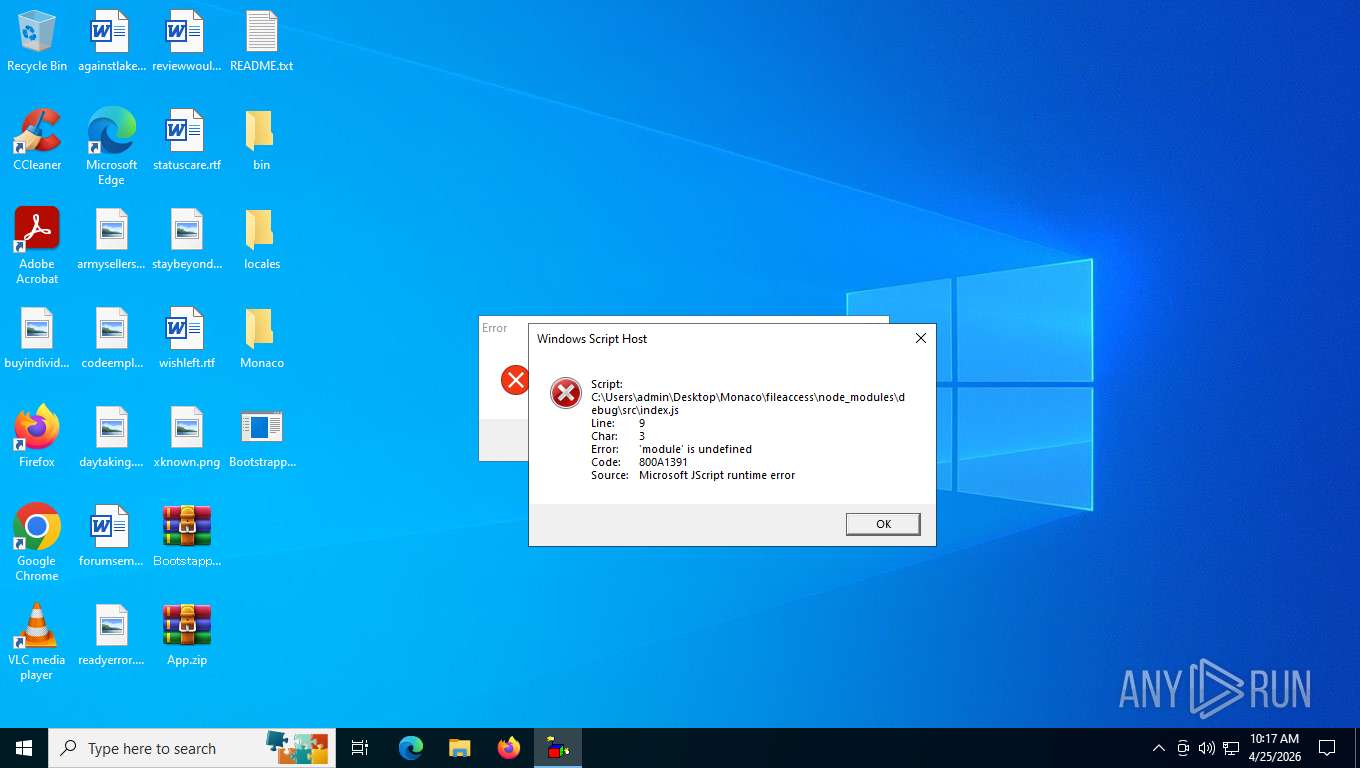
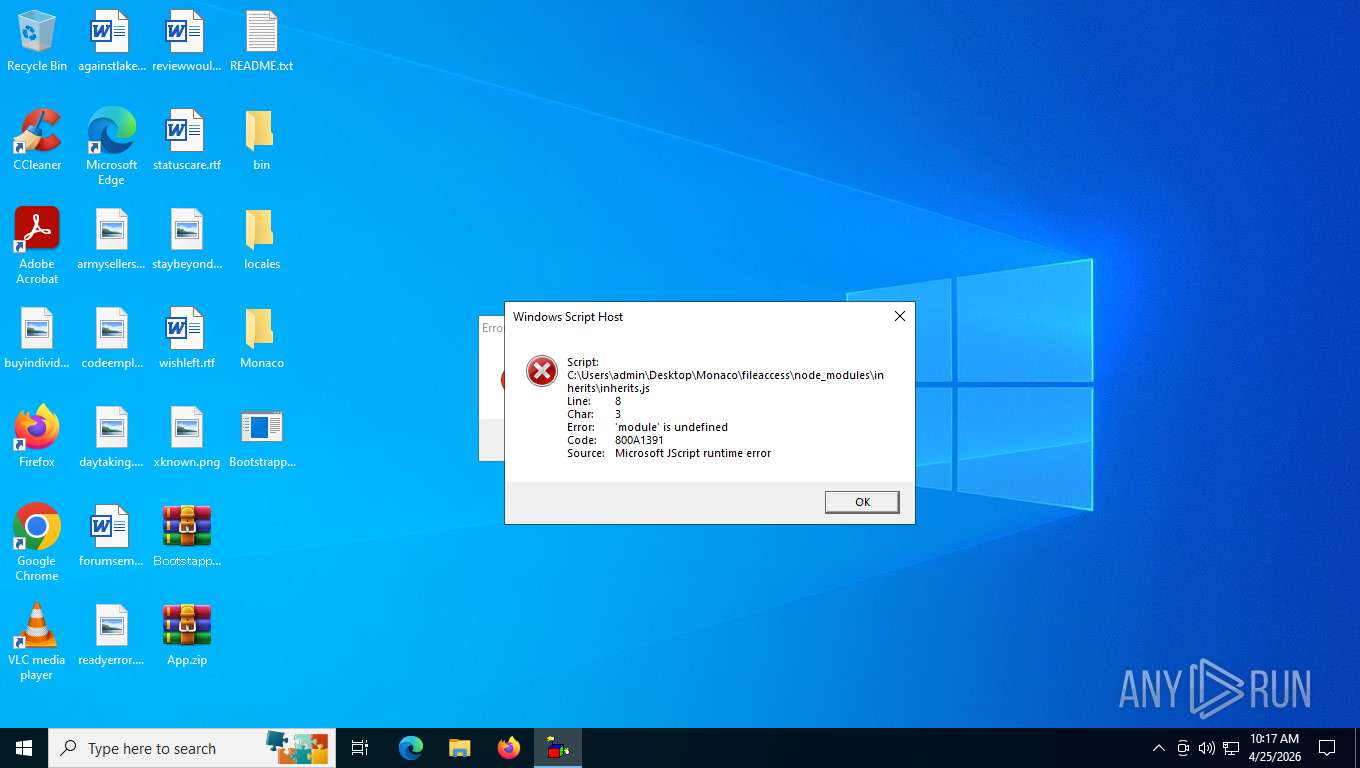
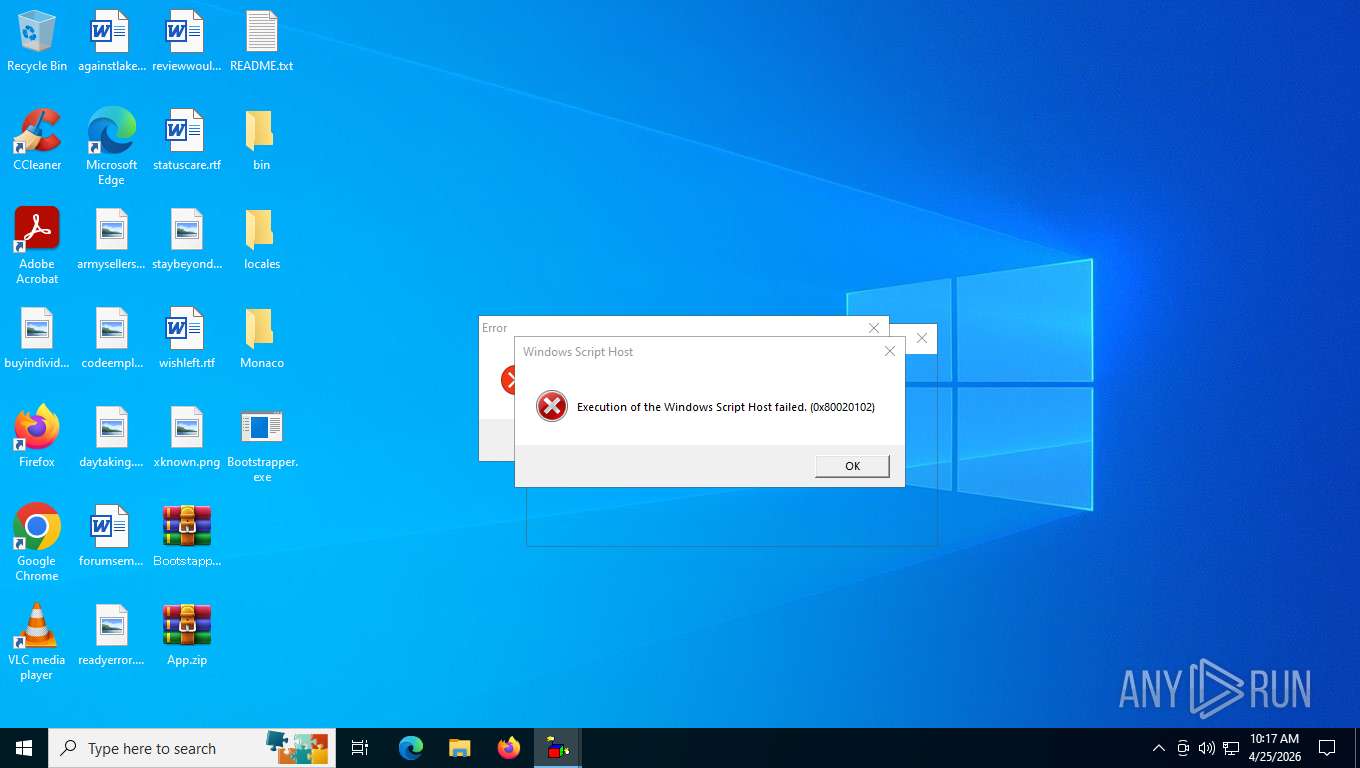
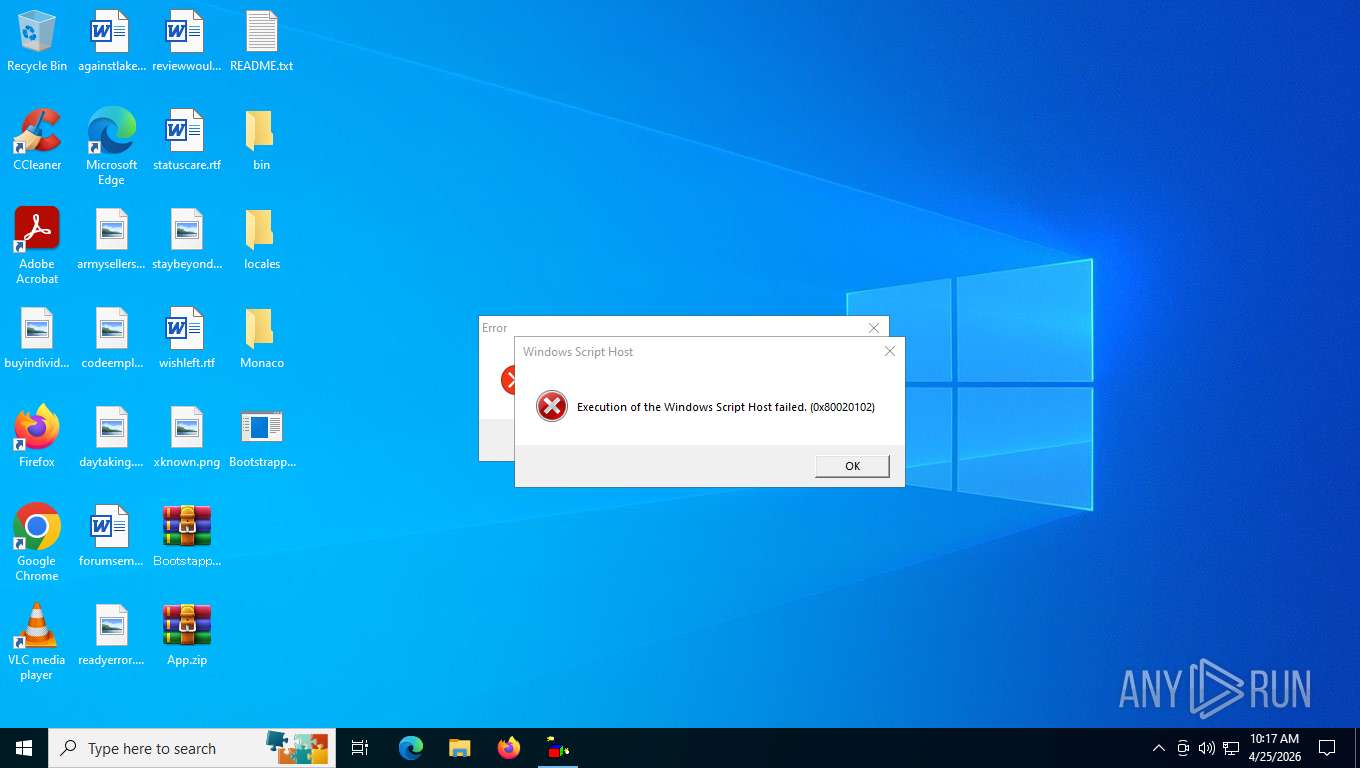
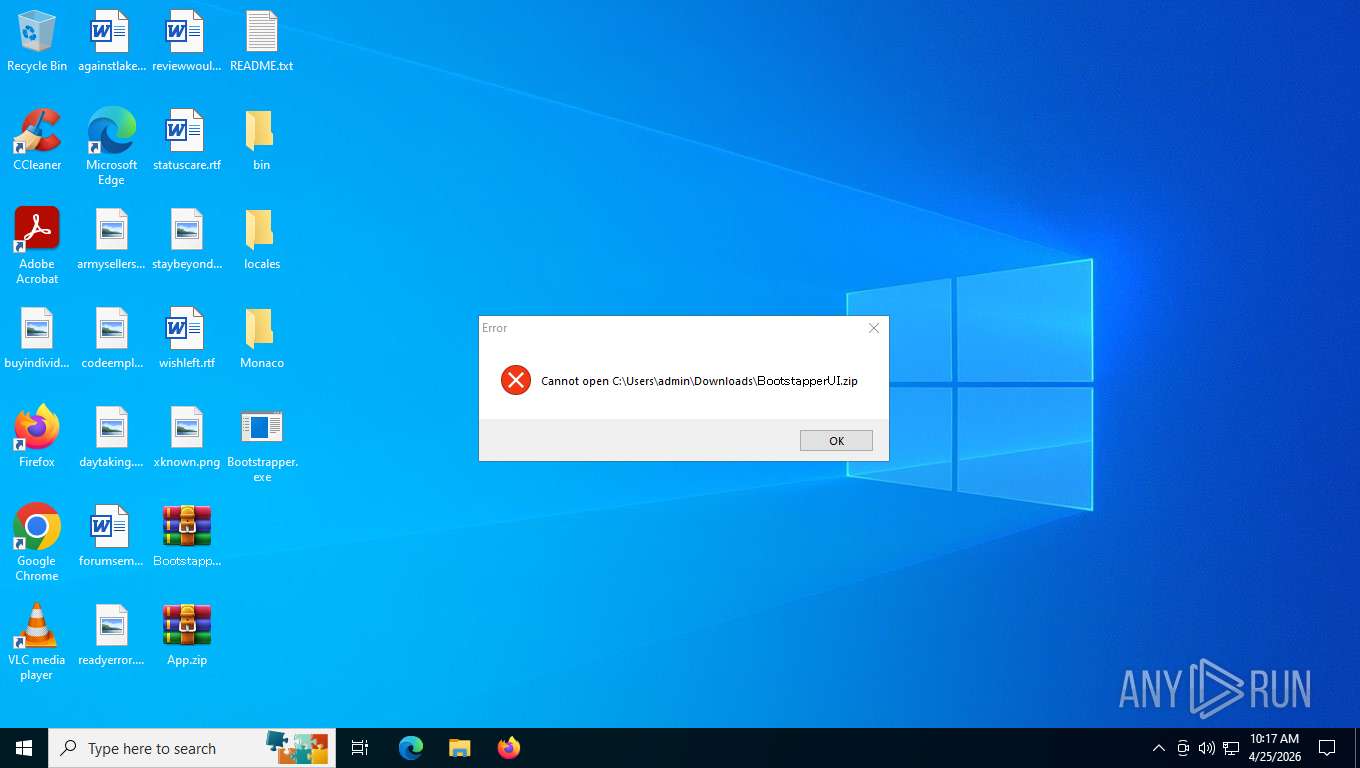
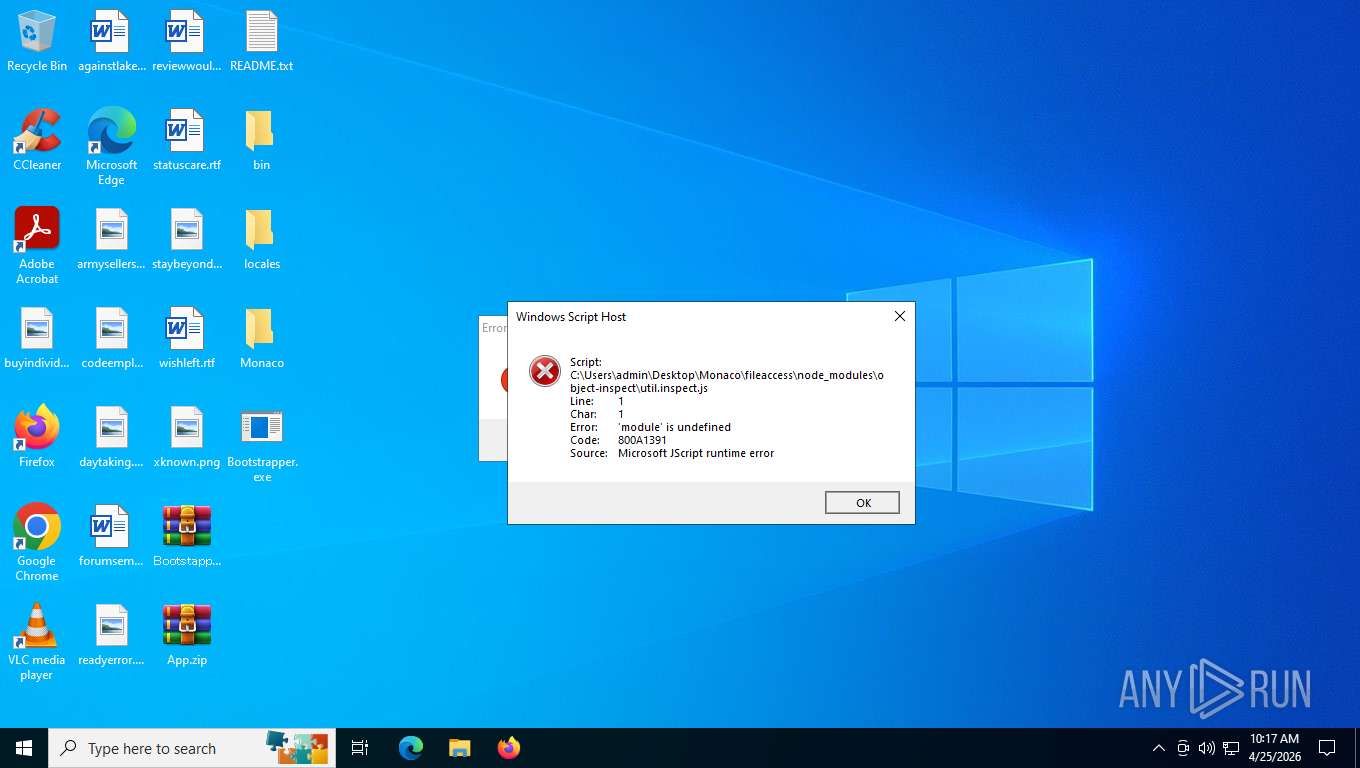
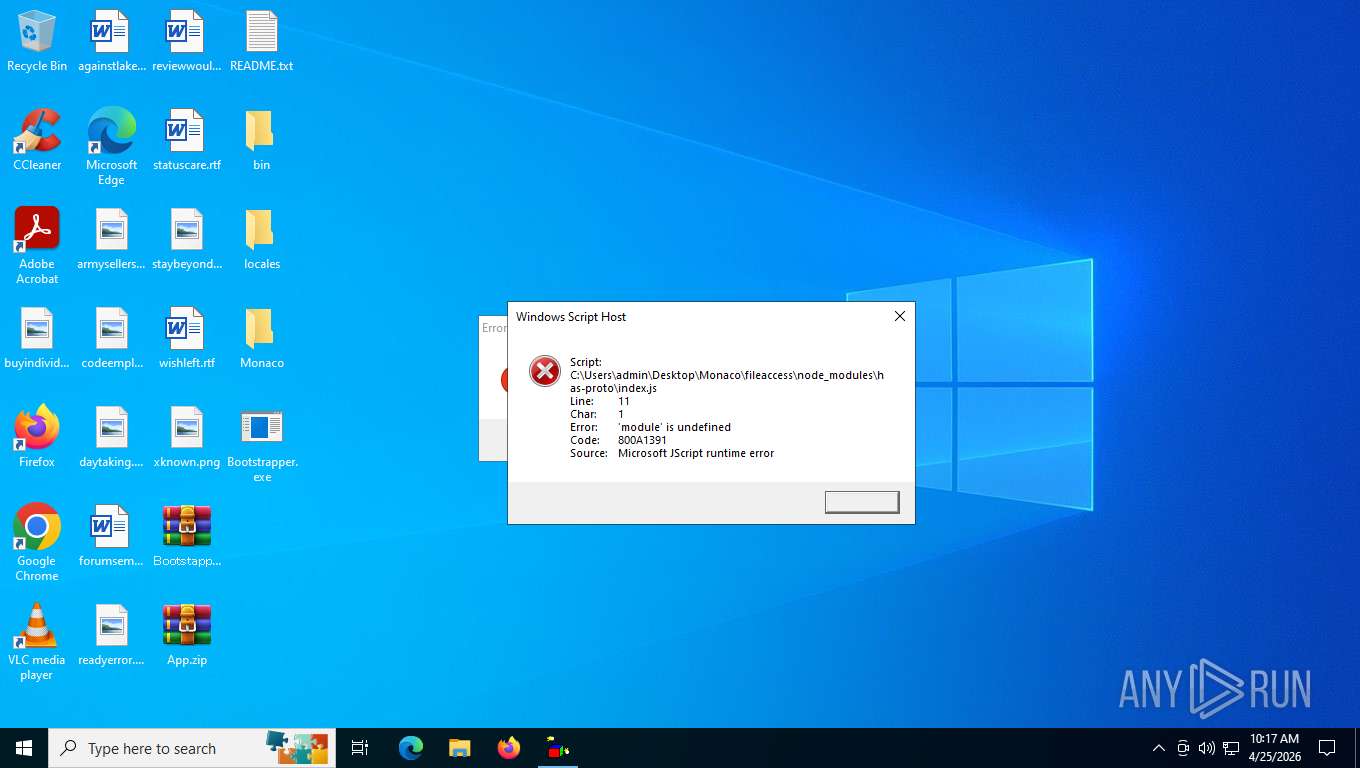
JScript runtime error (SCRIPT)
- wscript.exe (PID: 8388)
- wscript.exe (PID: 5524)
- wscript.exe (PID: 4348)
- wscript.exe (PID: 9148)
- wscript.exe (PID: 8988)
- wscript.exe (PID: 6504)
- wscript.exe (PID: 3104)
- wscript.exe (PID: 9180)
- wscript.exe (PID: 7880)
- wscript.exe (PID: 6108)
- wscript.exe (PID: 7116)
- wscript.exe (PID: 5304)
- wscript.exe (PID: 8296)
- wscript.exe (PID: 9012)
- wscript.exe (PID: 8400)
- wscript.exe (PID: 9140)
- wscript.exe (PID: 7992)
- wscript.exe (PID: 7964)
- wscript.exe (PID: 1864)
- wscript.exe (PID: 8028)
- wscript.exe (PID: 4712)
- wscript.exe (PID: 6672)
- wscript.exe (PID: 5672)
- wscript.exe (PID: 6532)
- wscript.exe (PID: 8208)
- wscript.exe (PID: 3996)
