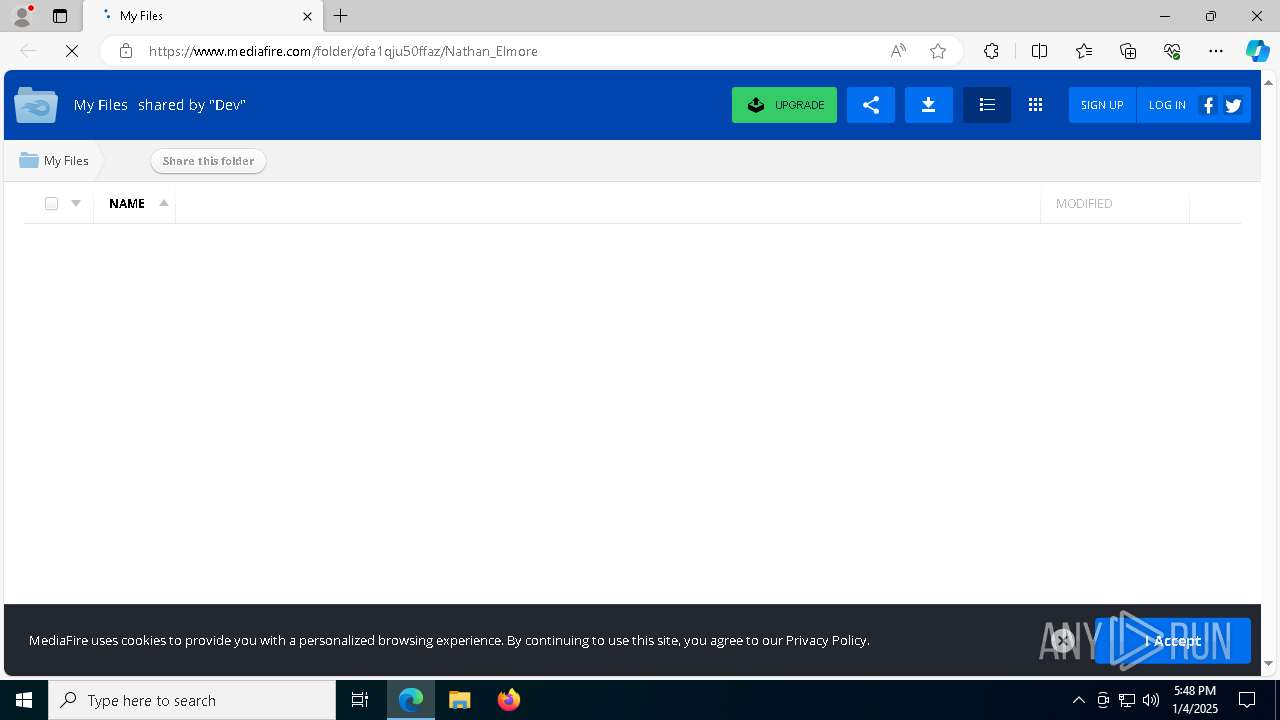
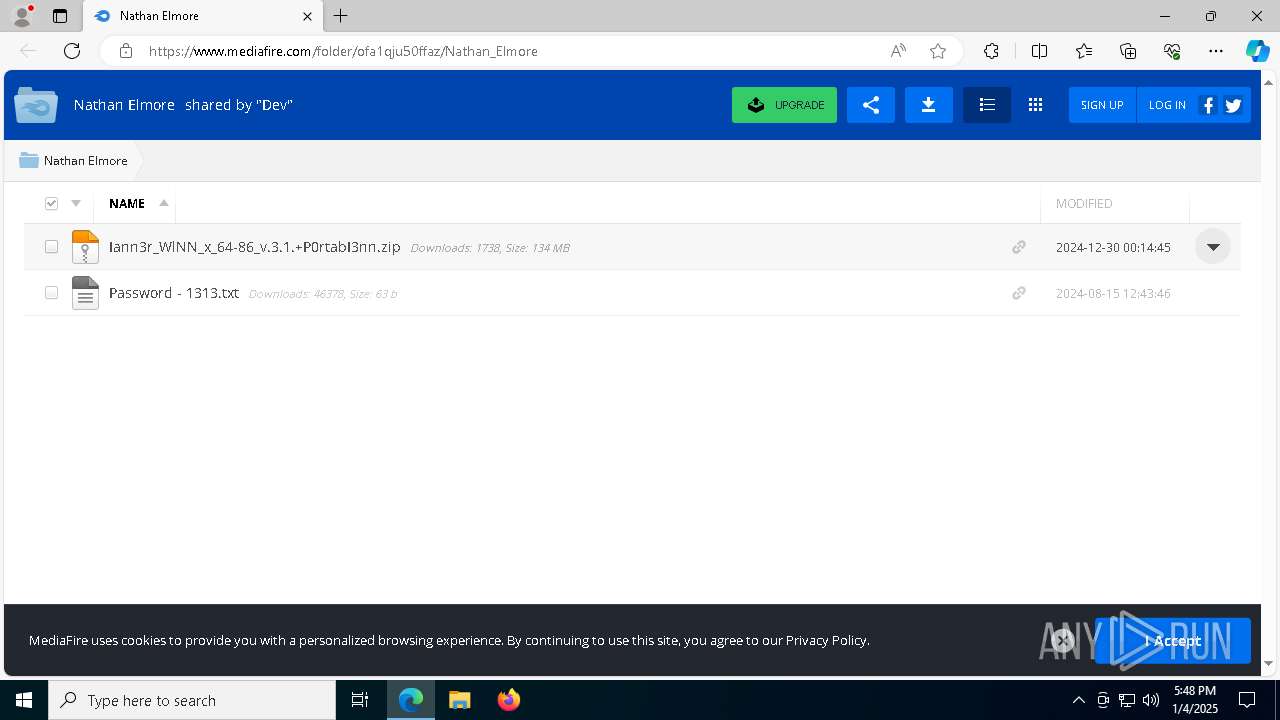
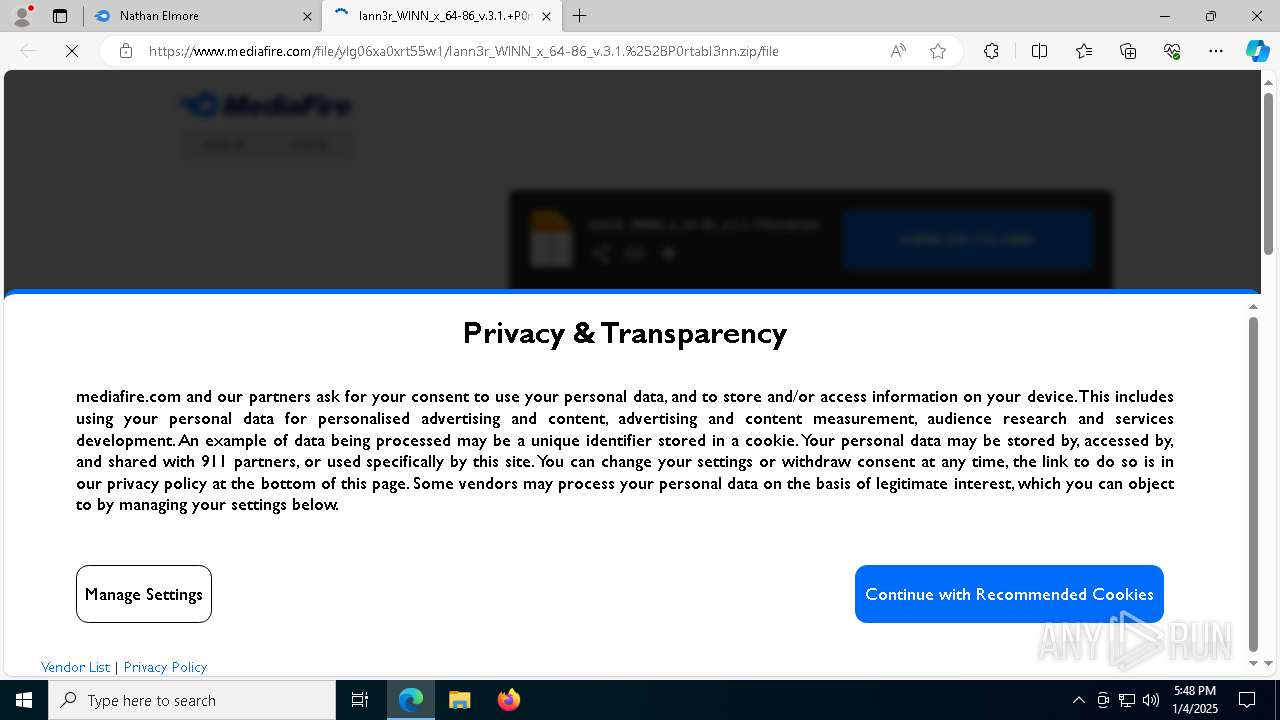
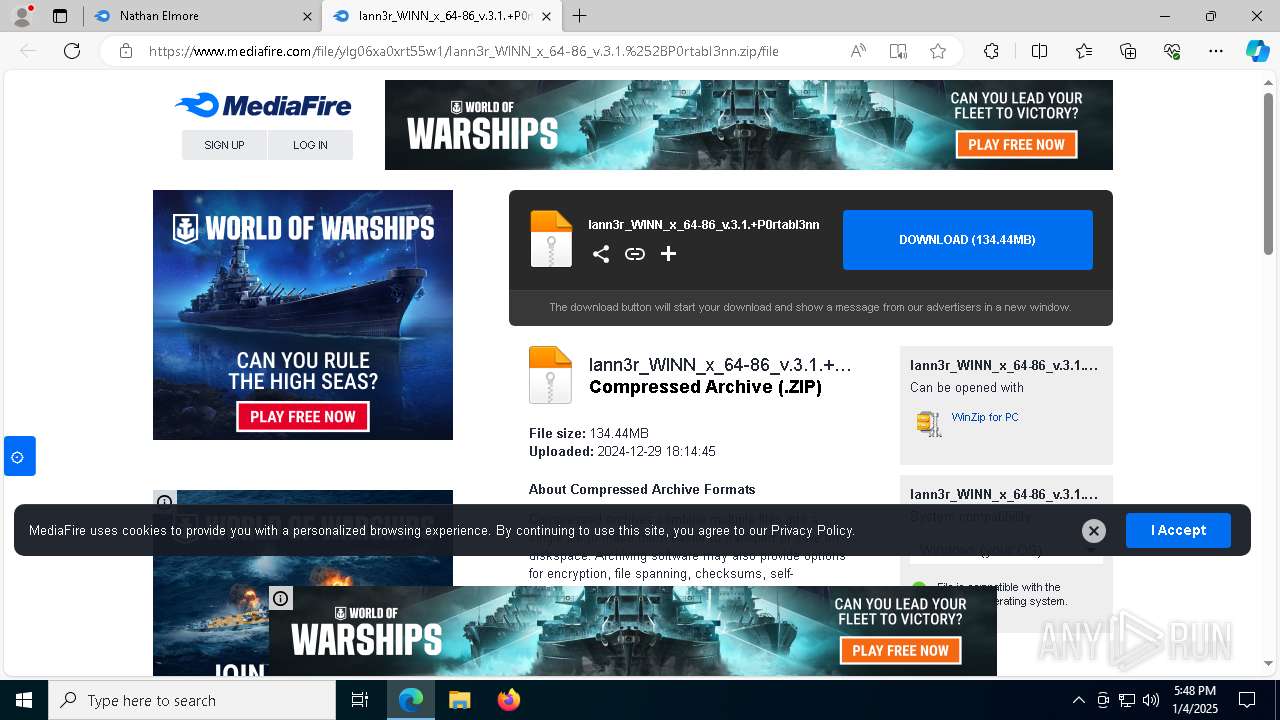
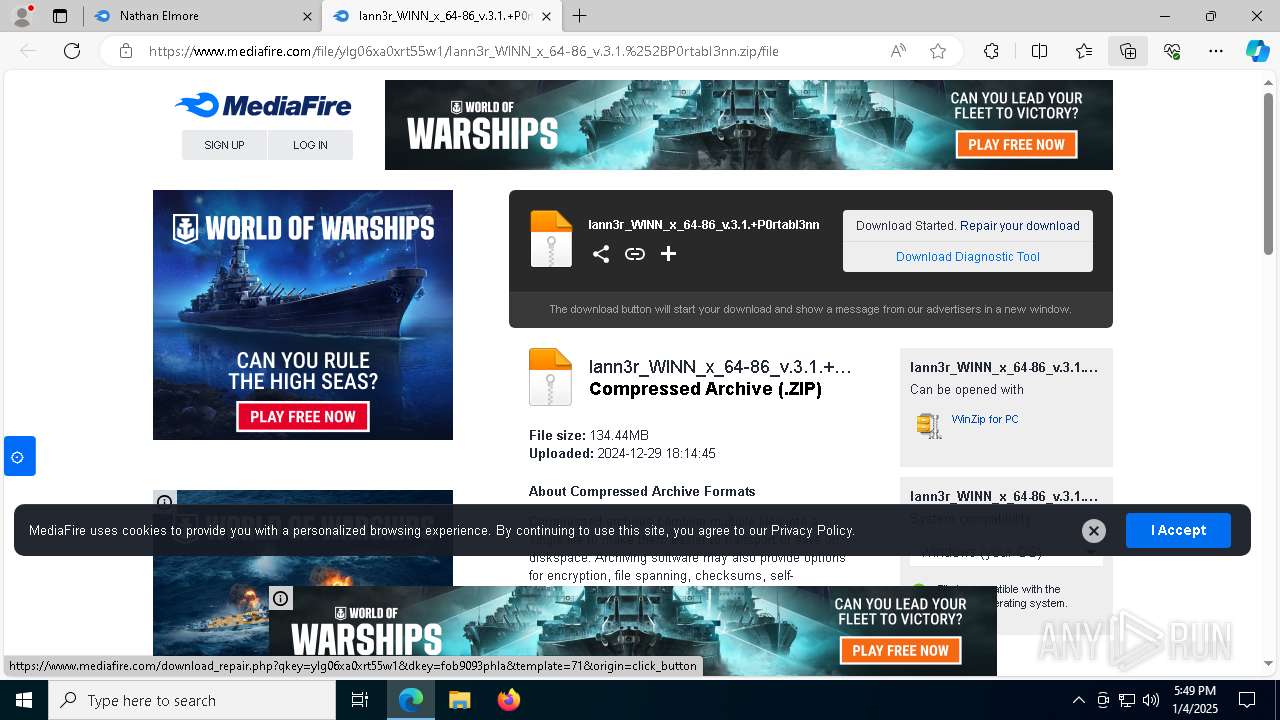
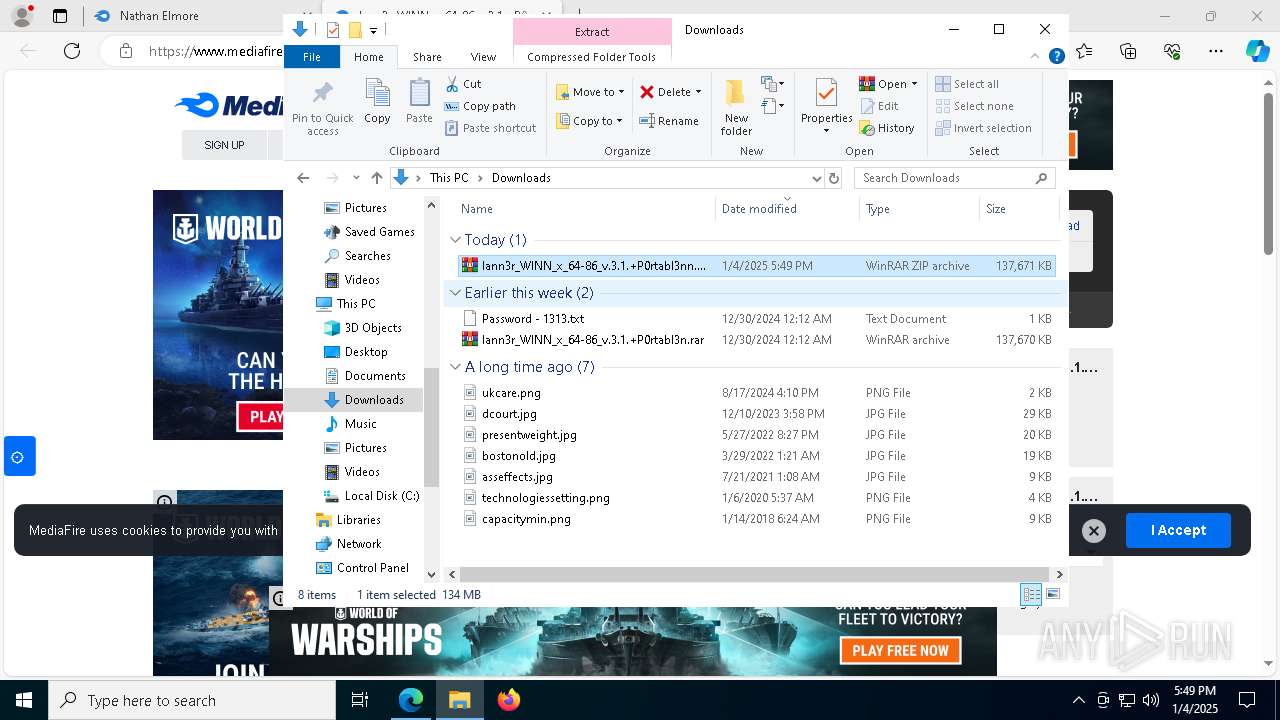
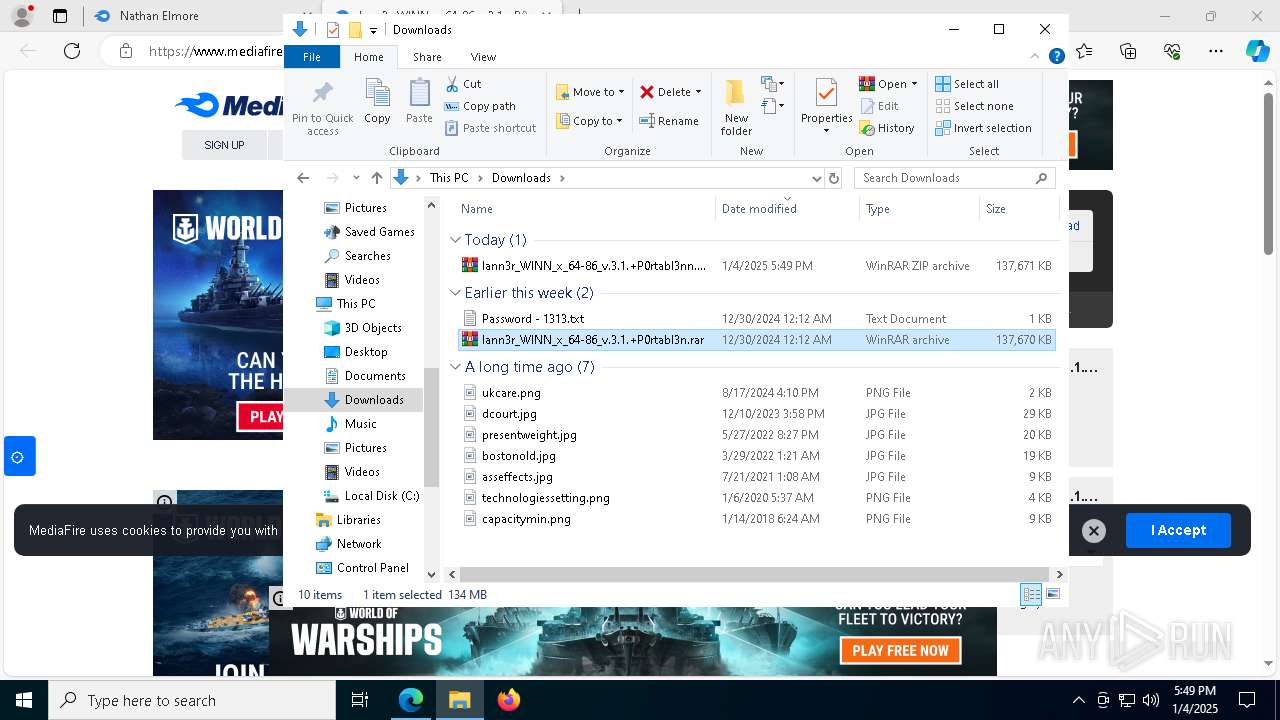
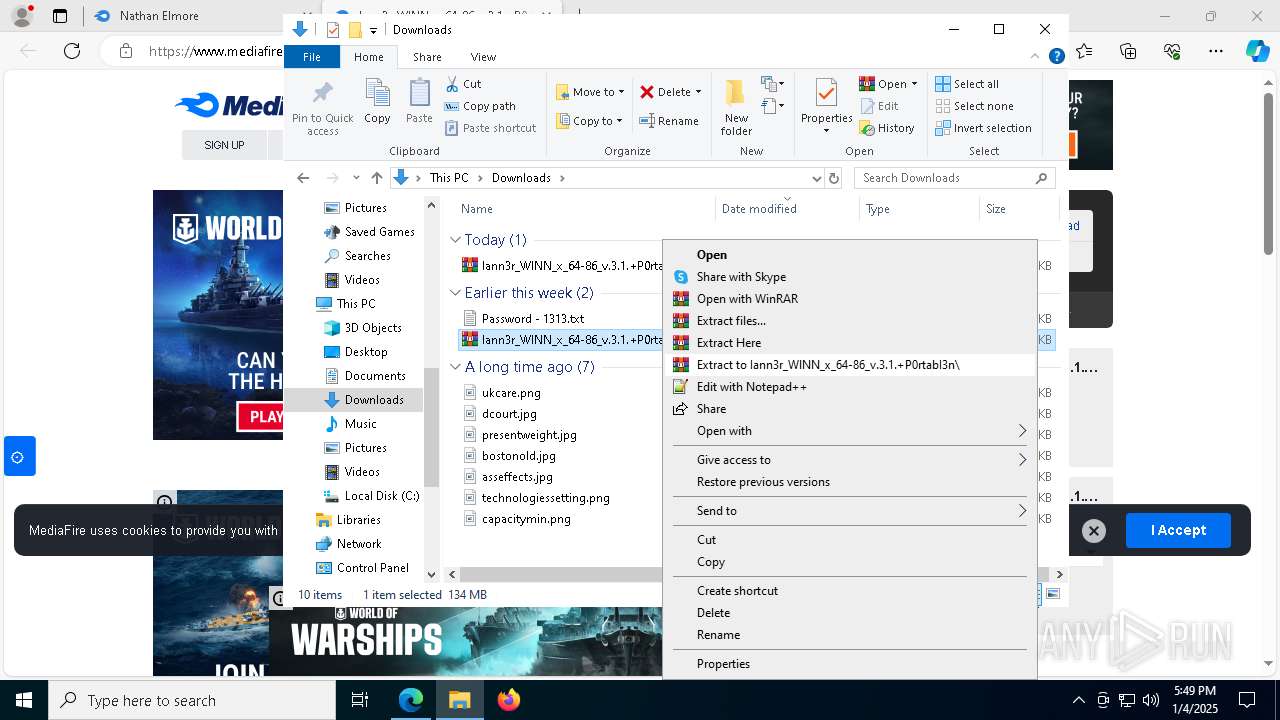
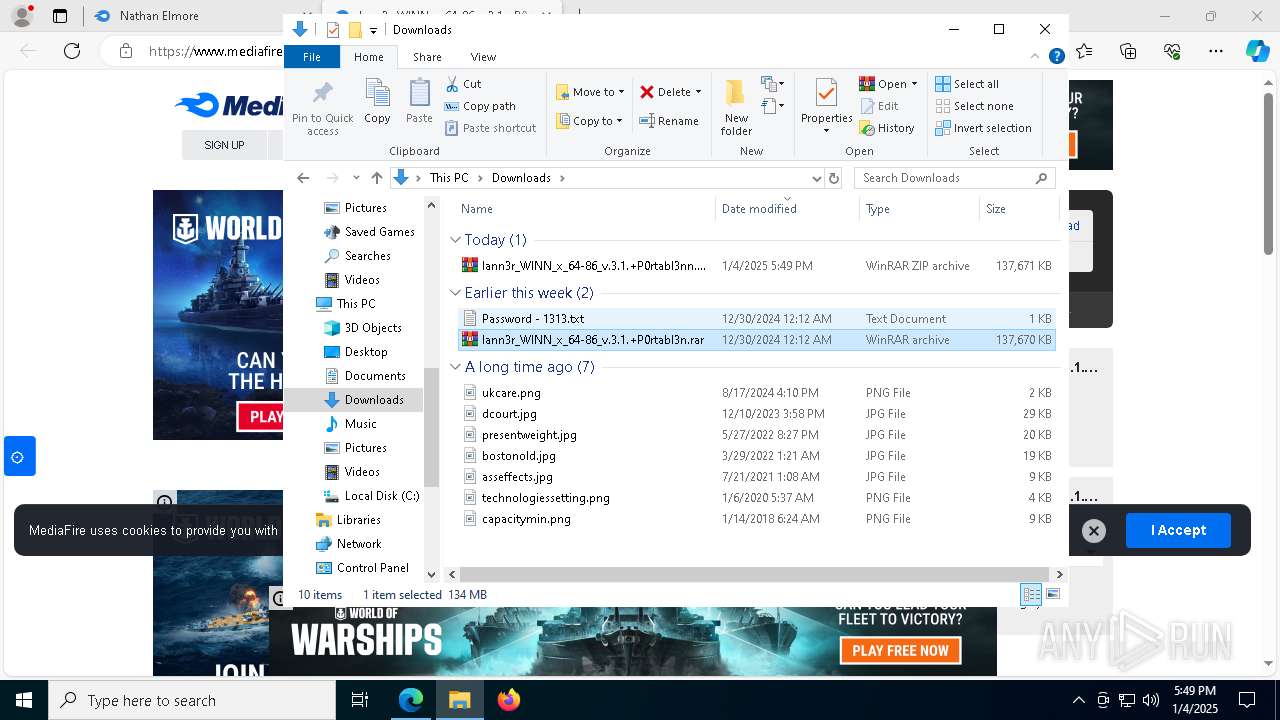
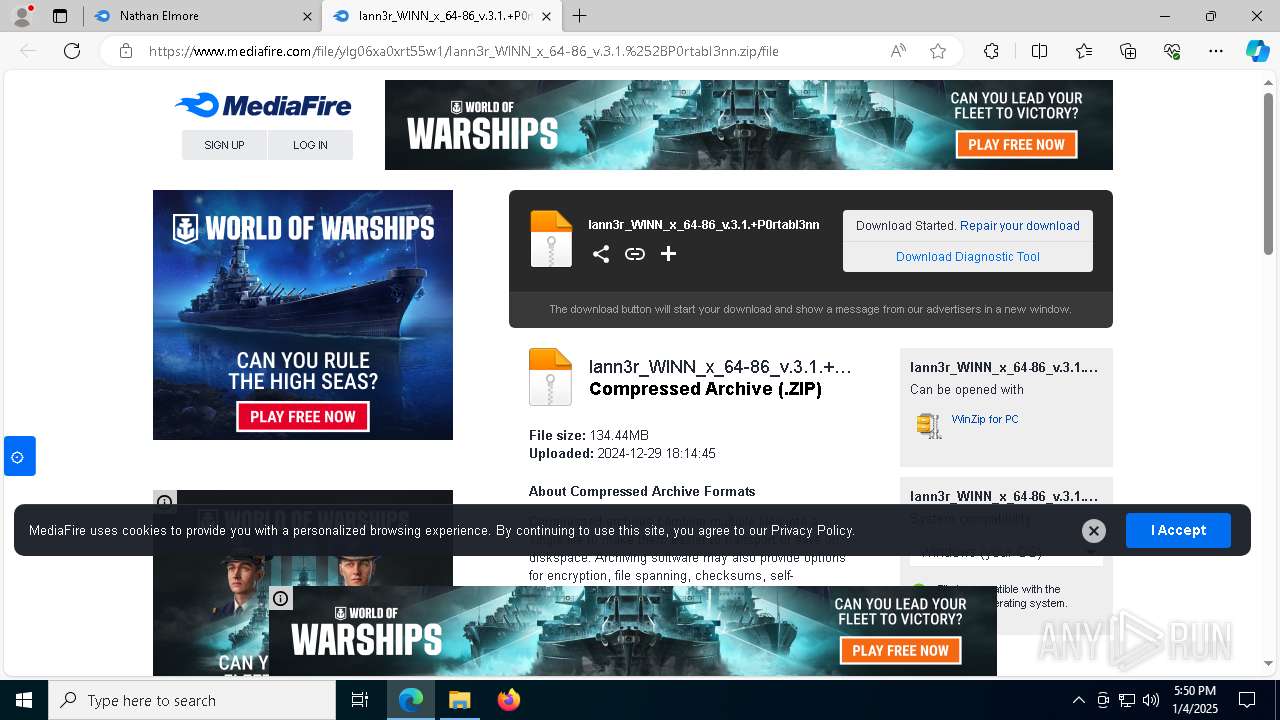
| URL: | https://www.mediafire.com/folder/ofa1qju50ffaz/Nathan_Elmore |
| Full analysis: | https://app.any.run/tasks/4623f44e-4bda-49d0-983d-6126953dc9a0 |
| Verdict: | Malicious activity |
| Threats: | INC Ransomware is a ransomware-as-a-service (RaaS) spotted in mid-2023. It targets industries like retail, real estate, finance, healthcare, and education, primarily in the U.S. and UK. It encrypts and exfiltrates data demanding a ransom. It employs advanced evasion techniques, destroys backup, and abuses legitimate system tools at all the stages of the kill chain. |
| Analysis date: | January 04, 2025, 17:48:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
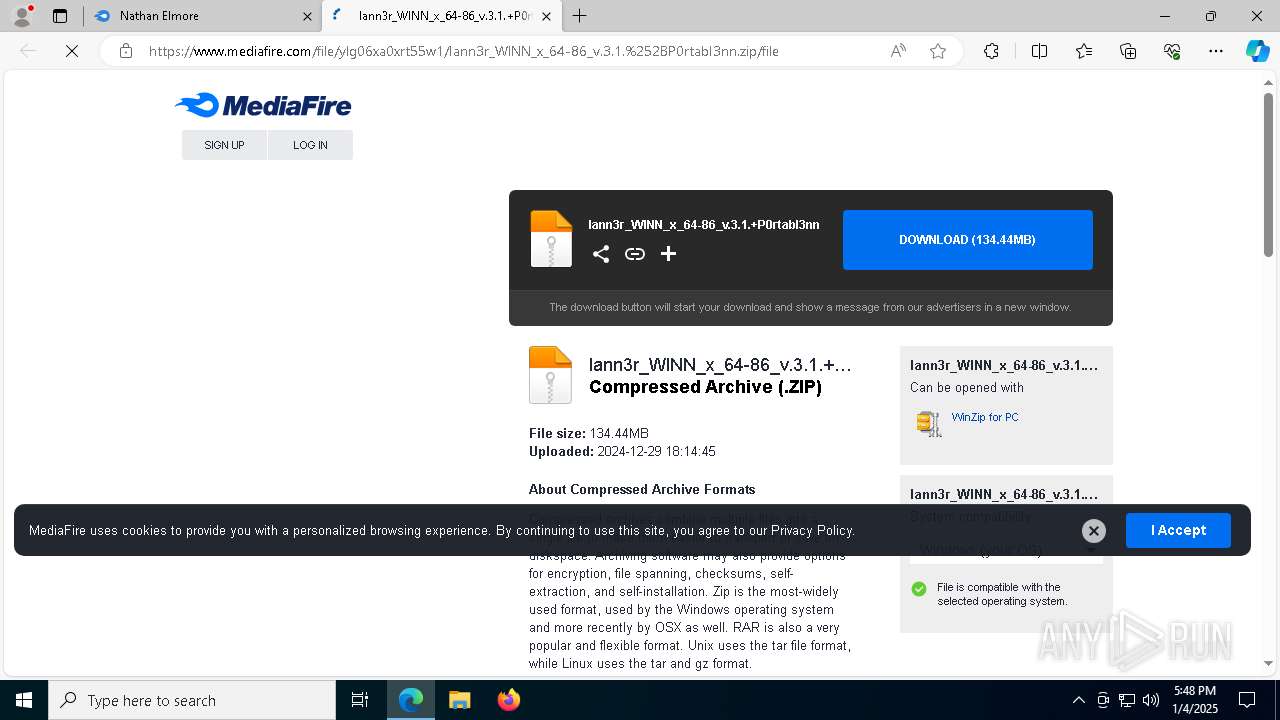
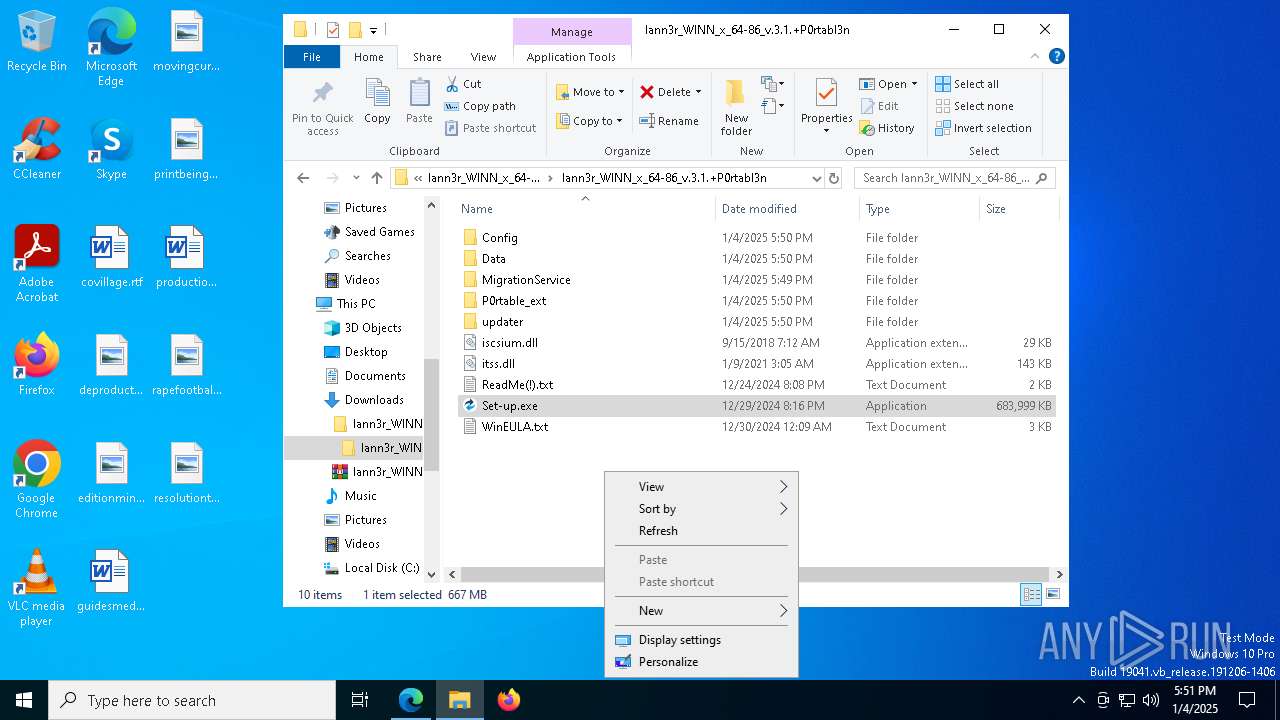
| MD5: | 1C23C3B46B361EFF2A35B76D7308AAE0 |
| SHA1: | CA1CEEEE3EED55D9440448D1F276F91AED4E2CDF |
| SHA256: | 14D6666EF529D255837795922934F2BE280DA442104B8059258273E243AA8A40 |
| SSDEEP: | 3:N8DSLw3eGUbKpUUoQHkZgJA:2OLw3eG+eUUVJJA |
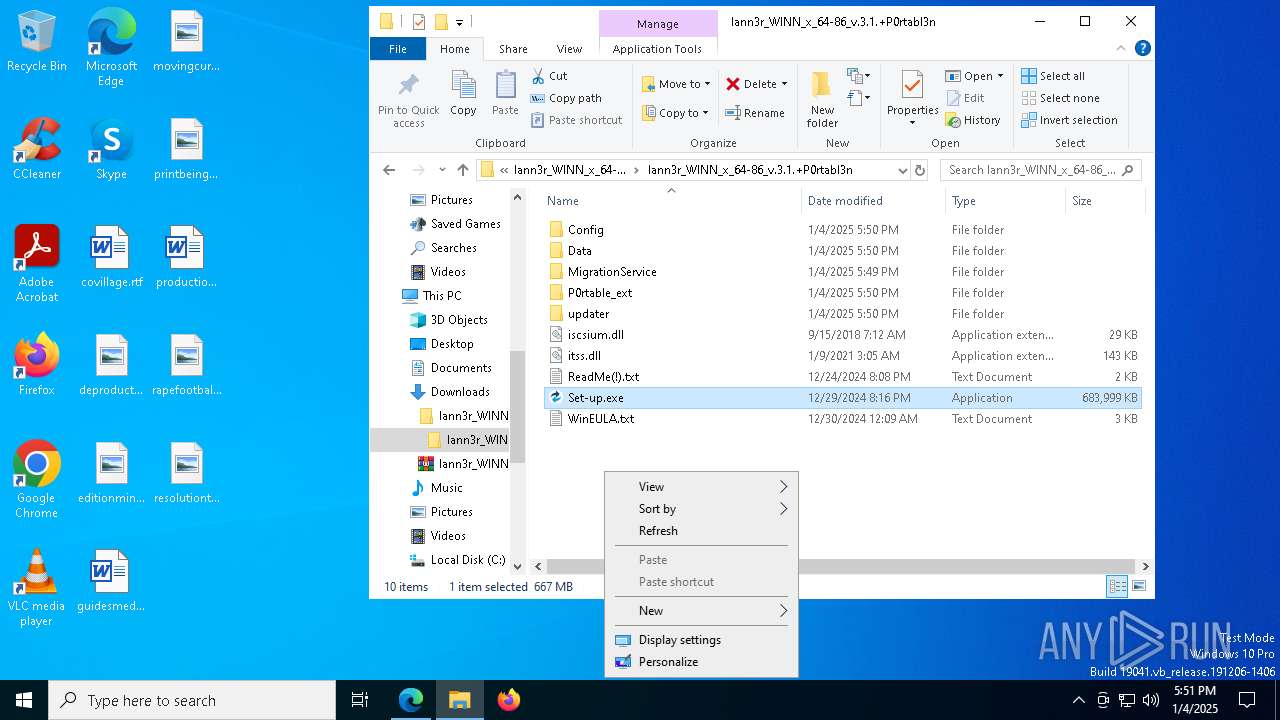
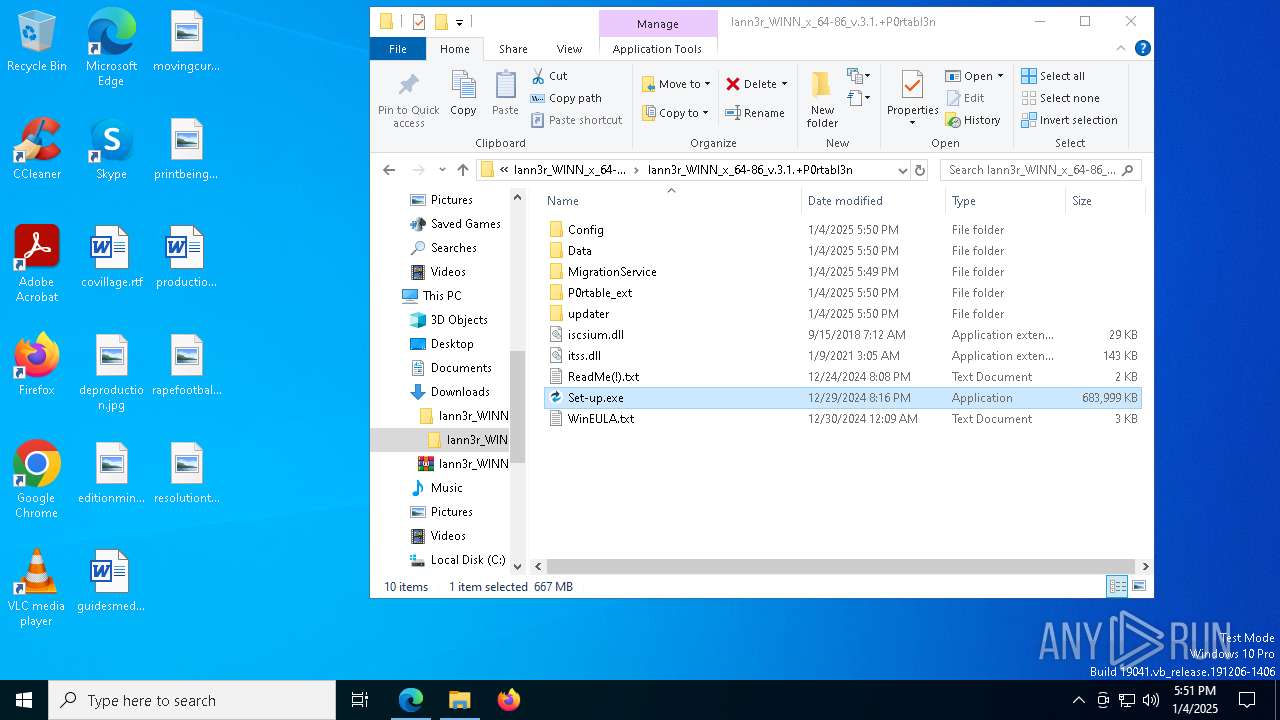
MALICIOUS
INC has been detected
- WinRAR.exe (PID: 3820)
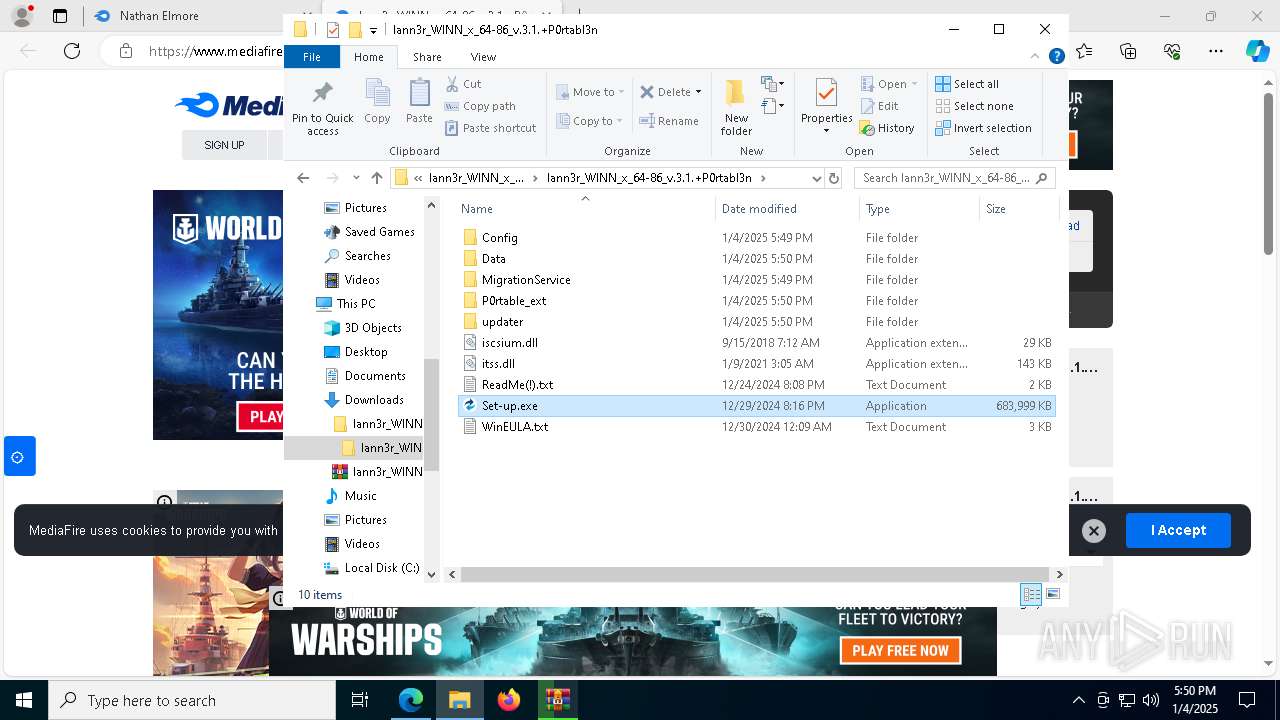
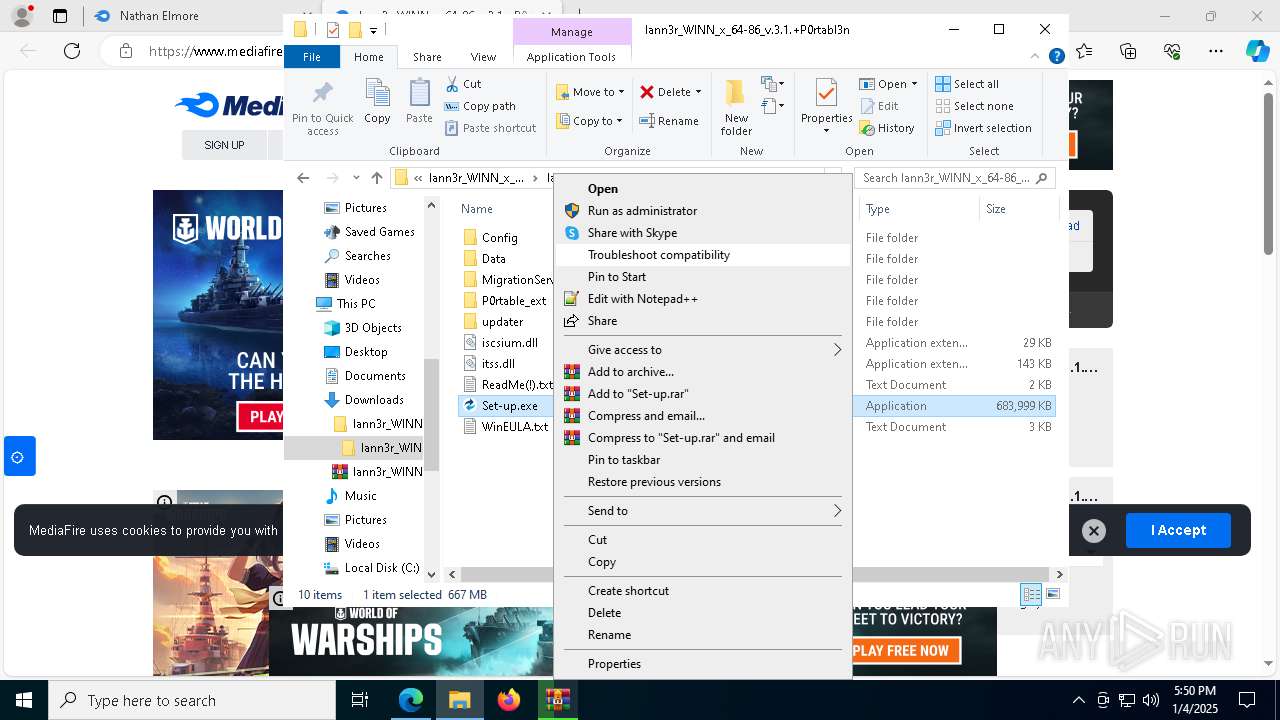
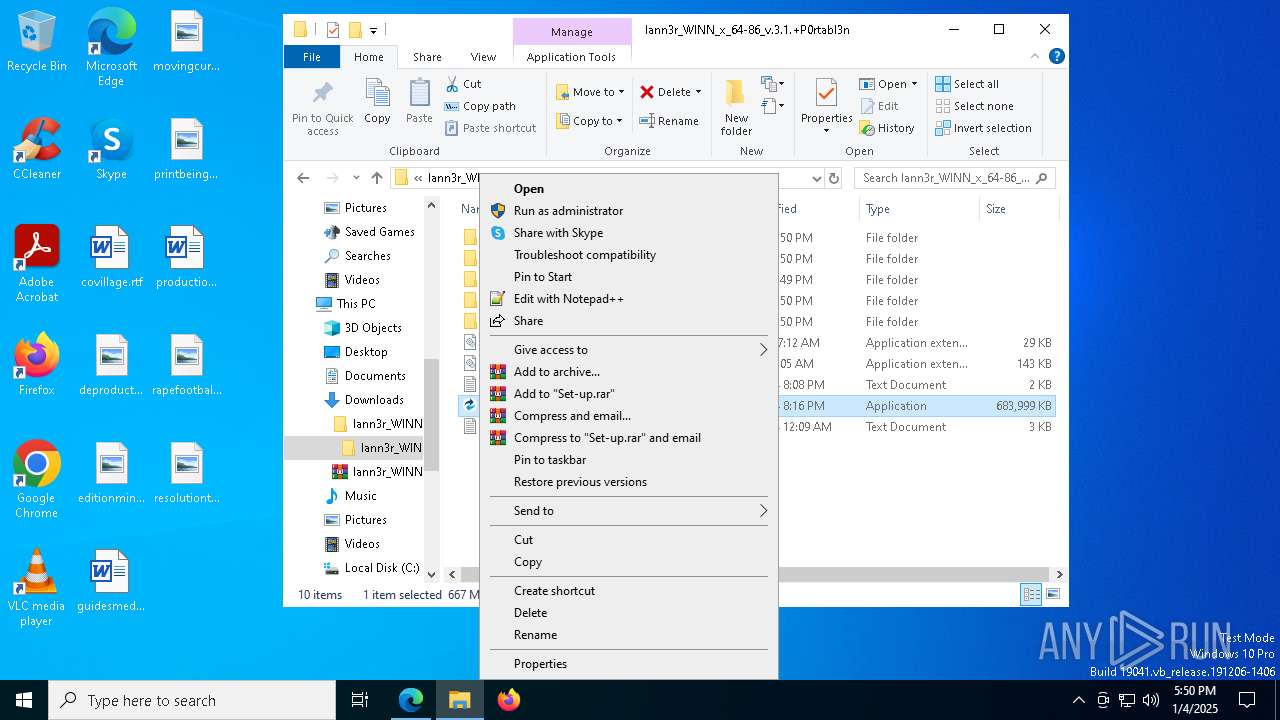
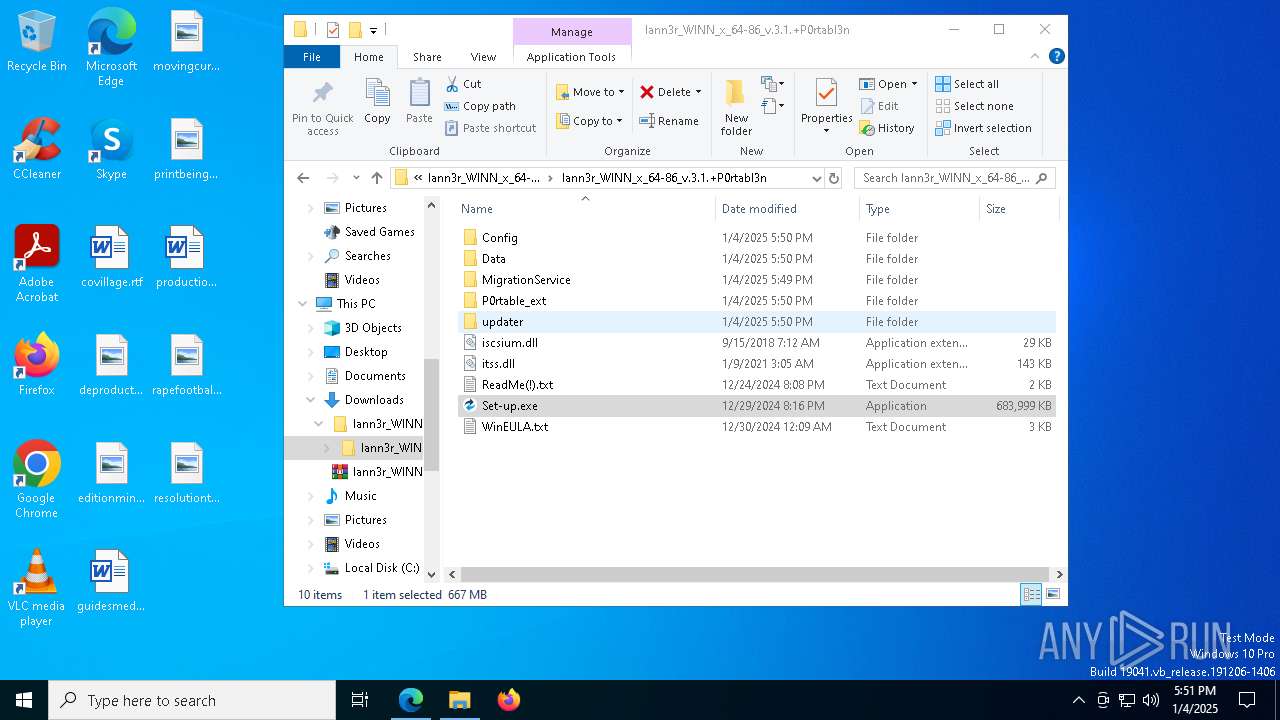
Executing a file with an untrusted certificate
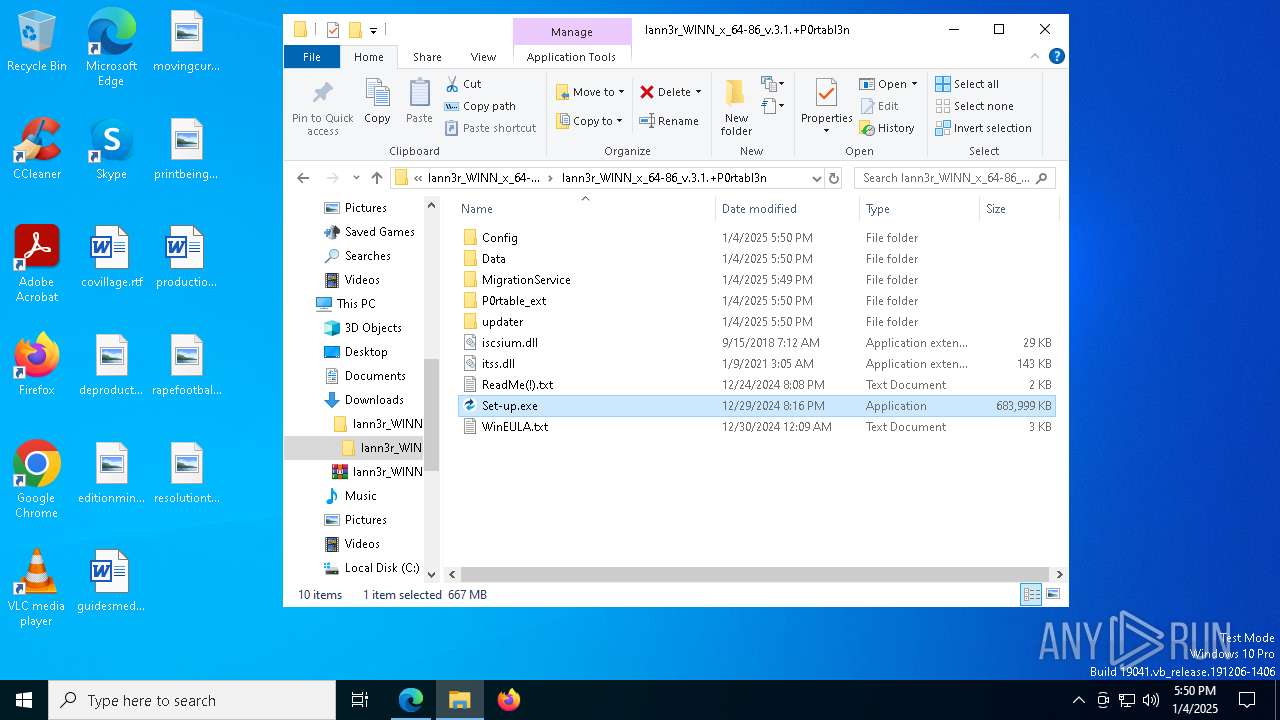
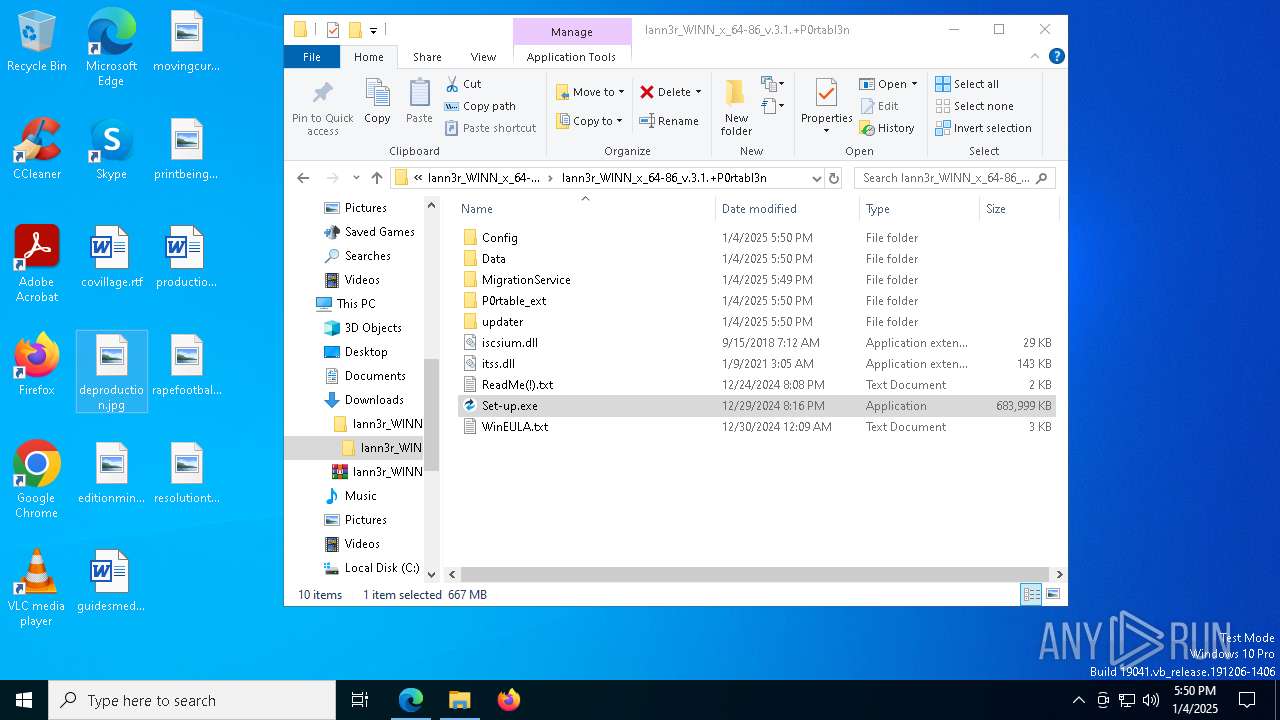
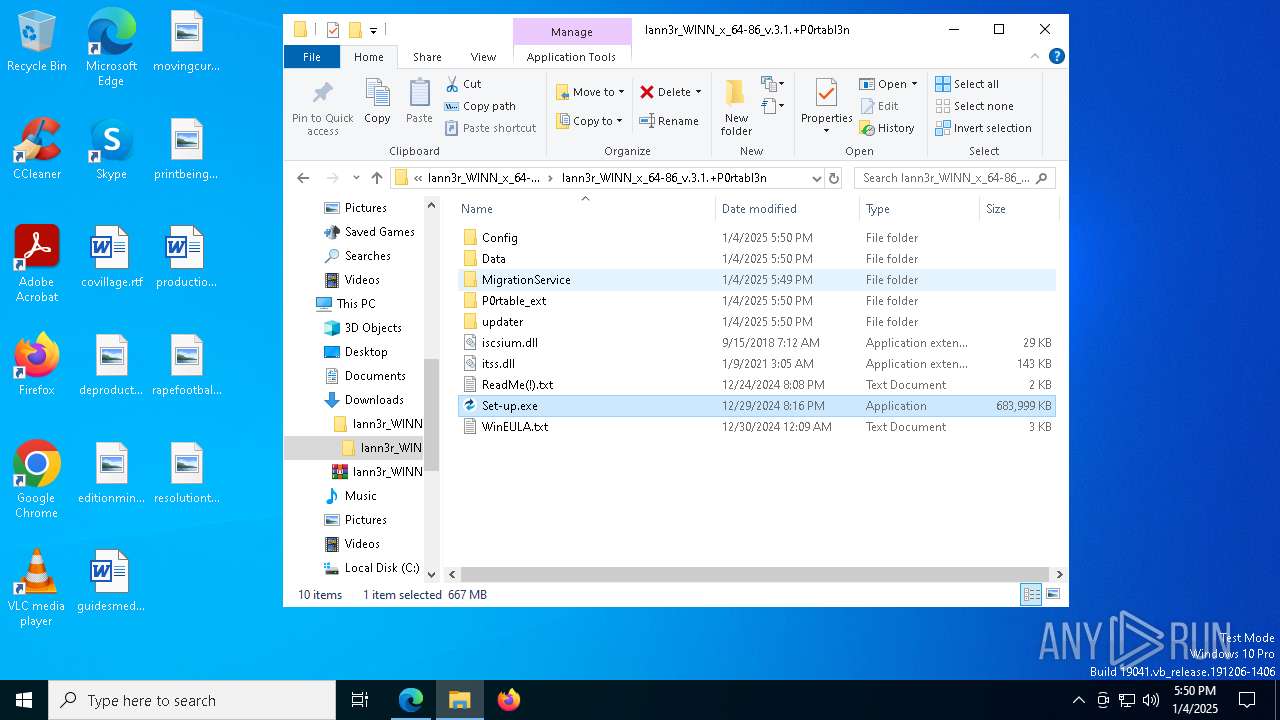
- Set-up.exe (PID: 7048)
- Set-up.exe (PID: 3092)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.exe (PID: 4864)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.exe (PID: 7036)
- R4O6AYWL3QVGJGB8MNCU1VO7.exe (PID: 7812)
- R4O6AYWL3QVGJGB8MNCU1VO7.exe (PID: 2072)
- Set-up.exe (PID: 4556)
- GR516RQU6ZU6Z2EDC2882C3.exe (PID: 7900)
- GR516RQU6ZU6Z2EDC2882C3.exe (PID: 8032)
- Set-up.exe (PID: 2216)
- WJZHF0YIRO44XO77SFM8KZGUK.exe (PID: 6976)
- WJZHF0YIRO44XO77SFM8KZGUK.exe (PID: 8084)
LUMMA mutex has been found
- Set-up.exe (PID: 7048)
- Set-up.exe (PID: 3092)
- Set-up.exe (PID: 4556)
- Set-up.exe (PID: 2216)
