| File name: | 3.exe |
| Full analysis: | https://app.any.run/tasks/e0e80b80-69f3-4127-8777-35cbd69da4a1 |
| Verdict: | Malicious activity |
| Analysis date: | July 23, 2019, 04:39:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5B4BD24D6240F467BFBC74803C9F15B0 |
| SHA1: | C17F98C182D299845C54069872E8137645768A1A |
| SHA256: | 14C7BEC7369D4175C6D92554B033862B3847FF98A04DFEBDF9F5BB30180ED13E |
| SSDEEP: | 6144:7qZQGv0d4dW6efSyahstfKVkW5XXnXXfXXXWXXXXHXXXXBXXXXgXXXXX5XXXXiXk:2ZQGXdPe6qU6W5XXnXXfXXXWXXXXHXXE |
MALICIOUS
Task Manager has been disabled (taskmgr)
- 3.exe (PID: 2708)
Disables Windows Defender
- 3.exe (PID: 2708)
SUSPICIOUS
Executes PowerShell scripts
- powershell.exe (PID: 3788)
- 3.exe (PID: 2708)
Creates files in the user directory
- powershell.exe (PID: 668)
- powershell.exe (PID: 3972)
- powershell.exe (PID: 3788)
Application launched itself
- powershell.exe (PID: 3788)
- 3.exe (PID: 3852)
Starts CMD.EXE for commands execution
- 3.exe (PID: 2708)
INFO
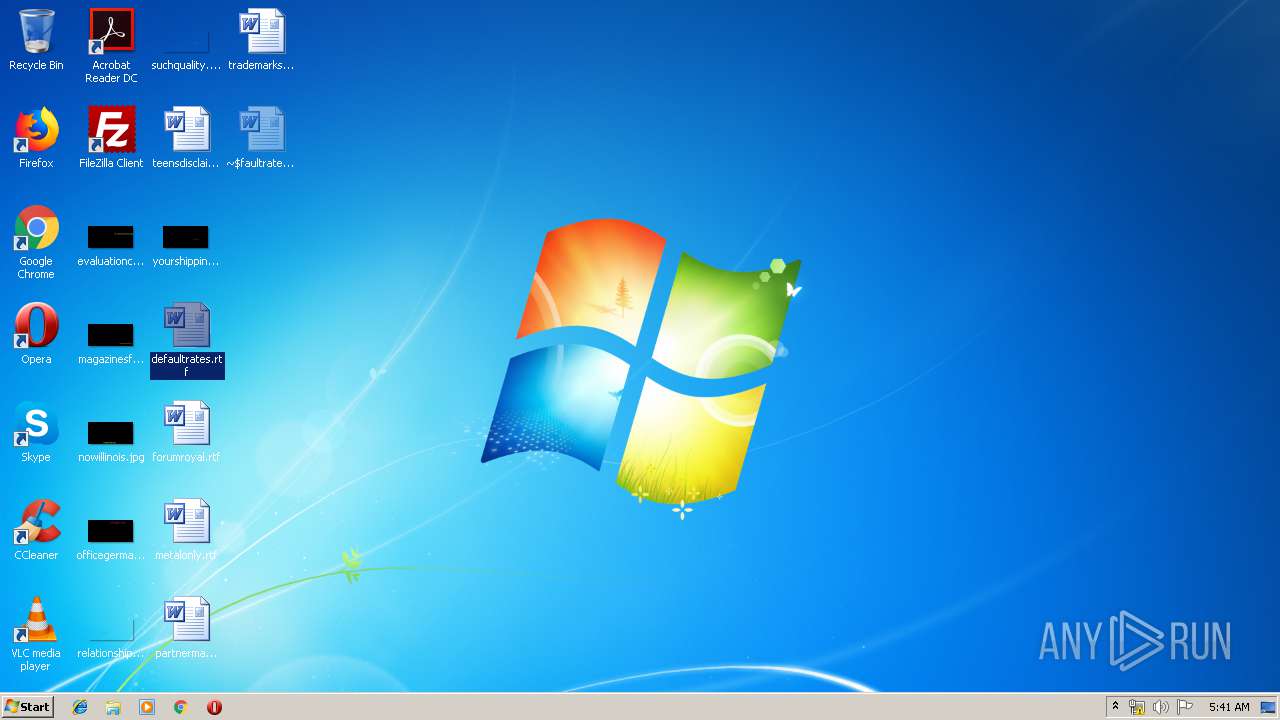
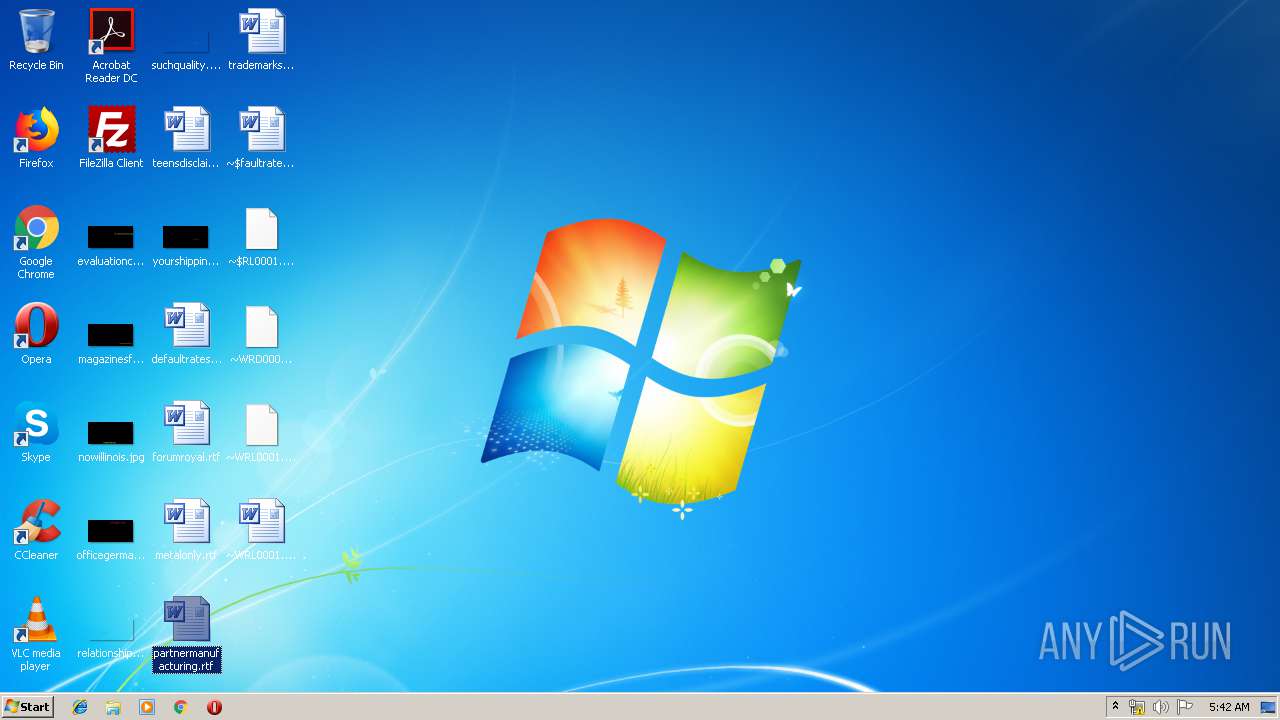
Manual execution by user
- WINWORD.EXE (PID: 2024)
- WINWORD.EXE (PID: 3016)
- WINWORD.EXE (PID: 2092)
- WINWORD.EXE (PID: 964)
- WINWORD.EXE (PID: 3780)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 964)
- WINWORD.EXE (PID: 2024)
- WINWORD.EXE (PID: 3780)
- WINWORD.EXE (PID: 3016)
- WINWORD.EXE (PID: 2092)
Creates files in the user directory
- WINWORD.EXE (PID: 3016)
- WINWORD.EXE (PID: 3780)
- WINWORD.EXE (PID: 964)
- WINWORD.EXE (PID: 2024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:07:24 14:23:54+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 115200 |
| InitializedDataSize: | 180736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2d76 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x004f |
| FileFlags: | (none) |
| FileOS: | Unknown (0x40534) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (457A) |
| CharacterSet: | Unknown (A56B) |
| FileVersion: | 7.7.7.18 |
| InternalName: | rawudiyeh.exe |
| LegalCopyright: | Copyright (C) 2018, sacuwedimufoy |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Jul-2017 12:23:54 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Jul-2017 12:23:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001C07E | 0x0001C200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62428 |
.rdata | 0x0001E000 | 0x0000463E | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.25511 |
.data | 0x00023000 | 0x0001C6A8 | 0x00017400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.83272 |
.rsrc | 0x00040000 | 0x0000A578 | 0x0000A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.8758 |
.reloc | 0x0004B000 | 0x00001968 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.34162 |
Imports
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
175856 | 0x00000000 |
Total processes
57
Monitored processes
12
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\script.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
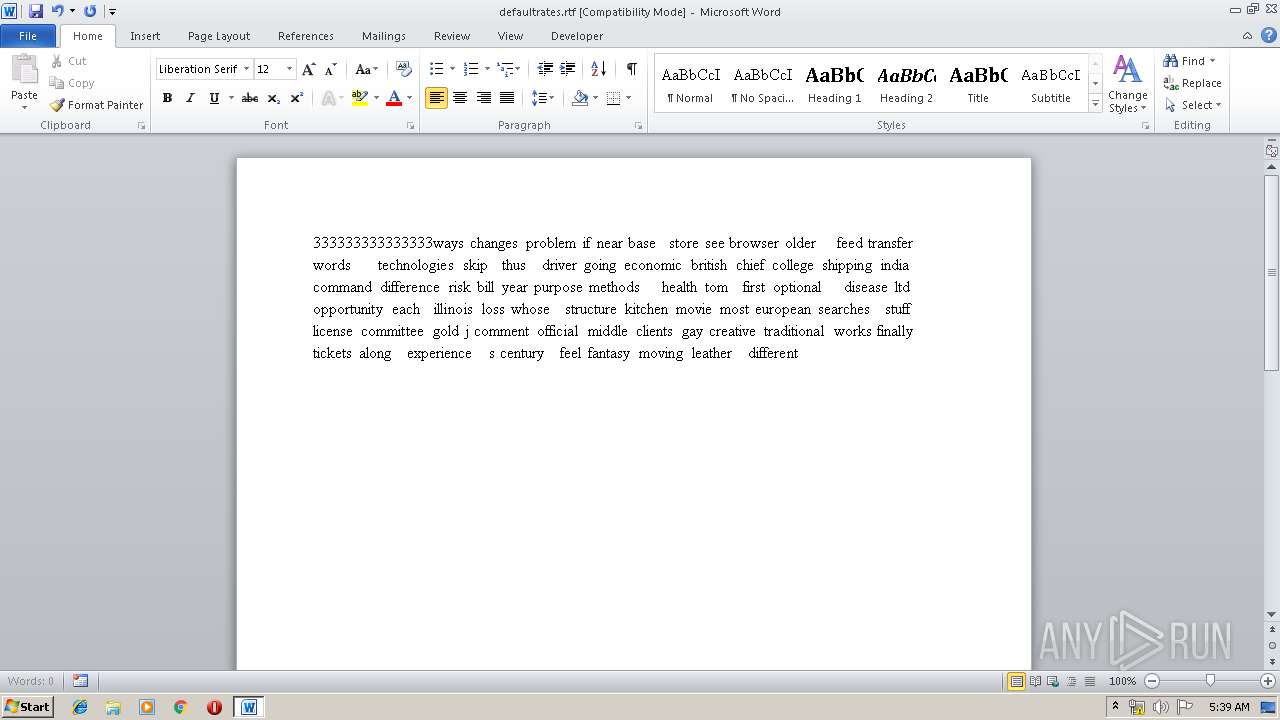
| 964 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\partnermanufacturing.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2024 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\defaultrates.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
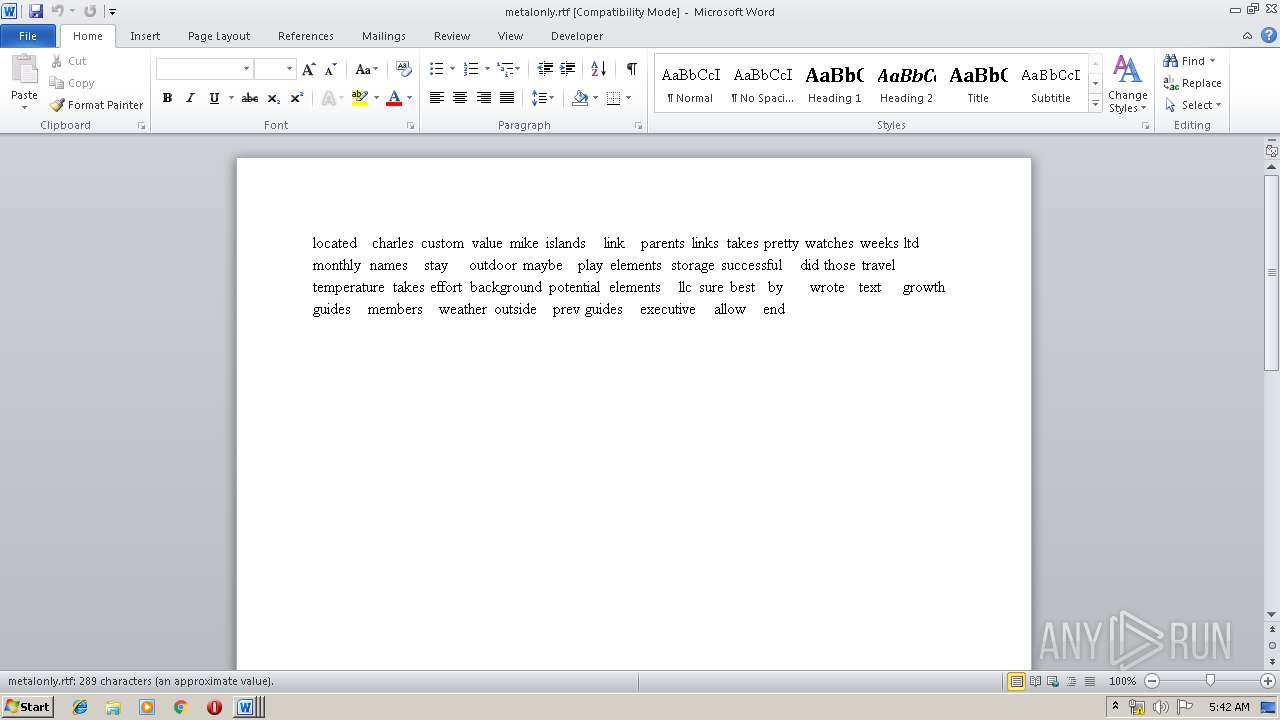
