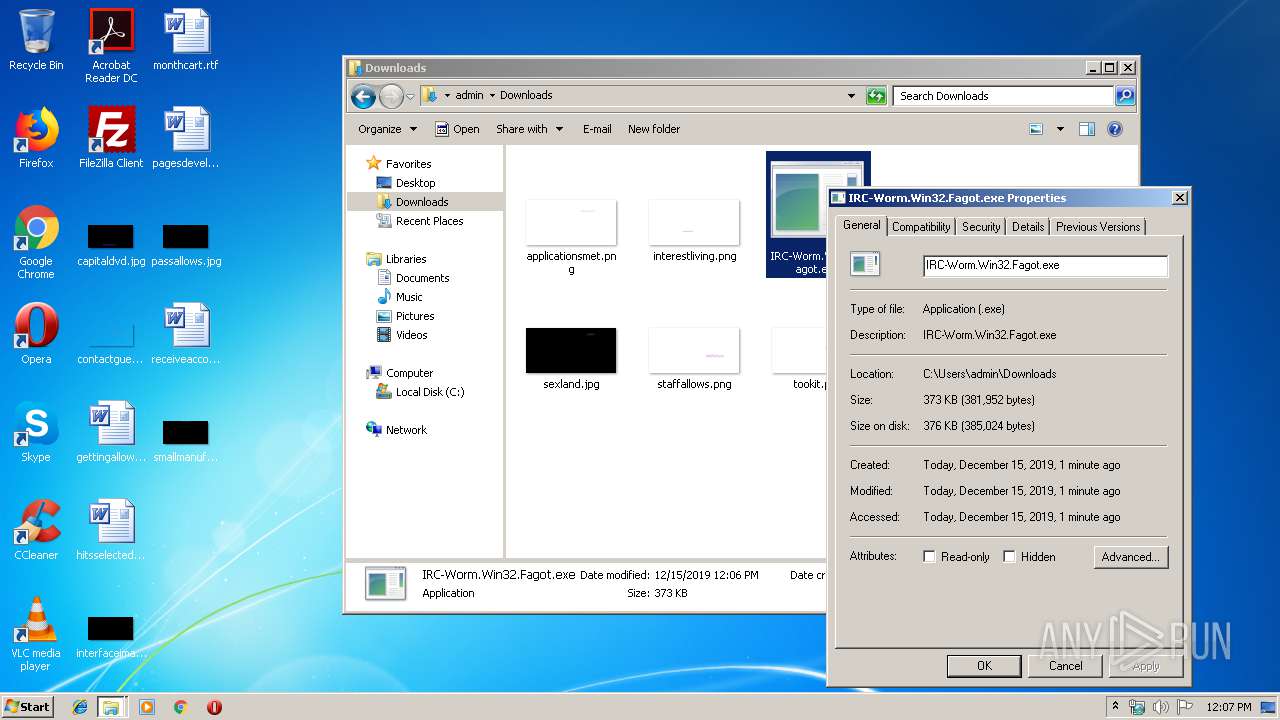
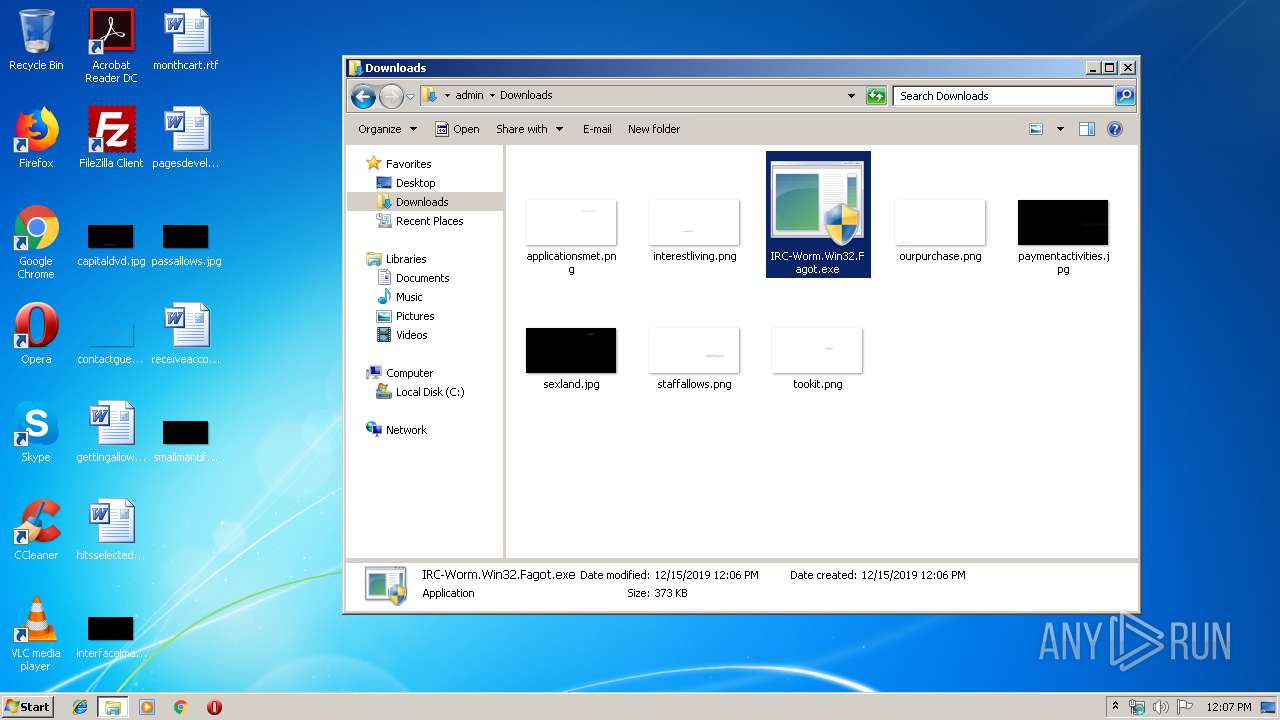
| File name: | C:\Users\admin\Desktop\IRC-Worm.Win32.Fagot.exe |
| Full analysis: | https://app.any.run/tasks/25c3ff10-69a0-4a9b-839f-7f0b4a41bb3f |
| Verdict: | Malicious activity |
| Analysis date: | December 15, 2019, 12:06:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 30CDAB5CF1D607EE7B34F44AB38E9190 |
| SHA1: | D4823F90D14EBA0801653E8C970F47D54F655D36 |
| SHA256: | 1517527C1D705A6EBC6EC9194AA95459E875AC3902A9F4AAB3BF24B6A6F8407F |
| SSDEEP: | 6144:Bjrk71gCl5D0nIMpAP40ShG4TmvgFNwUQs4zTBrgDYZJPSLJXaUtjk10he1:S79l5DixAPzwjegFNwVJzTLPSLJXT |
MALICIOUS
Deletes the SafeBoot registry key
- IRC-Worm.Win32.Fagot.exe (PID: 2516)
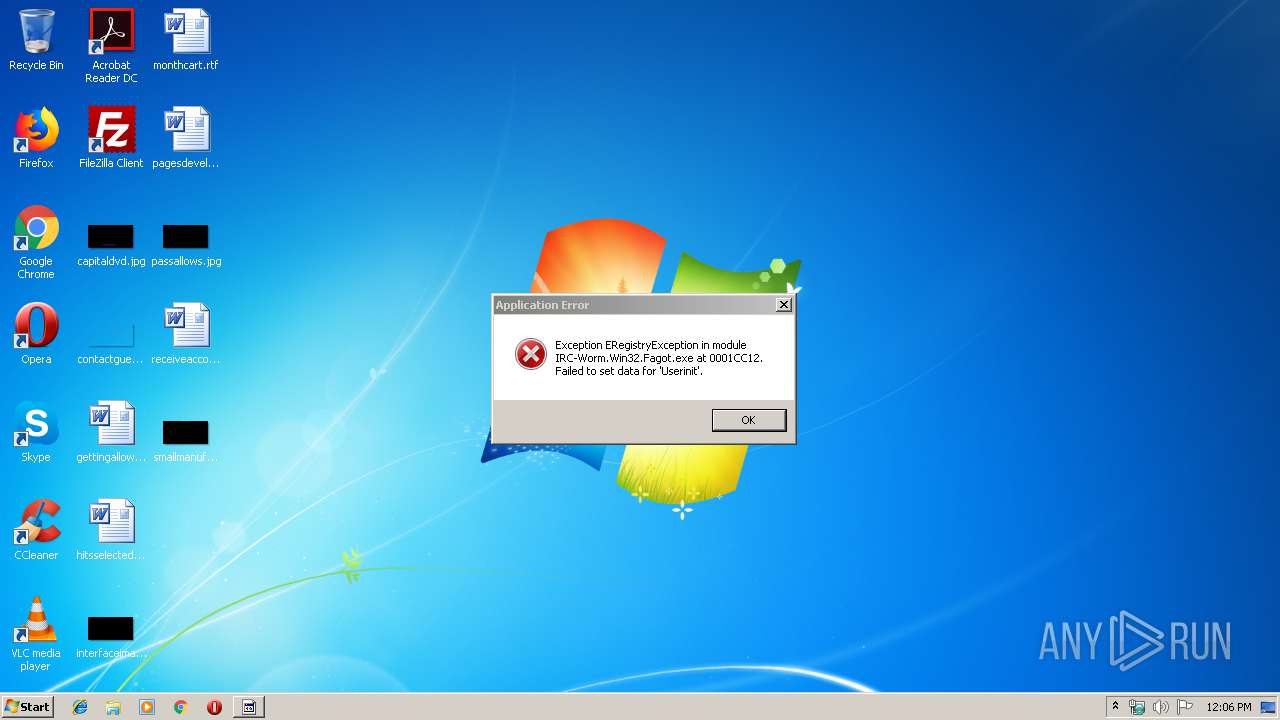
Changes the login/logoff helper path in the registry
- IRC-Worm.Win32.Fagot.exe (PID: 2516)
- IRC-Worm.Win32.Fagot.exe (PID: 1780)
Changes the autorun value in the registry
- IRC-Worm.Win32.Fagot.exe (PID: 2516)
SUSPICIOUS
Changes the started page of IE
- IRC-Worm.Win32.Fagot.exe (PID: 2516)
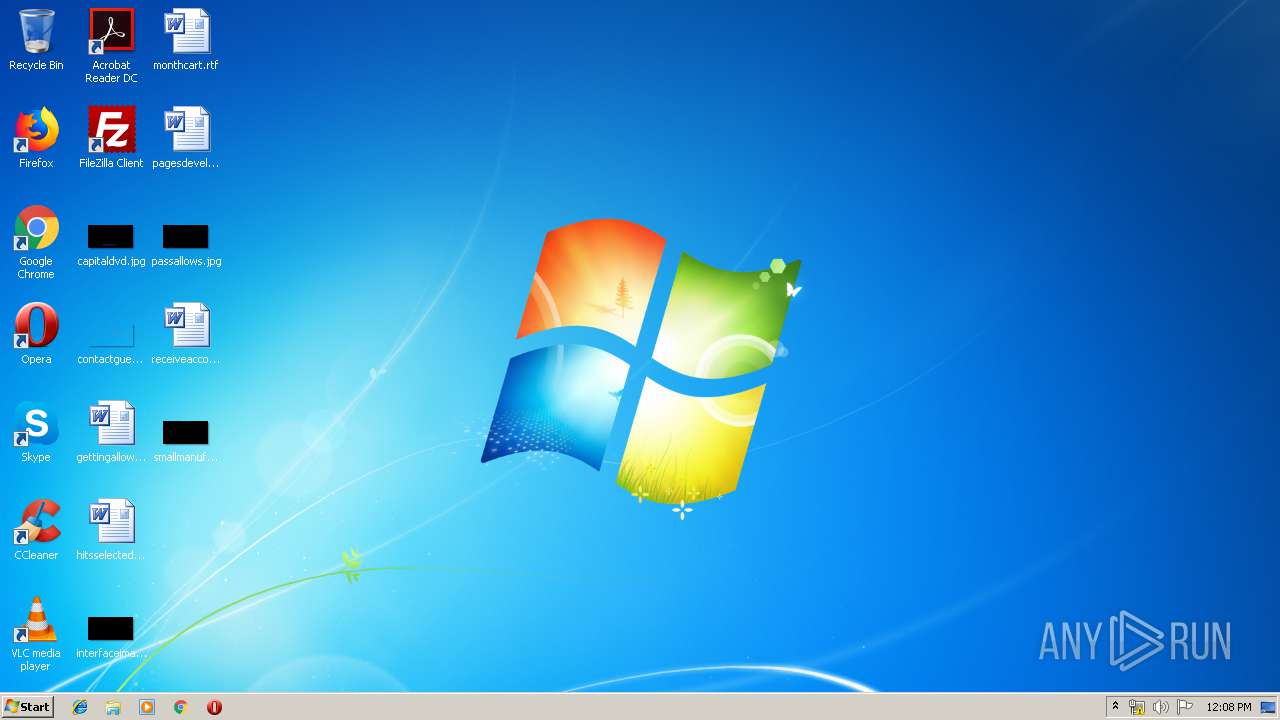
Creates files in the Windows directory
- IRC-Worm.Win32.Fagot.exe (PID: 2516)
Executable content was dropped or overwritten
- IRC-Worm.Win32.Fagot.exe (PID: 2516)
Reads the date of Windows installation
- IRC-Worm.Win32.Fagot.exe (PID: 2516)
Reads the Windows organization settings
- IRC-Worm.Win32.Fagot.exe (PID: 2516)
Reads Windows owner or organization settings
- IRC-Worm.Win32.Fagot.exe (PID: 2516)
Reads Windows Product ID
- IRC-Worm.Win32.Fagot.exe (PID: 2516)
Reads Environment values
- IRC-Worm.Win32.Fagot.exe (PID: 2516)
INFO
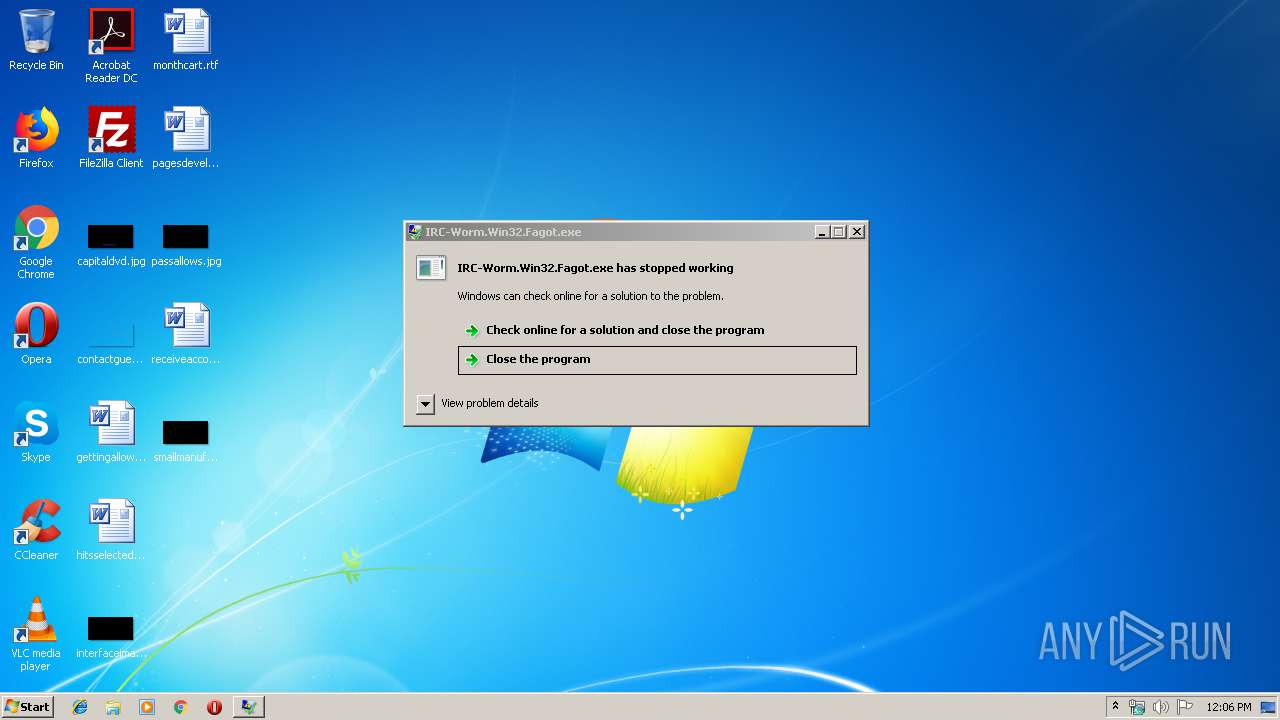
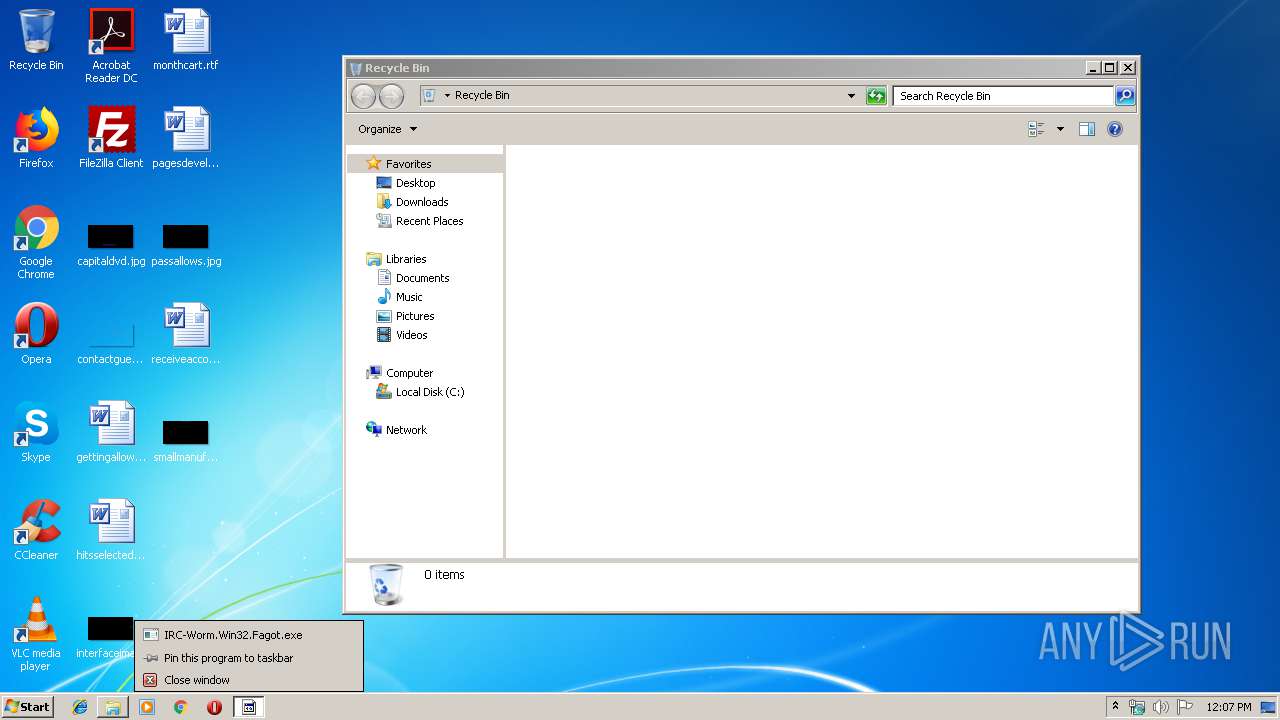
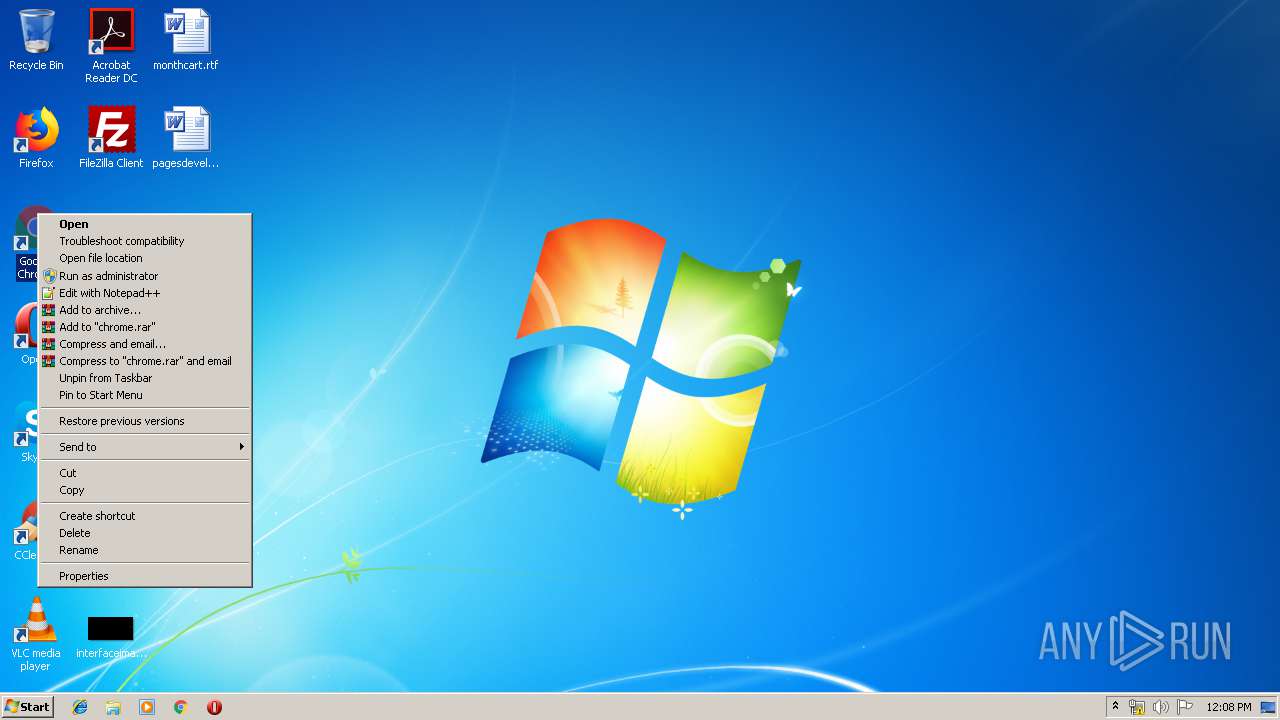
Manual execution by user
- wermgr.exe (PID: 2912)
- IRC-Worm.Win32.Fagot.exe (PID: 2516)
- IRC-Worm.Win32.Fagot.exe (PID: 1784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (93.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (1.9) |
| .scr | | | Windows screen saver (1.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.9) |
| .exe | | | Win32 Executable (generic) (0.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 333312 |
| InitializedDataSize: | 47616 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x50ac4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00051554 | 0x00051600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54229 |
DATA | 0x00053000 | 0x00000F38 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.97384 |
BSS | 0x00054000 | 0x00000C75 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00055000 | 0x000021A6 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.9013 |
.tls | 0x00058000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00059000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.200582 |
.reloc | 0x0005A000 | 0x000055A0 | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00060000 | 0x00003000 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.76567 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.6633 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
2 | 2.80231 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4085 | 3.14618 | 628 | UNKNOWN | UNKNOWN | RT_STRING |
4086 | 3.11286 | 252 | UNKNOWN | UNKNOWN | RT_STRING |
4087 | 3.14262 | 248 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
oleaut32.dll |
user32.dll |
Total processes
46
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
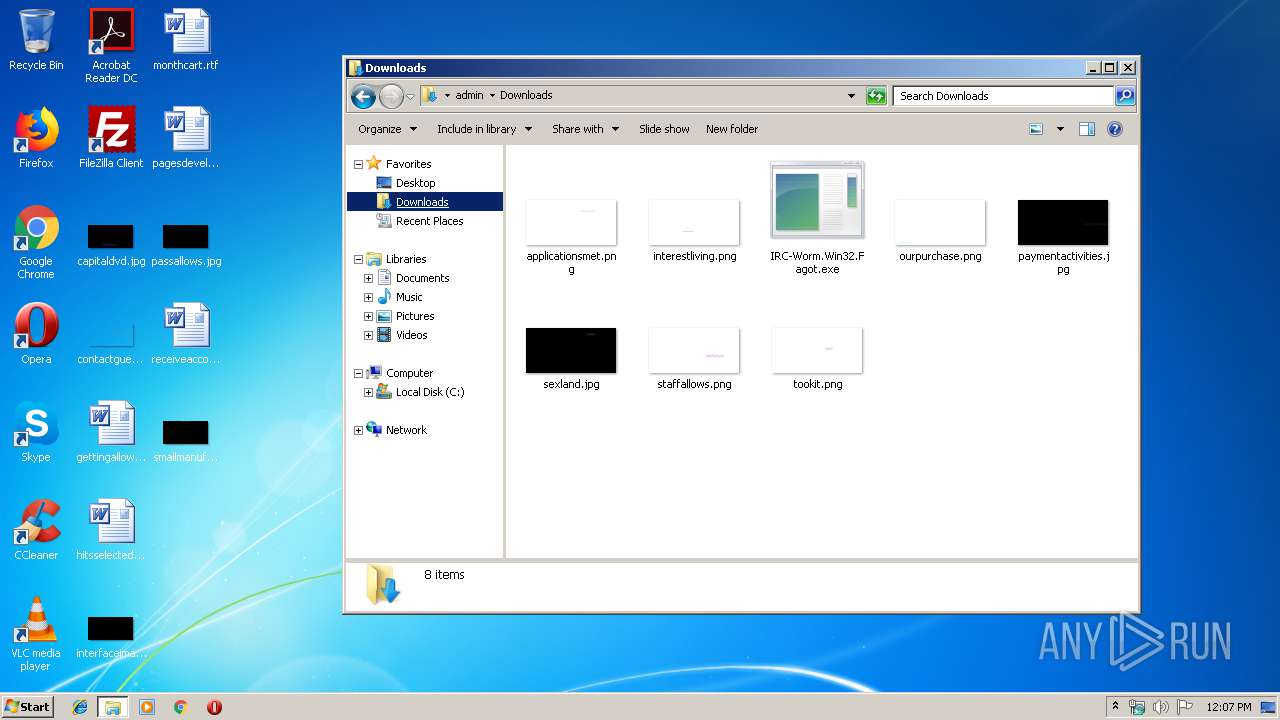
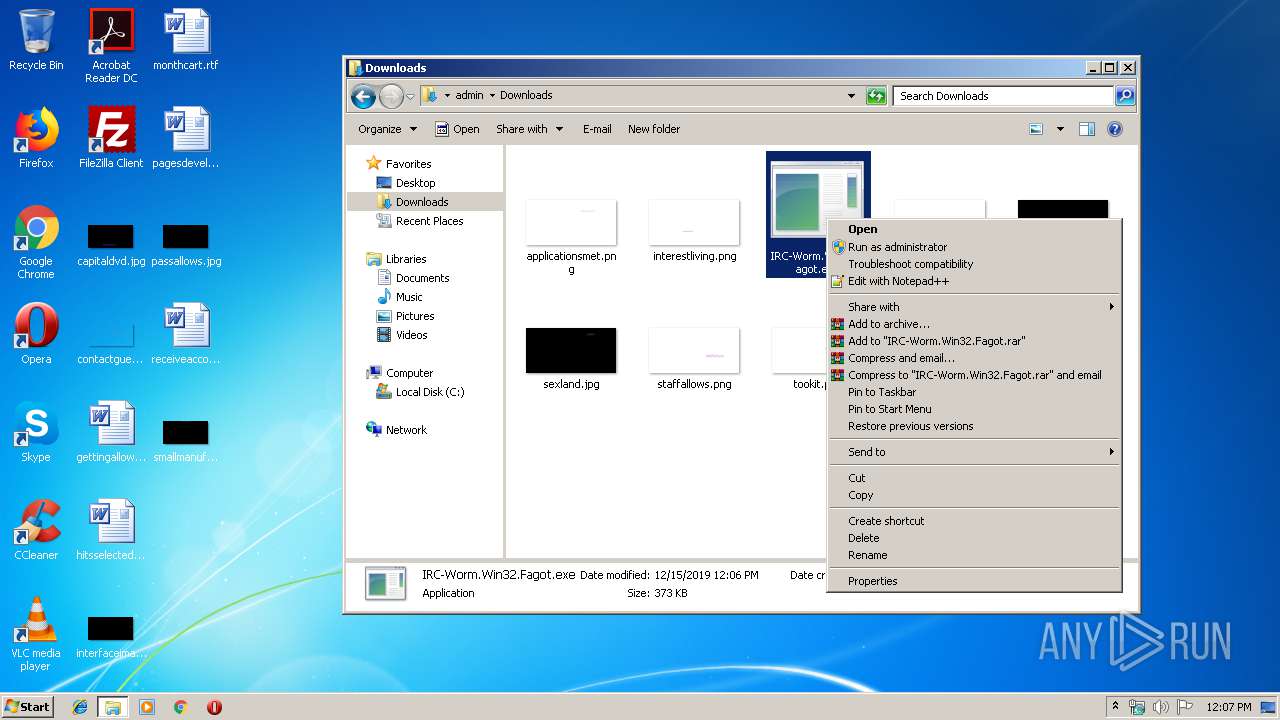
| 1780 | "C:\Users\admin\Downloads\IRC-Worm.Win32.Fagot.exe" | C:\Users\admin\Downloads\IRC-Worm.Win32.Fagot.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1784 | "C:\Users\admin\Downloads\IRC-Worm.Win32.Fagot.exe" | C:\Users\admin\Downloads\IRC-Worm.Win32.Fagot.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\Downloads\IRC-Worm.Win32.Fagot.exe" | C:\Users\admin\Downloads\IRC-Worm.Win32.Fagot.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2912 | "C:\Windows\system32\wermgr.exe" "-outproc" "352" "3644" | C:\Windows\system32\wermgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
13 087
Read events
68
Write events
6
Delete events
13 013
Modification events
| (PID) Process: | (1780) IRC-Worm.Win32.Fagot.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: C:\Windows\system32\userinit32.exe | |||
| (PID) Process: | (2516) IRC-Worm.Win32.Fagot.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Userinit |
Value: C:\Windows\system32\userinit32.exe | |||
| (PID) Process: | (2516) IRC-Worm.Win32.Fagot.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | dllhost32 |
Value: C:\Windows\system32\dllhost32.exe | |||
| (PID) Process: | (2516) IRC-Worm.Win32.Fagot.exe | Key: | HKEY_CURRENT_USER\Printers\DevModes2 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2516) IRC-Worm.Win32.Fagot.exe | Key: | HKEY_CURRENT_USER\Printers\DevModePerUser |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2516) IRC-Worm.Win32.Fagot.exe | Key: | HKEY_CURRENT_USER\Printers\Connections |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2516) IRC-Worm.Win32.Fagot.exe | Key: | HKEY_CURRENT_USER\Printers |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2516) IRC-Worm.Win32.Fagot.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\WinDefend |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2516) IRC-Worm.Win32.Fagot.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\ProfSvc |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2516) IRC-Worm.Win32.Fagot.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\Power |
| Operation: | delete key | Name: | |
Value: | |||
Executable files
10
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_IRC-Worm.Win32.F_fa1030ce183dd6b5bd19dcd88b1efc401fdb8872_cab_0b5a280f\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 2516 | IRC-Worm.Win32.Fagot.exe | C:\Windows\system32\dllhost32.exe | executable | |
MD5:30CDAB5CF1D607EE7B34F44AB38E9190 | SHA256:1517527C1D705A6EBC6EC9194AA95459E875AC3902A9F4AAB3BF24B6A6F8407F | |||
| 2516 | IRC-Worm.Win32.Fagot.exe | C:\windows\system32\chcp.exe | executable | |
MD5:30CDAB5CF1D607EE7B34F44AB38E9190 | SHA256:1517527C1D705A6EBC6EC9194AA95459E875AC3902A9F4AAB3BF24B6A6F8407F | |||
| 2516 | IRC-Worm.Win32.Fagot.exe | C:\windows\system32\bootok.exe | executable | |
MD5:30CDAB5CF1D607EE7B34F44AB38E9190 | SHA256:1517527C1D705A6EBC6EC9194AA95459E875AC3902A9F4AAB3BF24B6A6F8407F | |||
| 2516 | IRC-Worm.Win32.Fagot.exe | C:\windows\system32\imapi.exe | executable | |
MD5:30CDAB5CF1D607EE7B34F44AB38E9190 | SHA256:1517527C1D705A6EBC6EC9194AA95459E875AC3902A9F4AAB3BF24B6A6F8407F | |||
| 2516 | IRC-Worm.Win32.Fagot.exe | C:\windows\system32\logon.exe | executable | |
MD5:30CDAB5CF1D607EE7B34F44AB38E9190 | SHA256:1517527C1D705A6EBC6EC9194AA95459E875AC3902A9F4AAB3BF24B6A6F8407F | |||
| 2516 | IRC-Worm.Win32.Fagot.exe | C:\windows\system32\dumprep.exe | executable | |
MD5:30CDAB5CF1D607EE7B34F44AB38E9190 | SHA256:1517527C1D705A6EBC6EC9194AA95459E875AC3902A9F4AAB3BF24B6A6F8407F | |||
| 2912 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_IRC-Worm.Win32.F_fa1030ce183dd6b5bd19dcd88b1efc401fdb8872_cab_0b5a280f\appcompat.txt | xml | |
MD5:79E128F1E943A419A1E5B5D3B6F8539B | SHA256:7879D8E3BF1A620A6B0C0EB98FBA0C5F963061DDB43D5BA533840A0E56793C83 | |||
| 2516 | IRC-Worm.Win32.Fagot.exe | C:\windows\system32\MDM.exe | executable | |
MD5:30CDAB5CF1D607EE7B34F44AB38E9190 | SHA256:1517527C1D705A6EBC6EC9194AA95459E875AC3902A9F4AAB3BF24B6A6F8407F | |||
| 2516 | IRC-Worm.Win32.Fagot.exe | C:\windows\system32\win.exe | executable | |
MD5:30CDAB5CF1D607EE7B34F44AB38E9190 | SHA256:1517527C1D705A6EBC6EC9194AA95459E875AC3902A9F4AAB3BF24B6A6F8407F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
IRC-Worm.Win32.Fagot.exe | FTH: (2516): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|