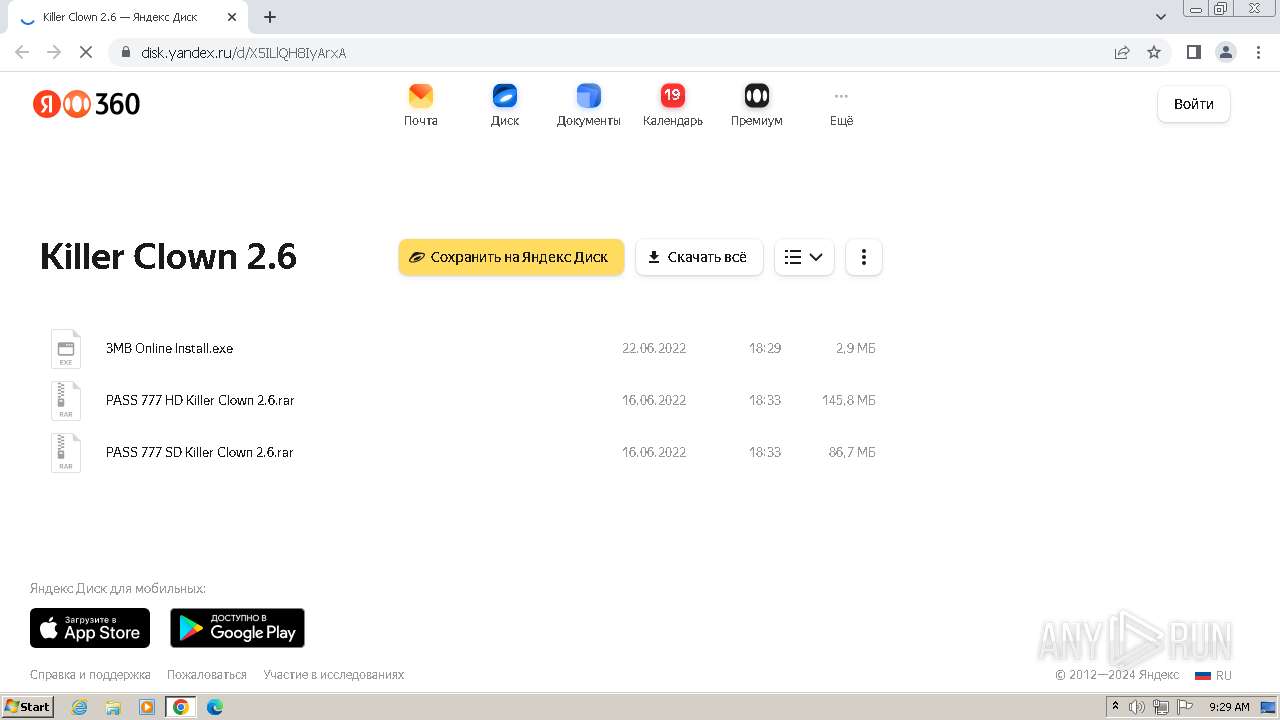
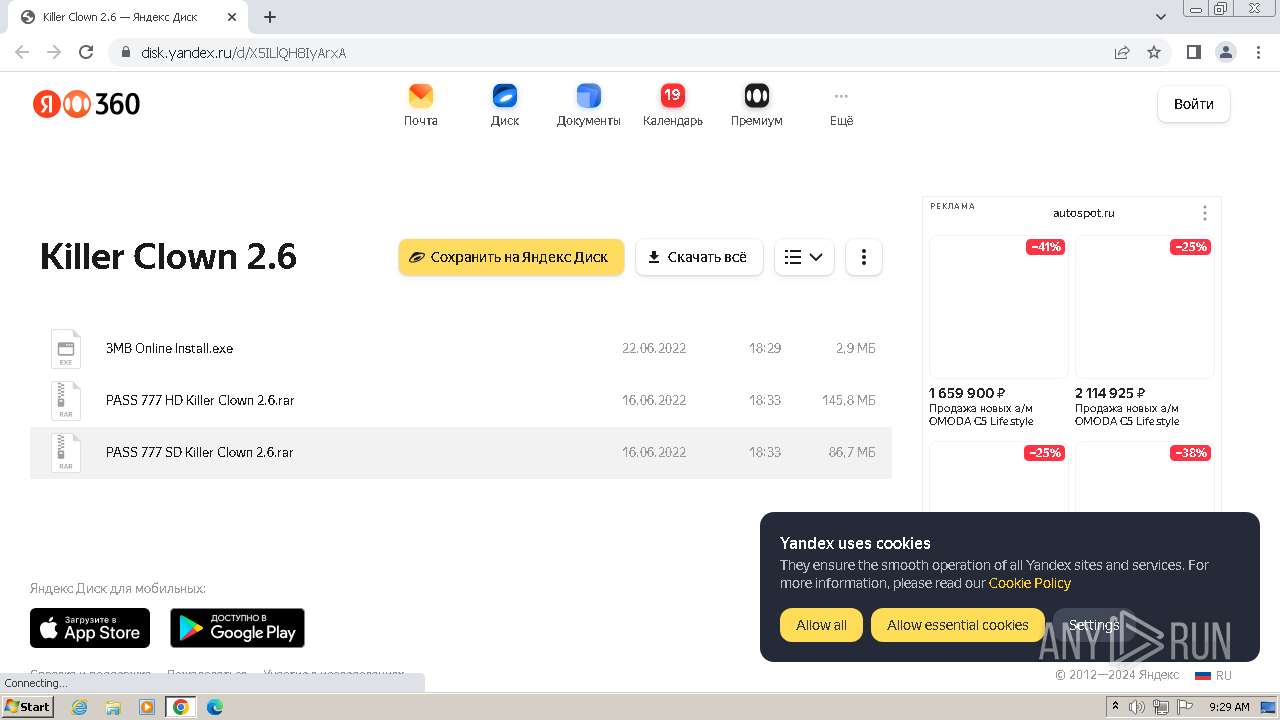
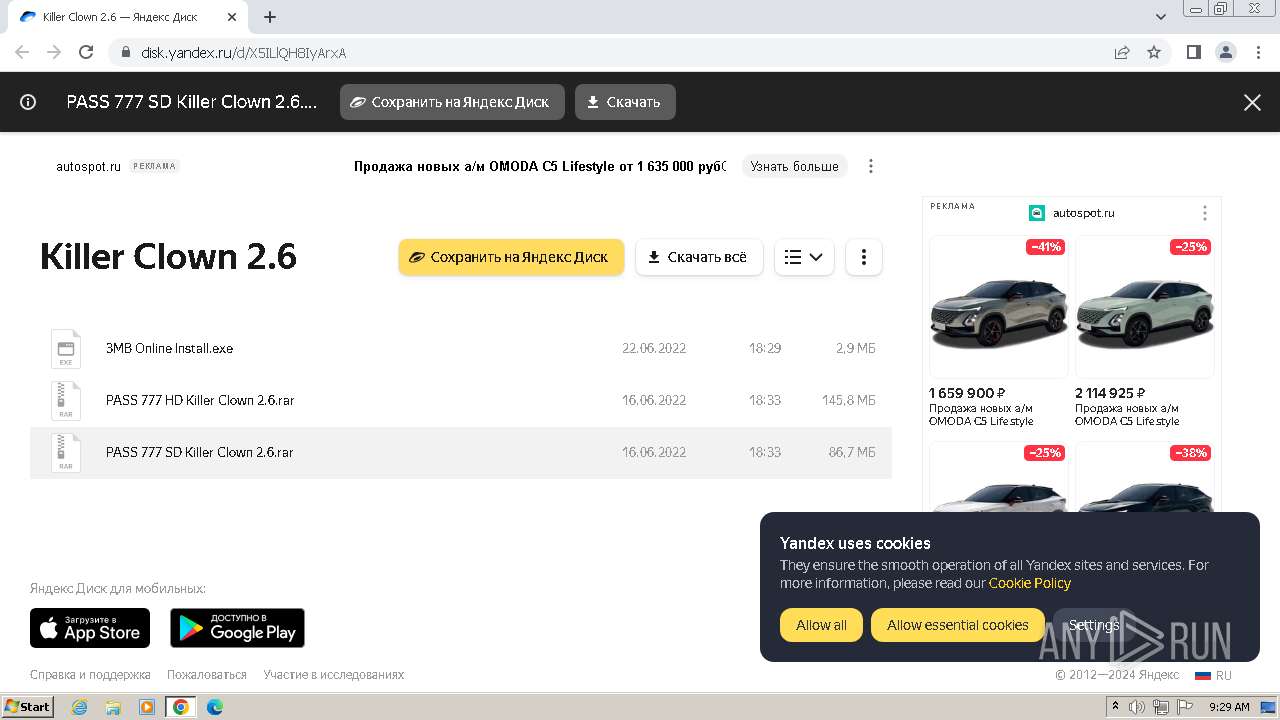
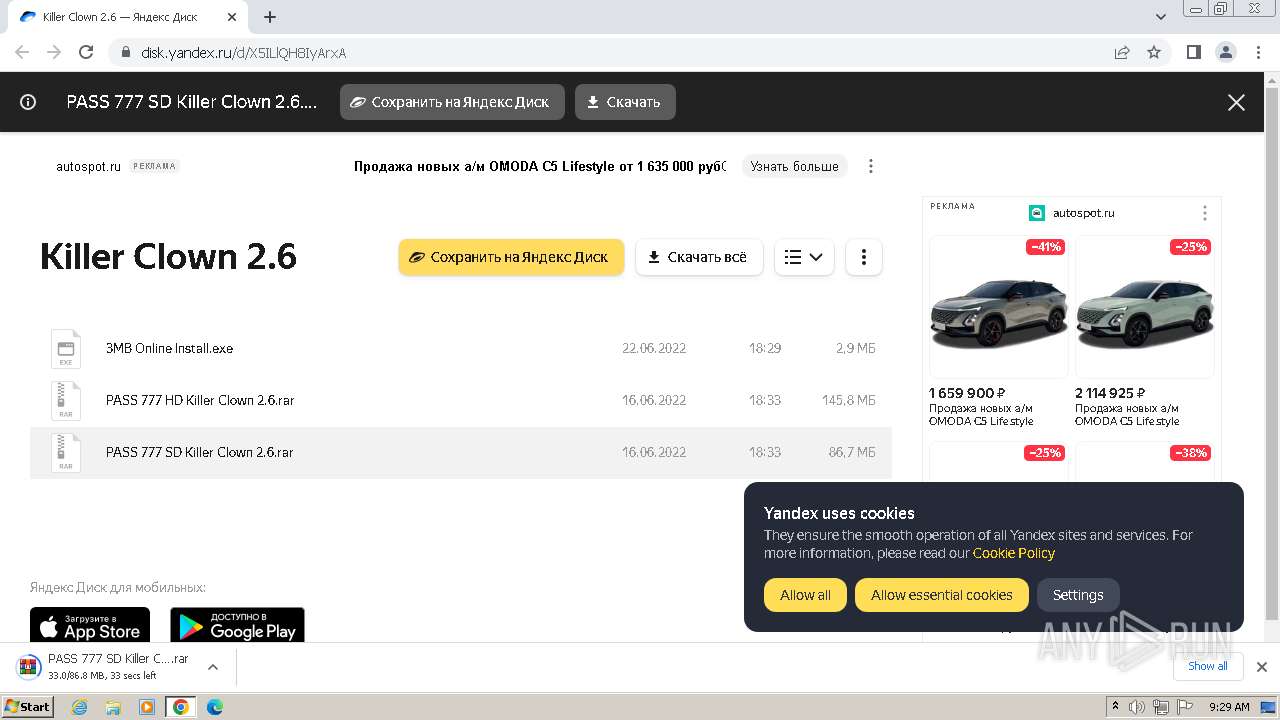
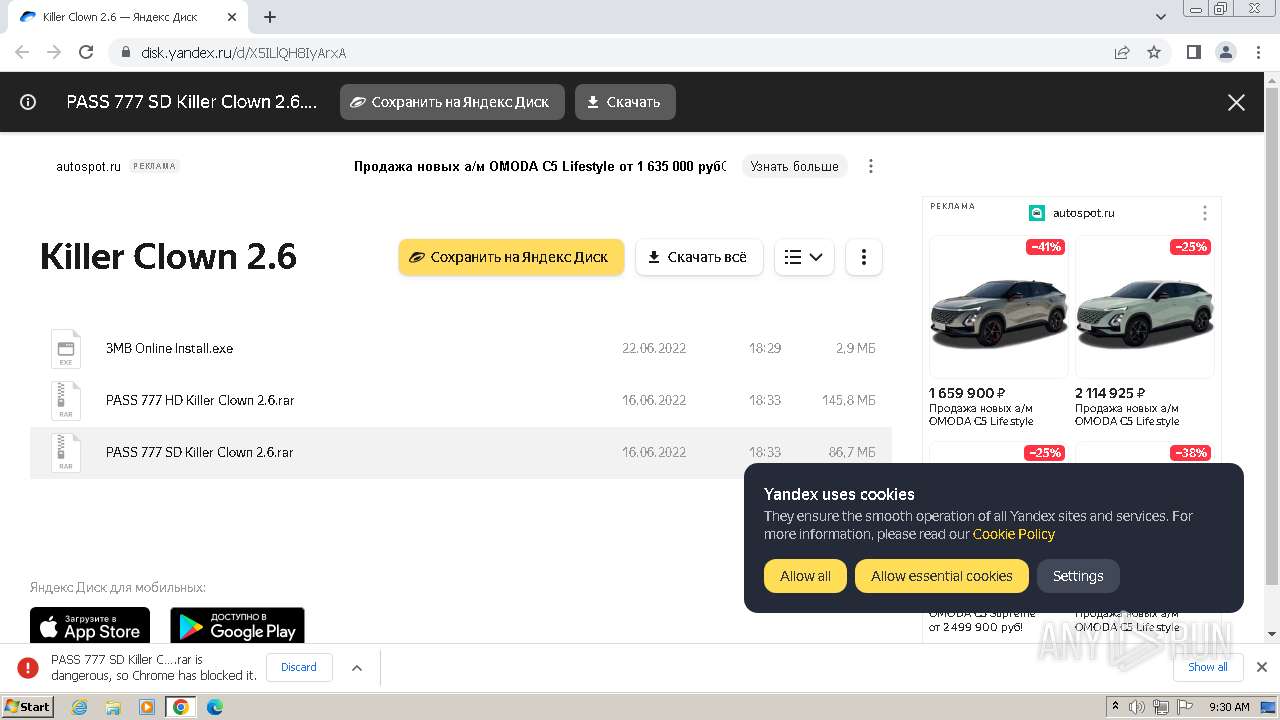
| URL: | https://disk.yandex.ru/d/X5ILlQH8IyArxA |
| Full analysis: | https://app.any.run/tasks/54ba3f37-2fa2-4c5e-9188-c13d85adb028 |
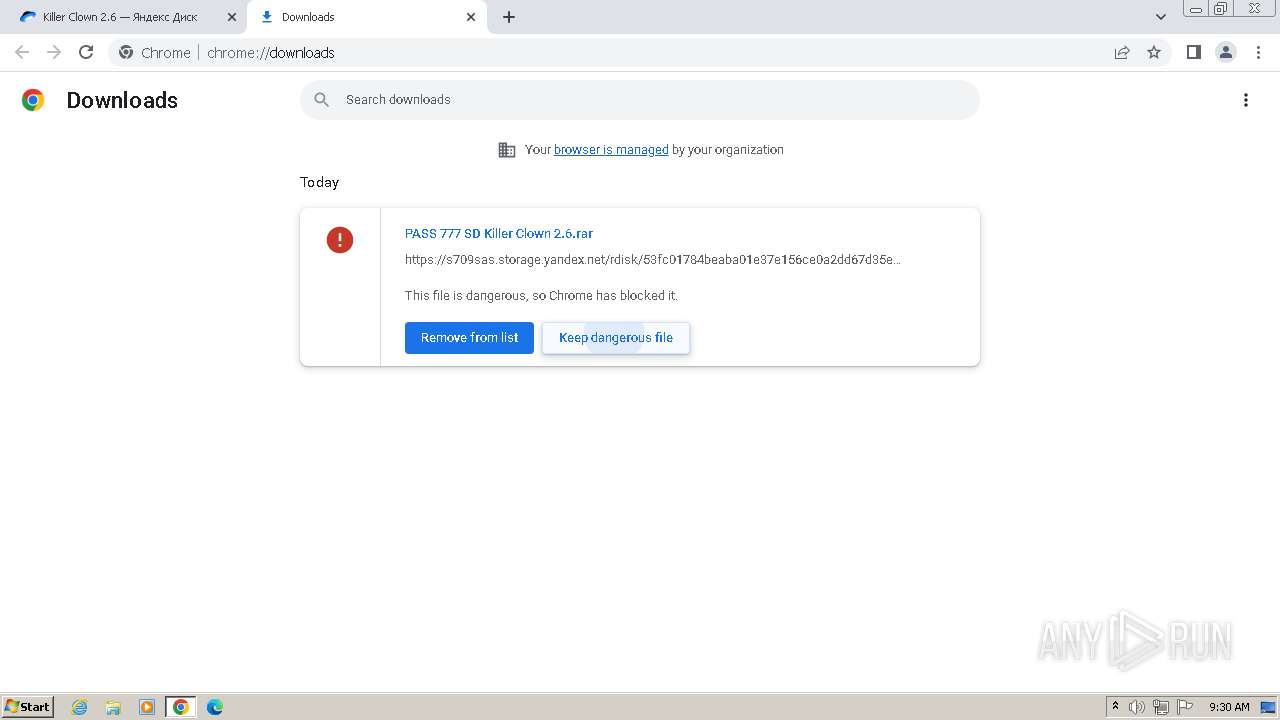
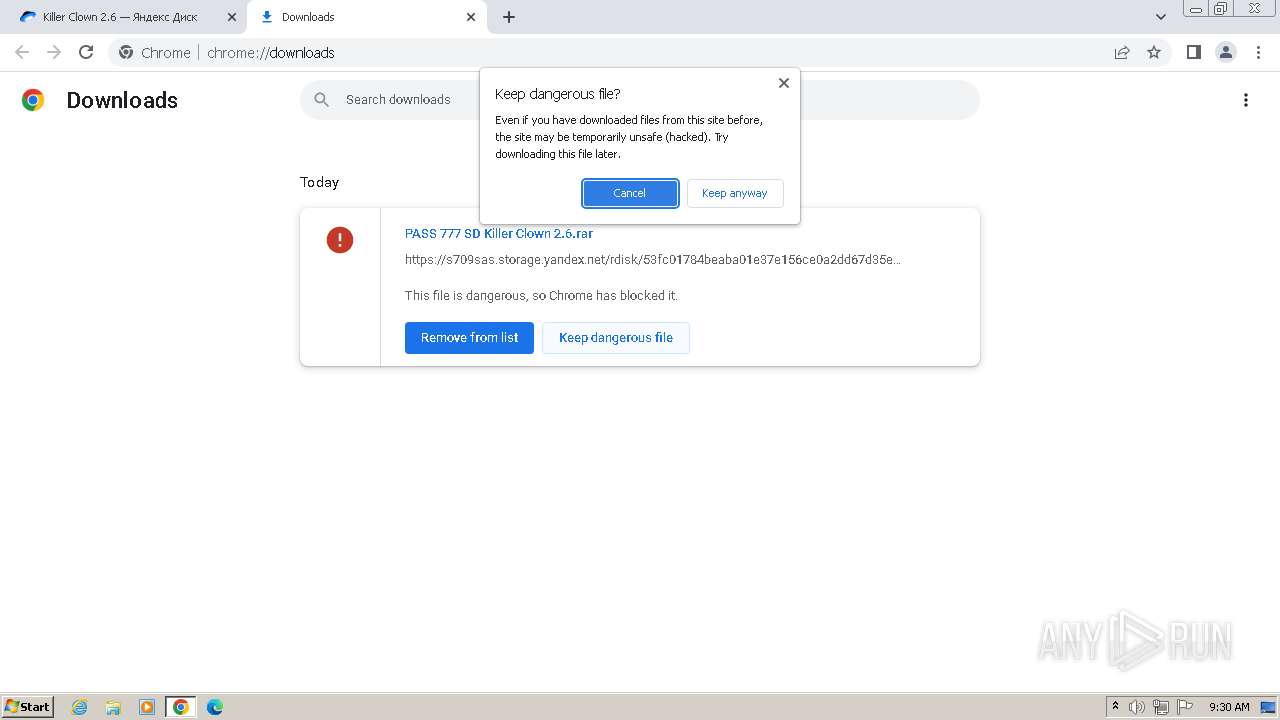
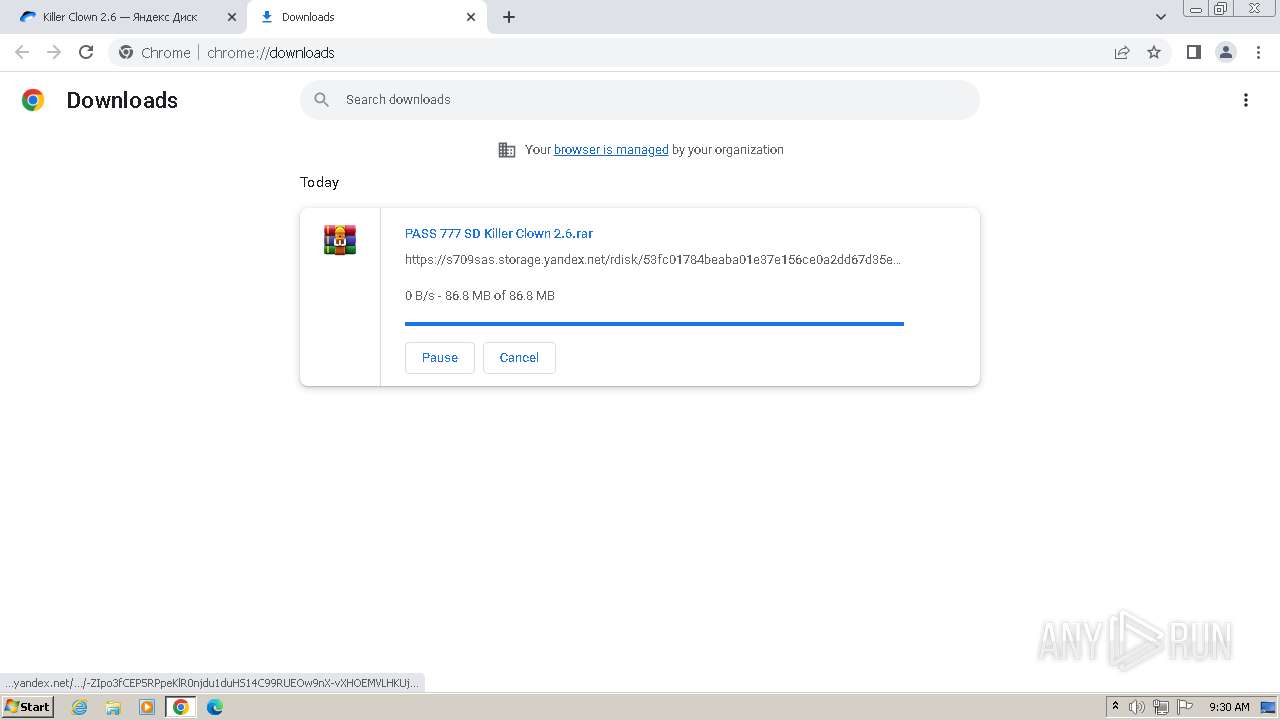
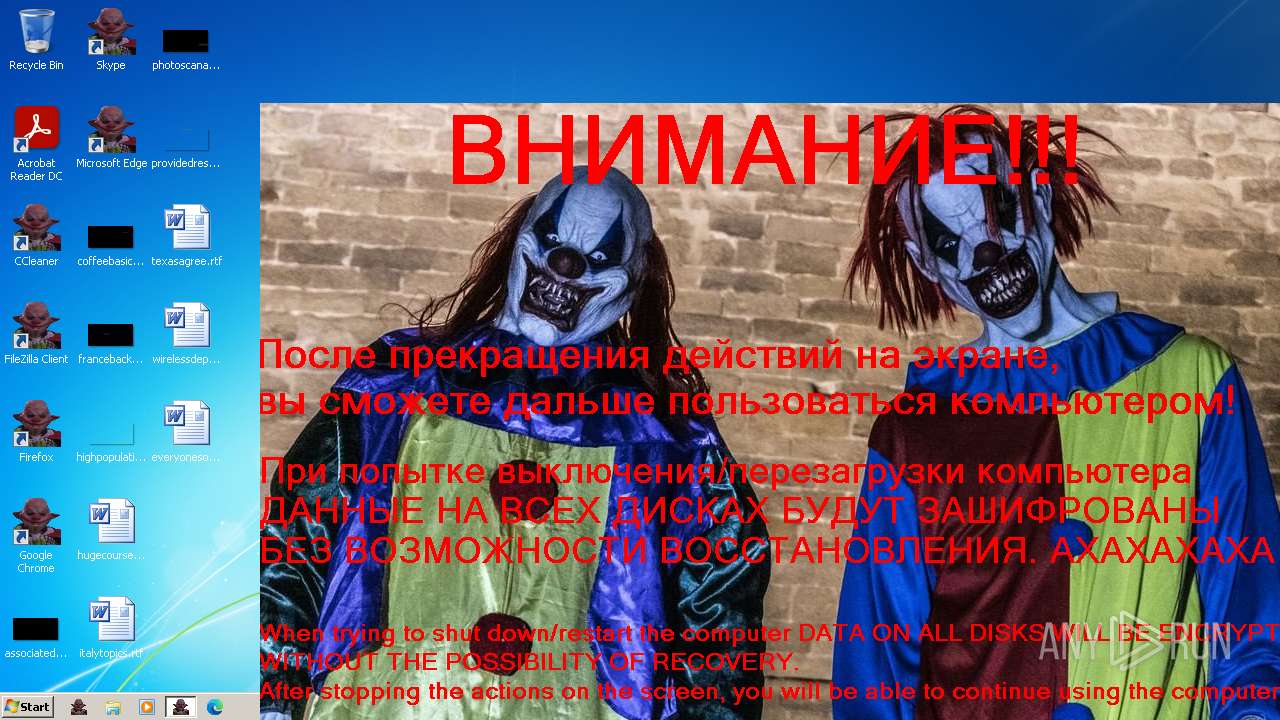
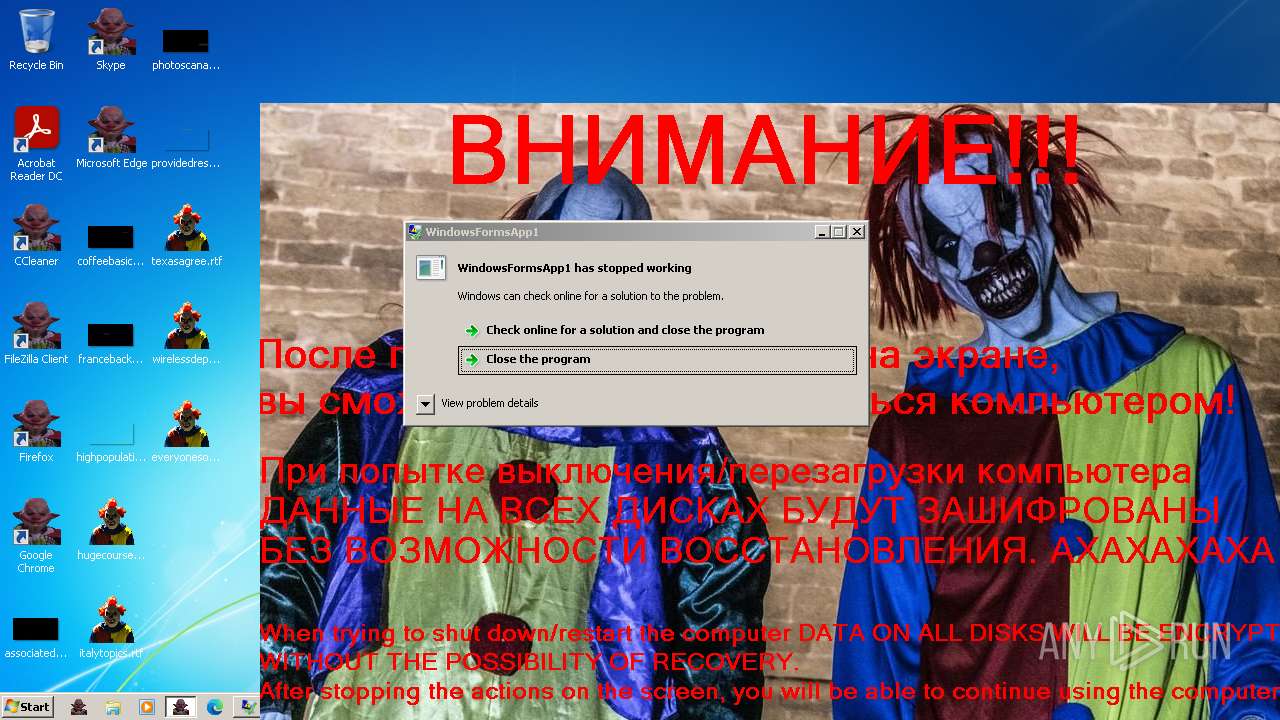
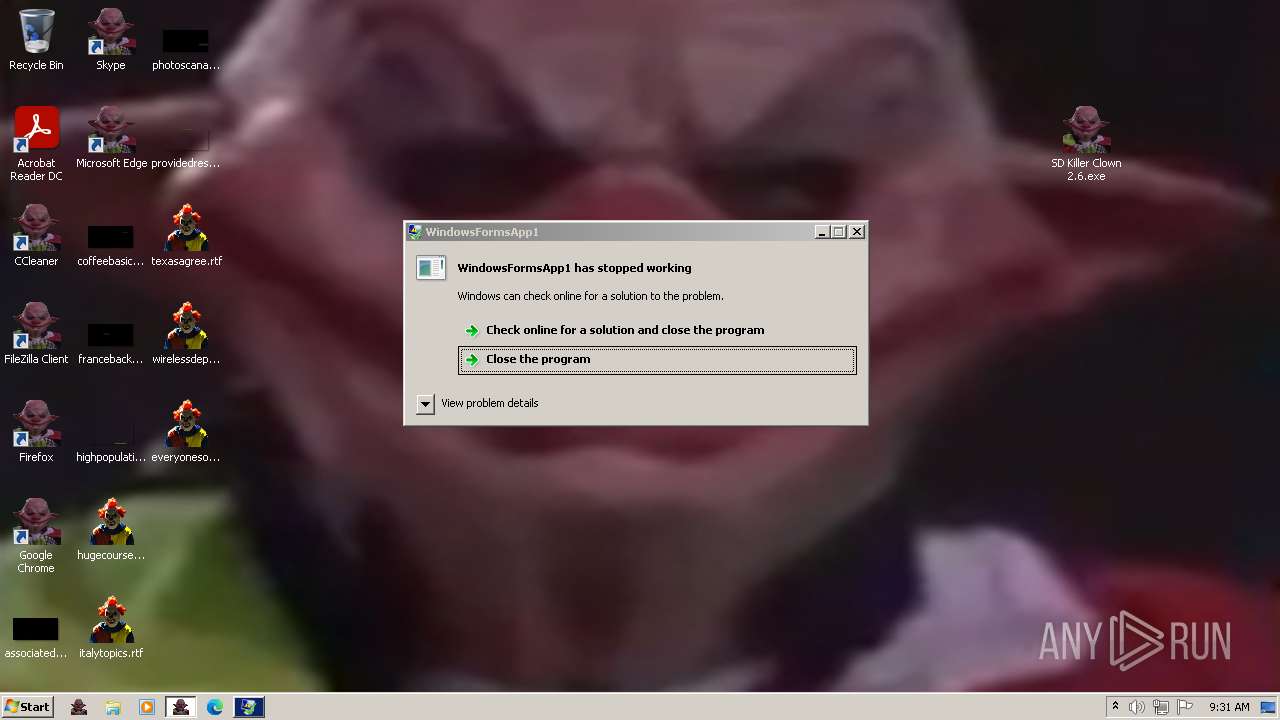
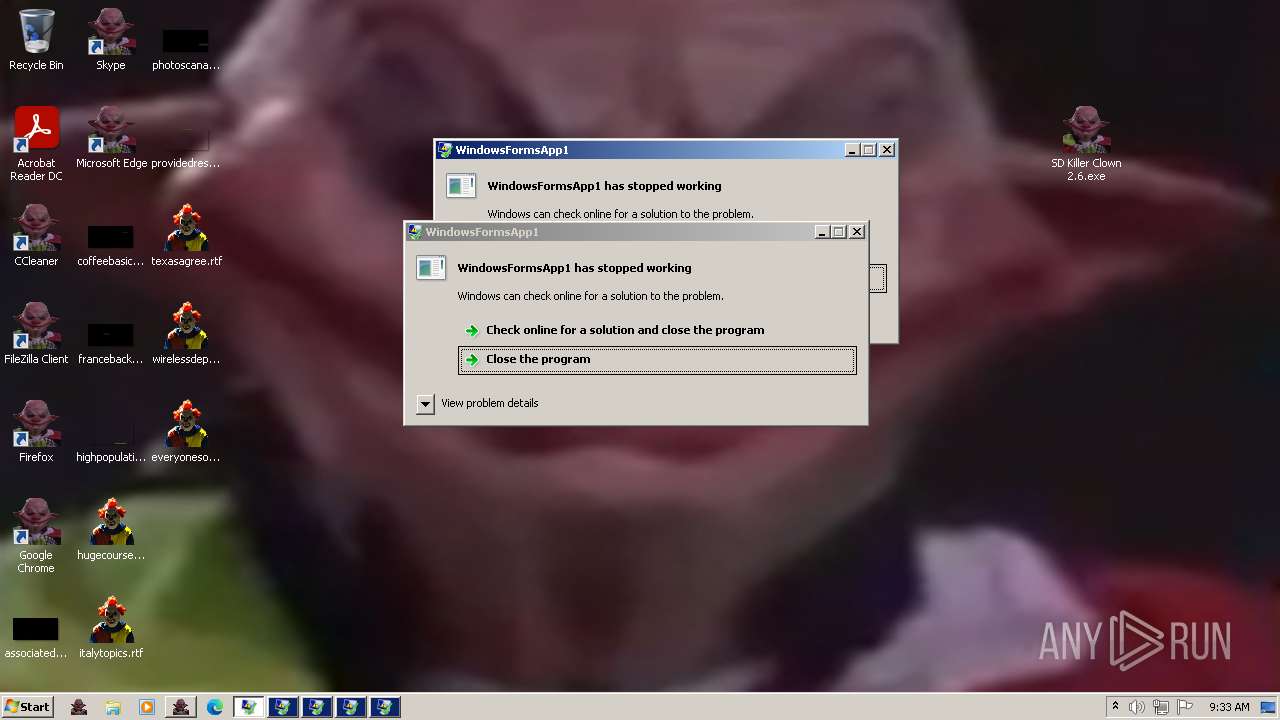
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2024, 08:28:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
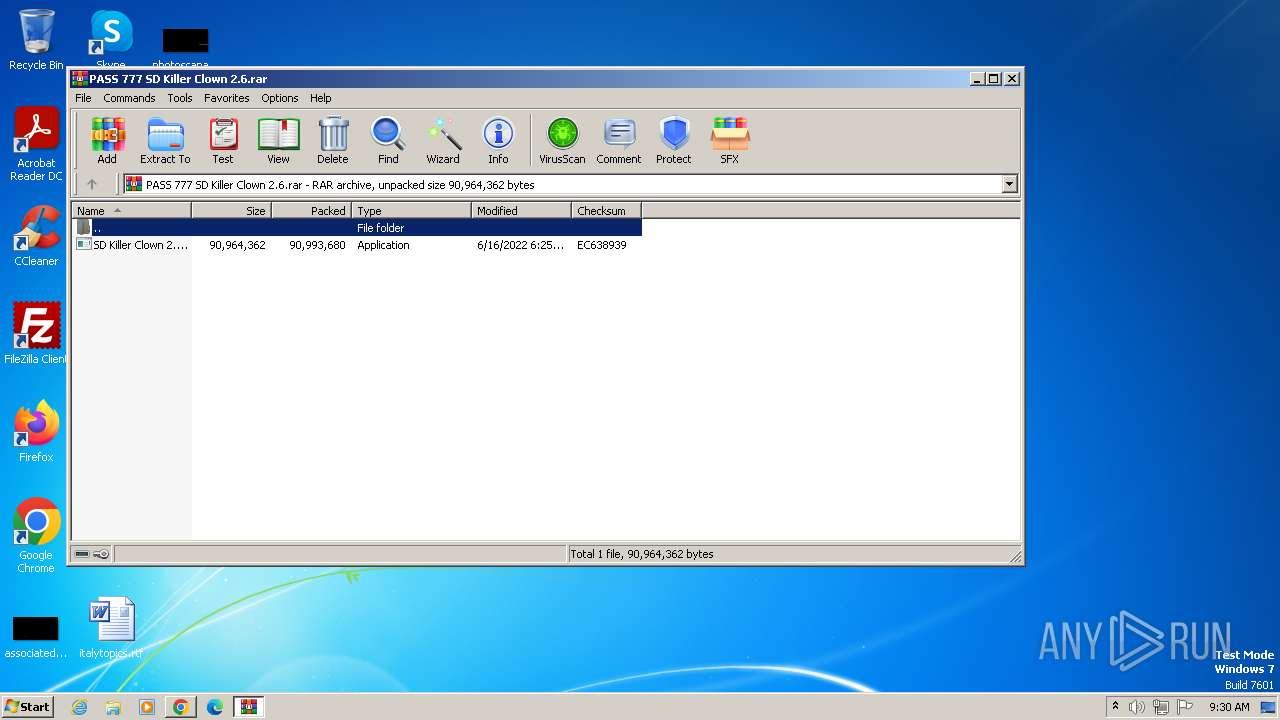
| MD5: | 3E4AD21726D51C415A1E9D8CA049A2DE |
| SHA1: | ECAEC5C9FF42D847374D0938AEA21E0F6A70B795 |
| SHA256: | 14A5B42F65D0AF41435A953B0EC6FD30AC1BA2C5AF2A3A364F13D91D5AD19D07 |
| SSDEEP: | 3:N8U2f09m:2U2p |
MALICIOUS
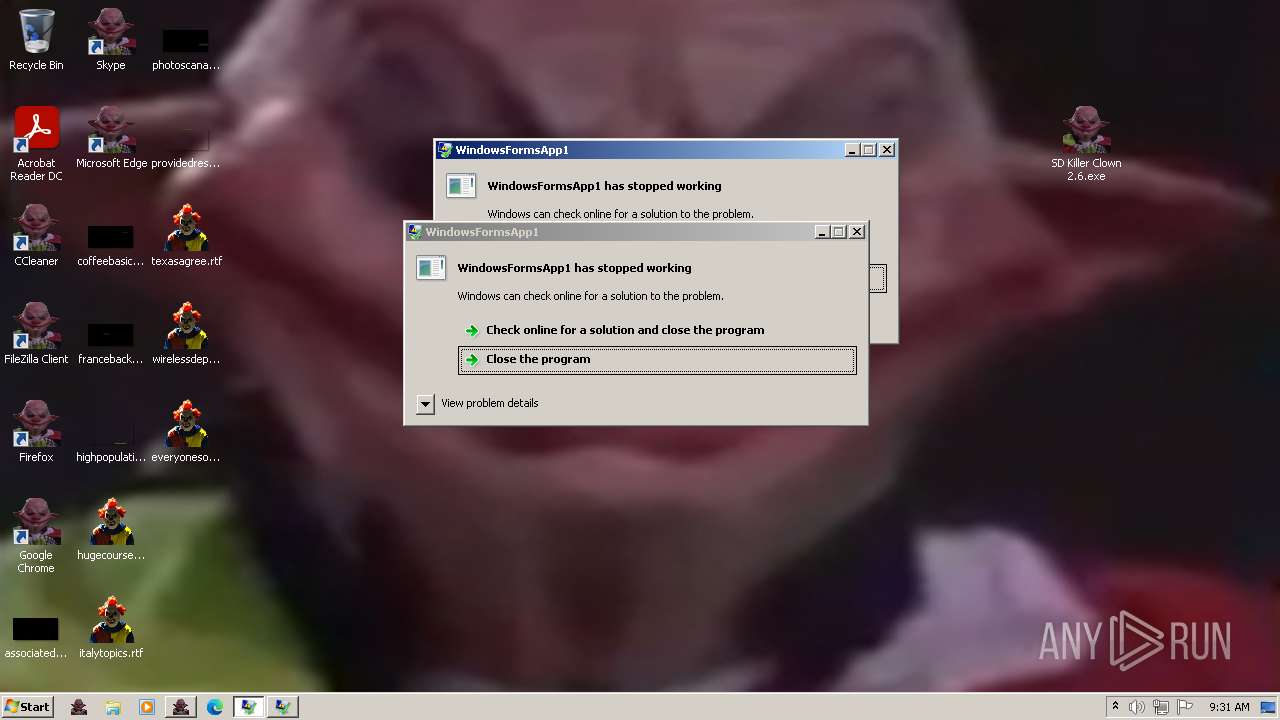
Drops the executable file immediately after the start
- SD Killer Clown 2.6.exe (PID: 3404)
- cmd.exe (PID: 3604)
- cmd.exe (PID: 3600)
Deletes shadow copies
- cmd.exe (PID: 3604)
Disables Windows Defender
- DisDef.exe (PID: 1396)
- DisDef.exe (PID: 2136)
Creates or modifies Windows services
- DisDef.exe (PID: 1396)
- DisDef.exe (PID: 2136)
UAC/LUA settings modification
- reg.exe (PID: 3660)
Changes the autorun value in the registry
- ie4uinit.exe (PID: 3772)
- ie4uinit.exe (PID: 1996)
Changes the login/logoff helper path in the registry
- Winlog.exe (PID: 2932)
- Winlog.exe (PID: 3972)
Create files in the Startup directory
- cmd.exe (PID: 3600)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 904)
SUSPICIOUS
Executable content was dropped or overwritten
- SD Killer Clown 2.6.exe (PID: 3404)
- cmd.exe (PID: 3604)
- cmd.exe (PID: 3600)
Drops 7-zip archiver for unpacking
- SD Killer Clown 2.6.exe (PID: 3404)
- cmd.exe (PID: 3604)
Process drops legitimate windows executable
- SD Killer Clown 2.6.exe (PID: 3404)
Reads the Internet Settings
- SD Killer Clown 2.6.exe (PID: 3404)
- clown.exe (PID: 3560)
- startban.exe (PID: 3540)
- startcur.exe (PID: 3532)
- startkey.exe (PID: 3912)
- def.exe (PID: 3528)
- key.exe (PID: 2268)
- WMIC.exe (PID: 3360)
- startdelstartup.exe (PID: 2564)
- startuac.exe (PID: 848)
- startauto.exe (PID: 2908)
- startWinlog.exe (PID: 2920)
- startExplorerIcons.exe (PID: 2724)
- uac.exe (PID: 2980)
- starticons.exe (PID: 1960)
- delstartup.exe (PID: 1888)
- auto.exe (PID: 3664)
- ExplorerIcons.exe (PID: 3712)
- icons.exe (PID: 3448)
- starthosts.exe (PID: 1816)
- clown.exe (PID: 2204)
- startWPChanger.exe (PID: 3516)
- startvol.exe (PID: 4064)
- startScreenBlocker.exe (PID: 3504)
- startcur.exe (PID: 1288)
- attention.exe (PID: 2392)
- hosts.exe (PID: 1396)
- startf.exe (PID: 236)
- startWinlog.exe (PID: 2696)
- vol.exe (PID: 3076)
- startban.exe (PID: 2028)
- f.exe (PID: 2848)
- VideoPlayer.exe (PID: 2696)
- VideoPlayer.exe (PID: 3432)
Reads security settings of Internet Explorer
- SD Killer Clown 2.6.exe (PID: 3404)
- clown.exe (PID: 3560)
- startban.exe (PID: 3540)
- startcur.exe (PID: 3532)
- startkey.exe (PID: 3912)
- def.exe (PID: 3528)
- key.exe (PID: 2268)
- startdelstartup.exe (PID: 2564)
- startuac.exe (PID: 848)
- startauto.exe (PID: 2908)
- startWinlog.exe (PID: 2920)
- startExplorerIcons.exe (PID: 2724)
- uac.exe (PID: 2980)
- starticons.exe (PID: 1960)
- delstartup.exe (PID: 1888)
- auto.exe (PID: 3664)
- ExplorerIcons.exe (PID: 3712)
- icons.exe (PID: 3448)
- starthosts.exe (PID: 1816)
- startWPChanger.exe (PID: 3516)
- clown.exe (PID: 2204)
- startvol.exe (PID: 4064)
- startcur.exe (PID: 1288)
- attention.exe (PID: 2392)
- hosts.exe (PID: 1396)
- startScreenBlocker.exe (PID: 3504)
- startf.exe (PID: 236)
- startWinlog.exe (PID: 2696)
- startban.exe (PID: 2028)
- vol.exe (PID: 3076)
- f.exe (PID: 2848)
Executing commands from a ".bat" file
- startban.exe (PID: 3540)
- clown.exe (PID: 3560)
- def.exe (PID: 3528)
- startkey.exe (PID: 3912)
- startcur.exe (PID: 3532)
- key.exe (PID: 2268)
- startdelstartup.exe (PID: 2564)
- startuac.exe (PID: 848)
- startauto.exe (PID: 2908)
- startWinlog.exe (PID: 2920)
- startExplorerIcons.exe (PID: 2724)
- uac.exe (PID: 2980)
- starticons.exe (PID: 1960)
- auto.exe (PID: 3664)
- delstartup.exe (PID: 1888)
- ExplorerIcons.exe (PID: 3712)
- icons.exe (PID: 3448)
- startWPChanger.exe (PID: 3516)
- starthosts.exe (PID: 1816)
- clown.exe (PID: 2204)
- startvol.exe (PID: 4064)
- startScreenBlocker.exe (PID: 3504)
- startcur.exe (PID: 1288)
- attention.exe (PID: 2392)
- hosts.exe (PID: 1396)
- startf.exe (PID: 236)
- startWinlog.exe (PID: 2696)
- startban.exe (PID: 2028)
- f.exe (PID: 2848)
- vol.exe (PID: 3076)
Starts CMD.EXE for commands execution
- clown.exe (PID: 3560)
- startban.exe (PID: 3540)
- def.exe (PID: 3528)
- startcur.exe (PID: 3532)
- startkey.exe (PID: 3912)
- key.exe (PID: 2268)
- startuac.exe (PID: 848)
- startdelstartup.exe (PID: 2564)
- startauto.exe (PID: 2908)
- startWinlog.exe (PID: 2920)
- startExplorerIcons.exe (PID: 2724)
- uac.exe (PID: 2980)
- starticons.exe (PID: 1960)
- auto.exe (PID: 3664)
- delstartup.exe (PID: 1888)
- ExplorerIcons.exe (PID: 3712)
- icons.exe (PID: 3448)
- starthosts.exe (PID: 1816)
- startWPChanger.exe (PID: 3516)
- startvol.exe (PID: 4064)
- clown.exe (PID: 2204)
- startScreenBlocker.exe (PID: 3504)
- startcur.exe (PID: 1288)
- attention.exe (PID: 2392)
- startf.exe (PID: 236)
- startWinlog.exe (PID: 2696)
- hosts.exe (PID: 1396)
- startban.exe (PID: 2028)
- f.exe (PID: 2848)
- vol.exe (PID: 3076)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1488)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 2856)
- cmd.exe (PID: 3884)
- cmd.exe (PID: 3512)
Application launched itself
- DisDef.exe (PID: 1396)
Executes as Windows Service
- VSSVC.exe (PID: 2168)
Changes default file association
- ie4uinit.exe (PID: 3772)
- ie4uinit.exe (PID: 1996)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 224)
- cmd.exe (PID: 3644)
The process executes VB scripts
- cmd.exe (PID: 3404)
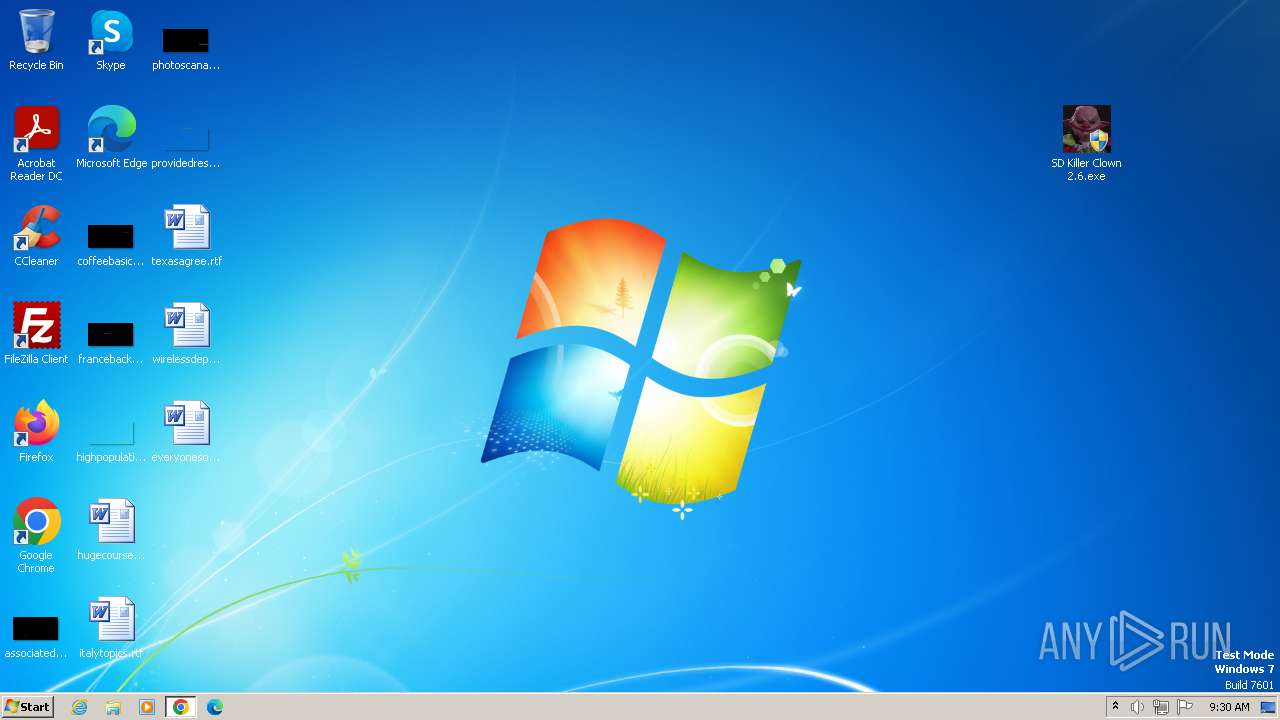
Changes the desktop background image
- WPChanger.exe (PID: 2900)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 224)
- cmd.exe (PID: 3644)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 2236)
- SD Killer Clown 2.6.exe (PID: 3404)
- clown.exe (PID: 3560)
- startban.exe (PID: 3540)
- def.exe (PID: 3528)
- startcur.exe (PID: 3532)
- startkey.exe (PID: 3912)
- DisDef.exe (PID: 1396)
- key.exe (PID: 2268)
- cur.exe (PID: 2368)
- DisDef.exe (PID: 2136)
- startdelstartup.exe (PID: 2564)
- startuac.exe (PID: 848)
- startauto.exe (PID: 2908)
- startWinlog.exe (PID: 2920)
- startExplorerIcons.exe (PID: 2724)
- uac.exe (PID: 2980)
- starticons.exe (PID: 1960)
- delstartup.exe (PID: 1888)
- Winlog.exe (PID: 2932)
- auto.exe (PID: 3664)
- ExplorerIcons.exe (PID: 3712)
- icons.exe (PID: 3448)
- starthosts.exe (PID: 1816)
- startWPChanger.exe (PID: 3516)
- clown.exe (PID: 2204)
- hosts.exe (PID: 1396)
- attention.exe (PID: 2392)
- WPChanger.exe (PID: 2900)
- startvol.exe (PID: 4064)
- startScreenBlocker.exe (PID: 3504)
- startcur.exe (PID: 1288)
- startf.exe (PID: 236)
- startban.exe (PID: 2028)
- ScreenBlocker.exe (PID: 2948)
- vol.exe (PID: 3076)
- startWinlog.exe (PID: 2696)
- hide.exe (PID: 2960)
- form.exe (PID: 3272)
- cur.exe (PID: 3852)
- f.exe (PID: 2848)
- Winlog.exe (PID: 3972)
- hide.exe (PID: 2644)
- hide.exe (PID: 2588)
- hide.exe (PID: 3296)
- VideoPlayer.exe (PID: 3432)
- hide.exe (PID: 3928)
- VideoPlayer.exe (PID: 2696)
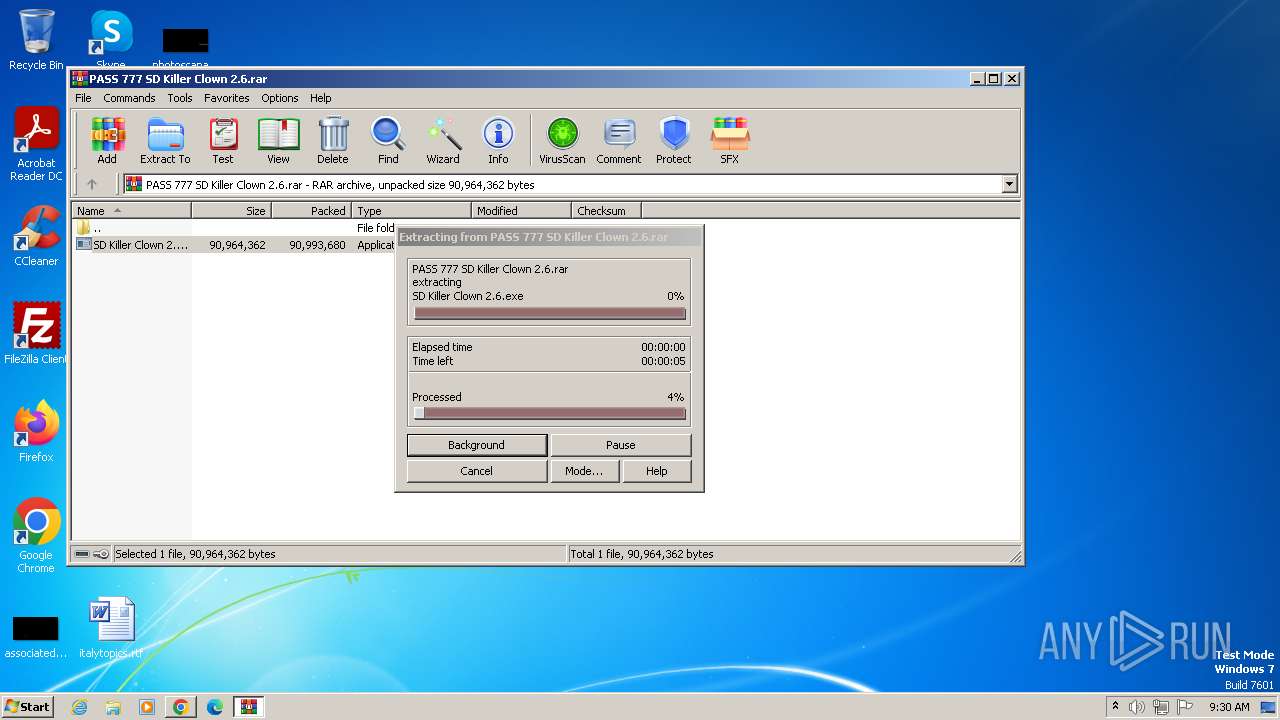
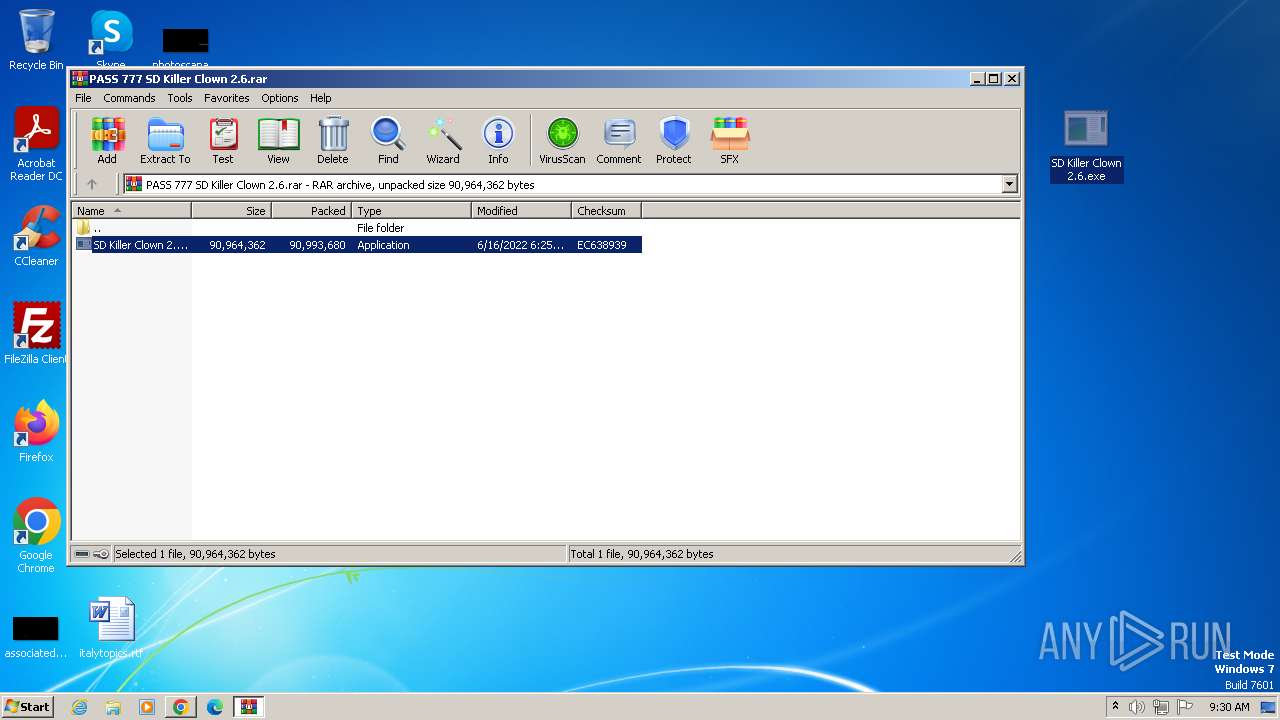
Manual execution by a user
- wmpnscfg.exe (PID: 2236)
- SD Killer Clown 2.6.exe (PID: 3404)
- SndVol.exe (PID: 2840)
- SD Killer Clown 2.6.exe (PID: 3200)
Reads the computer name
- wmpnscfg.exe (PID: 2236)
- SD Killer Clown 2.6.exe (PID: 3404)
- clown.exe (PID: 3560)
- startban.exe (PID: 3540)
- startcur.exe (PID: 3532)
- startkey.exe (PID: 3912)
- def.exe (PID: 3528)
- DisDef.exe (PID: 1396)
- key.exe (PID: 2268)
- cur.exe (PID: 2368)
- startdelstartup.exe (PID: 2564)
- startuac.exe (PID: 848)
- DisDef.exe (PID: 2136)
- startauto.exe (PID: 2908)
- startWinlog.exe (PID: 2920)
- startExplorerIcons.exe (PID: 2724)
- uac.exe (PID: 2980)
- delstartup.exe (PID: 1888)
- starticons.exe (PID: 1960)
- auto.exe (PID: 3664)
- ExplorerIcons.exe (PID: 3712)
- Winlog.exe (PID: 2932)
- icons.exe (PID: 3448)
- starthosts.exe (PID: 1816)
- startWPChanger.exe (PID: 3516)
- clown.exe (PID: 2204)
- startvol.exe (PID: 4064)
- startcur.exe (PID: 1288)
- attention.exe (PID: 2392)
- hosts.exe (PID: 1396)
- startScreenBlocker.exe (PID: 3504)
- startf.exe (PID: 236)
- startWinlog.exe (PID: 2696)
- startban.exe (PID: 2028)
- ScreenBlocker.exe (PID: 2948)
- hide.exe (PID: 2960)
- vol.exe (PID: 3076)
- cur.exe (PID: 3852)
- Winlog.exe (PID: 3972)
- f.exe (PID: 2848)
- form.exe (PID: 3272)
- WPChanger.exe (PID: 2900)
- hide.exe (PID: 2644)
- hide.exe (PID: 3296)
- hide.exe (PID: 3928)
- VideoPlayer.exe (PID: 3432)
- VideoPlayer.exe (PID: 2696)
- hide.exe (PID: 2588)
The process uses the downloaded file
- WinRAR.exe (PID: 1032)
- chrome.exe (PID: 2712)
Executable content was dropped or overwritten
- chrome.exe (PID: 3132)
- chrome.exe (PID: 1032)
Drops the executable file immediately after the start
- chrome.exe (PID: 3132)
- chrome.exe (PID: 1032)
Create files in a temporary directory
- clown.exe (PID: 3560)
- startban.exe (PID: 3540)
- def.exe (PID: 3528)
- startkey.exe (PID: 3912)
- startcur.exe (PID: 3532)
- key.exe (PID: 2268)
- DisDef.exe (PID: 1396)
- startdelstartup.exe (PID: 2564)
- startuac.exe (PID: 848)
- startauto.exe (PID: 2908)
- startWinlog.exe (PID: 2920)
- startExplorerIcons.exe (PID: 2724)
- starticons.exe (PID: 1960)
- uac.exe (PID: 2980)
- delstartup.exe (PID: 1888)
- icons.exe (PID: 3448)
- ExplorerIcons.exe (PID: 3712)
- auto.exe (PID: 3664)
- starthosts.exe (PID: 1816)
- clown.exe (PID: 2204)
- startWPChanger.exe (PID: 3516)
- hosts.exe (PID: 1396)
- startvol.exe (PID: 4064)
- startScreenBlocker.exe (PID: 3504)
- attention.exe (PID: 2392)
- startcur.exe (PID: 1288)
- startban.exe (PID: 2028)
- startWinlog.exe (PID: 2696)
- startf.exe (PID: 236)
- vol.exe (PID: 3076)
- f.exe (PID: 2848)
Application launched itself
- chrome.exe (PID: 3976)
Reads mouse settings
- DisDef.exe (PID: 1396)
- DisDef.exe (PID: 2136)
Creates files in the program directory
- cmd.exe (PID: 3604)
Reads the machine GUID from the registry
- Winlog.exe (PID: 2932)
- hide.exe (PID: 2960)
- form.exe (PID: 3272)
- Winlog.exe (PID: 3972)
- ScreenBlocker.exe (PID: 2948)
- WPChanger.exe (PID: 2900)
- hide.exe (PID: 2644)
- hide.exe (PID: 2588)
- hide.exe (PID: 3296)
- VideoPlayer.exe (PID: 2696)
- hide.exe (PID: 3928)
- VideoPlayer.exe (PID: 3432)
Checks proxy server information
- VideoPlayer.exe (PID: 2696)
- VideoPlayer.exe (PID: 3432)
Reads Environment values
- VideoPlayer.exe (PID: 2696)
- VideoPlayer.exe (PID: 3432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
424
Monitored processes
344
Malicious processes
18
Suspicious processes
20
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 204 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Icons" /v 112 /t REG_EXPAND_SZ /d C:\java\icons\5.ico /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3852 --field-trial-handle=1140,i,1835017371122547400,15868339868222336286,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 208 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Icons" /v 8 /t REG_EXPAND_SZ /d C:\java\icons\5.ico /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 208 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Icons" /v 114 /t REG_EXPAND_SZ /d C:\java\icons\5.ico /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 216 | reg add "HKEY_CLASSES_ROOT\ms-publisher\DefaultIcon" /ve /t REG_SZ /d "C:\java\icons\2.ico" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 224 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\2F74.tmp\2F75.tmp\2F76.bat C:\java\attention.exe" | C:\Windows\System32\cmd.exe | — | attention.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 236 | C:\java\protection\start\startf.exe | C:\java\protection\start\startf.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 236 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Icons" /v 68 /t REG_EXPAND_SZ /d C:\java\icons\5.ico /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 236 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Icons" /v 132 /t REG_EXPAND_SZ /d C:\java\icons\5.ico /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2040 --field-trial-handle=1140,i,1835017371122547400,15868339868222336286,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
36 259
Read events
35 502
Write events
654
Delete events
103
Modification events
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
63
Suspicious files
346
Text files
130
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1057f5.TMP | — | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF105a86.TMP | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF105bfd.TMP | text | |
MD5:E53573A93829681410D5E7DBB1B61C78 | SHA256:A82D28F2C1E22A2AE0ABC5F5AF0CC8EE7AD913BAB3A0BF84CE6D8D23F67E06A3 | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF1070fc.TMP | — | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3976 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF105a47.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
54
TCP/UDP connections
101
DNS requests
133
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3976 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
864 | chrome.exe | 142.251.173.84:443 | accounts.google.com | GOOGLE | US | unknown |
864 | chrome.exe | 87.250.250.50:443 | disk.yandex.ru | YANDEX LLC | RU | whitelisted |
864 | chrome.exe | 142.250.185.68:443 | www.google.com | GOOGLE | US | whitelisted |
3976 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
864 | chrome.exe | 178.154.131.215:443 | yastatic.net | YANDEX LLC | RU | whitelisted |
864 | chrome.exe | 77.88.21.148:443 | docviewer.yandex.ru | YANDEX LLC | RU | unknown |
864 | chrome.exe | 93.158.134.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
864 | chrome.exe | 77.88.44.66:443 | yandex.ru | YANDEX LLC | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
disk.yandex.ru |
| unknown |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
yastatic.net |
| whitelisted |
docviewer.yandex.ru |
| whitelisted |
mc.yandex.ru |
| whitelisted |
mc.yandex.com |
| whitelisted |
yandex.ru |
| whitelisted |
avatars.mds.yandex.net |
| whitelisted |
ads.adfox.ru |
| whitelisted |