- wscript.exe (PID: 3200)
- wscript.exe (PID: 4328)
Reads security settings of Internet Explorer
- notepad.exe (PID: 9132)
- notepad.exe (PID: 5200)
Reads Environment values
- identity_helper.exe (PID: 4308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
265
Monitored processes
124
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1404 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5736,i,4359393491328654762,4654060876770259338,262144 --variations-seed-version --mojo-platform-channel-handle=5372 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=9 --field-trial-handle=1928,i,16910109769634357767,16772250768624927892,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1992,i,16910109769634357767,16772250768624927892,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=1984 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1864 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Desktop\Monaco/fileaccess/node_modules/has-property-descriptors/index.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=8 --field-trial-handle=3620,i,803940942032278659,4246208114746915083,262144 --variations-seed-version=20260425-030030.652000-production --mojo-platform-channel-handle=3696 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2216 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2200,i,4359393491328654762,4654060876770259338,262144 --variations-seed-version --mojo-platform-channel-handle=2188 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2232 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ffe2392f208,0x7ffe2392f214,0x7ffe2392f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffe234afff8,0x7ffe234b0004,0x7ffe234b0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x220,0x224,0x228,0x1fc,0x22c,0x7ffe23d5fff8,0x7ffe23d60004,0x7ffe23d60010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
7 767
Read events
7 745
Write events
22
Delete events
0
Modification events
