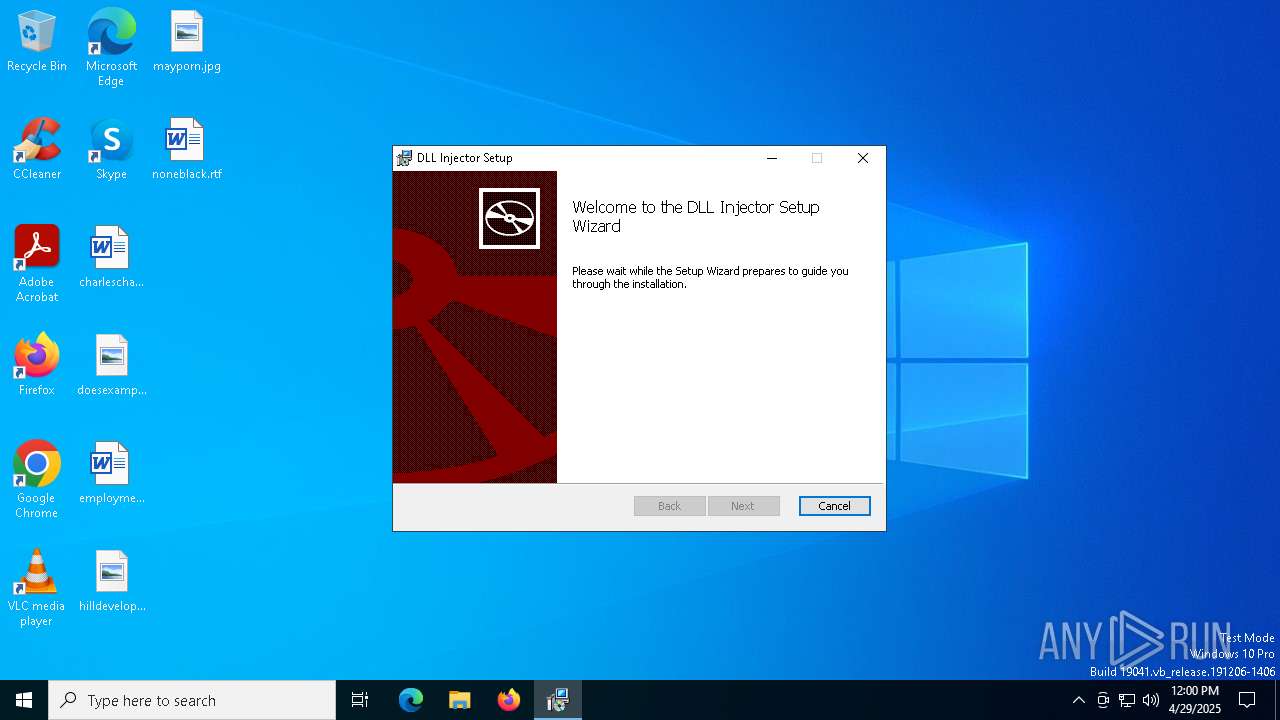
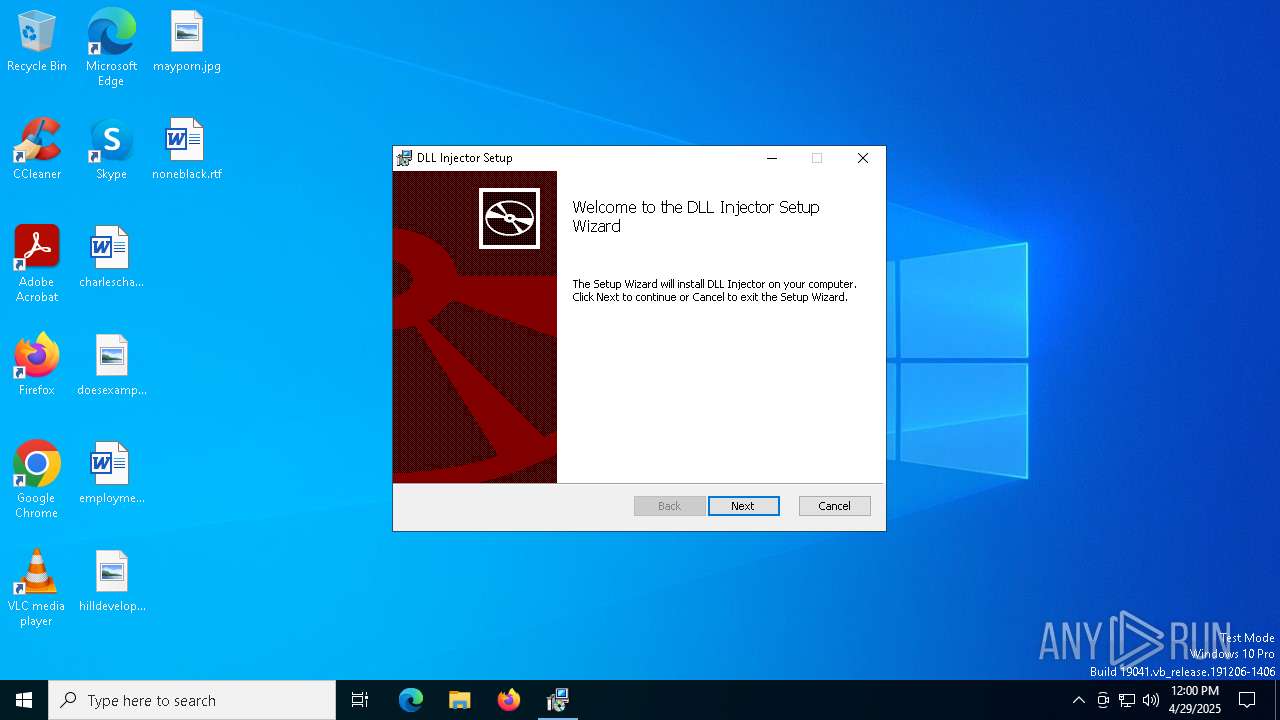
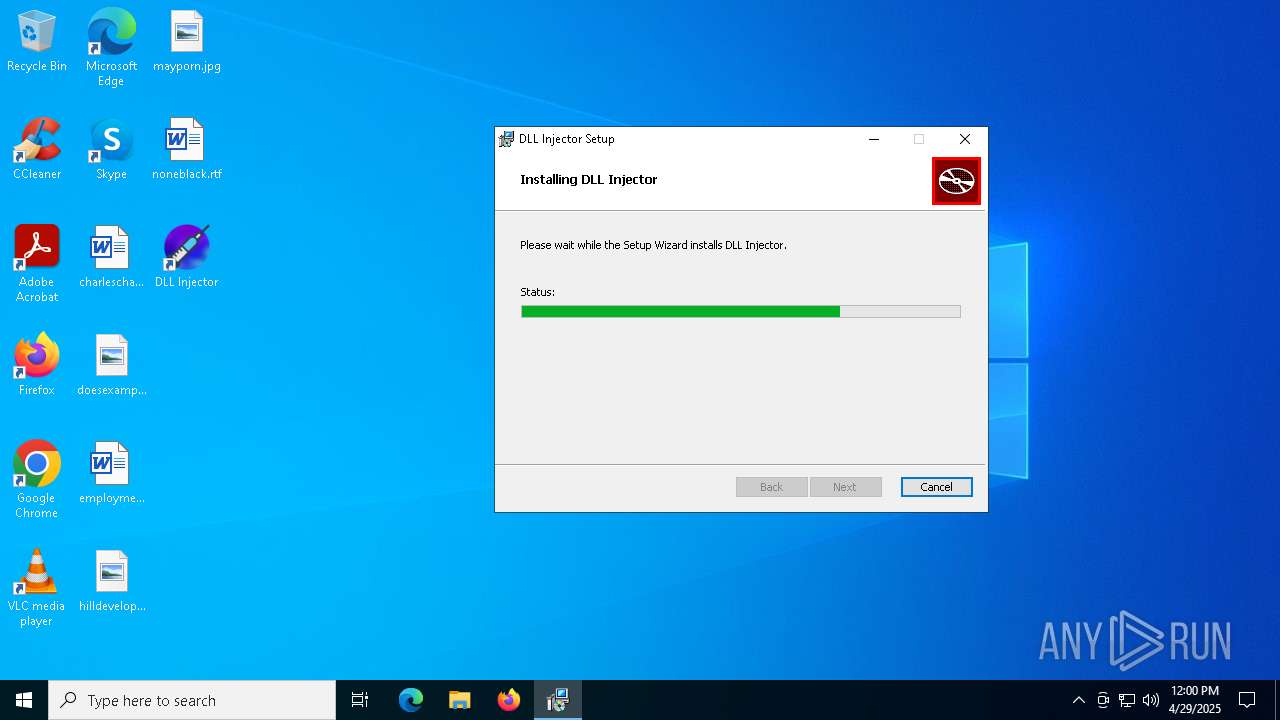
| File name: | DLL Injector_2.3.0_x86_en-US.msi |
| Full analysis: | https://app.any.run/tasks/378bd424-c284-4915-8970-c21c07aacb96 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 11:59:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: DLL Injector, Author: dllinjector, Keywords: Installer, Comments: This installer database contains the logic and data required to install DLL Injector., Template: Intel;0, Revision Number: {93458713-5CFA-4683-84C8-FCD0F4BAB129}, Create Time/Date: Sat Apr 26 11:05:00 2025, Last Saved Time/Date: Sat Apr 26 11:05:00 2025, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.1.8722), Security: 2 |
| MD5: | C6A084918010E2FC3E1503783F425722 |
| SHA1: | F43C3EC39BBBD697EB4D9A7952BDC6F7DB67372C |
| SHA256: | 1505ED92A9E341F0B0450A3525D1625D201E2931D2DA189354C3C6C66DBE43B8 |
| SSDEEP: | 98304:SKmuY8OxVhcoDdKjZHOAPNSeia21V8++FqwAkcGL5MfHQlrC8DPsr31A02egmrai:mZl9/xn |
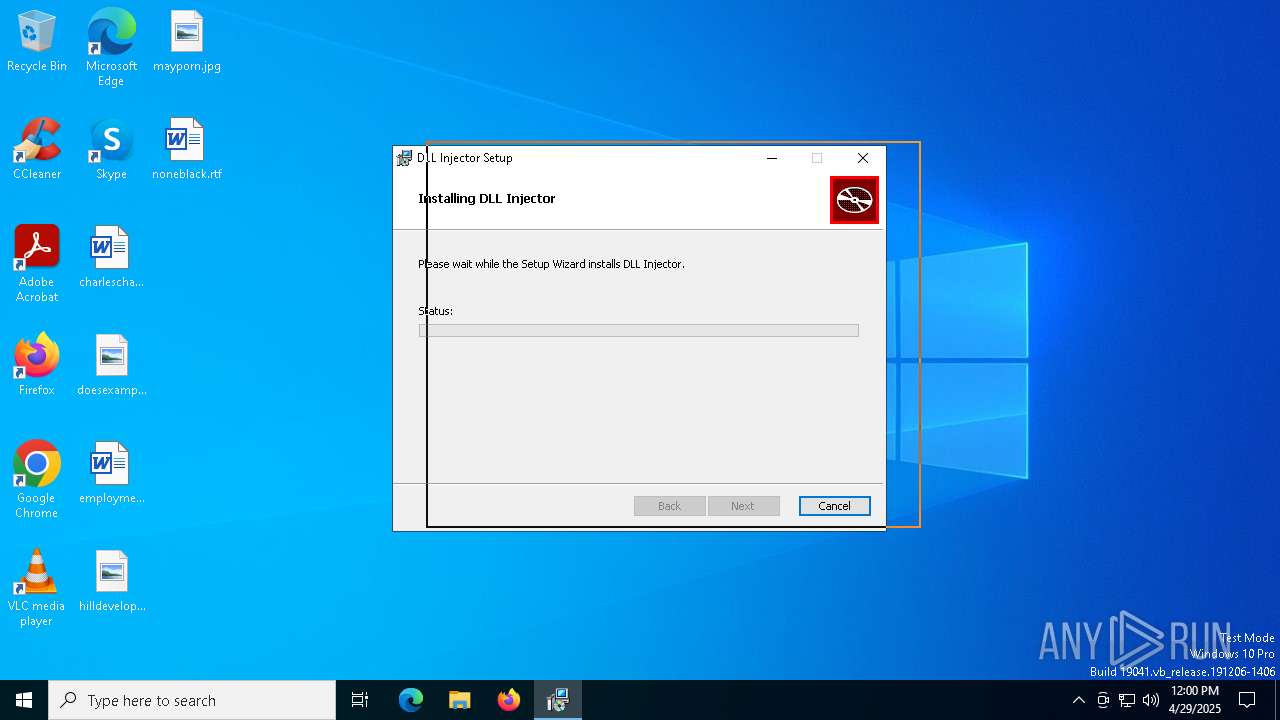
MALICIOUS
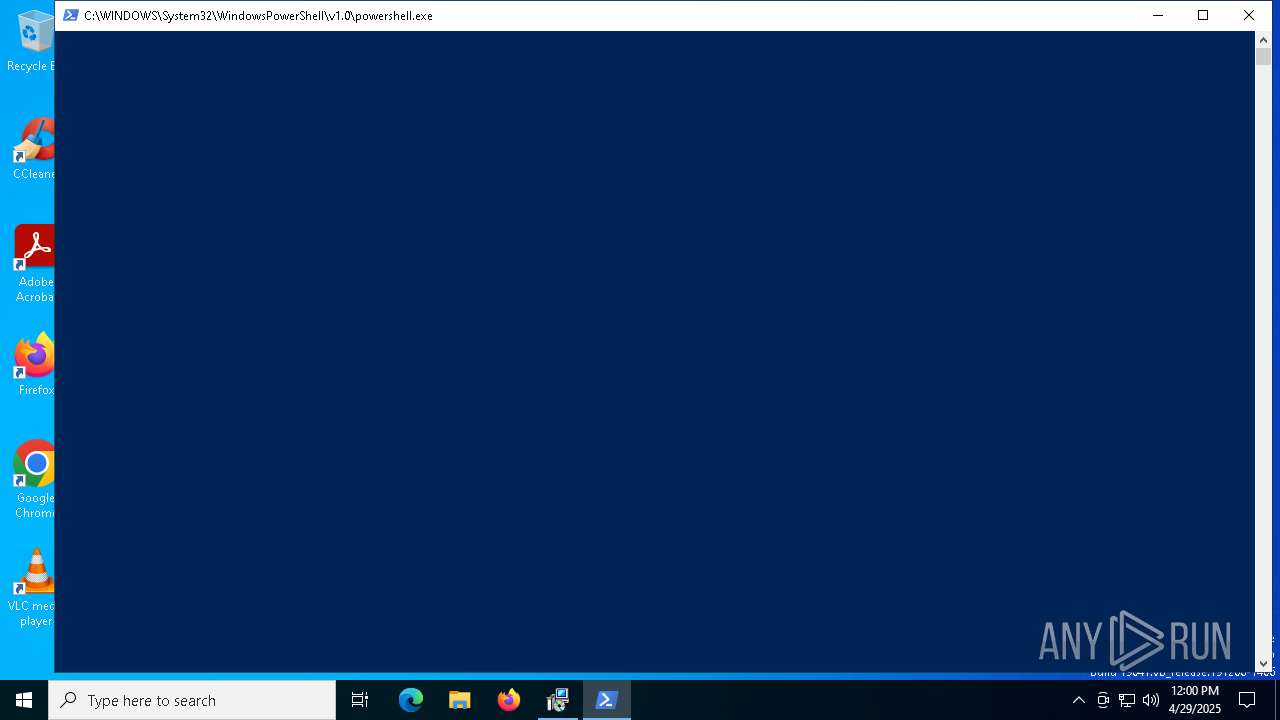
Run PowerShell with an invisible window
- powershell.exe (PID: 6676)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 5392)
Downloads file from URI via Powershell
- powershell.exe (PID: 6676)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 4776)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 4776)
Starts process via Powershell
- powershell.exe (PID: 6676)
Manipulates environment variables
- powershell.exe (PID: 6676)
Executable content was dropped or overwritten
- powershell.exe (PID: 6676)
- MicrosoftEdgeWebview2Setup.exe (PID: 856)
- MicrosoftEdgeUpdate.exe (PID: 6768)
Process drops legitimate windows executable
- MicrosoftEdgeWebview2Setup.exe (PID: 856)
- powershell.exe (PID: 6676)
- MicrosoftEdgeUpdate.exe (PID: 6768)
Starts a Microsoft application from unusual location
- MicrosoftEdgeUpdate.exe (PID: 6768)
- MicrosoftEdgeWebview2Setup.exe (PID: 856)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 6768)
INFO
Checks supported languages
- msiexec.exe (PID: 4776)
- msiexec.exe (PID: 5256)
An automatically generated document
- msiexec.exe (PID: 5936)
Reads the computer name
- msiexec.exe (PID: 4776)
- msiexec.exe (PID: 5256)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5936)
- msiexec.exe (PID: 4776)
Manages system restore points
- SrTasks.exe (PID: 6424)
The sample compiled with english language support
- MicrosoftEdgeWebview2Setup.exe (PID: 856)
- MicrosoftEdgeUpdate.exe (PID: 6768)
- powershell.exe (PID: 6676)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | DLL Injector |
| Author: | dllinjector |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install DLL Injector. |
| Template: | Intel;0 |
| RevisionNumber: | {93458713-5CFA-4683-84C8-FCD0F4BAB129} |
| CreateDate: | 2025:04:26 11:05:00 |
| ModifyDate: | 2025:04:26 11:05:00 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.1.8722) |
| Security: | Read-only recommended |
Total processes
150
Monitored processes
19
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe" /silent /install | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Setup Version: 1.3.195.49 Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" -Embedding | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.49 Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /regserver | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.195.49 Modules
| |||||||||||||||
| 2644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2656 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.49\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.49\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.49 Modules
| |||||||||||||||
| 4528 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /handoff "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=false" /installsource otherinstallcmd /sessionid "{F9481BC9-D5F6-4DE2-99AC-6FD9E59EF9C4}" /silent | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.49 Modules
| |||||||||||||||
| 4620 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4776 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 643
Read events
10 731
Write events
869
Delete events
43
Modification events
| (PID) Process: | (4776) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000FF86FB41FEB8DB01A8120000F4180000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4776) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000AD70B641FEB8DB01A8120000F4180000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4776) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000CCC0B841FEB8DB01A8120000F4180000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4776) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000003624F941FEB8DB01A8120000F4180000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4776) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000003624F941FEB8DB01A8120000F4180000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4776) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000093EAFD41FEB8DB01A8120000F4180000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4776) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (5392) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000CB7D7742FEB8DB011015000054140000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5392) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000CB7D7742FEB8DB01101500005C060000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5392) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000CB7D7742FEB8DB011015000028150000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
207
Suspicious files
14
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4776 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4776 | msiexec.exe | C:\Windows\Installer\112f89.msi | executable | |
MD5:C6A084918010E2FC3E1503783F425722 | SHA256:1505ED92A9E341F0B0450A3525D1625D201E2931D2DA189354C3C6C66DBE43B8 | |||
| 4776 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:B7A34490B643FBC8C1D96F6922D4DCB1 | SHA256:47A6E1A2F133DF41313EED9A89A4A4AEC5D2F981B1DE43AEAE3B1BD7456EB0BB | |||
| 5936 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIDA35.tmp | executable | |
MD5:CFBB8568BD3711A97E6124C56FCFA8D9 | SHA256:7F47D98AB25CFEA9B3A2E898C3376CC9BA1CD893B4948B0C27CAA530FD0E34CC | |||
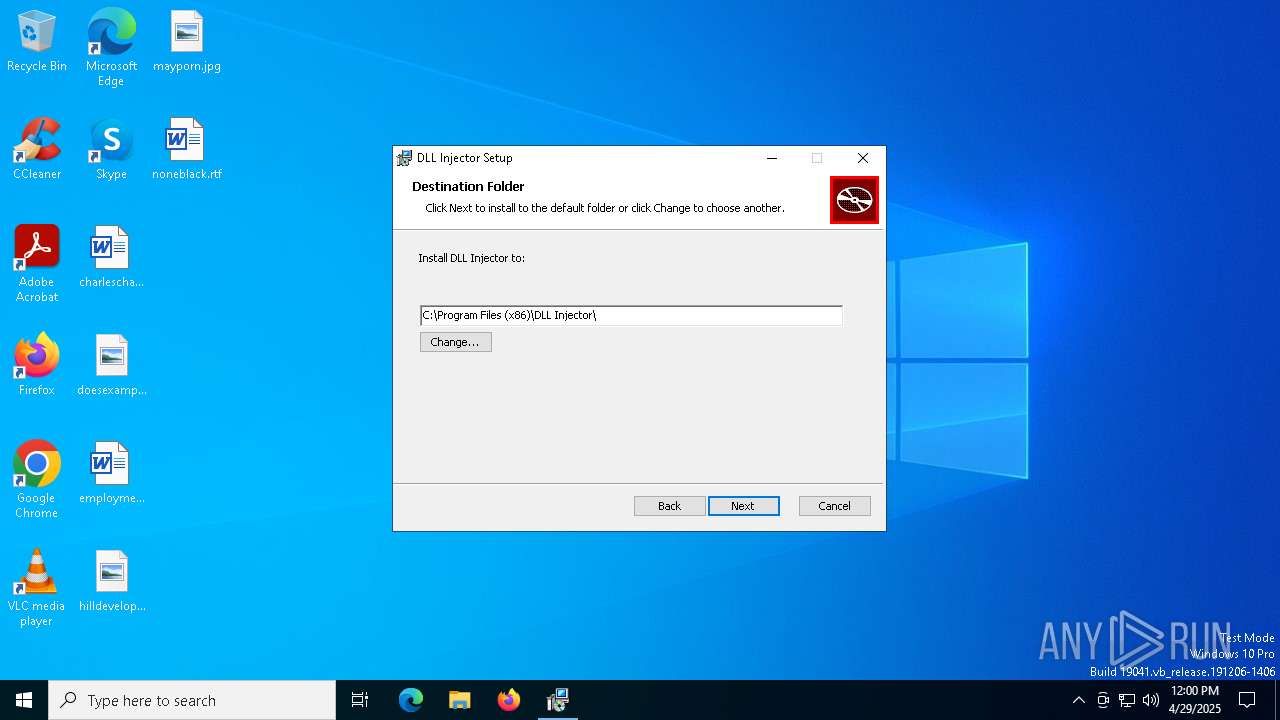
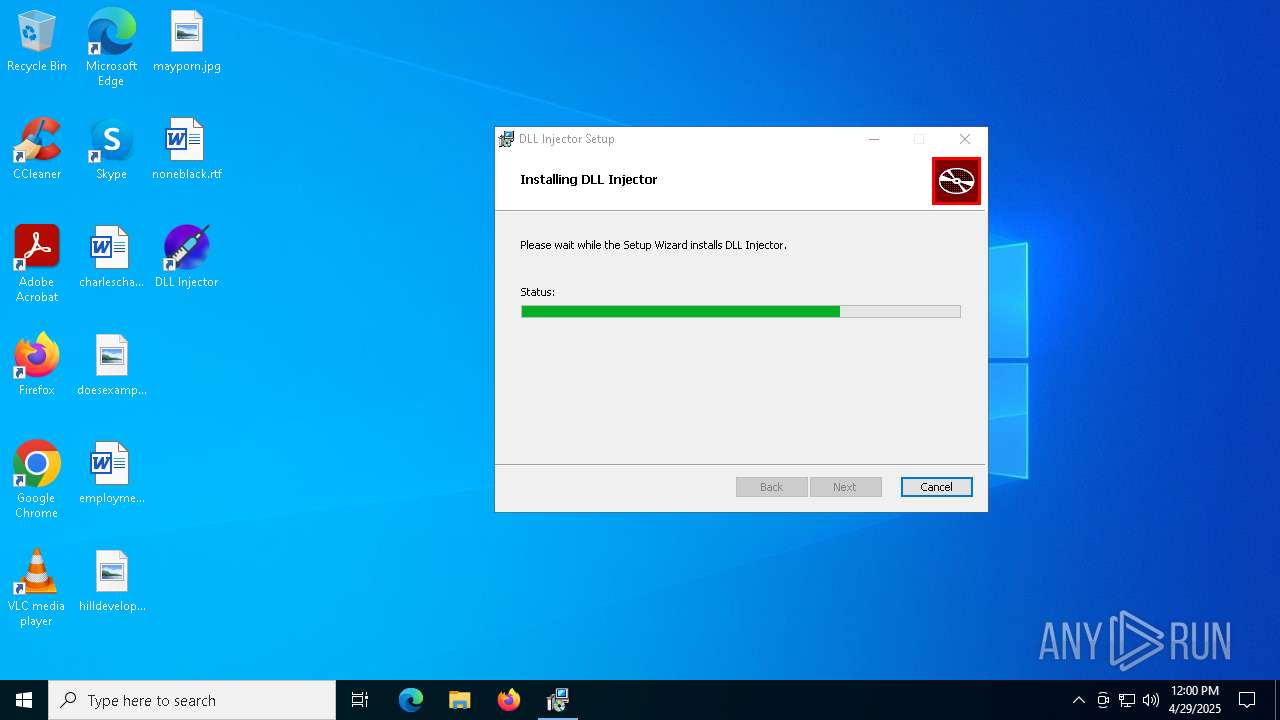
| 4776 | msiexec.exe | C:\Program Files (x86)\DLL Injector\DLL Injector.exe | executable | |
MD5:464F08B835F06868D6018CD2BFE1D354 | SHA256:7E5A4A5ECAC96C314D15C7B7F8897BD22B012E83222ED6D6F063937FD5A8B763 | |||
| 4776 | msiexec.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\DLL Injector\DLL Injector.lnk | binary | |
MD5:3115CD3B05E308E1010E54D1B66829DD | SHA256:A1ACEDA2FC703F6801A656DFB8098D42F3F48393481250E99C4241150AB8C6C1 | |||
| 4776 | msiexec.exe | C:\Program Files (x86)\DLL Injector\resources\x64-DLL-Injector.exe | executable | |
MD5:0085FA43C6EEBF59157932371F8CC923 | SHA256:26DA02B9C4D65B8F2D6596972630394DA4E862787E1F874642E6951D82DE26CF | |||
| 4776 | msiexec.exe | C:\Windows\Temp\~DF9E14F2A6AD889869.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 4776 | msiexec.exe | C:\Windows\Installer\{8CE606F6-65C7-4BAF-B349-666D84922F5D}\ProductIcon | image | |
MD5:6C883B19B0AAF17CE2D5813EF2C8F86B | SHA256:A3594272B1770553332858C93BD9F91BFF9437B5B33128A9D3D252DC87C458E0 | |||
| 4776 | msiexec.exe | C:\Program Files (x86)\DLL Injector\Uninstall DLL Injector.lnk | binary | |
MD5:1603CE4BBFE21027474607CB20217E66 | SHA256:ADCA8CC025CCAFB3BAEB3785C0317010AF3CF5A97B68932EBFA02FD6055FA672 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4988 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4988 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7240 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bef3bb0b-b1c2-4068-a2cd-1eae1dd922b4?P1=1746532841&P2=404&P3=2&P4=I5M350tpFsUgZ013QCCqiaewUwsIRhf0uHYialAw9EL1IZI4vfvju1Pn7FE%2fT1Rxf%2bOioTX2ScNELc9cBlpwSQ%3d%3d | unknown | — | — | whitelisted |
7240 | svchost.exe | GET | — | 199.232.210.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bef3bb0b-b1c2-4068-a2cd-1eae1dd922b4?P1=1746532841&P2=404&P3=2&P4=I5M350tpFsUgZ013QCCqiaewUwsIRhf0uHYialAw9EL1IZI4vfvju1Pn7FE%2fT1Rxf%2bOioTX2ScNELc9cBlpwSQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.25:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4988 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7240 | svchost.exe | Misc activity | ET INFO Packed Executable Download |