| File name: | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe |
| Full analysis: | https://app.any.run/tasks/b7941540-c9ad-4ca6-ba6c-978a7a5be55c |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2023, 23:45:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 2CFF3887C7DA60C8EB27F5B1A80B2D1A |
| SHA1: | D4C82FCB81C8E04EB72C5C1AF57682D93C386DFE |
| SHA256: | 151668EDF7A10B2A3E0C03D7373FE0BC891F75BB524CE33563B4E919EF2A22A6 |
| SSDEEP: | 196608:kS/gAzmxslo9GXzu7/72qe/zscv6WRR0dtt+wR3DhQnRqtoGZg70bQDxvfHjl:kcCCo7/Re/wK6WRudtt+gQnRXgsDx3 |
MALICIOUS
Application was dropped or rewritten from another process
- GameCenter.exe (PID: 3232)
SUSPICIOUS
Reads security settings of Internet Explorer
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
Checks Windows Trust Settings
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
Executable content was dropped or overwritten
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
Reads the Internet Settings
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
- GameCenter.exe (PID: 3232)
Detected use of alternative data streams (AltDS)
- GameCenter.exe (PID: 3232)
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
Reads settings of System Certificates
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
Searches for installed software
- GameCenter.exe (PID: 3232)
Connects to unusual port
- GameCenter.exe (PID: 3232)
INFO
Checks supported languages
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
- GameCenter.exe (PID: 3232)
- wmpnscfg.exe (PID: 3228)
Creates files or folders in the user directory
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
- GameCenter.exe (PID: 3232)
The process checks LSA protection
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
- GameCenter.exe (PID: 3232)
- wmpnscfg.exe (PID: 3228)
Reads the machine GUID from the registry
- GameCenter.exe (PID: 3232)
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
- wmpnscfg.exe (PID: 3228)
Process checks computer location settings
- GameCenter.exe (PID: 3232)
Reads the computer name
- GameCenter.exe (PID: 3232)
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
- wmpnscfg.exe (PID: 3228)
Checks proxy server information
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
Create files in a temporary directory
- BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe (PID: 2640)
[YARA] Network interface manipulation strings were found
- GameCenter.exe (PID: 3232)
Manual execution by a user
- wmpnscfg.exe (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| ProductVersion: | 4.0.1714.63306 |
|---|---|
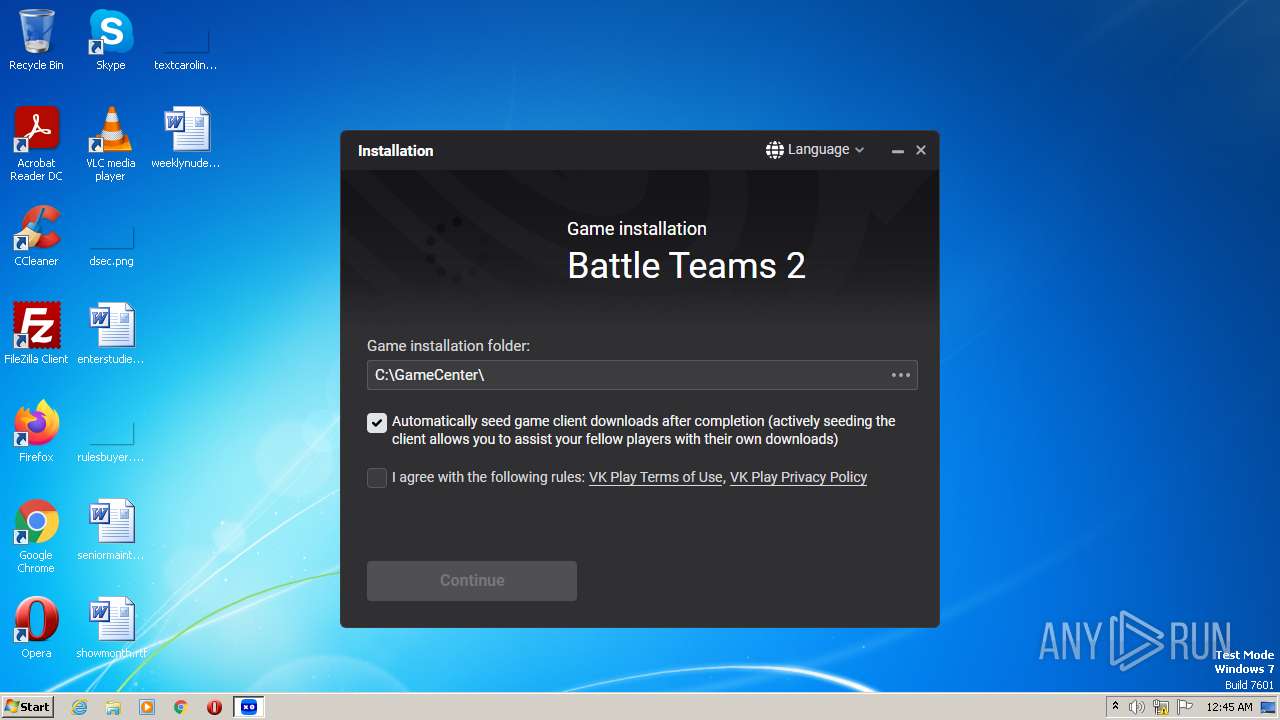
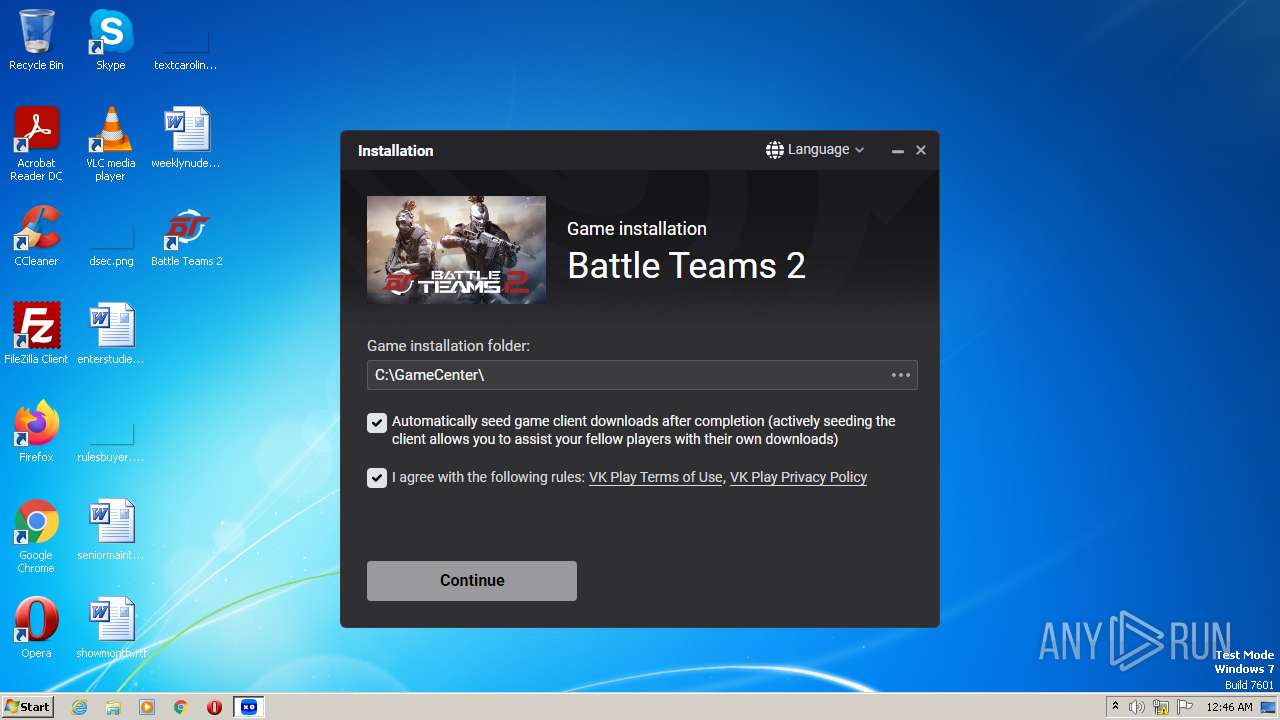
| ProductName: | GameCenter |
| OriginalFileName: | GameCenter.exe |
| LegalCopyright: | Copyright (C) 2023 VK Play LLC |
| FileVersion: | 4.0.1714.63306 |
| FileDescription: | GameCenter |
| CompanyName: | VK Play LLC |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 4.0.1714.63306 |
| FileVersionNumber: | 4.0.1714.63306 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x24892f0 |
| UninitializedDataSize: | 25886720 |
| InitializedDataSize: | 28672 |
| CodeSize: | 12423168 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 2023:03:29 07:32:03+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Mar-2023 07:32:03 |
| Detected languages: |
|
| CompanyName: | VK Play LLC |
| FileDescription: | GameCenter |
| FileVersion: | 4.0.1714.63306 |
| LegalCopyright: | Copyright (C) 2023 VK Play LLC |
| OriginalFilename: | GameCenter.exe |
| ProductName: | GameCenter |
| ProductVersion: | 4.0.1714.63306 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 29-Mar-2023 07:32:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x018B0000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x018B1000 | 0x00BD9000 | 0x00BD9000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99999 |
.rsrc | 0x0248A000 | 0x00007000 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.48593 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33982 | 1376 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 7.7275 | 1067 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 7.78984 | 1592 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 7.88551 | 2520 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 7.88677 | 3468 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 7.92774 | 6786 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 7.80665 | 5123 | Latin 1 / Western European | English - United States | RT_ICON |
4088 | 7.07276 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4089 | 7.74417 | 744 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 7.74084 | 824 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
KERNEL32.DLL |
advapi32.dll |
crypt32.dll |
netapi32.dll |
ntdll.dll |
ole32.dll |
oleaut32.dll |
psapi.dll |
shell32.dll |
user32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x0007D628 |
__dbk_fcall_wrapper | 2 | 0x0000BDC8 |
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2640 | "C:\Users\admin\AppData\Local\Temp\BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe" | C:\Users\admin\AppData\Local\Temp\BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | explorer.exe | ||||||||||||
User: admin Company: VK Play LLC Integrity Level: MEDIUM Description: GameCenter Exit code: 0 Version: 4.0.1714.63306 Modules
| |||||||||||||||
| 3228 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3232 | "C:\Users\admin\AppData\Local\GameCenter\GameCenter.exe" -startedbysetup "installer=C:\Users\admin\AppData\Local\Temp\BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe" game=0.2016988 -removeifinstallcanceled | C:\Users\admin\AppData\Local\GameCenter\GameCenter.exe | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | ||||||||||||
User: admin Company: VK Play LLC Integrity Level: MEDIUM Description: GameCenter.exe Exit code: 0 Version: 4.0.1714.63306 Modules
| |||||||||||||||
Total events
25 642
Read events
25 534
Write events
102
Delete events
6
Modification events
| (PID) Process: | (2640) BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2640) BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2640) BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2640) BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2640) BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2640) BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2640) BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3232) GameCenter.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Explorer.EXE | |||
| (PID) Process: | (2640) BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2640) BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
24
Suspicious files
28
Text files
34
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | C:\Users\admin\AppData\Local\GameCenter\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | C:\Users\admin\AppData\Local\GameCenter\GameCenter.exe.sig | pi2 | |
MD5:— | SHA256:— | |||
| 2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | C:\Users\admin\AppData\Local\GameCenter\bigup2.dll.sig | pi2 | |
MD5:— | SHA256:— | |||
| 2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | C:\Users\admin\AppData\Local\GameCenter\libcurl.dll.sig | pi2 | |
MD5:— | SHA256:— | |||
| 2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | C:\Users\admin\AppData\Local\GameCenter\SkiAcc.dll.sig | pi2 | |
MD5:— | SHA256:— | |||
| 2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | C:\Users\admin\AppData\Local\GameCenter\bigup2.dll | executable | |
MD5:— | SHA256:— | |||
| 2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | C:\Users\admin\AppData\Local\GameCenter\gclay.dll | executable | |
MD5:— | SHA256:— | |||
| 2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | C:\Users\admin\AppData\Local\GameCenter\HG64.exe | executable | |
MD5:— | SHA256:— | |||
| 2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | C:\Users\admin\AppData\Local\GameCenter\lightupdate.dll.sig | pi2 | |
MD5:— | SHA256:— | |||
| 2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | C:\Users\admin\AppData\Local\GameCenter\GCLay64.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
51
DNS requests
31
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3232 | GameCenter.exe | GET | — | 188.93.63.21:80 | http://p2p.dl.mail.ru/announce.php?info_hash=%8d%c8%e4dC%94D%98T%8f%f5%5c%20%a6%19%d00%d6%60%0b&peer_id=-BU12M0-AvlLWNlUUFDd&port=6881&uploaded=0&downloaded=0&left=100312&corrupt=0&key=CC976340&event=started&numwant=200&compact=1&no_peer_id=1&redundant=0&ip=192.168.100.51 | RU | — | — | suspicious |
3232 | GameCenter.exe | GET | 200 | 185.30.176.134:80 | http://static.gc.my.com/trnts/ipspec.xml?_c_1383098787 | NL | xml | 10.0 Kb | suspicious |
2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | GET | 200 | 2.16.241.12:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMoYfBVif0Eq0AUSUQfepl0Hw%3D%3D | unknown | der | 503 b | shared |
3232 | GameCenter.exe | GET | 200 | 185.30.176.134:80 | http://static.gc.my.com/trnts/mirrors.xml?_c_523514630 | NL | xml | 1.44 Kb | suspicious |
3232 | GameCenter.exe | GET | 200 | 185.30.176.134:80 | http://static.gc.my.com/trnts/repository.xml?_c_635000241 | NL | xml | 1.67 Kb | suspicious |
3232 | GameCenter.exe | GET | 200 | 188.93.63.180:80 | http://static.gc.vkplay.ru/torrents/mirrors.xml?_c_1452055330 | RU | xml | 528 b | suspicious |
3232 | GameCenter.exe | GET | 200 | 185.30.176.134:80 | http://static.gc.my.com/trnts/revision.txt?_c_2143985715 | NL | text | 6 b | suspicious |
3232 | GameCenter.exe | GET | 200 | 185.30.176.134:80 | http://static.gc.my.com/trnts/mcsettings.xml?_c_184448122 | NL | xml | 967 b | suspicious |
2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | GET | 200 | 23.37.41.57:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | GET | 200 | 8.241.9.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?4fb10617a3cfd060 | US | compressed | 61.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | 178.22.88.34:443 | stat.gc.my.games | LLC VK | RU | suspicious |
3232 | GameCenter.exe | 178.22.89.26:443 | authdl.vkplay.ru | LLC VK | RU | unknown |
2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | 23.37.41.57:80 | x1.c.lencr.org | AKAMAI-AS | DE | suspicious |
2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | 2.16.241.12:80 | r3.o.lencr.org | Akamai International B.V. | DE | suspicious |
2640 | BattleTeams2Loader_c9b3eb225e44fdfbf17869a4a04fb47f.exe | 8.241.9.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3232 | GameCenter.exe | 178.22.88.34:443 | stat.gc.my.games | LLC VK | RU | suspicious |
3232 | GameCenter.exe | 178.22.89.40:443 | games.mail.ru | LLC VK | RU | unknown |
— | — | 185.30.176.134:80 | static.gc.my.com | My.com B.V. | NL | suspicious |
— | — | 188.93.63.180:80 | static.gc.vkplay.ru | LLC VK | RU | suspicious |
3232 | GameCenter.exe | 185.30.176.134:443 | static.gc.my.com | My.com B.V. | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stat.gc.my.games |
| suspicious |
authdl.vkplay.ru |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
games.mail.ru |
| unknown |
stat.gc.vkplay.ru |
| unknown |
router.utorrent.com |
| whitelisted |
router.bittorrent.com |
| shared |
dht.transmissionbt.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
3232 | GameCenter.exe | Potential Corporate Privacy Violation | GPL P2P BitTorrent transfer |
6 ETPRO signatures available at the full report