| (PID) Process: | (8620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (8620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8620) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8804) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8804) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8804) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8804) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6504) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\wscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: B7840F0000000000 | |||
Executable files
45
Suspicious files
865
Text files
685
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RFdfe94.TMP | — | |
MD5:— | SHA256:— | |||
| 5196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RFdfea4.TMP | — | |
MD5:— | SHA256:— | |||
| 5196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RFdfe94.TMP | — | |
MD5:— | SHA256:— | |||
| 5196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RFdfea4.TMP | — | |
MD5:— | SHA256:— | |||
| 5196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFdfea4.TMP | — | |
MD5:— | SHA256:— | |||
| 5196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5196 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
816
TCP/UDP connections
176
DNS requests
183
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6672 | chrome.exe | GET | 204 | 142.251.110.119:443 | https://i.ytimg.com/generate_204 | US | — | — | whitelisted |
— | — | GET | 200 | 204.79.197.203:80 | http://oneocsp.microsoft.com/ocsp/MFQwUjBQME4wTDAJBgUrDgMCGgUABBQ3L3%2F%2Fa6ADK8NraY2GXzVaYrHG4AQUb6t%2B2v%2BXQ3LsO2d33oJhNYhHQoUCEzMAAAAGb6JMMcOVb6sAAAAAAAY%3D | US | binary | 960 b | whitelisted |
6672 | chrome.exe | GET | 200 | 142.250.154.95:443 | https://fonts.googleapis.com/css2?family=Roboto:wght@300;400;500;700&family=YouTube+Sans:wght@300..900&display=swap | US | text | 84.1 Kb | whitelisted |
4872 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6672 | chrome.exe | GET | 302 | 142.251.127.84:443 | https://accounts.google.com/ServiceLogin?service=youtube&uilel=3&passive=true&continue=https%3A%2F%2Fwww.youtube.com%2Fsignin%3Faction_handle_signin%3Dtrue%26app%3Ddesktop%26hl%3Den%26next%3D%252Fsignin_passive%26feature%3Dpassive&hl=en | US | — | — | whitelisted |
— | — | GET | 200 | 23.11.41.157:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAjTxtAB8my1oj8MfWpz%2F7Y%3D | NL | binary | 312 b | whitelisted |
6672 | chrome.exe | GET | 200 | 142.251.13.139:80 | http://clients2.google.com/time/1/current?cup2key=8:Je4acvBioWR33N5QwrwYyNAW_TcTcYJY0RvukC4gXh4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 108 b | whitelisted |
6672 | chrome.exe | GET | 200 | 142.251.20.95:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | US | binary | 41 b | whitelisted |
6672 | chrome.exe | GET | 200 | 142.251.13.101:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=133 | US | compressed | 88.7 Kb | whitelisted |
6672 | chrome.exe | GET | 200 | 142.251.20.91:443 | https://www.youtube.com/results?search_query=roblox+executor&sp=EgYIAxABGAQ%253D | US | html | 1.01 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4872 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5532 | SearchApp.exe | 95.101.23.83:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.11.41.157:80 | ocsp.digicert.com | AKAMAI-AMS | NL | whitelisted |
— | — | 204.79.197.203:80 | oneocsp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6672 | chrome.exe | 142.251.13.101:443 | clients2.google.com | GOOGLE | US | whitelisted |
6672 | chrome.exe | 142.251.20.91:443 | www.youtube.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
oneocsp.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.youtube.com |
| whitelisted |
accounts.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4872 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
8852 | Bootstrapper.exe | A Network Trojan was detected | MALWARE [ANY.RUN] Go/Generic Agent related HTTP POST request (access_token=&debug=) |