Actions looks like stealing of personal data
- Set-up.exe (PID: 7048)
- Set-up.exe (PID: 3092)
- Set-up.exe (PID: 4556)
- Set-up.exe (PID: 2216)
Steals credentials from Web Browsers
- Set-up.exe (PID: 7048)
- Set-up.exe (PID: 3092)
- Set-up.exe (PID: 4556)
- Set-up.exe (PID: 2216)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 5920)
- tasklist.exe (PID: 3876)
- find.exe (PID: 6908)
- cmd.exe (PID: 7280)
- tasklist.exe (PID: 6448)
- find.exe (PID: 6300)
- find.exe (PID: 8188)
- cmd.exe (PID: 7988)
- tasklist.exe (PID: 8132)
- cmd.exe (PID: 3812)
- tasklist.exe (PID: 2736)
- find.exe (PID: 7856)
- cmd.exe (PID: 1988)
- tasklist.exe (PID: 1220)
- find.exe (PID: 7056)
- cmd.exe (PID: 3700)
- tasklist.exe (PID: 7228)
- cmd.exe (PID: 6380)
- find.exe (PID: 7020)
- cmd.exe (PID: 7520)
- tasklist.exe (PID: 3076)
- find.exe (PID: 8116)
- tasklist.exe (PID: 7716)
- find.exe (PID: 7644)
- cmd.exe (PID: 4244)
- tasklist.exe (PID: 8036)
- find.exe (PID: 8028)
- cmd.exe (PID: 8076)
- tasklist.exe (PID: 4136)
- find.exe (PID: 7816)
- cmd.exe (PID: 3952)
- find.exe (PID: 8080)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 4204)
- tasklist.exe (PID: 5828)
- find.exe (PID: 5848)
- find.exe (PID: 7560)
- tasklist.exe (PID: 968)
- cmd.exe (PID: 7240)
- tasklist.exe (PID: 3364)
- find.exe (PID: 4864)
- tasklist.exe (PID: 7940)
- find.exe (PID: 7880)
- cmd.exe (PID: 6996)
- tasklist.exe (PID: 7308)
- cmd.exe (PID: 5920)
- tasklist.exe (PID: 7524)
- find.exe (PID: 2572)
- find.exe (PID: 4188)
- cmd.exe (PID: 244)
- tasklist.exe (PID: 3436)
- cmd.exe (PID: 1684)
- tasklist.exe (PID: 4540)
- tasklist.exe (PID: 1988)
- cmd.exe (PID: 5848)
- find.exe (PID: 1612)
- cmd.exe (PID: 4428)
- tasklist.exe (PID: 2224)
- find.exe (PID: 2496)
- find.exe (PID: 7824)
SUSPICIOUS
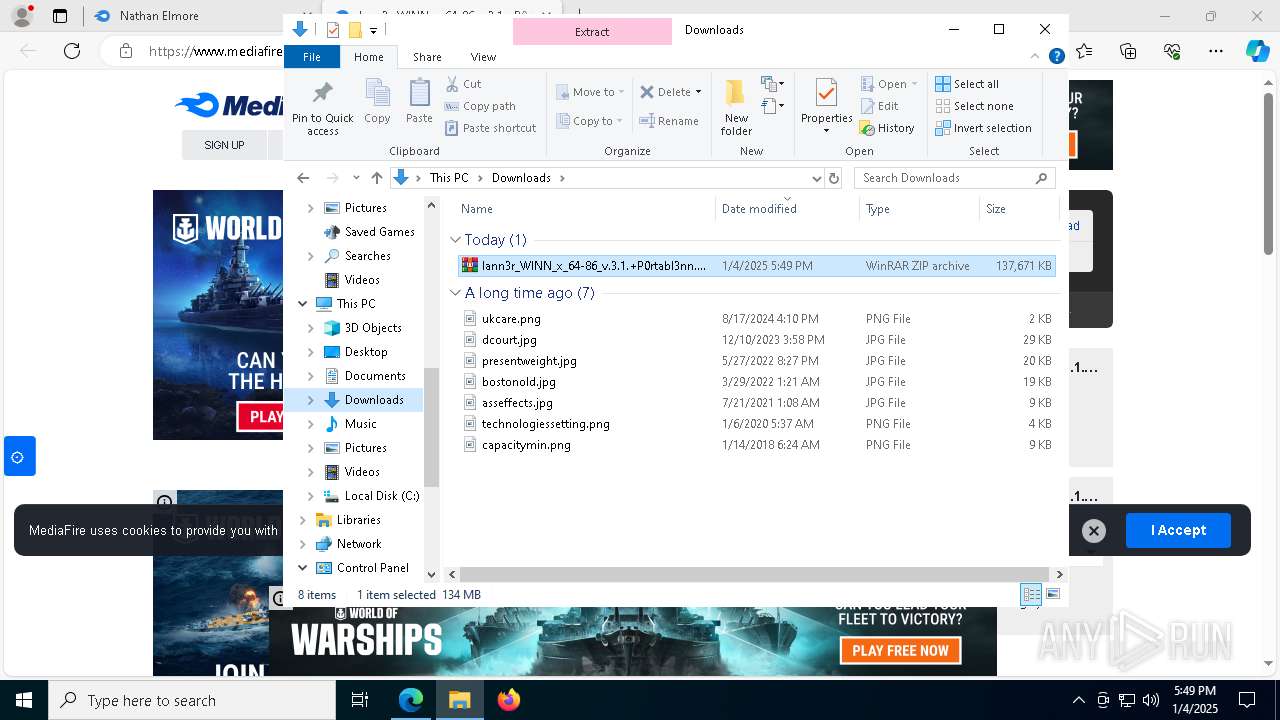
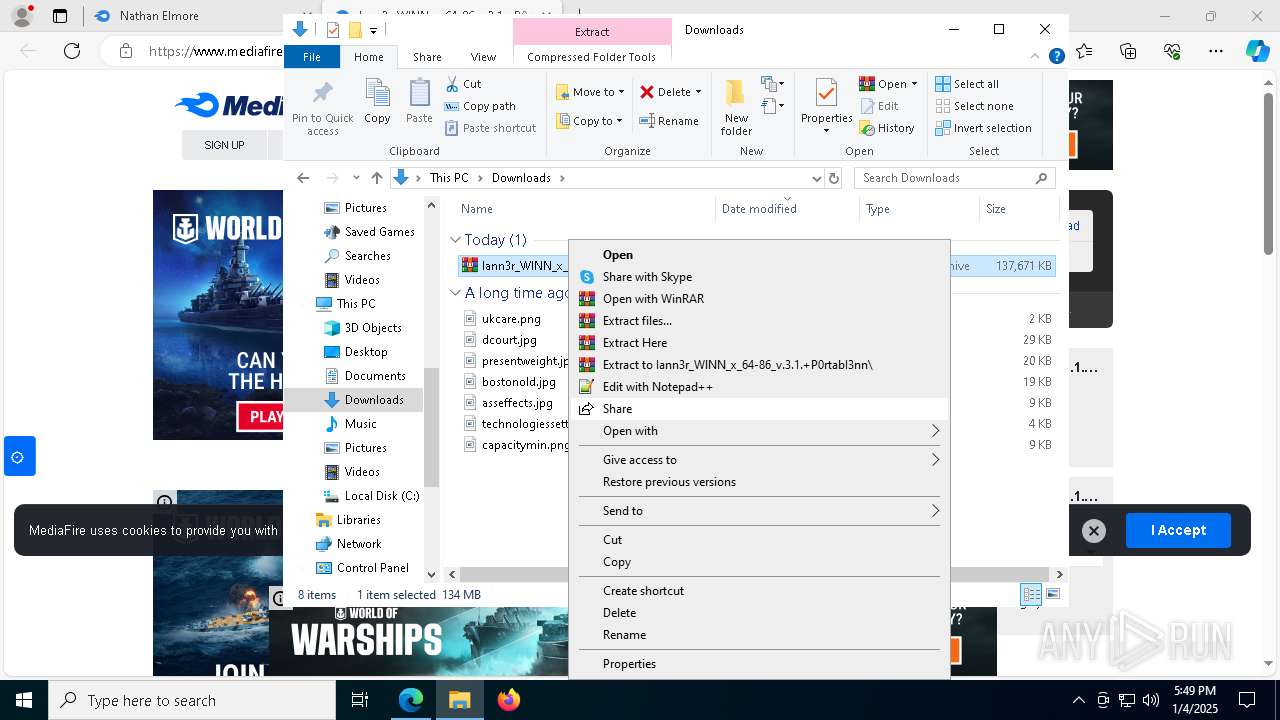
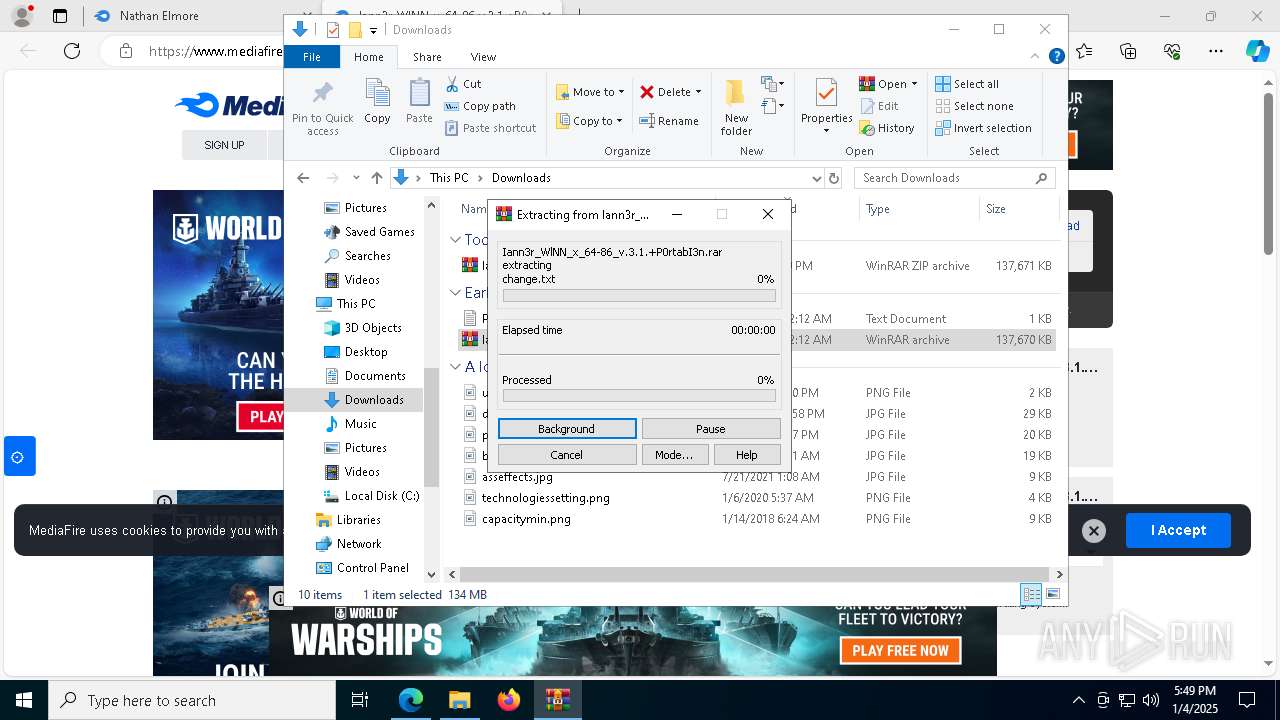
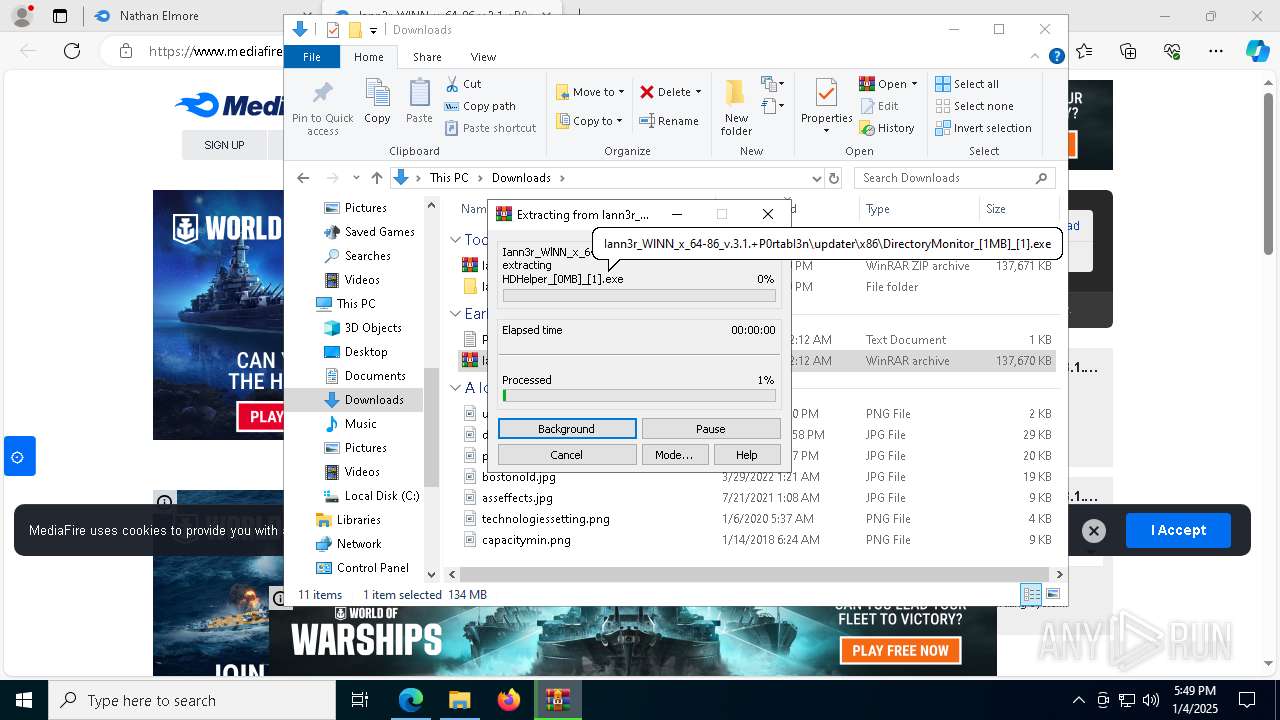
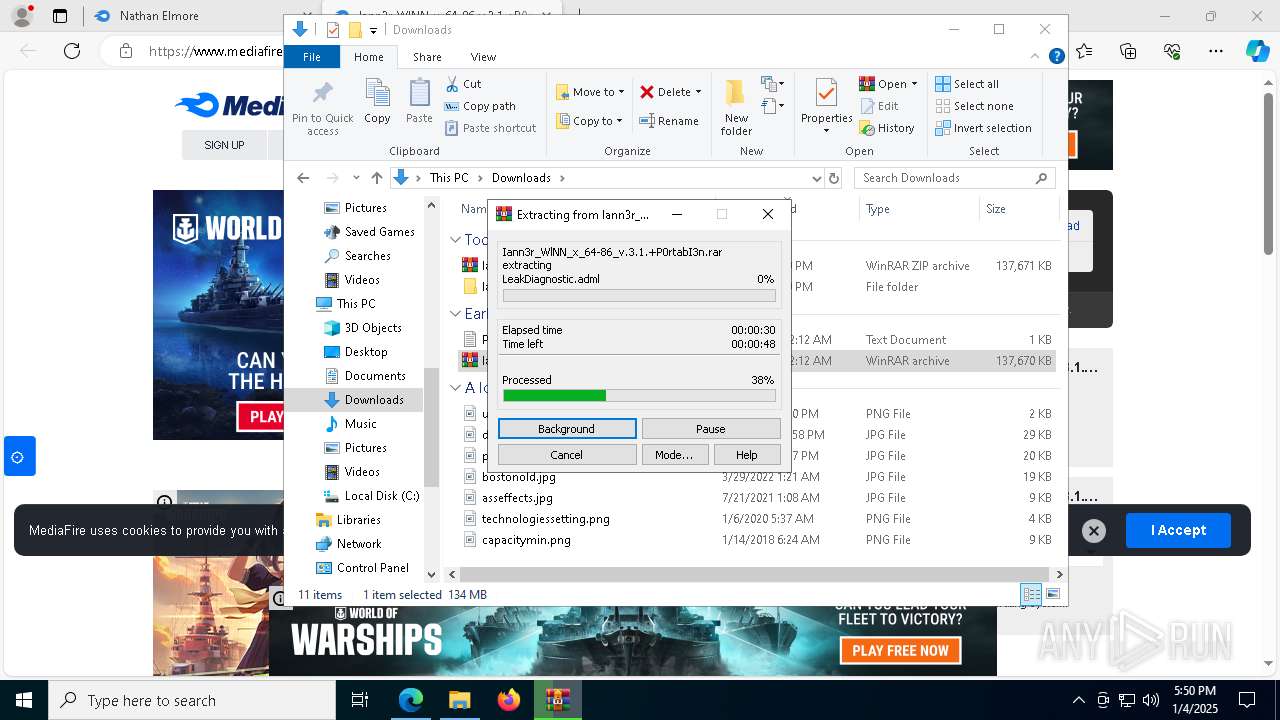
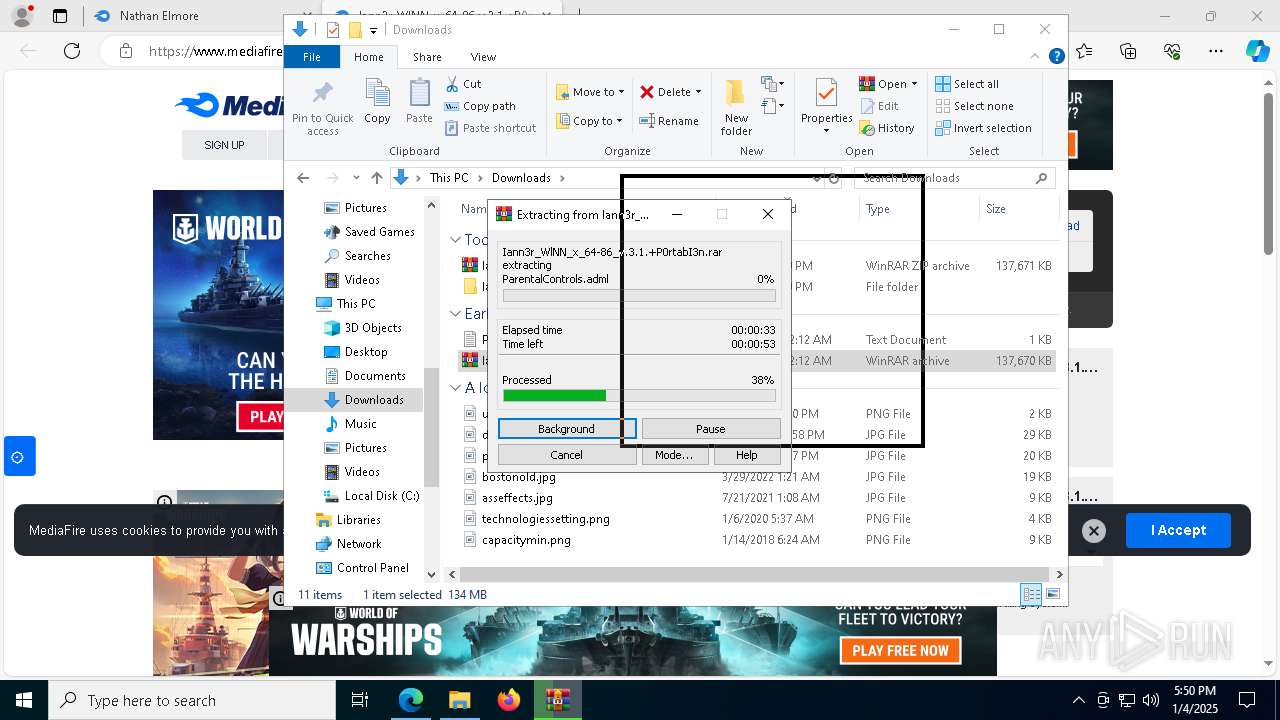
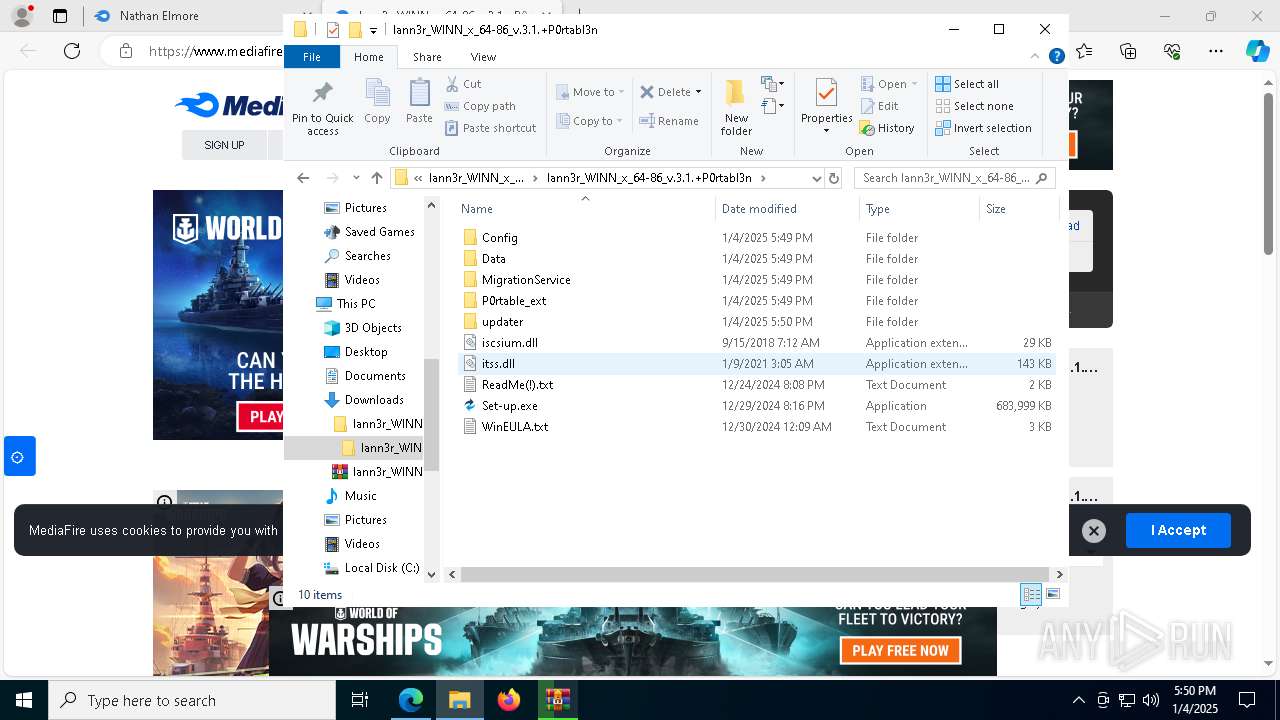
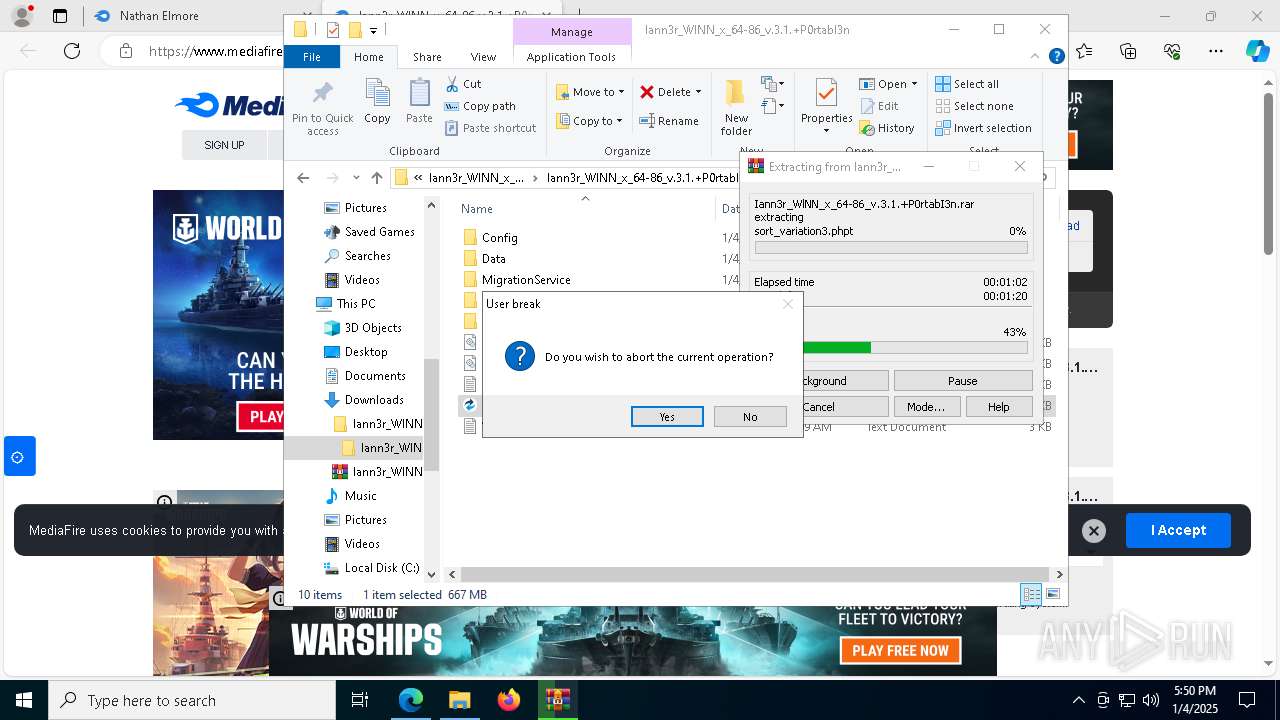
Process drops legitimate windows executable
- WinRAR.exe (PID: 3820)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 3820)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 8168)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7896)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 5236)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7324)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 7888)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 3288)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 5788)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 6152)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 7832)
