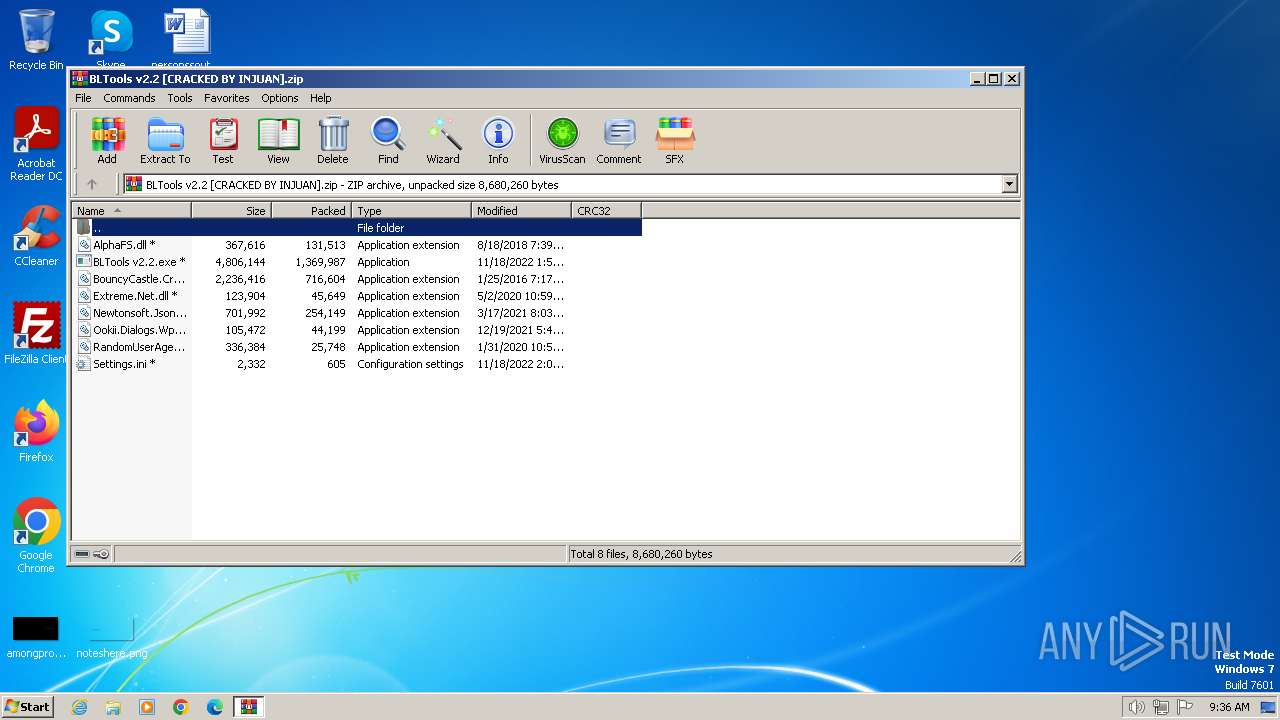
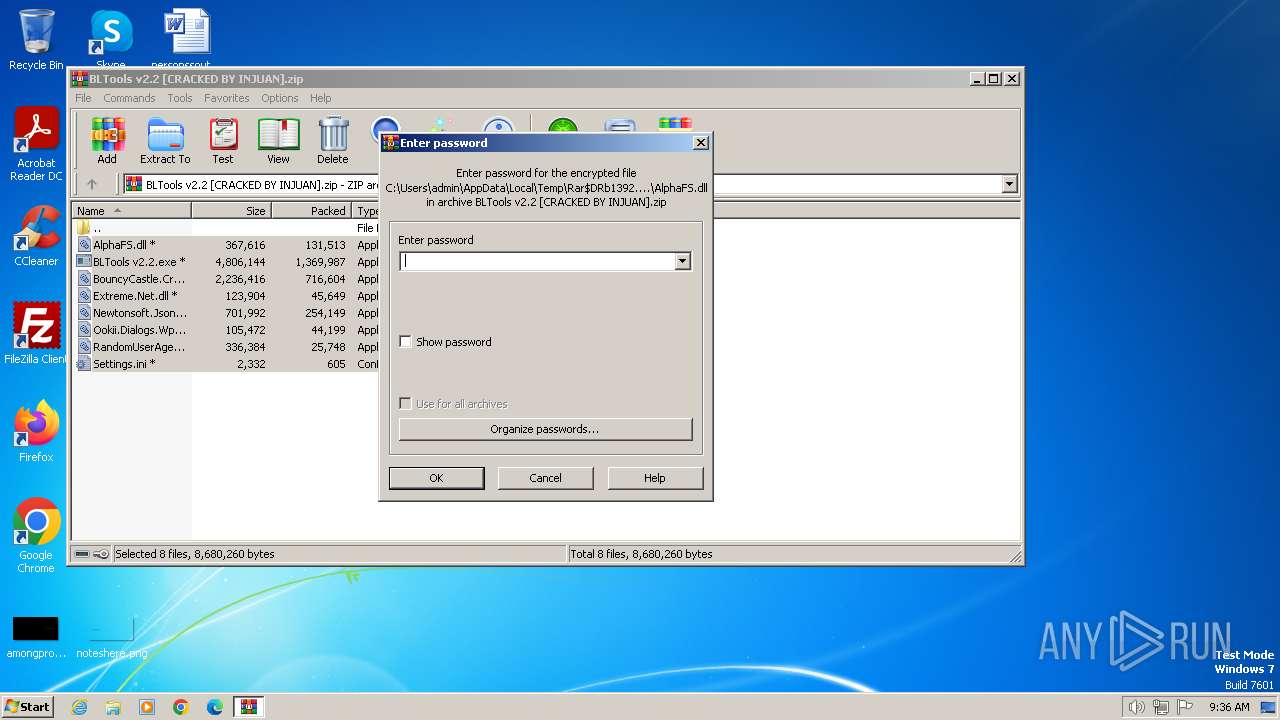
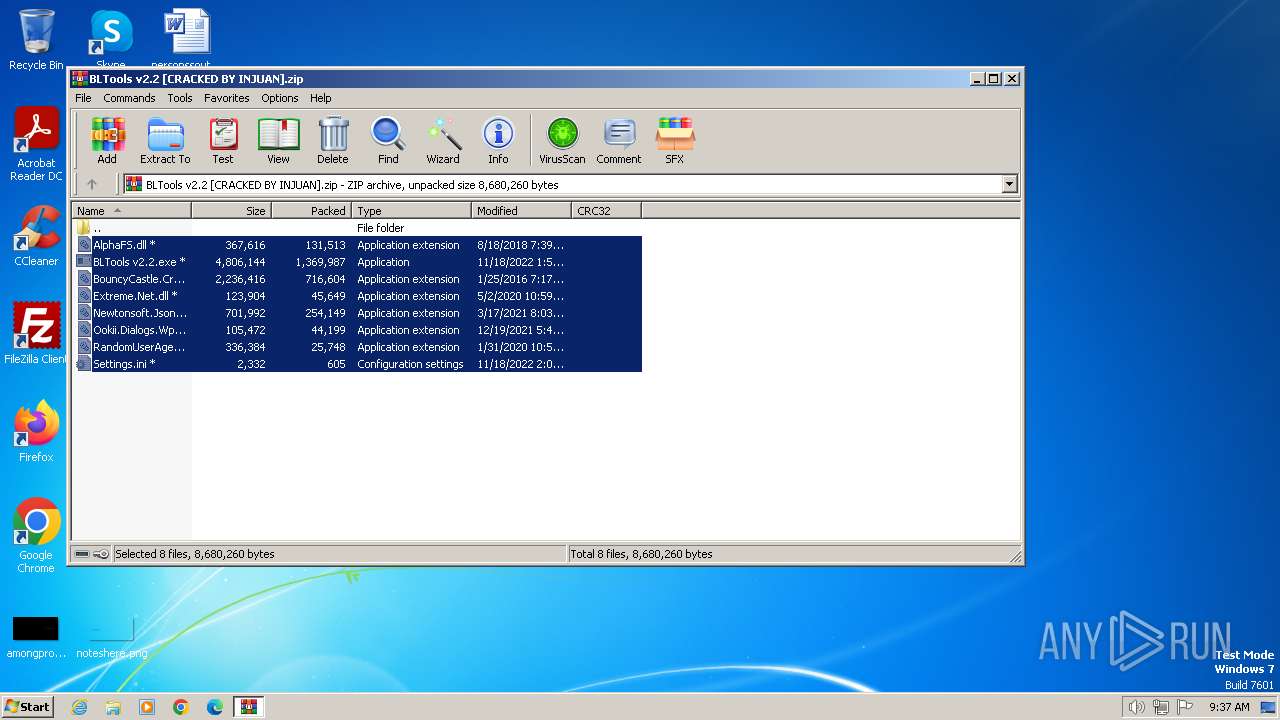
| File name: | BLTools v2.2 [CRACKED BY INJUAN].zip |
| Full analysis: | https://app.any.run/tasks/49d9831c-c6f9-42a5-86b2-f35ce67cd2ab |
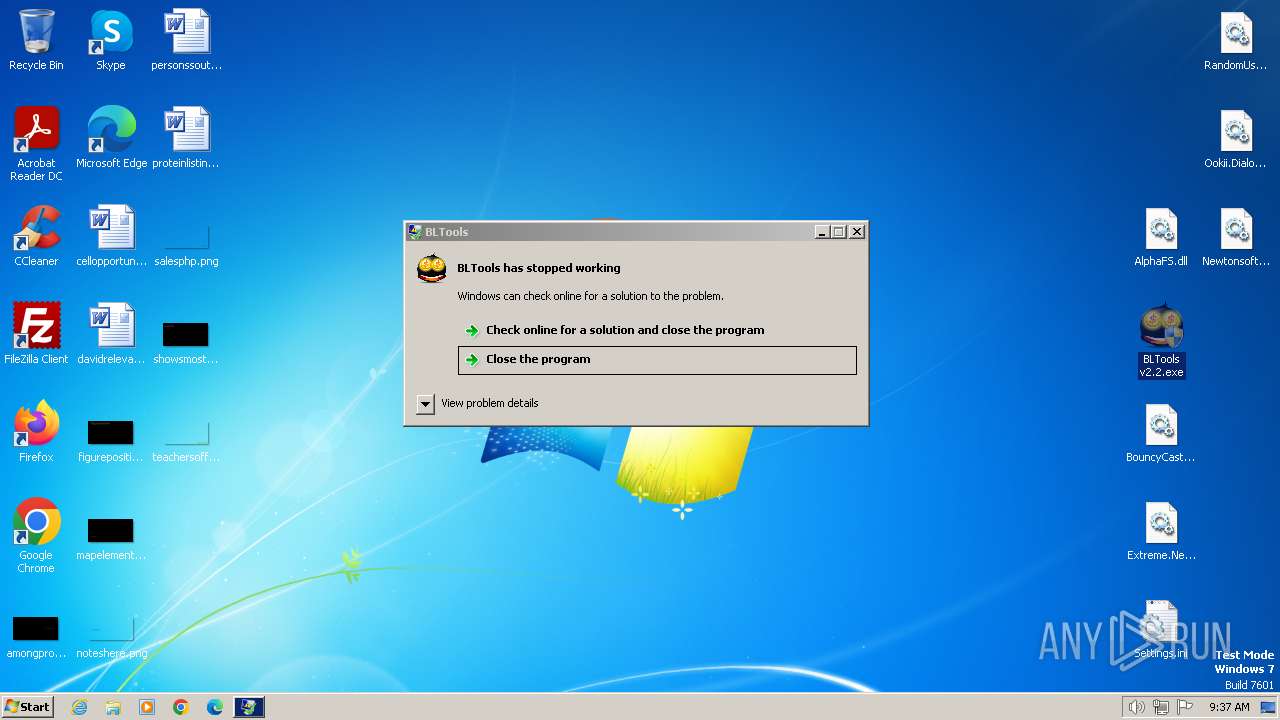
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2024, 09:36:21 |
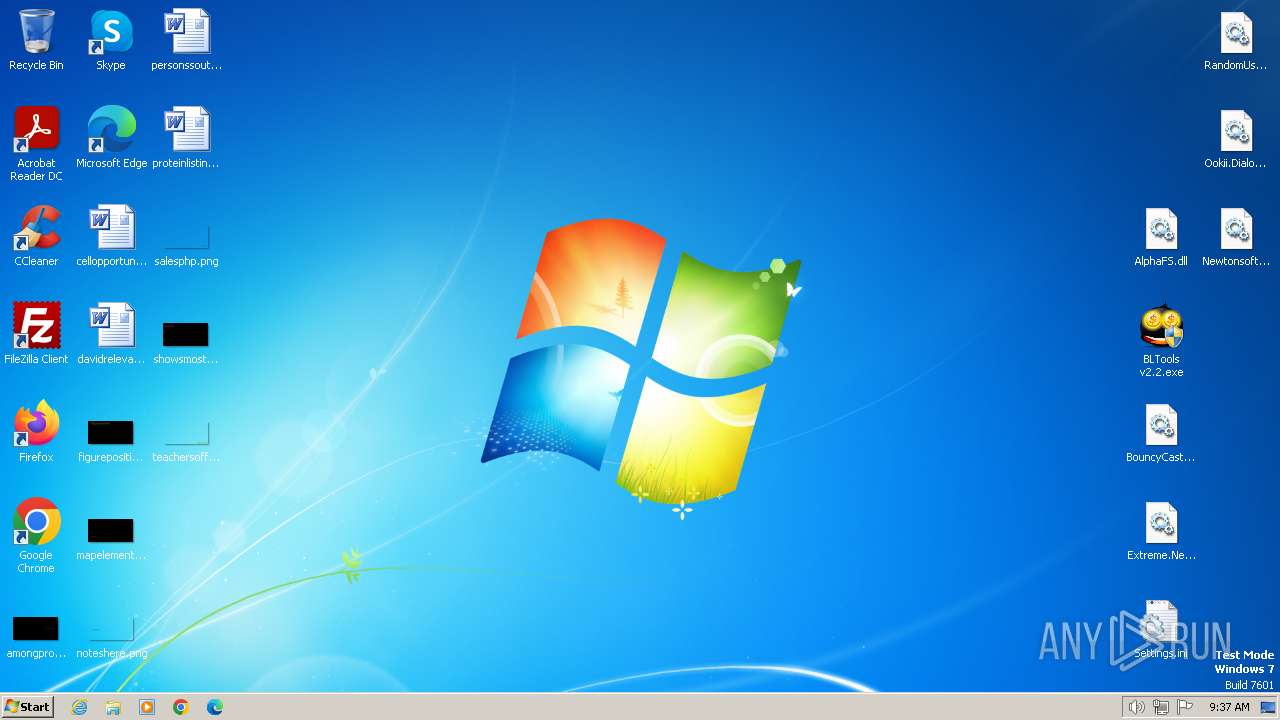
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 313CF576A3576E724100F2BD23625ACB |
| SHA1: | 964D05747E6541B74389B39BBE0A284C05B6C0FF |
| SHA256: | 1523E6ED822B5C276FC77E930E5E697D3CC2B1BB04A3010E44EE8AFCABDD0822 |
| SSDEEP: | 49152:ayilPJ22l1pbHUPnLG2FscjSPWIVe9t3Zo7Bq3iRICvMKcpzghi:ayQl1pbaLnxjSP1eFolq3s0Kcpkhi |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads settings of System Certificates
- BLTools v2.2.exe (PID: 3040)
- BLTools v2.6.3_[Crack].exe (PID: 2064)
Reads the Internet Settings
- BLTools v2.2.exe (PID: 3040)
- BLTools v2.6.3_[Crack].exe (PID: 2064)
Adds/modifies Windows certificates
- BLTools v2.6.3_[Crack].exe (PID: 2064)
INFO
Reads the computer name
- BLTools v2.2.exe (PID: 3040)
- BLTools v2.6.3_[Crack].exe (PID: 2064)
Reads Environment values
- BLTools v2.2.exe (PID: 3040)
- BLTools v2.6.3_[Crack].exe (PID: 2064)
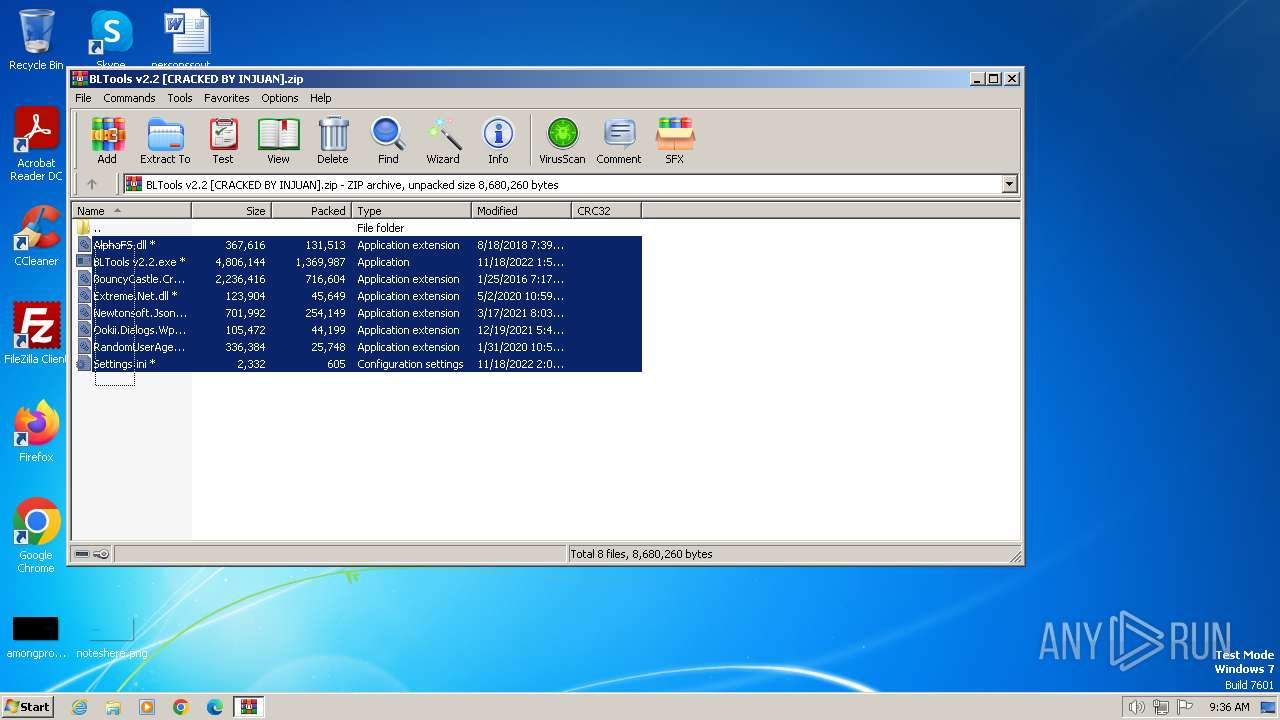
Manual execution by a user
- BLTools v2.2.exe (PID: 3040)
- BLTools v2.2.exe (PID: 324)
- BLTools v2.6.3_[Crack].exe (PID: 2064)
- BLTools v2.6.3_[Crack].exe (PID: 3276)
- WinRAR.exe (PID: 2636)
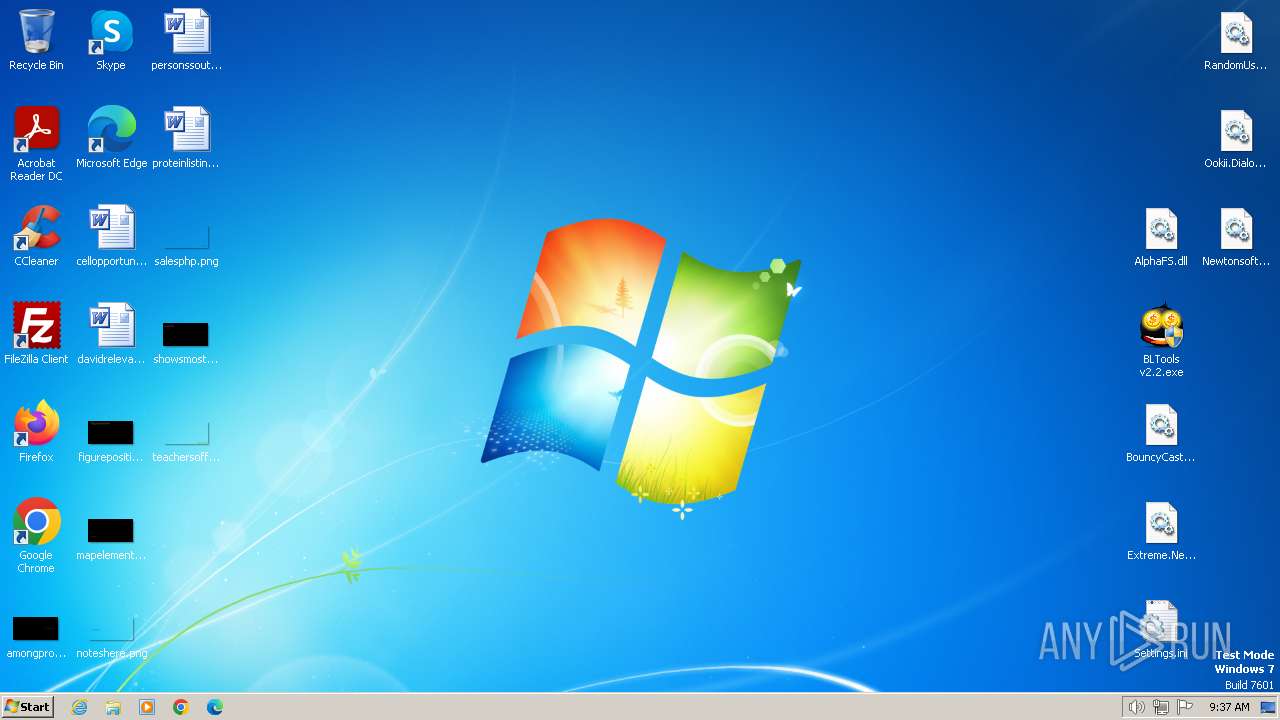
Drops the executable file immediately after the start
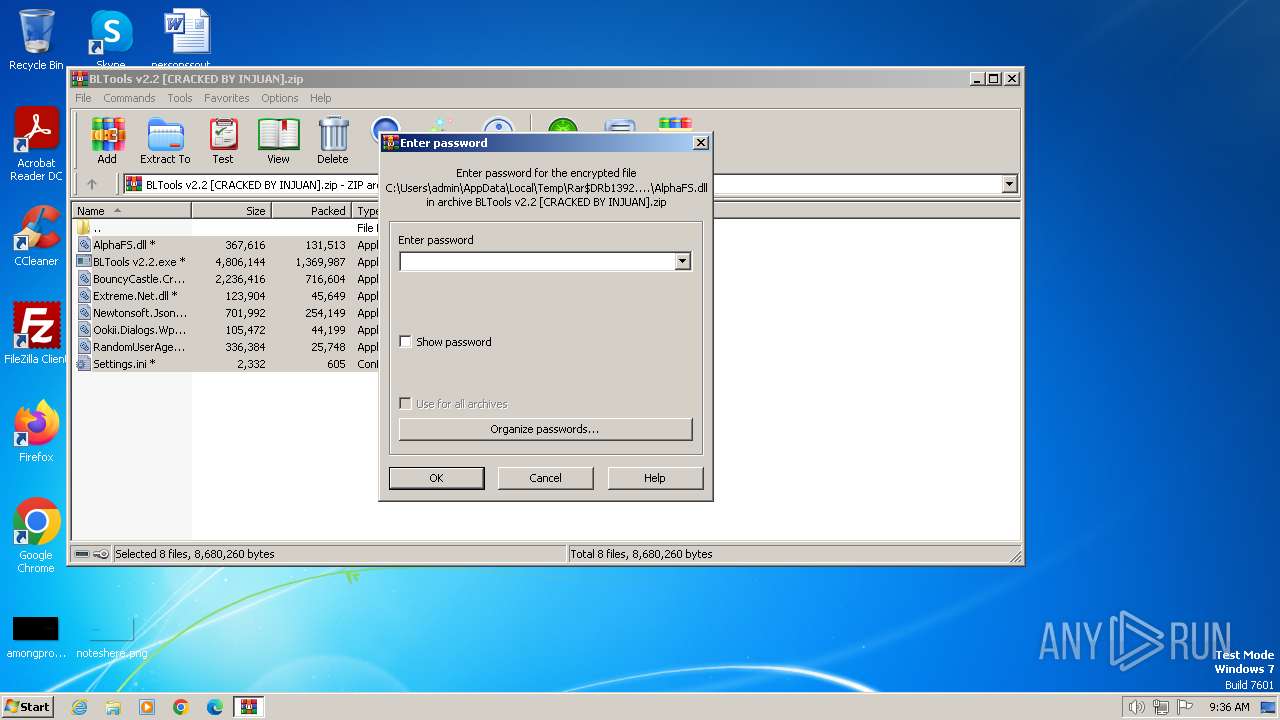
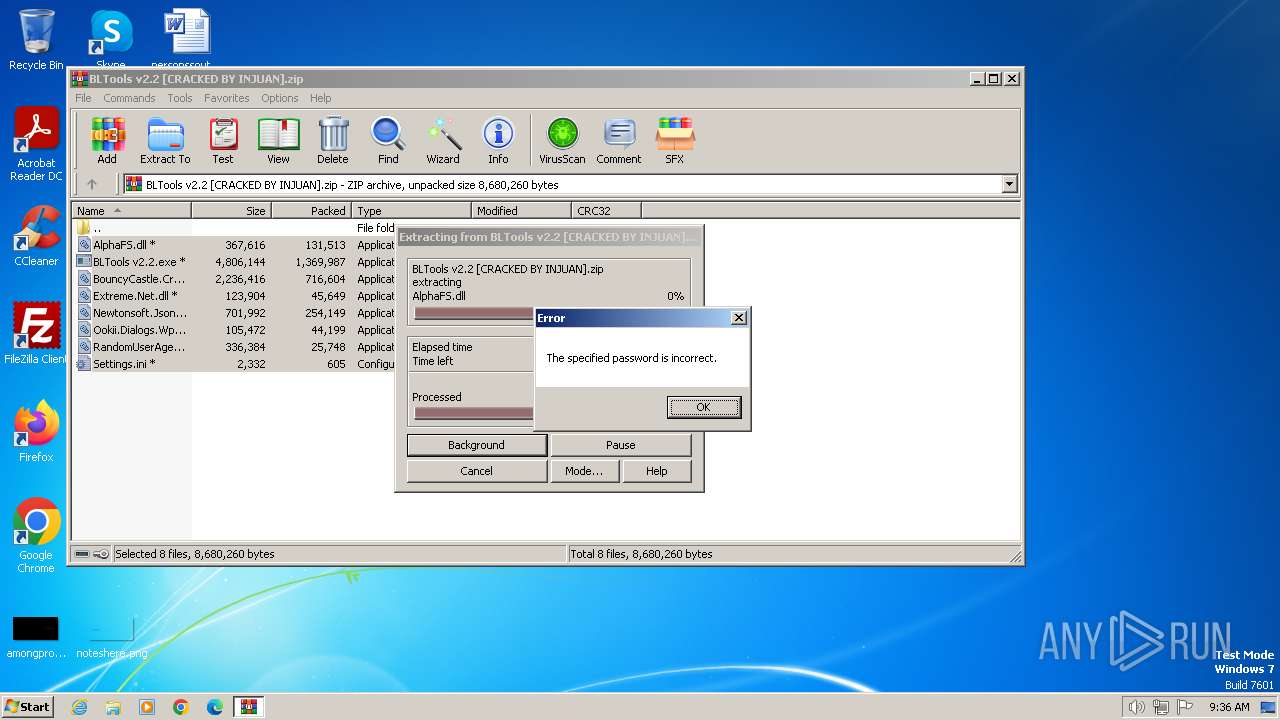
- WinRAR.exe (PID: 1392)
- WinRAR.exe (PID: 2636)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1392)
- WinRAR.exe (PID: 2636)
Checks supported languages
- BLTools v2.6.3_[Crack].exe (PID: 2064)
- BLTools v2.2.exe (PID: 3040)
Reads the machine GUID from the registry
- BLTools v2.2.exe (PID: 3040)
- BLTools v2.6.3_[Crack].exe (PID: 2064)
Create files in a temporary directory
- BLTools v2.6.3_[Crack].exe (PID: 2064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2018:08:18 21:39:52 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 131513 |
| ZipUncompressedSize: | 367616 |
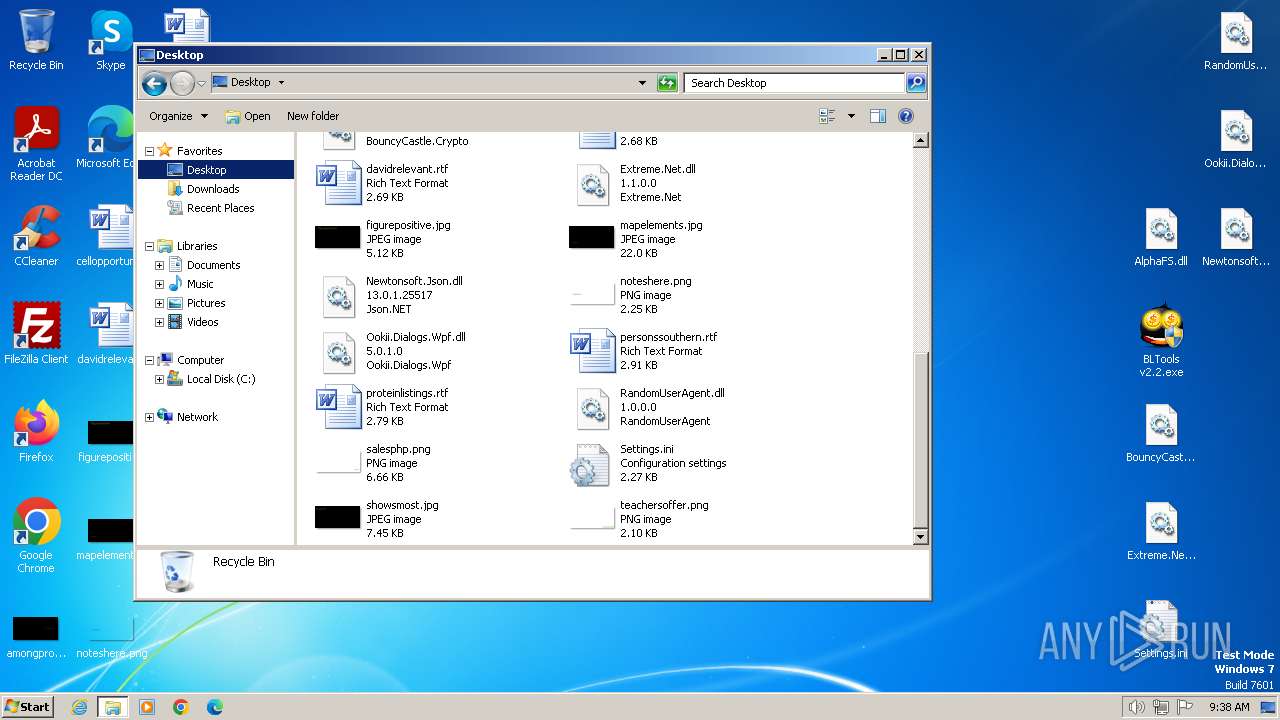
| ZipFileName: | AlphaFS.dll |
Total processes
57
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Users\admin\Desktop\BLTools v2.2.exe" | C:\Users\admin\Desktop\BLTools v2.2.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: BLTools Exit code: 3221226540 Version: 2.2.0.0 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\BLTools v2.2 [CRACKED BY INJUAN].zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
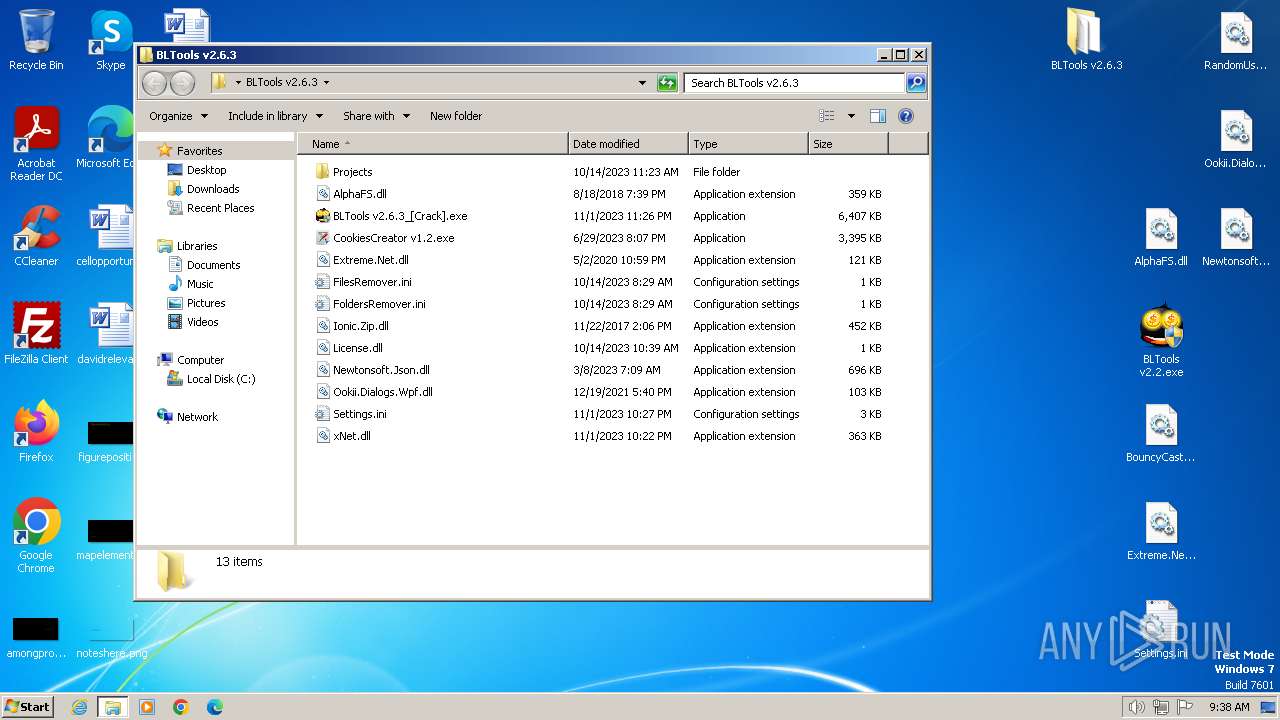
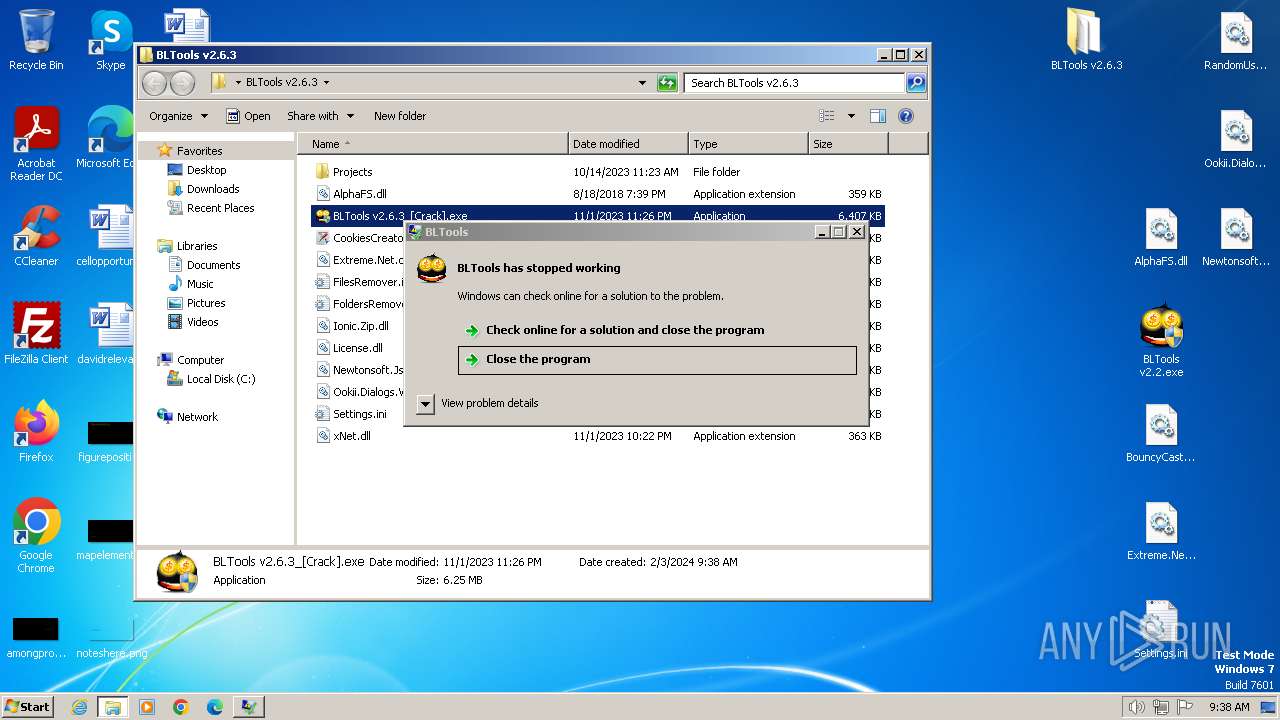
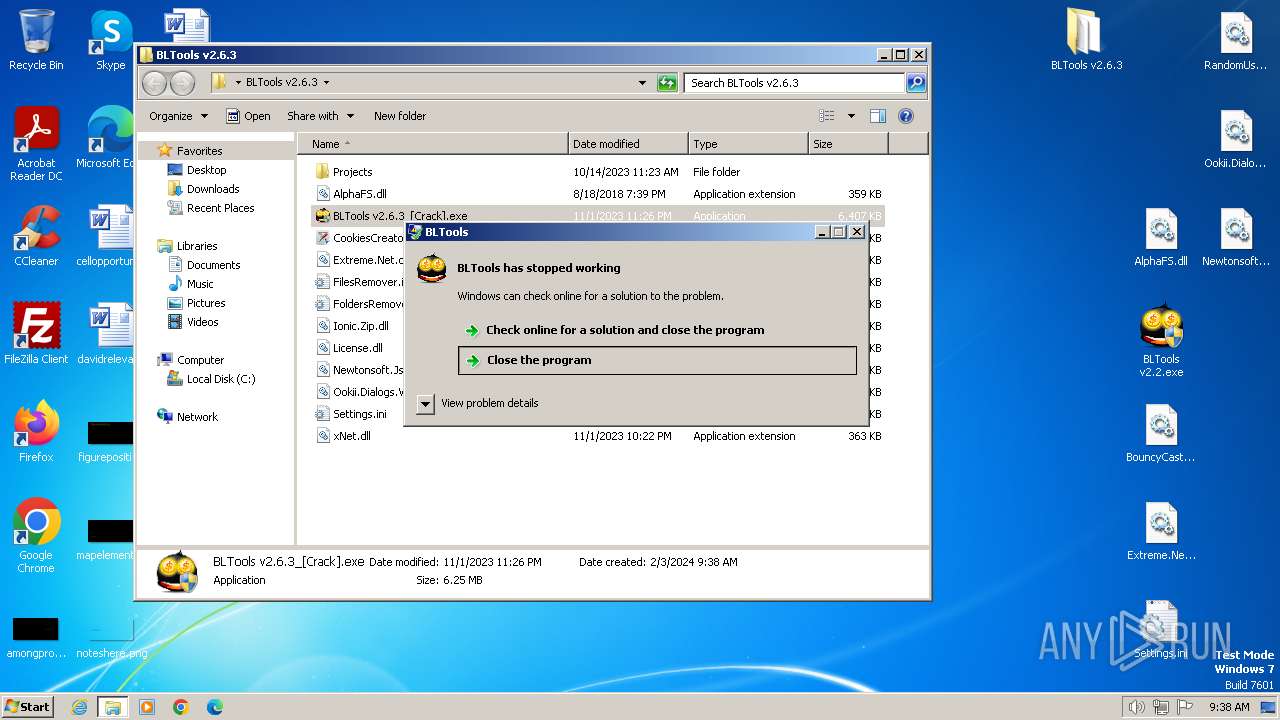
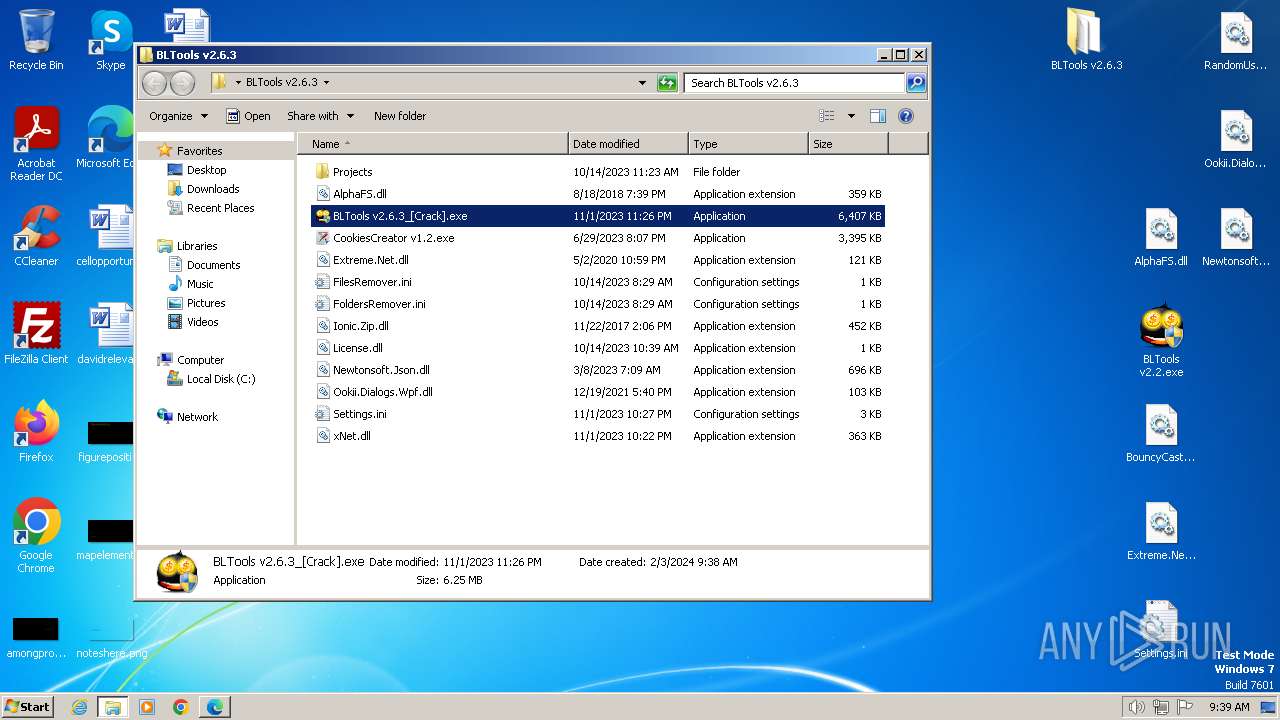
| 2064 | "C:\Users\admin\Desktop\BLTools v2.6.3\BLTools v2.6.3_[Crack].exe" | C:\Users\admin\Desktop\BLTools v2.6.3\BLTools v2.6.3_[Crack].exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: BLTools Exit code: 3762504530 Version: 2.6.3.0 Modules
| |||||||||||||||
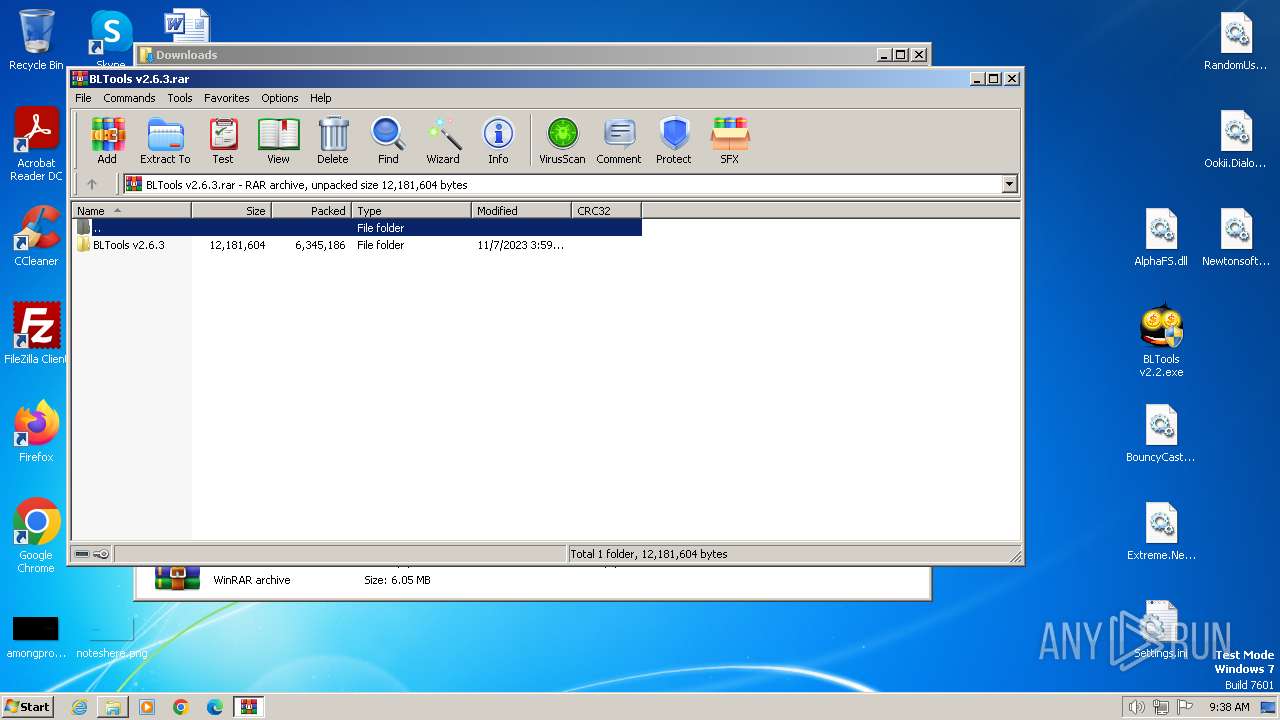
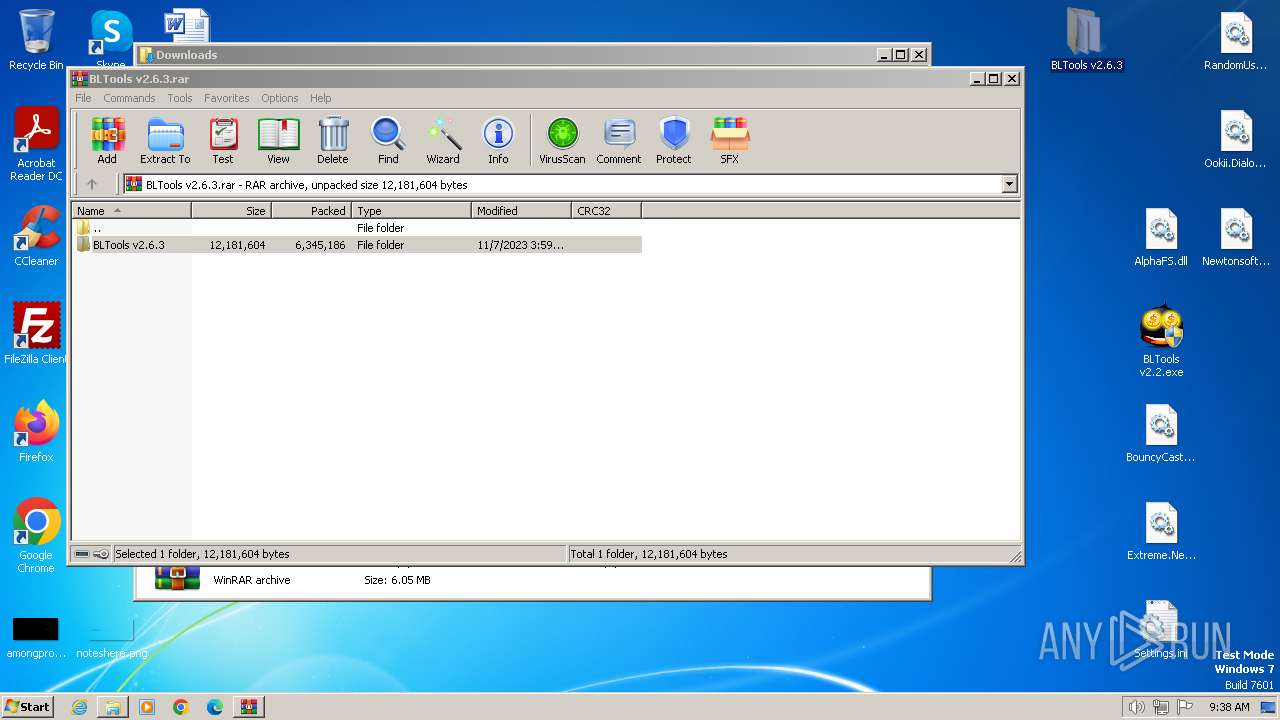
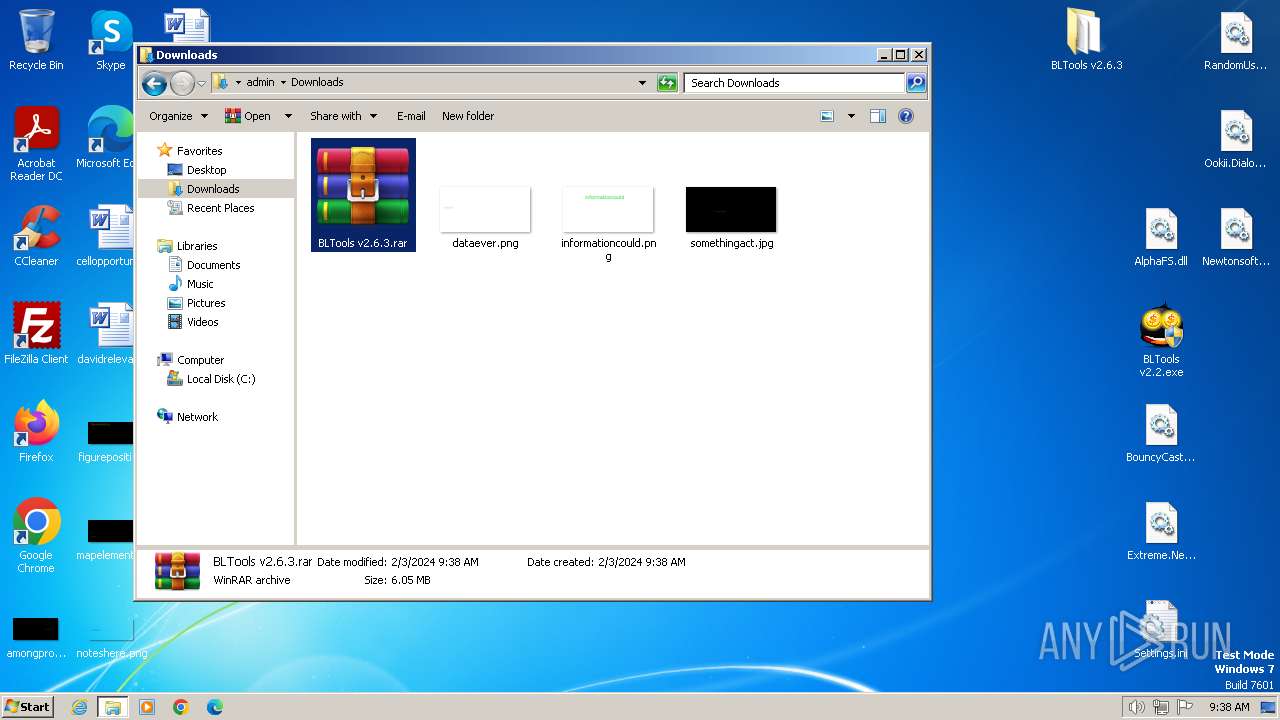
| 2636 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\BLTools v2.6.3.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3040 | "C:\Users\admin\Desktop\BLTools v2.2.exe" | C:\Users\admin\Desktop\BLTools v2.2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: BLTools Exit code: 3762504530 Version: 2.2.0.0 Modules
| |||||||||||||||
| 3276 | "C:\Users\admin\Desktop\BLTools v2.6.3\BLTools v2.6.3_[Crack].exe" | C:\Users\admin\Desktop\BLTools v2.6.3\BLTools v2.6.3_[Crack].exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: BLTools Exit code: 3221226540 Version: 2.6.3.0 Modules
| |||||||||||||||
Total events
9 650
Read events
9 575
Write events
75
Delete events
0
Modification events
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
14
Suspicious files
5
Text files
6
Unknown types
0
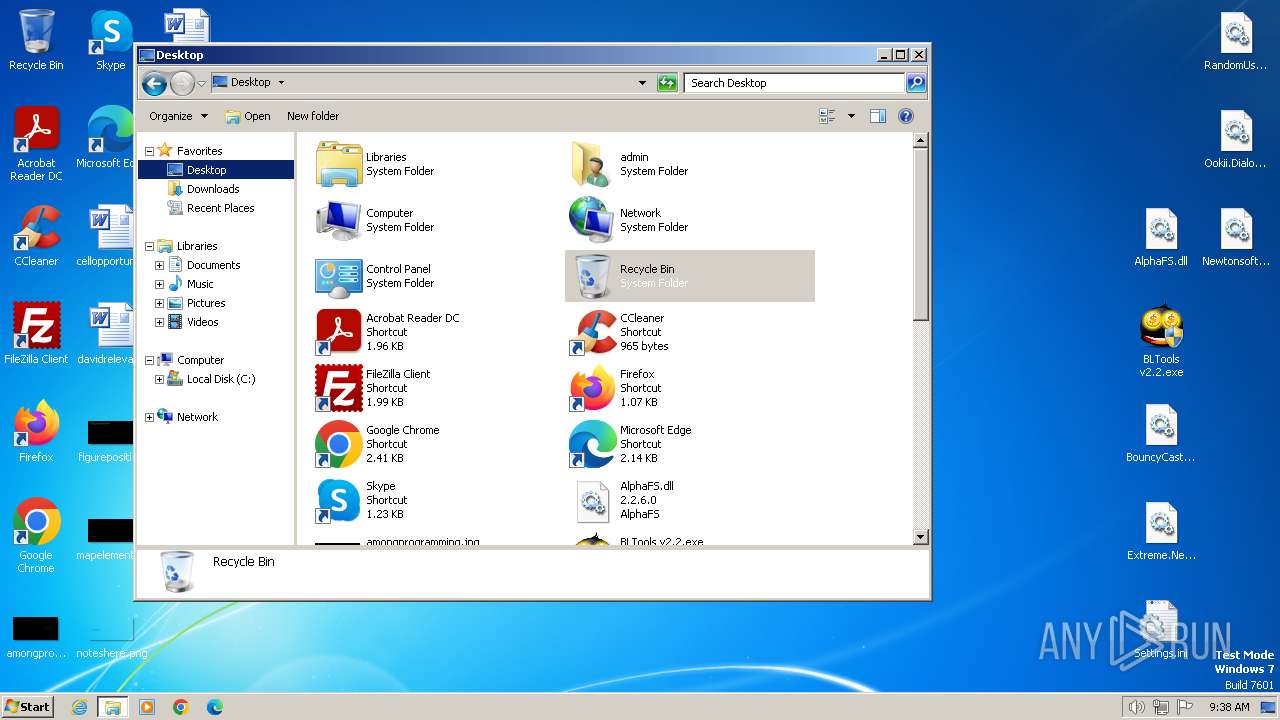
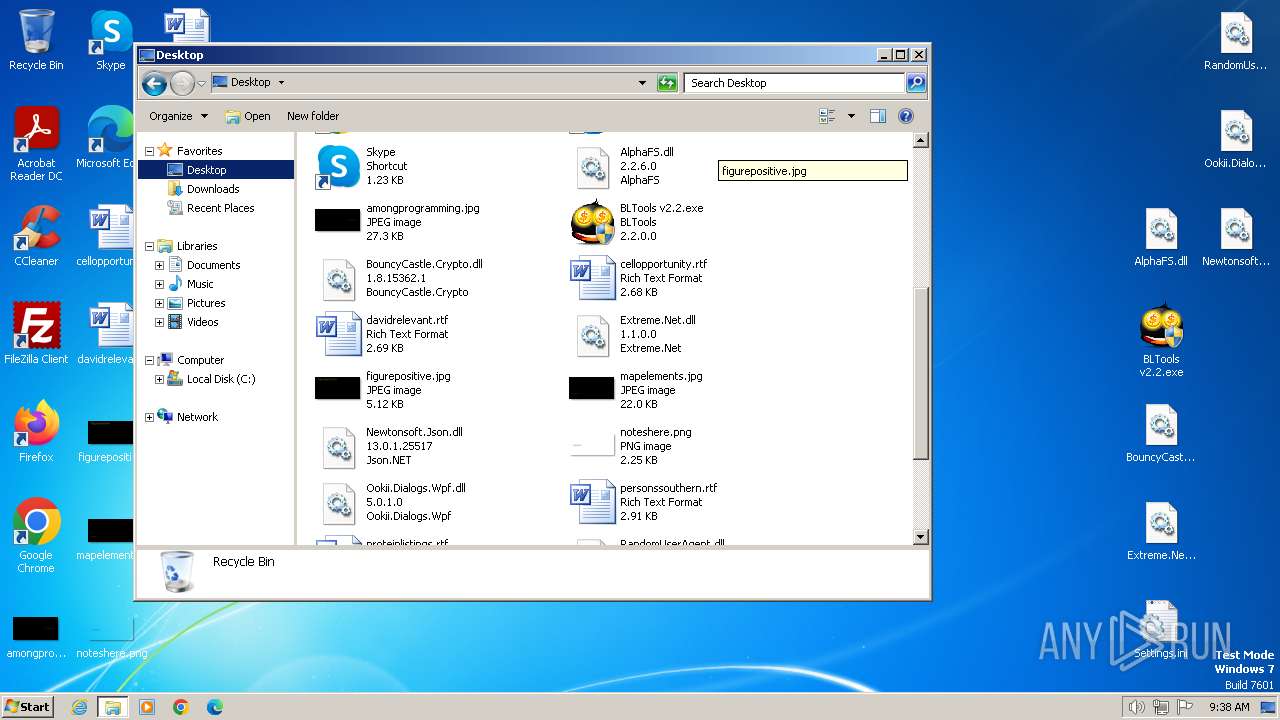
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1392.47849\BLTools v2.2.exe | executable | |
MD5:C7F2E182794882C0450F6674439D983C | SHA256:A42D9F80EF502F004EBD0B850164D9706DA51359F1BD27DDE891C66F4BA8E55B | |||
| 1392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1392.47849\BouncyCastle.Crypto.dll | executable | |
MD5:3CF6BF0E0A27F3665EDD6362D137E4CC | SHA256:1985B85BB44BE6C6EAF35E02EF11E23A890E809B8EC2E53210A4AD5A85B26C70 | |||
| 1392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1392.47849\Settings.ini | text | |
MD5:AC450A5117532D56F9C117F2F2825B26 | SHA256:AD09D32E5BB4968039A5BC0C365AFF05760DE27B6E20642514A419B4025C8AA8 | |||
| 1392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1392.47849\Extreme.Net.dll | executable | |
MD5:F79F0E3A0361CAC000E2D3553753CD68 | SHA256:8A6518AB7419FBEC3AC9875BAA3AFB410AD1398C7AA622A09CD9084EC6CADFCD | |||
| 1392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1392.47849\Newtonsoft.Json.dll | executable | |
MD5:081D9558BBB7ADCE142DA153B2D5577A | SHA256:B624949DF8B0E3A6153FDFB730A7C6F4990B6592EE0D922E1788433D276610F3 | |||
| 1392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1392.47849\RandomUserAgent.dll | executable | |
MD5:839CD4CE1930EEE45F55F6259468D649 | SHA256:53331BFF5E585C471FAD6789313A2A8A687A586CC0A8D006B24085B91ED7FC9A | |||
| 2636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2636.9725\BLTools v2.6.3\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
| 1392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1392.47849\Ookii.Dialogs.Wpf.dll | executable | |
MD5:932EBB3F9E7113071C6A17818342B7CC | SHA256:285AA8225732DDBCF211B1158BD6CFF8BF3ACBEEAB69617F4BE85862B7105AB5 | |||
| 2636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2636.9725\BLTools v2.6.3\FilesRemover.ini | text | |
MD5:6760B68C981281F170A5FEA12295D745 | SHA256:B600F591D3616A6262F9D683B0DA45970AF7EDA2201462E7C7517AEF291336D0 | |||
| 2636 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2636.9725\BLTools v2.6.3\BLTools v2.6.3_[Crack].exe | executable | |
MD5:27D6C103163348DAB89FF03091DAADE6 | SHA256:24DF47D2E8B3732294DE5F175EE361F5B2C0859D724791A74CCA34B3EB80588B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
3
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2064 | BLTools v2.6.3_[Crack].exe | GET | 200 | 2.19.126.137:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?50d04d123d05b6ae | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3040 | BLTools v2.2.exe | 193.109.246.157:443 | bltools.moy.su | Compubyte Limited | RU | unknown |
2064 | BLTools v2.6.3_[Crack].exe | 104.26.1.5:443 | keyauth.win | CLOUDFLARENET | US | unknown |
2064 | BLTools v2.6.3_[Crack].exe | 2.19.126.137:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bltools.moy.su |
| unknown |
keyauth.win |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain in DNS Lookup (keyauth .win) |
2064 | BLTools v2.6.3_[Crack].exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain (keyauth .win) in TLS SNI |