| File name: | ACESETUP.EXE |
| Full analysis: | https://app.any.run/tasks/ebe66bbd-f7d3-4a88-b49c-ce9fb9efed23 |
| Verdict: | Malicious activity |
| Analysis date: | September 12, 2020, 09:00:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D72657FA3BF7CB5395A654FD5BB78260 |
| SHA1: | 606E1CE5377E9966106EE72674AA61B200C6BC0C |
| SHA256: | 1511EDF42BCAED5580EF8632AEE6CEB9AF23D3B1CA9BB2ABA8E71FA2331DFE87 |
| SSDEEP: | 24576:s1q5MIW9vJcE3btQ60F4T5zoLz+VSB7Ps+dv3YTXUSeG00E098lne5L5RhM:d5t3o0koLyVY70+BITgXk98E5RhM |
MALICIOUS
Application was dropped or rewritten from another process
- irsetup.exe (PID: 2712)
- RCT acCeSS.exe (PID: 1852)
SUSPICIOUS
Executable content was dropped or overwritten
- ACESETUP.EXE (PID: 2004)
- irsetup.exe (PID: 2712)
Creates files in the program directory
- irsetup.exe (PID: 2712)
Removes files from Windows directory
- irsetup.exe (PID: 2712)
Creates files in the Windows directory
- irsetup.exe (PID: 2712)
Creates a software uninstall entry
- irsetup.exe (PID: 2712)
INFO
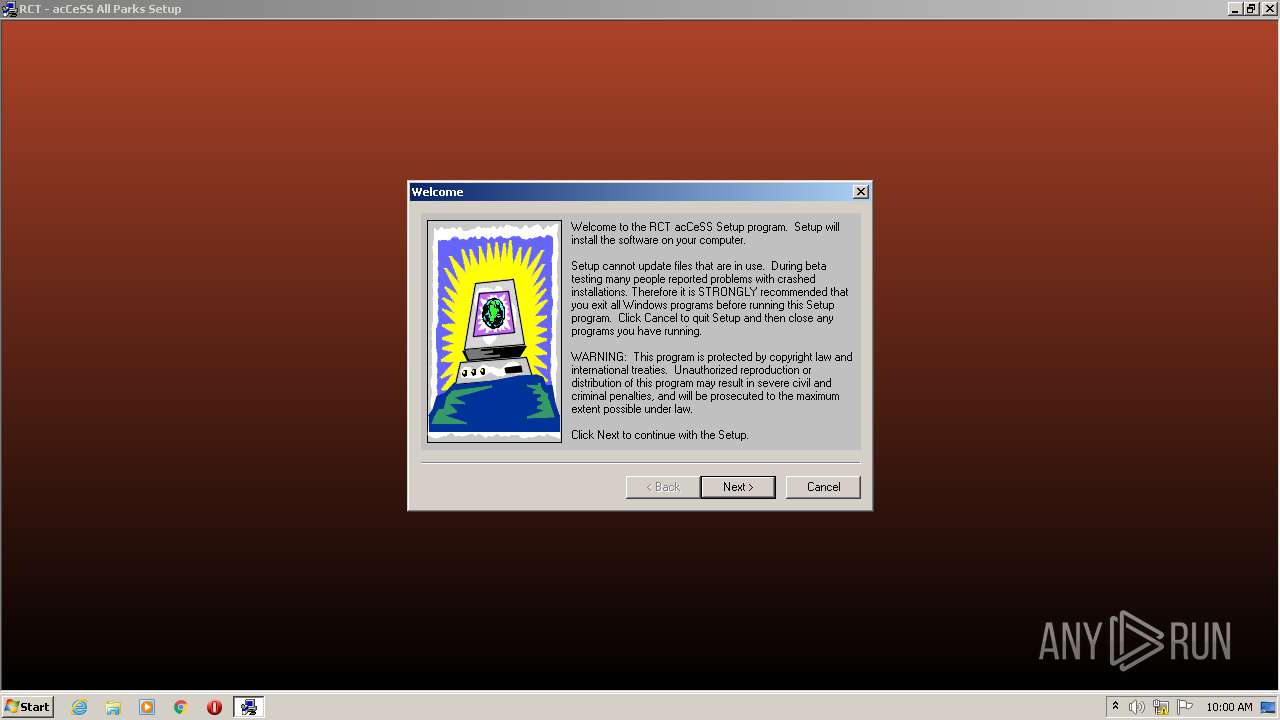
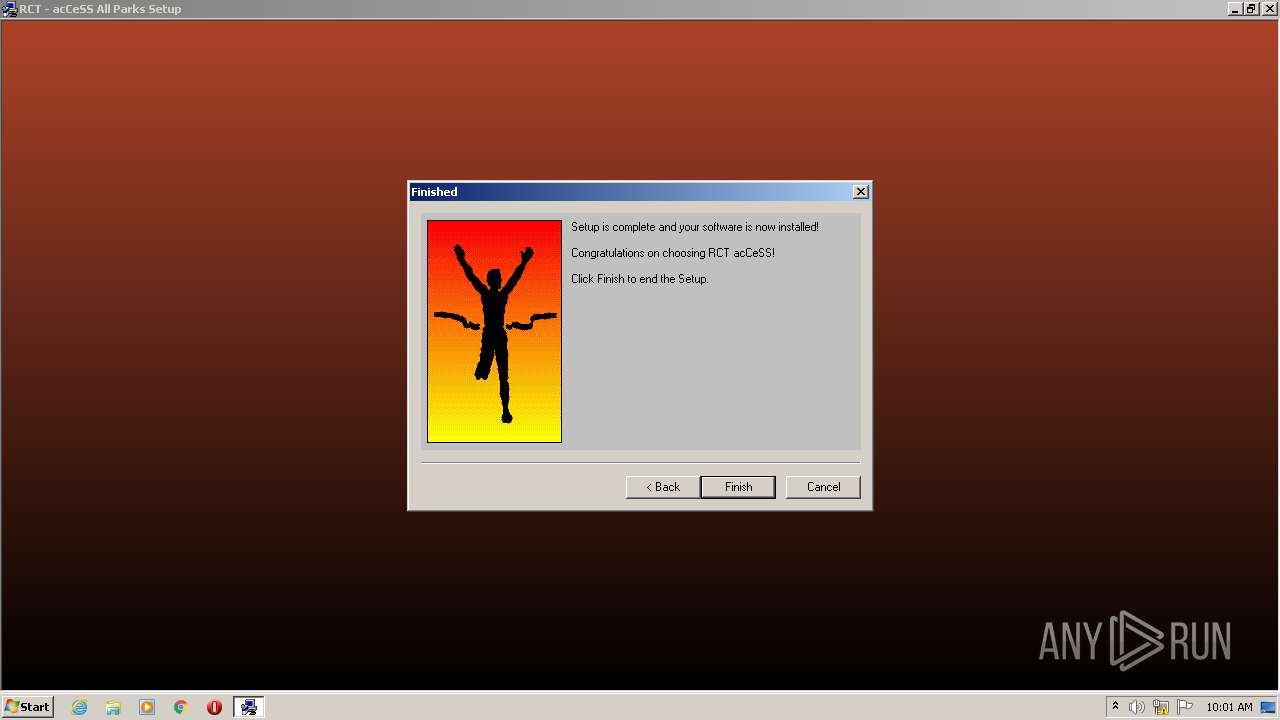
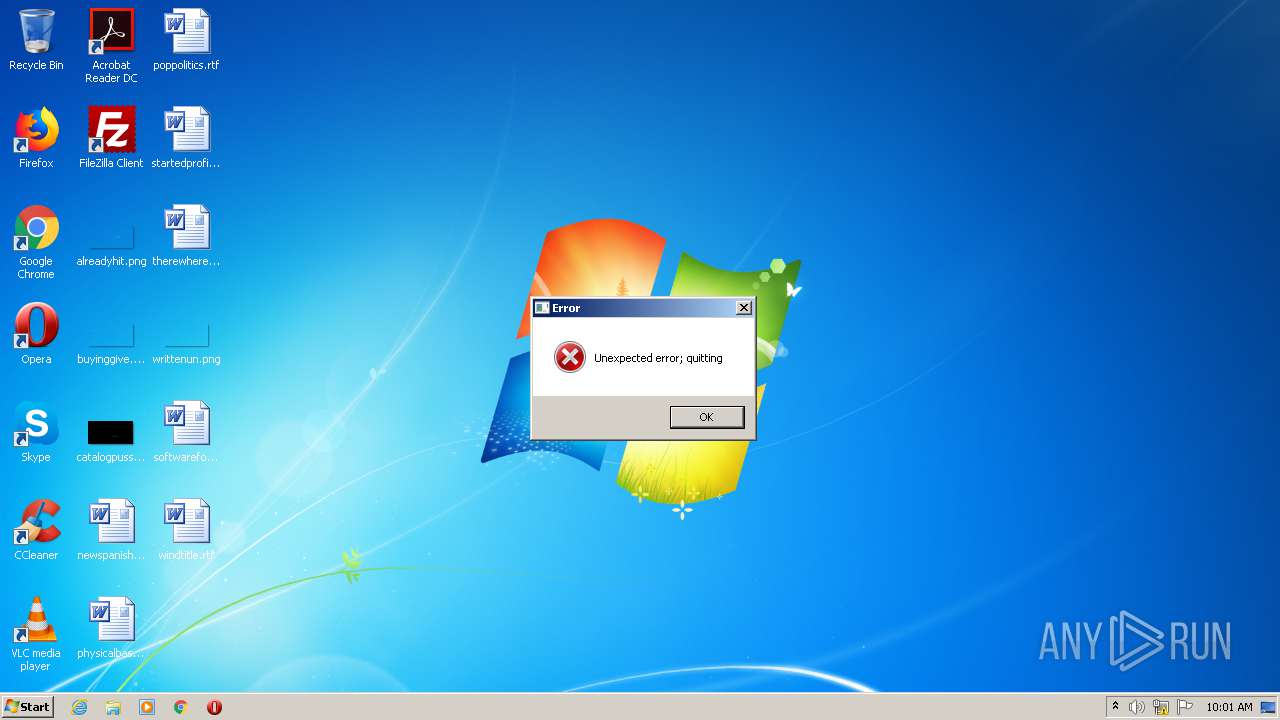
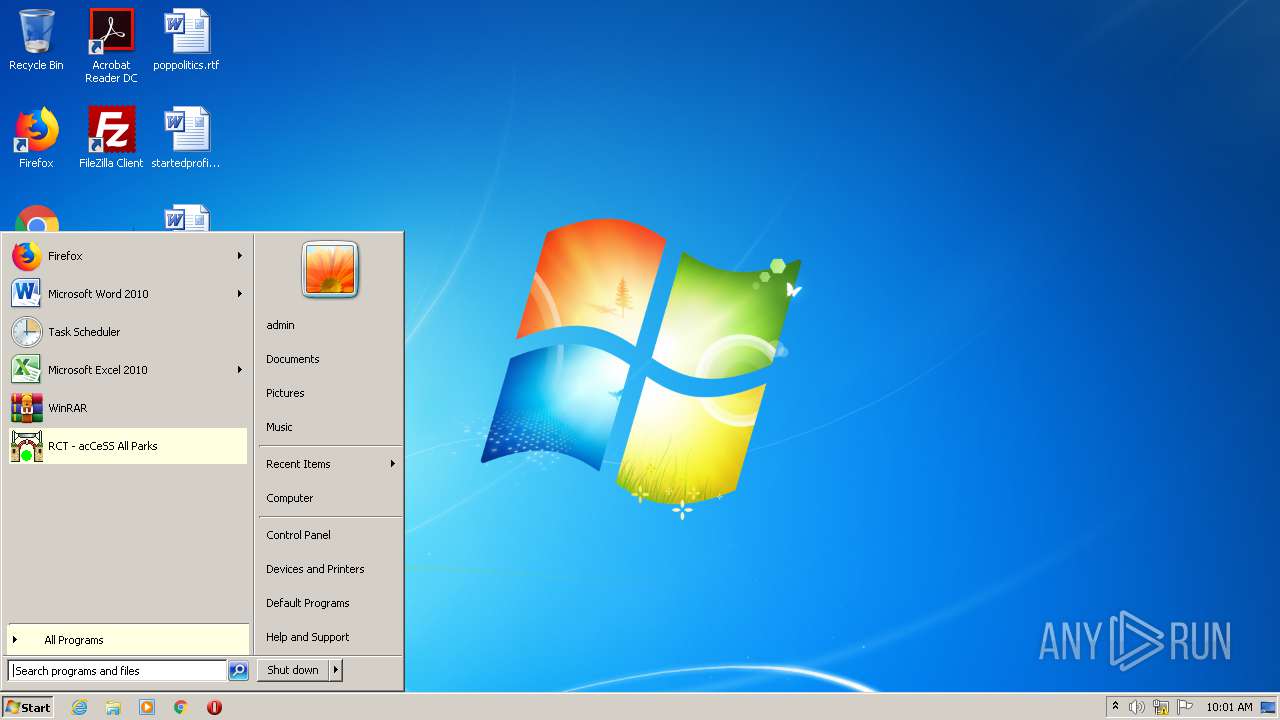
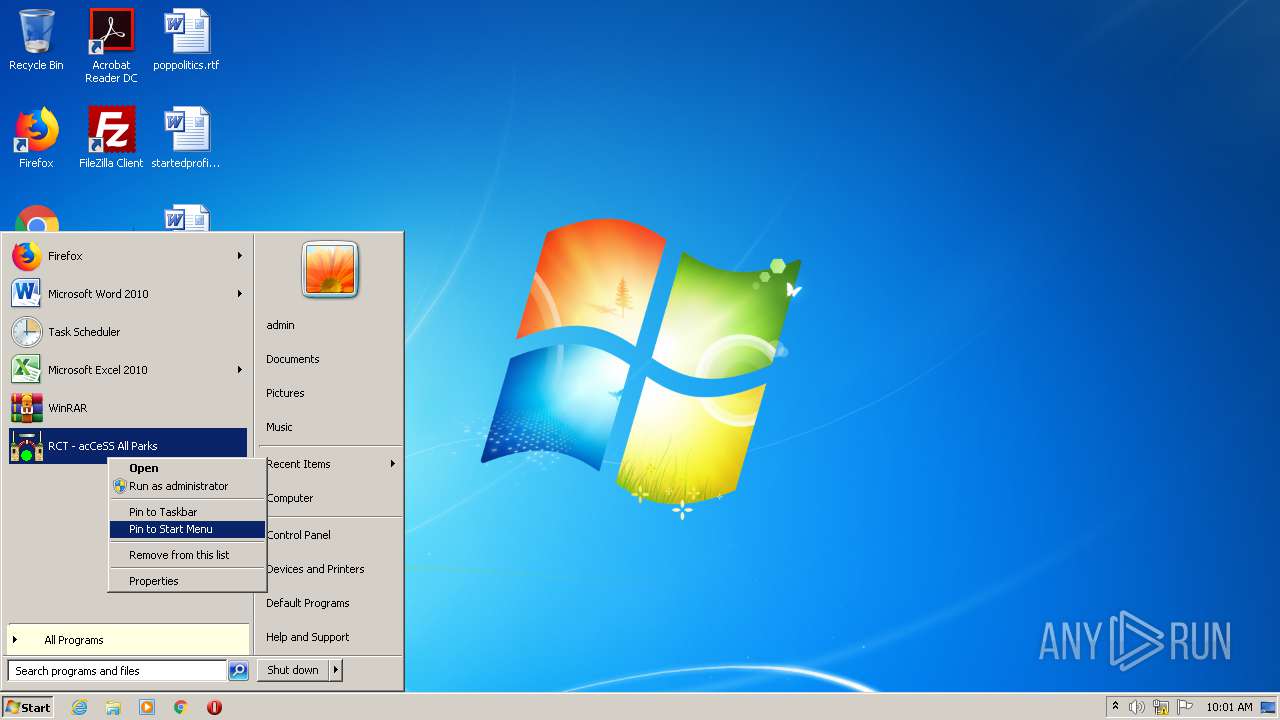
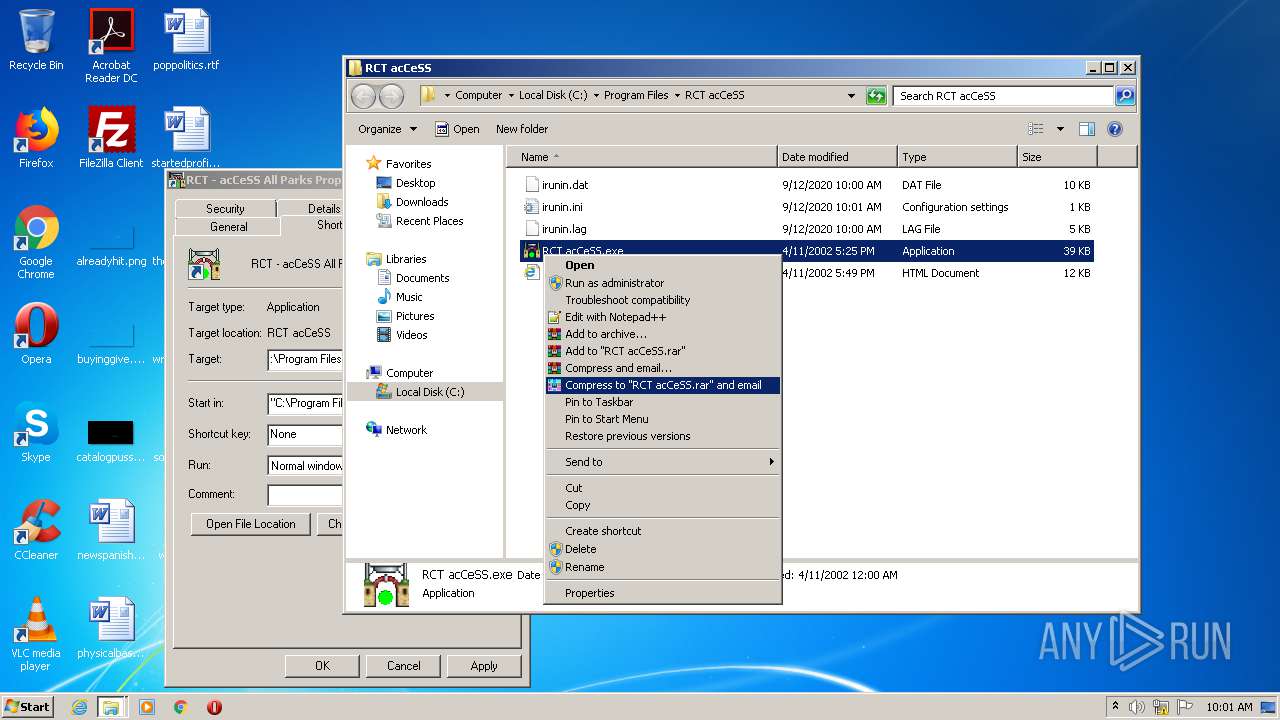
Manual execution by user
- RCT acCeSS.exe (PID: 1852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (40.9) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win32 Executable MS Visual FoxPro 7 (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2000:04:12 23:01:32+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 16384 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20fb |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.8.0 |
| ProductVersionNumber: | 4.0.8.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
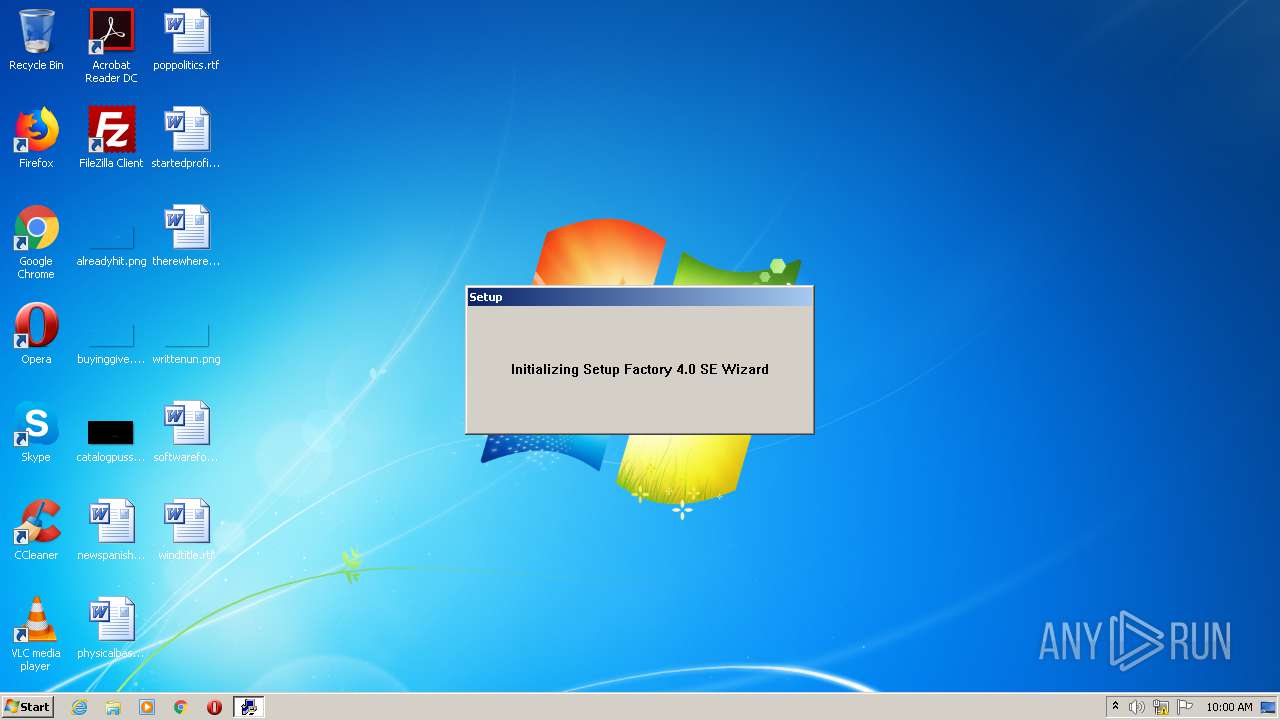
| Comments: | This setup code is the property of Indigo Rose Corporation - Setup Factory 4.0 SE |
| CompanyName: | Indigo Rose Corporation http://www.indigorose.com |
| FileDescription: | Setup Factory 4.0 SE setup launcher |
| FileVersion: | 4.08 |
| InternalName: | setup |
| LegalCopyright: | Copyright © 2000 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFileName: | setup.exe |
| PrivateBuild: | - |
| ProductName: | Setup Factory SE |
| ProductVersion: | 4.08 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Apr-2000 21:01:32 |
| Detected languages: |
|
| Comments: | This setup code is the property of Indigo Rose Corporation - Setup Factory 4.0 SE |
| CompanyName: | Indigo Rose Corporation http://www.indigorose.com |
| FileDescription: | Setup Factory 4.0 SE setup launcher |
| FileVersion: | 4.08 |
| InternalName: | setup |
| LegalCopyright: | Copyright © 2000 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFilename: | setup.exe |
| PrivateBuild: | - |
| ProductName: | Setup Factory SE |
| ProductVersion: | 4.08 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 12-Apr-2000 21:01:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00003866 | 0x00004000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.08192 |
.rdata | 0x00005000 | 0x00000B32 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.21465 |
.data | 0x00006000 | 0x00001658 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.64204 |
.rsrc | 0x00008000 | 0x00000E70 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.34143 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.38157 | 1256 | UNKNOWN | English - United States | RT_VERSION |
2 | 2.76778 | 296 | UNKNOWN | English - United States | RT_ICON |
101 | 2.37086 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
44
Monitored processes
4
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
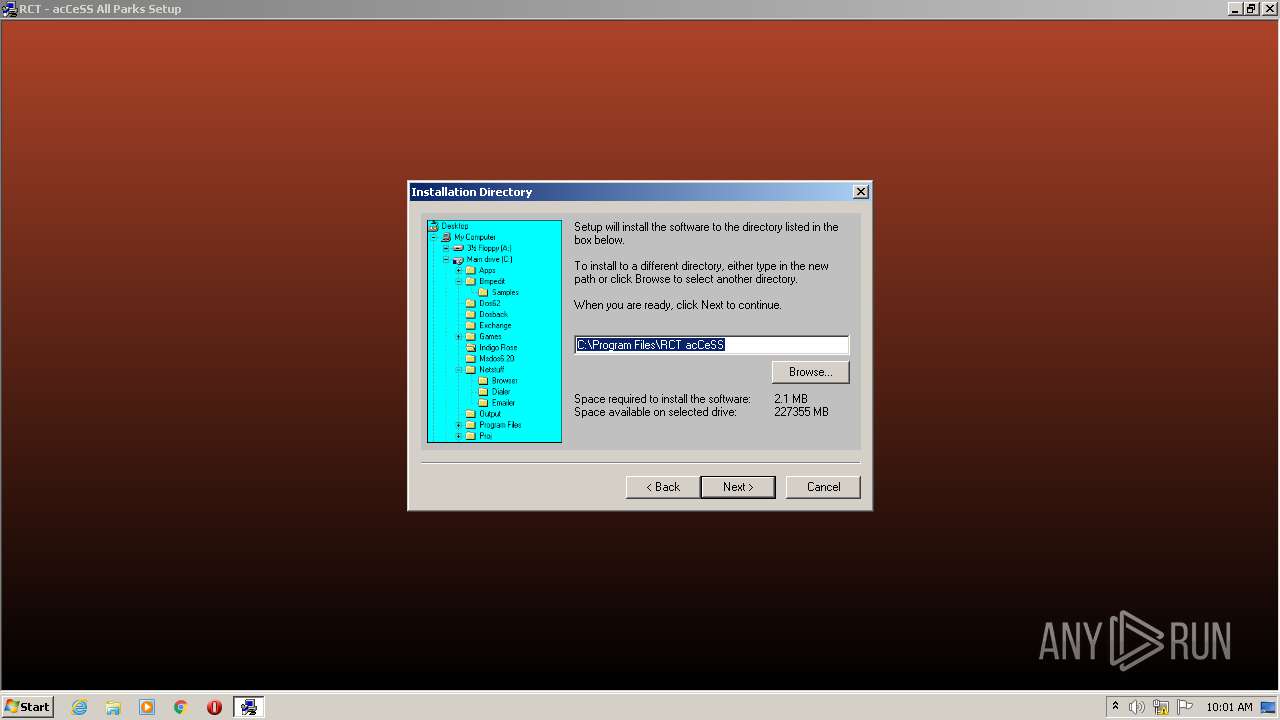
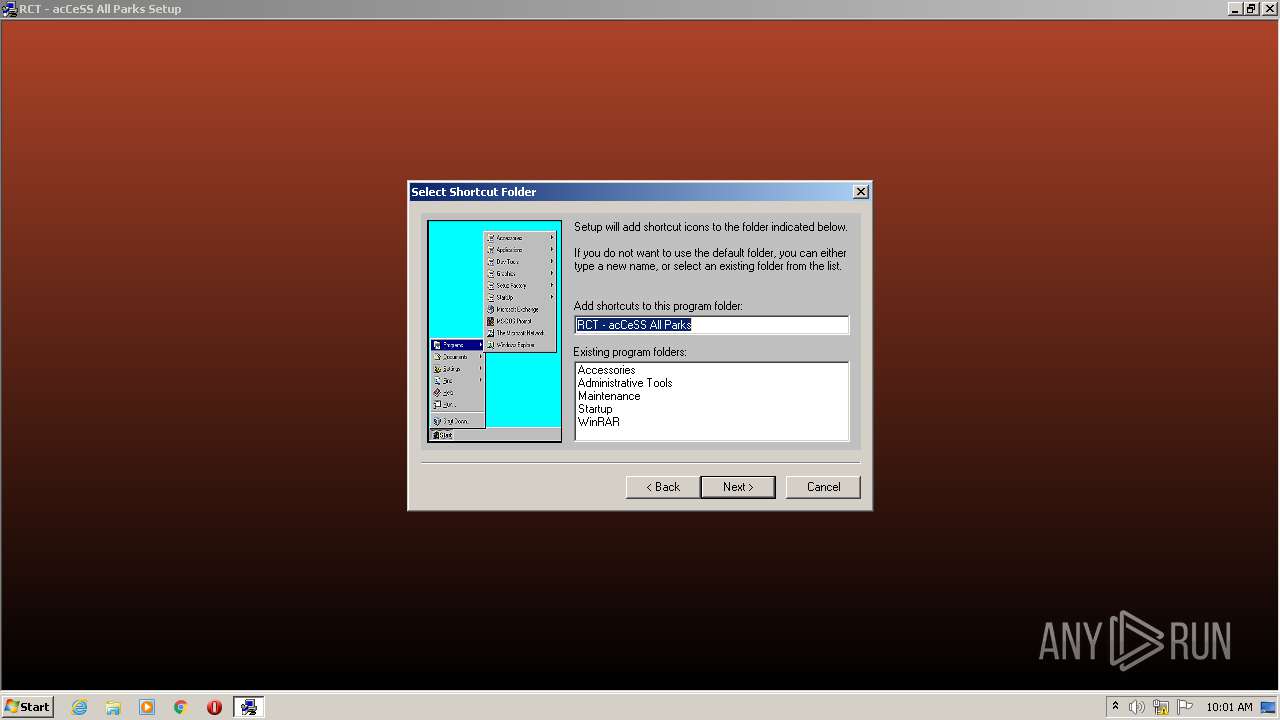
| 928 | "C:\Users\admin\AppData\Local\Temp\ACESETUP.EXE" | C:\Users\admin\AppData\Local\Temp\ACESETUP.EXE | — | explorer.exe | |||||||||||
User: admin Company: Indigo Rose Corporation http://www.indigorose.com Integrity Level: MEDIUM Description: Setup Factory 4.0 SE setup launcher Exit code: 3221226540 Version: 4.08 Modules
| |||||||||||||||
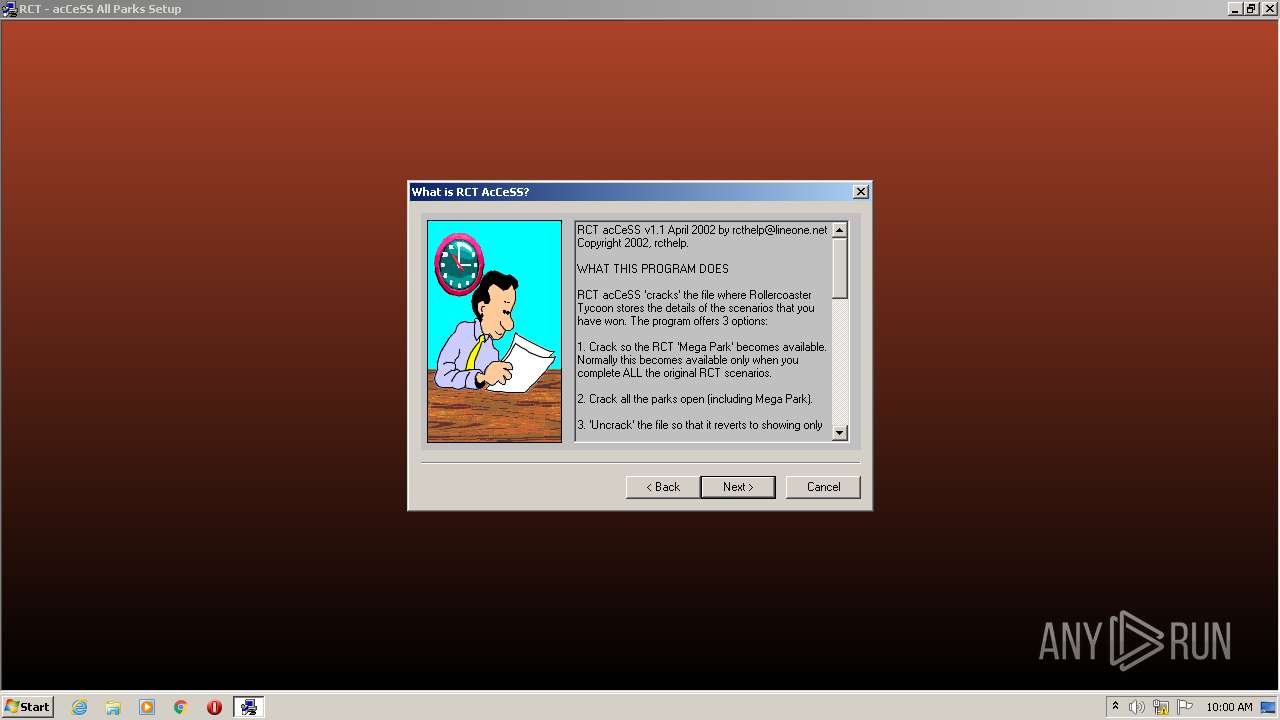
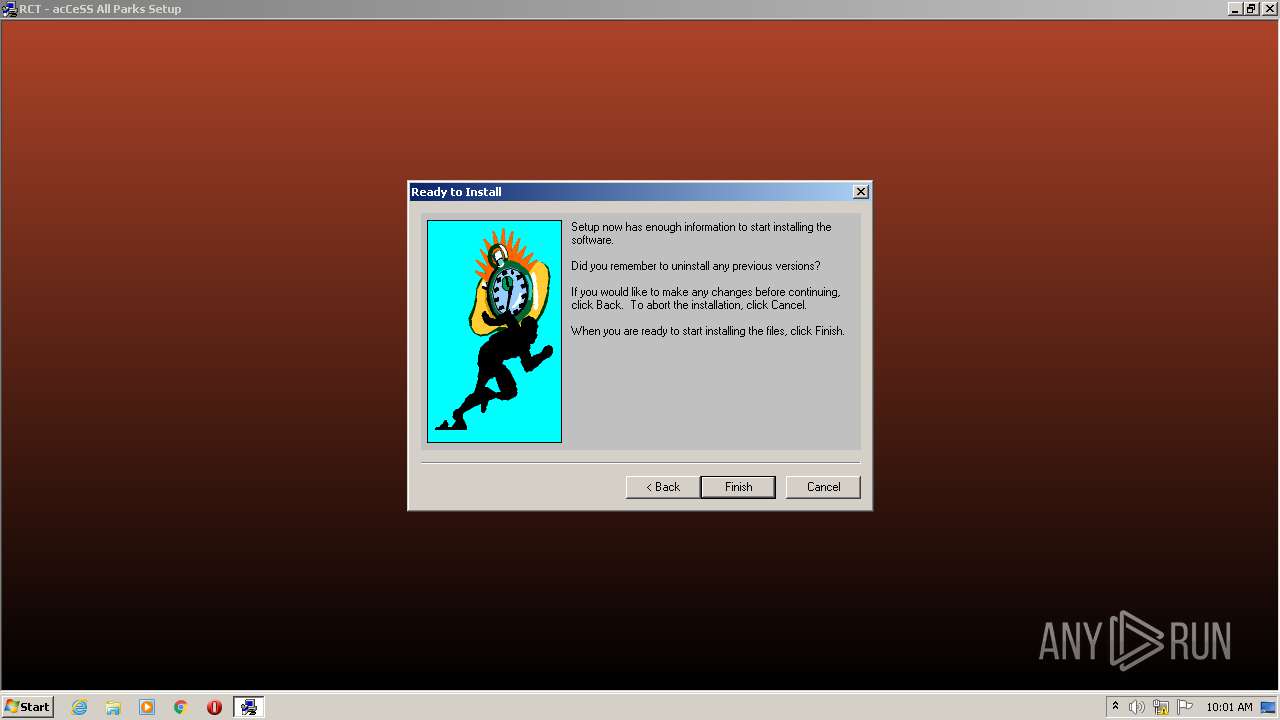
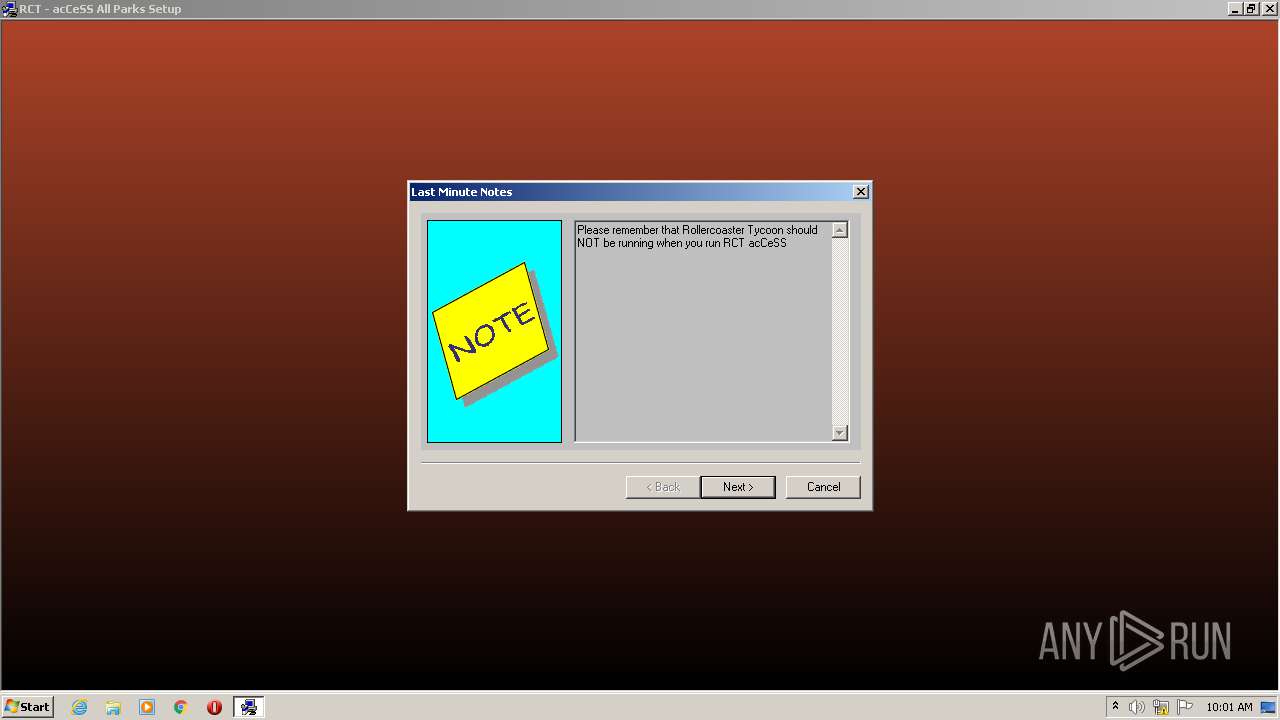
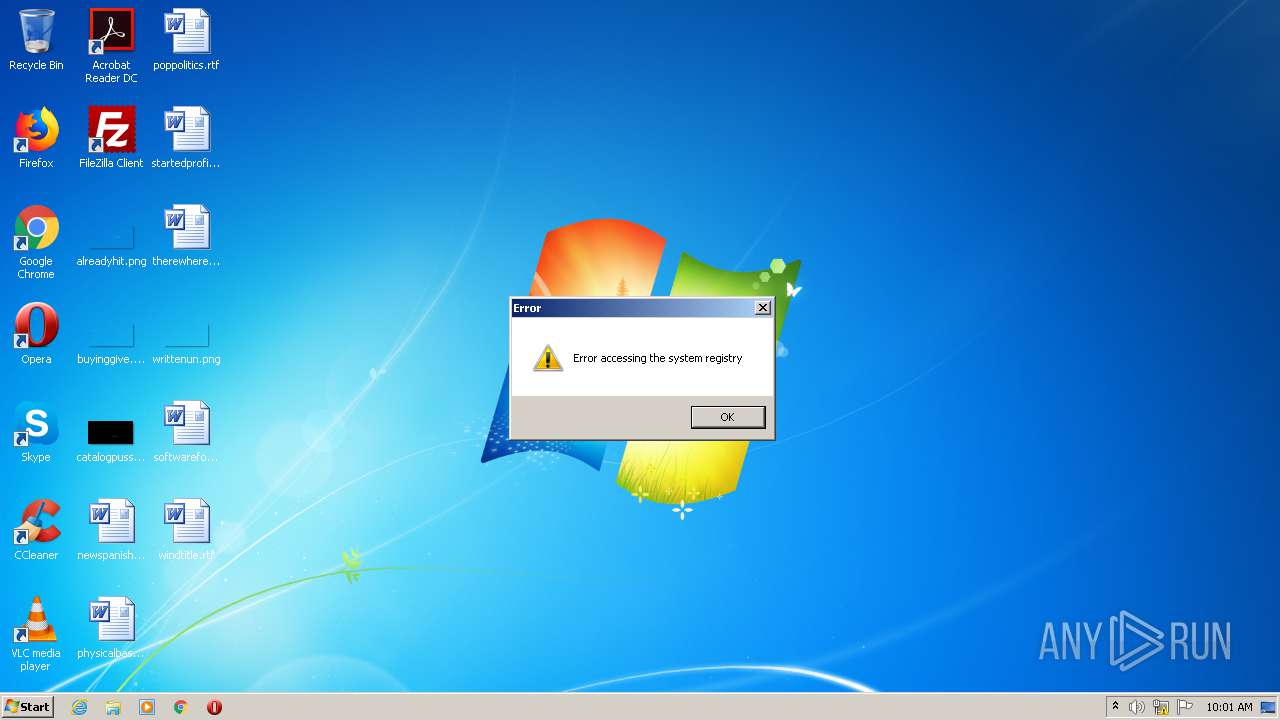
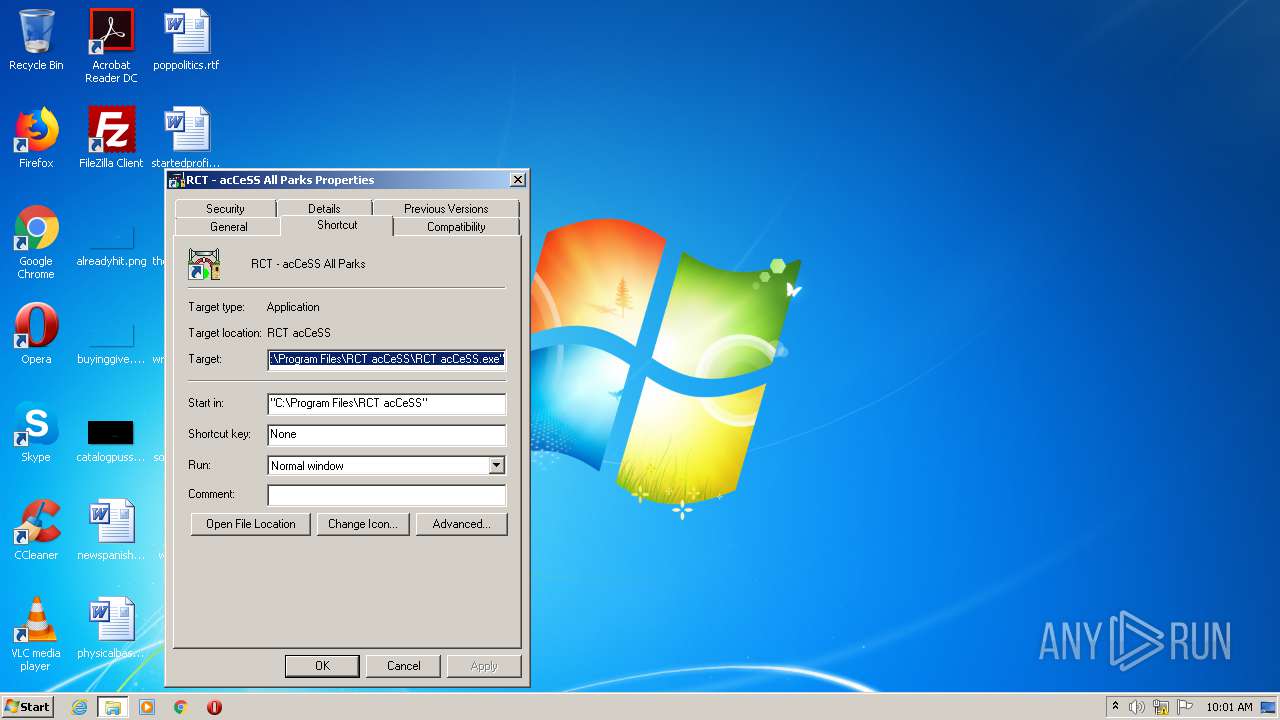
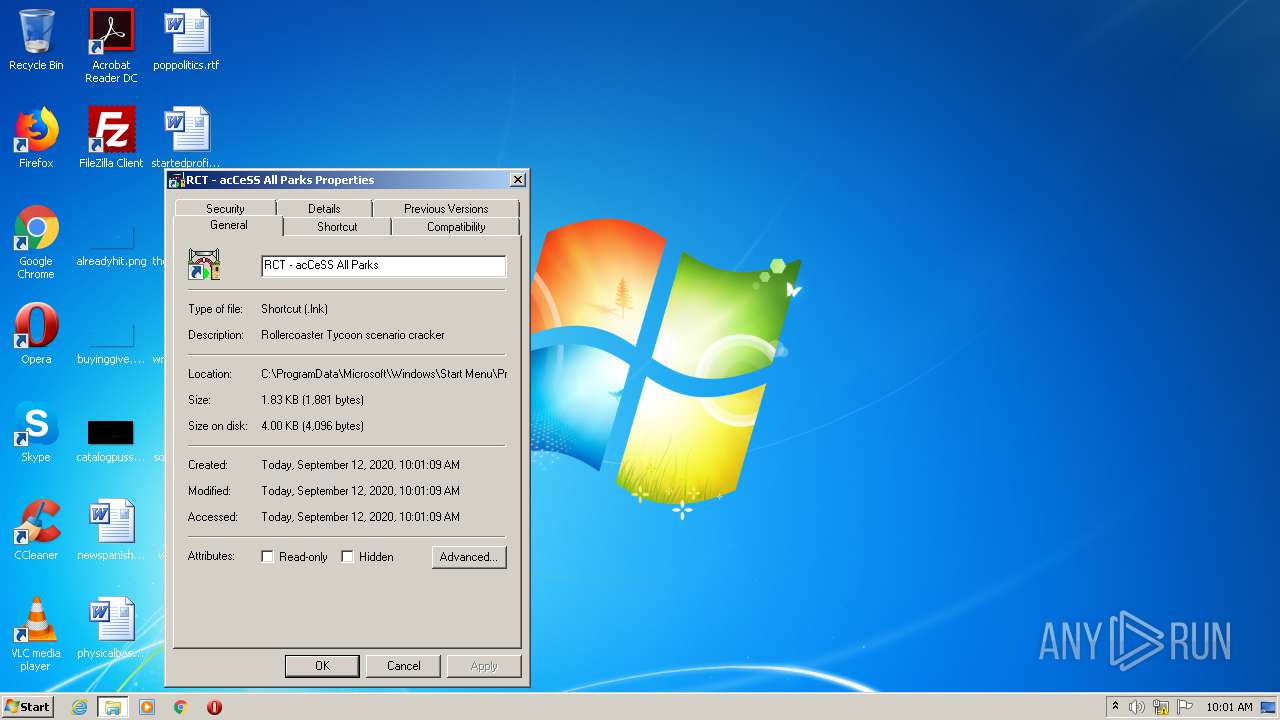
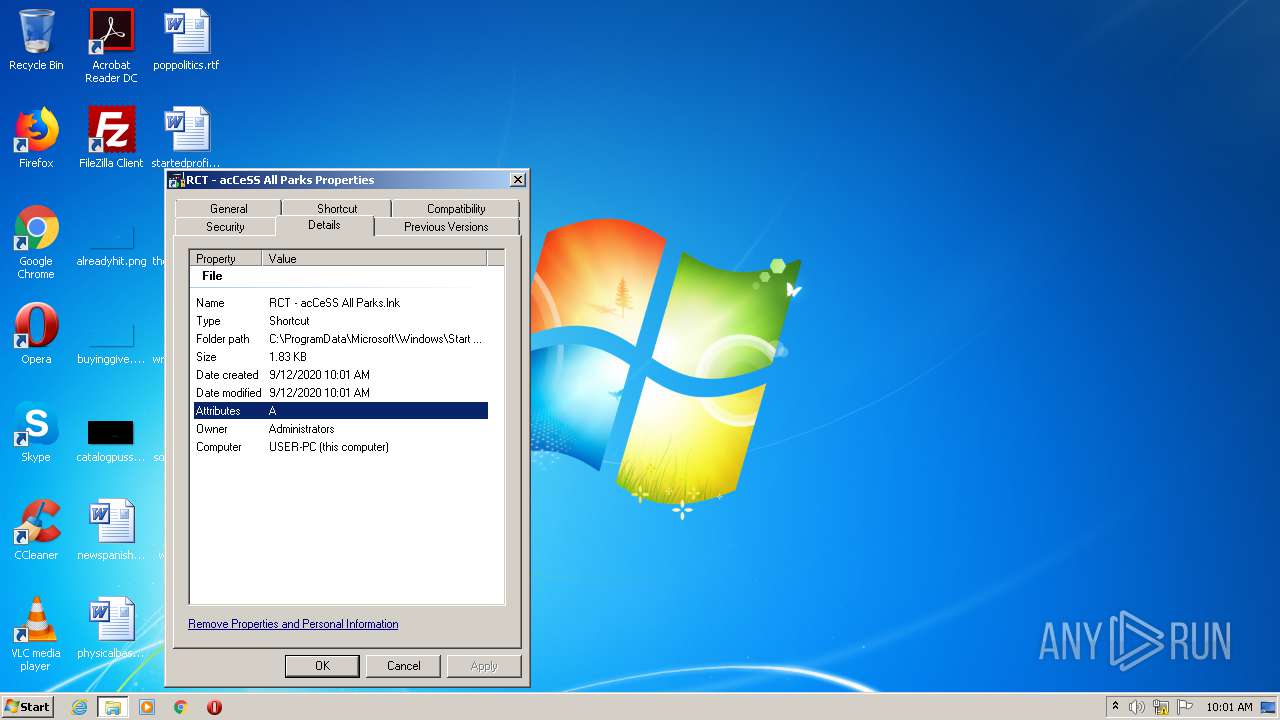
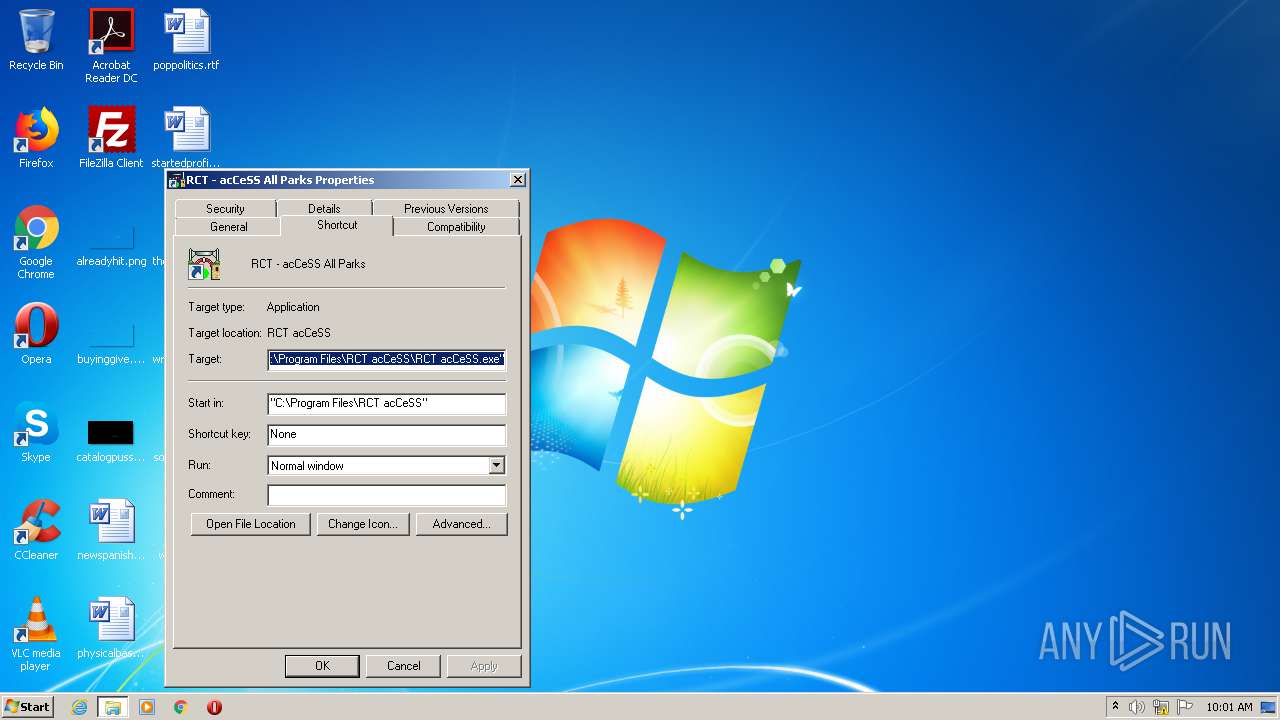
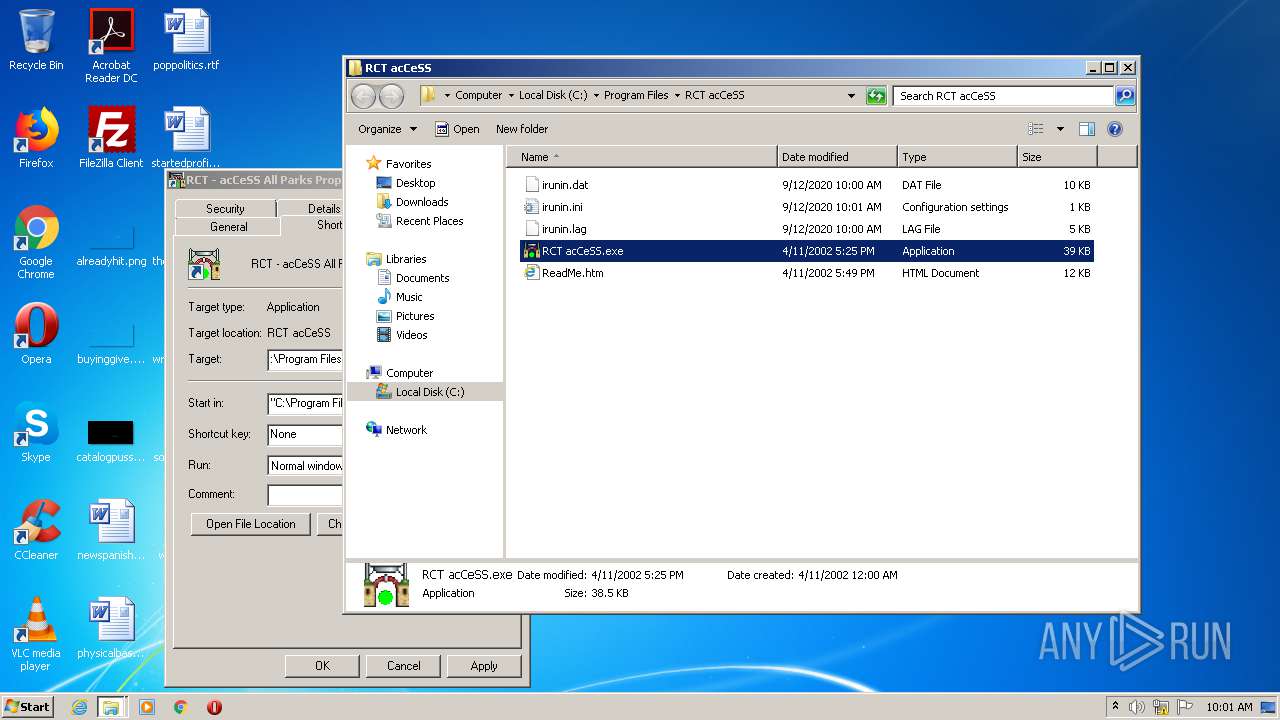
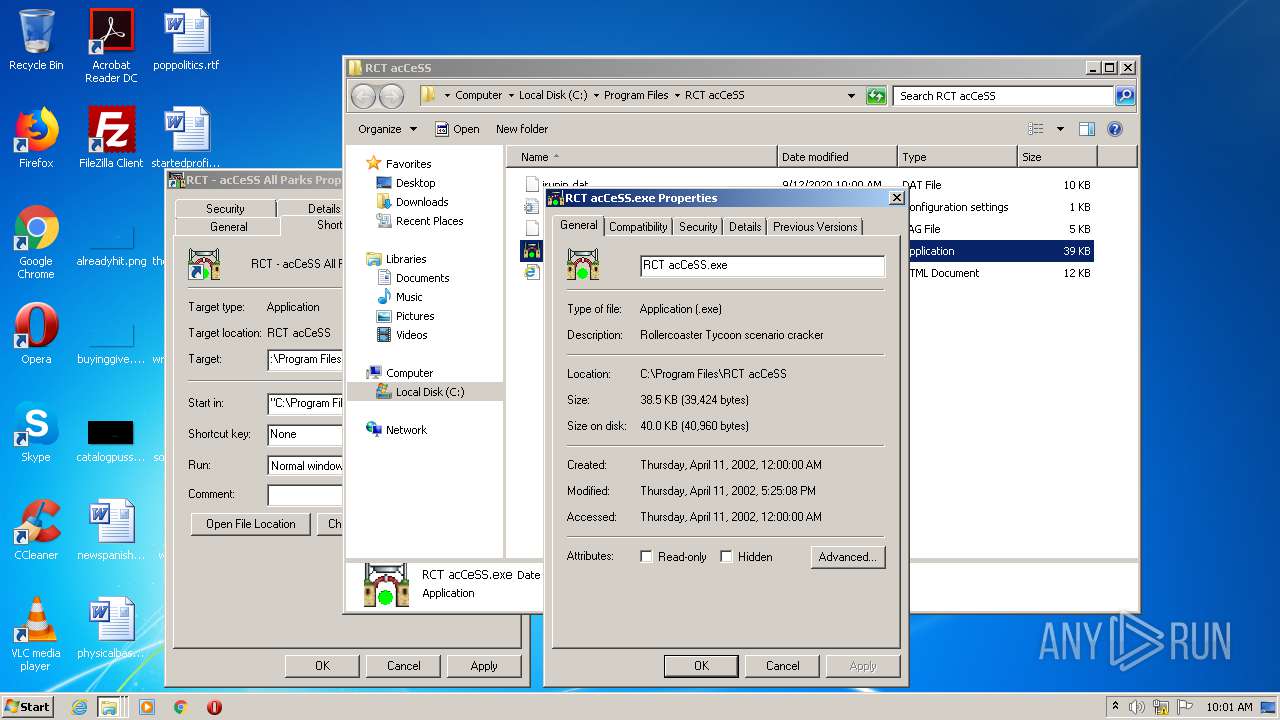
| 1852 | "C:\Program Files\RCT acCeSS\RCT acCeSS.exe" | C:\Program Files\RCT acCeSS\RCT acCeSS.exe | — | explorer.exe | |||||||||||
User: admin Company: Ferneberga Industries Integrity Level: MEDIUM Description: Rollercoaster Tycoon scenario cracker Exit code: 0 Version: 1.01 Modules
| |||||||||||||||
| 2004 | "C:\Users\admin\AppData\Local\Temp\ACESETUP.EXE" | C:\Users\admin\AppData\Local\Temp\ACESETUP.EXE | explorer.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation http://www.indigorose.com Integrity Level: HIGH Description: Setup Factory 4.0 SE setup launcher Exit code: 0 Version: 4.08 Modules
| |||||||||||||||
| 2712 | C:\Users\admin\AppData\Local\Temp\irsetup.dat | C:\Users\admin\AppData\Local\Temp\irsetup.exe | ACESETUP.EXE | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: HIGH Description: Setup program generated by Setup Factory 4.0 http://www.indigorose.com Exit code: 0 Version: 4, 0, 0, 8 Modules
| |||||||||||||||
Total events
167
Read events
156
Write events
11
Delete events
0
Modification events
| (PID) Process: | (2712) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\VB40032.DLL |
Value: 1 | |||
| (PID) Process: | (2712) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\ven2232.olb |
Value: 2 | |||
| (PID) Process: | (2712) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\olepro32.dll |
Value: 1 | |||
| (PID) Process: | (2712) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\msvcrt20.dll |
Value: 1 | |||
| (PID) Process: | (2712) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\msvcrt40.dll |
Value: 1 | |||
| (PID) Process: | (2712) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\CTL3D32.DLL |
Value: 1 | |||
| (PID) Process: | (2712) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\oleaut32.dll |
Value: 1 | |||
| (PID) Process: | (2712) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\msvcrt.dll |
Value: 1 | |||
| (PID) Process: | (2712) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RCTACCESS |
| Operation: | write | Name: | DisplayName |
Value: RCT acCeSS | |||
| (PID) Process: | (2712) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RCTACCESS |
| Operation: | write | Name: | UninstallString |
Value: C:\Windows\iun3405.exe C:\Program Files\RCT acCeSS | |||
Executable files
6
Suspicious files
4
Text files
32
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2712 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\WRP4E93.tmp | — | |
MD5:— | SHA256:— | |||
| 2004 | ACESETUP.EXE | C:\Users\admin\AppData\Local\Temp\IRIMG2.BMP | image | |
MD5:079F5D7A99367681DD8E051B6EAF1E30 | SHA256:BAD099728883EA6671E96506B9099F00E35C39C6FF3A6A7AE317234D2416DD88 | |||
| 2004 | ACESETUP.EXE | C:\Users\admin\AppData\Local\Temp\irsetup.dat | binary | |
MD5:D09D72865792DDF2CA7EC9D33DBED86A | SHA256:3EE6CEDB27BCAF51CFB82C3D14CEFF4C38435F968D6FD73C1088EAC47ED1AE01 | |||
| 2004 | ACESETUP.EXE | C:\Users\admin\AppData\Local\Temp\IRIMG7.BMP | image | |
MD5:14C1105C292A3F554A362FD991AF6B52 | SHA256:DDE01EB03C42739E18D90EDF65BC48597CA64DA60038F4C697D69AC32BD3EE90 | |||
| 2004 | ACESETUP.EXE | C:\Users\admin\AppData\Local\Temp\IRIMG5.BMP | image | |
MD5:49B0DACD359614505316A42B181FEE05 | SHA256:AA2839B08314632D680A188216691E2EED49853E61E60040AF21BB8B1EBC6E2F | |||
| 2004 | ACESETUP.EXE | C:\Users\admin\AppData\Local\Temp\irsetup.avi | avi | |
MD5:34B5BC08ACDA9850686B42C869E631A3 | SHA256:C49C3293383D2777BEEDF2265F01D87E9C122328681065E9EB2F9C1D5A75CCCE | |||
| 2004 | ACESETUP.EXE | C:\Users\admin\AppData\Local\Temp\irsetup.ini | text | |
MD5:982DFACF4AC545F0FF9B6B23ED29CDD4 | SHA256:15BB4513C09E1341891672F2A3AA85B2AF9621B58DA1908DA35D07CE454F0DC1 | |||
| 2004 | ACESETUP.EXE | C:\Users\admin\AppData\Local\Temp\IRIMG4.BMP | image | |
MD5:63A8671CC4332E74F509584D87E5EE95 | SHA256:D393F2FA0E1C765A06AF67BEF800400F12B30B3BD4CFE1CC3CAC6E16CA9F6856 | |||
| 2004 | ACESETUP.EXE | C:\Users\admin\AppData\Local\Temp\IRIMG1.BMP | image | |
MD5:969D3D92AEFF094958701AB2199D1E2B | SHA256:4821E581D9579E3C2CE15DAF582C5105642437EEE52AE33A75A437377D6E51FD | |||
| 2004 | ACESETUP.EXE | C:\Users\admin\AppData\Local\Temp\IRIMG6.BMP | image | |
MD5:5835AD11EE8E02633D12529BDFF4F078 | SHA256:EE1FFC8EDC042A1328D6370A0003BCB2473855FC8A56C3315D058B3522A2C8AE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report