Executable content was dropped or overwritten
- Set-up.exe (PID: 7048)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.exe (PID: 4864)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7896)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7324)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.exe (PID: 7036)
- Set-up.exe (PID: 3092)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 5236)
- R4O6AYWL3QVGJGB8MNCU1VO7.exe (PID: 7812)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 3288)
- R4O6AYWL3QVGJGB8MNCU1VO7.exe (PID: 2072)
- Set-up.exe (PID: 4556)
- GR516RQU6ZU6Z2EDC2882C3.exe (PID: 8032)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 7888)
- GR516RQU6ZU6Z2EDC2882C3.exe (PID: 7900)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 5788)
- Set-up.exe (PID: 2216)
- WJZHF0YIRO44XO77SFM8KZGUK.exe (PID: 6976)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 6152)
- WJZHF0YIRO44XO77SFM8KZGUK.exe (PID: 8084)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 7832)
Reads the Windows owner or organization settings
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7896)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7324)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 5236)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 3288)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 7888)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 5788)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 6152)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 7832)
Uses TIMEOUT.EXE to delay execution
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7324)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 3288)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 5788)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 7832)
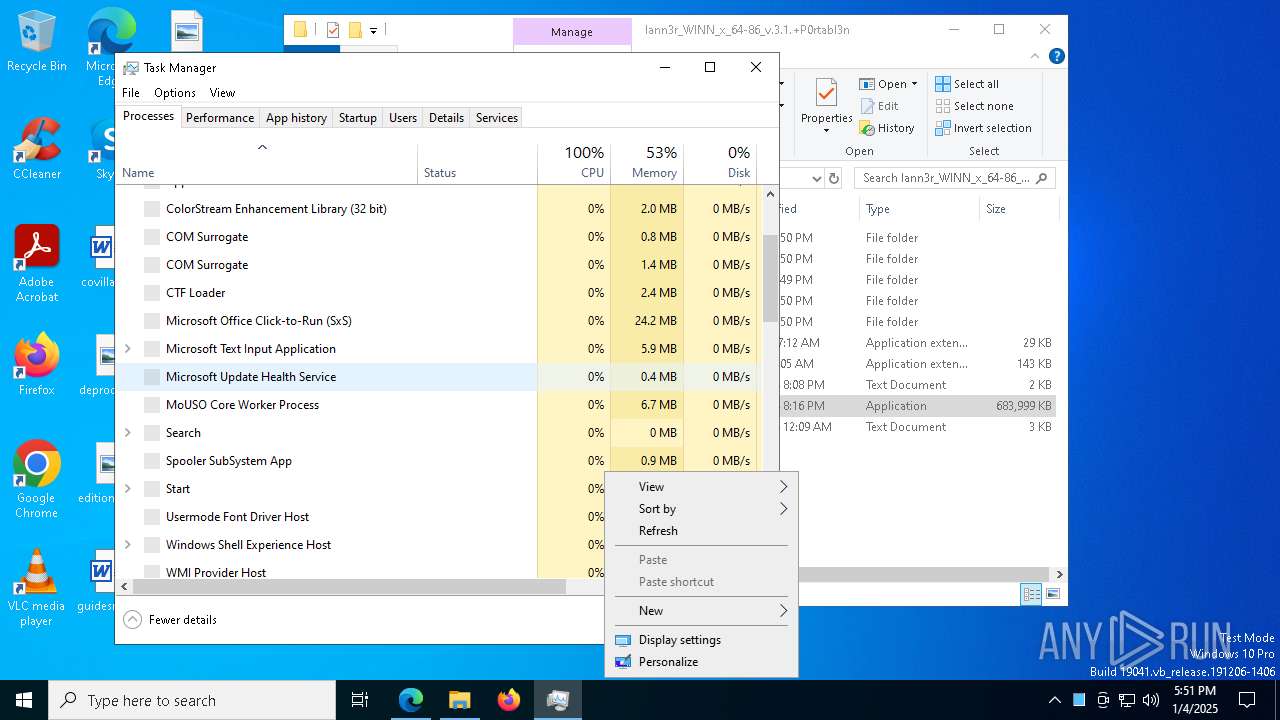
Get information on the list of running processes
- cmd.exe (PID: 5920)
- cmd.exe (PID: 4244)
- cmd.exe (PID: 7280)
- cmd.exe (PID: 7988)
- cmd.exe (PID: 3812)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7324)
- cmd.exe (PID: 1988)
- cmd.exe (PID: 3700)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 6380)
- cmd.exe (PID: 7520)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 3288)
- cmd.exe (PID: 3952)
- cmd.exe (PID: 4244)
- cmd.exe (PID: 8076)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 6328)
- cmd.exe (PID: 4204)
- cmd.exe (PID: 7240)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 5788)
- cmd.exe (PID: 6996)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 7832)
- cmd.exe (PID: 5920)
- cmd.exe (PID: 1400)
- cmd.exe (PID: 244)
- cmd.exe (PID: 1684)
- cmd.exe (PID: 5848)
- cmd.exe (PID: 4428)
Starts CMD.EXE for commands execution
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7324)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 3288)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 5788)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 7832)
INFO
Checks supported languages
- identity_helper.exe (PID: 7328)
- ShellExperienceHost.exe (PID: 8168)
- Set-up.exe (PID: 7048)
- Set-up.exe (PID: 3092)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.exe (PID: 4864)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7896)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.exe (PID: 7036)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7324)
- R4O6AYWL3QVGJGB8MNCU1VO7.exe (PID: 7812)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 5236)
- R4O6AYWL3QVGJGB8MNCU1VO7.exe (PID: 2072)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 3288)
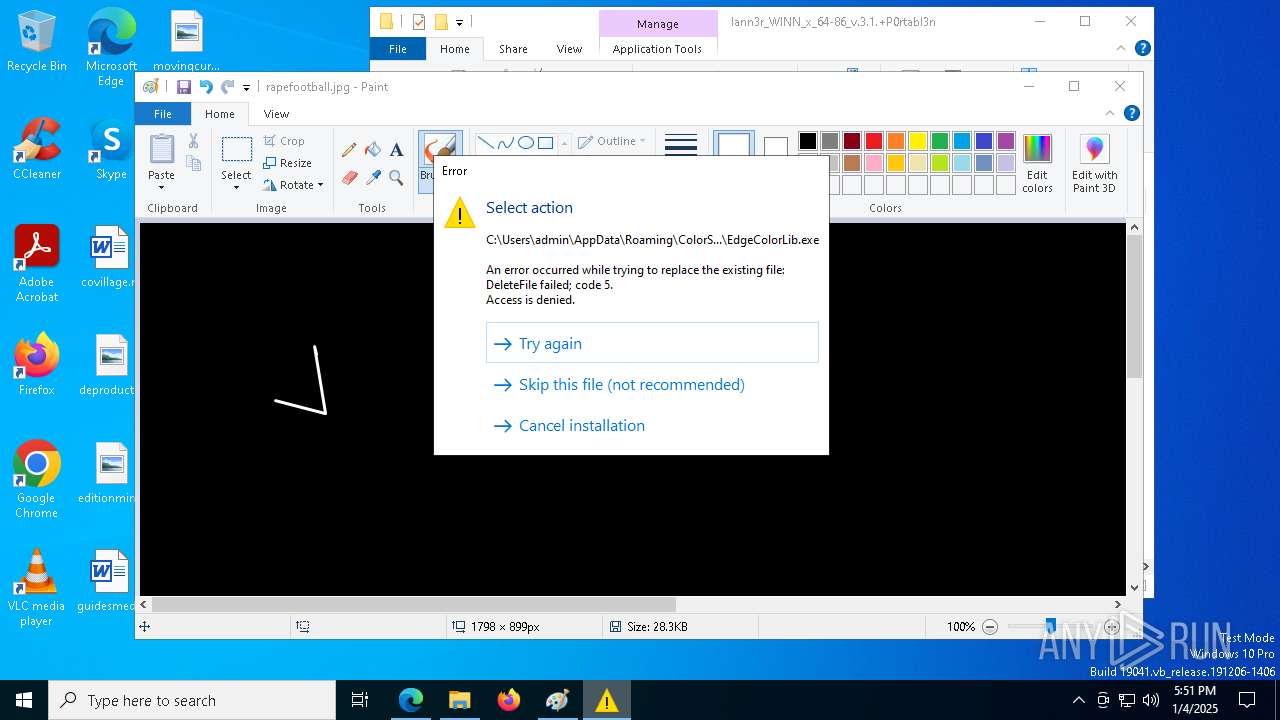
- EdgeColorLib.exe (PID: 7284)
- Set-up.exe (PID: 4556)
- GR516RQU6ZU6Z2EDC2882C3.exe (PID: 7900)
- GR516RQU6ZU6Z2EDC2882C3.exe (PID: 8032)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 5788)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 7888)
- EdgeColorLib.exe (PID: 308)
- EdgeColorLib.exe (PID: 3652)
- Set-up.exe (PID: 2216)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 6152)
- WJZHF0YIRO44XO77SFM8KZGUK.exe (PID: 8084)
- WJZHF0YIRO44XO77SFM8KZGUK.exe (PID: 6976)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 7832)
- EdgeColorLib.exe (PID: 8104)
Application launched itself
- msedge.exe (PID: 4668)
Reads the computer name
- identity_helper.exe (PID: 7328)
- ShellExperienceHost.exe (PID: 8168)
- Set-up.exe (PID: 7048)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.exe (PID: 4864)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.exe (PID: 7036)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7324)
- Set-up.exe (PID: 3092)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7896)
- R4O6AYWL3QVGJGB8MNCU1VO7.exe (PID: 7812)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 5236)
- R4O6AYWL3QVGJGB8MNCU1VO7.exe (PID: 2072)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 3288)
- Set-up.exe (PID: 4556)
- EdgeColorLib.exe (PID: 7284)
- GR516RQU6ZU6Z2EDC2882C3.exe (PID: 8032)
- GR516RQU6ZU6Z2EDC2882C3.exe (PID: 7900)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 7888)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 5788)
- EdgeColorLib.exe (PID: 308)
- EdgeColorLib.exe (PID: 3652)
- Set-up.exe (PID: 2216)
- WJZHF0YIRO44XO77SFM8KZGUK.exe (PID: 6976)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 6152)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 7832)
- WJZHF0YIRO44XO77SFM8KZGUK.exe (PID: 8084)
- EdgeColorLib.exe (PID: 8104)
Reads Environment values
- identity_helper.exe (PID: 7328)
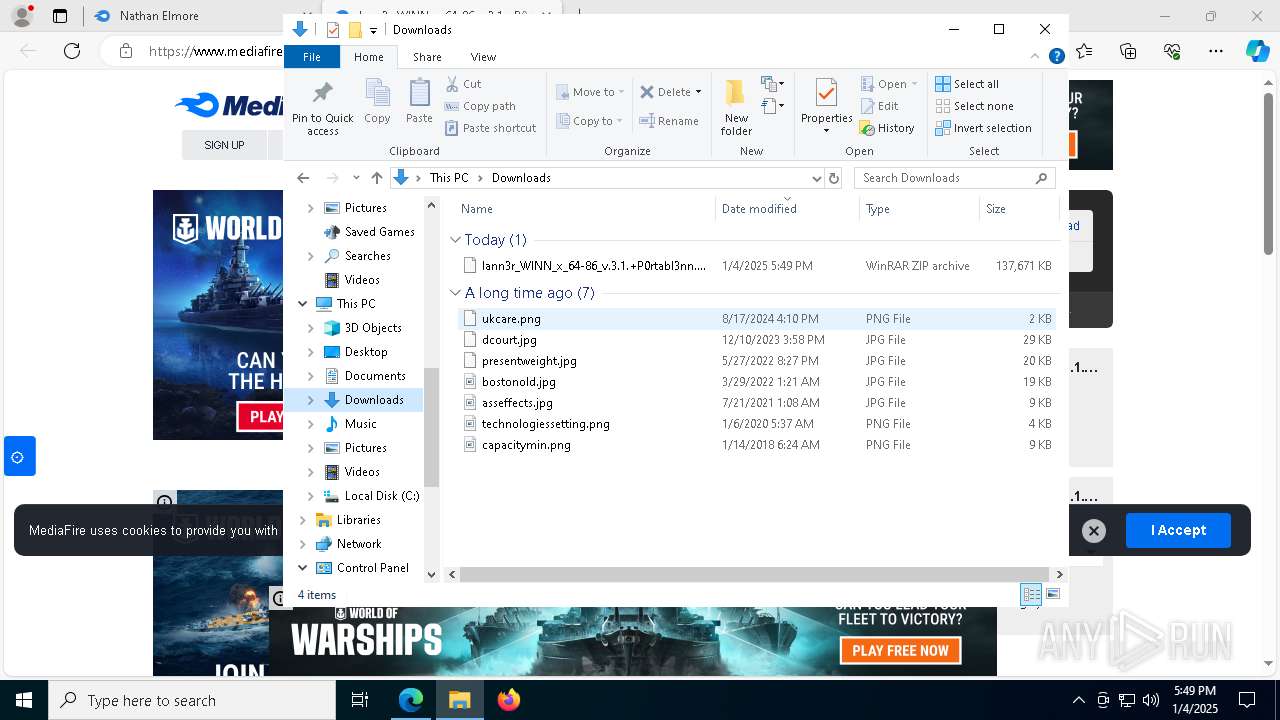
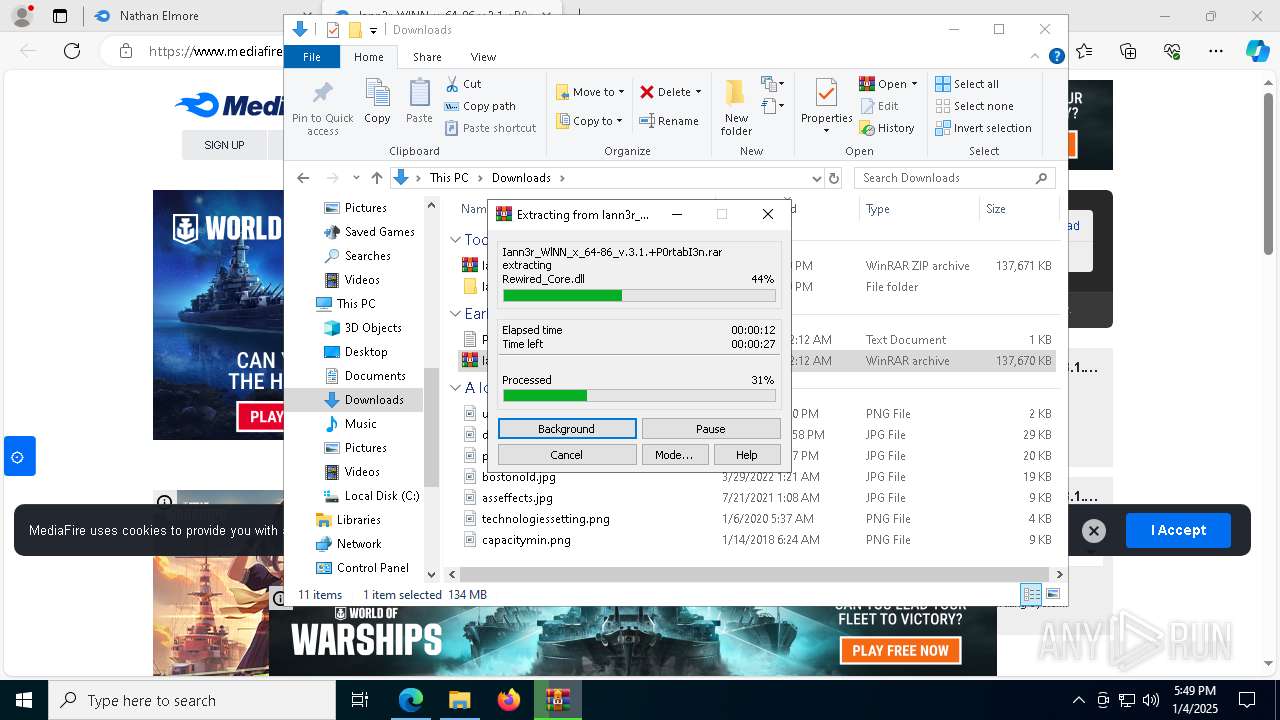
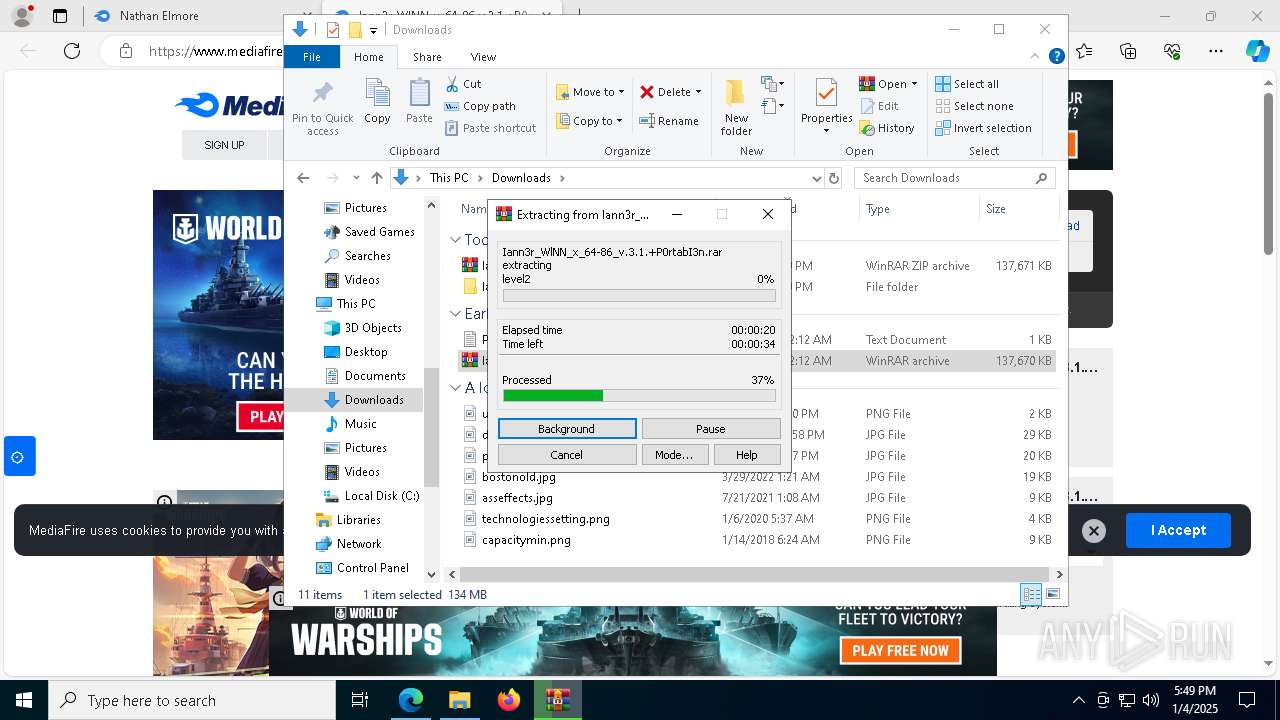
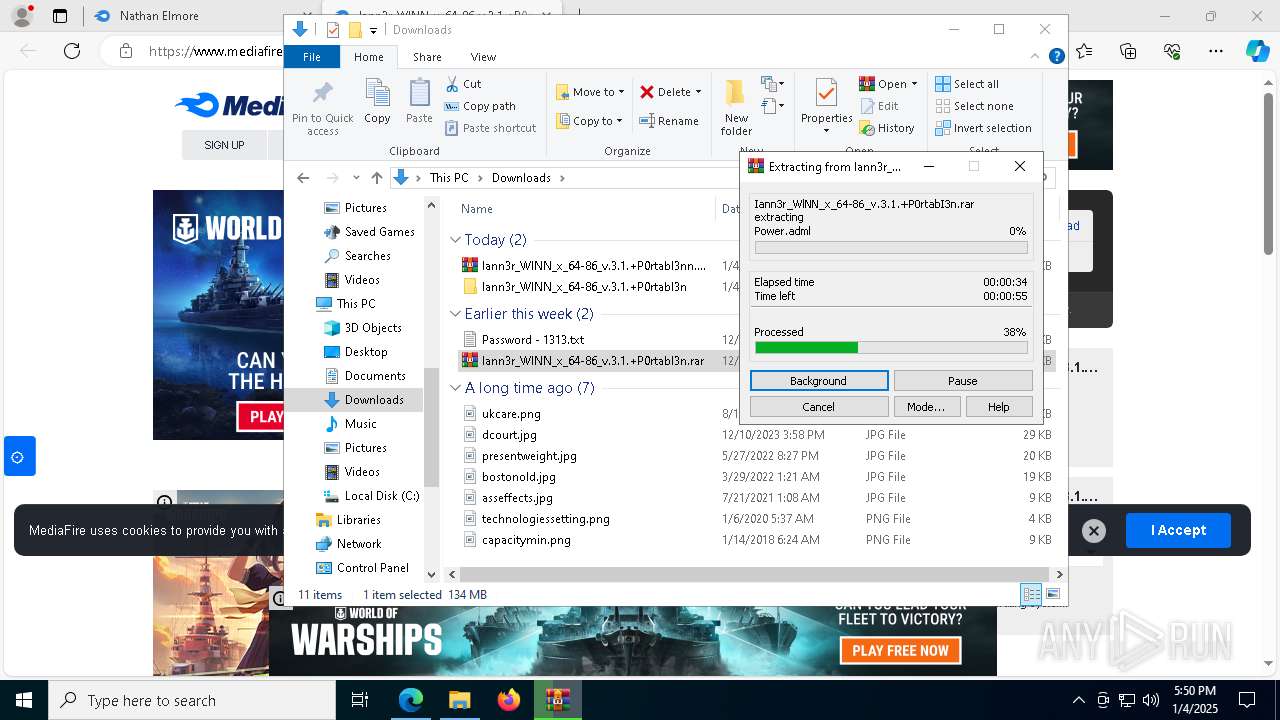
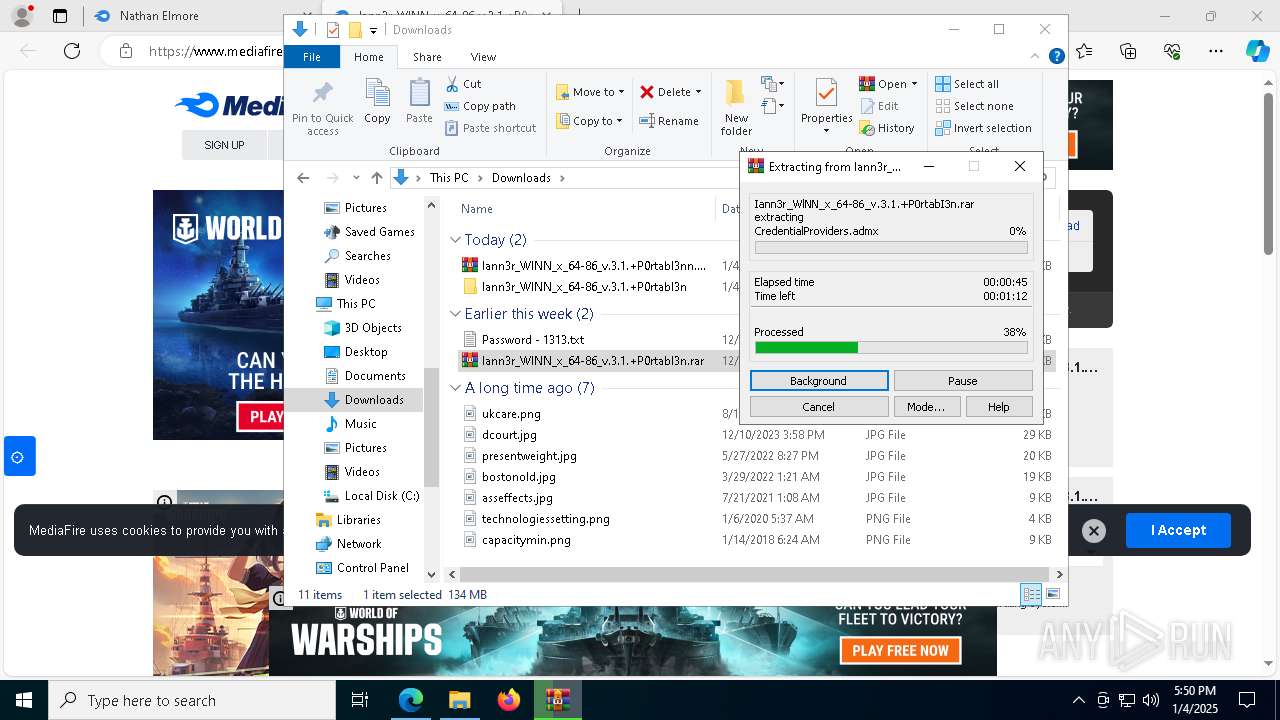
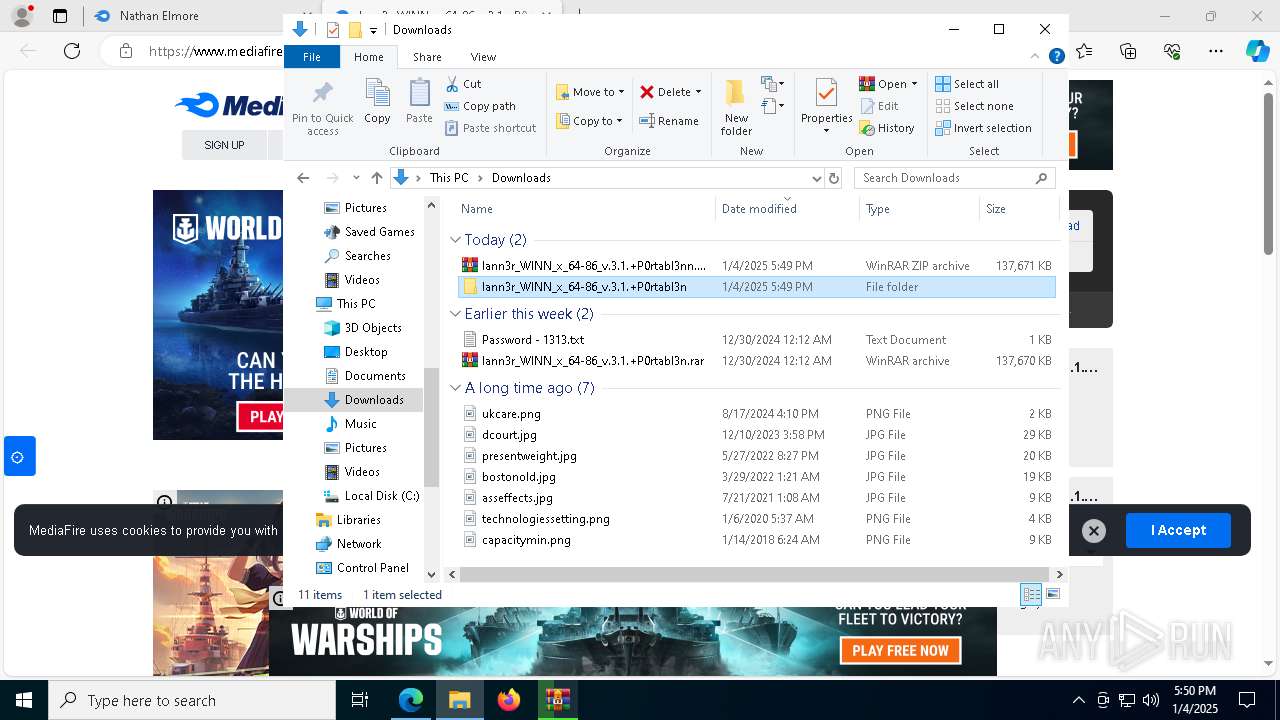
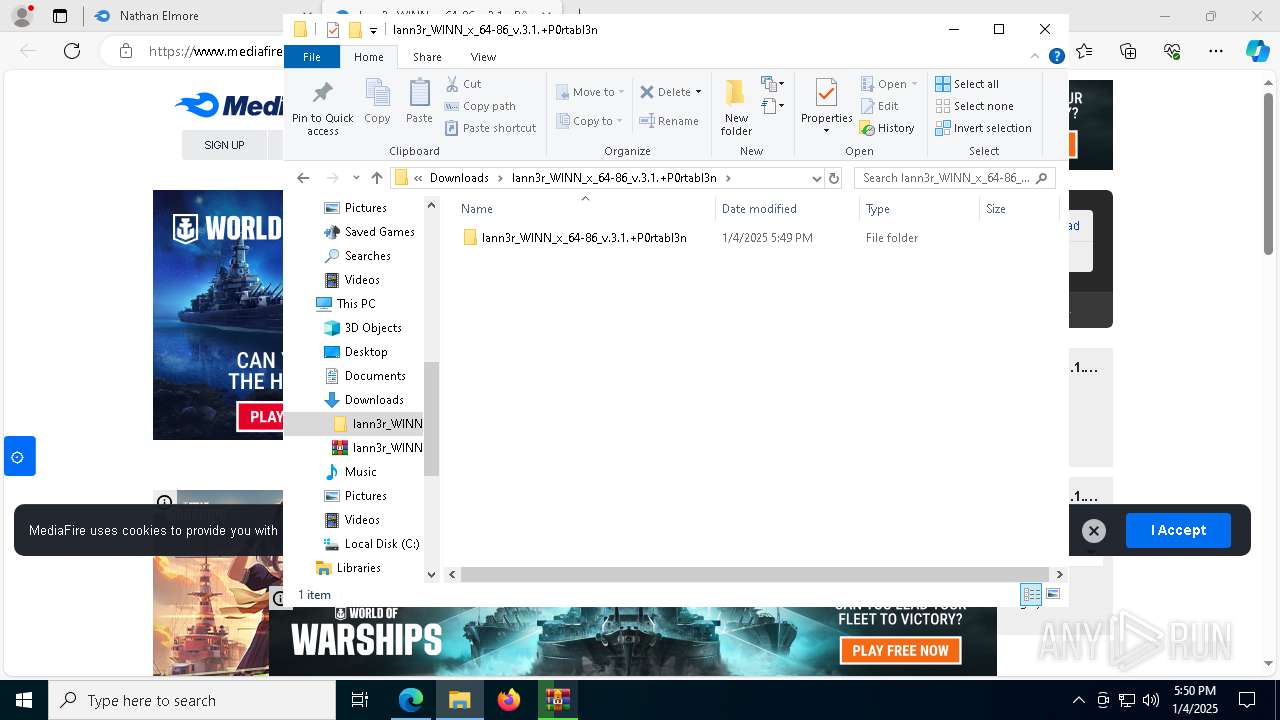
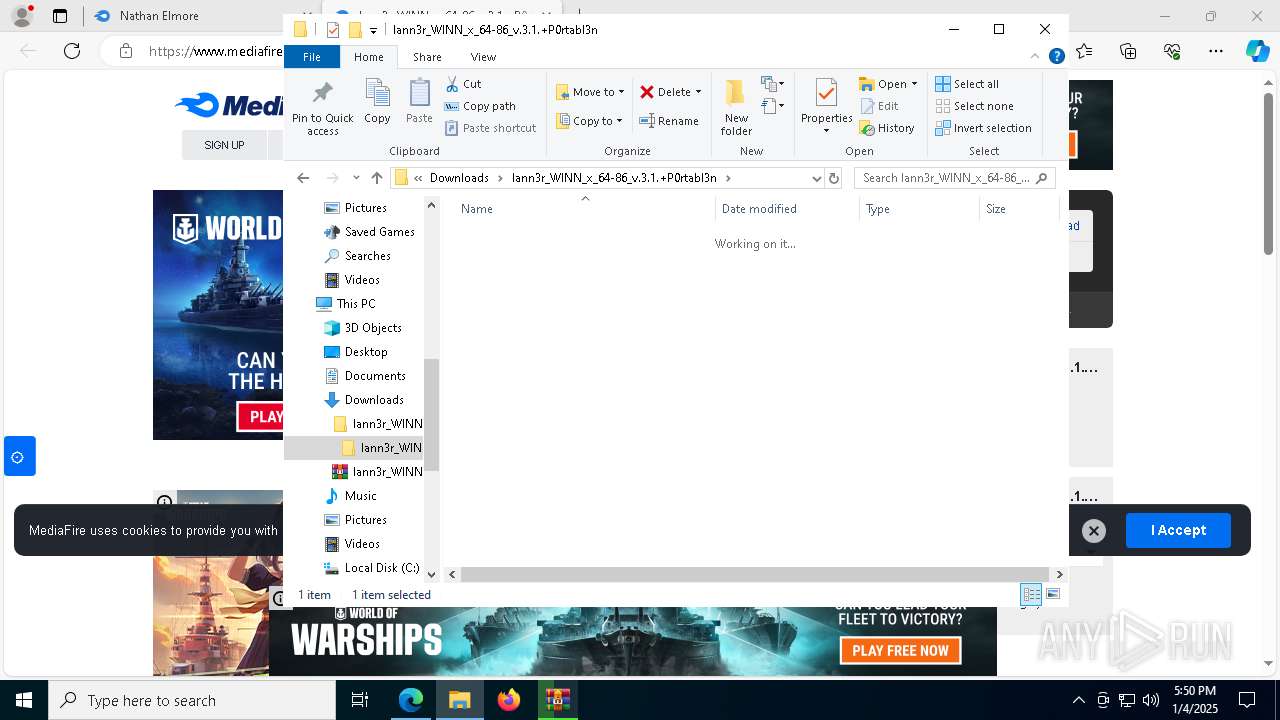
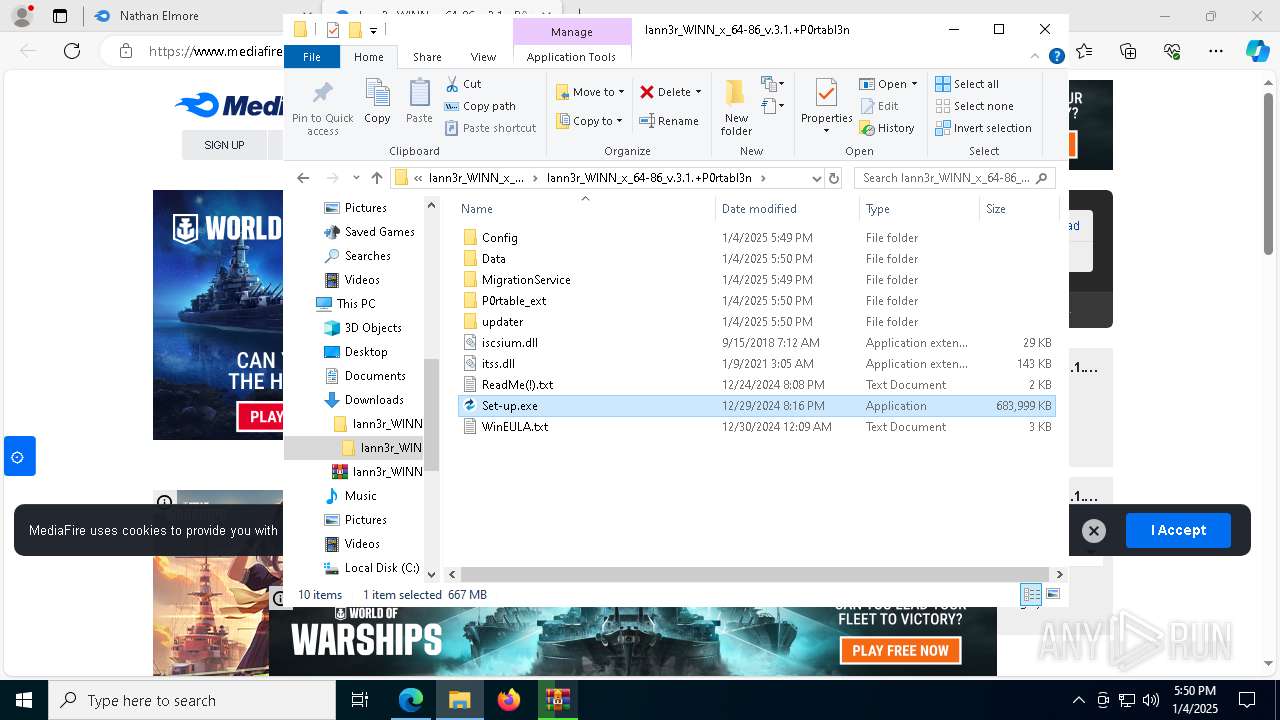
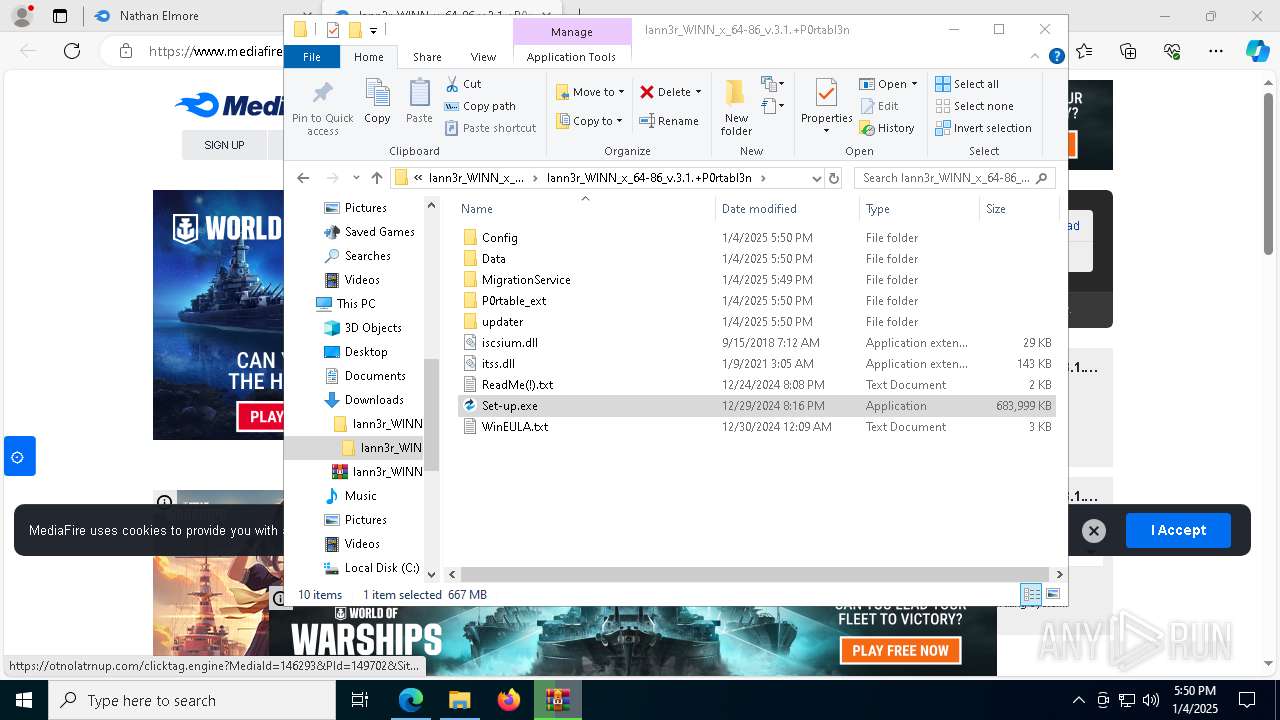
The process uses the downloaded file
- msedge.exe (PID: 8116)
- WinRAR.exe (PID: 3820)
- WinRAR.exe (PID: 1596)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7896)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 5236)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7324)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 7888)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 3288)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 5788)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 6152)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 7832)
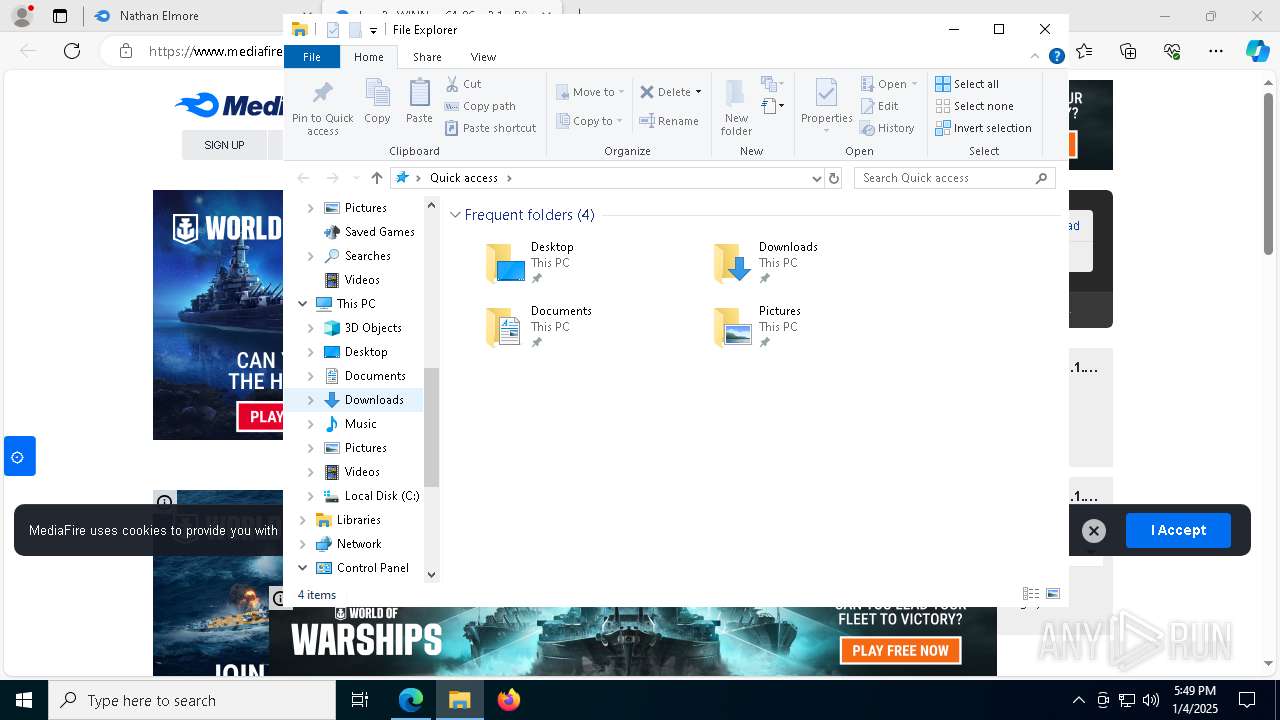
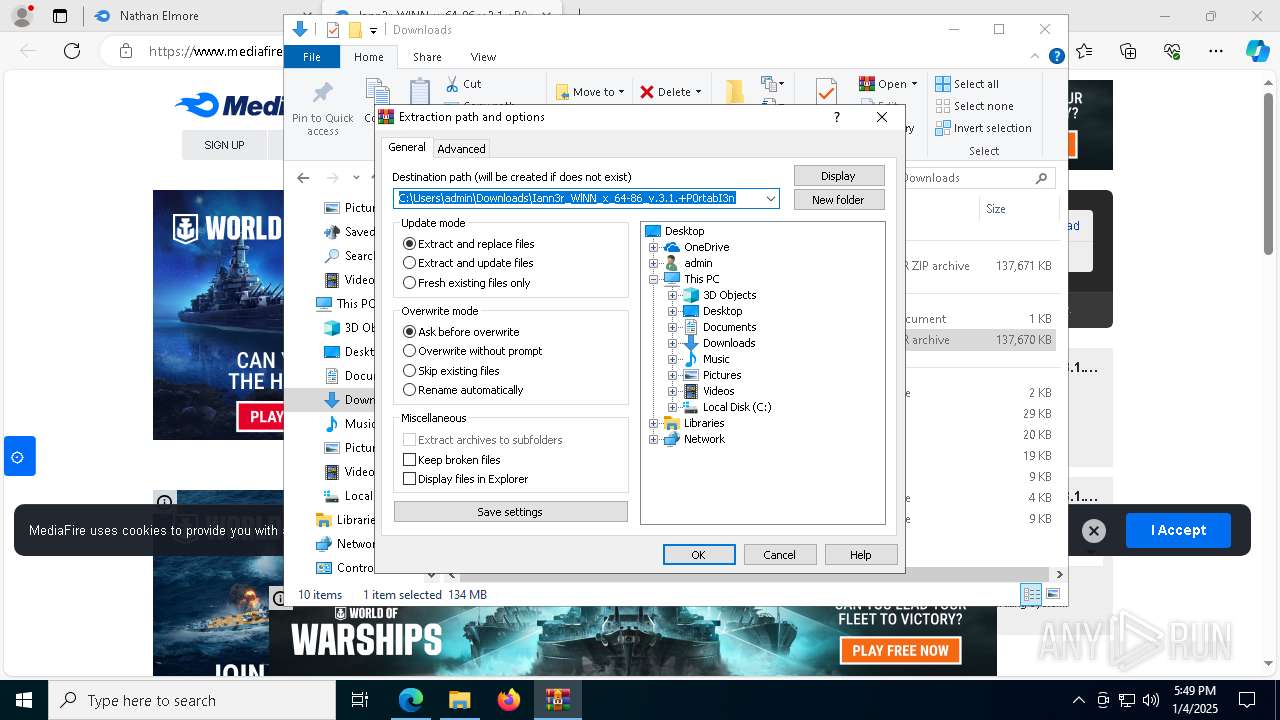
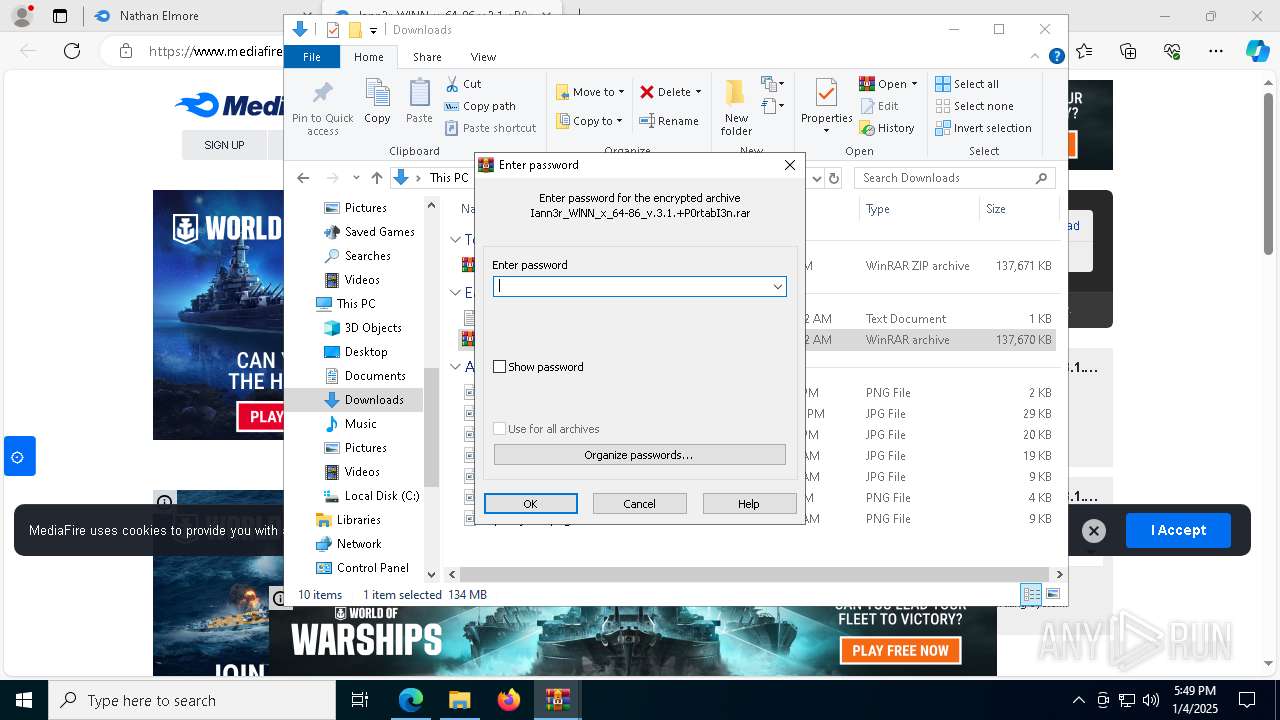
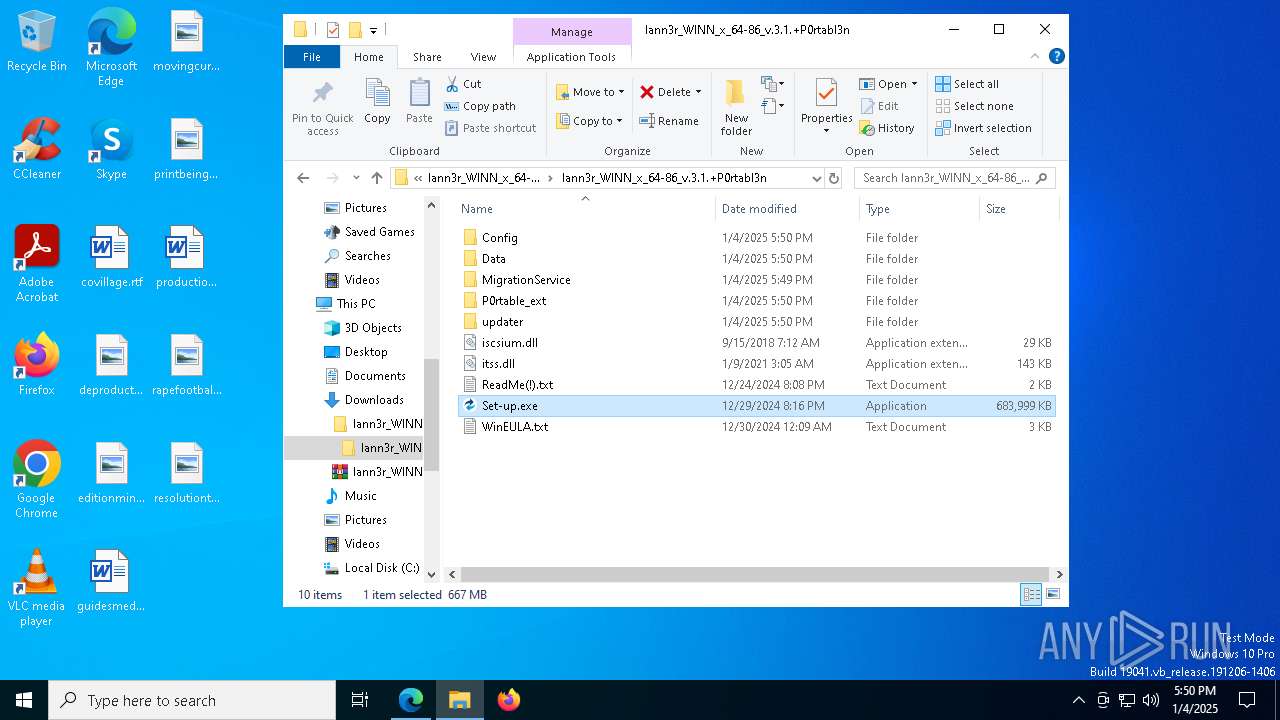
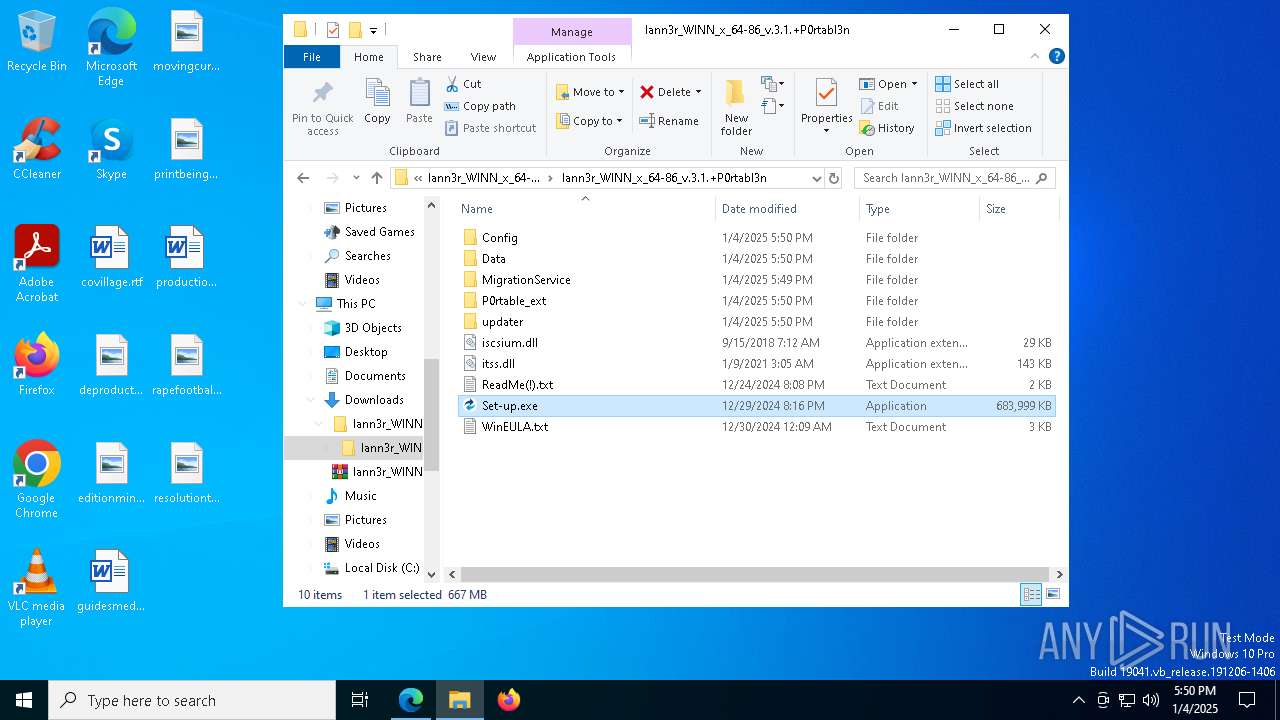
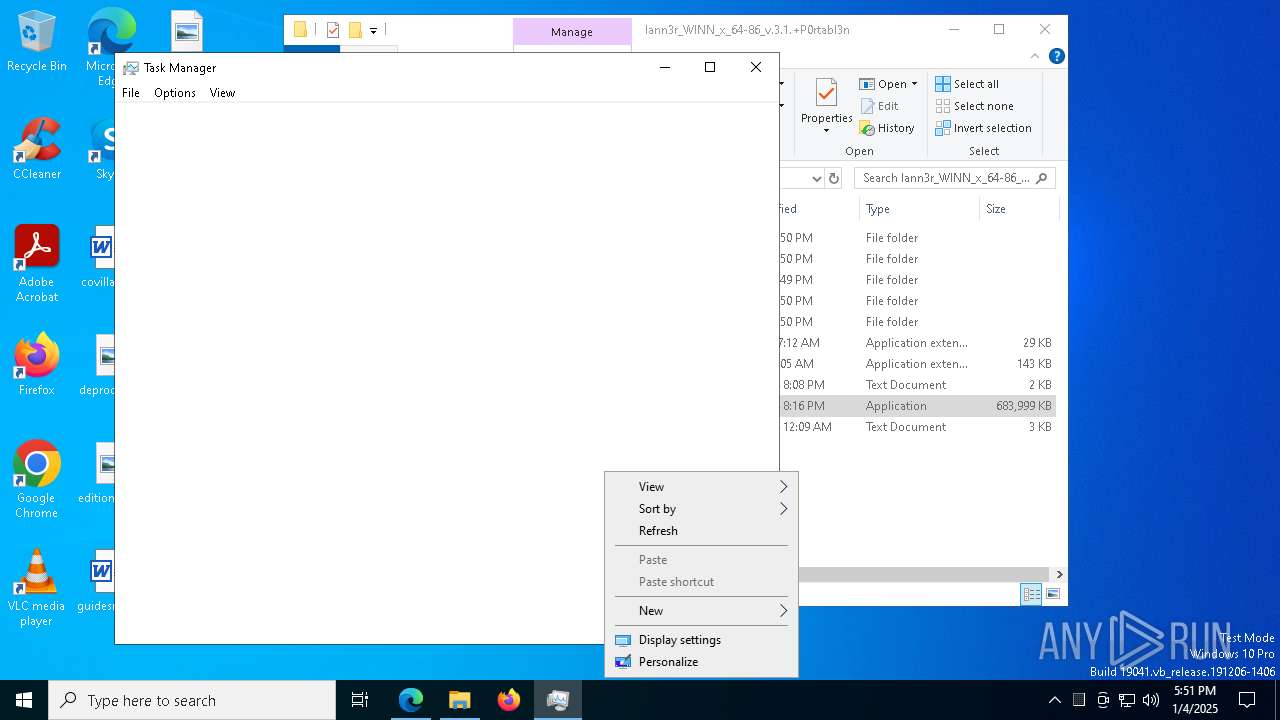
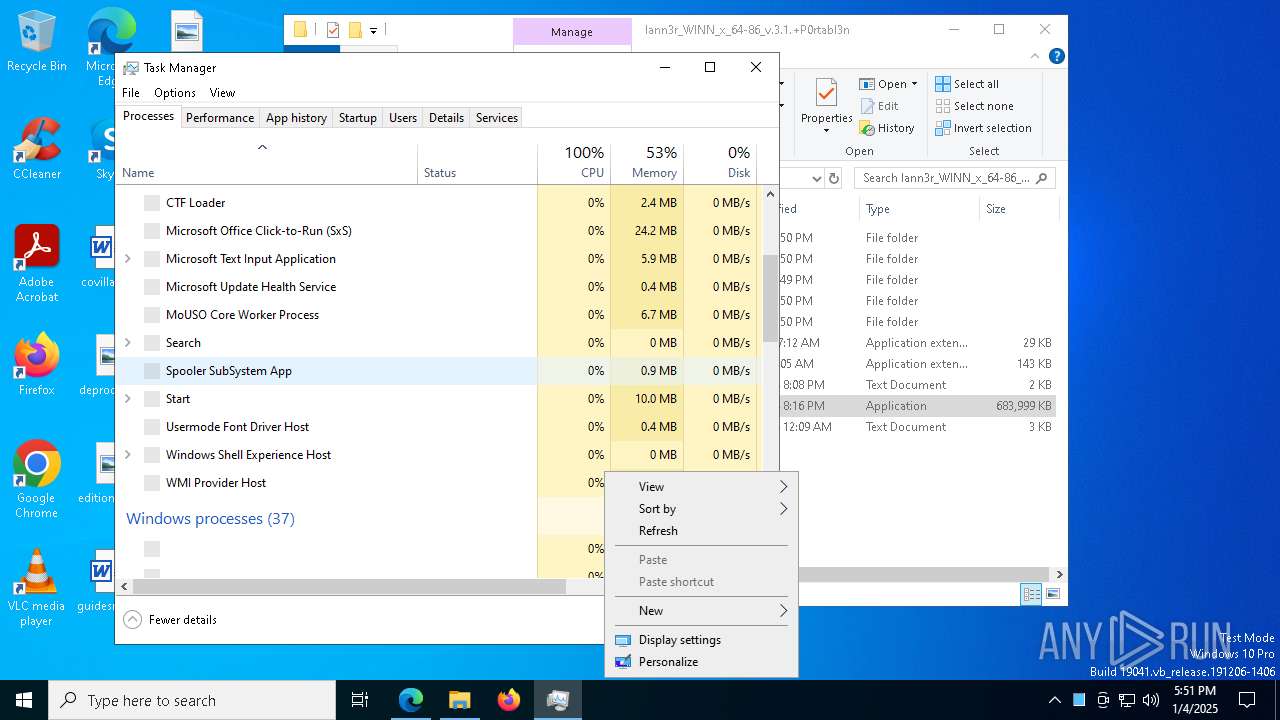
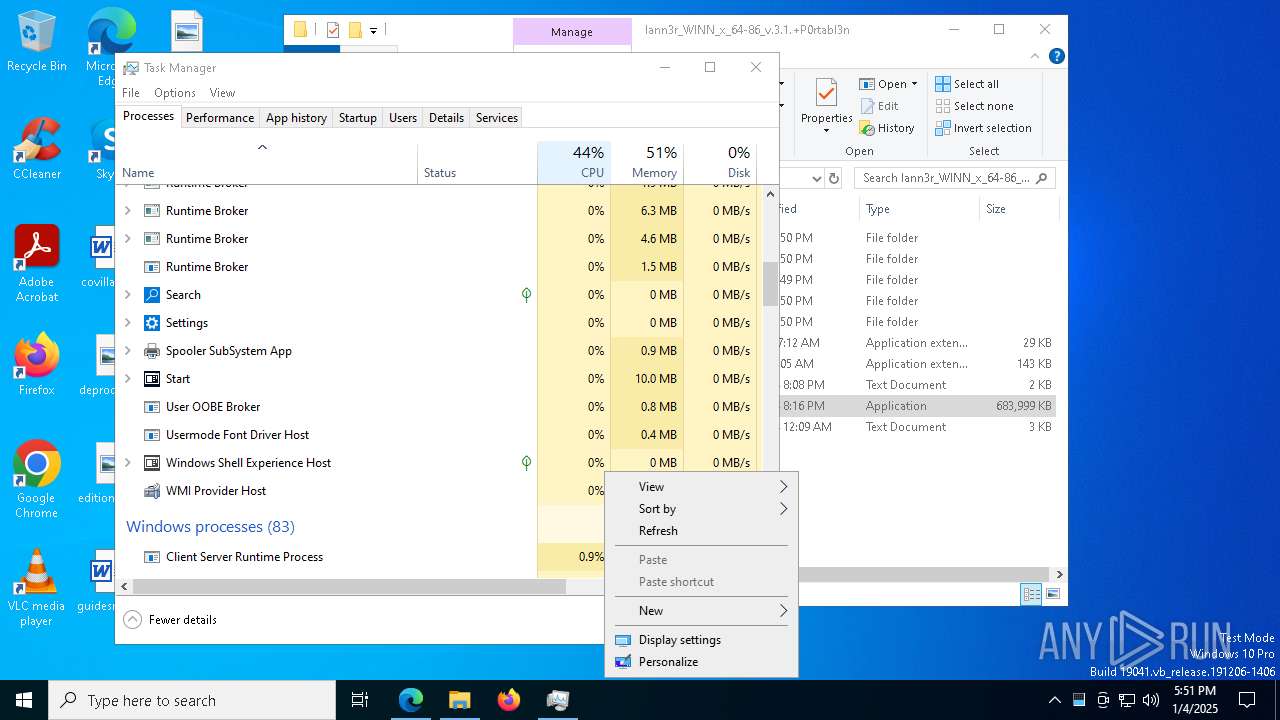
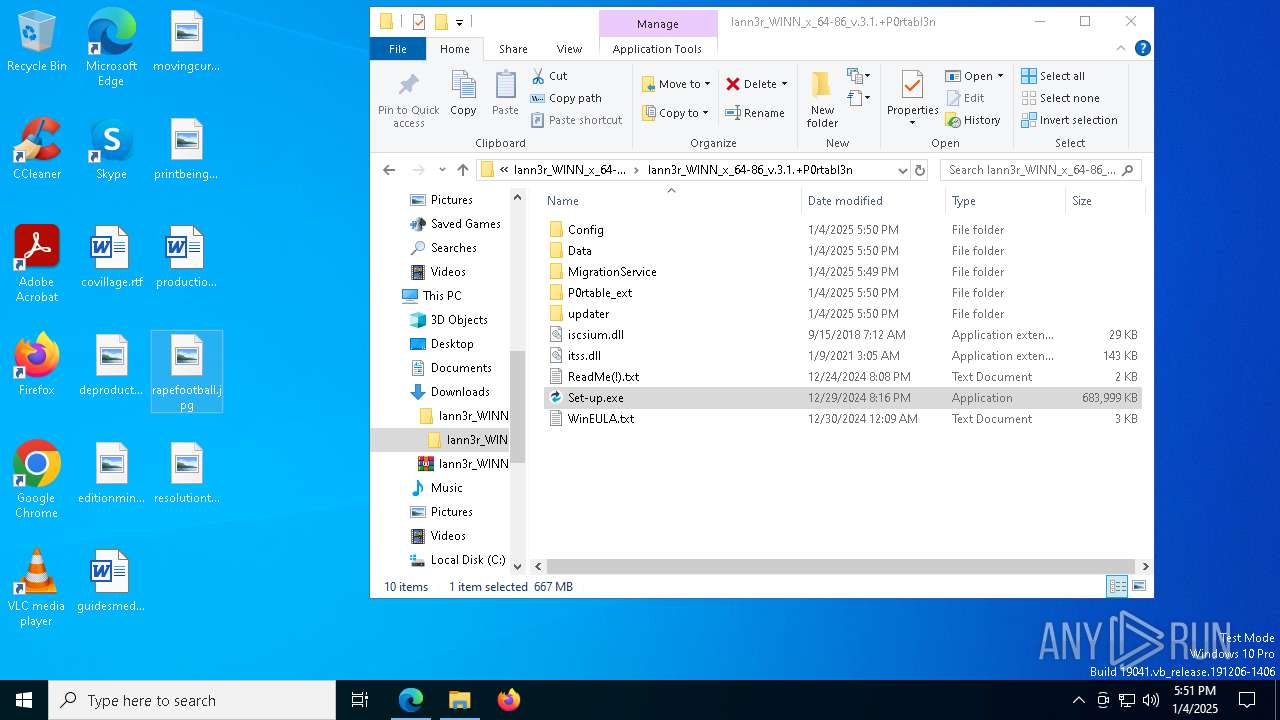
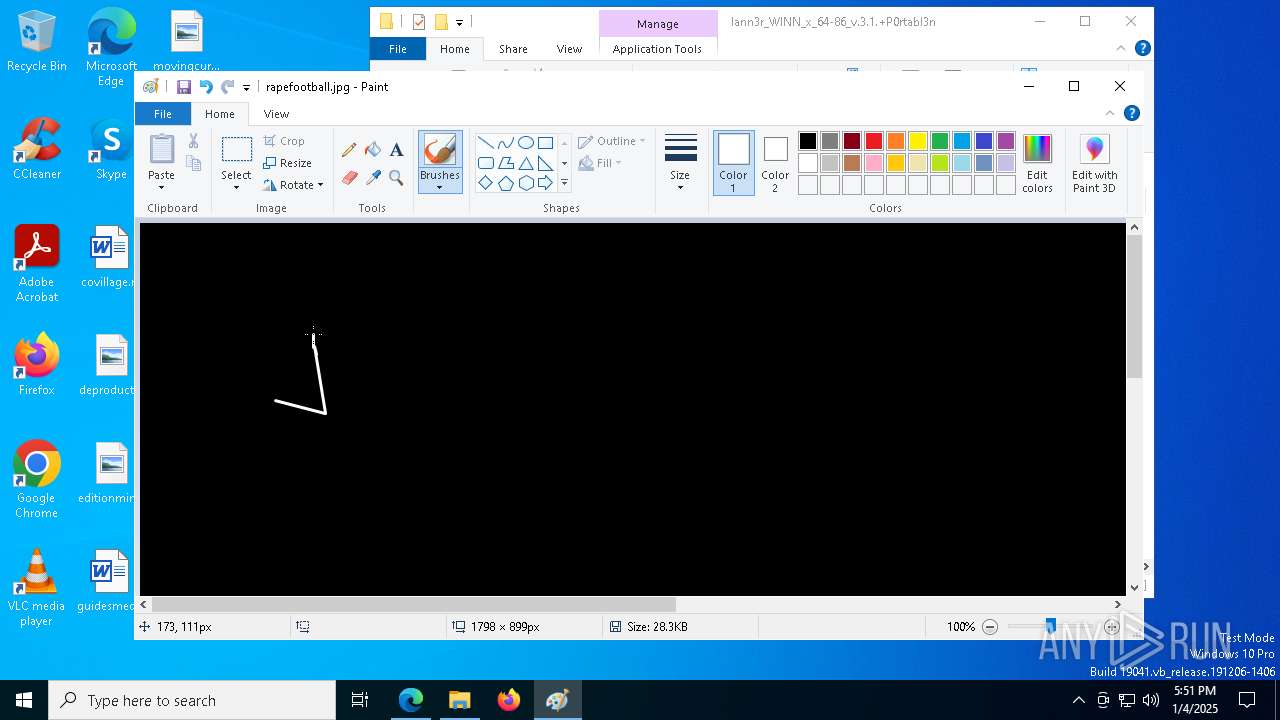
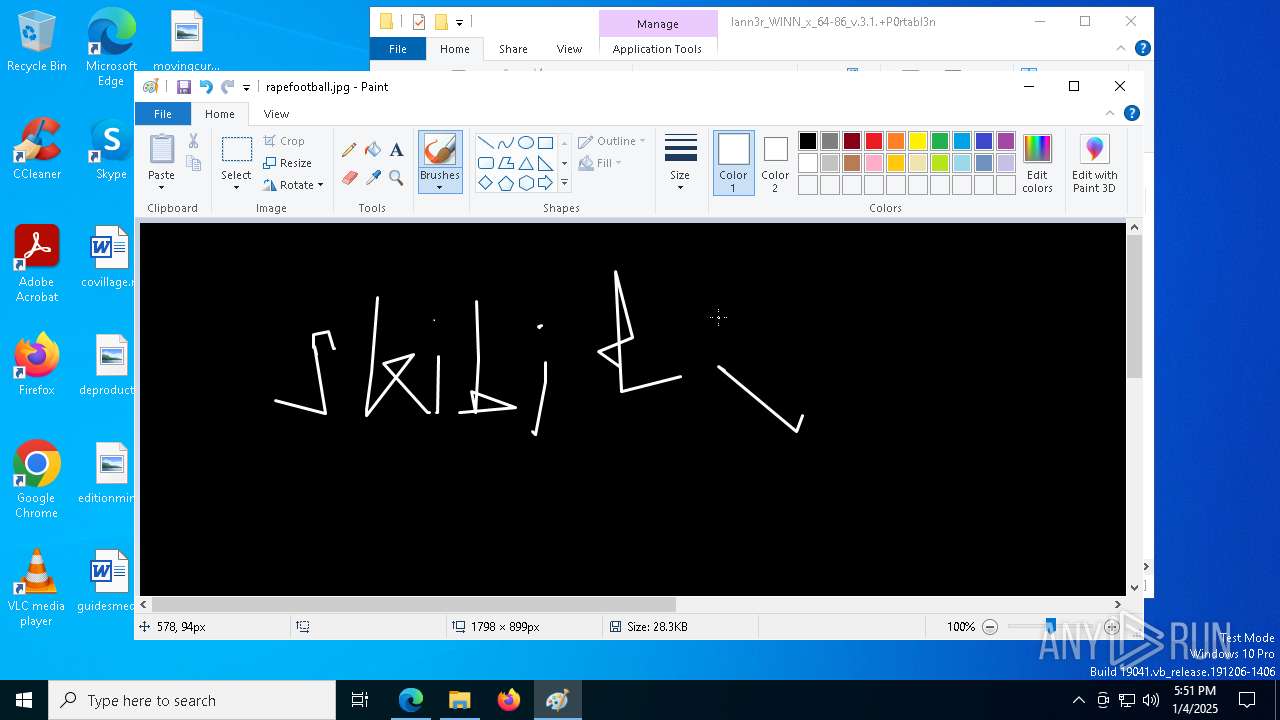
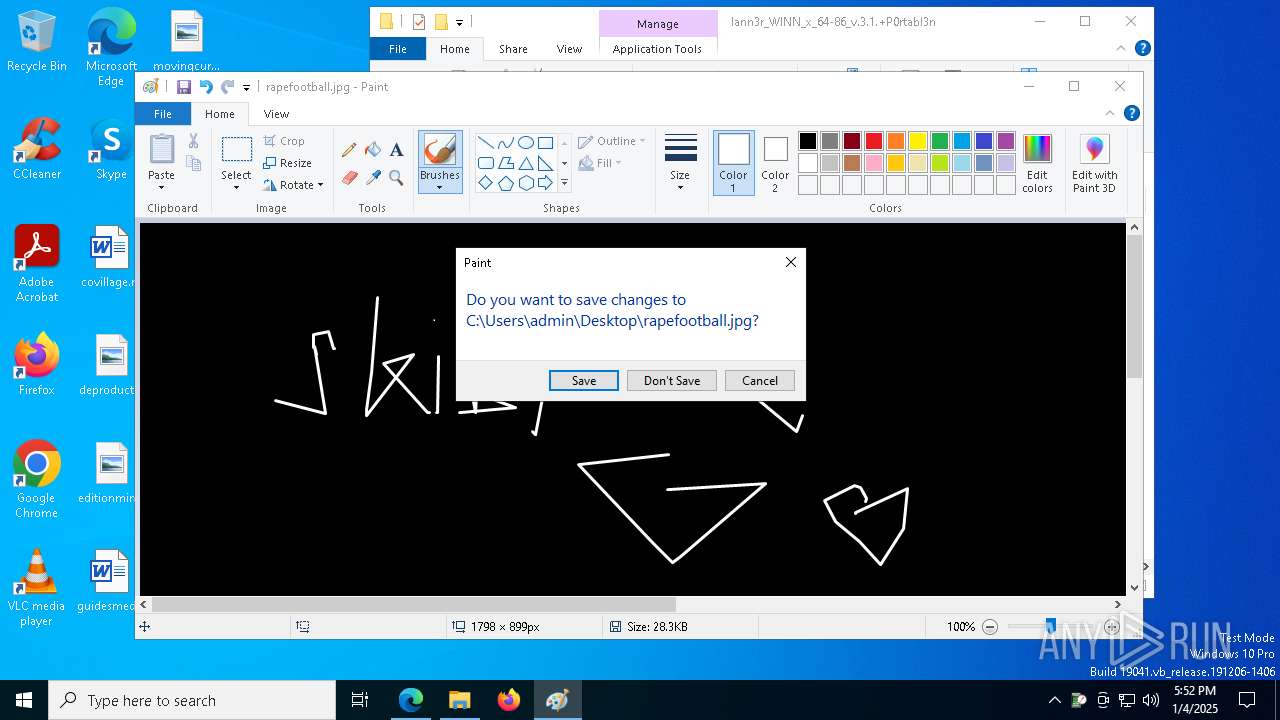
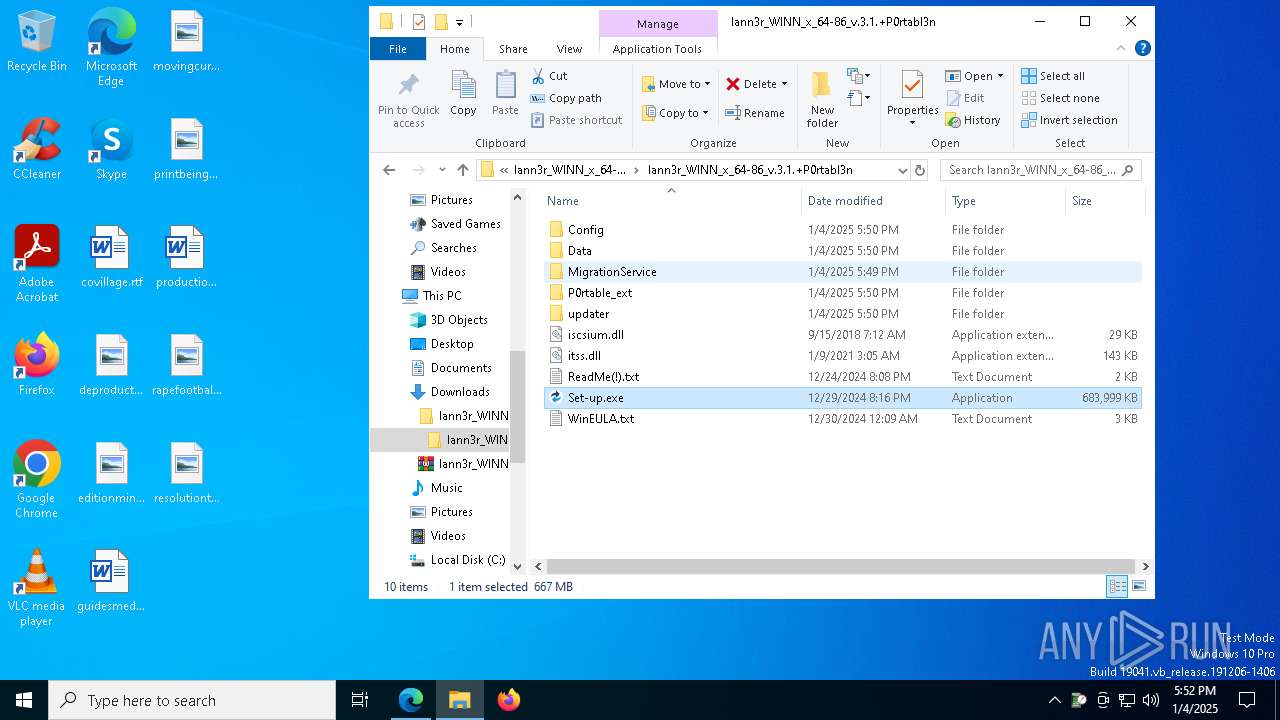
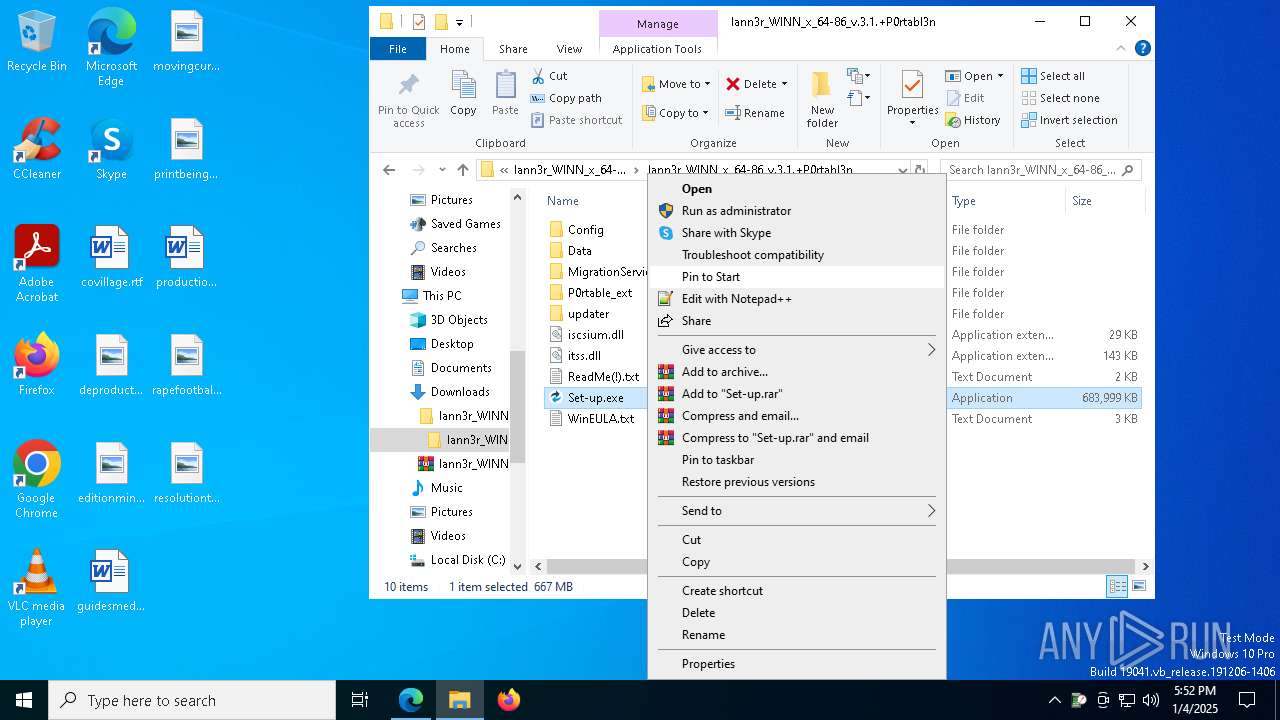
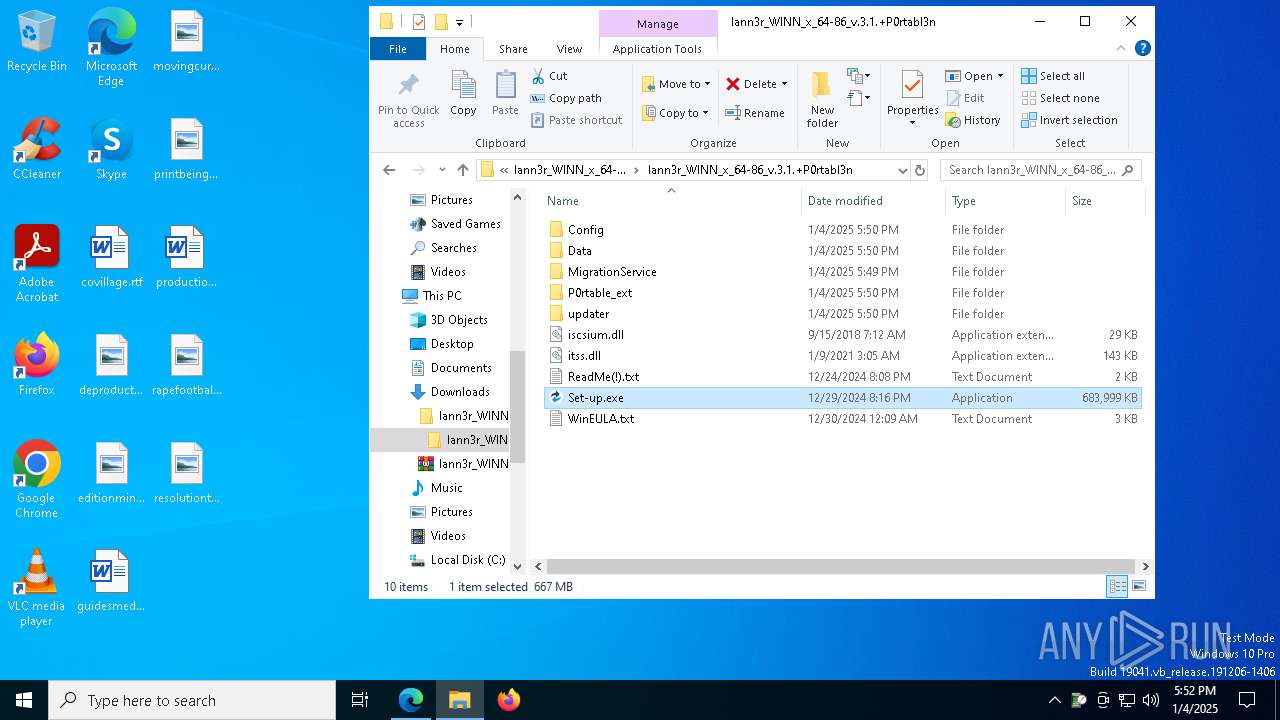
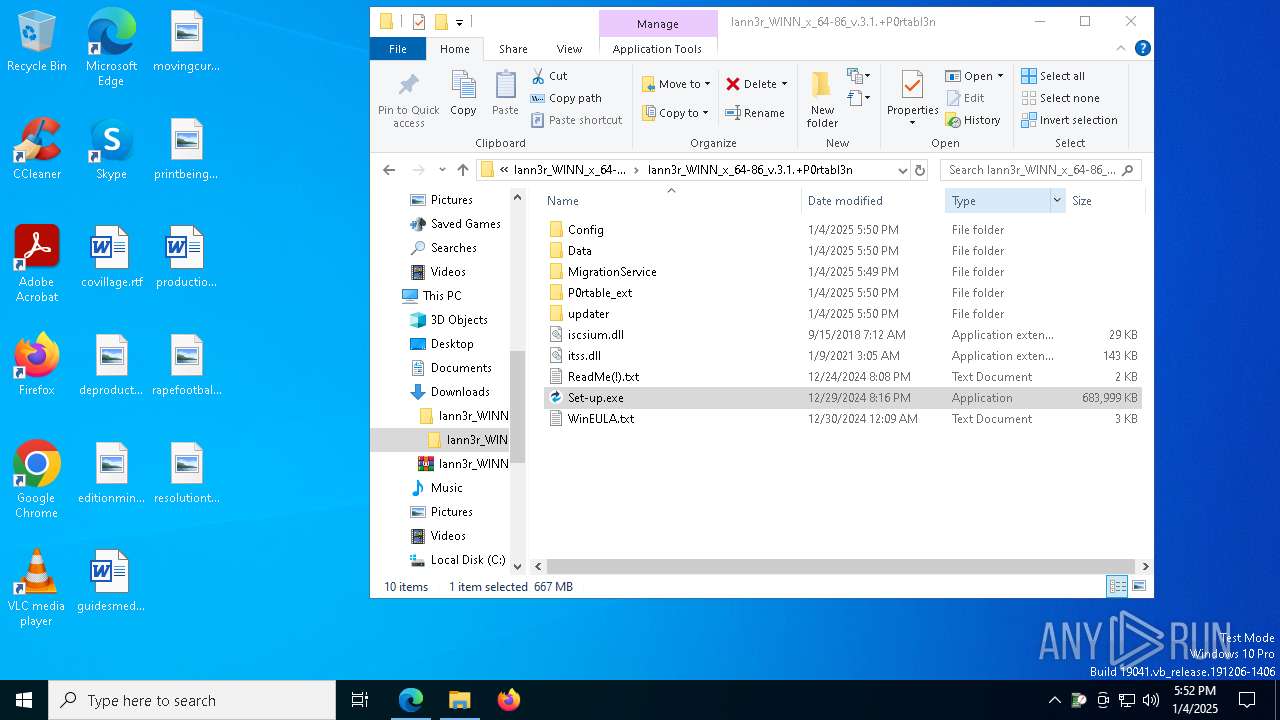
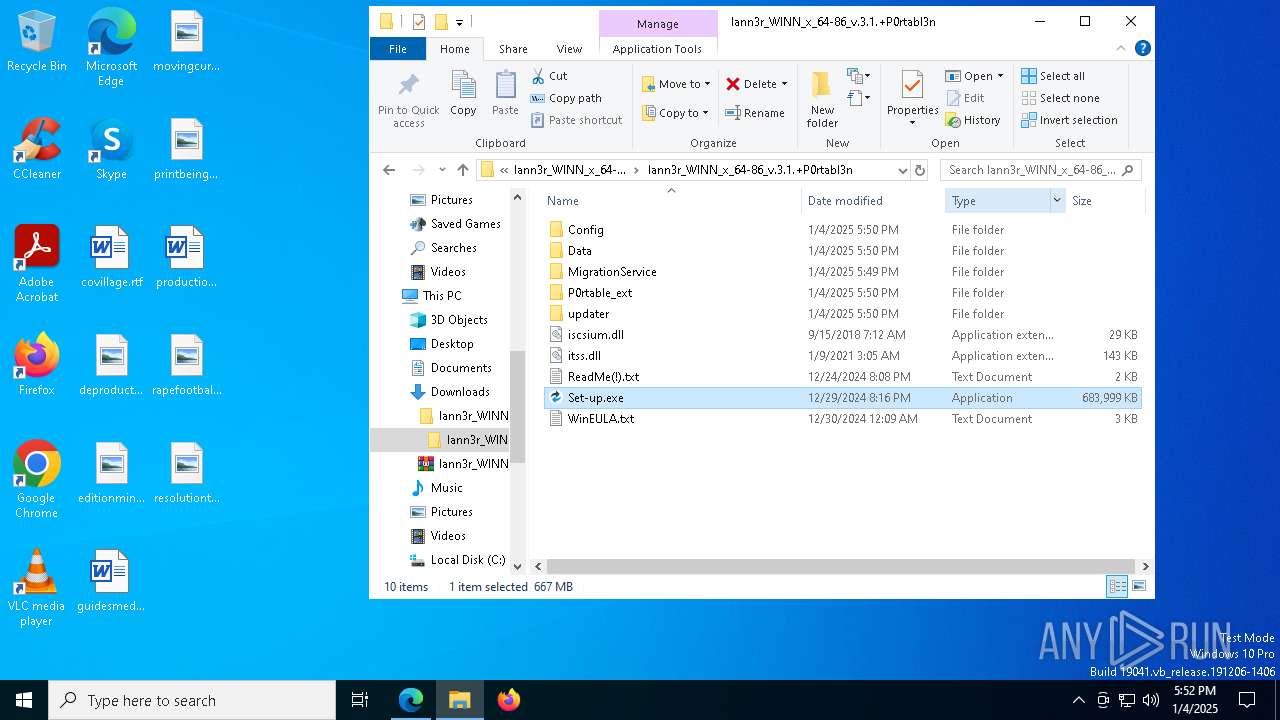
Manual execution by a user
- WinRAR.exe (PID: 3820)
- WinRAR.exe (PID: 1596)
- Set-up.exe (PID: 7048)
- mspaint.exe (PID: 7476)
- Set-up.exe (PID: 3092)
- Taskmgr.exe (PID: 2136)
- Taskmgr.exe (PID: 7560)
- mspaint.exe (PID: 3296)
- Set-up.exe (PID: 4556)
- Set-up.exe (PID: 2216)
The sample compiled with english language support
- WinRAR.exe (PID: 3820)
- msedge.exe (PID: 7156)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3820)
- msedge.exe (PID: 7156)
Reads the software policy settings
- Set-up.exe (PID: 7048)
- Set-up.exe (PID: 3092)
- Set-up.exe (PID: 4556)
- Set-up.exe (PID: 2216)
Create files in a temporary directory
- L9KXFTZ4XHT4HFN4DZQ05ZF9.exe (PID: 4864)
- Set-up.exe (PID: 7048)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7896)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.exe (PID: 7036)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7324)
- R4O6AYWL3QVGJGB8MNCU1VO7.exe (PID: 7812)
- Set-up.exe (PID: 3092)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 3288)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 5236)
- R4O6AYWL3QVGJGB8MNCU1VO7.exe (PID: 2072)
- Set-up.exe (PID: 4556)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 7888)
- GR516RQU6ZU6Z2EDC2882C3.exe (PID: 8032)
- EdgeColorLib.exe (PID: 7284)
- GR516RQU6ZU6Z2EDC2882C3.exe (PID: 7900)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 5788)
- EdgeColorLib.exe (PID: 308)
- EdgeColorLib.exe (PID: 3652)
- WJZHF0YIRO44XO77SFM8KZGUK.exe (PID: 6976)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 6152)
- Set-up.exe (PID: 2216)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 7832)
- WJZHF0YIRO44XO77SFM8KZGUK.exe (PID: 8084)
- EdgeColorLib.exe (PID: 8104)
Sends debugging messages
- ShellExperienceHost.exe (PID: 8168)
Creates files or folders in the user directory
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7324)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 3288)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 5788)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 7832)
Process checks computer location settings
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7896)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 5236)
- L9KXFTZ4XHT4HFN4DZQ05ZF9.tmp (PID: 7324)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 7888)
- R4O6AYWL3QVGJGB8MNCU1VO7.tmp (PID: 3288)
- GR516RQU6ZU6Z2EDC2882C3.tmp (PID: 5788)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 6152)
- WJZHF0YIRO44XO77SFM8KZGUK.tmp (PID: 7832)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
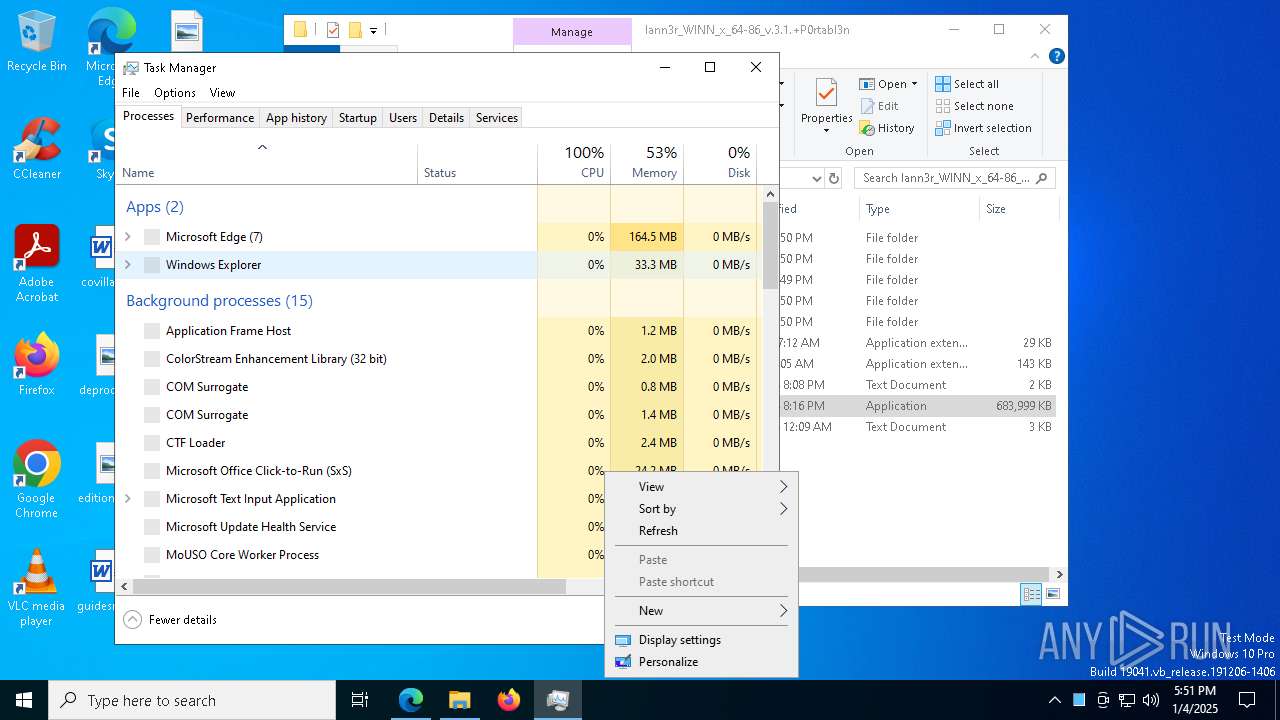
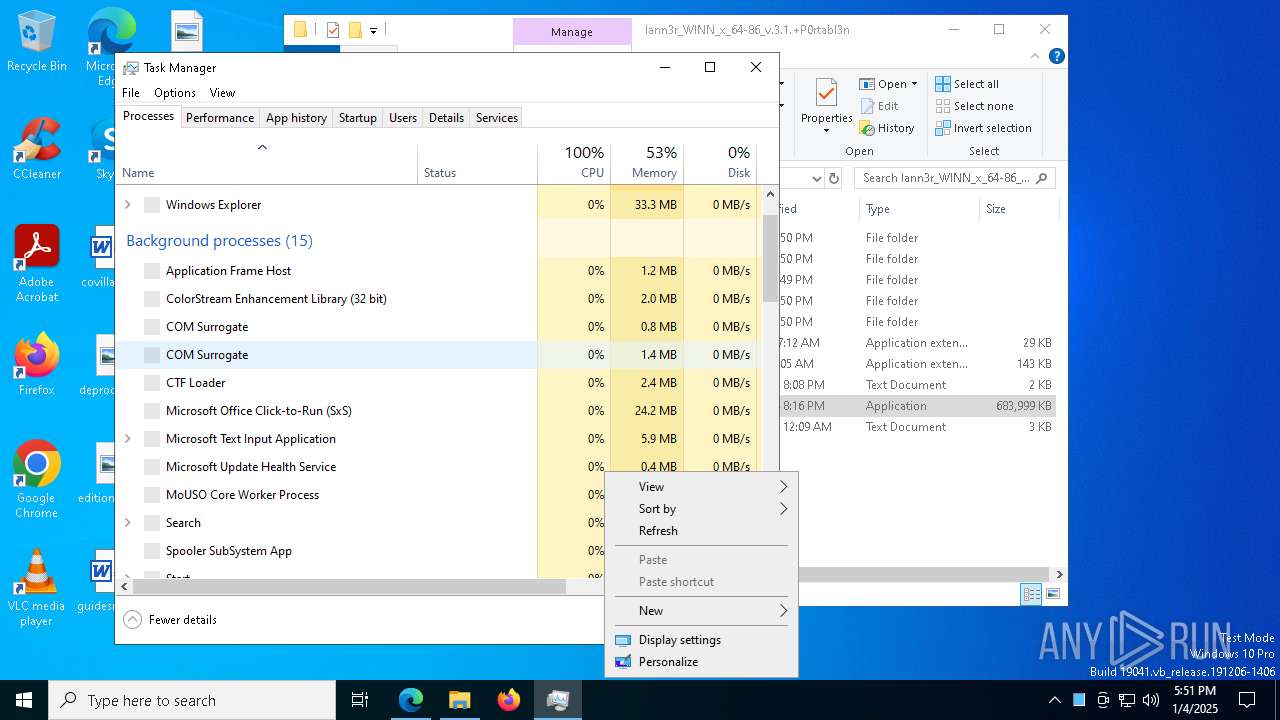
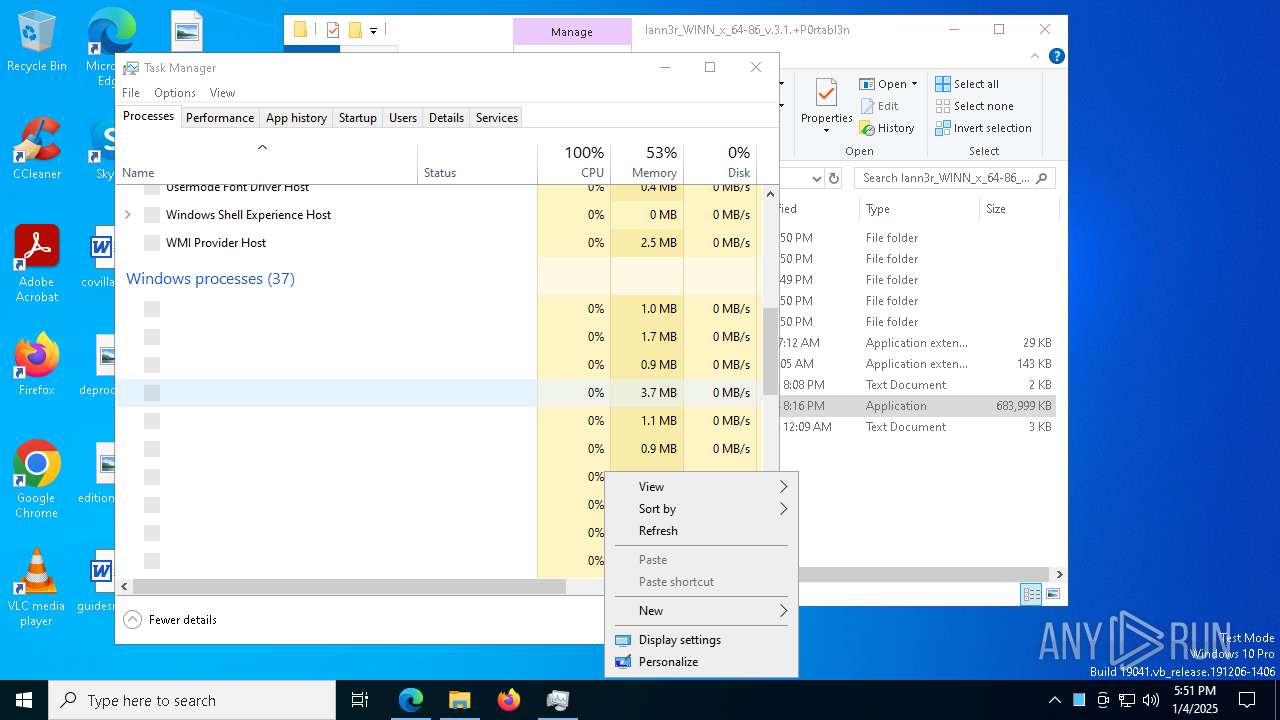
Total processes
339
Monitored processes
198
Malicious processes
23
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6436 --field-trial-handle=2360,i,2528570669324890035,16745926135366042308,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 244 | "cmd.exe" /C tasklist /FI "IMAGENAME eq avgui.exe" /FO CSV /NH | find /I "avgui.exe" | C:\Windows\System32\cmd.exe | — | WJZHF0YIRO44XO77SFM8KZGUK.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 308 | "C:\Users\admin\AppData\Roaming\ColorStreamLib\EdgeColorLib.exe" | C:\Users\admin\AppData\Roaming\ColorStreamLib\EdgeColorLib.exe | — | R4O6AYWL3QVGJGB8MNCU1VO7.tmp | |||||||||||
User: admin Company: Michael Uno Integrity Level: HIGH Description: Notifies process activities Exit code: 0 Version: 0.0.0.4 Modules
| |||||||||||||||
| 644 | find /I "opssvc.exe" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6460 --field-trial-handle=2360,i,2528570669324890035,16745926135366042308,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --mojo-platform-channel-handle=8000 --field-trial-handle=2360,i,2528570669324890035,16745926135366042308,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | tasklist /FI "IMAGENAME eq avgui.exe" /FO CSV /NH | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1220 | tasklist /FI "IMAGENAME eq sophoshealth.exe" /FO CSV /NH | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1400 | "cmd.exe" /C tasklist /FI "IMAGENAME eq opssvc.exe" /FO CSV /NH | find /I "opssvc.exe" | C:\Windows\System32\cmd.exe | — | WJZHF0YIRO44XO77SFM8KZGUK.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 705
Read events
19 571
Write events
108
Delete events
26
Modification events
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4649DA477B892F00 | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 79A3E5477B892F00 | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328372 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CFEB5BC8-564D-4468-8705-6C09A2ED9BD0} | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328372 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {49518C3A-1D8F-4F3F-8853-1D5B31F55E35} | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328372 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C56223EA-BFA9-49DB-88E4-98A6BE34301C} | |||
| (PID) Process: | (4668) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328372 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A4D47C3E-CD1D-4C2D-8AFA-B7E5EDCAF714} | |||
Executable files
520
Suspicious files
720
Text files
885
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135845.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135845.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135854.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135854.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135864.TMP | — | |
MD5:— | SHA256:— | |||
| 4668 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
251
DNS requests
229
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4308 | svchost.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6908 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6908 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7416 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ed1297e-f6c9-4355-aec4-433ea371b116?P1=1736223824&P2=404&P3=2&P4=ZnOf3nfRBmIbmM7IOQJ7H7%2fdSPSrC%2bQb2i3rUOsNAs9UFQx3uQNAjPAgE5pEB%2fayG%2bu4RA%2bYagYe%2fB%2fY5%2f6FYw%3d%3d | unknown | — | — | whitelisted |
7416 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ed1297e-f6c9-4355-aec4-433ea371b116?P1=1736223824&P2=404&P3=2&P4=ZnOf3nfRBmIbmM7IOQJ7H7%2fdSPSrC%2bQb2i3rUOsNAs9UFQx3uQNAjPAgE5pEB%2fayG%2bu4RA%2bYagYe%2fB%2fY5%2f6FYw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | unknown |
4712 | MoUsoCoreWorker.exe | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4308 | svchost.exe | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4308 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.137:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
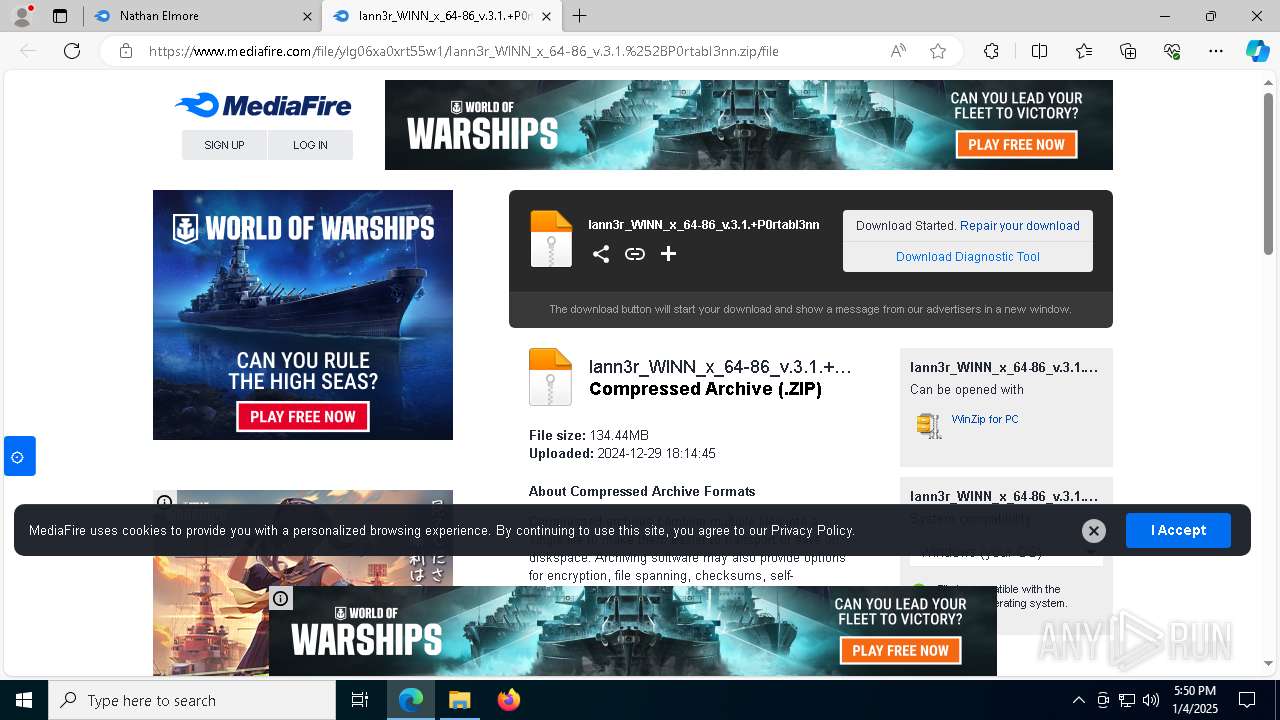
www.mediafire.com |
| shared |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
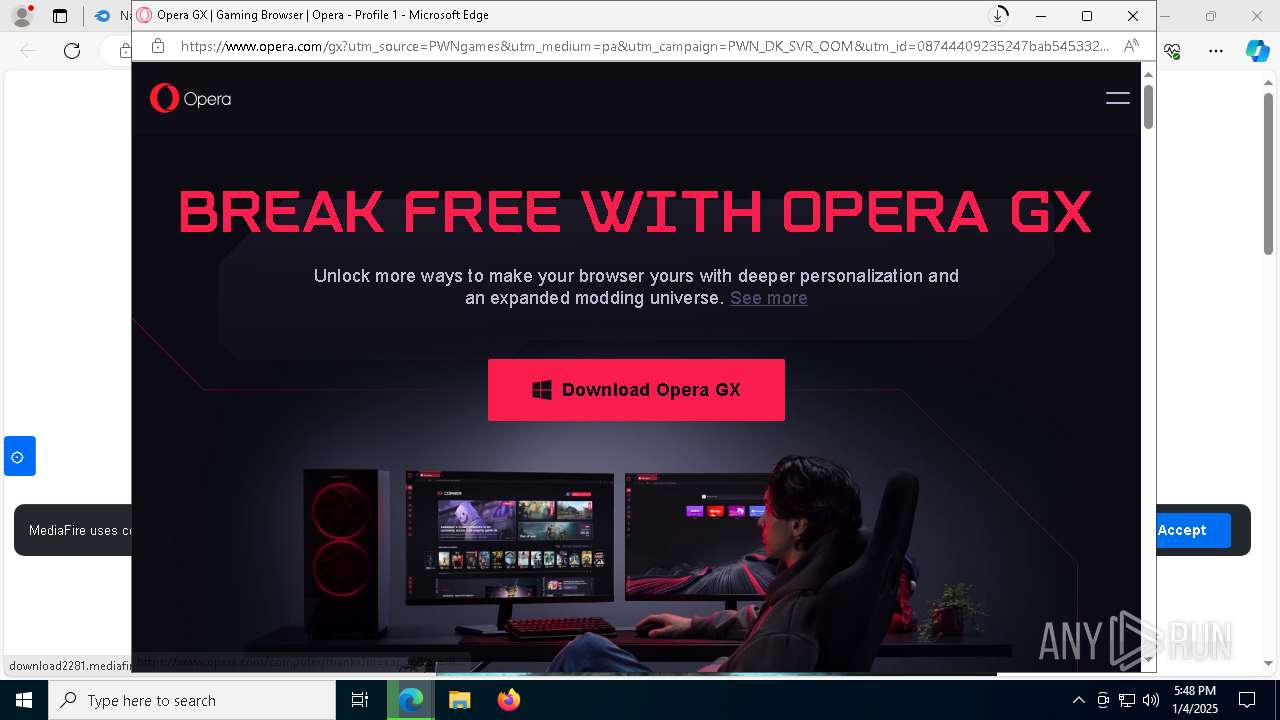
6464 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6464 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6464 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6464 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6464 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6464 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6464 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6464 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6464 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6464 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |