| File name: | TabularEditor.2.25.0.Installer 1.msi |
| Full analysis: | https://app.any.run/tasks/ec45c847-6cce-4b5f-8719-1c91d91da454 |
| Verdict: | Malicious activity |
| Analysis date: | January 20, 2025, 07:47:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Create Time/Date: Mon Jun 21 07:00:00 1999, Name of Creating Application: Windows Installer, Security: 1, Code page: 1252, Template: Intel;1033, Number of Pages: 200, Revision Number: {C2557C06-7F50-4A74-BCAA-C167C2FC77F3}, Title: Tabular Editor Installer, Author: Daniel Otykier, Number of Words: 2, Last Saved Time/Date: Fri Jul 5 10:25:22 2024, Last Printed: Fri Jul 5 10:25:22 2024 |
| MD5: | 367BF7EA38A681F0FC49A11846703D4A |
| SHA1: | 0665FB473DD031E9FB30F5157C246DD919569E98 |
| SHA256: | 150E73F4B1532A36482517EB7BB04592713F8A83E48A4DF4ABF007597E49B0FB |
| SSDEEP: | 98304:AiRM4VSFN3tKSPaK8oqX6AxvV9slX4X4H2XHaH/z8u+DQRRoBswgTAxscshorqJM:a3V5P72 |
MALICIOUS
Opens a text file (SCRIPT)
- msiexec.exe (PID: 6388)
Accesses environment variables (SCRIPT)
- msiexec.exe (PID: 6388)
SUSPICIOUS
Process drops legitimate windows executable
- msiexec.exe (PID: 5964)
- msiexec.exe (PID: 5920)
Checks Windows Trust Settings
- msiexec.exe (PID: 5920)
Executes as Windows Service
- VSSVC.exe (PID: 712)
Creates FileSystem object to access computer's file system (SCRIPT)
- msiexec.exe (PID: 6388)
Writes binary data to a Stream object (SCRIPT)
- msiexec.exe (PID: 6388)
Reads data from a binary Stream object (SCRIPT)
- msiexec.exe (PID: 6388)
Executable content was dropped or overwritten
- TabularEditor.exe (PID: 4516)
Reads security settings of Internet Explorer
- TabularEditor.exe (PID: 4516)
INFO
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5964)
The sample compiled with english language support
- msiexec.exe (PID: 5964)
- msiexec.exe (PID: 5920)
Checks supported languages
- msiexec.exe (PID: 5920)
- msiexec.exe (PID: 6184)
- msiexec.exe (PID: 6332)
- TabularEditor.exe (PID: 4516)
Reads the computer name
- msiexec.exe (PID: 6184)
- msiexec.exe (PID: 5920)
- msiexec.exe (PID: 6332)
- TabularEditor.exe (PID: 4516)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5964)
- msiexec.exe (PID: 5920)
Create files in a temporary directory
- msiexec.exe (PID: 6184)
Manages system restore points
- SrTasks.exe (PID: 836)
Reads the software policy settings
- msiexec.exe (PID: 5964)
Reads the machine GUID from the registry
- msiexec.exe (PID: 5920)
- TabularEditor.exe (PID: 4516)
Creates files or folders in the user directory
- msiexec.exe (PID: 5920)
The process uses the downloaded file
- TabularEditor.exe (PID: 4516)
Checks proxy server information
- TabularEditor.exe (PID: 4516)
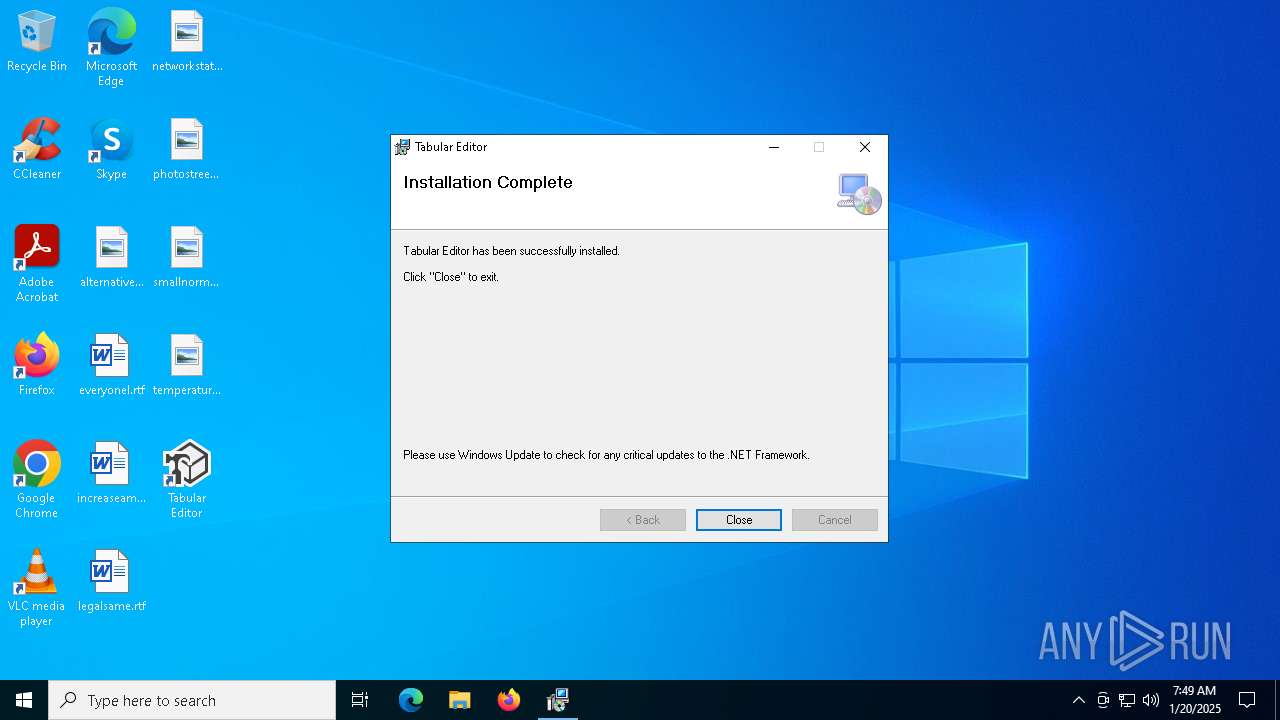
Manual execution by a user
- TabularEditor.exe (PID: 4516)
Creates files in the program directory
- TabularEditor.exe (PID: 4516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (90.2) |
|---|---|---|
| .msp | | | Windows Installer Patch (8.4) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CreateDate: | 1999:06:21 07:00:00 |
|---|---|
| Software: | Windows Installer |
| Security: | Password protected |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | Intel;1033 |
| Pages: | 200 |
| RevisionNumber: | {C2557C06-7F50-4A74-BCAA-C167C2FC77F3} |
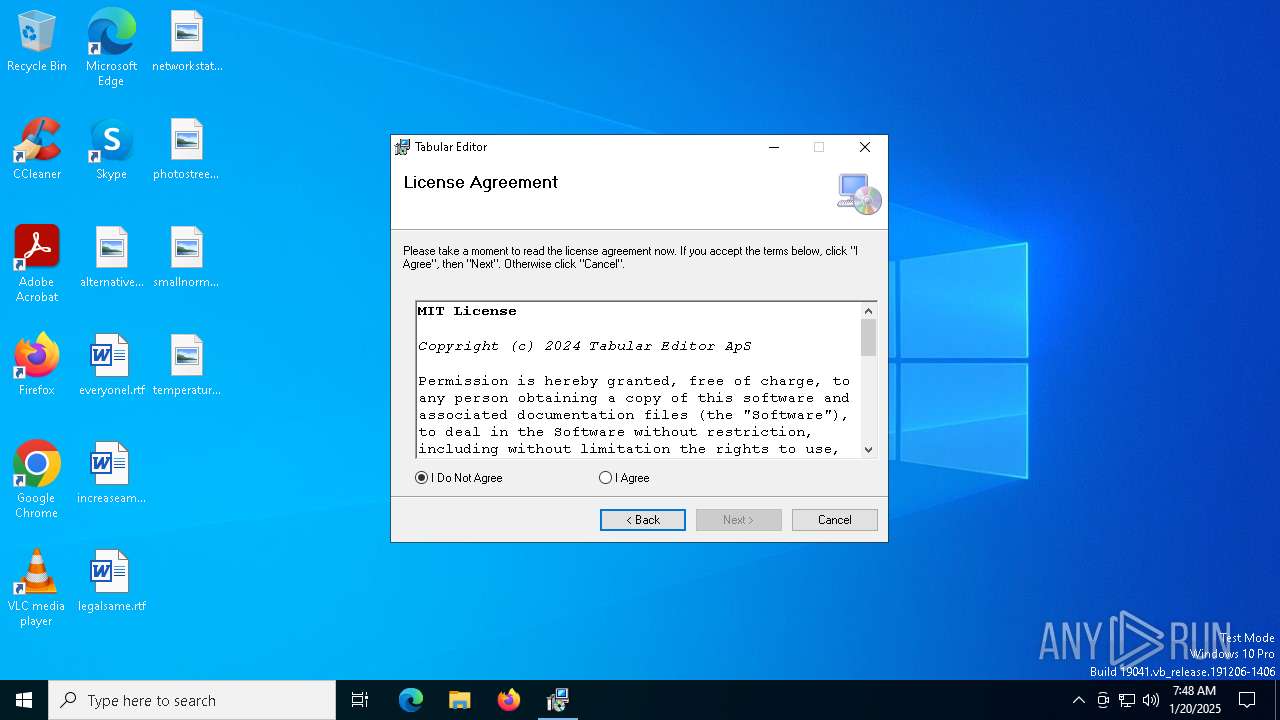
| Title: | Tabular Editor Installer |
| Subject: | - |
| Author: | Daniel Otykier |
| Keywords: | - |
| Comments: | - |
| Words: | 2 |
| ModifyDate: | 2024:07:05 10:25:22 |
| LastPrinted: | 2024:07:05 10:25:22 |
Total processes
140
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 712 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 836 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
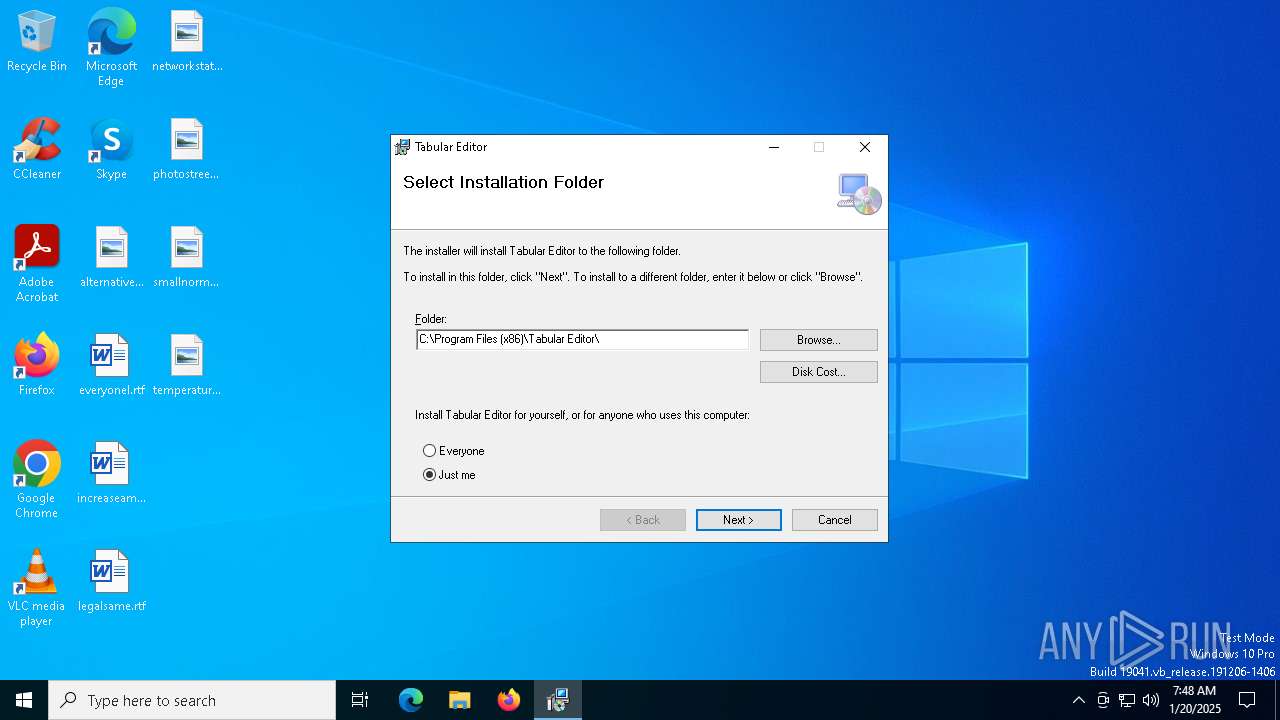
| 4516 | "C:\Program Files (x86)\Tabular Editor\TabularEditor.exe" | C:\Program Files (x86)\Tabular Editor\TabularEditor.exe | explorer.exe | ||||||||||||
User: admin Company: Tabular Editor ApS Integrity Level: MEDIUM Description: Tabular Editor Exit code: 0 Version: 2.25.8952.22276 Modules
| |||||||||||||||
| 5592 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5920 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5964 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\TabularEditor.2.25.0.Installer 1.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6184 | C:\Windows\syswow64\MsiExec.exe -Embedding FE66D584323904A6F74ECCBCD2D9D51C C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6332 | C:\Windows\syswow64\MsiExec.exe -Embedding C2B07C4AD6507129C24C25BB6FD135C6 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6388 | C:\Windows\syswow64\MsiExec.exe -Embedding F02707B7290468B14F8771131C391B3F E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 100
Read events
10 782
Write events
301
Delete events
17
Modification events
| (PID) Process: | (5920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000004DBF23BA0F6BDB012017000094140000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000242326BA0F6BDB012017000094140000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000010428ABA0F6BDB012017000094140000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000010428ABA0F6BDB012017000094140000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000026CE93BA0F6BDB012017000094140000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000000A0C8FBA0F6BDB012017000094140000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000364E19BB0F6BDB012017000094140000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000C1171EBB0F6BDB012017000098150000E8030000010000000000000000000000BB3F595E2A5BAC44BFE4EA804DC936D200000000000000000000000000000000 | |||
| (PID) Process: | (5920) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (712) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 480000000000000047783FBB0F6BDB01C8020000E00E0000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
22
Suspicious files
29
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5920 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5920 | msiexec.exe | C:\Windows\Installer\1448cf.msi | — | |
MD5:— | SHA256:— | |||
| 5964 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | binary | |
MD5:DBACECDF54C3C8FF919A6EE4E00CDB3D | SHA256:0D8DC7110F42F84D533F597DA0EB4F3C73BEEB15E81DC2AACF9BA3D721EE597A | |||
| 5964 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | binary | |
MD5:FD1272EA49FE2C7C67465E223159FD56 | SHA256:01DDC9CAF10C9190399639A0199C31FFDA3DCC3C5CFB9BAA6F64167135DF481D | |||
| 5920 | msiexec.exe | C:\Windows\Installer\MSI4DC2.tmp | executable | |
MD5:B77A2A2768B9CC78A71BBFFB9812B978 | SHA256:F74C97B1A53541B059D3BFAFE41A79005CE5065F8210D7DE9F1B600DC4E28AA0 | |||
| 5964 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6489.tmp | executable | |
MD5:B77A2A2768B9CC78A71BBFFB9812B978 | SHA256:F74C97B1A53541B059D3BFAFE41A79005CE5065F8210D7DE9F1B600DC4E28AA0 | |||
| 5964 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6621.tmp | executable | |
MD5:B77A2A2768B9CC78A71BBFFB9812B978 | SHA256:F74C97B1A53541B059D3BFAFE41A79005CE5065F8210D7DE9F1B600DC4E28AA0 | |||
| 5920 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{5e593fbb-5b2a-44ac-bfe4-ea804dc936d2}_OnDiskSnapshotProp | binary | |
MD5:C2E83E5F1415EE68F31151E7D04D1562 | SHA256:C34CC8FEB6A428E19168A0AE5E9C331B723921100CED7B3F33CEB7E18C948118 | |||
| 5920 | msiexec.exe | C:\Windows\Installer\MSI4D44.tmp | executable | |
MD5:B77A2A2768B9CC78A71BBFFB9812B978 | SHA256:F74C97B1A53541B059D3BFAFE41A79005CE5065F8210D7DE9F1B600DC4E28AA0 | |||
| 6332 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CFG4DB1.tmp | xml | |
MD5:60FB4130A1EAFD4452919F271B3866E5 | SHA256:52545F3C621CC2676F4F550938D8F6771FAAD209401CF054BC72F92FBB52E7C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
36
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5964 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
5964 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDDXdiRAXZ6AmEHenYA%3D%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7012 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7012 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6564 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5856 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5964 | msiexec.exe | 104.18.21.226:80 | ocsp.globalsign.com | CLOUDFLARENET | — | whitelisted |
5856 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.23.227.215:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
5064 | SearchApp.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |