| URL: | https://hcu-client.com/download/hcu-client-v1-0-0-0362/?wpdmdl=667&refresh=5fd213ce2e7e91607603150 |
| Full analysis: | https://app.any.run/tasks/fa200e27-6a86-4e7d-b88f-afc05a72cc8f |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2020, 12:27:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4E5A846DF9ECDE27636D0BE78FEB111A |
| SHA1: | C70F55403B55A735D22EDE6F5D0F2E4961FA21E0 |
| SHA256: | 14F244008F88D1E7C94D153634C6918AE18ECF35EF99F941495E4B48560CF75D |
| SSDEEP: | 3:N86QNBl2BLGeBluUI2WADQHASAJVQk:26QM0PRgzJKk |
MALICIOUS
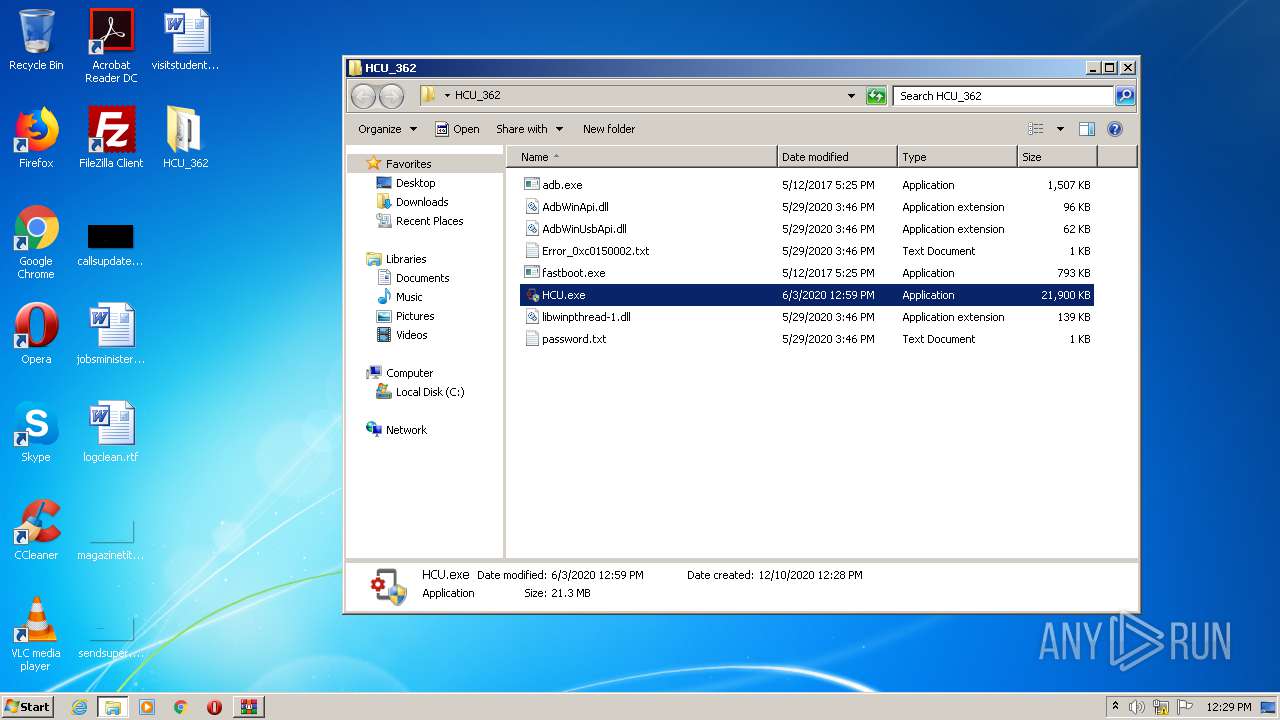
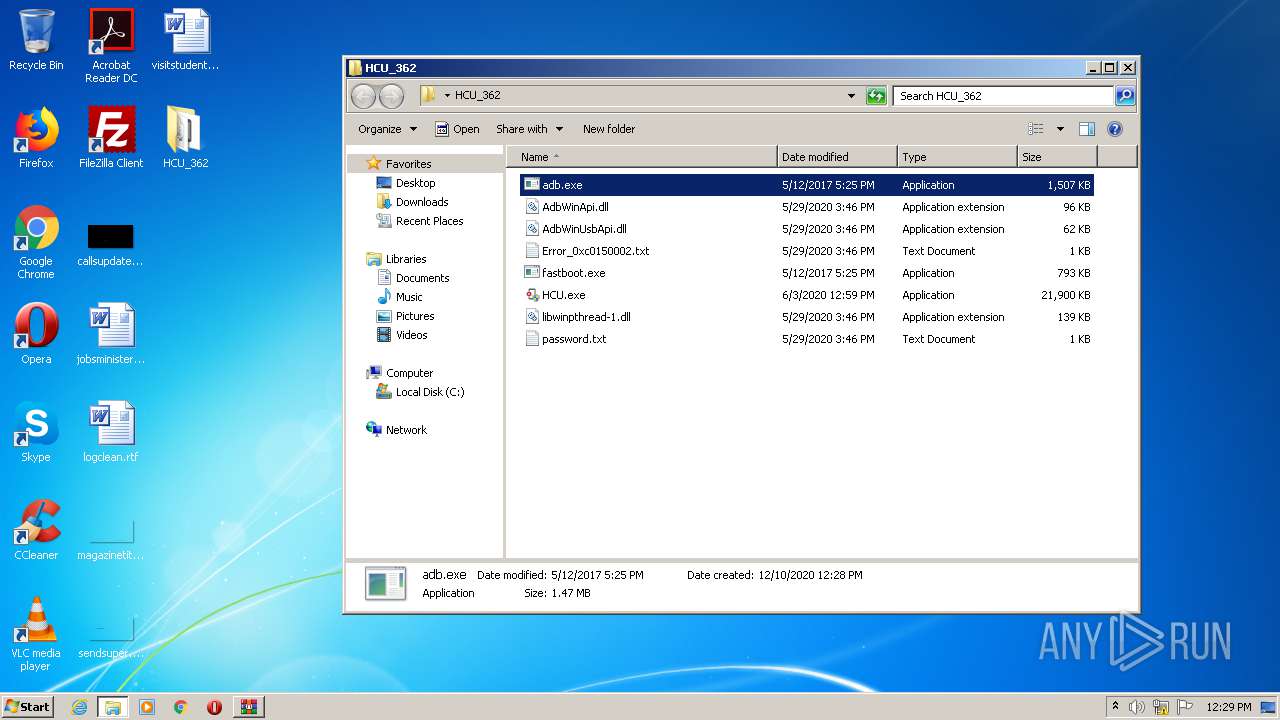
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 848)
- adb.exe (PID: 2568)
Application was dropped or rewritten from another process
- HCU.exe (PID: 2516)
- HCU.exe (PID: 4044)
- HCU.exe (PID: 3356)
- adb.exe (PID: 2568)
- HCU.exe (PID: 2296)
SUSPICIOUS
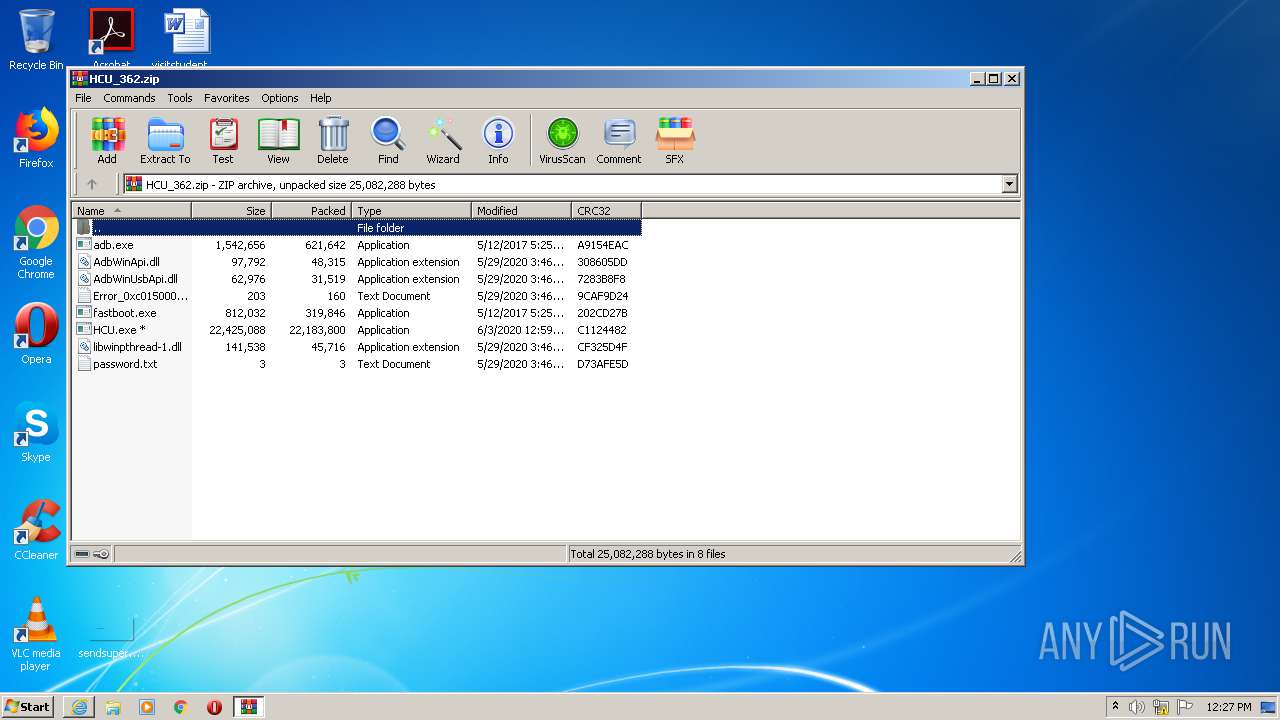
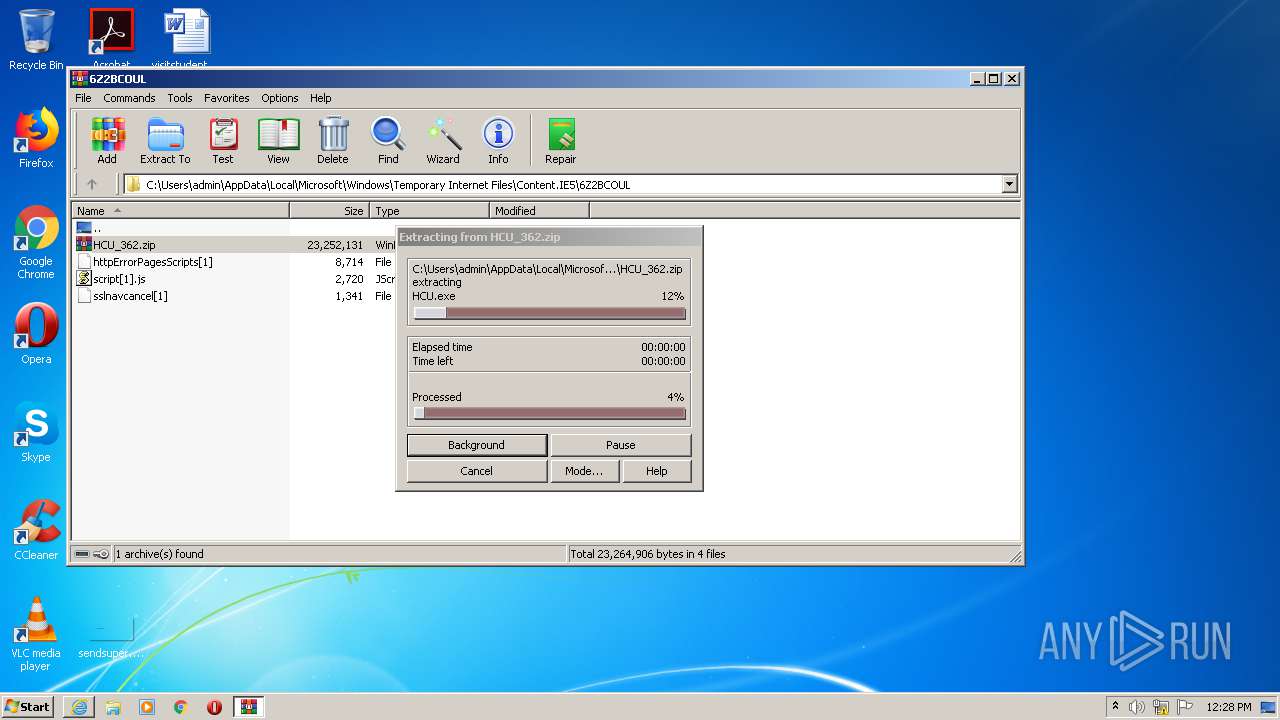
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1524)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 1524)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 1524)
Drops a file with too old compile date
- WinRAR.exe (PID: 1524)
INFO
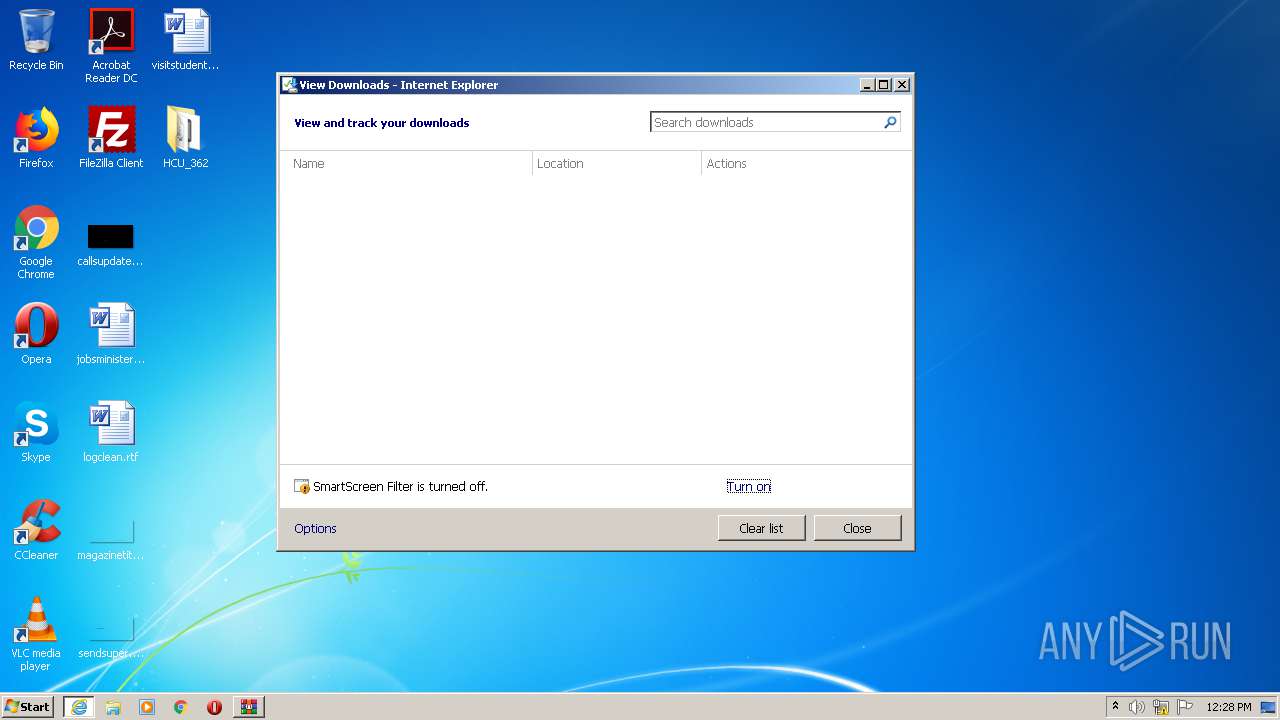
Changes internet zones settings
- iexplore.exe (PID: 2660)
Reads settings of System Certificates
- iexplore.exe (PID: 404)
- iexplore.exe (PID: 2660)
Creates files in the user directory
- iexplore.exe (PID: 2660)
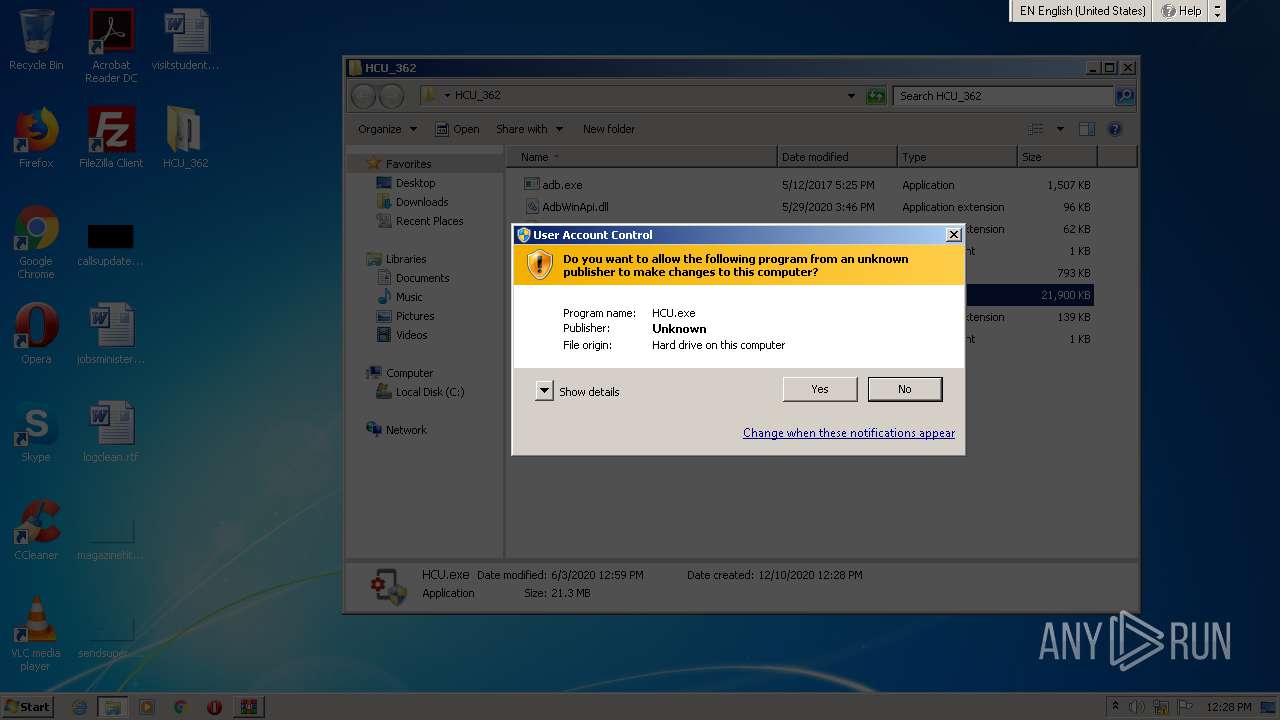
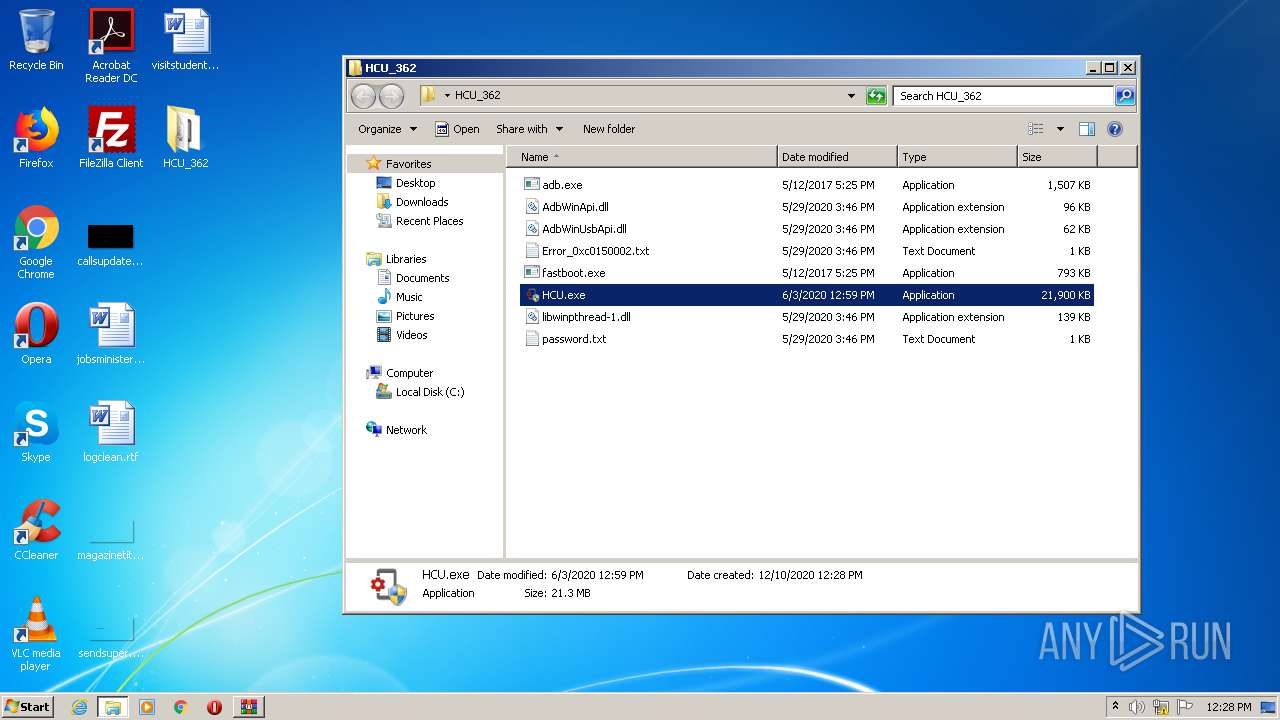
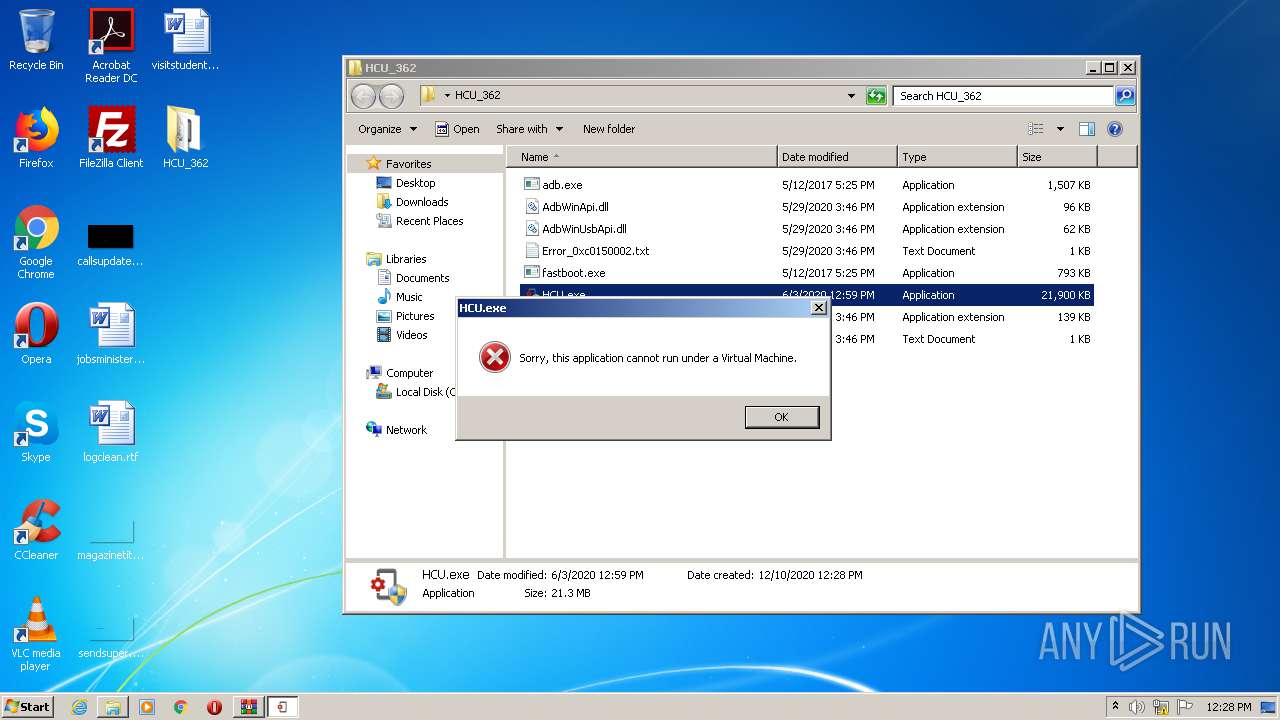
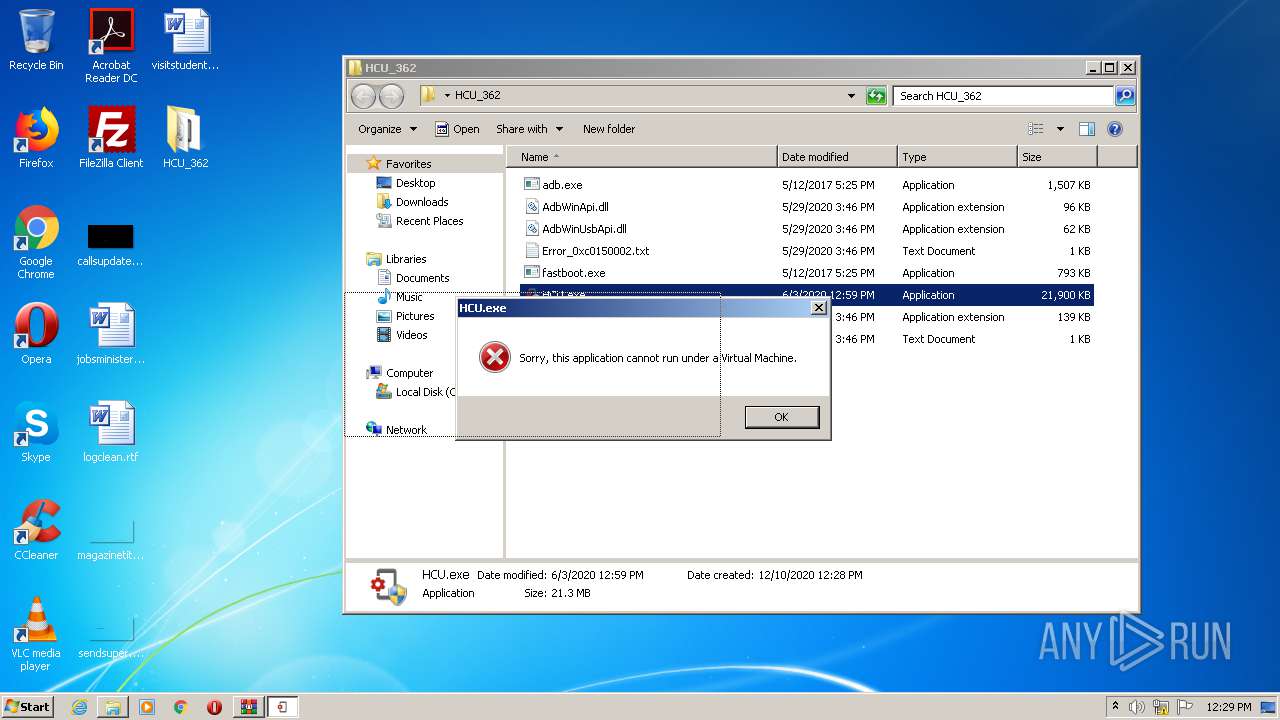
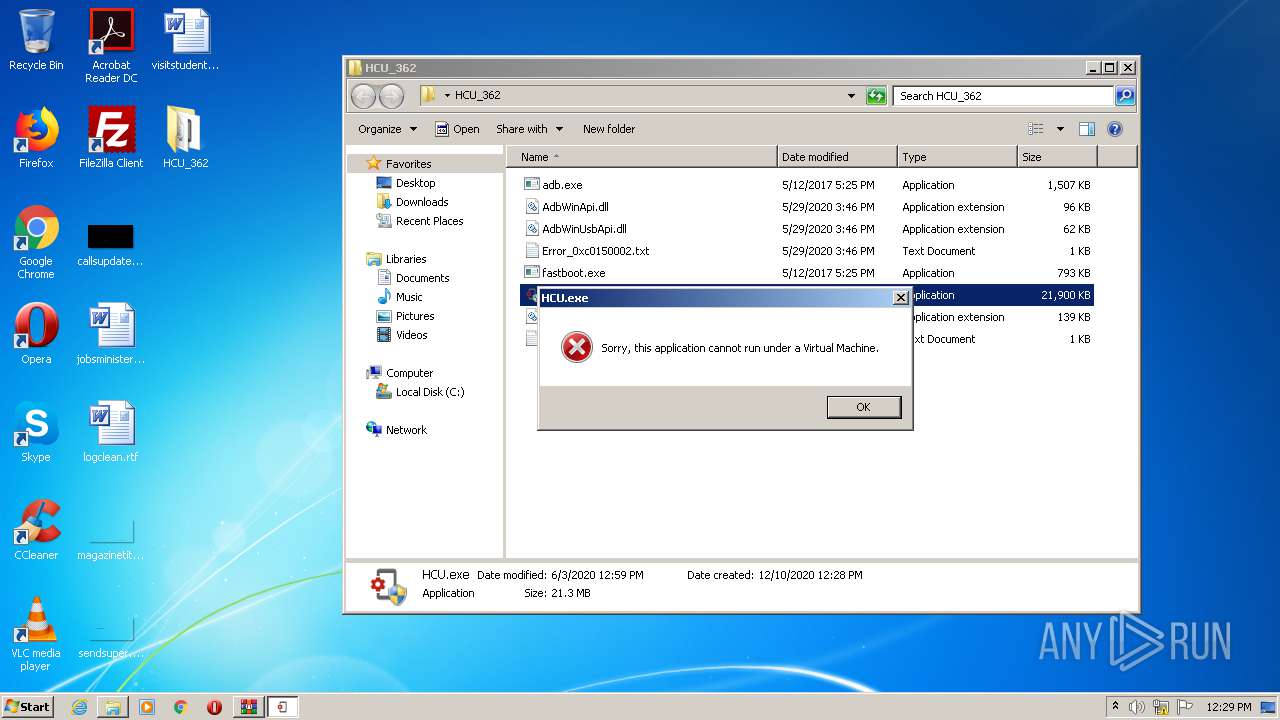
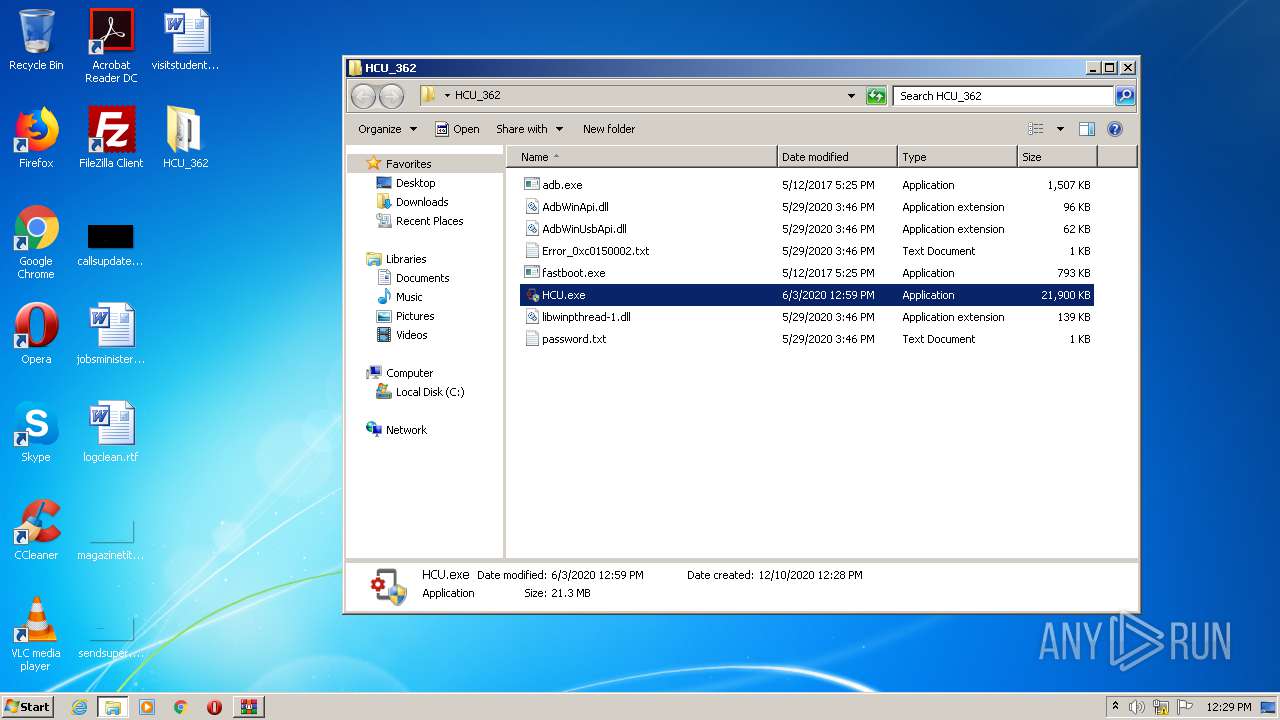
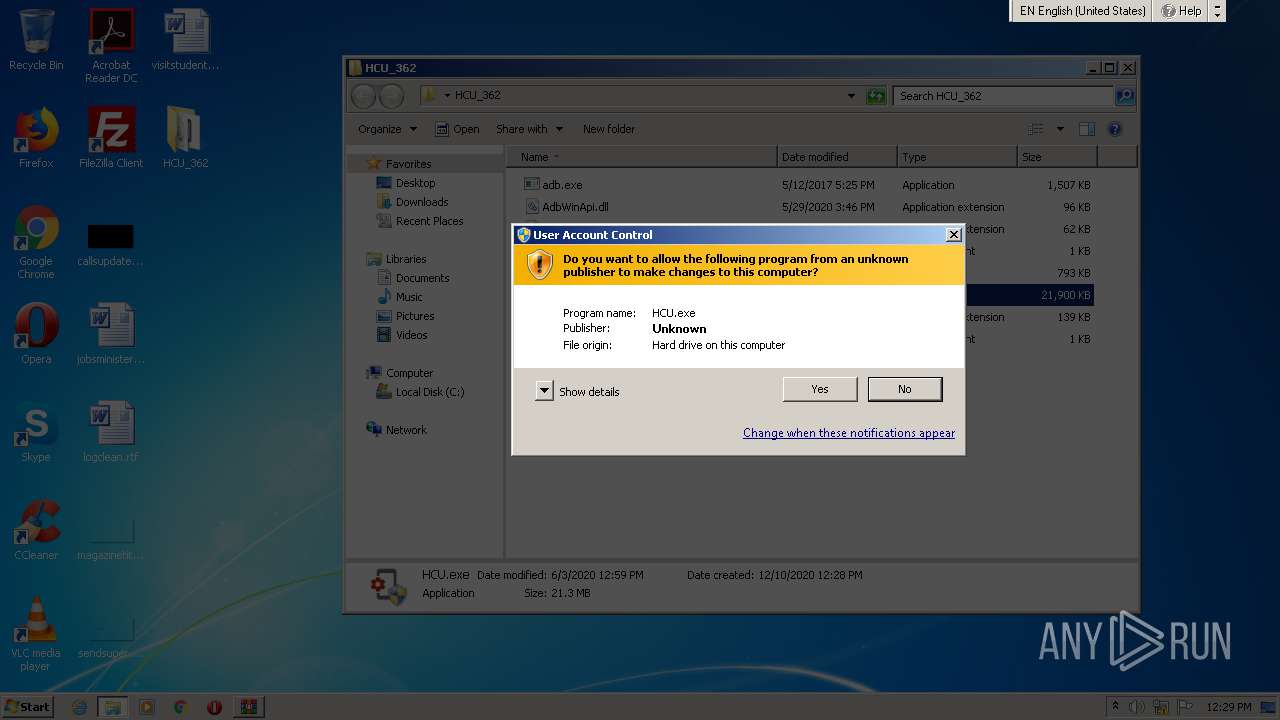
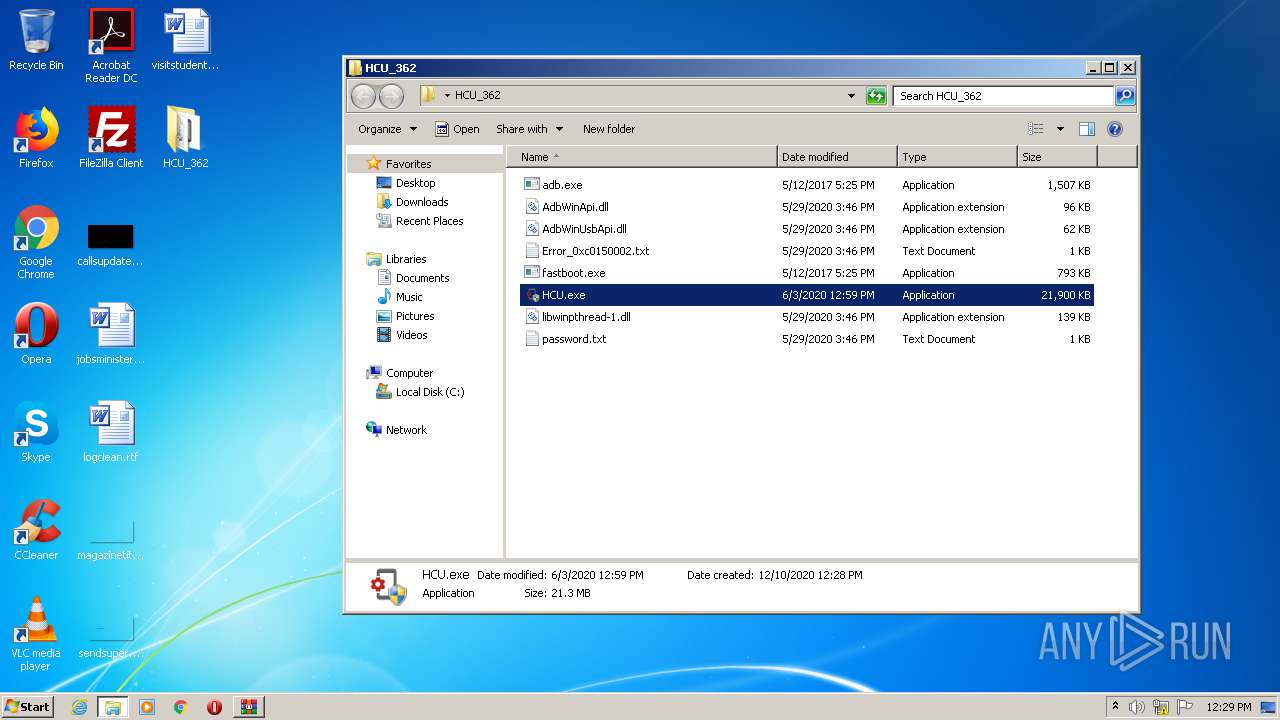
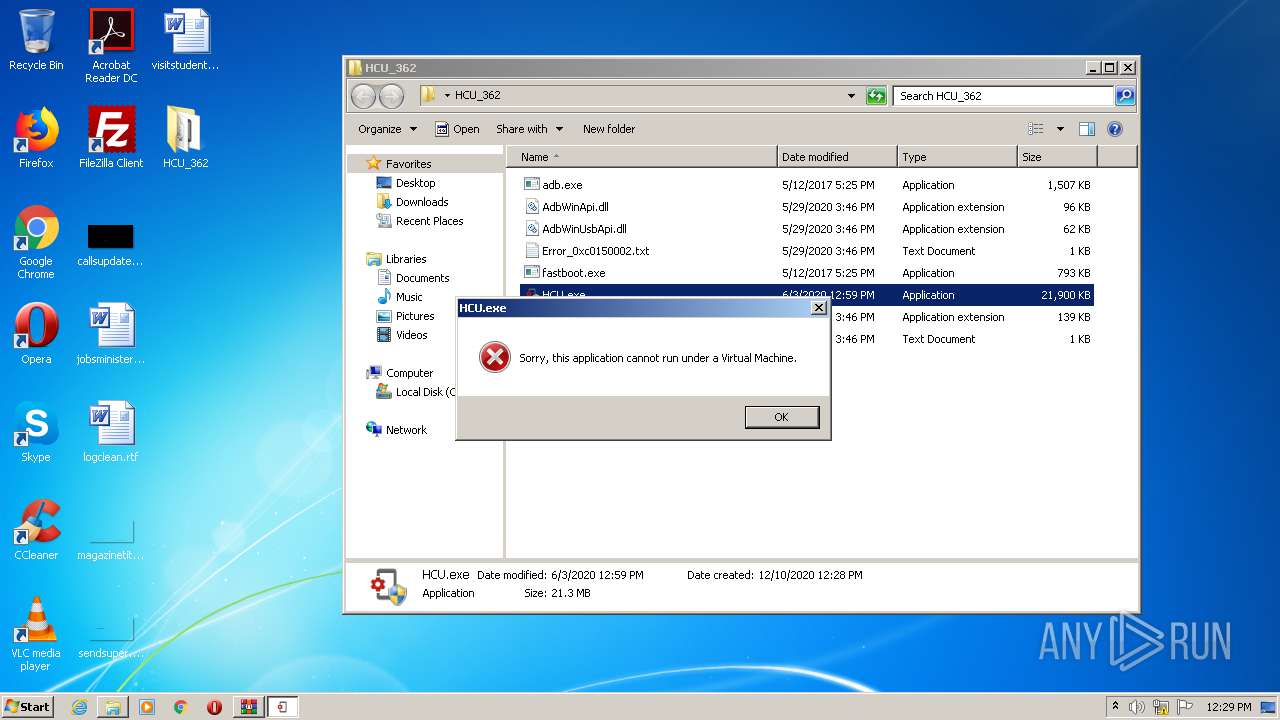
Manual execution by user
- HCU.exe (PID: 2296)
- HCU.exe (PID: 3356)
- HCU.exe (PID: 4044)
- adb.exe (PID: 2568)
- HCU.exe (PID: 2516)
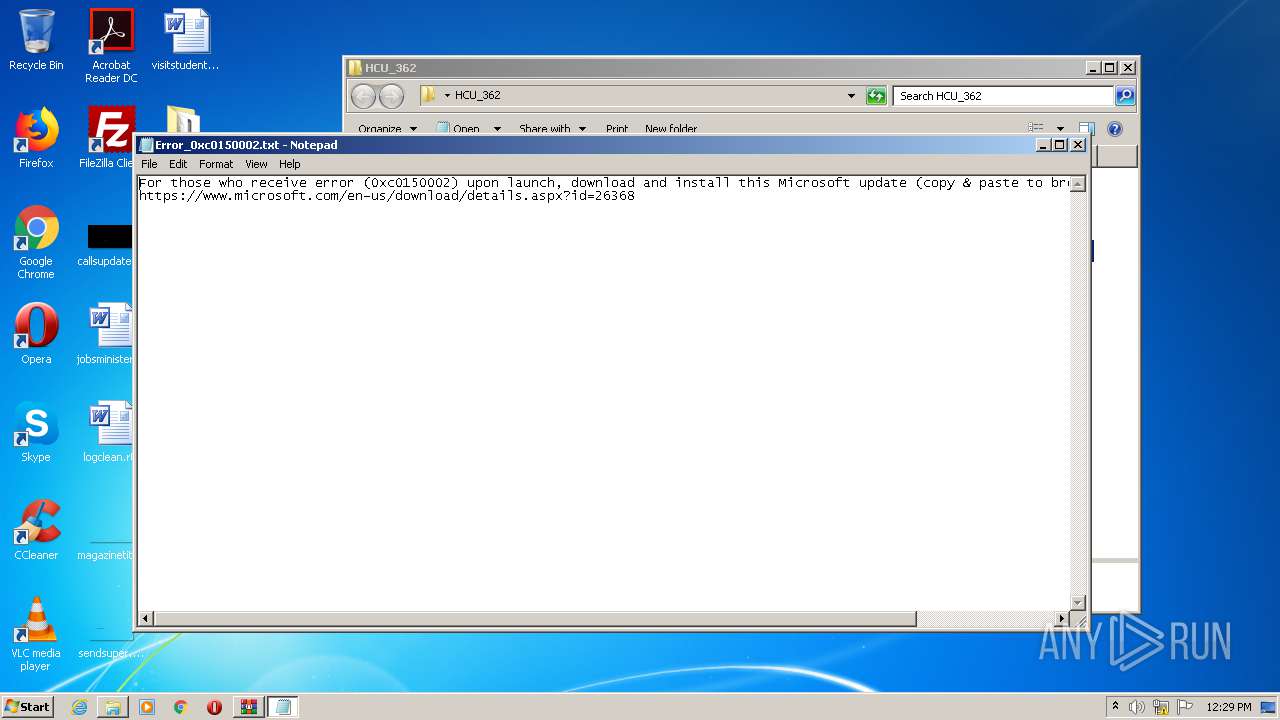
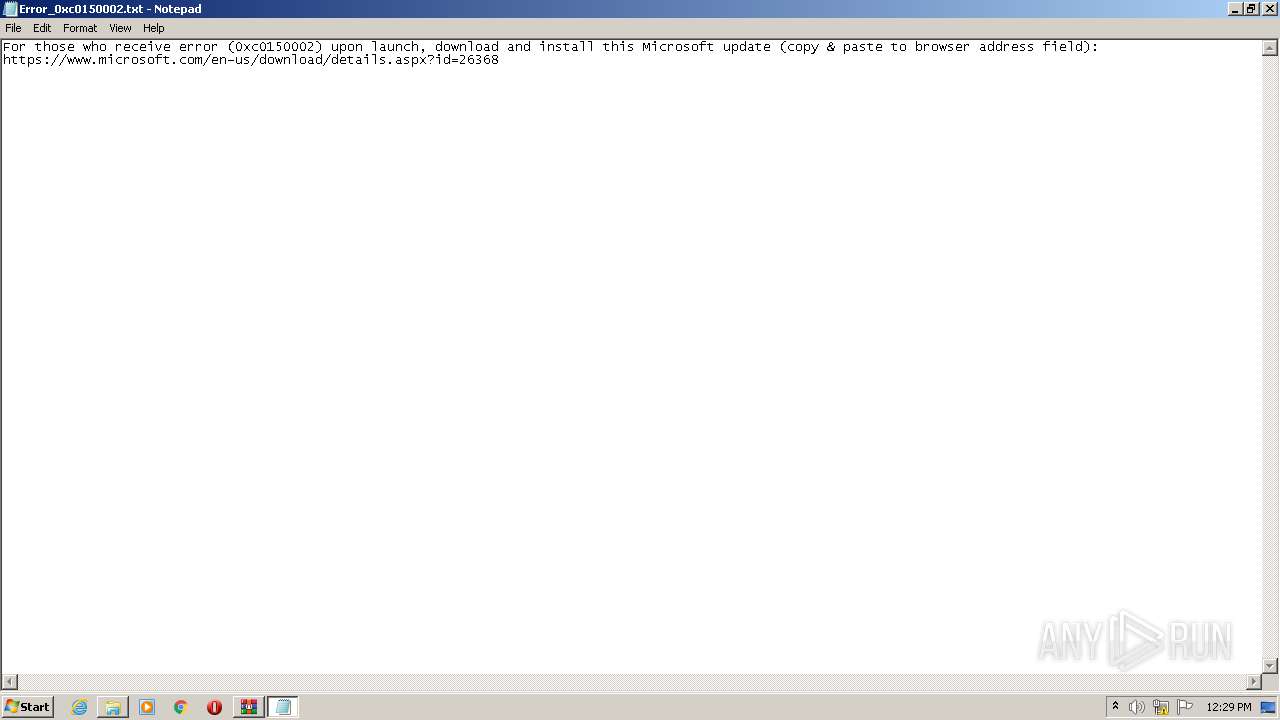
- NOTEPAD.EXE (PID: 4076)
Application launched itself
- iexplore.exe (PID: 2660)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2660)
Changes settings of System certificates
- iexplore.exe (PID: 2660)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
10
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2660 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 848 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe5_ Global\UsGthrCtrlFltPipeMssGthrPipe5 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
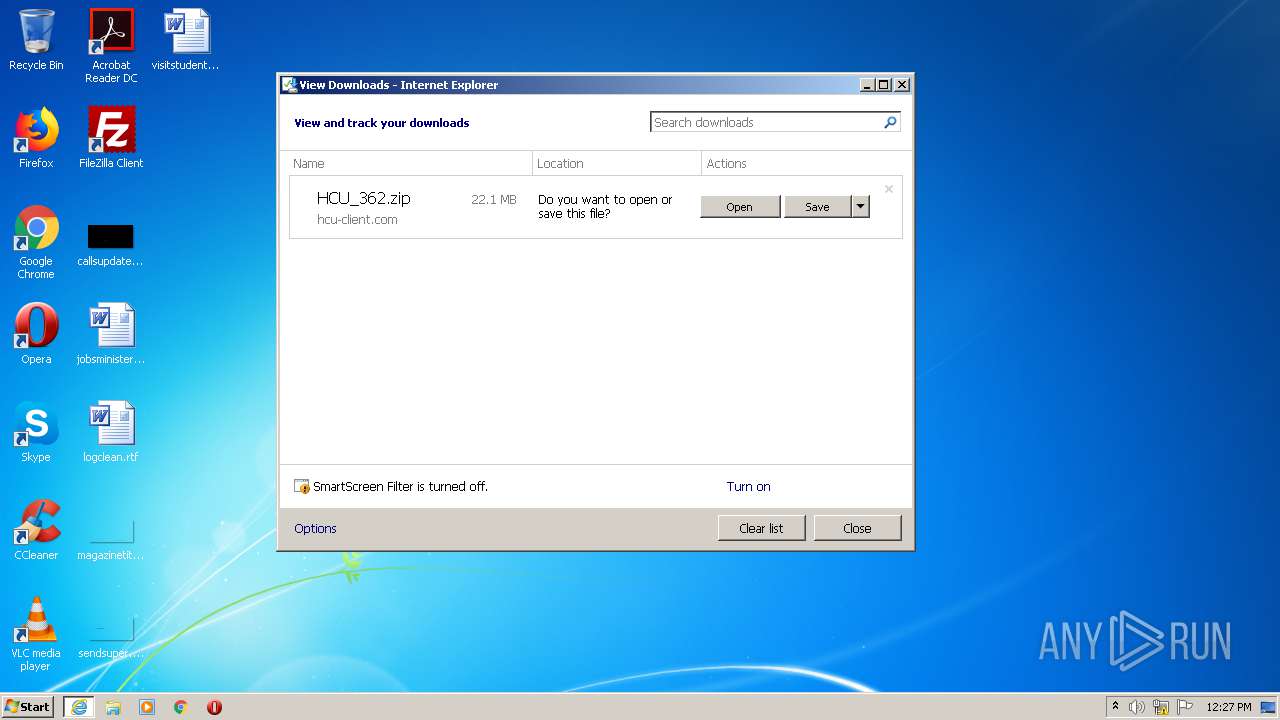
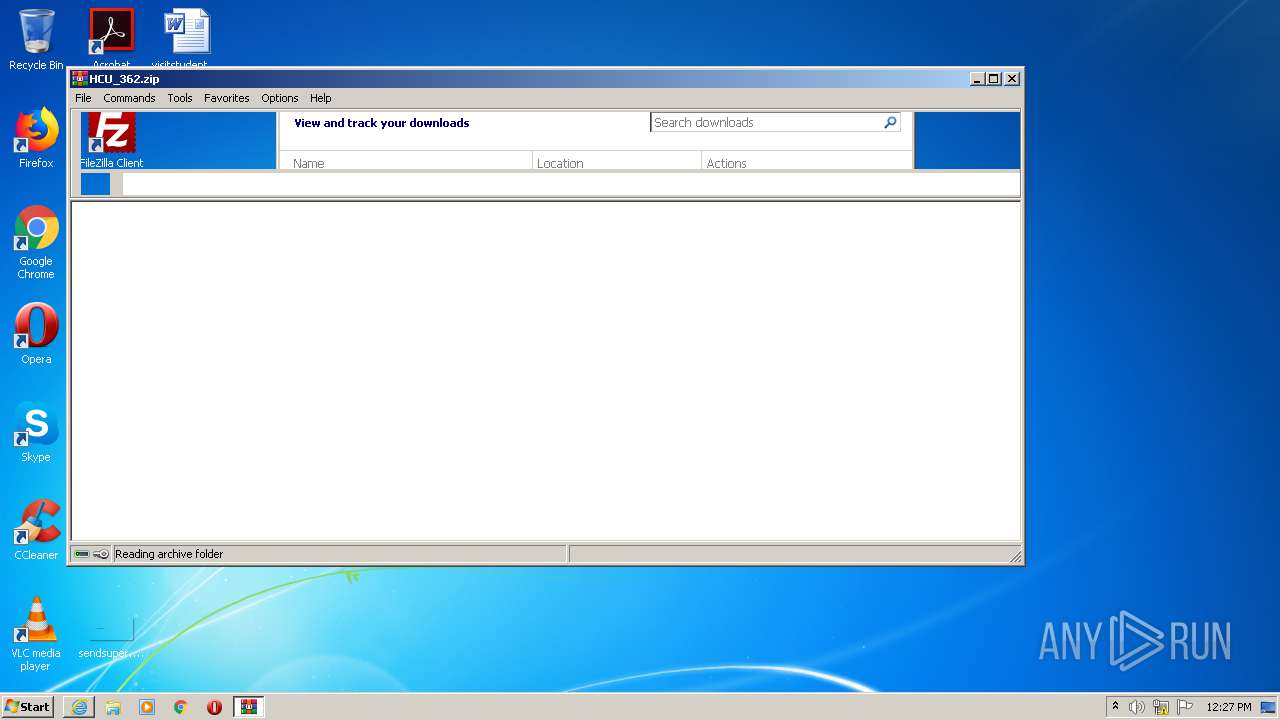
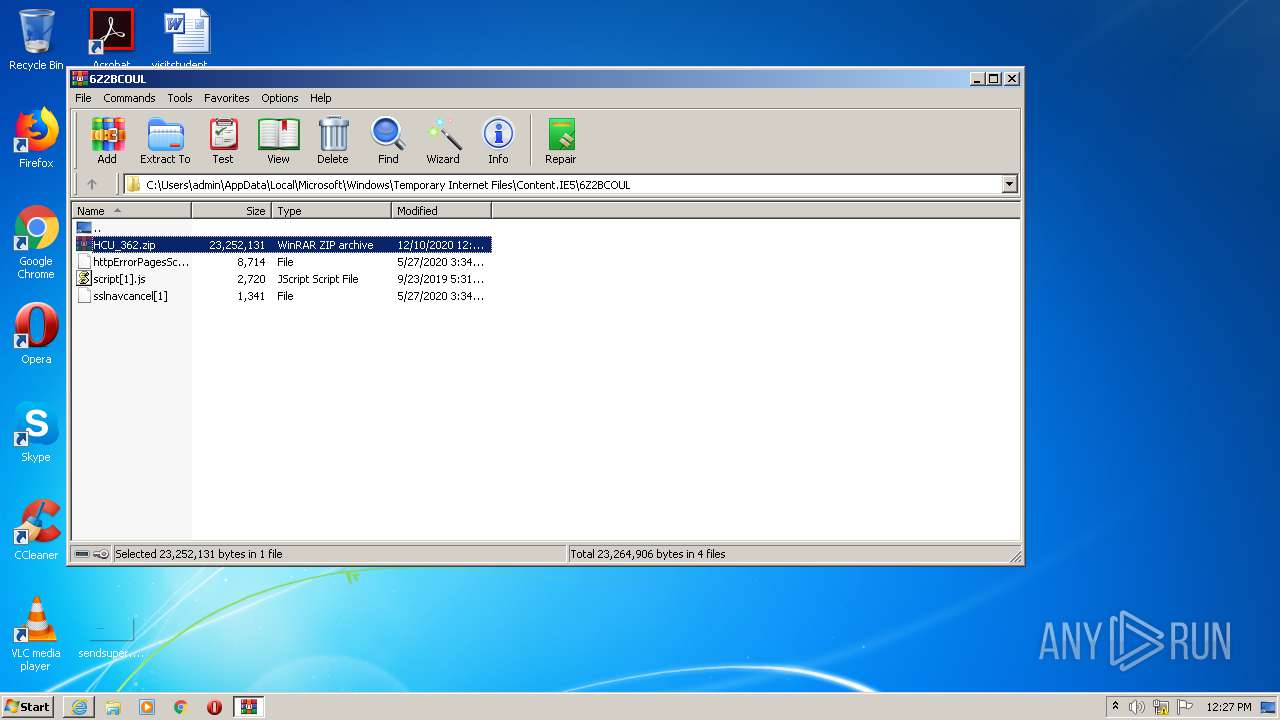
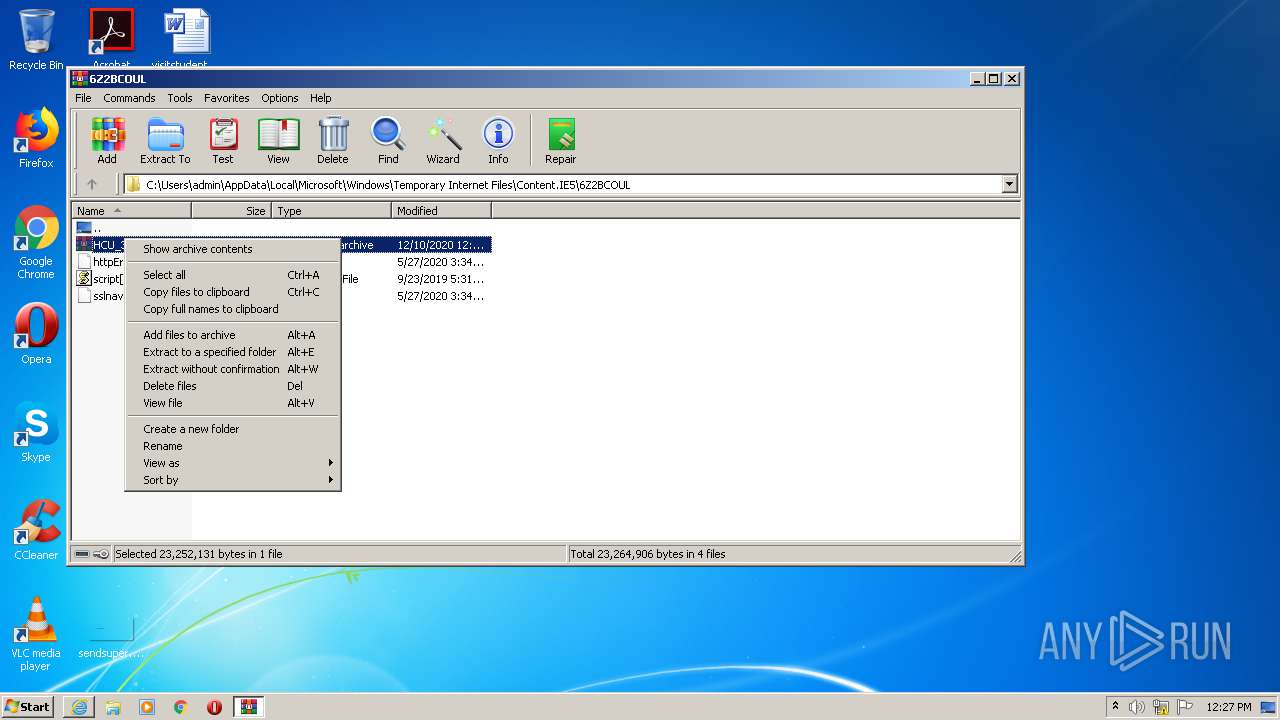
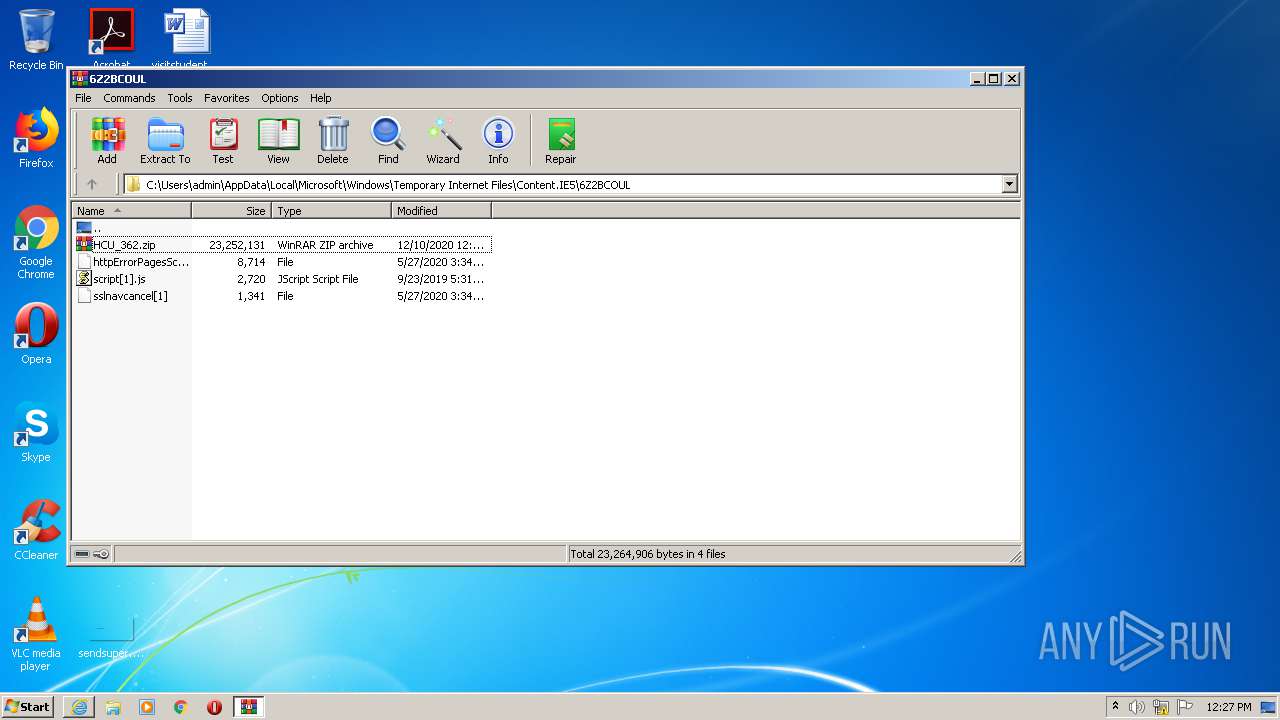
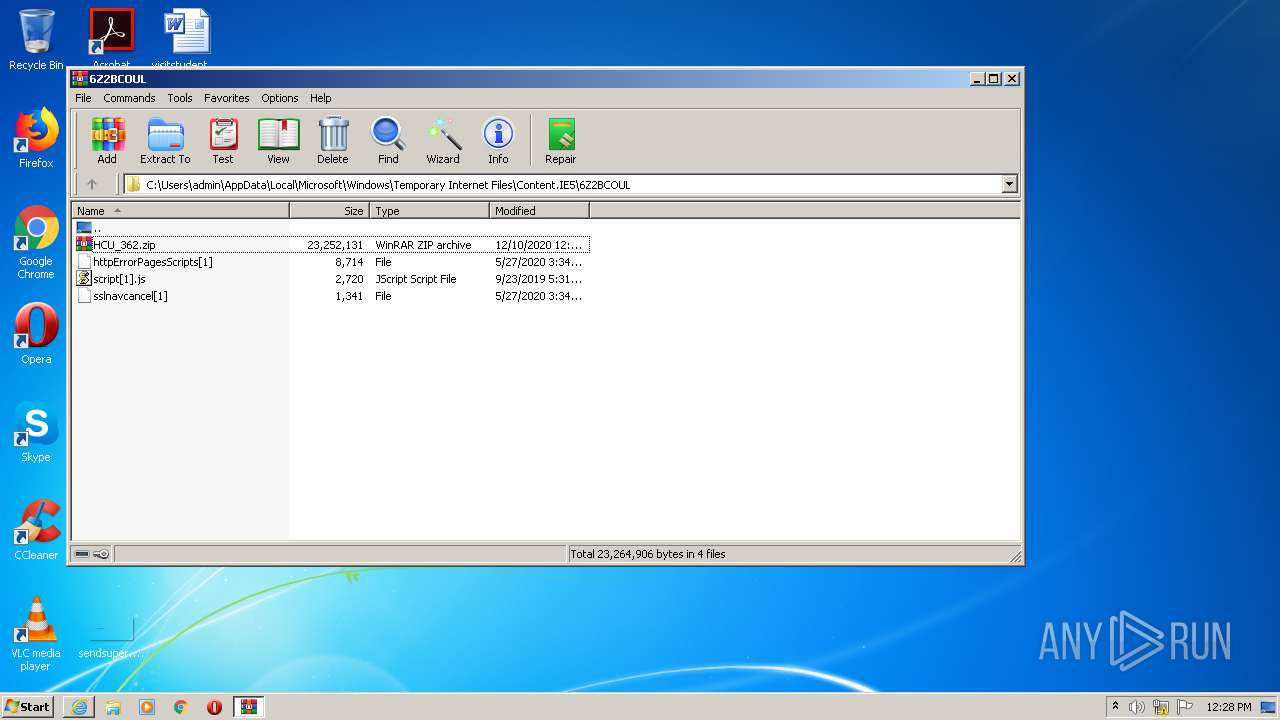
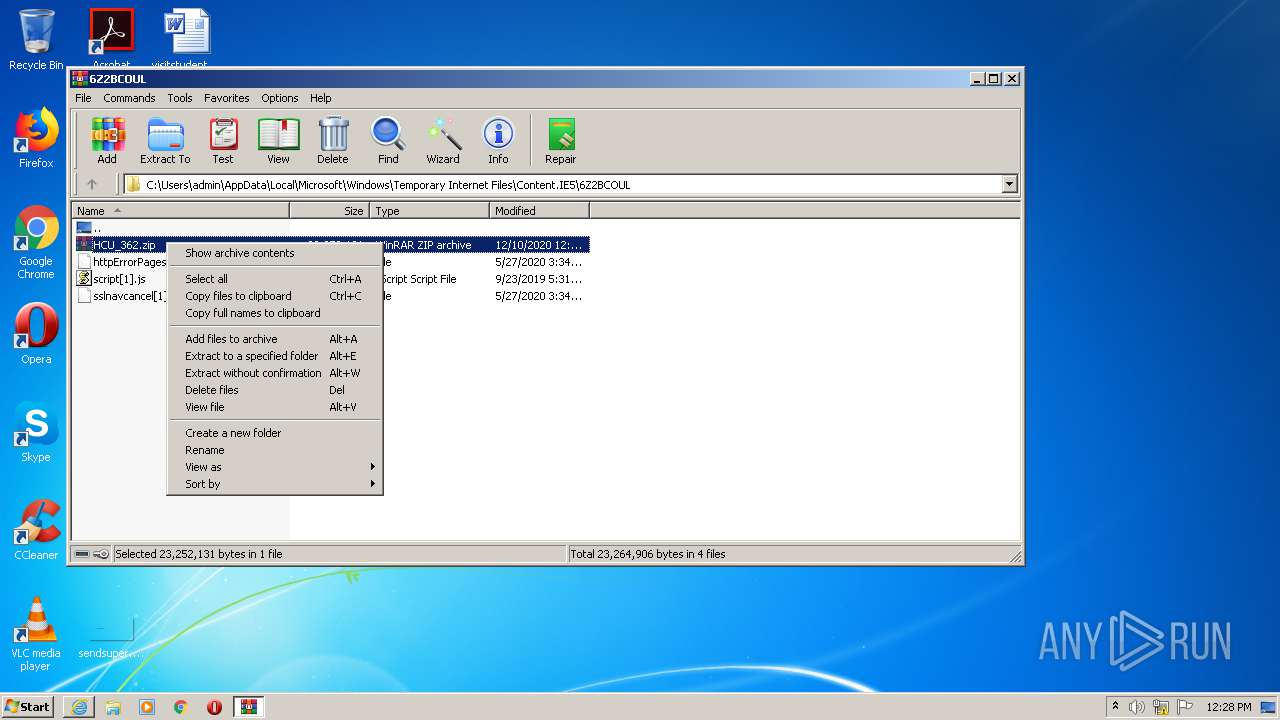
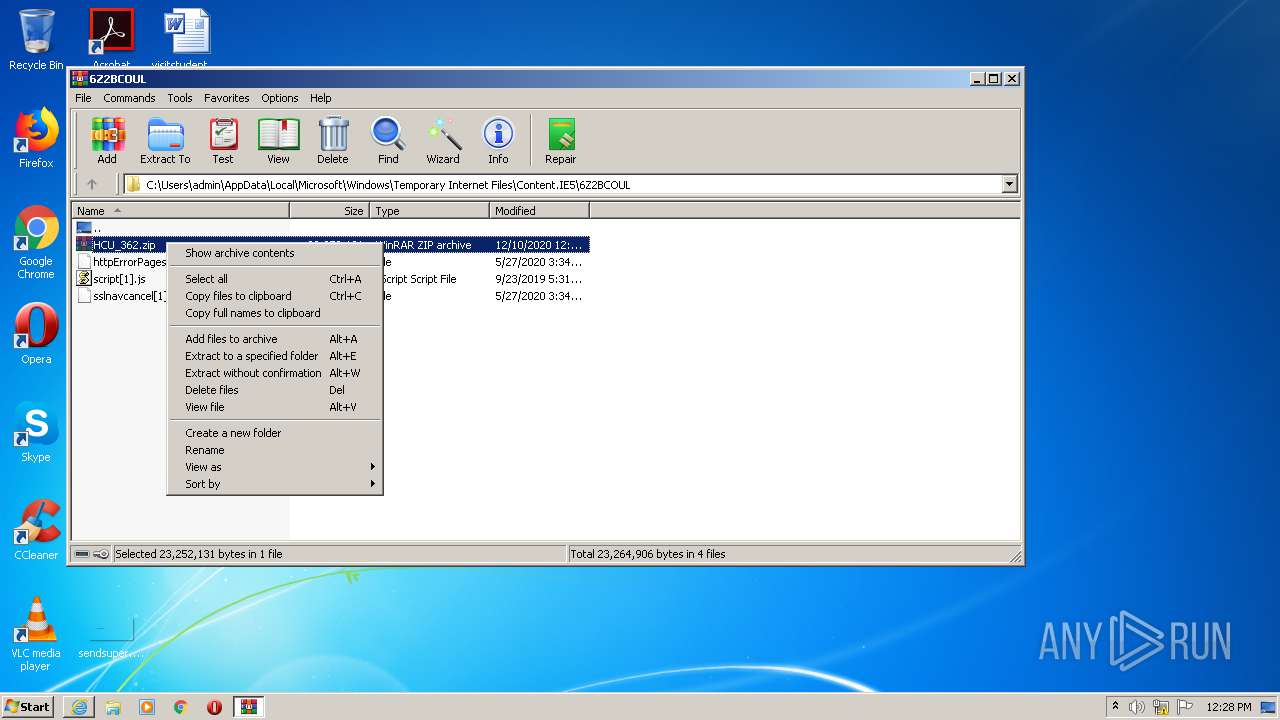
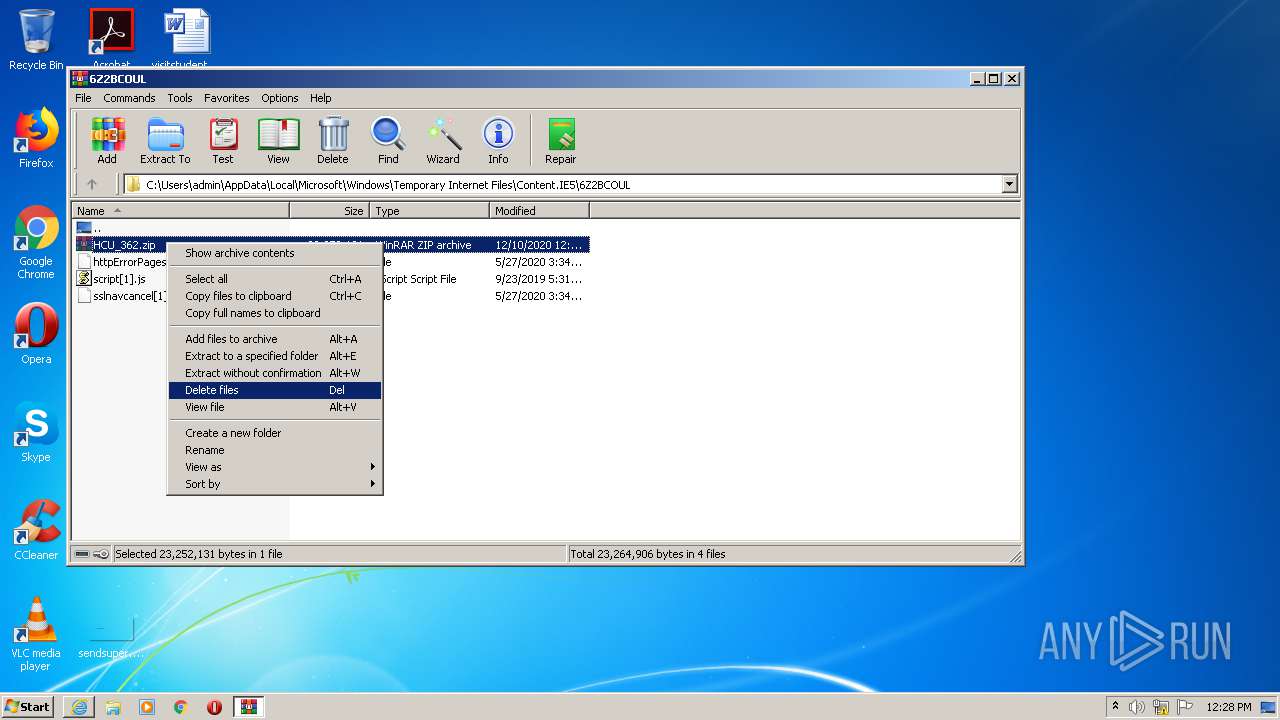
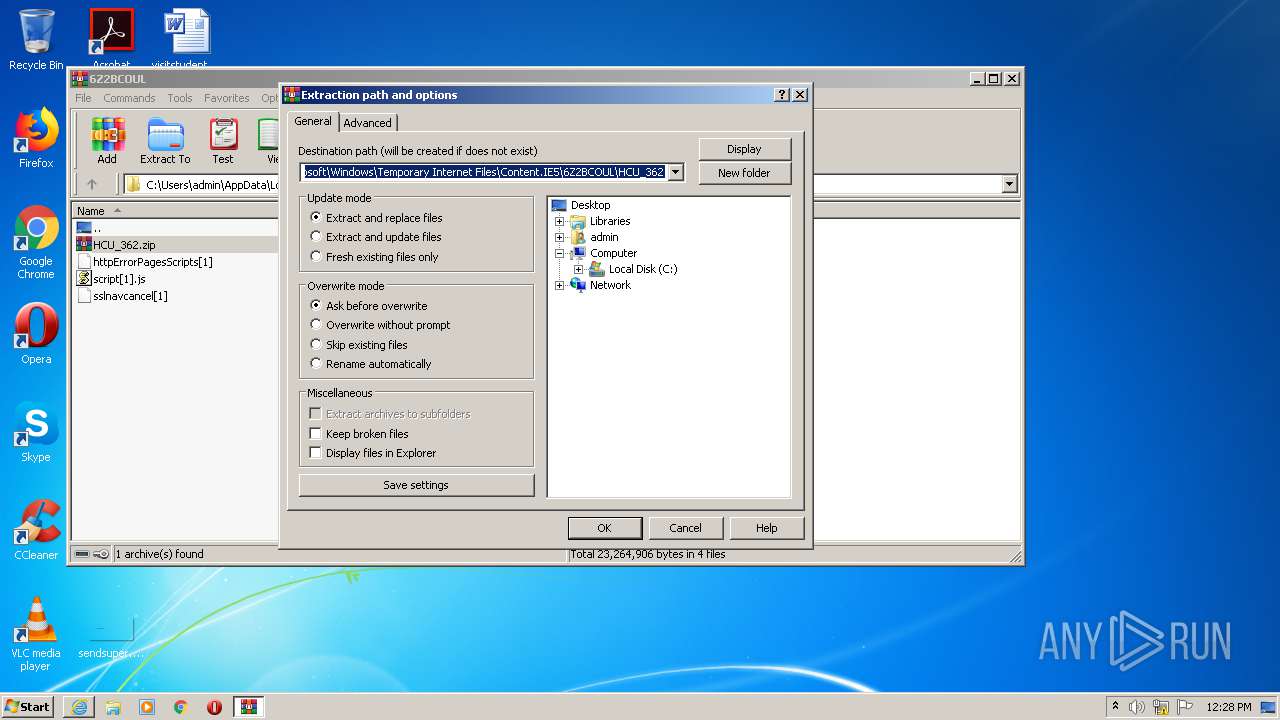
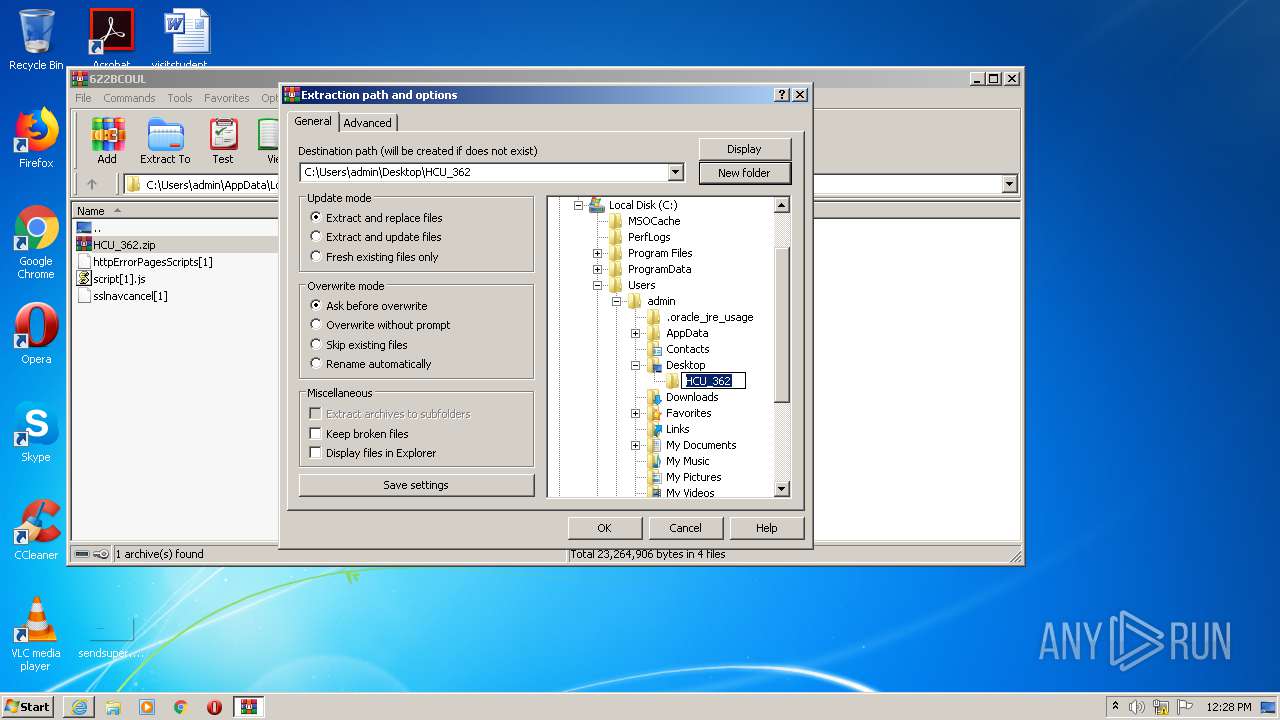
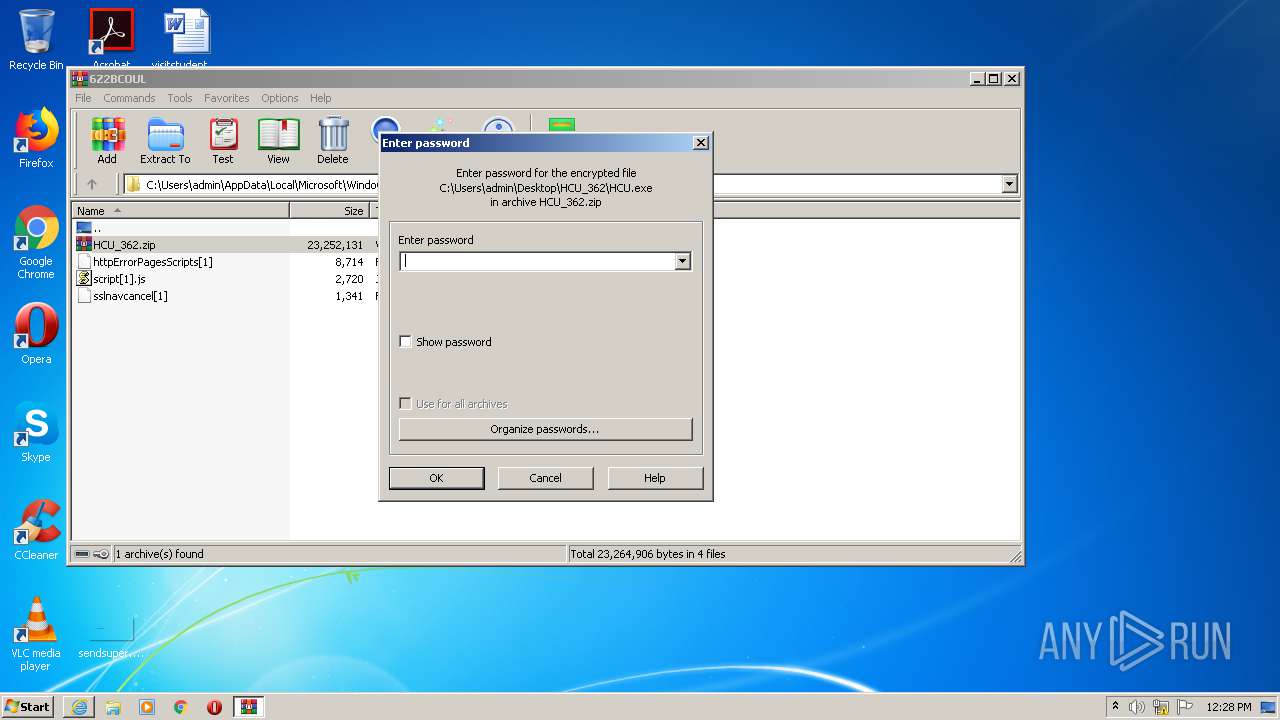
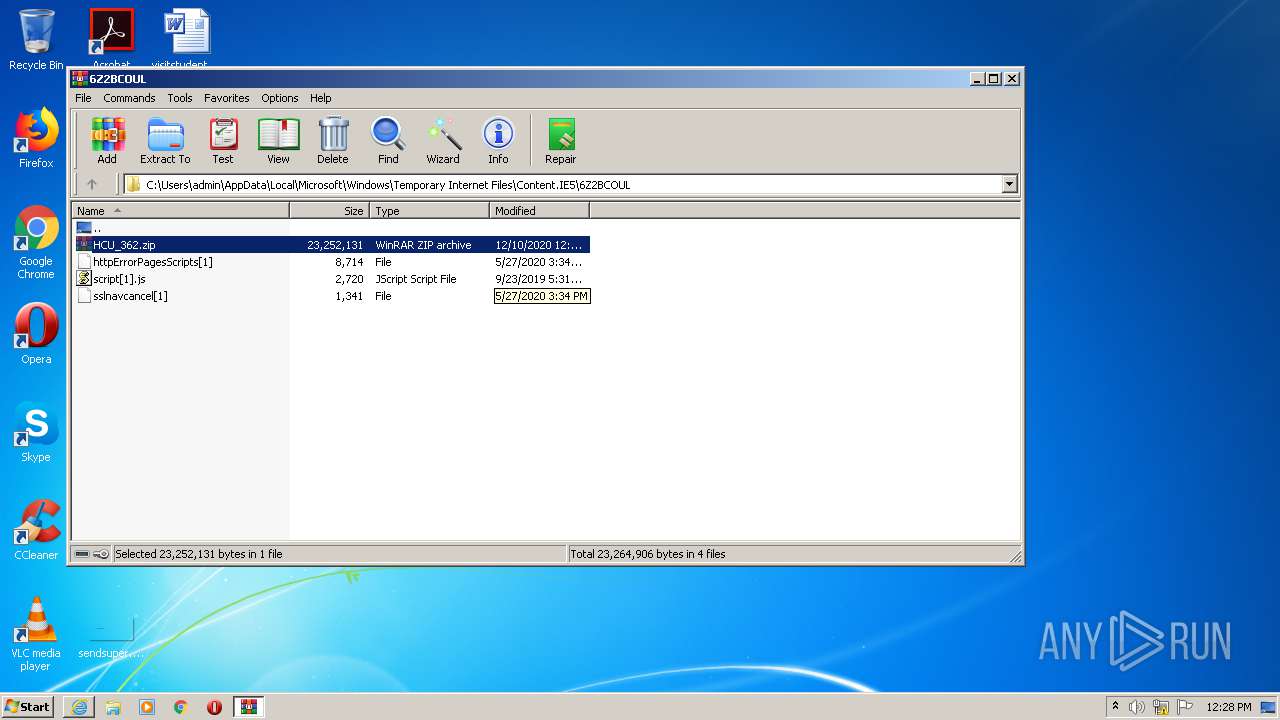
| 1524 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\HCU_362.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
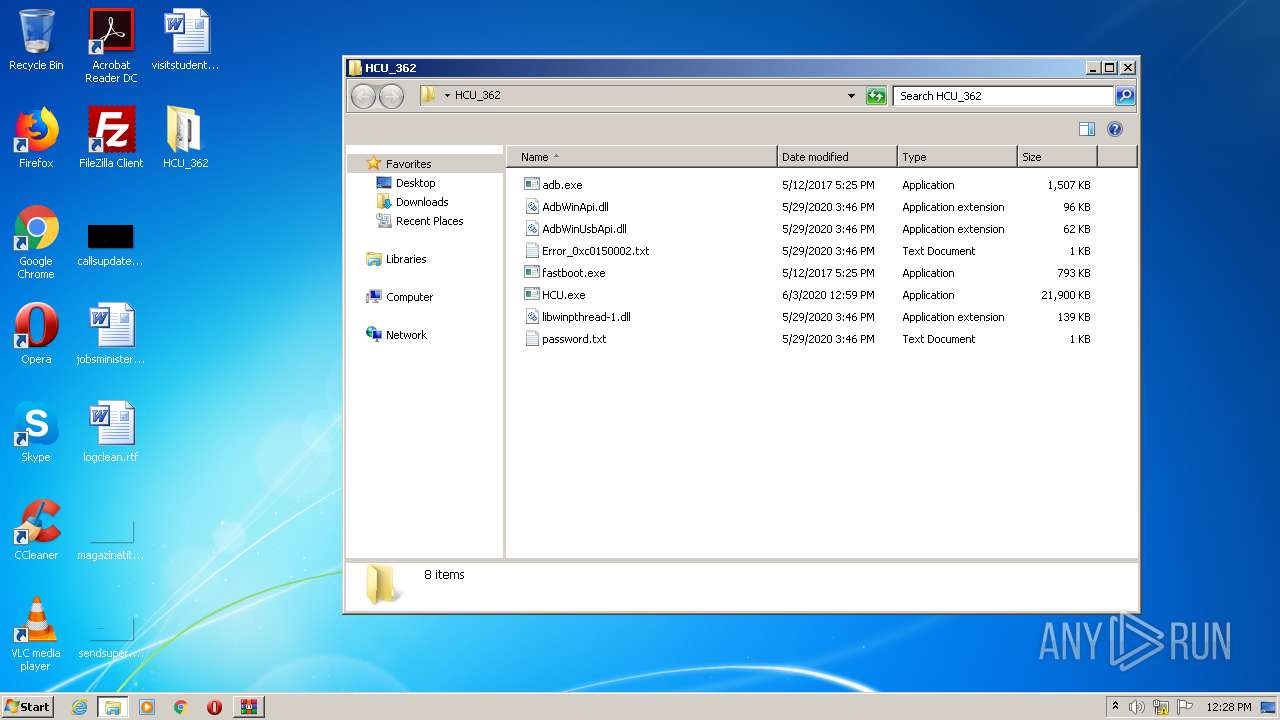
| 2296 | "C:\Users\admin\Desktop\HCU_362\HCU.exe" | C:\Users\admin\Desktop\HCU_362\HCU.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: HCU Exit code: 3735929054 Version: 1.0.0.362 Modules
| |||||||||||||||
| 2516 | "C:\Users\admin\Desktop\HCU_362\HCU.exe" | C:\Users\admin\Desktop\HCU_362\HCU.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: HCU Exit code: 3221226540 Version: 1.0.0.362 Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\Desktop\HCU_362\adb.exe" | C:\Users\admin\Desktop\HCU_362\adb.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://hcu-client.com/download/hcu-client-v1-0-0-0362/?wpdmdl=667&refresh=5fd213ce2e7e91607603150" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3356 | "C:\Users\admin\Desktop\HCU_362\HCU.exe" | C:\Users\admin\Desktop\HCU_362\HCU.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: HCU Exit code: 3221226540 Version: 1.0.0.362 Modules
| |||||||||||||||
| 4044 | "C:\Users\admin\Desktop\HCU_362\HCU.exe" | C:\Users\admin\Desktop\HCU_362\HCU.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: HCU Exit code: 3735929054 Version: 1.0.0.362 Modules
| |||||||||||||||
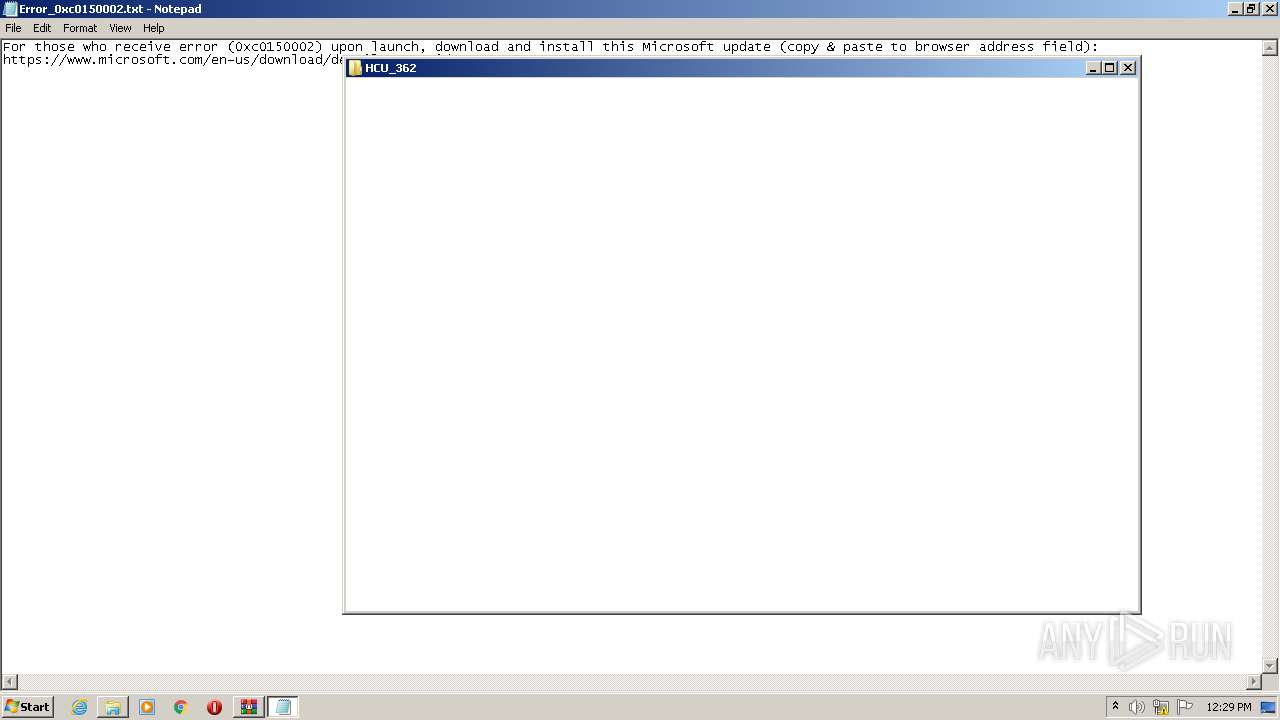
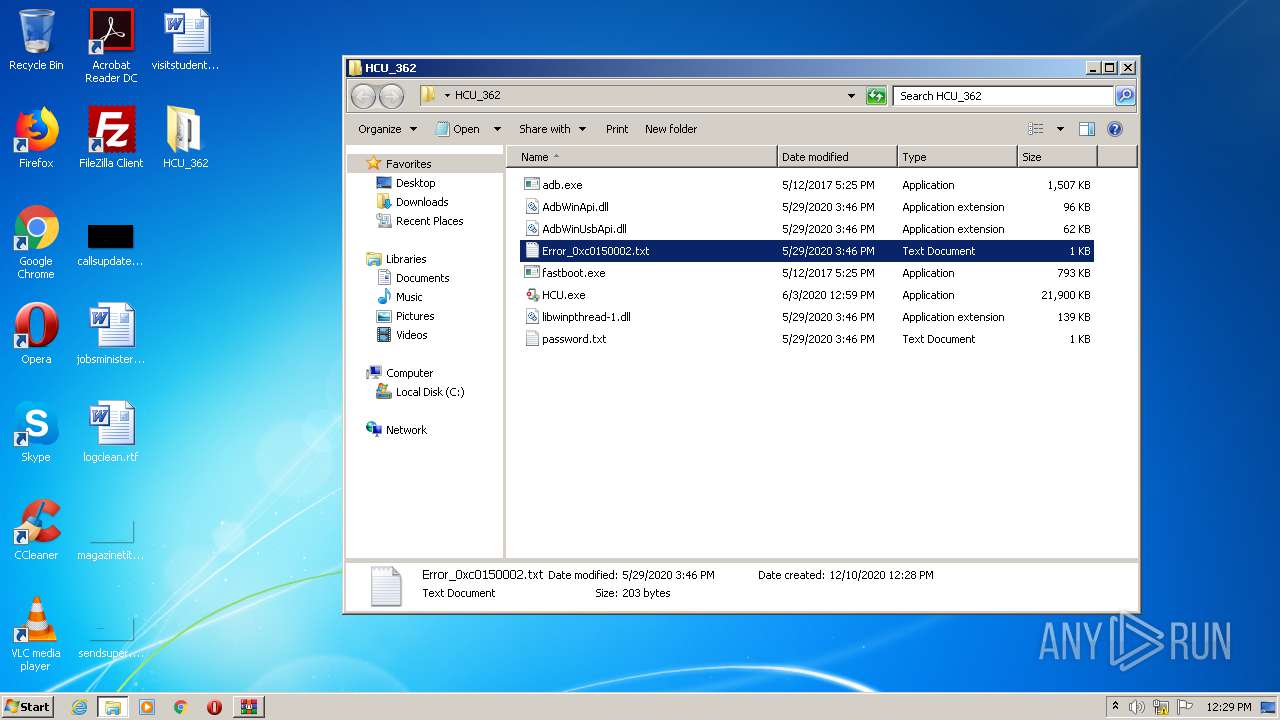
| 4076 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\HCU_362\Error_0xc0150002.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 058
Read events
1 958
Write events
97
Delete events
3
Modification events
| (PID) Process: | (2660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3823912330 | |||
| (PID) Process: | (2660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30854895 | |||
| (PID) Process: | (2660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2660) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
6
Suspicious files
22
Text files
5
Unknown types
7
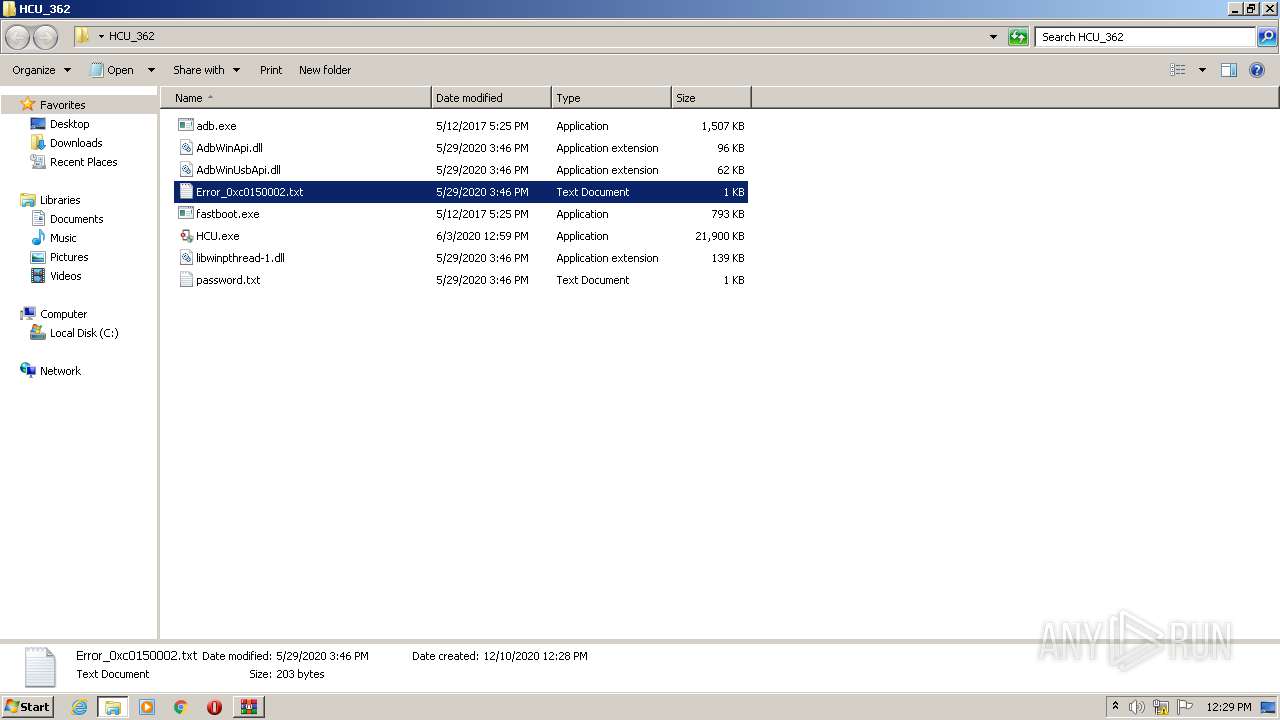
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 404 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabCE91.tmp | — | |
MD5:— | SHA256:— | |||
| 404 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarCE92.tmp | — | |
MD5:— | SHA256:— | |||
| 404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\HCU_362[1].zip | — | |
MD5:— | SHA256:— | |||
| 404 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\HCU_362.zip.kno63dq.partial | — | |
MD5:— | SHA256:— | |||
| 2660 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3145F3B4C4705C44.TMP | — | |
MD5:— | SHA256:— | |||
| 2660 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\HCU_362.zip.kno63dq.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2660 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\CabB6DE.tmp | — | |
MD5:— | SHA256:— | |||
| 2660 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\TarB6DF.tmp | — | |
MD5:— | SHA256:— | |||
| 2660 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\verB71F.tmp | — | |
MD5:— | SHA256:— | |||
| 404 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C1B9A110C69E47072FD0C9C833798DBD | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
14
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
404 | iexplore.exe | GET | 200 | 2.16.177.195:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
2660 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2660 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
404 | iexplore.exe | GET | 200 | 2.16.177.160:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgOxKBdvgnDC5mRY%2Fkm5YkhNLg%3D%3D | unknown | der | 527 b | whitelisted |
2660 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 471 b | whitelisted |
2660 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 471 b | whitelisted |
2660 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
404 | iexplore.exe | GET | 200 | 2.16.177.195:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
404 | iexplore.exe | 3.13.119.240:443 | hcu-client.com | — | US | unknown |
2660 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
404 | iexplore.exe | 2.16.177.160:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | unknown |
2660 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2660 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | Microsoft Corporation | US | whitelisted |
404 | iexplore.exe | 2.16.177.195:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hcu-client.com |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |