| File name: | Xenos64.exe |
| Full analysis: | https://app.any.run/tasks/487cad6b-951a-467c-9f69-93ac880d65e7 |
| Verdict: | Malicious activity |
| Analysis date: | October 08, 2023, 19:48:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 91E92810B13CEF03EA8FE2D30B51272C |
| SHA1: | 3F3F74B2CE54BACD3C5A3E53515B8DA4B5DDF533 |
| SHA256: | 1506FFB2EBD0B2EBF87875DA6F93535C80119202A536A9BFF0F3D4635068C61E |
| SSDEEP: | 49152:7UxpHfwXQ7rNMum4mcXAnTJC9oDC0/8xe5wKrERQXzhGJ6xoobu:AzHf4wNMcwTJIoDv5UWUEDu |
MALICIOUS
Drops the executable file immediately after the start
- Xenos64.exe (PID: 3444)
Application was dropped or rewritten from another process
- HOST.EXE (PID: 3136)
SUSPICIOUS
Reads the Internet Settings
- Xenos64.exe (PID: 3444)
The process creates files with name similar to system file names
- Xenos64.exe (PID: 3444)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 4024)
- Xenos64.exe (PID: 3444)
- HOST.EXE (PID: 3136)
Reads the computer name
- wmpnscfg.exe (PID: 4024)
- Xenos64.exe (PID: 3444)
- HOST.EXE (PID: 3136)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 4024)
- HOST.EXE (PID: 3136)
Create files in a temporary directory
- Xenos64.exe (PID: 3444)
Reads Environment values
- HOST.EXE (PID: 3136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (19.1) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (4) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:07:03 11:05:04+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 31232 |
| InitializedDataSize: | 1607680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3248 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3136 | "C:\Users\admin\AppData\Local\Temp\HOST.EXE" | C:\Users\admin\AppData\Local\Temp\HOST.EXE | Xenos64.exe | ||||||||||||
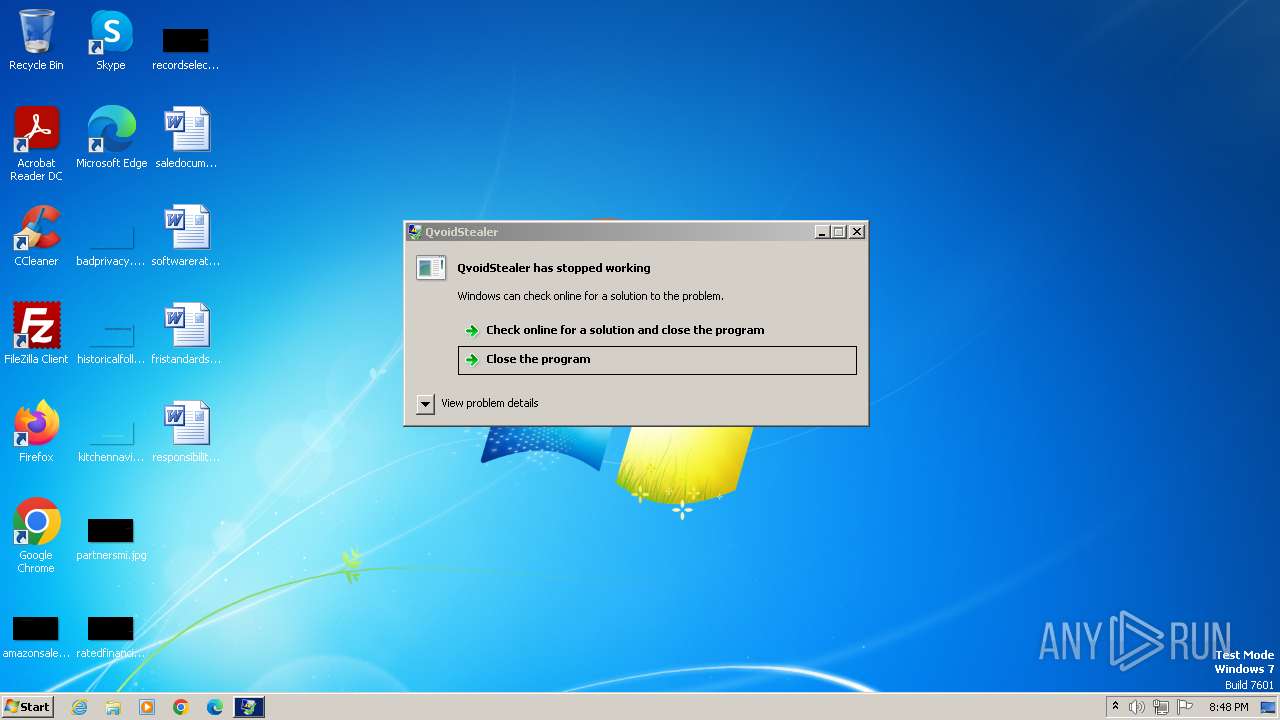
User: admin Integrity Level: MEDIUM Description: QvoidStealer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3444 | "C:\Users\admin\AppData\Local\Temp\Xenos64.exe" | C:\Users\admin\AppData\Local\Temp\Xenos64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 4024 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
826
Read events
807
Write events
16
Delete events
3
Modification events
| (PID) Process: | (4024) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{4F7ED865-3ADE-42F3-930E-F06E409B41EE}\{AFD3766B-3E25-4009-AAC0-F5159BBBEBD0} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4024) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{4F7ED865-3ADE-42F3-930E-F06E409B41EE} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4024) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{BE032C21-AD49-413C-B1FC-9D07019A5544} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3444) Xenos64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3444) Xenos64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3444) Xenos64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3444) Xenos64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3444 | Xenos64.exe | C:\Users\admin\AppData\Local\Temp\HOST.EXE | executable | |
MD5:3E0B5ED4C5560CE845C4B8C83B5DBA91 | SHA256:65C08267680EEE6CB0563668233BF1D2C0242D9FED43F8B18355FAA86FFB0E51 | |||
| 3444 | Xenos64.exe | C:\Users\admin\AppData\Local\Temp\XENOS.EXE | executable | |
MD5:E2BE25EC1C860B98EA99A835CC981D28 | SHA256:922163713B973CF8C4AD80F16CF69305ED0CA319B314E7EC8AE1982ED5F2A9ED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Threats
Process | Message |
|---|---|
Xenos64.exe | C:\Users\admin\AppData\Local\Temp\HOST.EXE |
Xenos64.exe | C:\Users\admin\AppData\Local\Temp\XENOS.EXE |