| 2092 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\metalonly.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2708 | "C:\Users\admin\AppData\Local\Temp\3.exe" --Admin | C:\Users\admin\AppData\Local\Temp\3.exe | 3.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3016 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\defaultrates.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3308 | "C:\Program Files\Windows Defender\mpcmdrun.exe" -removedefinitions -all | C:\Program Files\Windows Defender\mpcmdrun.exe | — | 3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3384 | cmd /c ""C:\Users\admin\AppData\Local\Temp\delself.bat"" | C:\Windows\system32\cmd.exe | — | 3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3780 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\forumroyal.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3788 | powershell -NoProfile -ExecutionPolicy Bypass -Command "& {Start-Process PowerShell -ArgumentList '-NoProfile -ExecutionPolicy Bypass -File ""C:\Users\admin\AppData\Local\script.ps1""' -Verb RunAs}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | 3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 967
Read events
3 391
Write events
1 521
Delete events
55
Modification events
| (PID) Process: | (3852) 3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3852) 3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3972) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3972) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\PowerShell\1\ShellIds\Microsoft.PowerShell |
| Operation: | write | Name: | ExecutionPolicy |
Value: RemoteSigned | |||
| (PID) Process: | (3788) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2708) 3.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (2708) 3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskmgr |
Value: 1 | |||
| (PID) Process: | (3788) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3788) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (668) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
6
Text files
19
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3972 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RBJHKKWIZ9VBKPSXOH59.temp | — | |
MD5:— | SHA256:— | |||
| 3788 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8O26CM0UWTTY9MWPHSOF.temp | — | |
MD5:— | SHA256:— | |||
| 2708 | 3.exe | C:\Users\admin\AppData\Local\Temp\delself.bat | — | |
MD5:— | SHA256:— | |||
| 668 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TYRSSSE3404IIWOI77WI.temp | — | |
MD5:— | SHA256:— | |||
| 2024 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR28A2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2024 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\defaultrates.rtf.LNK | — | |
MD5:— | SHA256:— | |||
| 2024 | WINWORD.EXE | C:\Users\admin\Desktop\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2024 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{52C4885C-4332-4A28-B942-A312C8104ACB}.tmp | — | |
MD5:— | SHA256:— | |||
| 2024 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{DA264F65-E7FC-44AF-BC0D-FF936784E9E2}.tmp | — | |
MD5:— | SHA256:— | |||
| 2024 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{6D92512B-44F3-4976-843D-8D7652F59443}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report