| File name: | Cisco-Secure-Client-Windows.x64.exe |
| Full analysis: | https://app.any.run/tasks/eea21927-7d66-4136-bcfd-96f4b761b193 |
| Verdict: | Malicious activity |
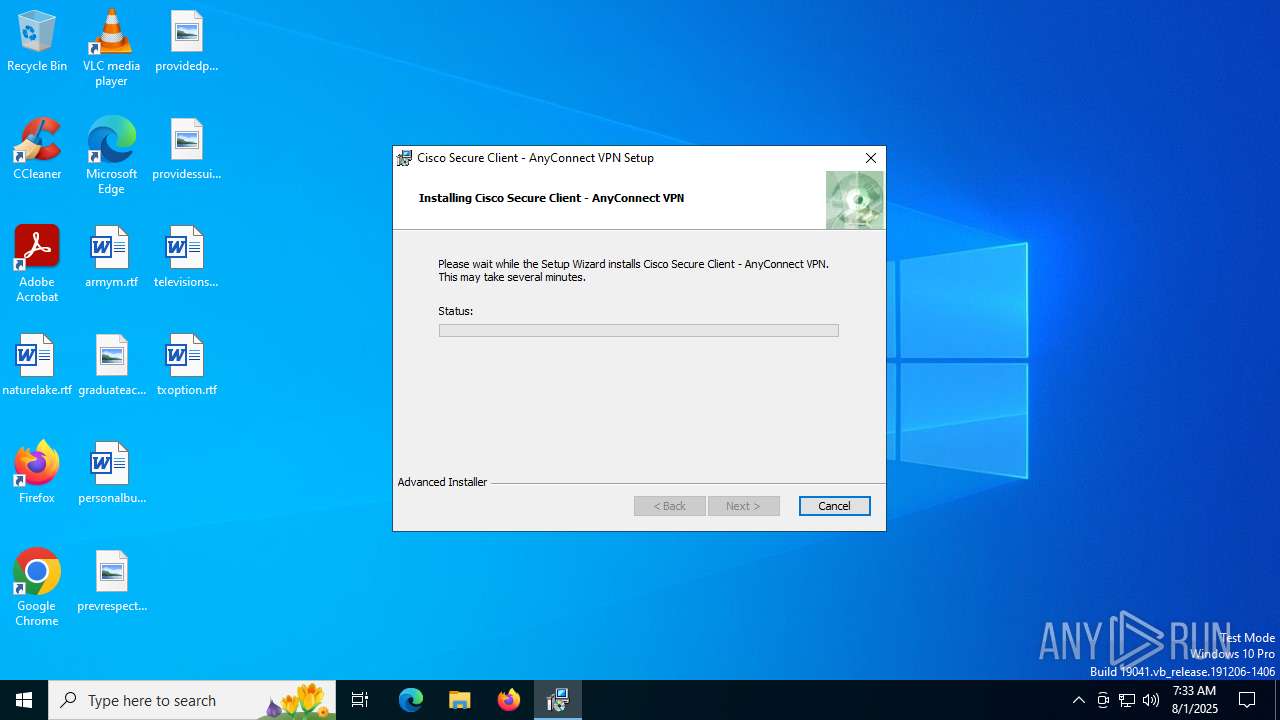
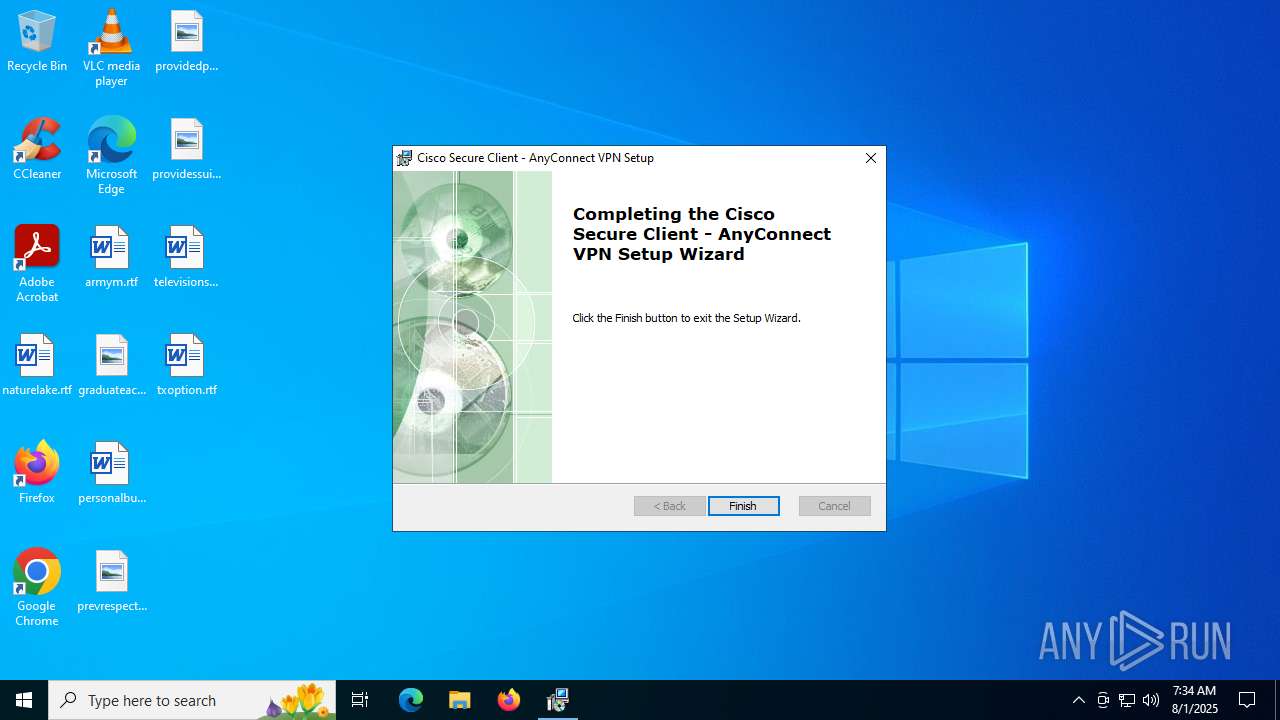
| Analysis date: | August 01, 2025, 07:33:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows, 11 sections |
| MD5: | FEFA02CCFDFEE489C3AEAF835B6FE675 |
| SHA1: | 37311DB6DBEFC6D7F94C17D7EA07D6A093234122 |
| SHA256: | 14E6171511D17CCA3B66EFC7CC9A63EAB66FD529445B33D071D8EF4A45E0172A |
| SSDEEP: | 3072:A8XukqvRmmrCGkE9gll8+mA+vG3C5Rj53mcKg253vpdgG5IZg9q5g6X:gLCIdIg253vpdgG5IZg9q5g6X |
MALICIOUS
Changes the autorun value in the registry
- msiexec.exe (PID: 3400)
- msiexec.exe (PID: 4864)
- vpnagent.exe (PID: 1864)
SUSPICIOUS
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 760)
Executes as Windows Service
- VSSVC.exe (PID: 7044)
- vpnagent.exe (PID: 1864)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3400)
Executes application which crashes
- msiexec.exe (PID: 2192)
The process creates files with name similar to system file names
- msiexec.exe (PID: 3400)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 3400)
- msiexec.exe (PID: 4864)
- drvinst.exe (PID: 6572)
- drvinst.exe (PID: 2428)
The process drops C-runtime libraries
- msiexec.exe (PID: 3400)
Process drops legitimate windows executable
- msiexec.exe (PID: 3400)
Creates/Modifies COM task schedule object
- InstallHelper.exe (PID: 4308)
Creates files in the driver directory
- msiexec.exe (PID: 4864)
- drvinst.exe (PID: 6572)
- VACon64.exe (PID: 4060)
- drvinst.exe (PID: 2428)
Executable content was dropped or overwritten
- drvinst.exe (PID: 6572)
- drvinst.exe (PID: 2428)
Creates or modifies Windows services
- drvinst.exe (PID: 2428)
Reads security settings of Internet Explorer
- InstallHelper.exe (PID: 6720)
- vpnagent.exe (PID: 1864)
Application launched itself
- msiexec.exe (PID: 3400)
INFO
Checks supported languages
- Cisco-Secure-Client-Windows.x64.exe (PID: 2964)
- msiexec.exe (PID: 1644)
- msiexec.exe (PID: 3400)
- msiexec.exe (PID: 3556)
- msiexec.exe (PID: 2192)
- InstallHelper.exe (PID: 6720)
- InstallHelper.exe (PID: 2032)
- InstallHelper.exe (PID: 6340)
- msiexec.exe (PID: 3768)
- InstallHelper.exe (PID: 4308)
- InstallHelper.exe (PID: 5468)
- InstallHelper.exe (PID: 5780)
- msiexec.exe (PID: 4864)
- drvinst.exe (PID: 6572)
- VACon64.exe (PID: 4060)
- InstallHelper.exe (PID: 6720)
- drvinst.exe (PID: 2428)
- InstallHelper.exe (PID: 1632)
- vpnagent.exe (PID: 1864)
- InstallHelper.exe (PID: 2504)
- InstallHelper.exe (PID: 3956)
- InstallHelper.exe (PID: 4768)
Reads the computer name
- Cisco-Secure-Client-Windows.x64.exe (PID: 2964)
- msiexec.exe (PID: 1644)
- msiexec.exe (PID: 3400)
- msiexec.exe (PID: 3556)
- InstallHelper.exe (PID: 6340)
- InstallHelper.exe (PID: 6720)
- InstallHelper.exe (PID: 2032)
- msiexec.exe (PID: 2192)
- msiexec.exe (PID: 3768)
- InstallHelper.exe (PID: 5468)
- InstallHelper.exe (PID: 4308)
- InstallHelper.exe (PID: 4768)
- InstallHelper.exe (PID: 5780)
- msiexec.exe (PID: 4864)
- VACon64.exe (PID: 4060)
- drvinst.exe (PID: 6572)
- InstallHelper.exe (PID: 6720)
- InstallHelper.exe (PID: 1632)
- InstallHelper.exe (PID: 2504)
- vpnagent.exe (PID: 1864)
- InstallHelper.exe (PID: 3956)
- drvinst.exe (PID: 2428)
Create files in a temporary directory
- Cisco-Secure-Client-Windows.x64.exe (PID: 2964)
Checks proxy server information
- msiexec.exe (PID: 760)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 760)
- runonce.exe (PID: 6180)
Manages system restore points
- SrTasks.exe (PID: 2120)
Reads the software policy settings
- msiexec.exe (PID: 760)
- msiexec.exe (PID: 3400)
- VACon64.exe (PID: 4060)
- drvinst.exe (PID: 6572)
- vpnagent.exe (PID: 1864)
Reads Environment values
- msiexec.exe (PID: 1644)
- msiexec.exe (PID: 3556)
The sample compiled with english language support
- msiexec.exe (PID: 760)
- msiexec.exe (PID: 3400)
- msiexec.exe (PID: 4864)
- drvinst.exe (PID: 6572)
- drvinst.exe (PID: 2428)
Creates files or folders in the user directory
- msiexec.exe (PID: 760)
Executable content was dropped or overwritten
- msiexec.exe (PID: 760)
- msiexec.exe (PID: 3400)
- msiexec.exe (PID: 4864)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3400)
- VACon64.exe (PID: 4060)
- drvinst.exe (PID: 6572)
- vpnagent.exe (PID: 1864)
Creates or modifies Windows services
- msiexec.exe (PID: 3400)
Launching a file from a Registry key
- msiexec.exe (PID: 3400)
- msiexec.exe (PID: 4864)
- vpnagent.exe (PID: 1864)
Creates a software uninstall entry
- msiexec.exe (PID: 3400)
Reads the time zone
- runonce.exe (PID: 6180)
Creates files in the program directory
- InstallHelper.exe (PID: 6720)
- vpnagent.exe (PID: 1864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:07:23 13:43:51+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.43 |
| CodeSize: | 68608 |
| InitializedDataSize: | 91136 |
| UninitializedDataSize: | 3584 |
| EntryPoint: | 0x13c0 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
174
Monitored processes
31
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 760 | msiexec.exe /i C:\Users\admin\AppData\Local\Temp\Cisco-AnyConnect-win-4.11.msi | C:\Windows\System32\msiexec.exe | Cisco-Secure-Client-Windows.x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1336 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 2192 -s 844 | C:\Windows\SysWOW64\WerFault.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1632 | "C:\Program Files (x86)\Cisco\Cisco Secure Client\InstallHelper.exe" -deleteRestrictedUser | C:\Program Files (x86)\Cisco\Cisco Secure Client\InstallHelper.exe | — | msiexec.exe | |||||||||||
User: admin Company: Cisco Systems, Inc. Integrity Level: MEDIUM Description: Install Helper Exit code: 1 Version: 5, 1, 4, 74 Modules
| |||||||||||||||
| 1644 | C:\Windows\syswow64\MsiExec.exe -Embedding 459114FD3B50CD039EA2B190E98F6D62 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1864 | "C:\Program Files (x86)\Cisco\Cisco Secure Client\vpnagent.exe" | C:\Program Files (x86)\Cisco\Cisco Secure Client\vpnagent.exe | services.exe | ||||||||||||
User: SYSTEM Company: Cisco Systems, Inc. Integrity Level: SYSTEM Description: VPN Agent Service Version: 5, 1, 4, 74 Modules
| |||||||||||||||
| 2032 | "C:\Program Files (x86)\Cisco\Cisco Secure Client\InstallHelper.exe" -copyFiles "C:\Users\admin\AppData\Local\Temp\Profiles\feedback\\" "C:\ProgramData\Cisco\Cisco Secure Client\CustomerExperienceFeedback\\" "CustomerExperience_Feedback.xml" | C:\Program Files (x86)\Cisco\Cisco Secure Client\InstallHelper.exe | — | msiexec.exe | |||||||||||
User: admin Company: Cisco Systems, Inc. Integrity Level: MEDIUM Description: Install Helper Exit code: 1 Version: 5, 1, 4, 74 Modules
| |||||||||||||||
| 2120 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\Windows\syswow64\MsiExec.exe -Embedding 88726D2DC31D416882E73B916B0AB96A E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 255 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | DrvInst.exe "2" "211" "ROOT\NET\0000" "C:\WINDOWS\INF\oem1.inf" "oem1.inf:573bd3b1d858e0ac:Cisco.ndi.NTamd64:4.10.5040.0:vpnva," "458dd218b" "00000000000001F4" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 066
Read events
26 135
Write events
903
Delete events
28
Modification events
| (PID) Process: | (3400) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000097C21B9FB602DC01480D000088190000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3400) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000097C21B9FB602DC01480D000088190000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3400) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000063261E9FB602DC01480D000088190000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3400) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000061795E9FB602DC01480D000088190000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3400) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E1DE609FB602DC01480D000094180000E80300000100000000000000000000006B71418AD73FF34686F4E453C52CFA8D00000000000000000000000000000000 | |||
| (PID) Process: | (7044) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000007B736F9FB602DC01841B0000F4160000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7044) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000007B736F9FB602DC01841B0000E80F0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7044) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000007B736F9FB602DC01841B000080090000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7044) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000007B736F9FB602DC01841B000074120000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3400) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000011DBFC9EB602DC01480D000088190000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
78
Suspicious files
48
Text files
105
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | Cisco-Secure-Client-Windows.x64.exe | C:\Users\admin\AppData\Local\Temp\Cisco-AnyConnect-win-4.11.msi | — | |
MD5:— | SHA256:— | |||
| 3400 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3400 | msiexec.exe | C:\Windows\Installer\1942ac.msi | — | |
MD5:— | SHA256:— | |||
| 3400 | msiexec.exe | C:\Windows\Installer\MSI4725.tmp | — | |
MD5:— | SHA256:— | |||
| 760 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | der | |
MD5:D87EFFE6C7ECB07A57B8104223379162 | SHA256:F947FA5CCEC777A464D31C0073C2816E8124CCB7136BDD233F0FF8EF088B47F0 | |||
| 760 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:EE4DCD8A33FDE7BBE35C5207B20280EE | SHA256:8394013526F62F67924A9448D9CF9BAA4990F37342B9C68D66D20E49E6514F32 | |||
| 760 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSID647.tmp | executable | |
MD5:BDA991D64E27606AC1D3ABB659A0B33B | SHA256:FFEA8222126B77F8DA93E27EDBADEB8B97FB023EF0D6A51522C35688F66283CA | |||
| 760 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSID669.tmp | executable | |
MD5:BDA991D64E27606AC1D3ABB659A0B33B | SHA256:FFEA8222126B77F8DA93E27EDBADEB8B97FB023EF0D6A51522C35688F66283CA | |||
| 760 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSID658.tmp | executable | |
MD5:BDA991D64E27606AC1D3ABB659A0B33B | SHA256:FFEA8222126B77F8DA93E27EDBADEB8B97FB023EF0D6A51522C35688F66283CA | |||
| 3400 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{8a41716b-3fd7-46f3-86f4-e453c52cfa8d}_OnDiskSnapshotProp | binary | |
MD5:EF583C289FCDB17C8151D2770FCDE2F4 | SHA256:20A0DD95178B05C26D552EAEE24B256A0FF551415FE28C7DCC3C339DC42D205C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
36
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3644 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
760 | msiexec.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6664 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6664 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
760 | msiexec.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
760 | msiexec.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAi2zK41dGls0yj5mh7CGx0%3D | unknown | — | — | whitelisted |
2964 | Cisco-Secure-Client-Windows.x64.exe | GET | — | 188.114.97.3:80 | http://vvindowsupdate.org/Cisco-AnyConnect-win-4.11.msi | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
472 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2964 | Cisco-Secure-Client-Windows.x64.exe | 188.114.97.3:80 | vvindowsupdate.org | CLOUDFLARENET | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
760 | msiexec.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
3644 | svchost.exe | 40.126.32.138:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3644 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
vvindowsupdate.org |
| unknown |
praise-ambien-infected-inform.trycloudflare.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to Commonly Abused Cloudflare Domain (trycloudflare .com) |
2200 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Cloudflare Tunnel (TryCloudflare) |
Process | Message |
|---|---|
VACon64.exe | VACON: -install
|
vpnagent.exe | [I-1864-7156|CreateCbasedInterface] Instanced shim v5.1.4.55 |
vpnagent.exe | [I-1864-6452|CPlannedDisruptionHandler::workerThreadFn] Starting worker thread execution |