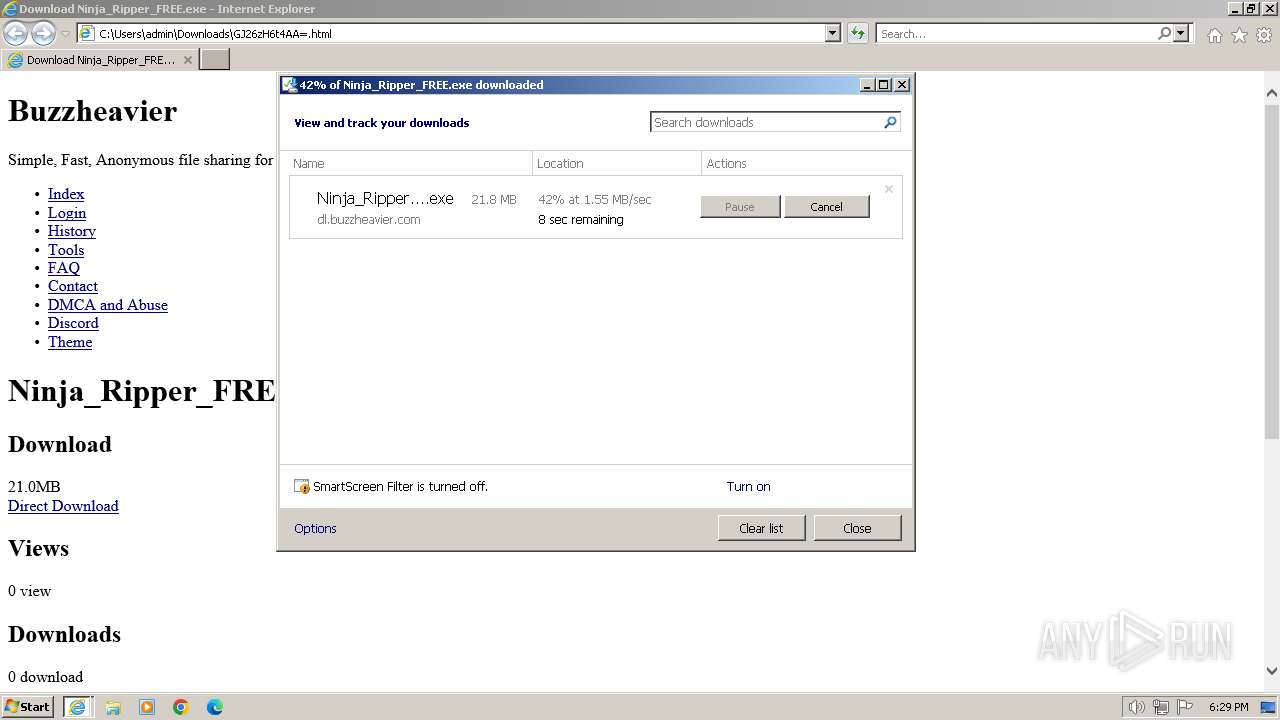
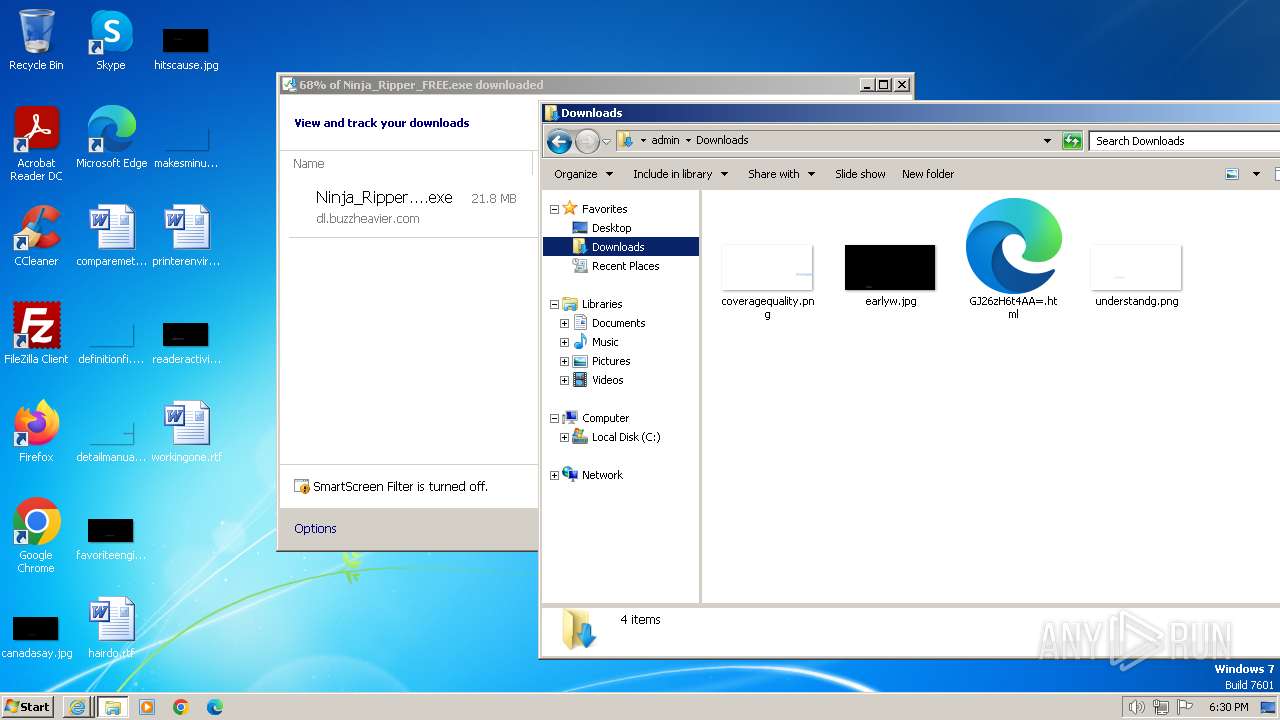
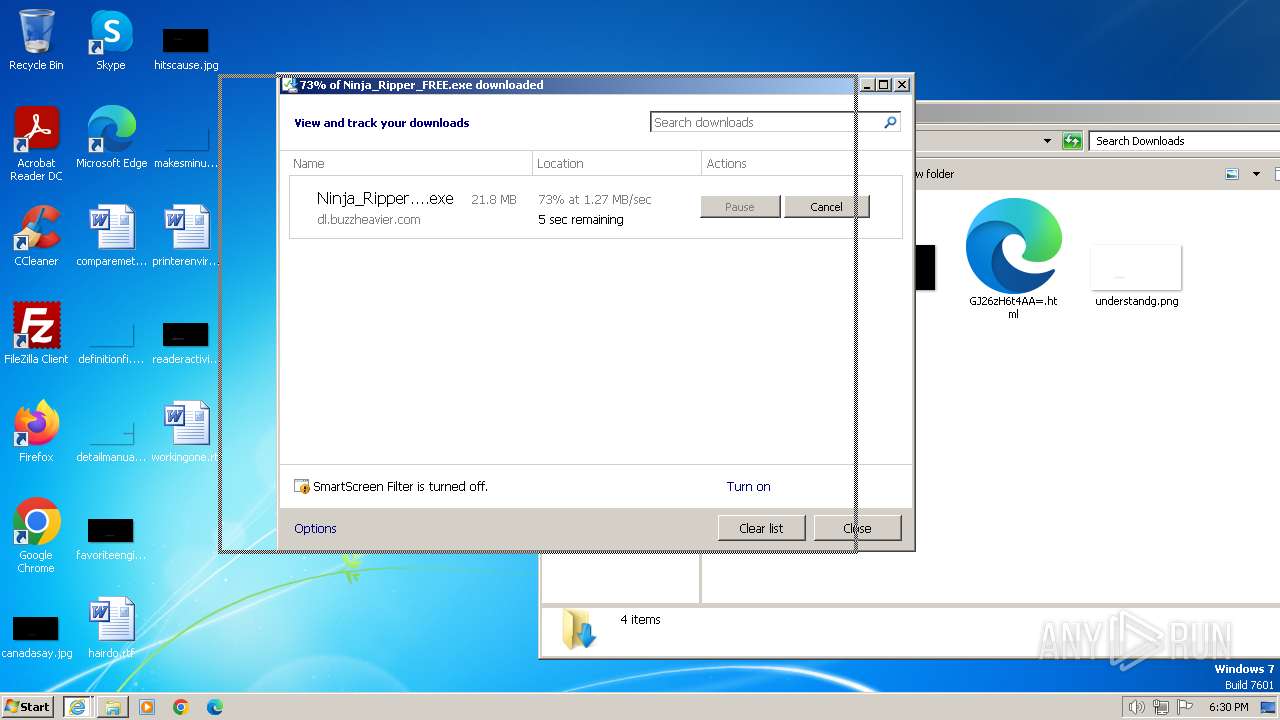
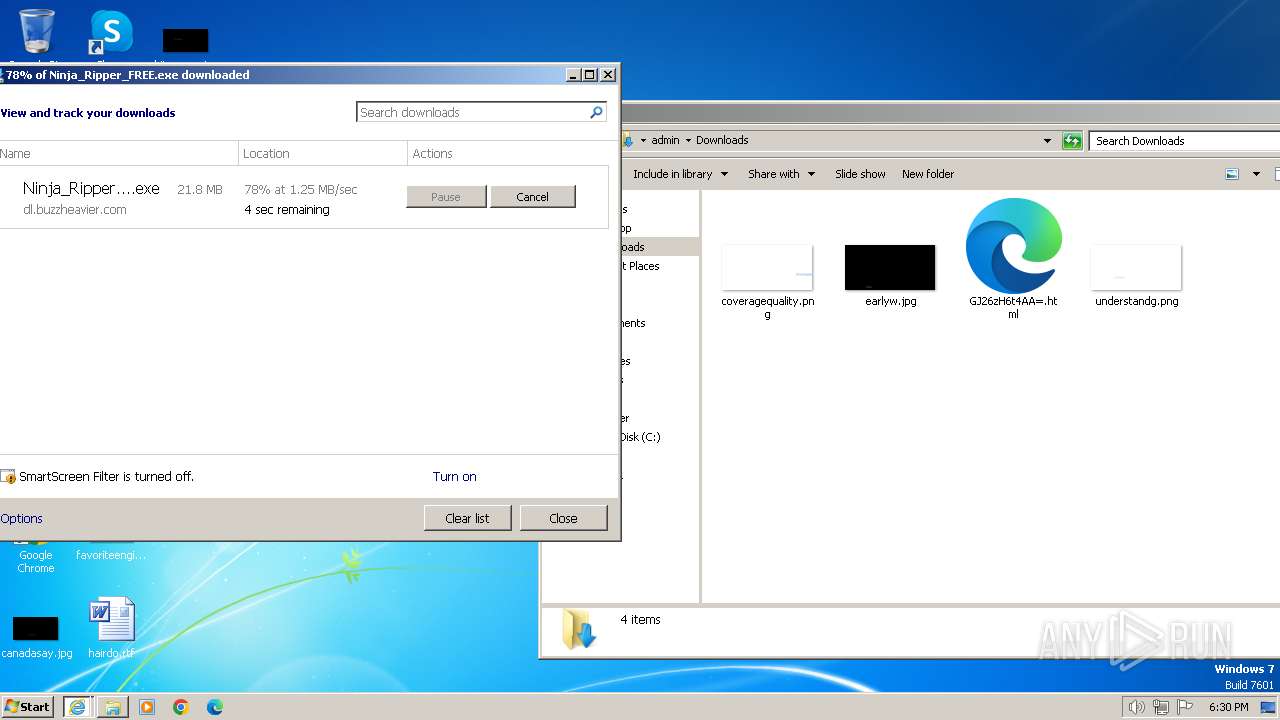
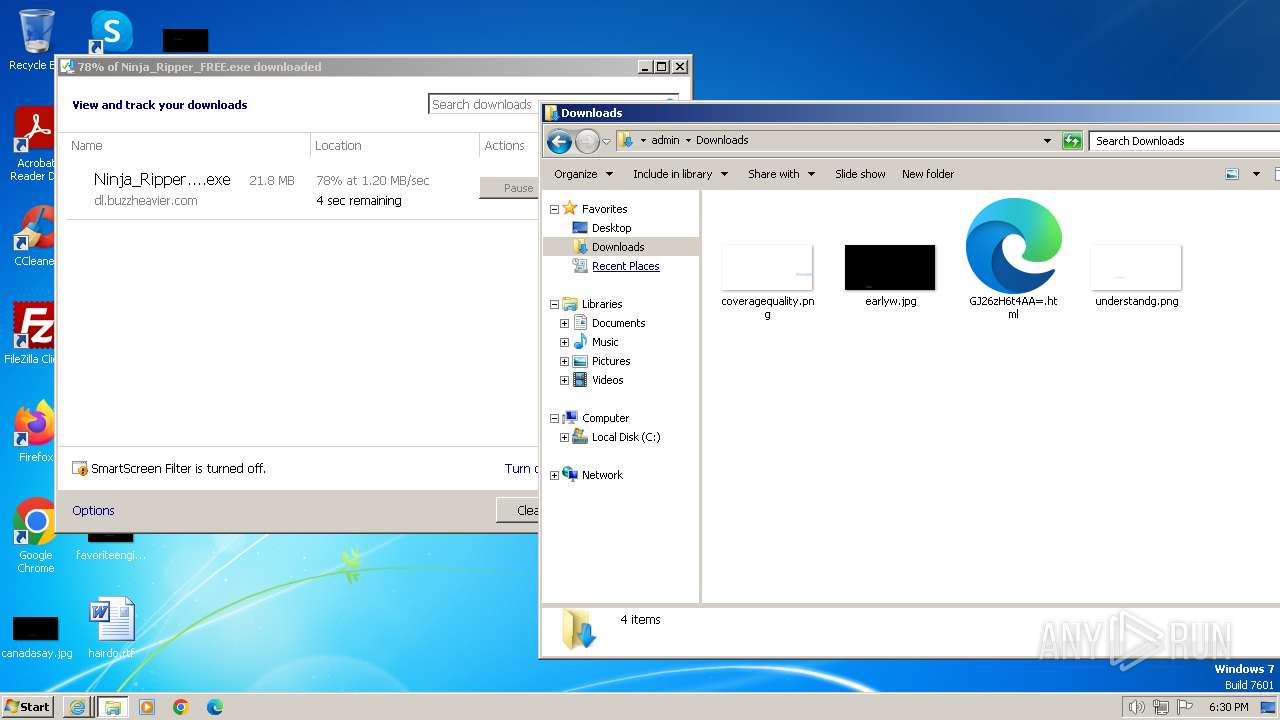
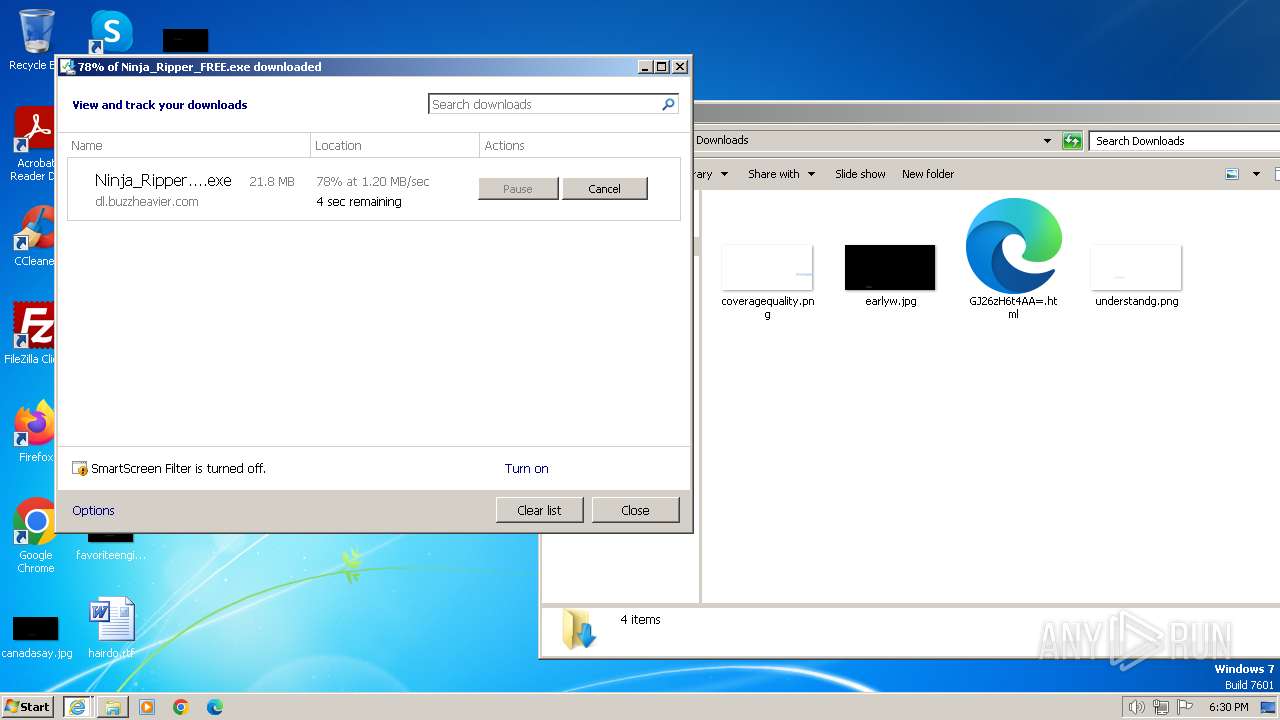
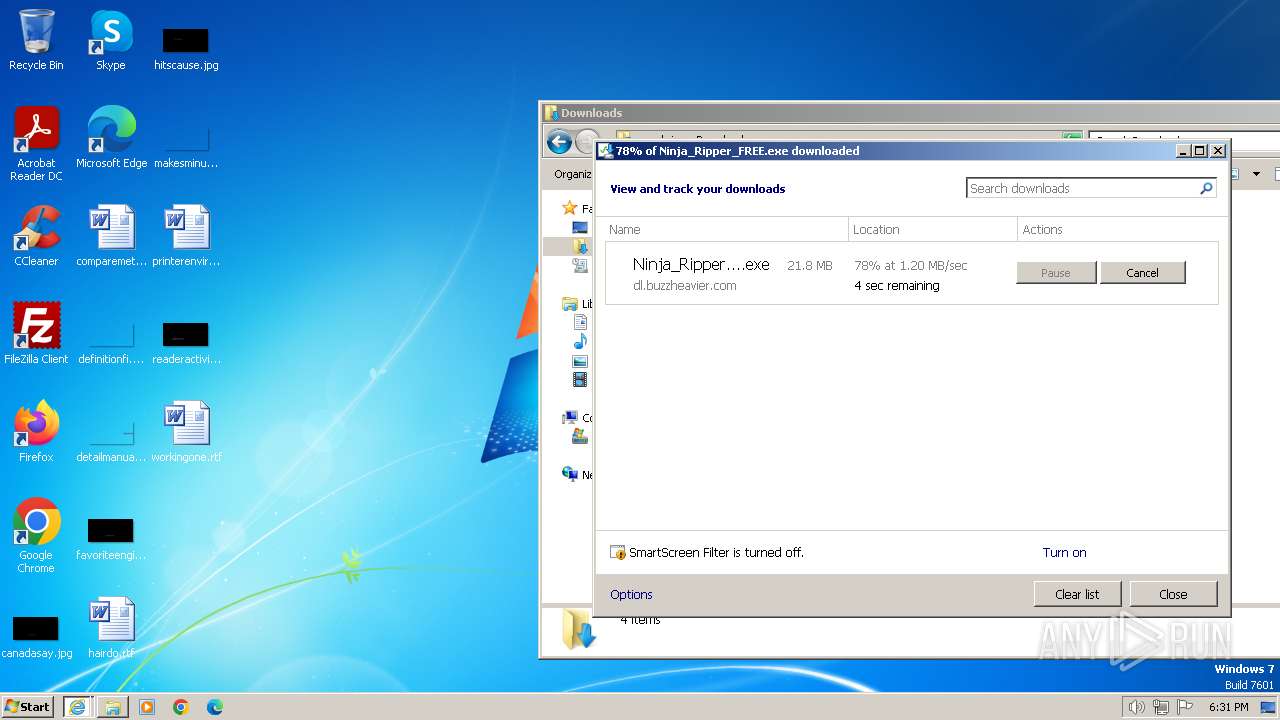
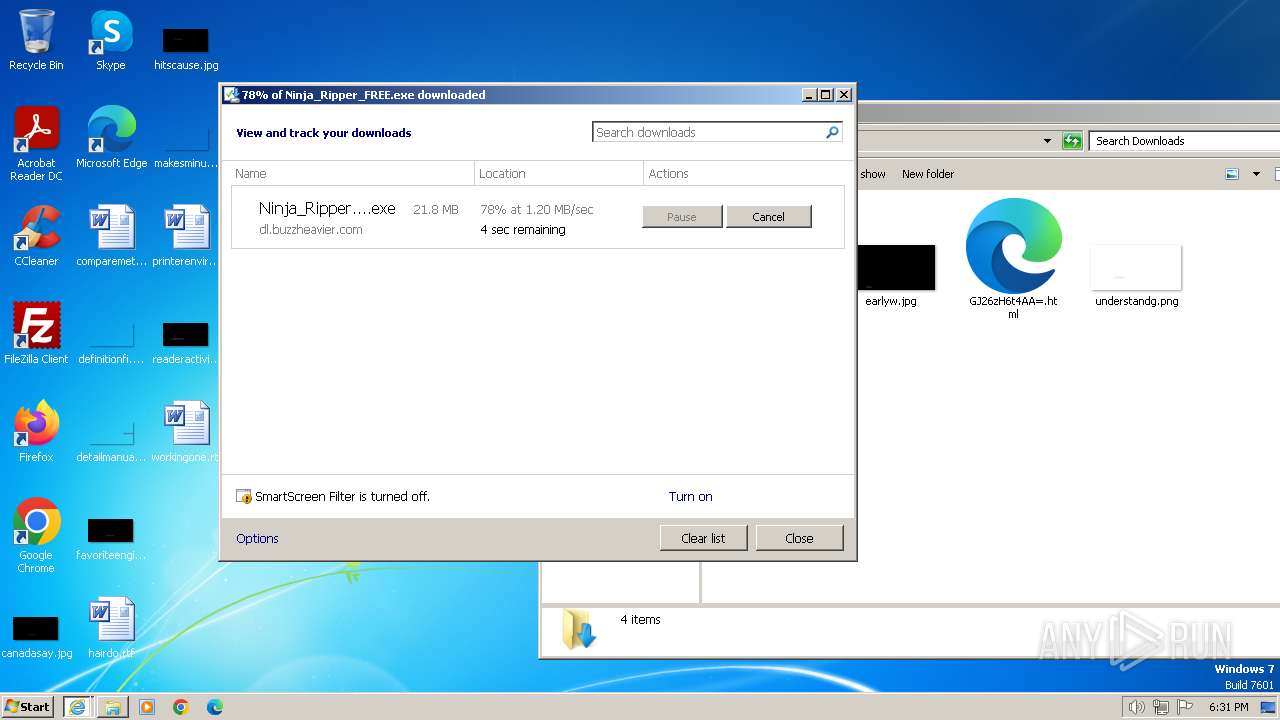
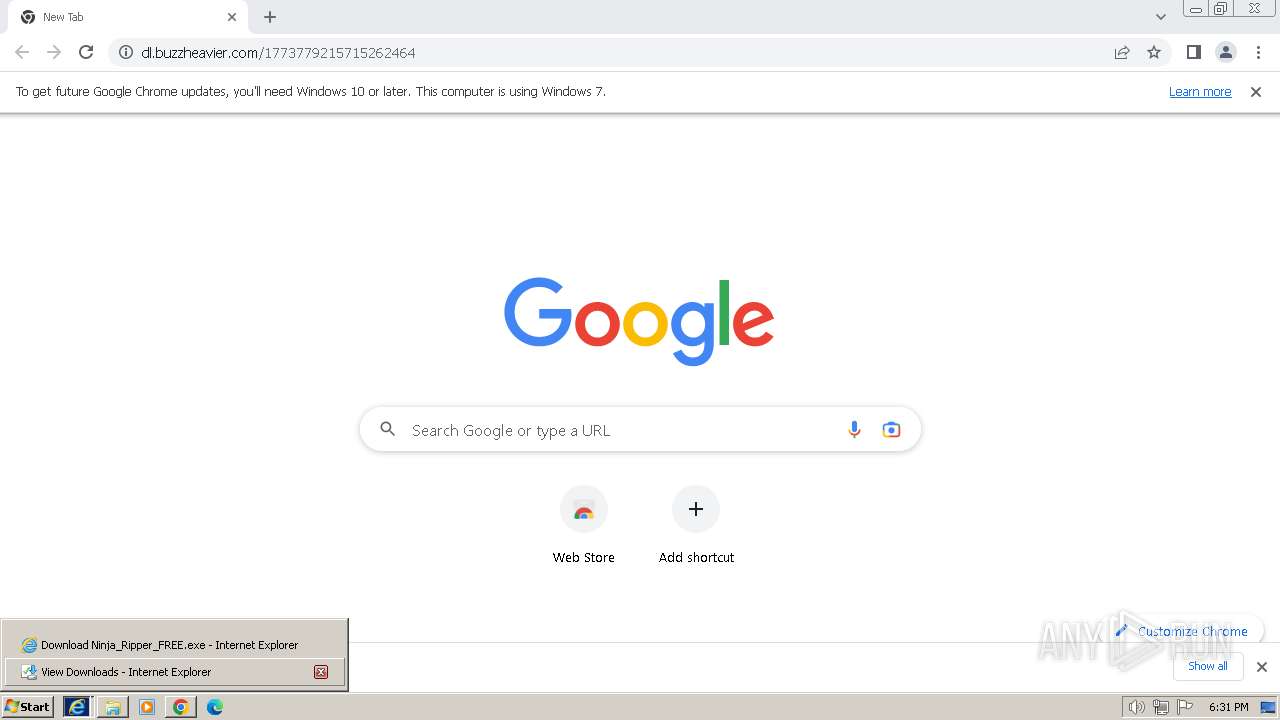
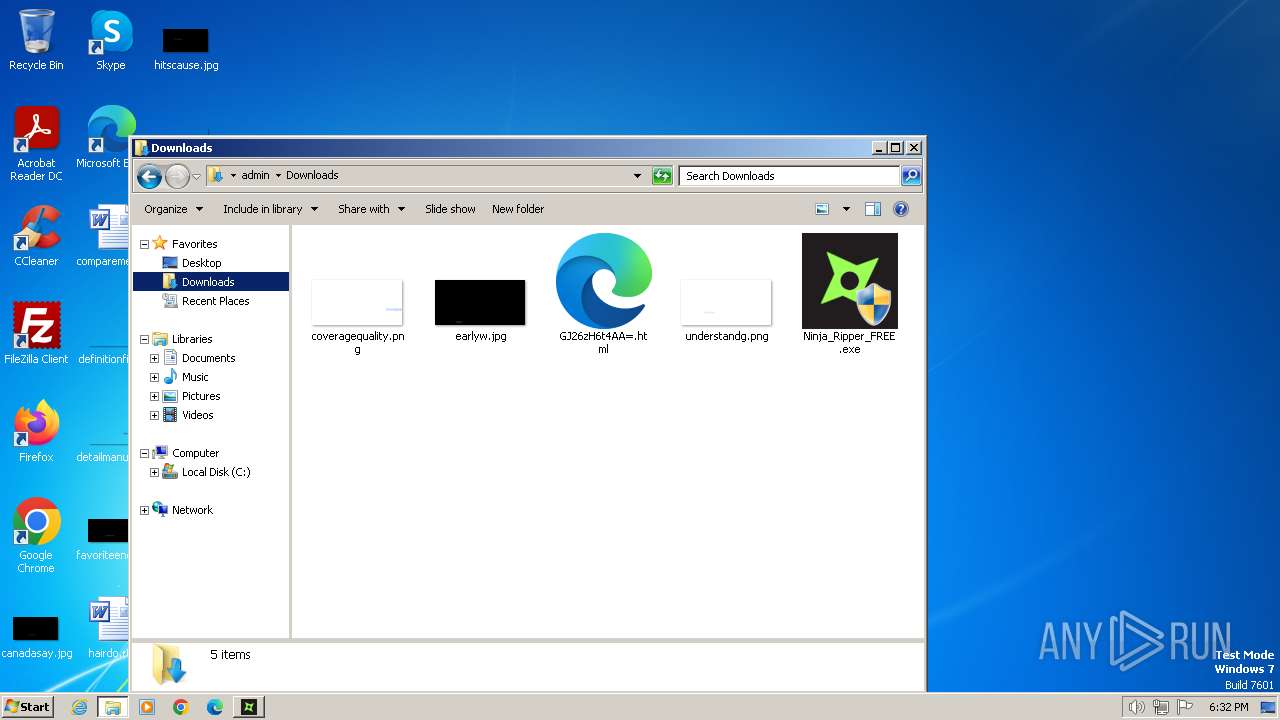
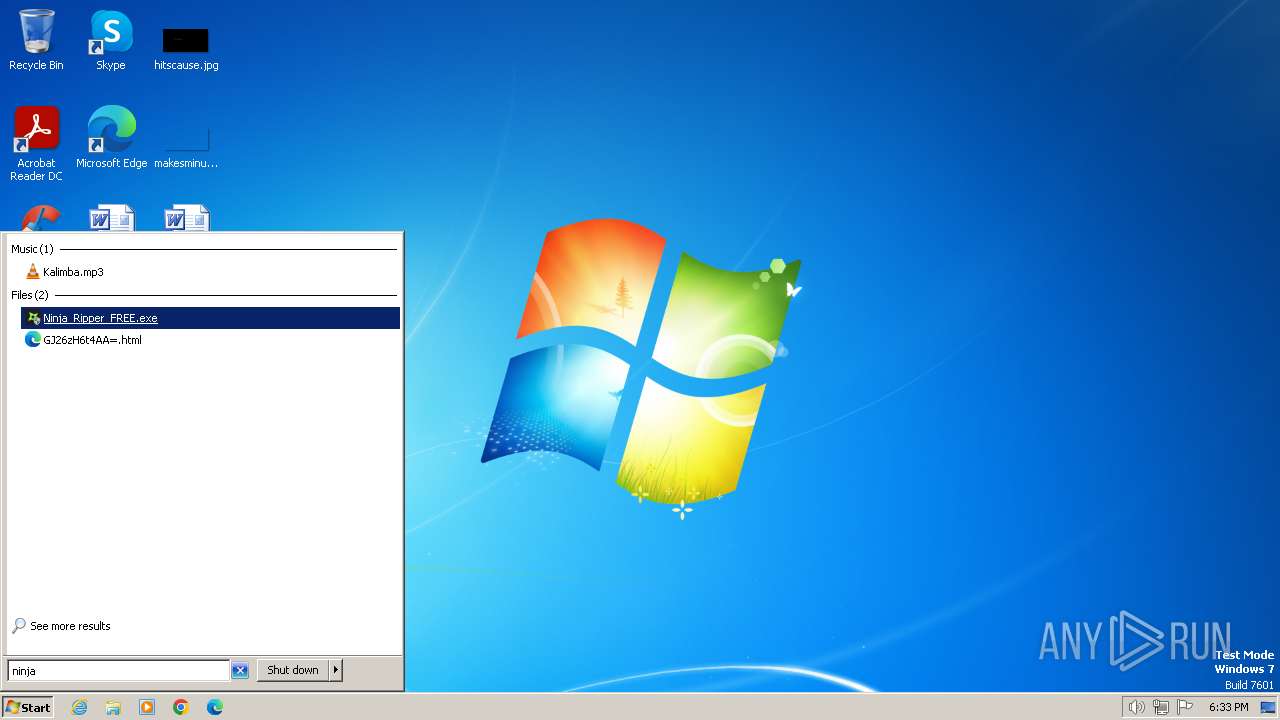
| download: | /f/GJ26zH6t4AA= |
| Full analysis: | https://app.any.run/tasks/fd82689e-3878-4355-b7f2-b8f12b04333b |
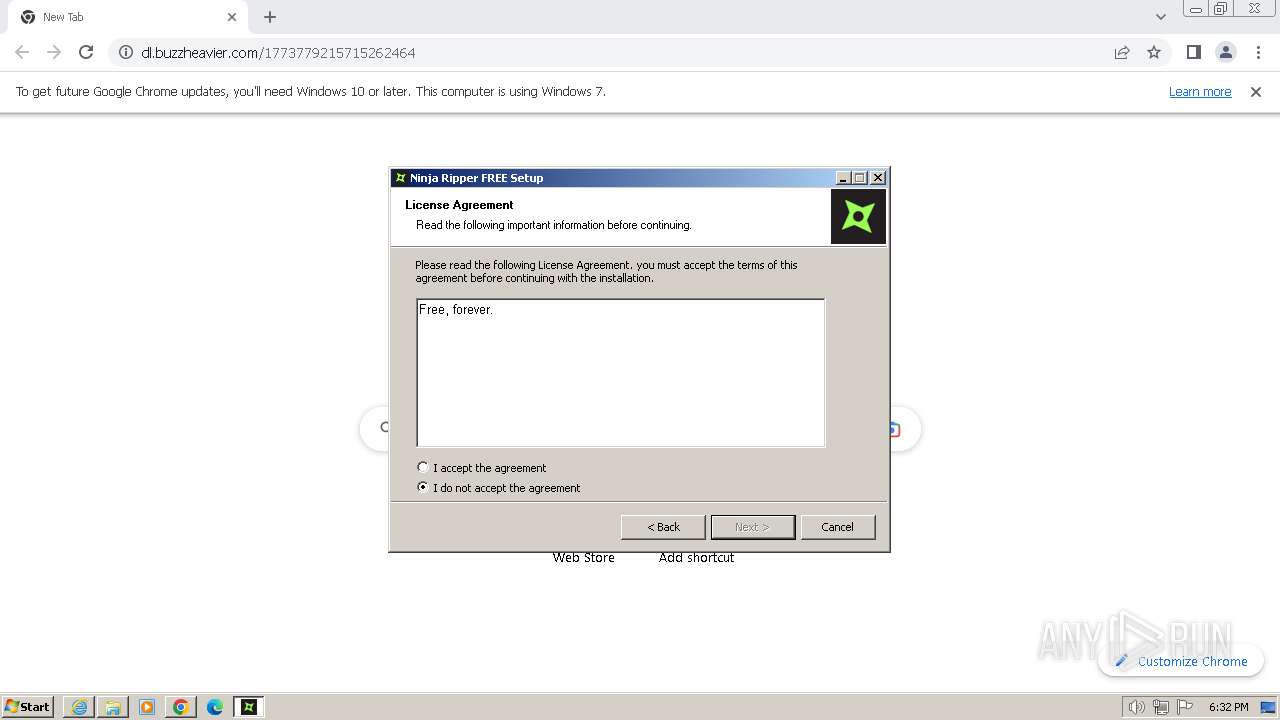
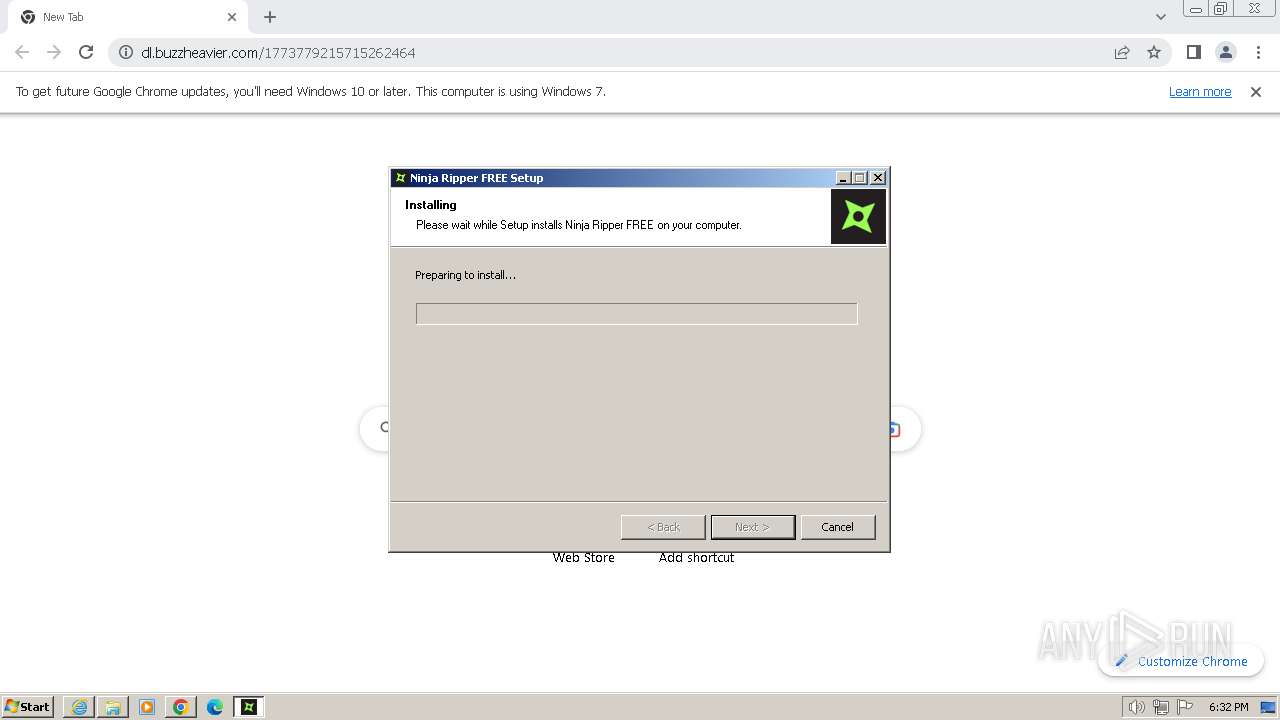
| Verdict: | Malicious activity |
| Analysis date: | March 29, 2024, 18:29:28 |
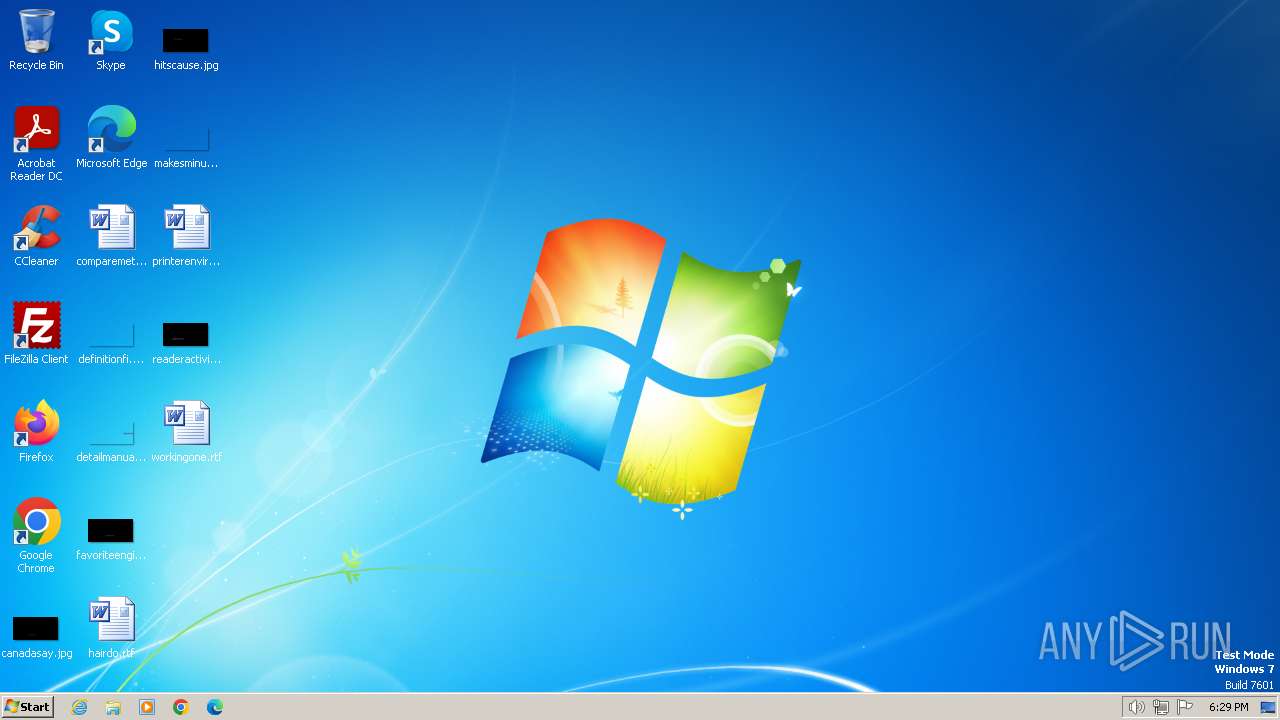
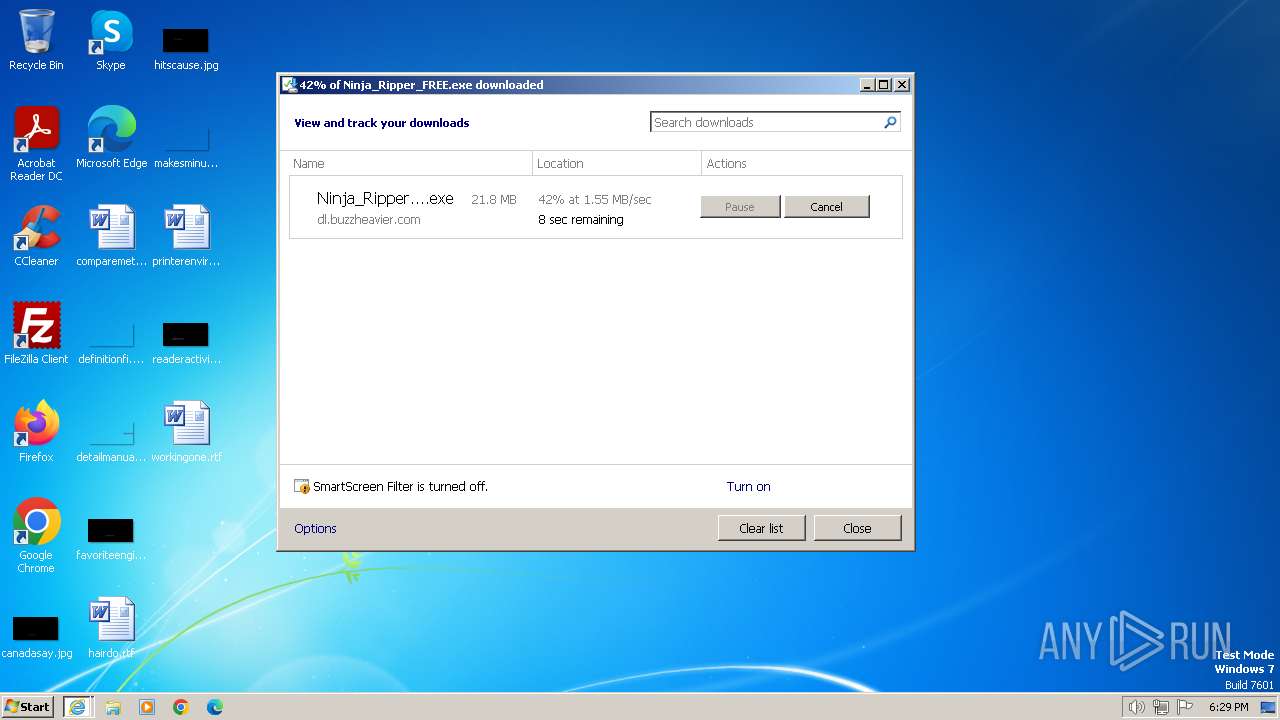
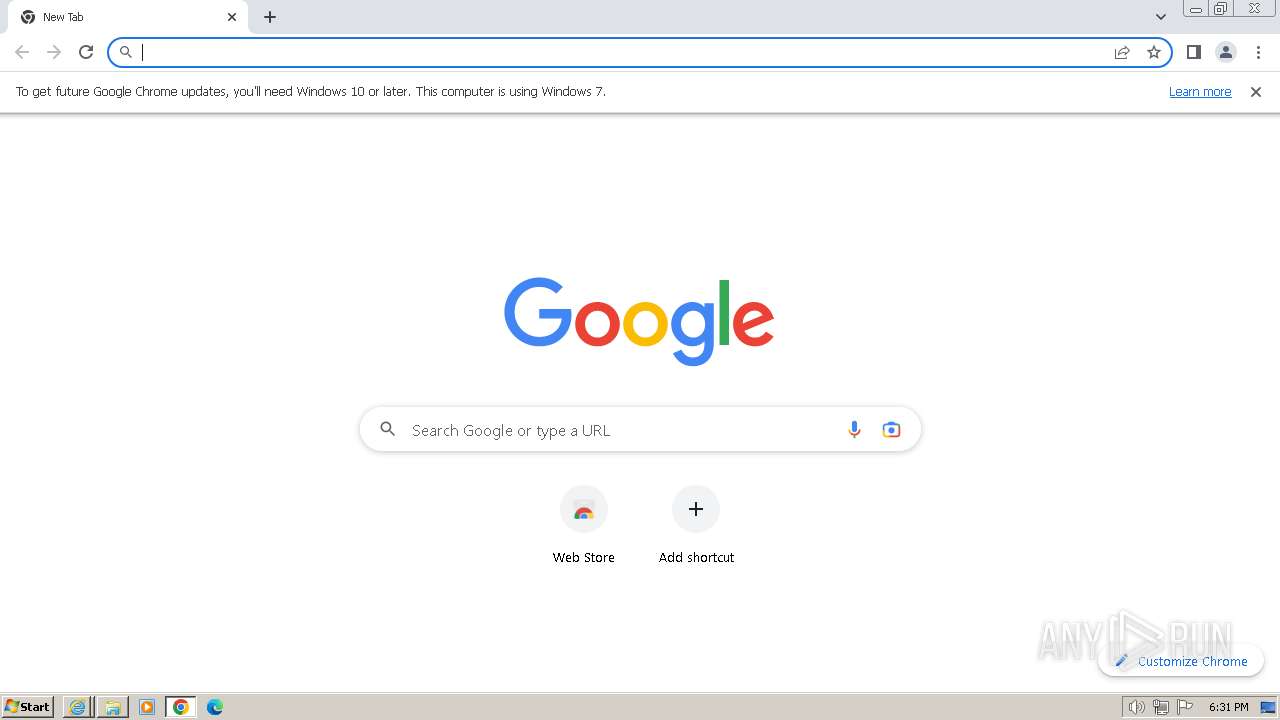
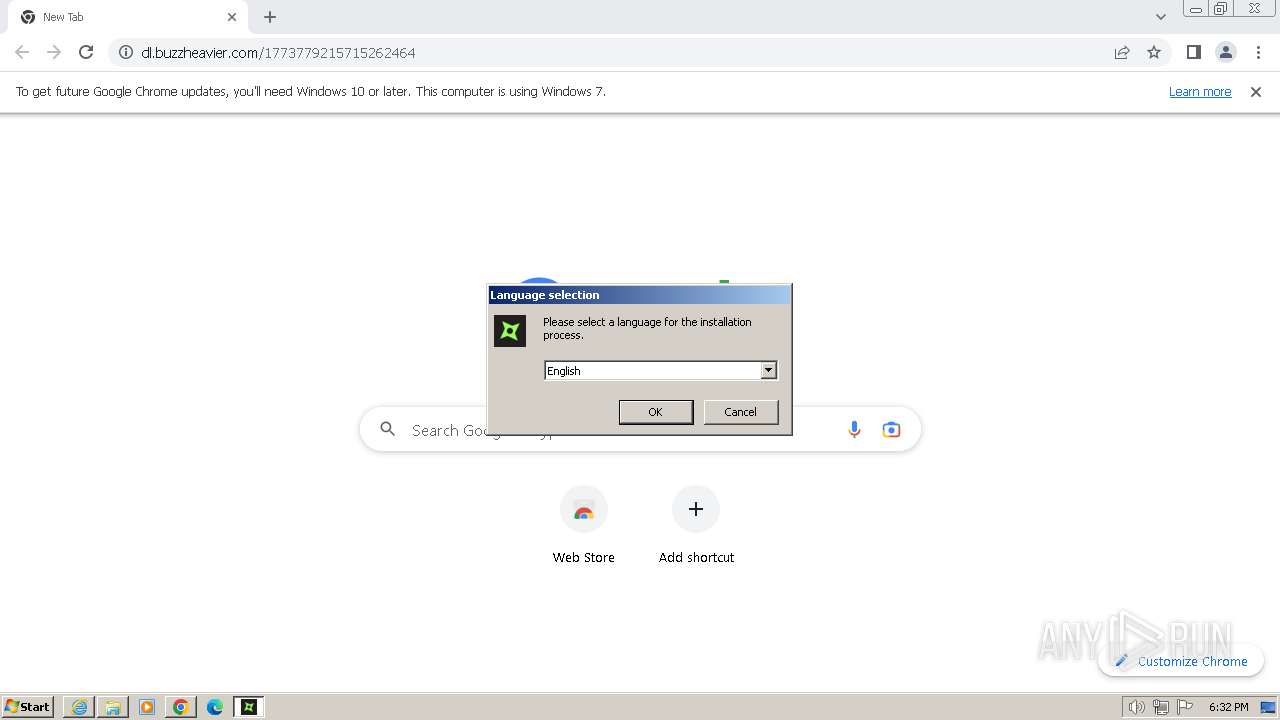
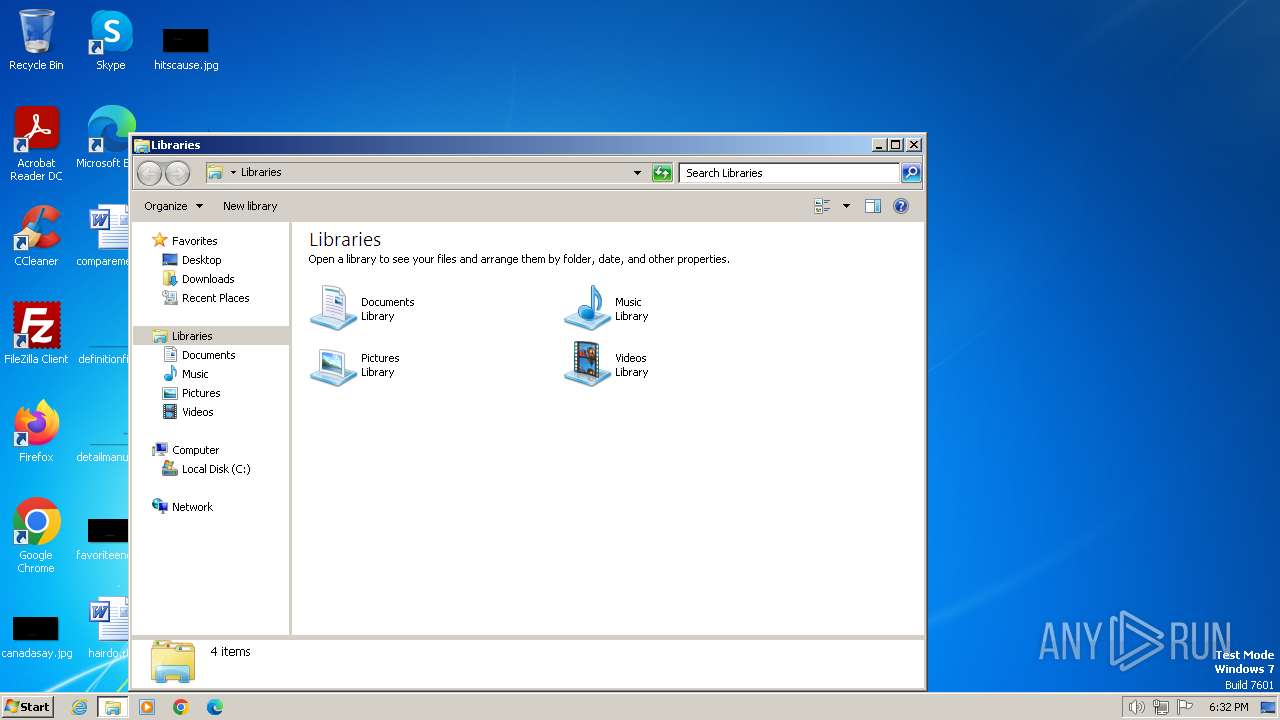
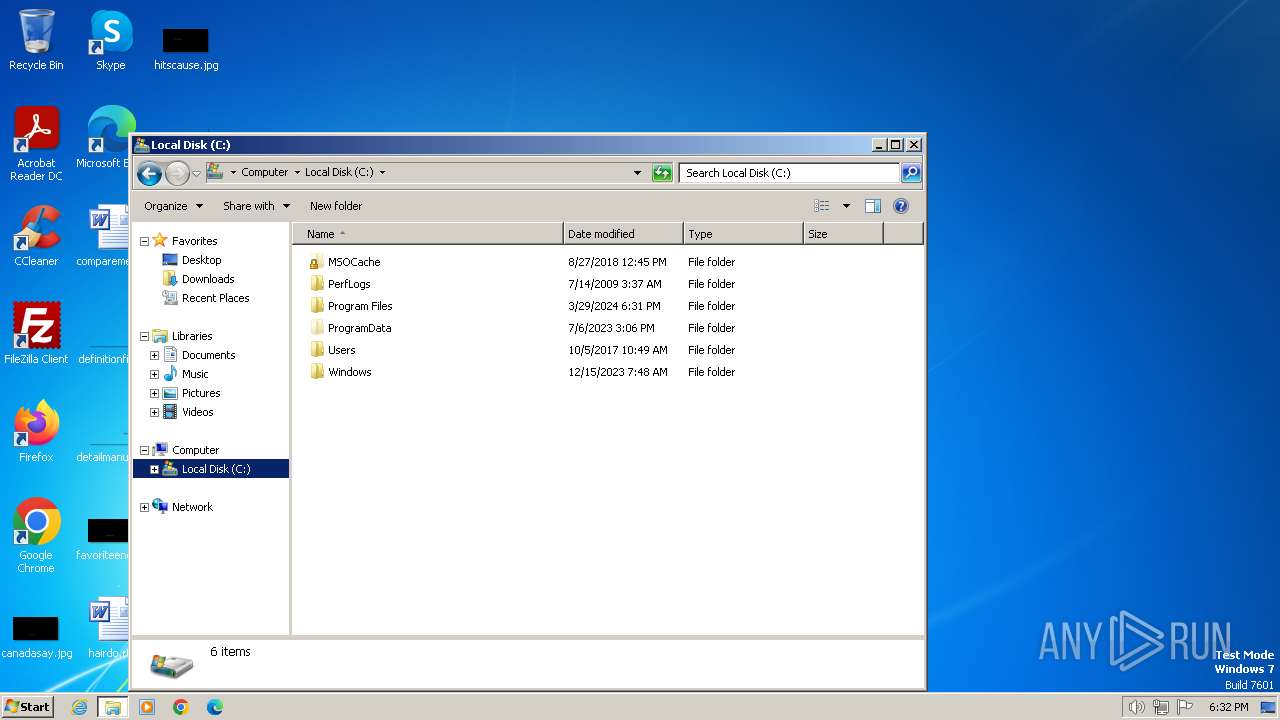
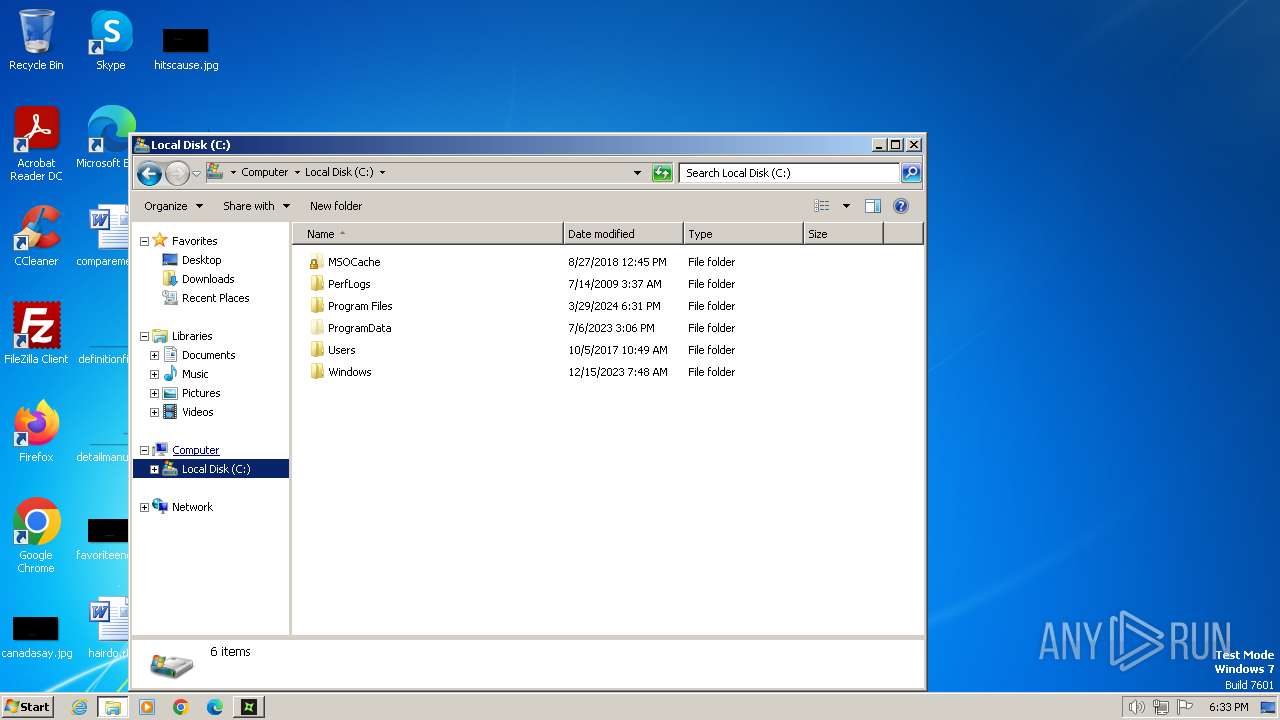
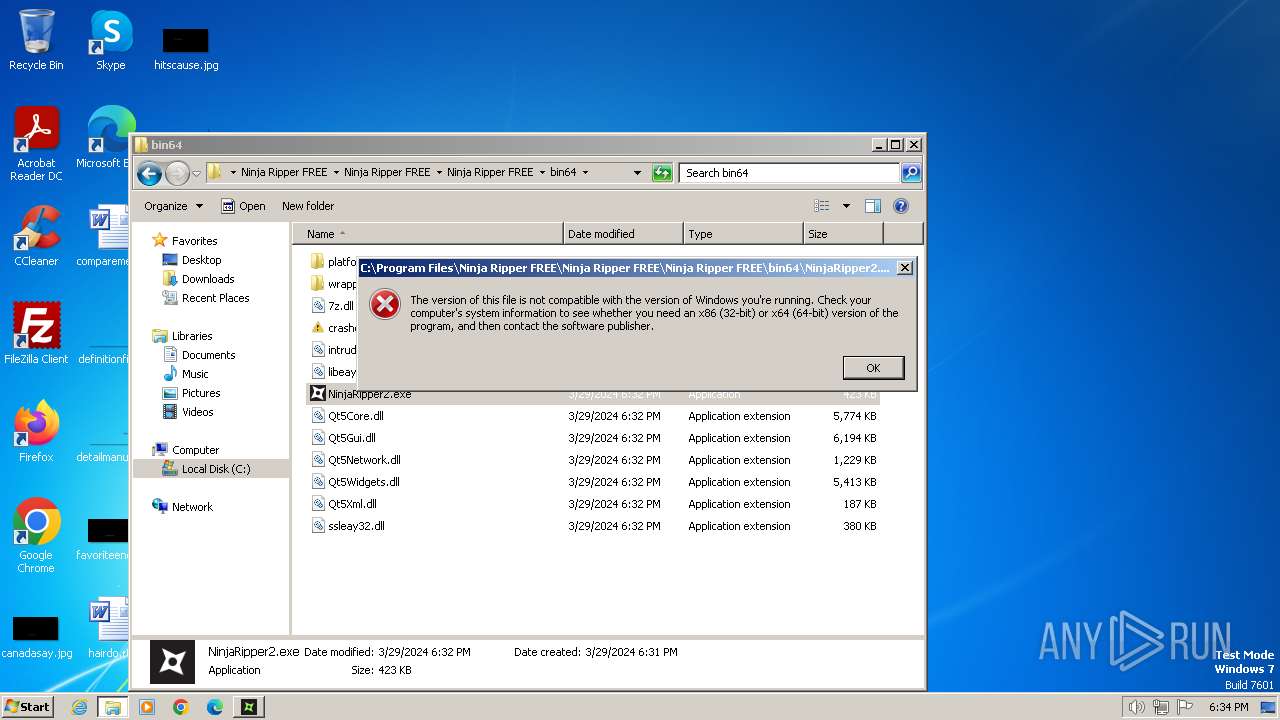
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines (1728) |
| MD5: | AEBB0C7CBCEDE037D056F6AFA634256A |
| SHA1: | 9243222FB281056932F62EEE547B16BDCA8594CA |
| SHA256: | 1510396739138CF20192FF4DE006C60378C04080E4DD70ECE32E408740CEDD52 |
| SSDEEP: | 192:Q9VqkFykndLMmCnWJ31ZOh1Ga8MU/R/eq71himFiji5X+pr:GTLMmCWJlZ21GxMSniiijiN+9 |
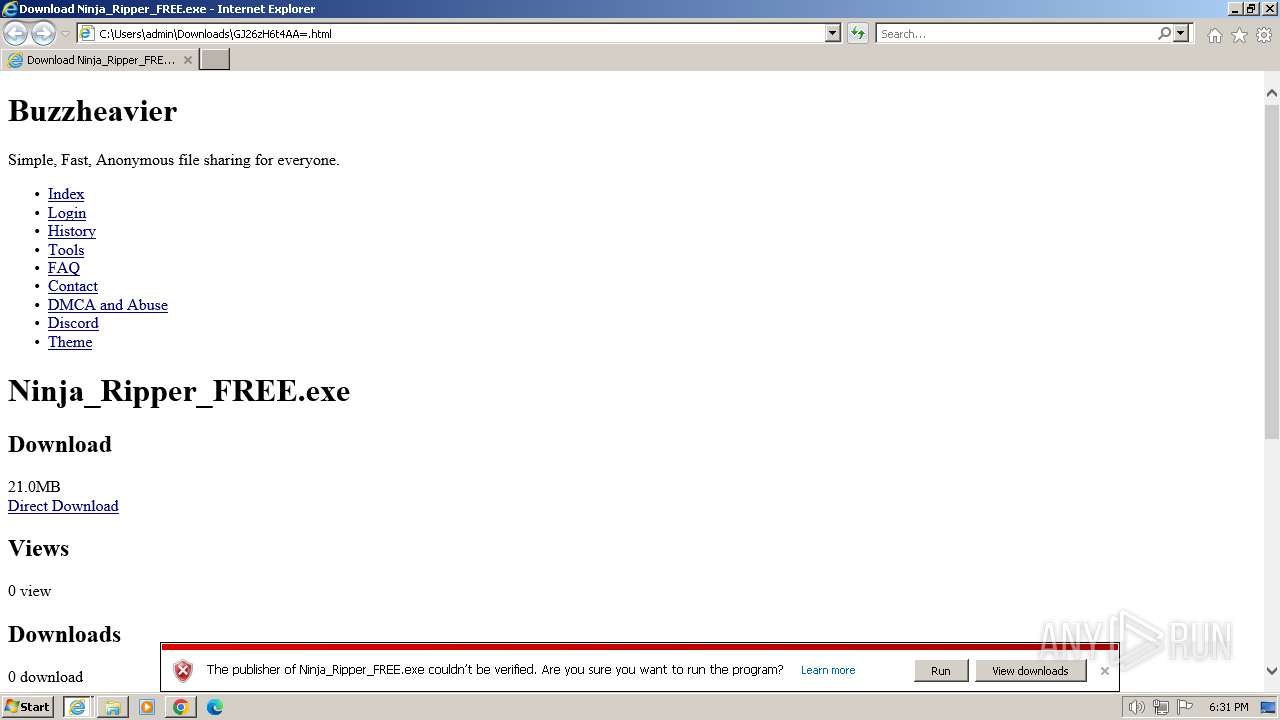
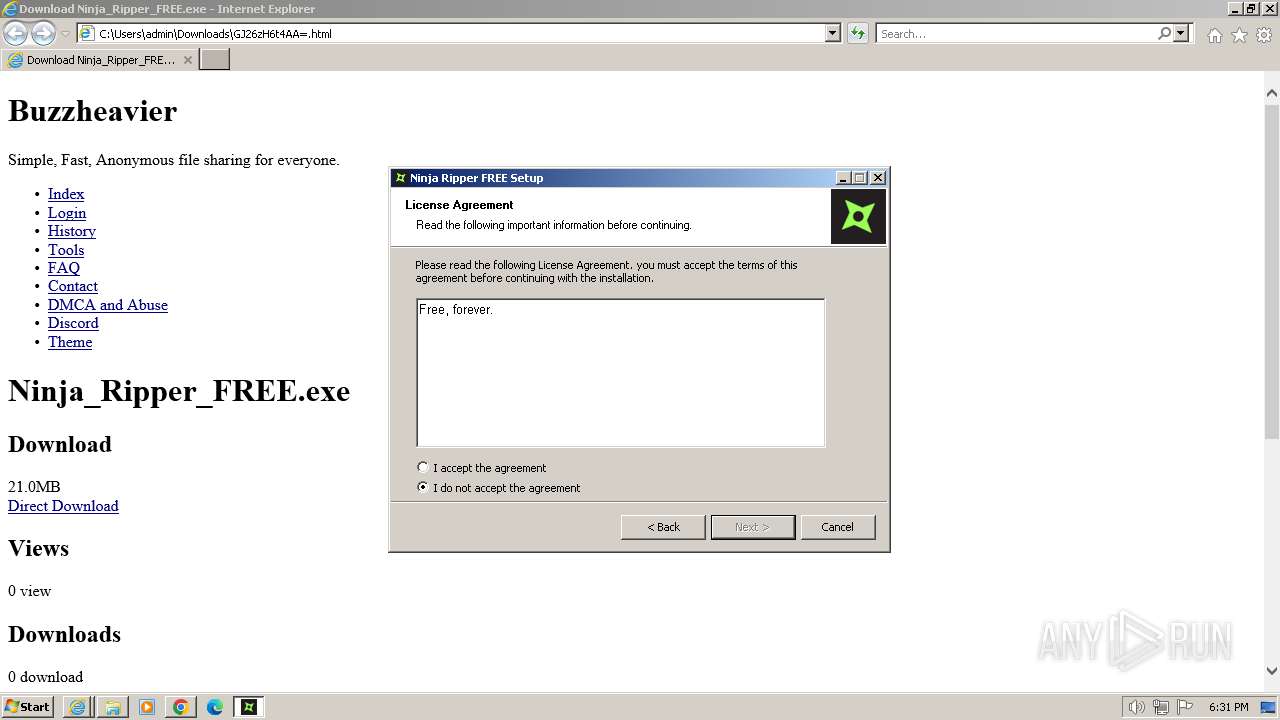
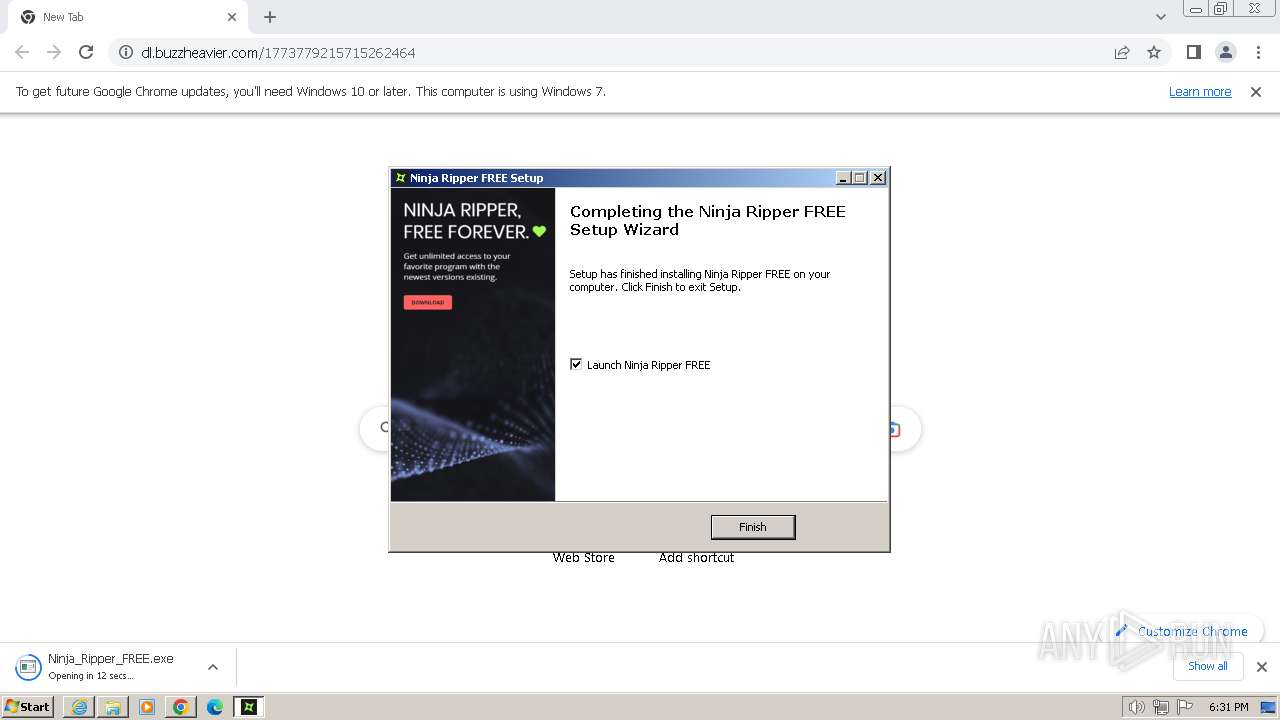
MALICIOUS
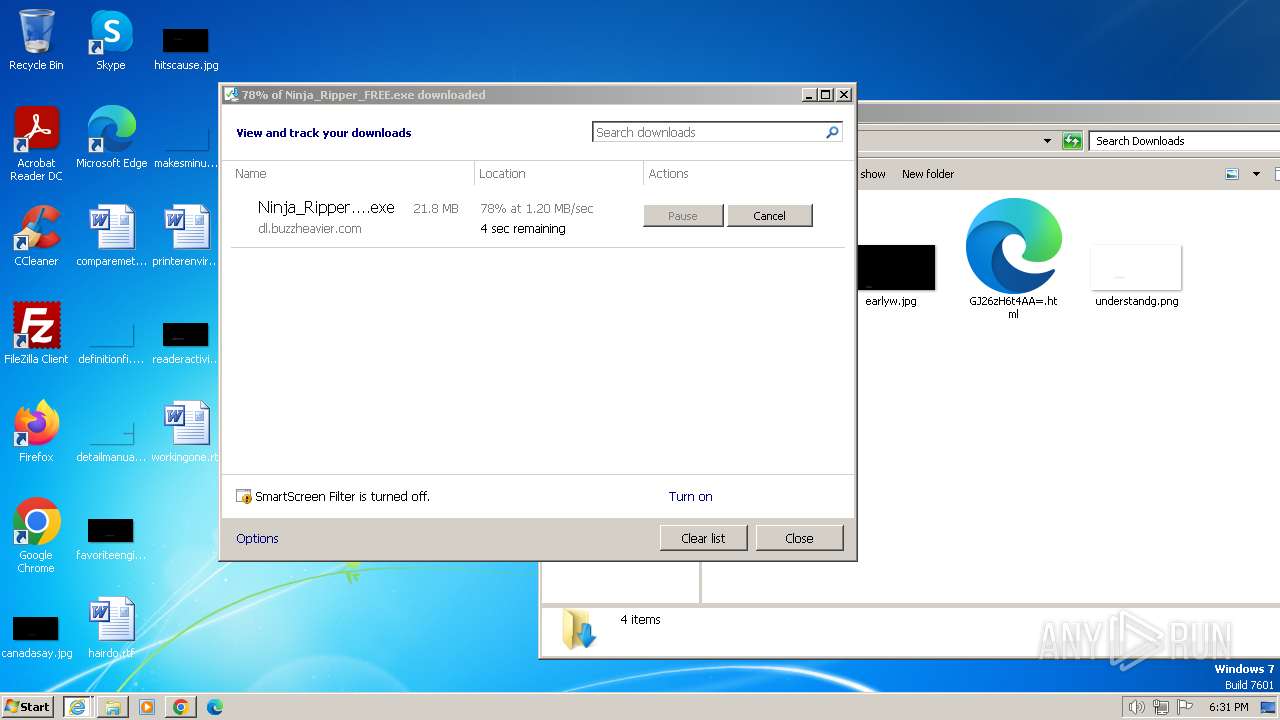
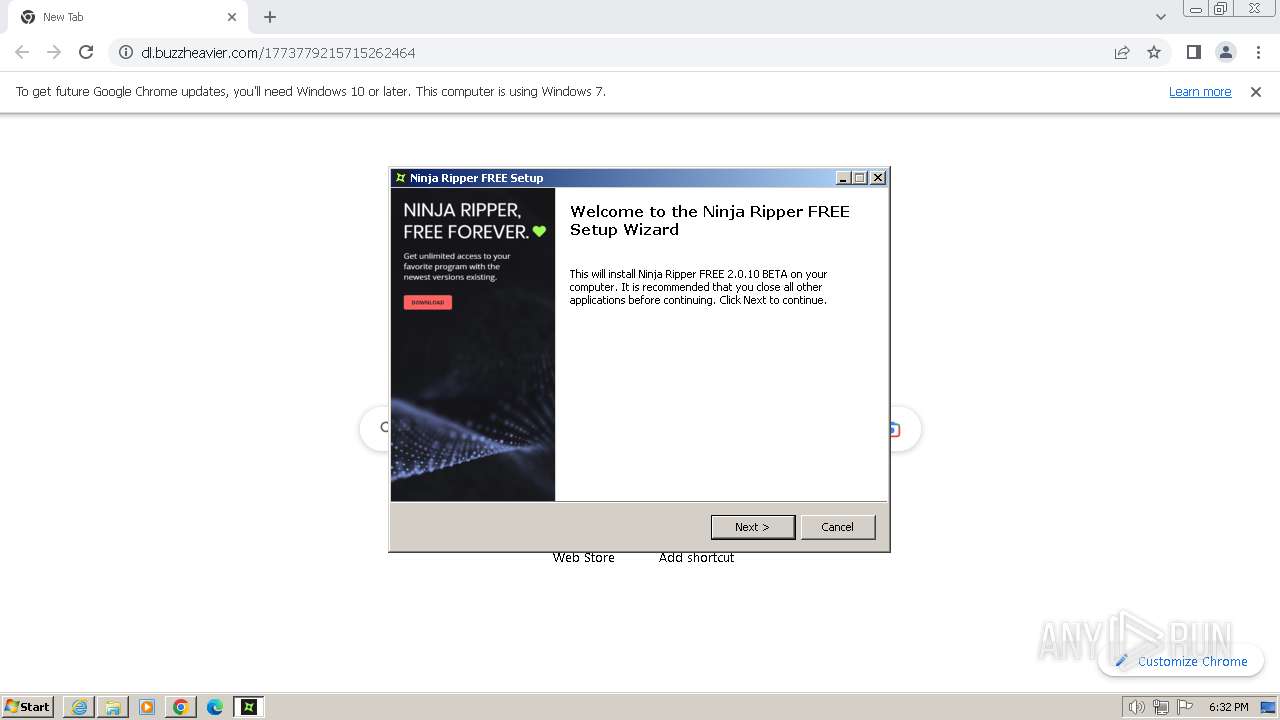
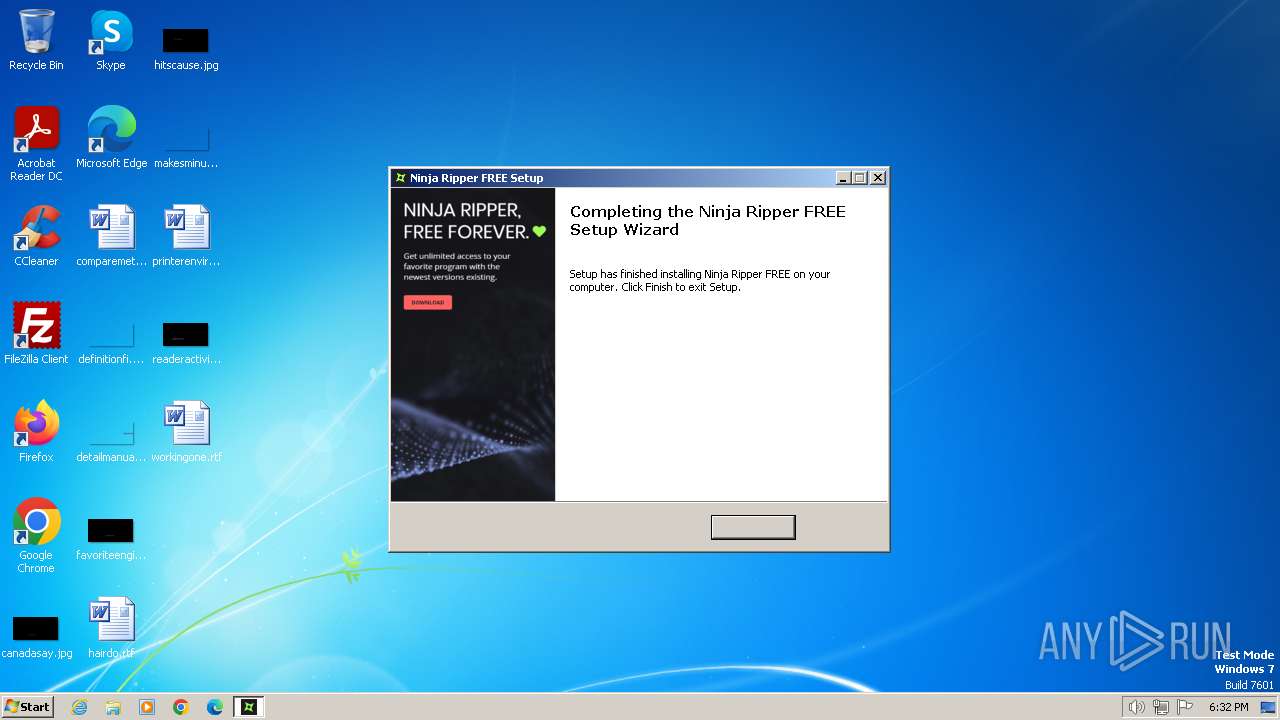
Drops the executable file immediately after the start
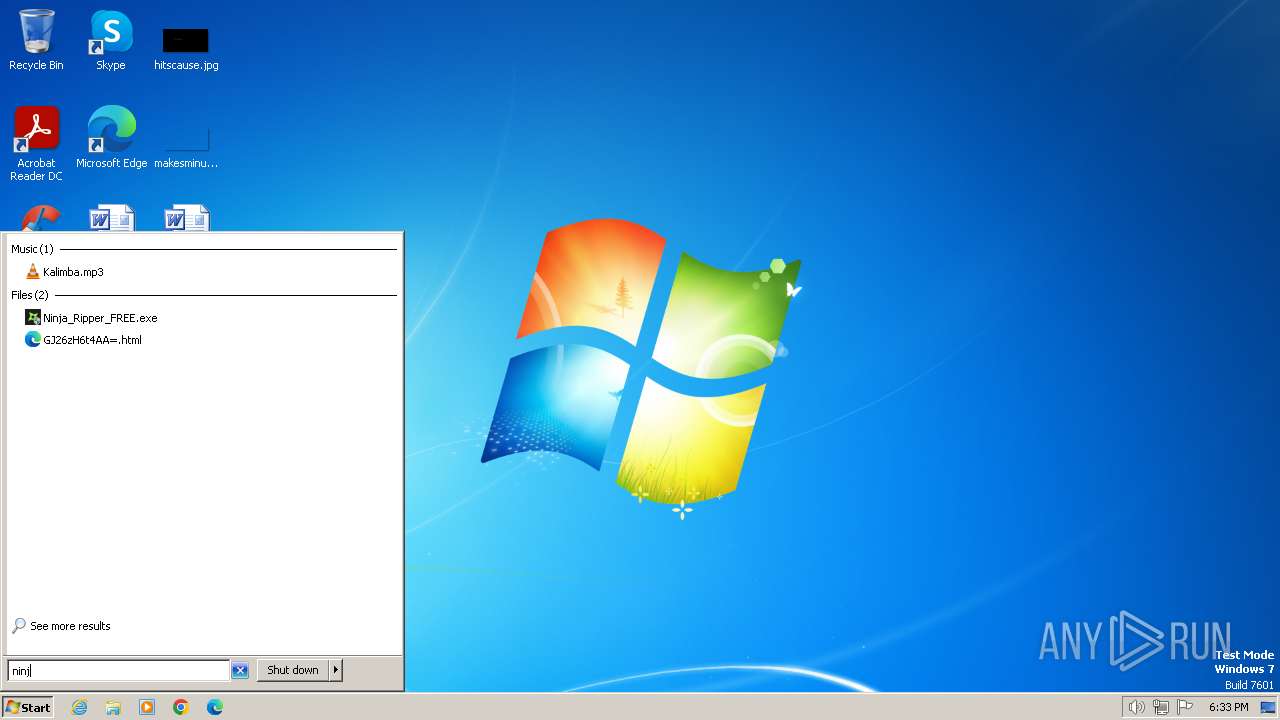
- Ninja_Ripper_FREE.exe (PID: 2864)
SUSPICIOUS
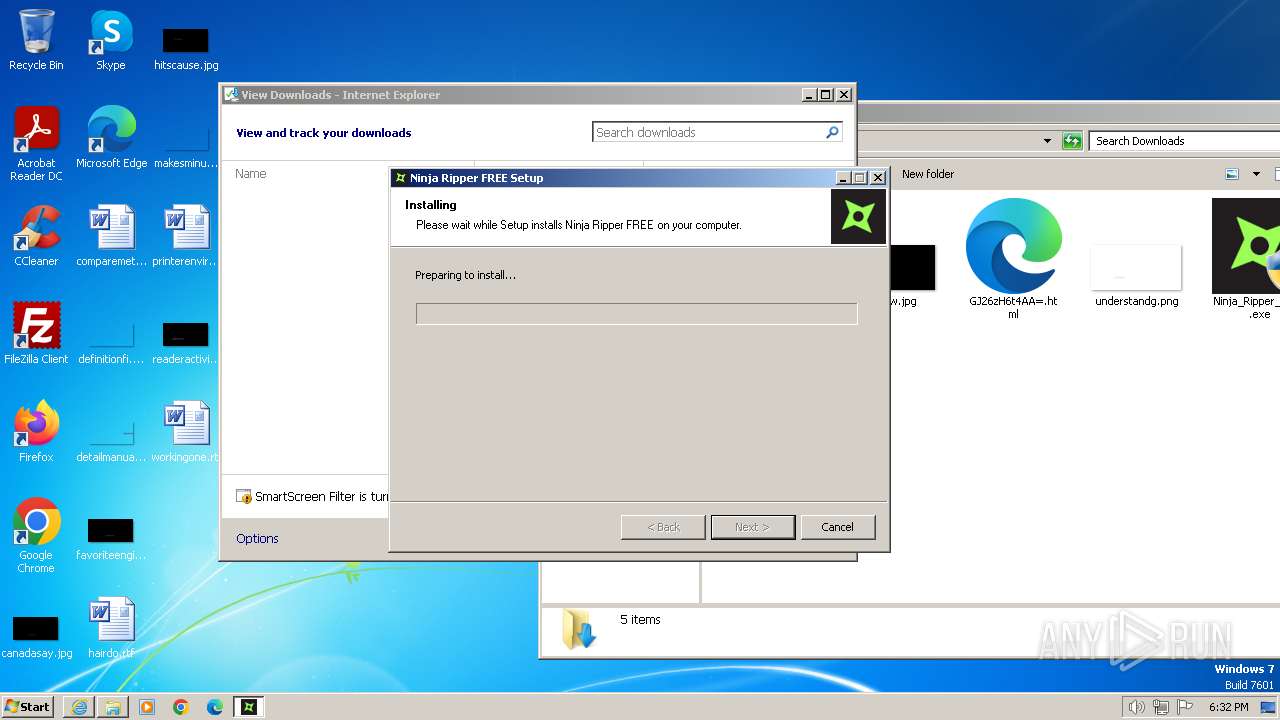
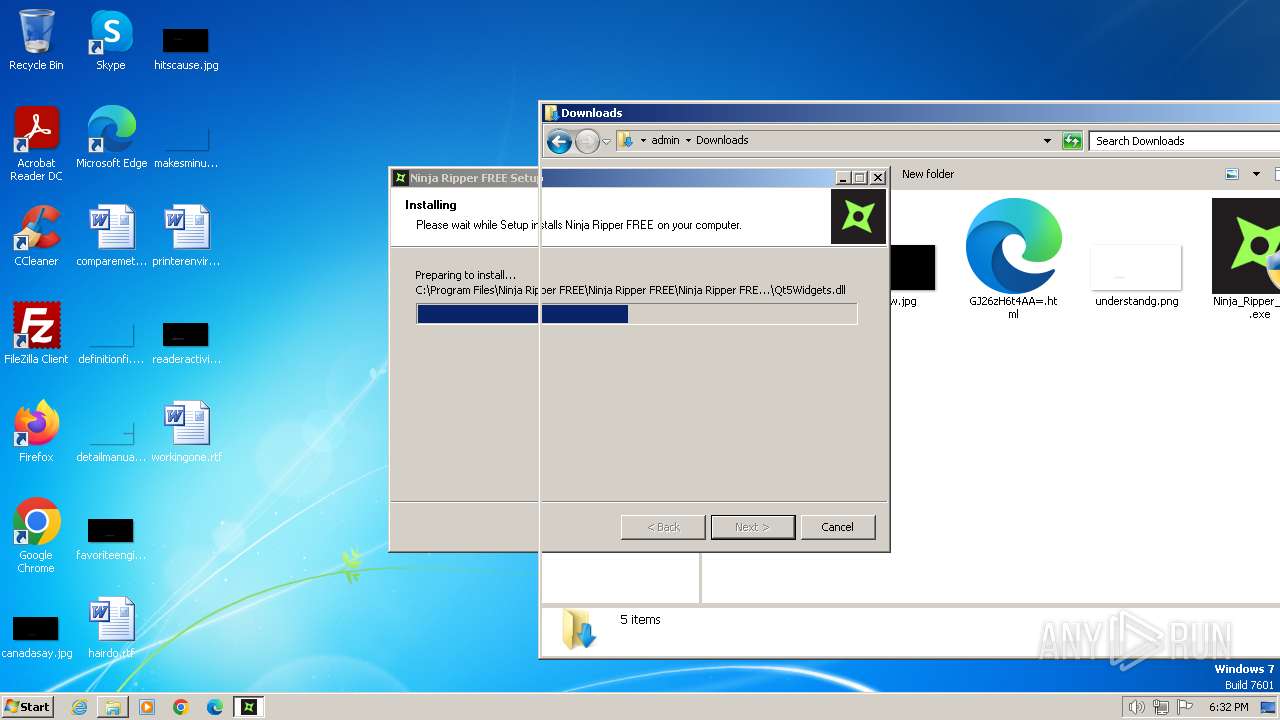
Drops 7-zip archiver for unpacking
- Ninja_Ripper_FREE.exe (PID: 2864)
Reads security settings of Internet Explorer
- Ninja_Ripper_FREE.exe (PID: 2864)
- Ninja_Ripper_FREE.exe (PID: 1056)
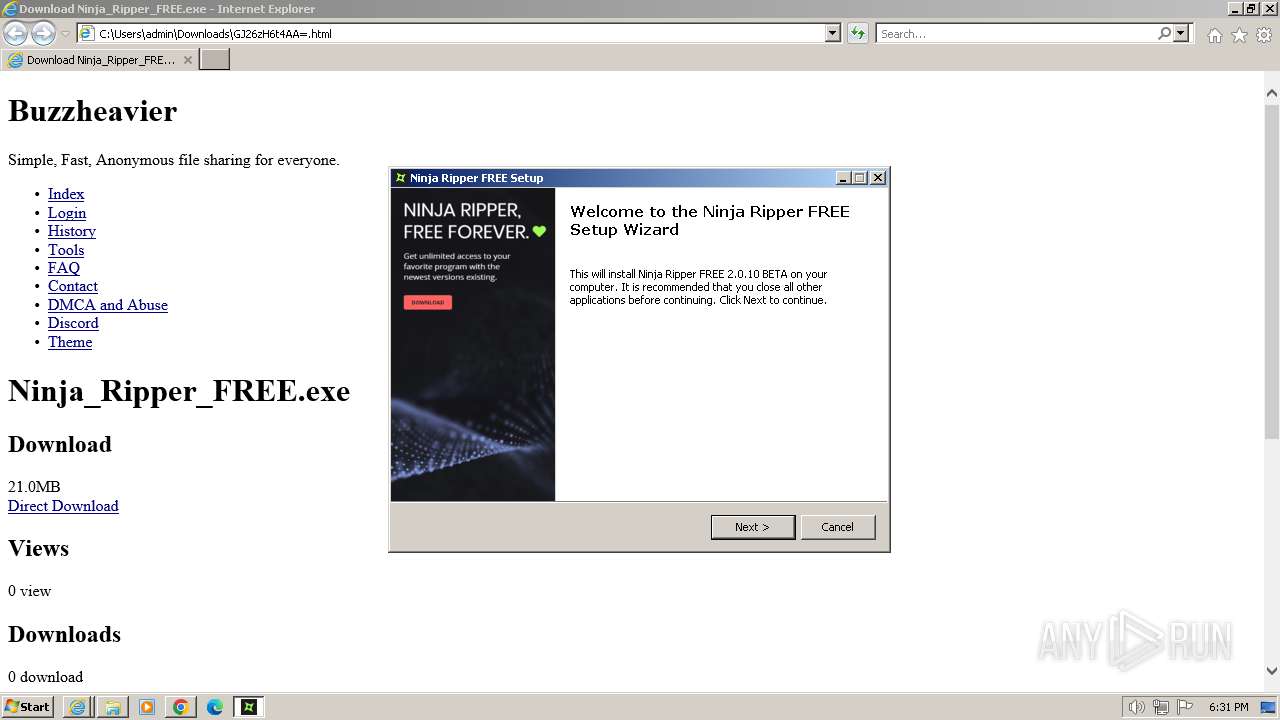
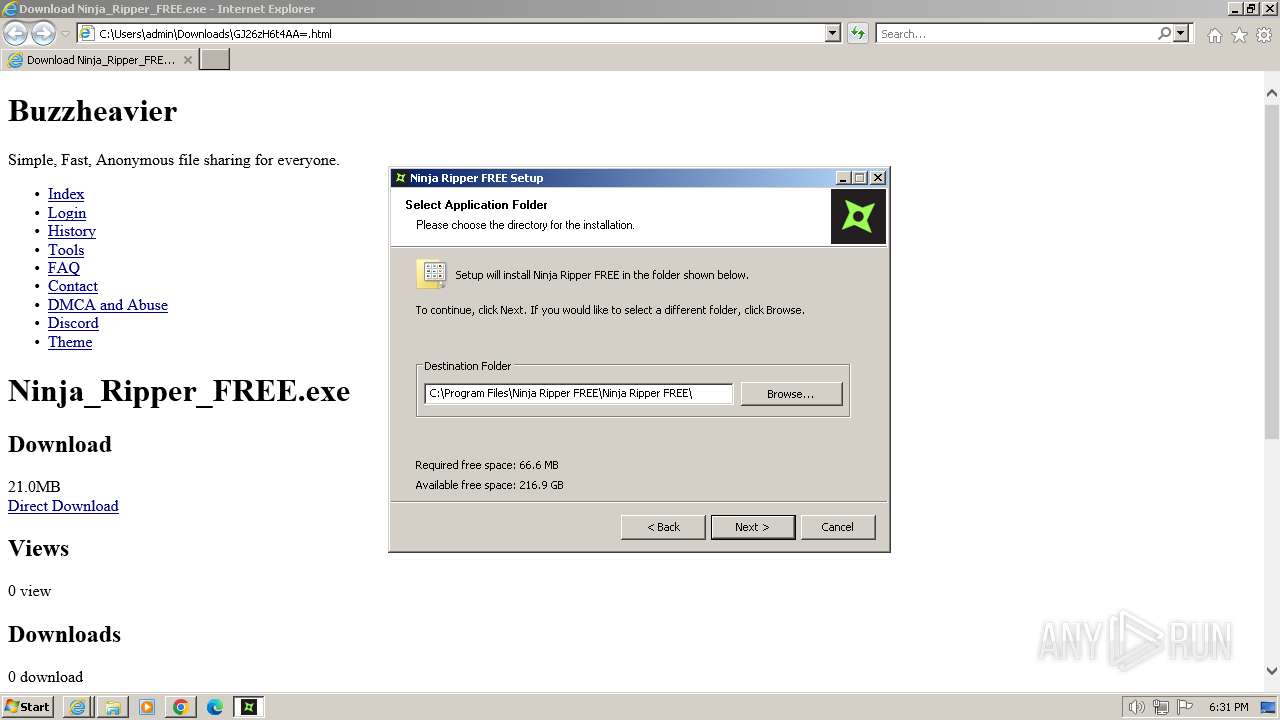
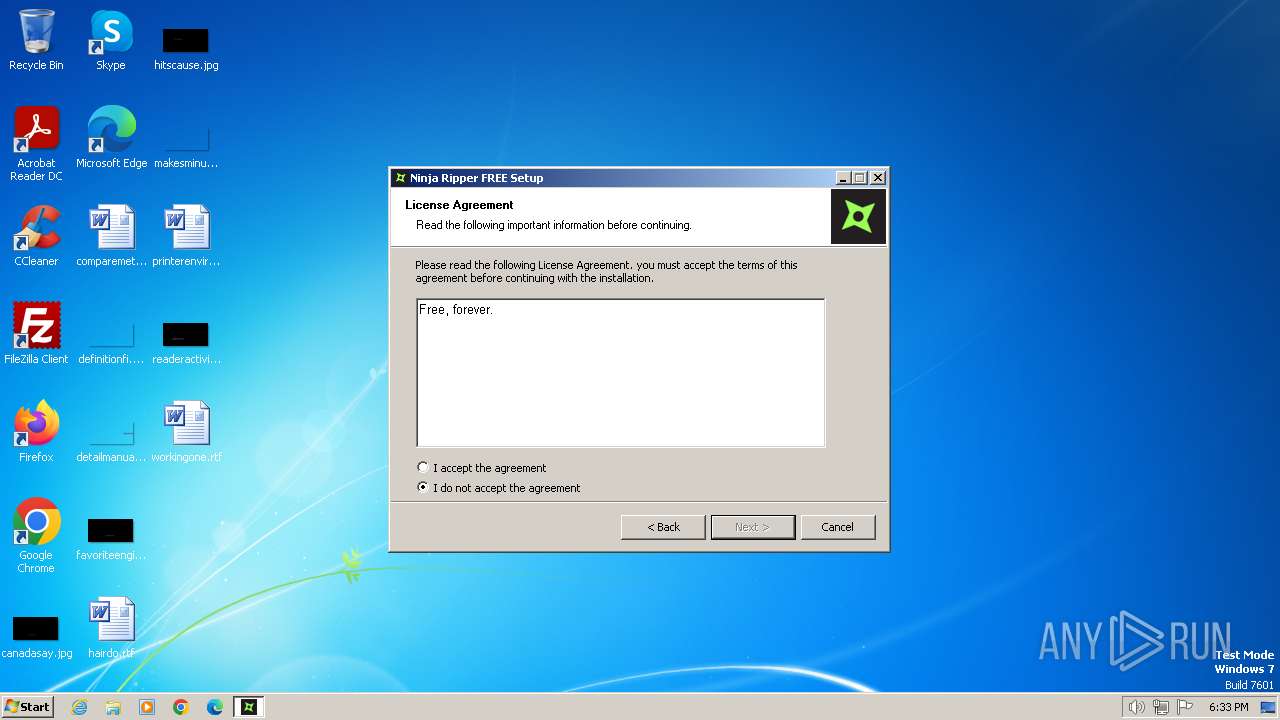
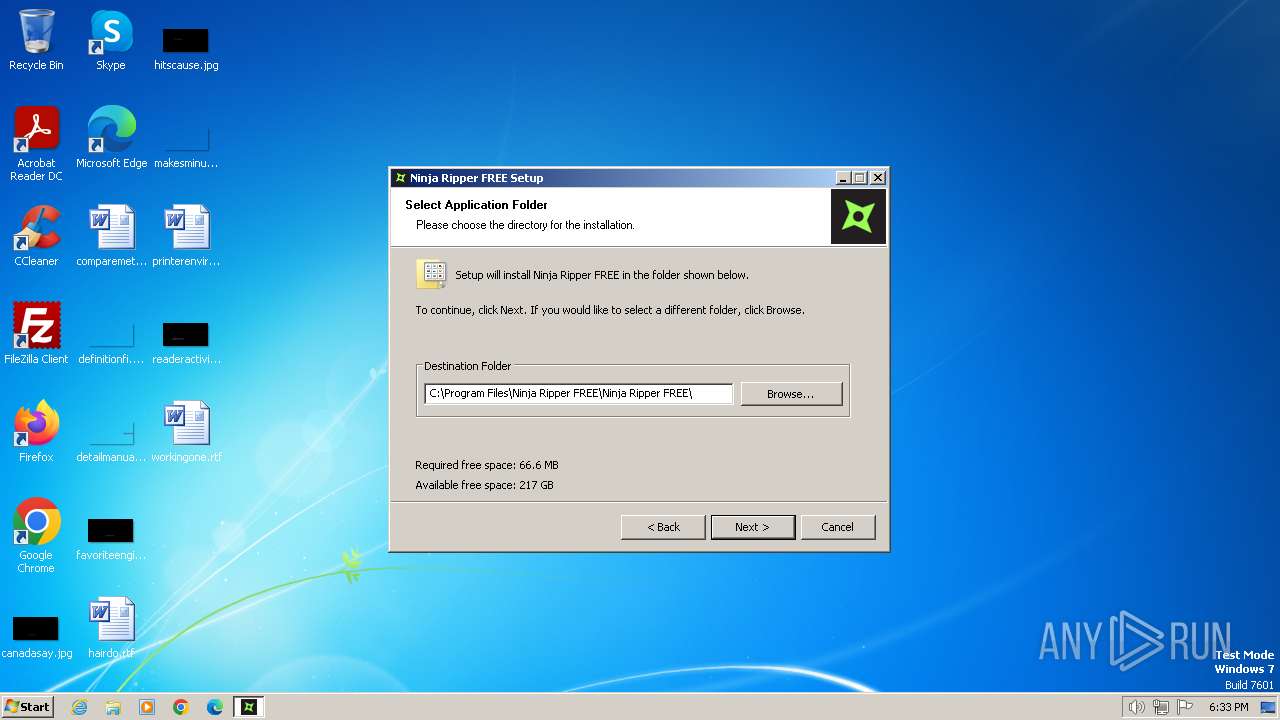
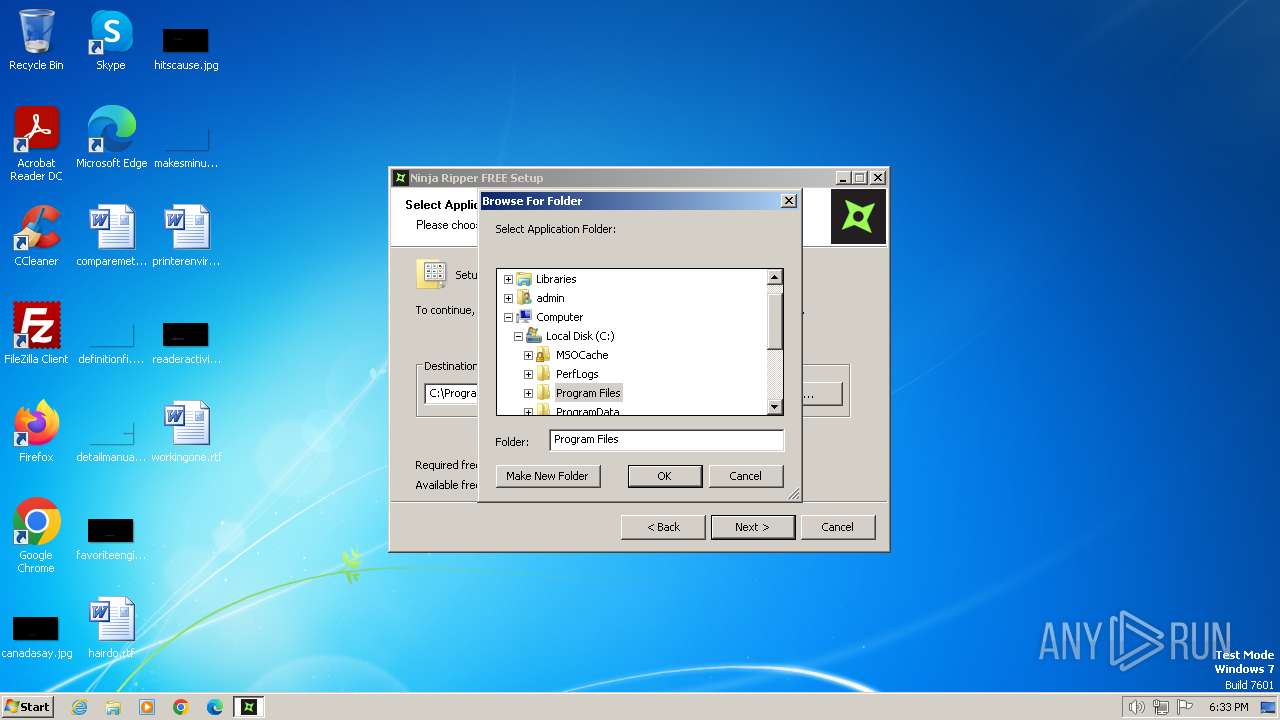
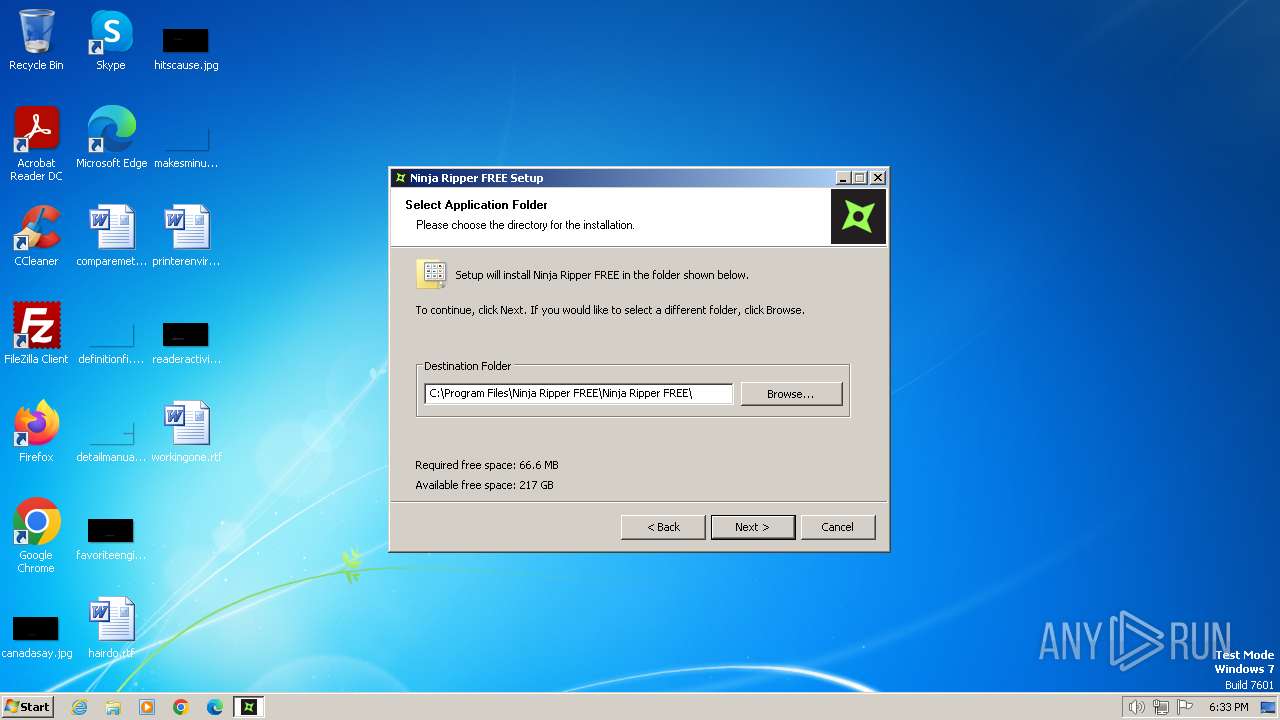
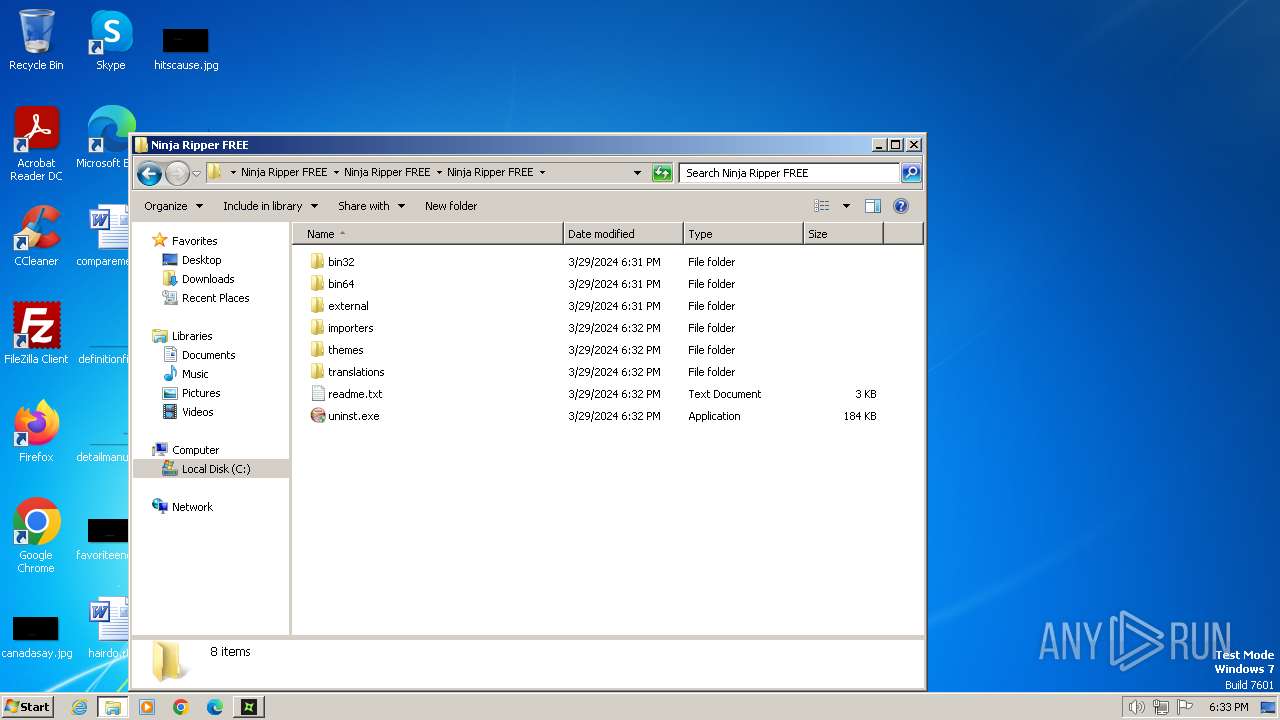
Creates a software uninstall entry
- Ninja_Ripper_FREE.exe (PID: 2864)
- Ninja_Ripper_FREE.exe (PID: 1056)
Reads the Internet Settings
- Ninja_Ripper_FREE.exe (PID: 2864)
- Ninja_Ripper_FREE.exe (PID: 1056)
- NinjaRipper2.exe (PID: 3136)
Creates file in the systems drive root
- Ninja_Ripper_FREE.exe (PID: 2356)
Reads settings of System Certificates
- NinjaRipper2.exe (PID: 3136)
INFO
Modifies the phishing filter of IE
- iexplore.exe (PID: 1836)
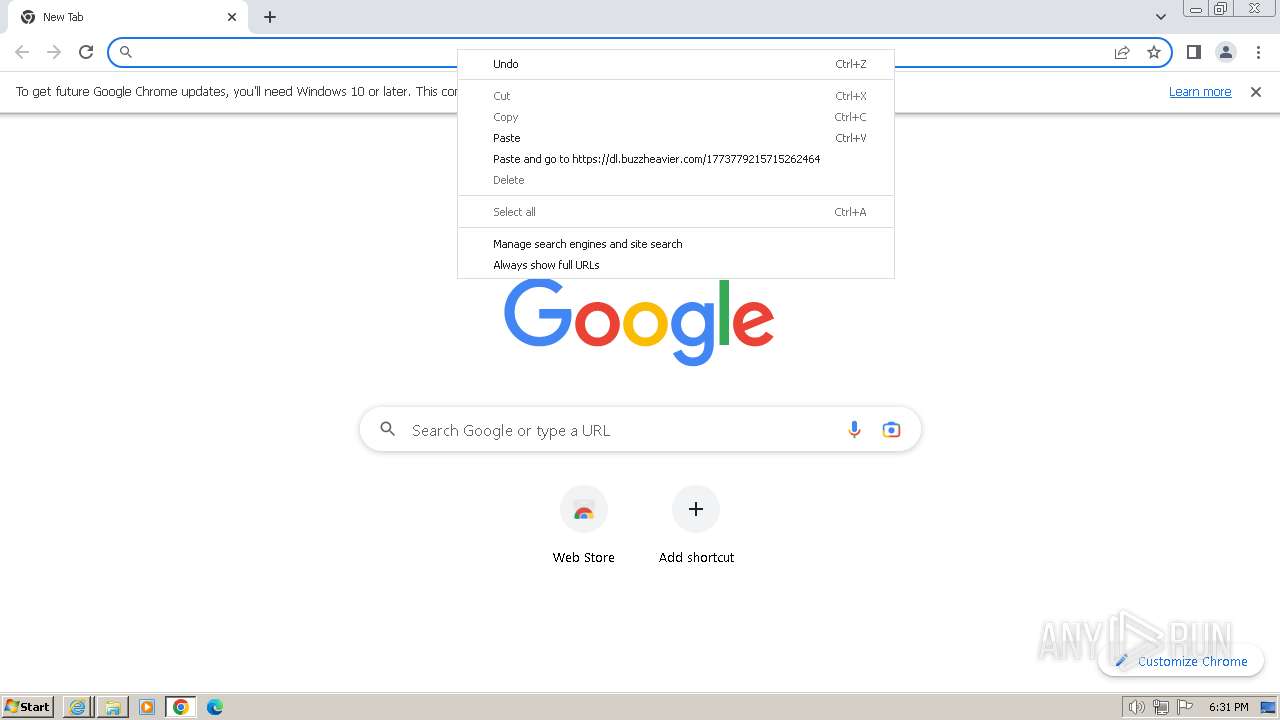
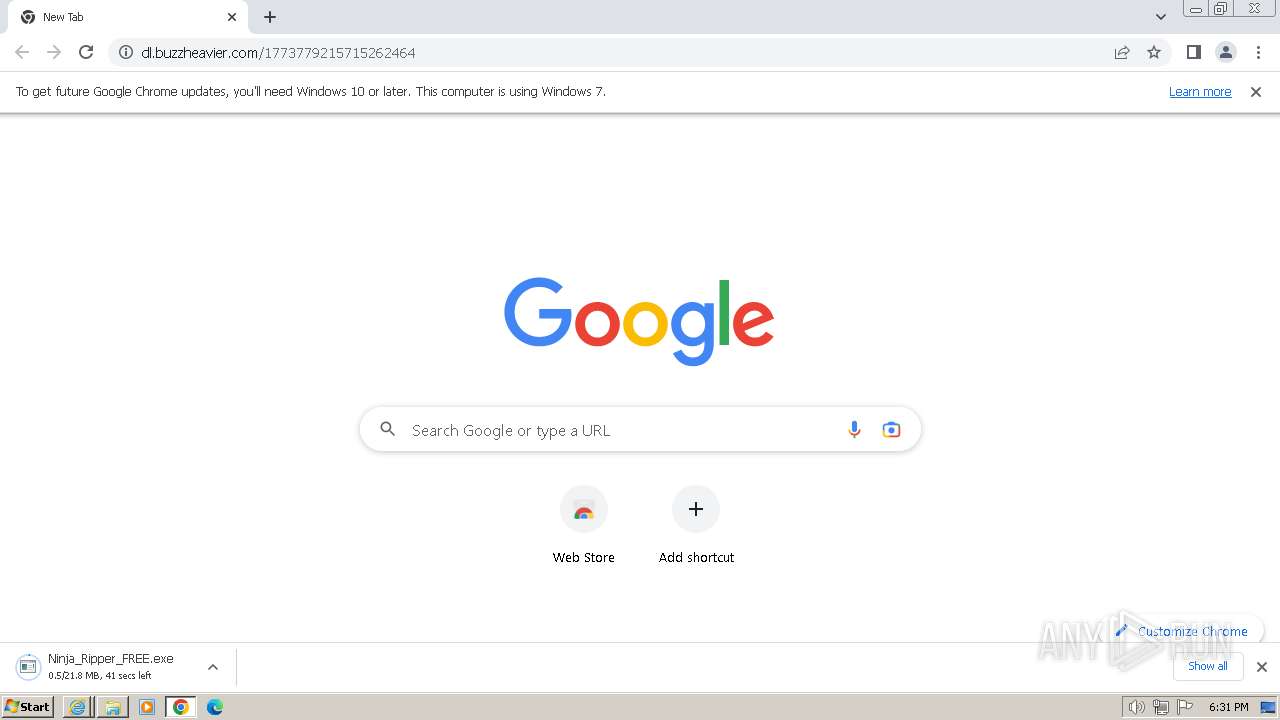
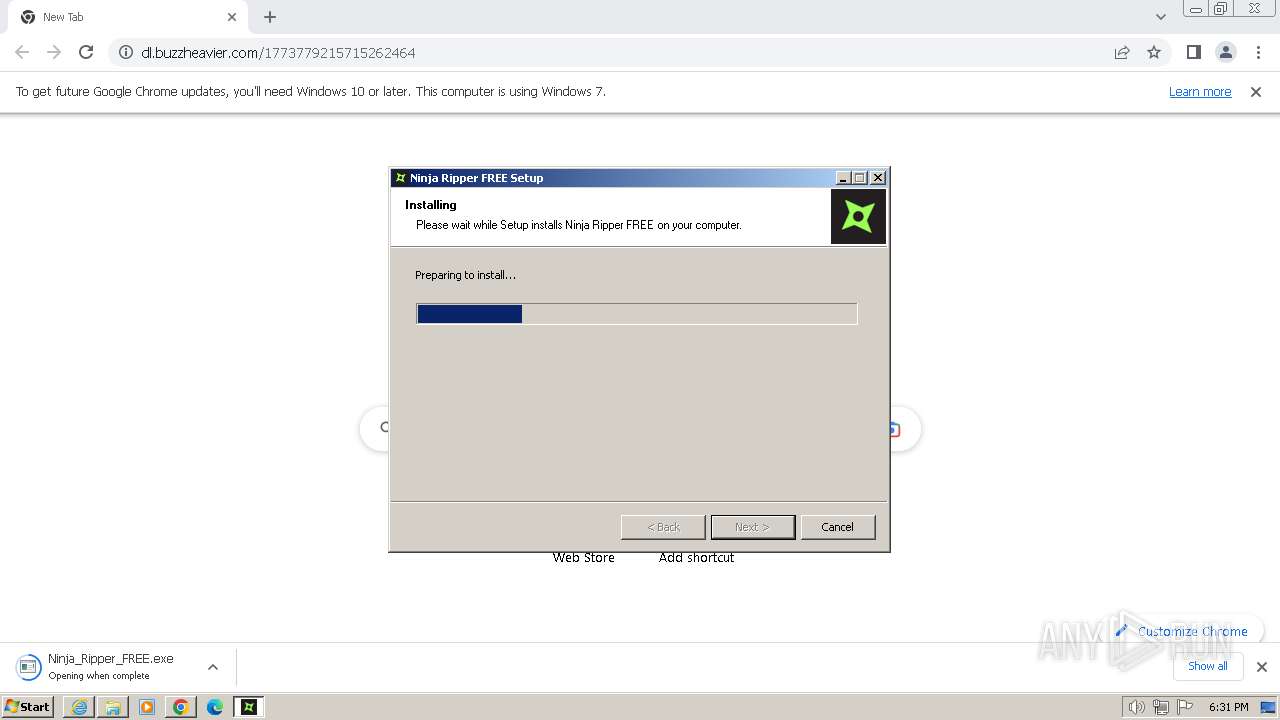
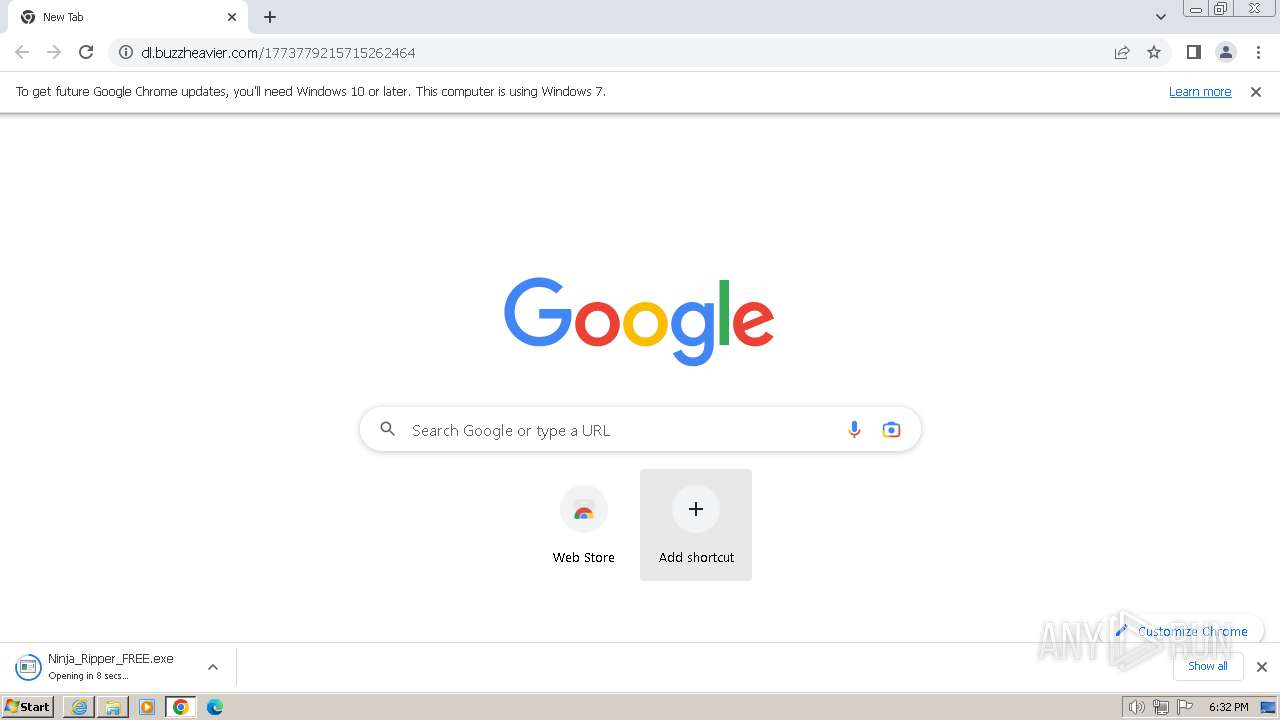
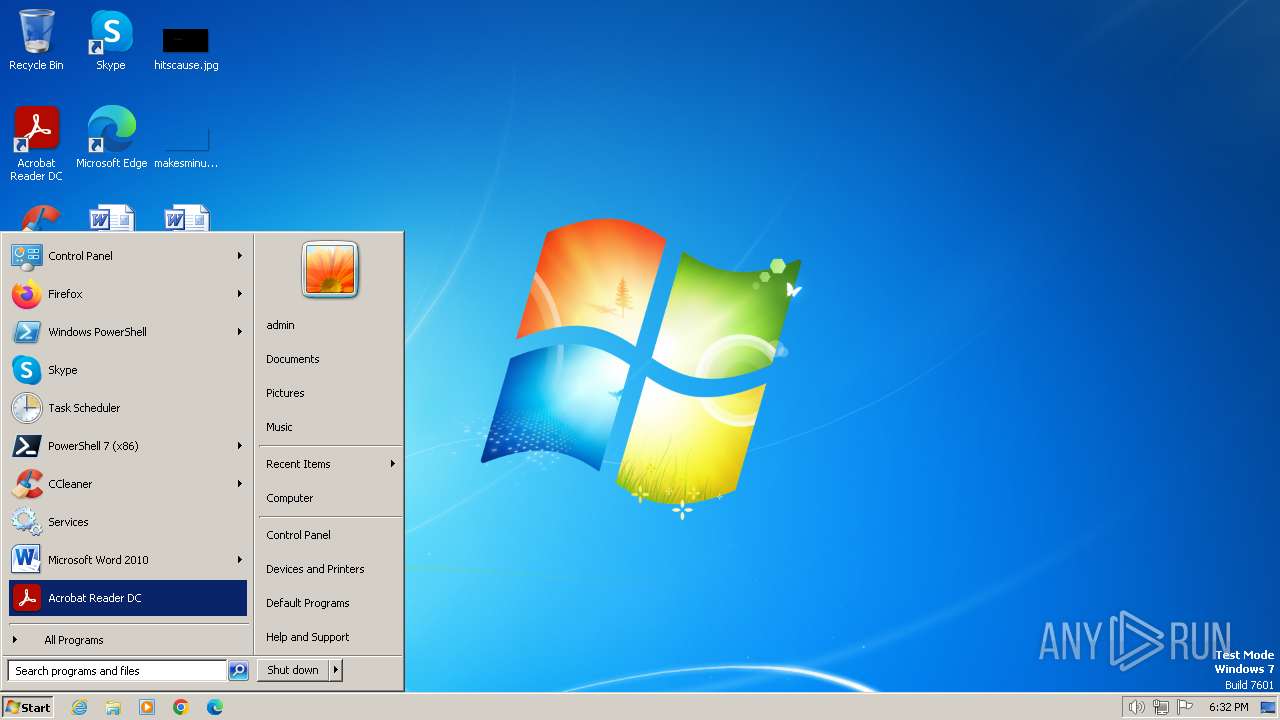
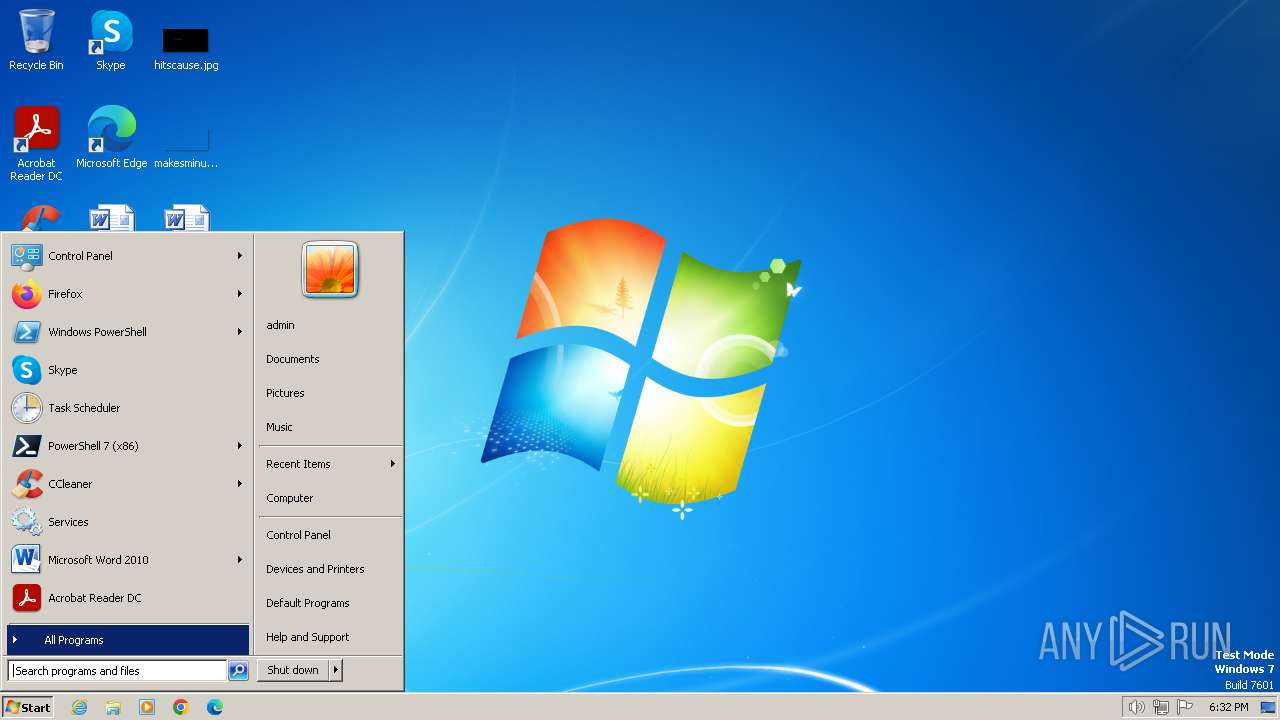
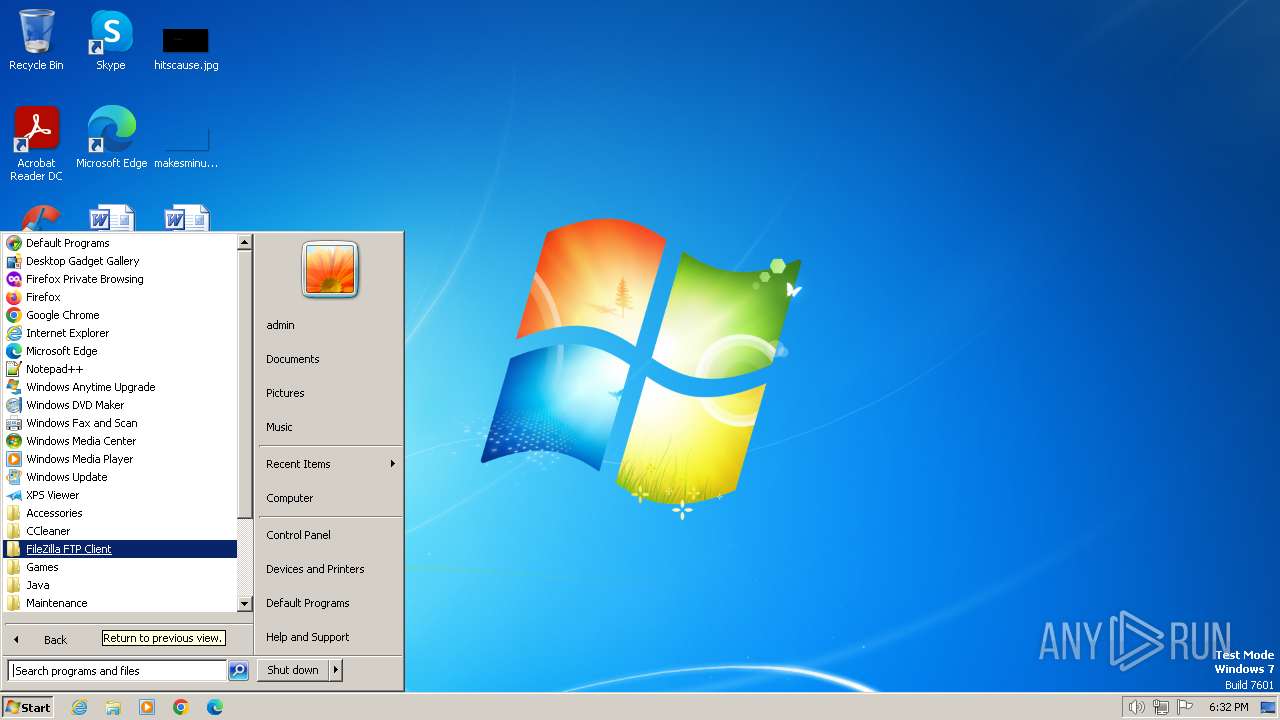
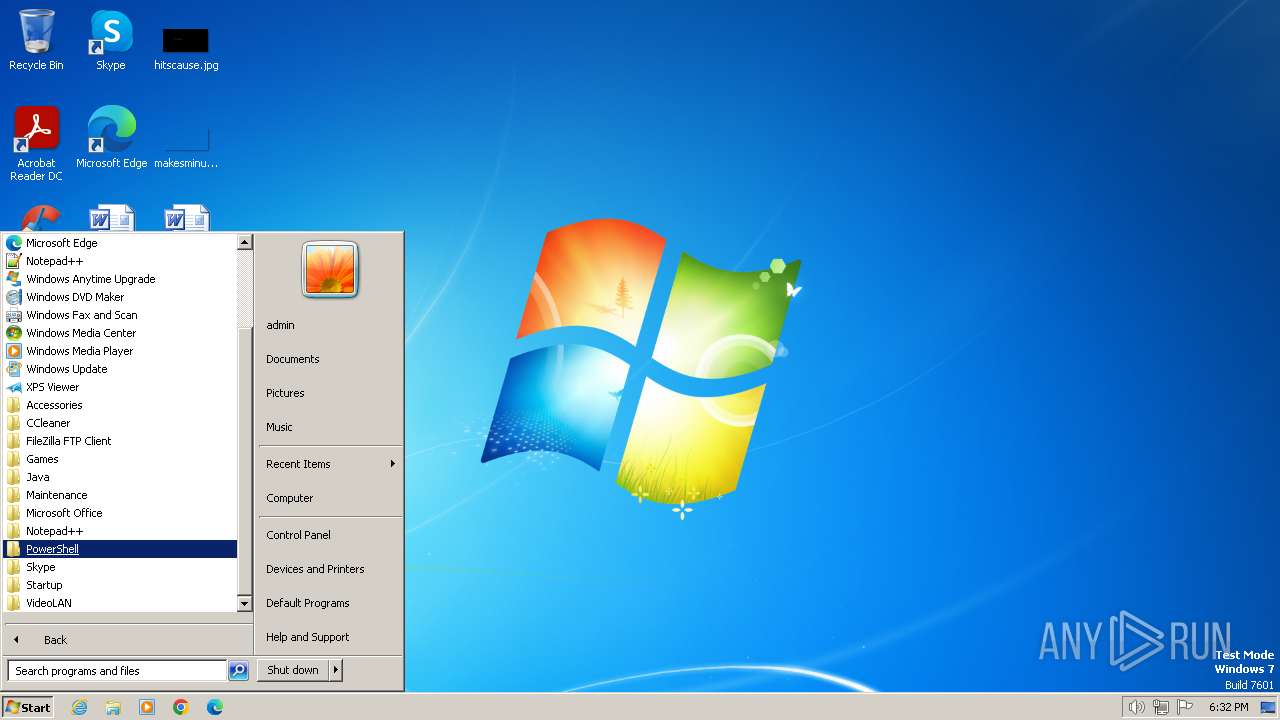
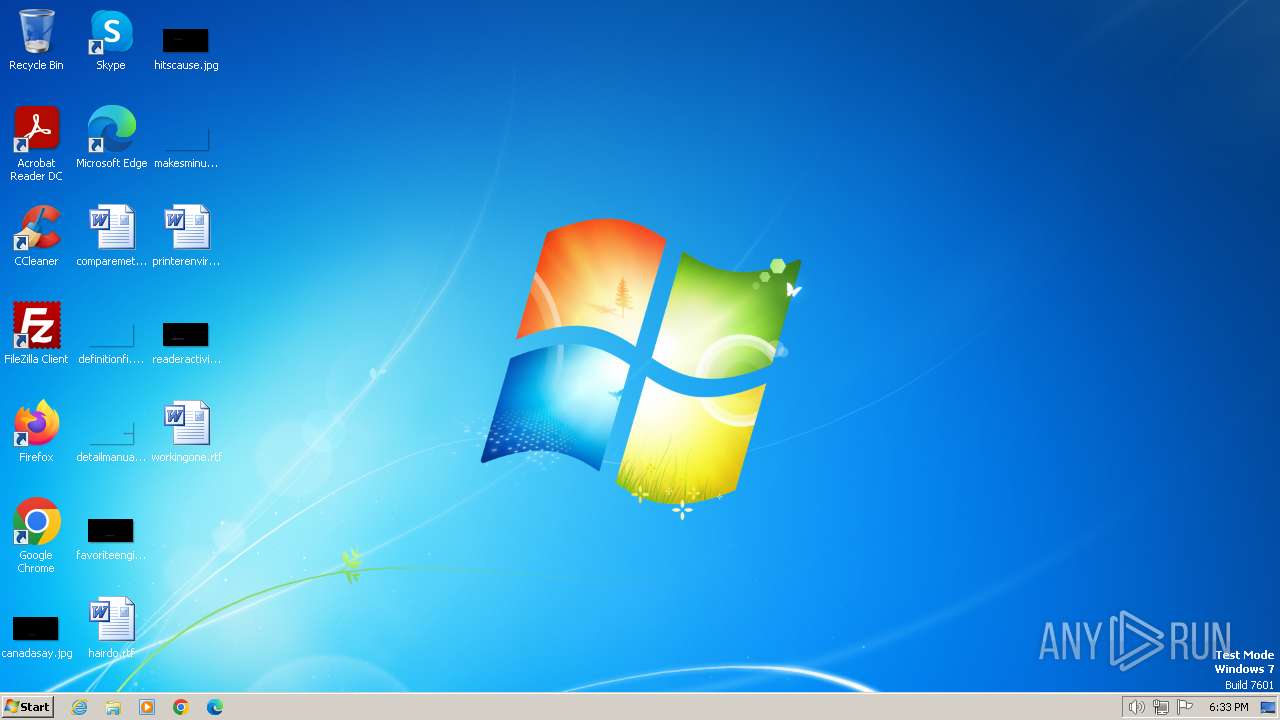
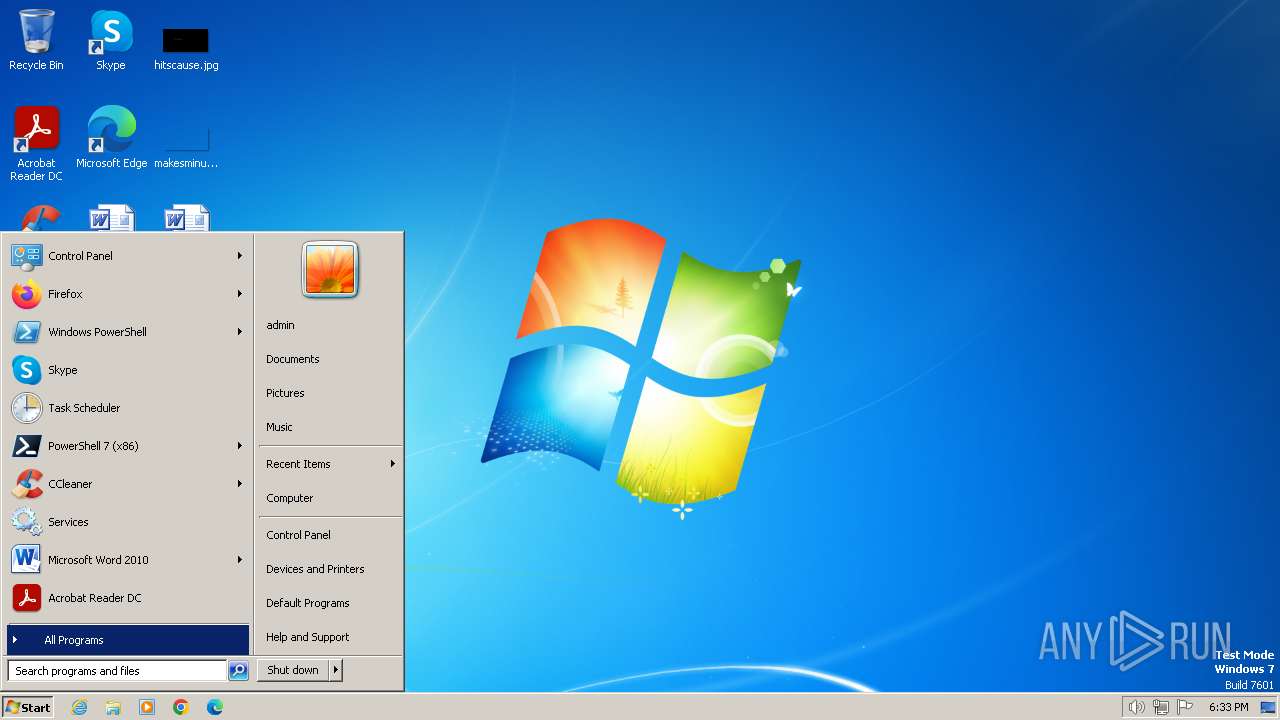
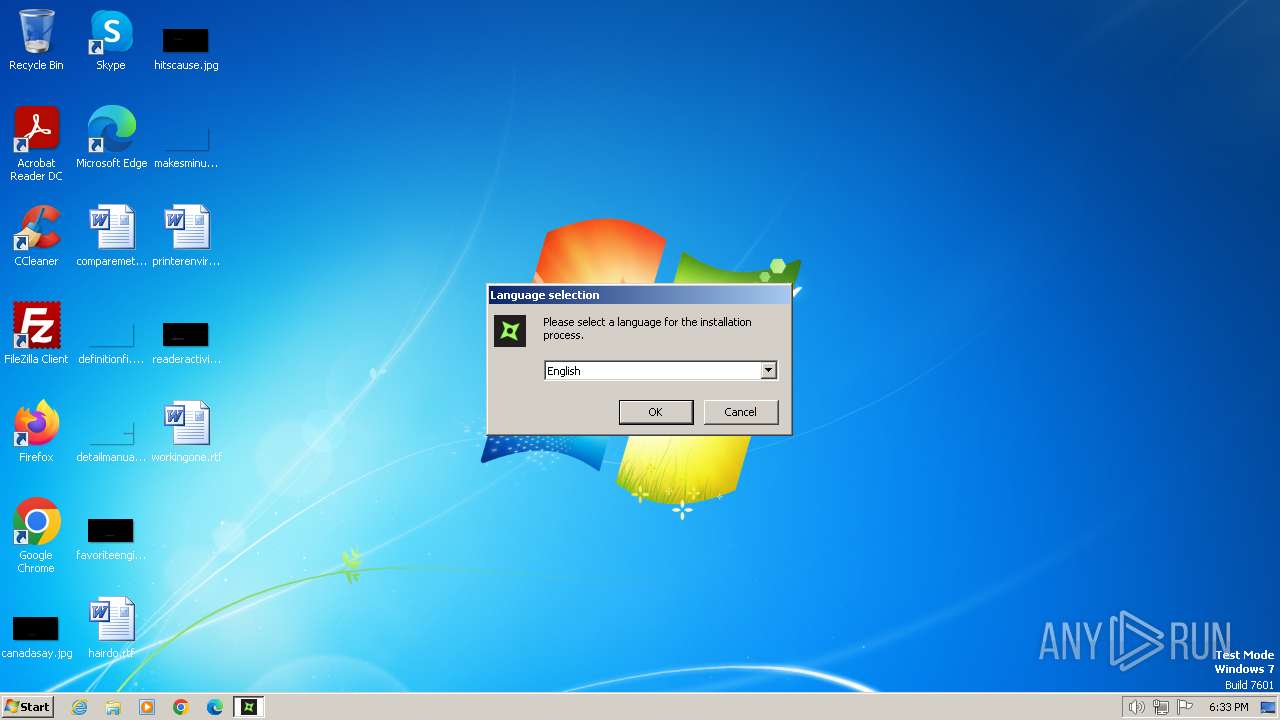
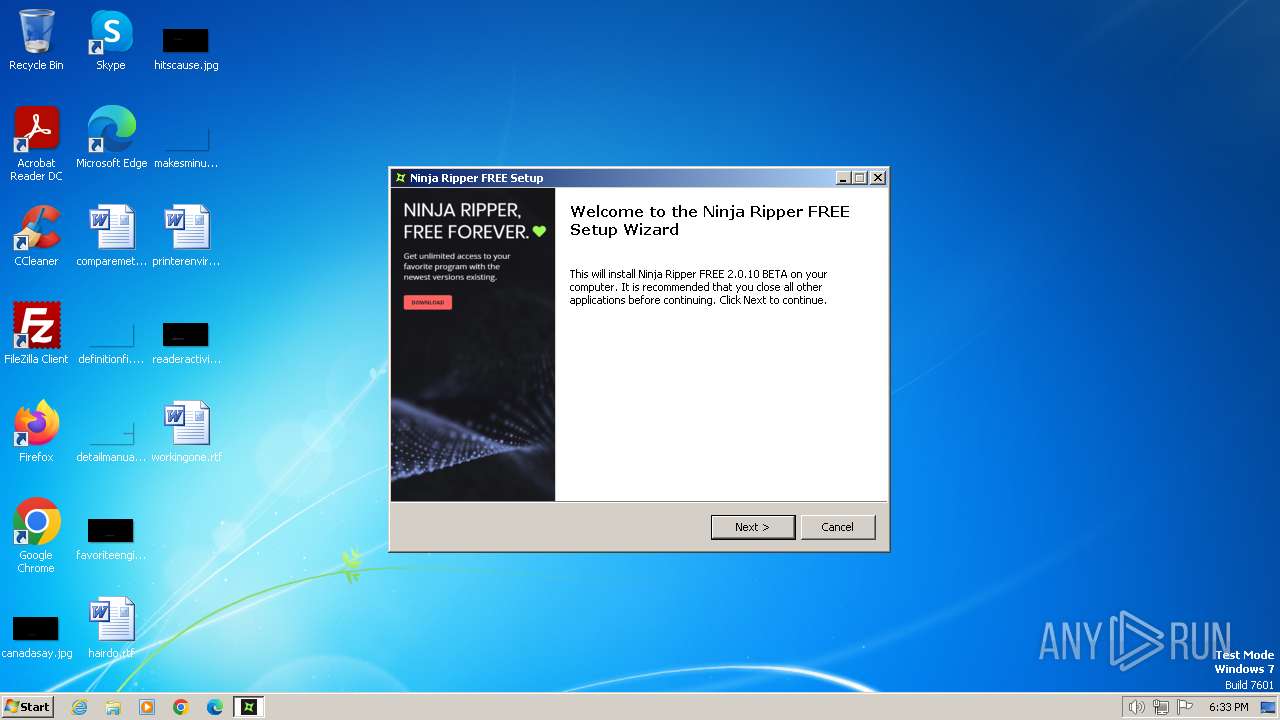
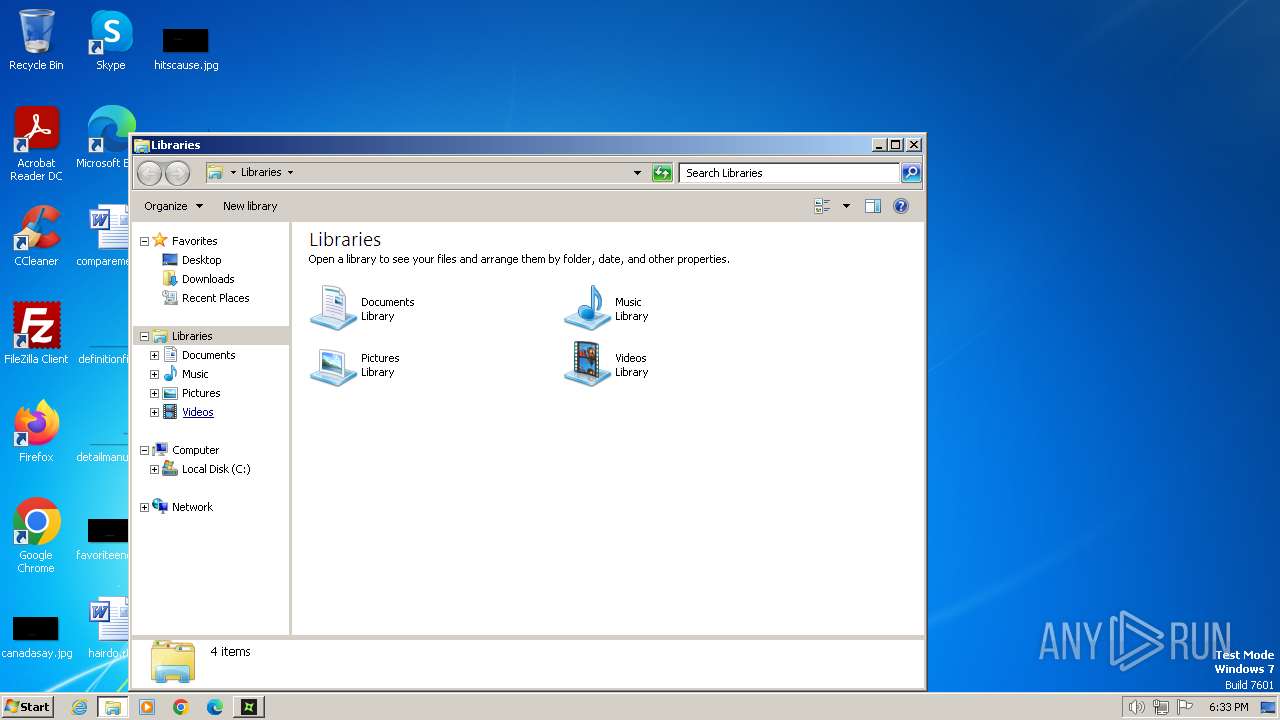
Manual execution by a user
- explorer.exe (PID: 2804)
- chrome.exe (PID: 2640)
- Ninja_Ripper_FREE.exe (PID: 2356)
- explorer.exe (PID: 3420)
- Ninja_Ripper_FREE.exe (PID: 3904)
- explorer.exe (PID: 3964)
- notepad.exe (PID: 3756)
- NinjaRipper2.exe (PID: 3136)
Application launched itself
- iexplore.exe (PID: 4000)
- chrome.exe (PID: 2640)
- iexplore.exe (PID: 1836)
Drops the executable file immediately after the start
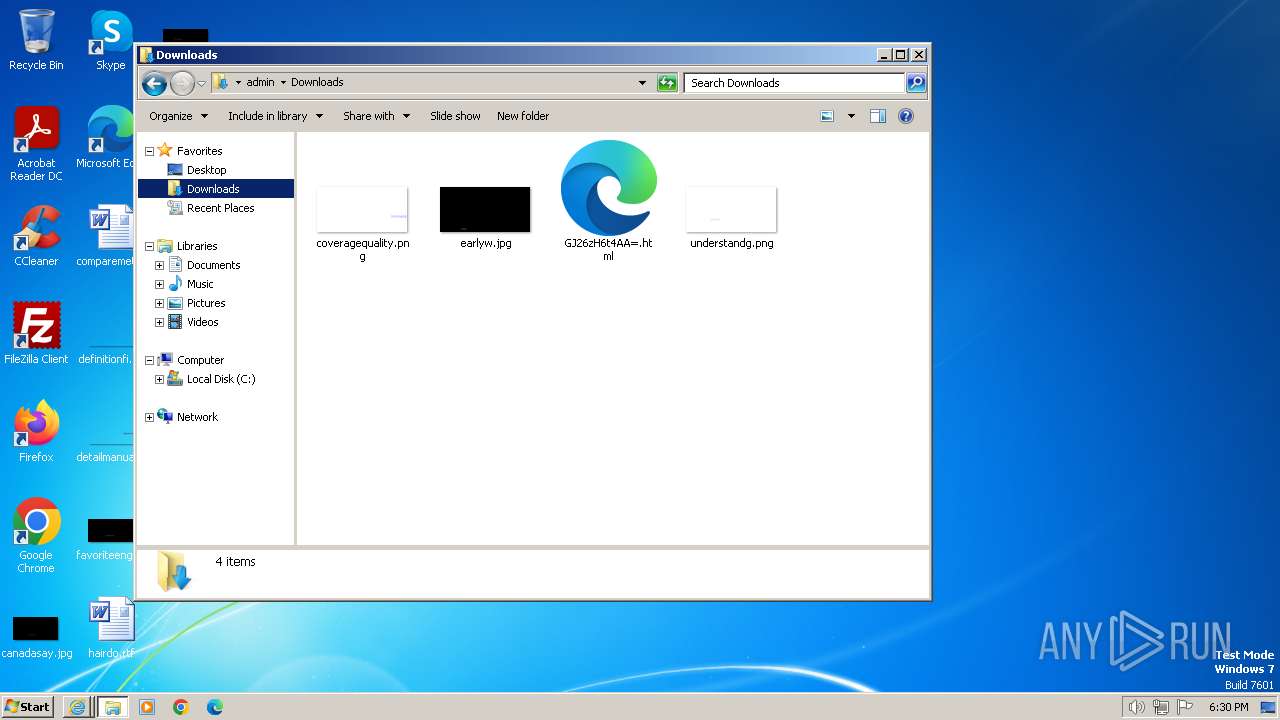
- iexplore.exe (PID: 1976)
- chrome.exe (PID: 2640)
- chrome.exe (PID: 3192)
The process uses the downloaded file
- iexplore.exe (PID: 1836)
- chrome.exe (PID: 2772)
- chrome.exe (PID: 2640)
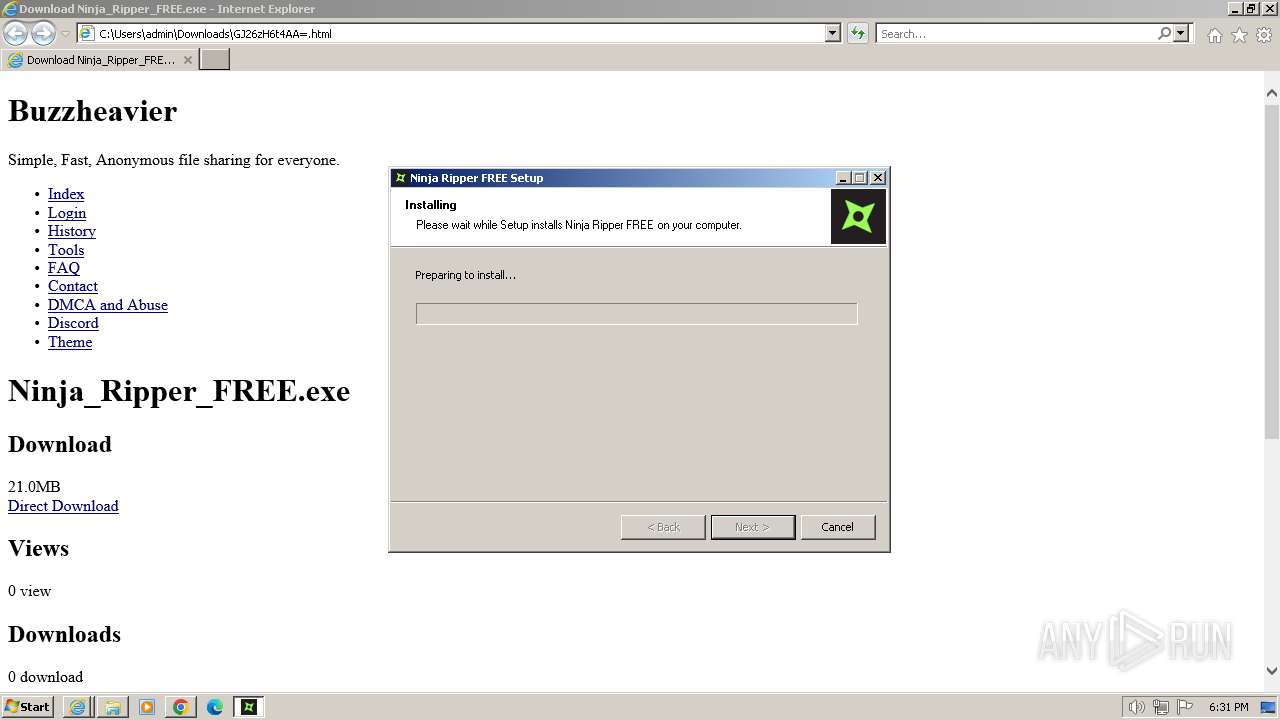
Create files in a temporary directory
- Ninja_Ripper_FREE.exe (PID: 2864)
- Ninja_Ripper_FREE.exe (PID: 1056)
- Ninja_Ripper_FREE.exe (PID: 2356)
Reads the computer name
- Ninja_Ripper_FREE.exe (PID: 2864)
- Ninja_Ripper_FREE.exe (PID: 1056)
- Ninja_Ripper_FREE.exe (PID: 2356)
- NinjaRipper2.exe (PID: 3136)
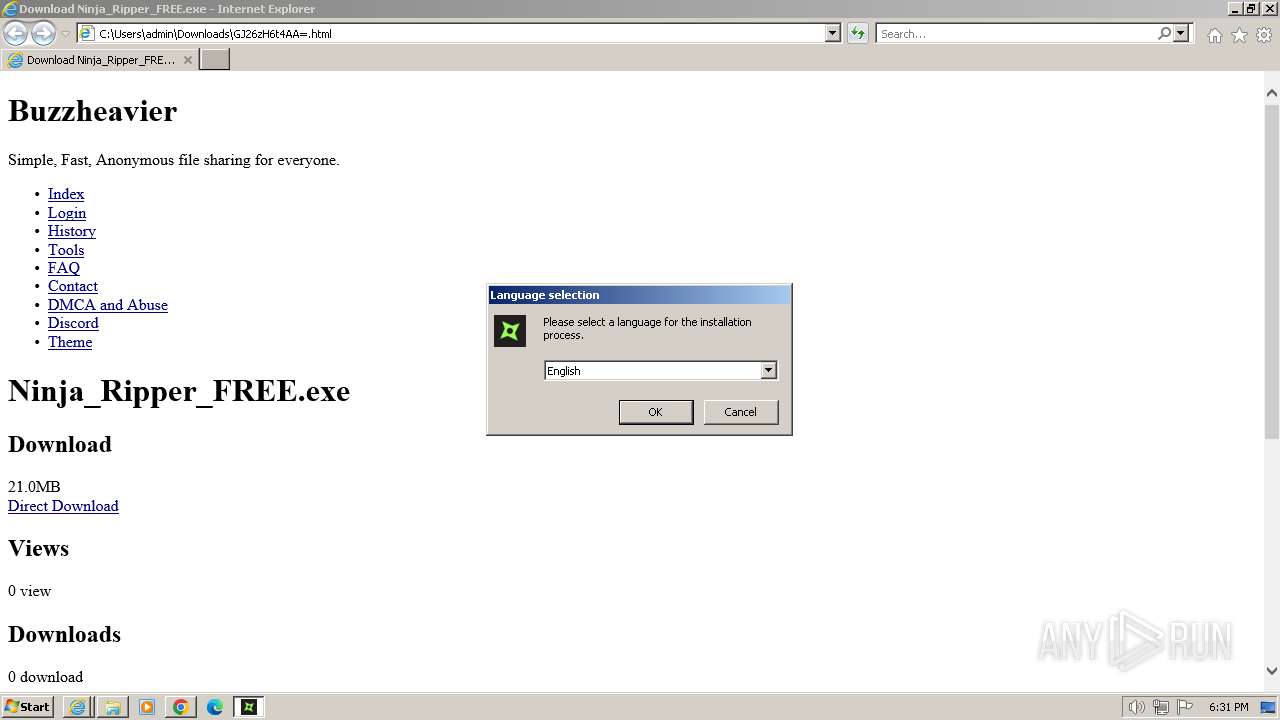
Checks supported languages
- Ninja_Ripper_FREE.exe (PID: 2864)
- Ninja_Ripper_FREE.exe (PID: 1056)
- Ninja_Ripper_FREE.exe (PID: 2356)
- NinjaRipper2.exe (PID: 3136)
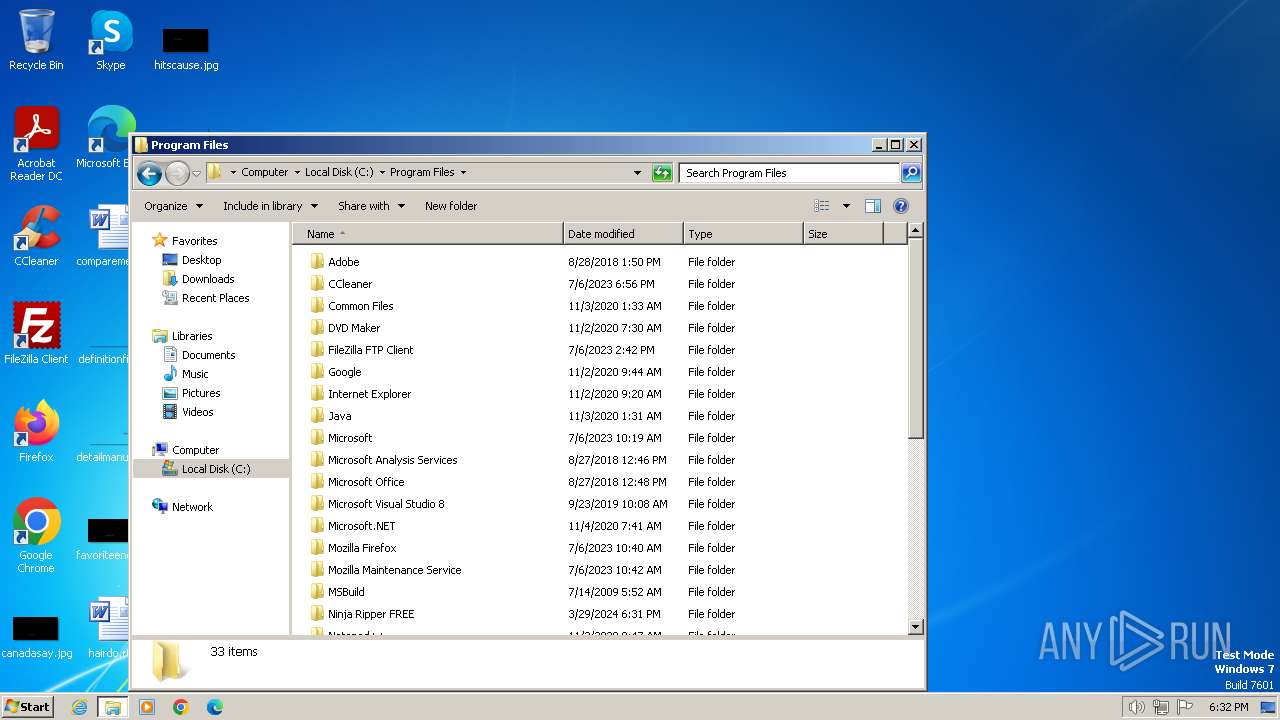
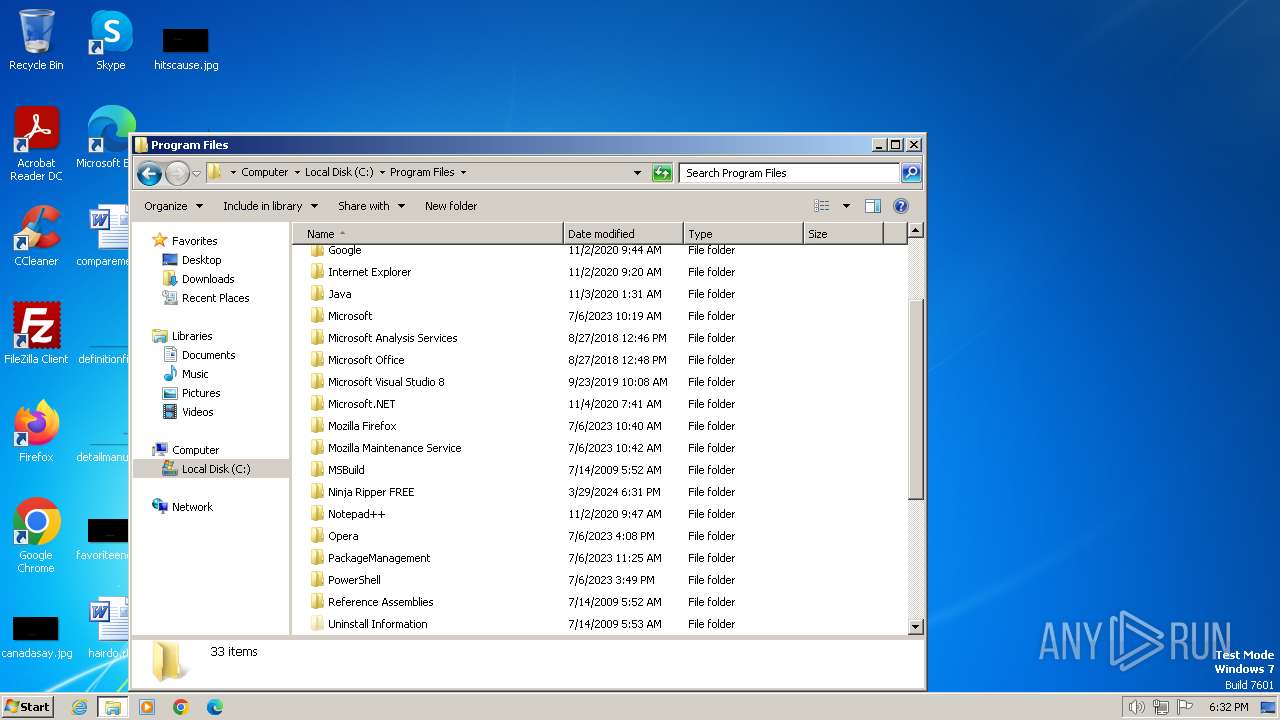
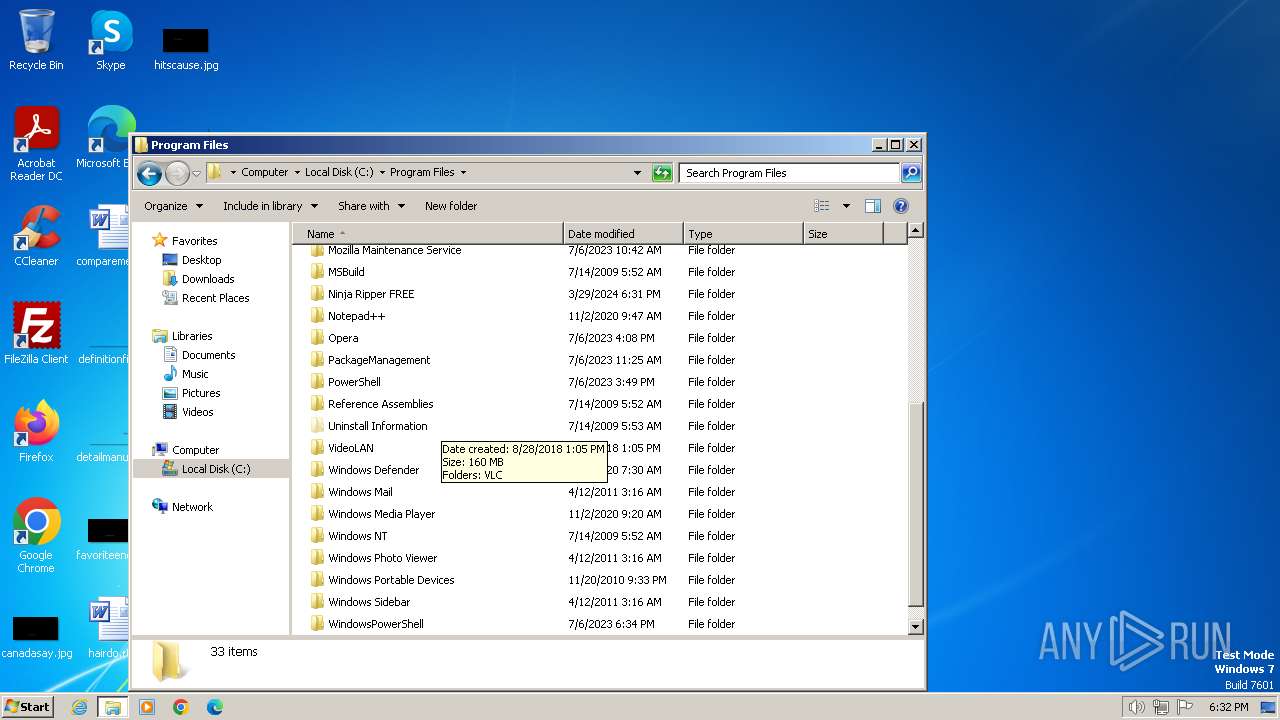
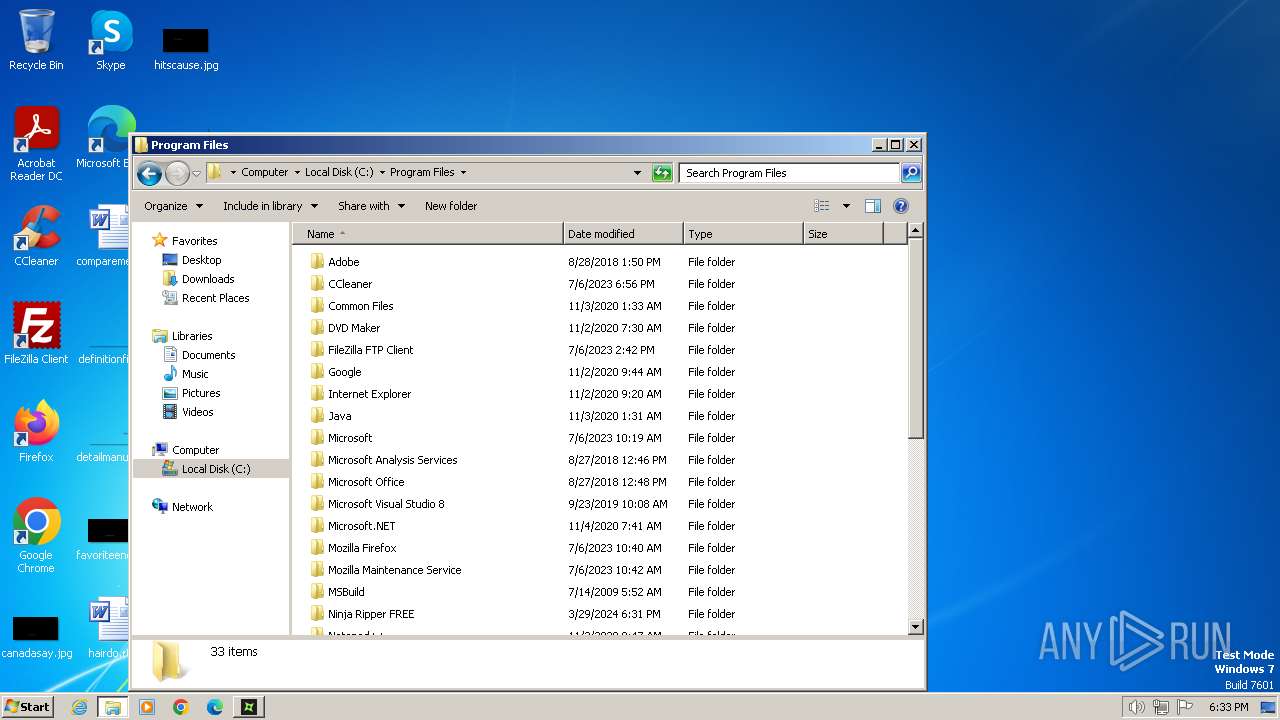
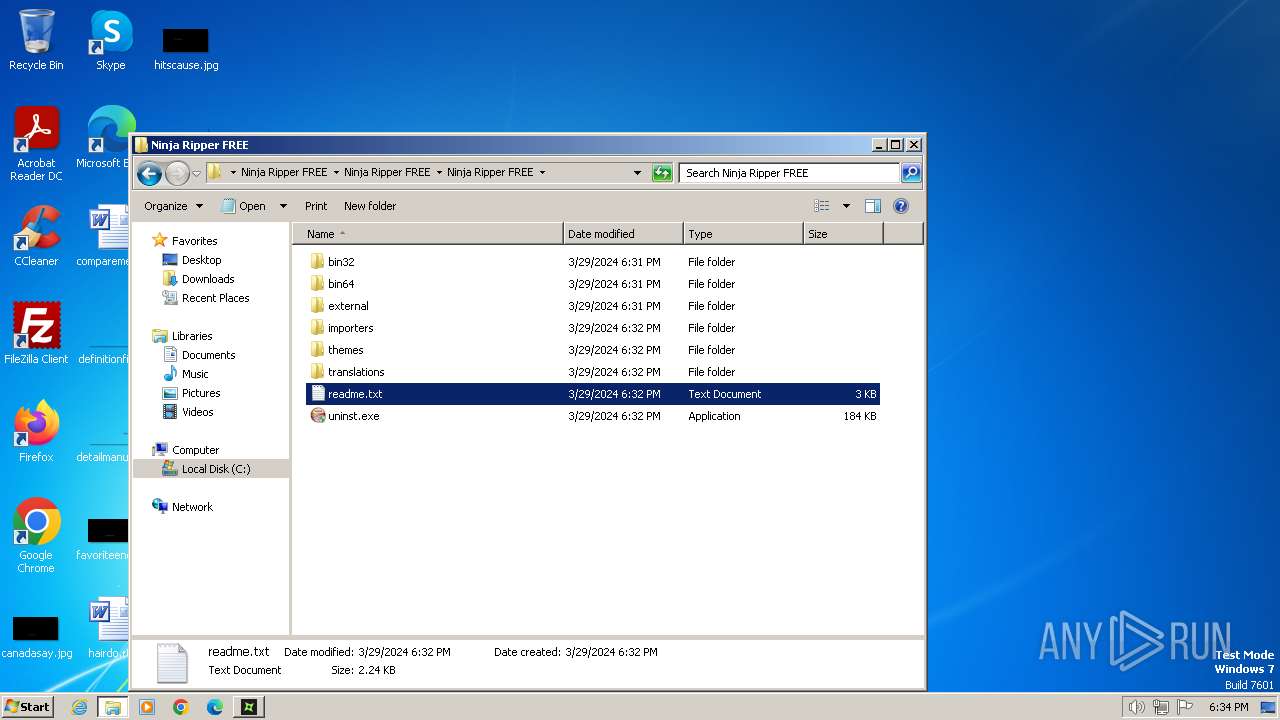
Creates files in the program directory
- Ninja_Ripper_FREE.exe (PID: 2864)
Reads the machine GUID from the registry
- NinjaRipper2.exe (PID: 3136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| Viewport: | width=device-width, initial-scale=1.0 |
|---|---|
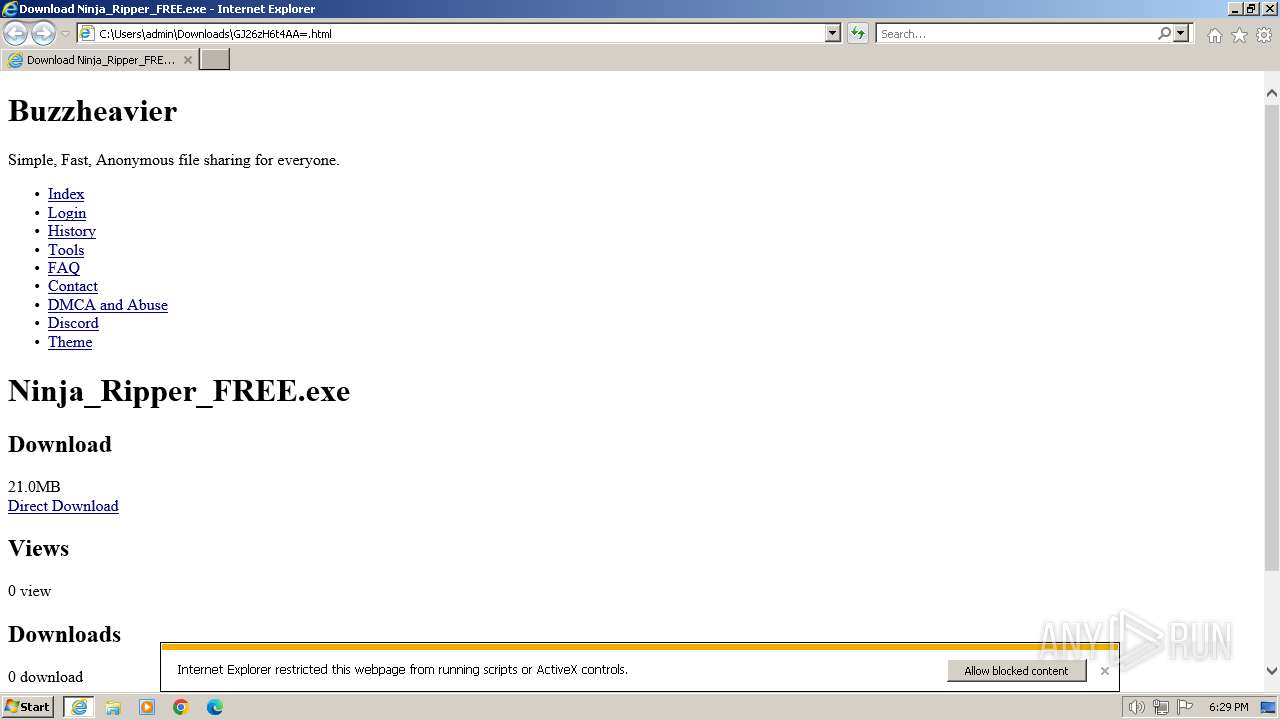
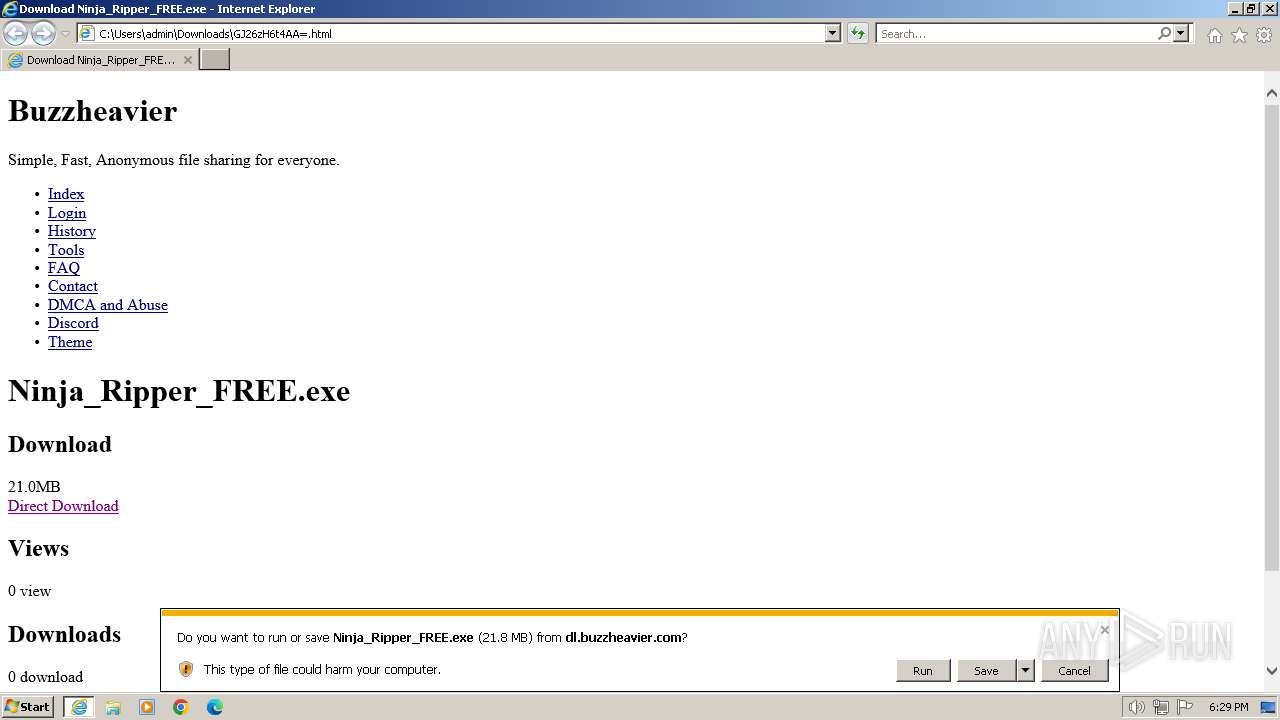
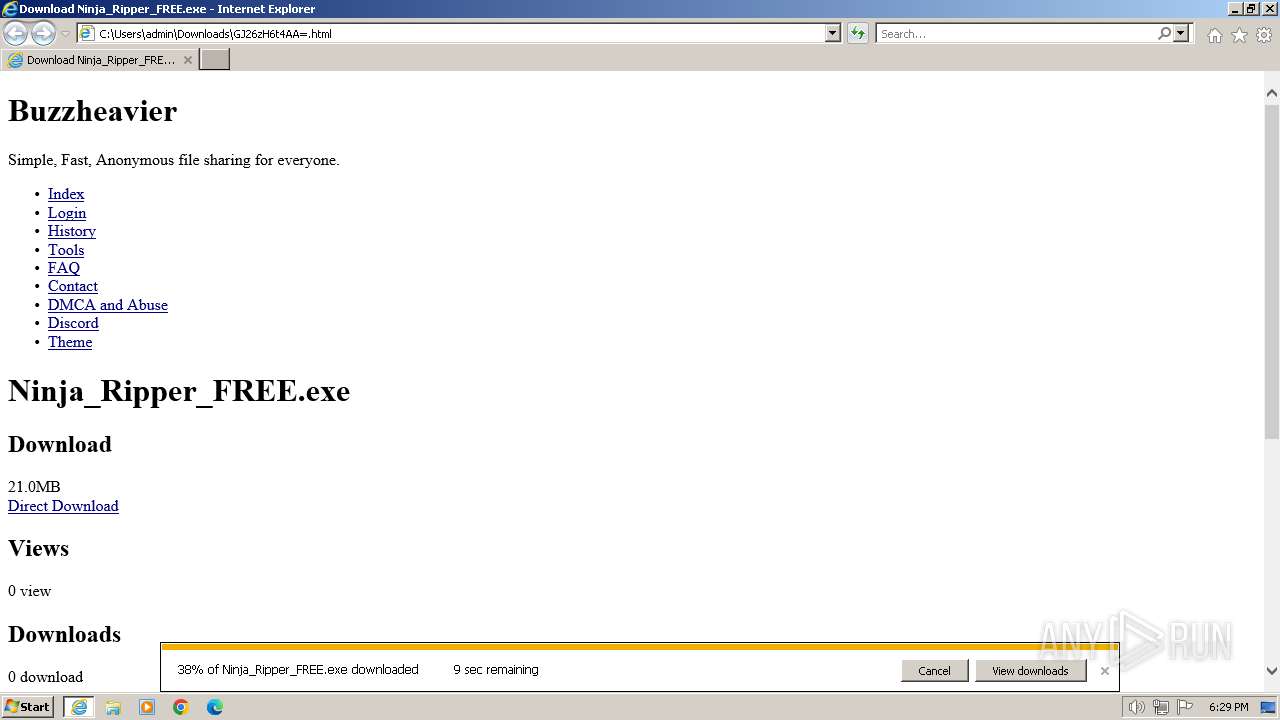
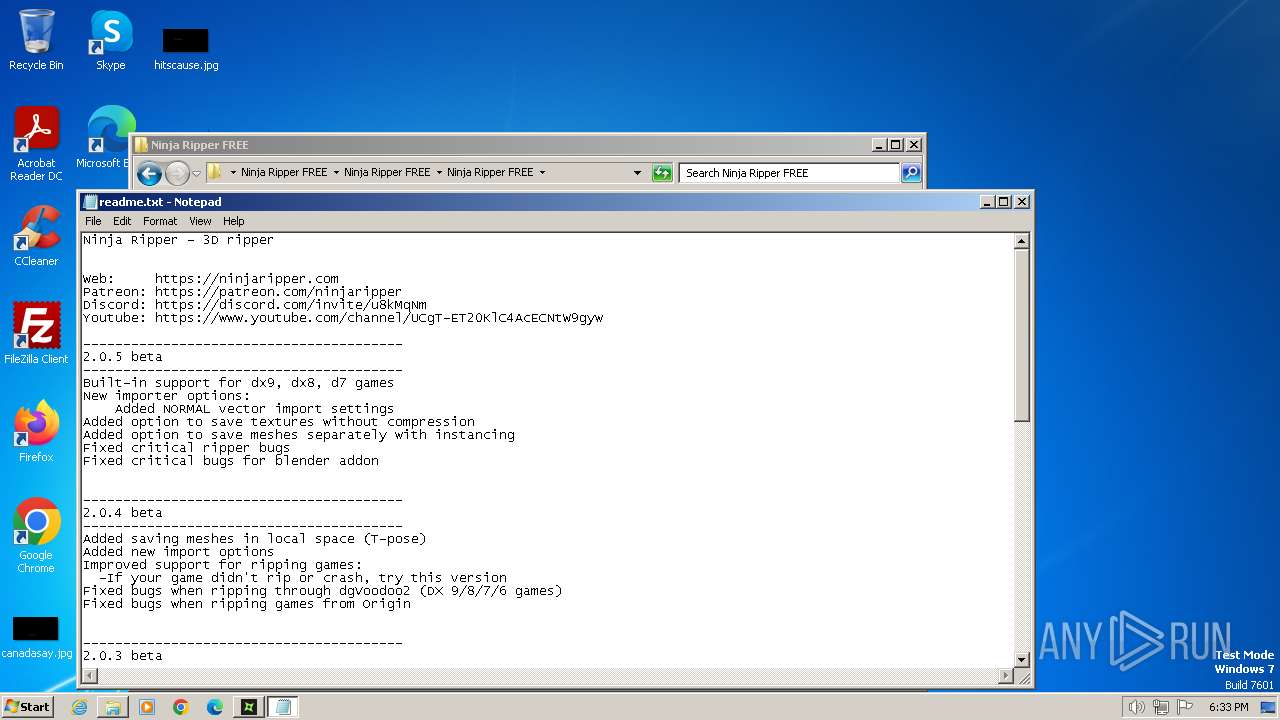
| Title: | Download Ninja_Ripper_FREE.exe |
| Description: | Simple, Fast, Anonymous file sharing for everyone. |
| ThemeColor: | #ff6600 |
| Keywords: | Anonymous File Sharing, Unlimited File Size Upload, Large File Transfer, Secure File Sharing, No Size Limit File Upload, Private File Sharing Service, High-Speed File Transfer, High-Speed File Transfer, Online File Sharing Platform, Data Sharing Service, Free File Sharing, Cloud File Sharing, File Sharing for Large Files, Easy File Transfer, File Sharing Without Registration |
| MsapplicationTileColor: | #ff6600 |
| MsapplicationTileImage: | /static/favicon/mstile-144x144.png |
| MsapplicationSquare70x70logo: | /static/favicon/mstile-70x70.png |
| MsapplicationSquare150x150logo: | /static/favicon/mstile-150x150.png |
| MsapplicationWide310x150logo: | /static/favicon/mstile-310x150.png |
| MsapplicationSquare310x310logo: | /static/favicon/mstile-310x310.png |
| ApplicationName: | Buzzheavier |
| GoogleAdsenseAccount: | ca-pub-2938777398053735 |
Total processes
85
Monitored processes
31
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1836 --field-trial-handle=1200,i,104547026071744231,15388417033771222856,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1056 | "C:\Users\admin\Downloads\Ninja_Ripper_FREE.exe" | C:\Users\admin\Downloads\Ninja_Ripper_FREE.exe | chrome.exe | ||||||||||||
User: admin Company: Ninja Ripper FREE Integrity Level: HIGH Exit code: 0 Version: 2.0.10 BETA Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=4128 --field-trial-handle=1200,i,104547026071744231,15388417033771222856,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1548 | "C:\Users\admin\Downloads\Ninja_Ripper_FREE.exe" | C:\Users\admin\Downloads\Ninja_Ripper_FREE.exe | — | chrome.exe | |||||||||||
User: admin Company: Ninja Ripper FREE Integrity Level: MEDIUM Exit code: 3221226540 Version: 2.0.10 BETA Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2132 --field-trial-handle=1200,i,104547026071744231,15388417033771222856,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\Downloads\GJ26zH6t4AA=.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1620 --field-trial-handle=1200,i,104547026071744231,15388417033771222856,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1836 CREDAT:333057 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3644 --field-trial-handle=1200,i,104547026071744231,15388417033771222856,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2356 | "C:\Users\admin\Downloads\Ninja_Ripper_FREE.exe" | C:\Users\admin\Downloads\Ninja_Ripper_FREE.exe | explorer.exe | ||||||||||||
User: admin Company: Ninja Ripper FREE Integrity Level: HIGH Version: 2.0.10 BETA Modules
| |||||||||||||||
Total events
51 856
Read events
51 503
Write events
277
Delete events
76
Modification events
| (PID) Process: | (1836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 220537104 | |||
| (PID) Process: | (1836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31097351 | |||
| (PID) Process: | (1836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 520539604 | |||
| (PID) Process: | (1836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31097351 | |||
| (PID) Process: | (1836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1836) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
59
Suspicious files
35
Text files
143
Unknown types
68
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A16C6C16D94F76E0808C087DFC657D99_1853FD72A62259DD3FE7DD105517DA38 | binary | |
MD5:— | SHA256:— | |||
| 4000 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A16C6C16D94F76E0808C087DFC657D99_1853FD72A62259DD3FE7DD105517DA38 | binary | |
MD5:— | SHA256:— | |||
| 1976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
45
DNS requests
36
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4000 | iexplore.exe | GET | 304 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?af0106393379bc3d | unknown | — | — | unknown |
4000 | iexplore.exe | GET | 304 | 23.32.238.208:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?46a3771404230298 | unknown | — | — | unknown |
4000 | iexplore.exe | GET | 304 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2f4d99b3d0fa2efd | unknown | — | — | unknown |
4000 | iexplore.exe | GET | 304 | 23.32.238.208:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2bcc7bd96f118a84 | unknown | — | — | unknown |
4000 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | — | — | unknown |
4000 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | — | — | unknown |
4000 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
4000 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDE1ACspricKQppQk%2FKo0ZI | unknown | — | — | unknown |
1976 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | — | — | unknown |
1836 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4000 | iexplore.exe | 104.17.3.184:443 | challenges.cloudflare.com | CLOUDFLARENET | — | unknown |
4000 | iexplore.exe | 142.250.185.226:443 | pagead2.googlesyndication.com | GOOGLE | US | unknown |
4000 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
4000 | iexplore.exe | 23.32.238.208:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
4000 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4000 | iexplore.exe | 142.250.184.227:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
1976 | iexplore.exe | 188.114.96.3:443 | dl.buzzheavier.com | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pagead2.googlesyndication.com |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
dl.buzzheavier.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
tpc.googlesyndication.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4000 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
4000 | iexplore.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
Process | Message |
|---|---|
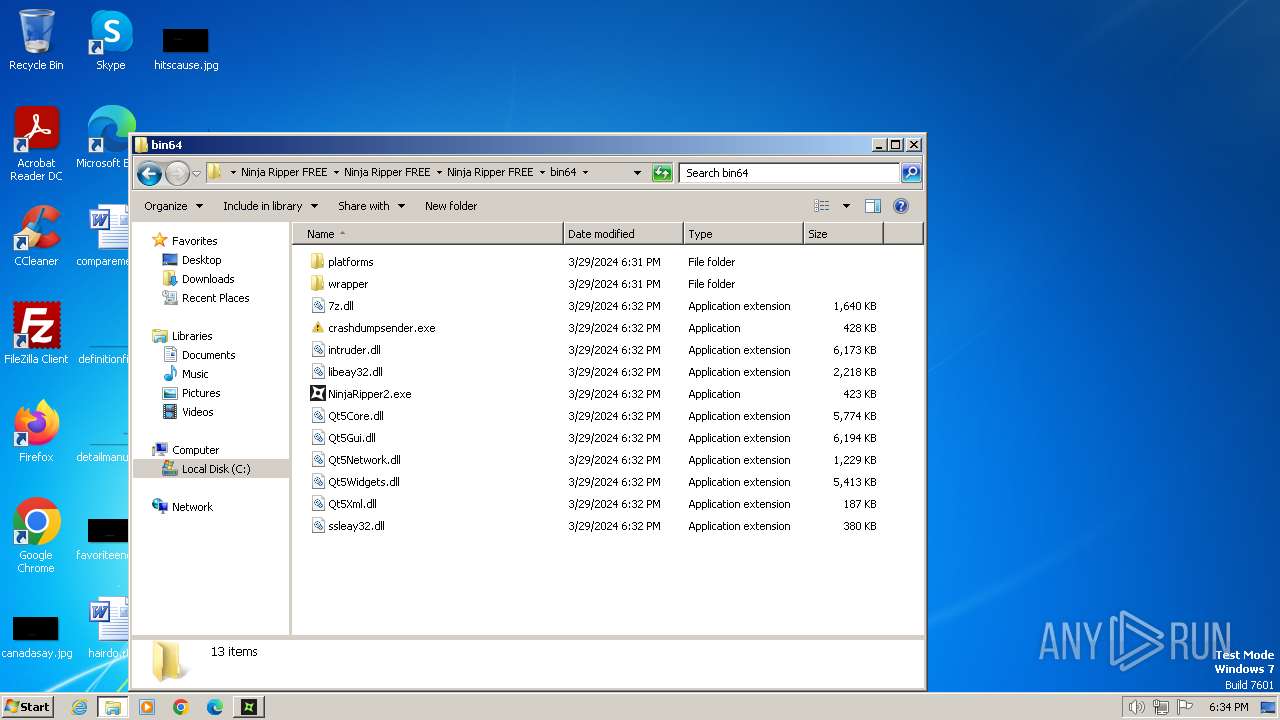
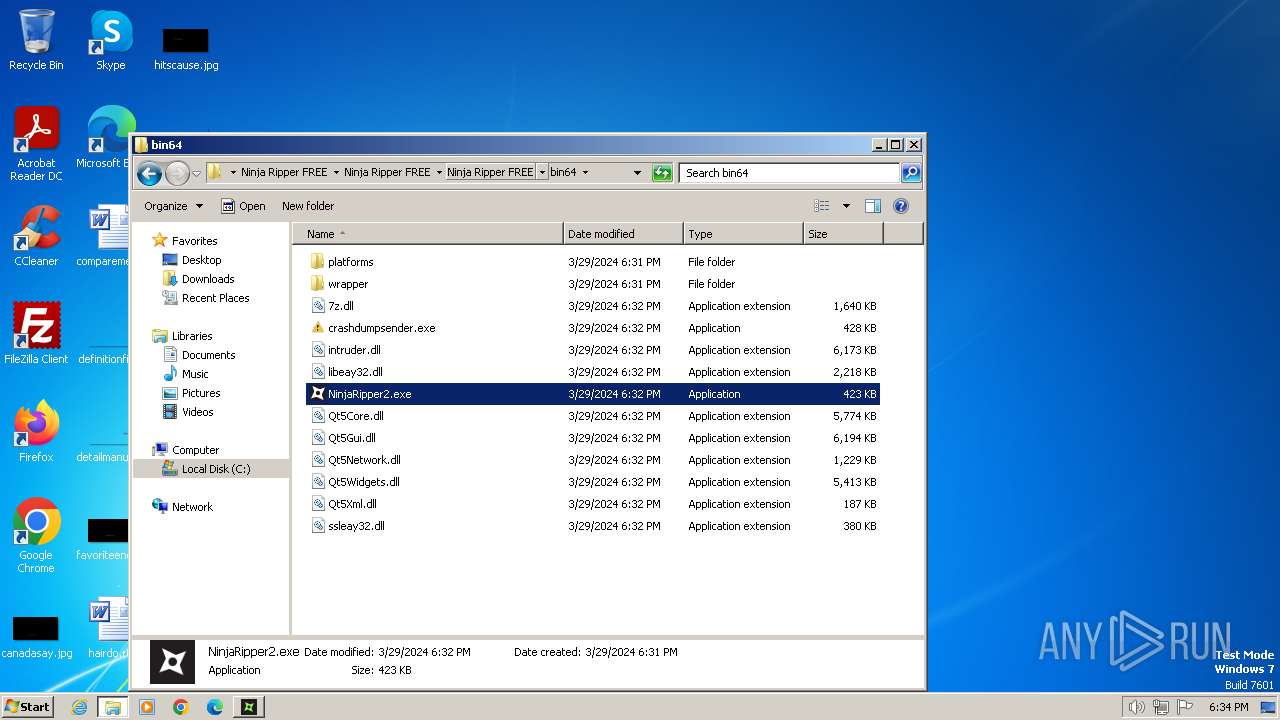
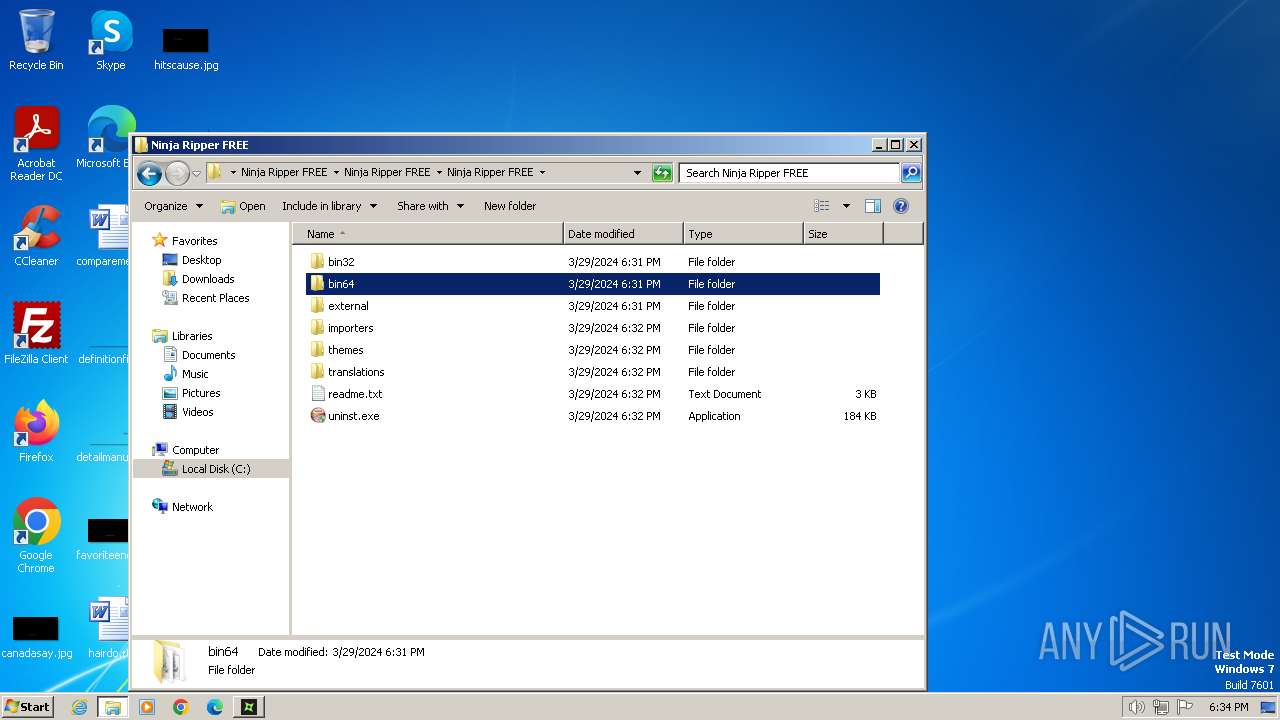
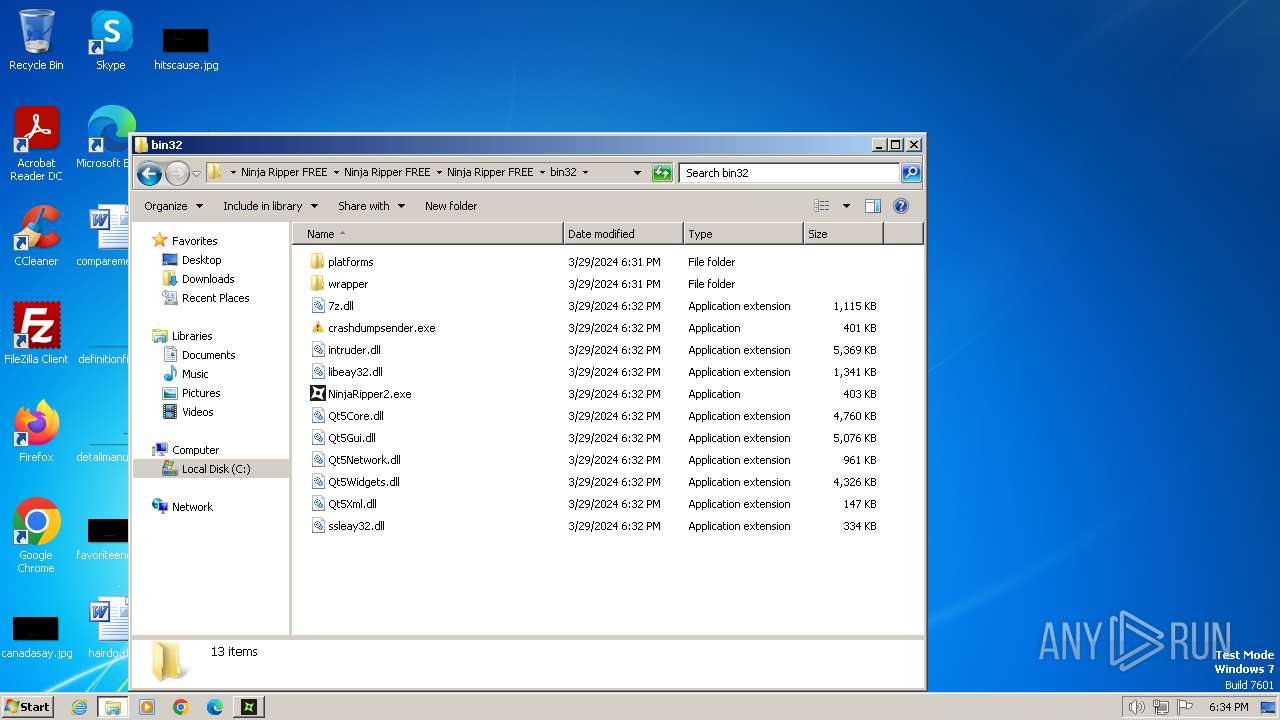
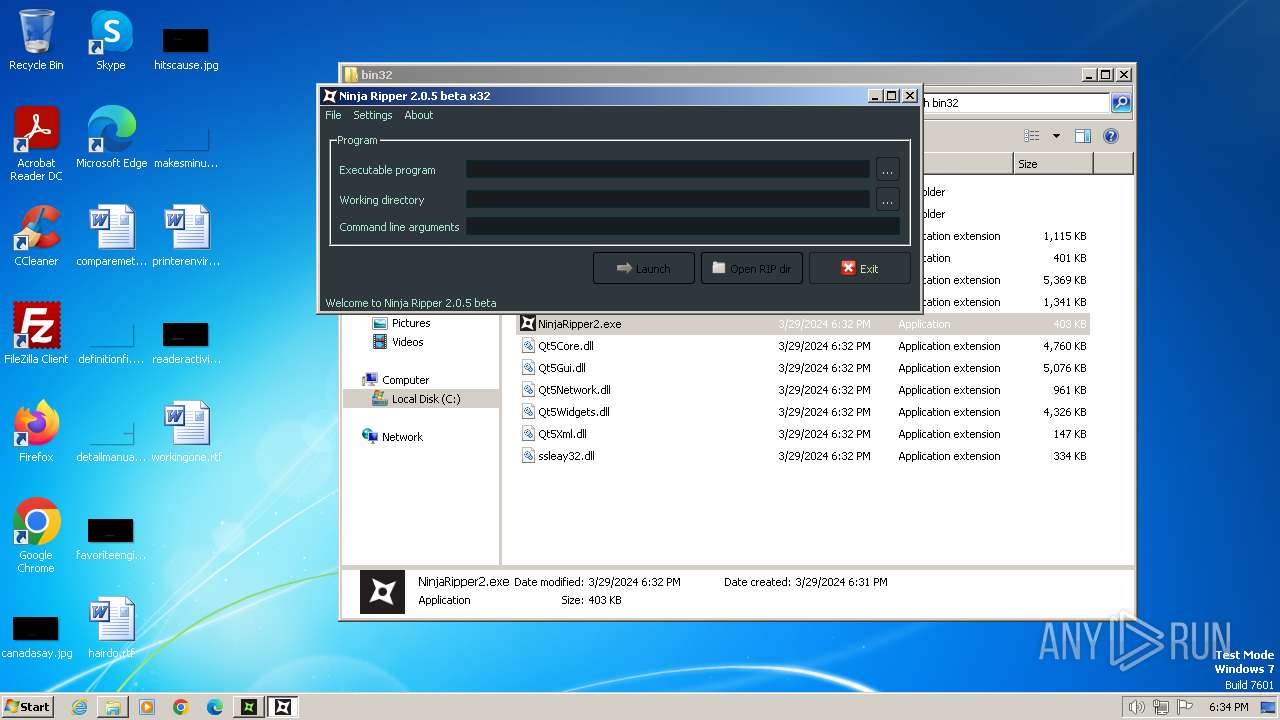
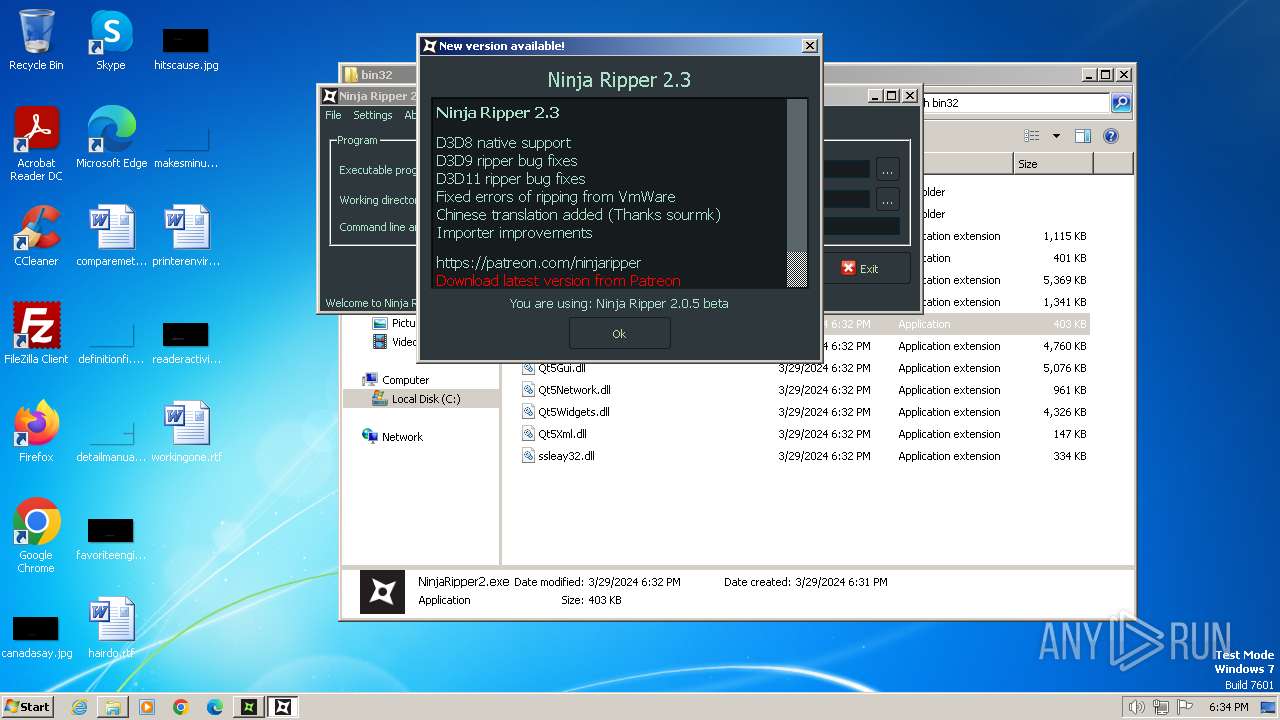
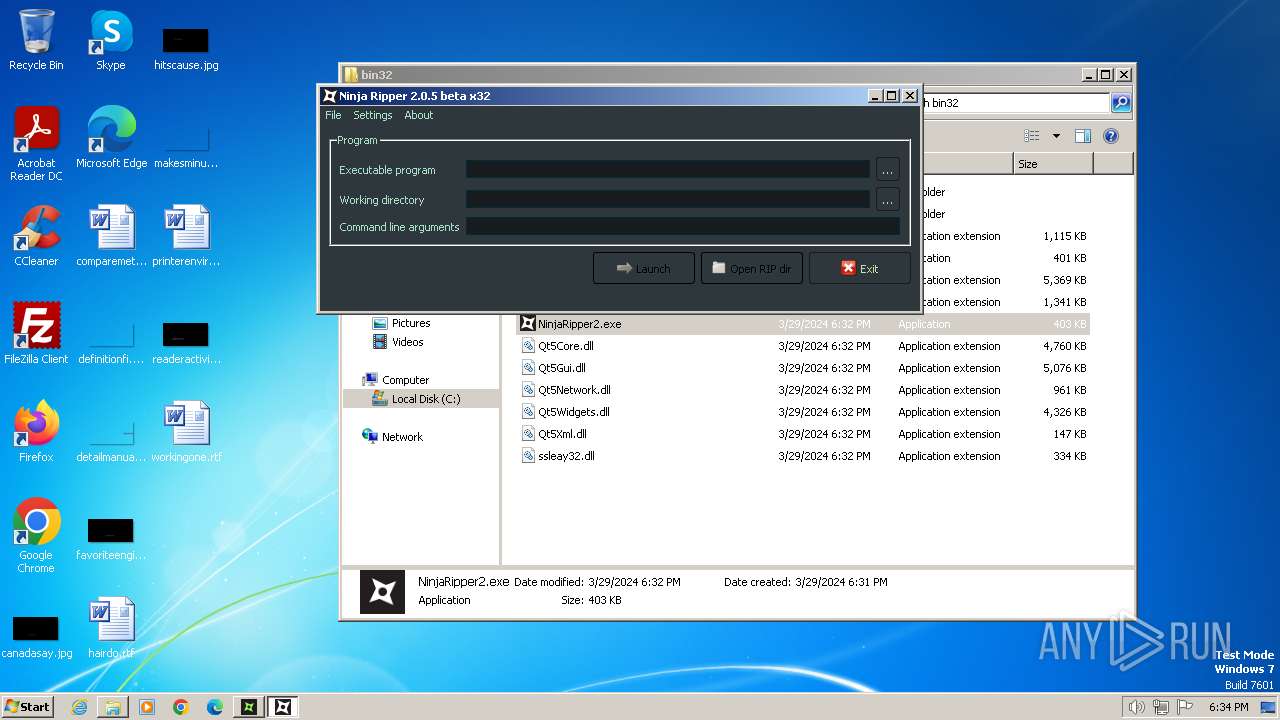
NinjaRipper2.exe | NR[3888]: WorkDir: C:\Program Files\Ninja Ripper FREE\Ninja Ripper FREE\Ninja Ripper FREE\bin32
|
NinjaRipper2.exe | NR[3888]: New QtPlugin dir=C:\Program Files\Ninja Ripper FREE\Ninja Ripper FREE\Ninja Ripper FREE\bin32\
|
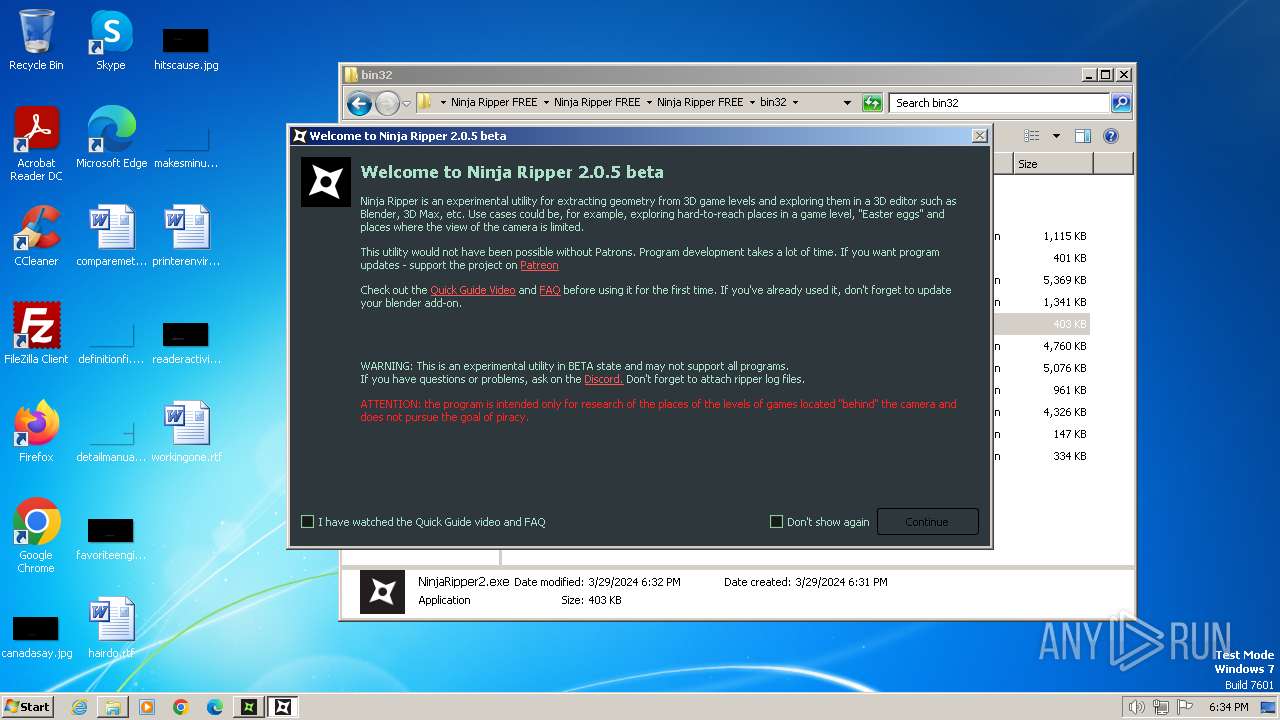
NinjaRipper2.exe | NR[3888]: ****NinjaRipper2****
|
NinjaRipper2.exe | NR[3888]: Pid=3136
|
NinjaRipper2.exe | NR[3888]: Exe: C:\Program Files\Ninja Ripper FREE\Ninja Ripper FREE\Ninja Ripper FREE\bin32\NinjaRipper2.exe
|
NinjaRipper2.exe | NR[3888]: New QtPlugin dir=C:\Program Files\Ninja Ripper FREE\Ninja Ripper FREE\Ninja Ripper FREE\bin32\platforms
|
NinjaRipper2.exe | NR[3888]: CmdLine: "C:\Program Files\Ninja Ripper FREE\Ninja Ripper FREE\Ninja Ripper FREE\bin32\NinjaRipper2.exe"
|