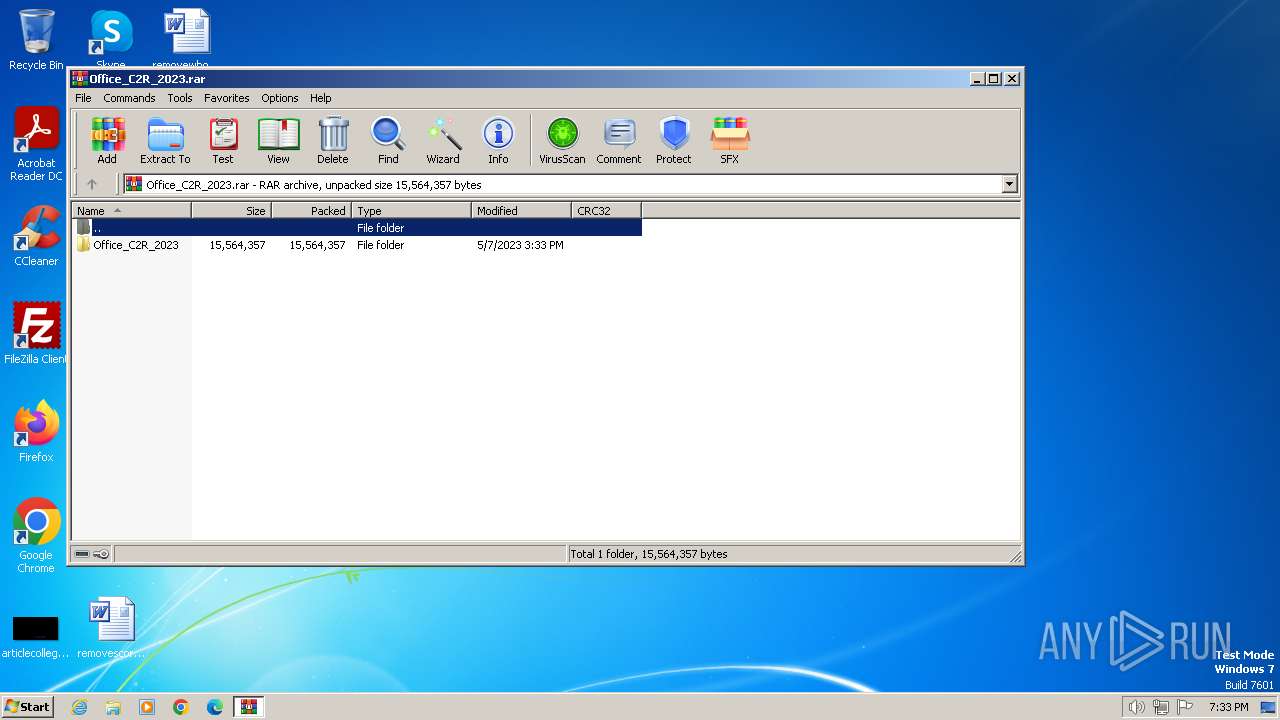
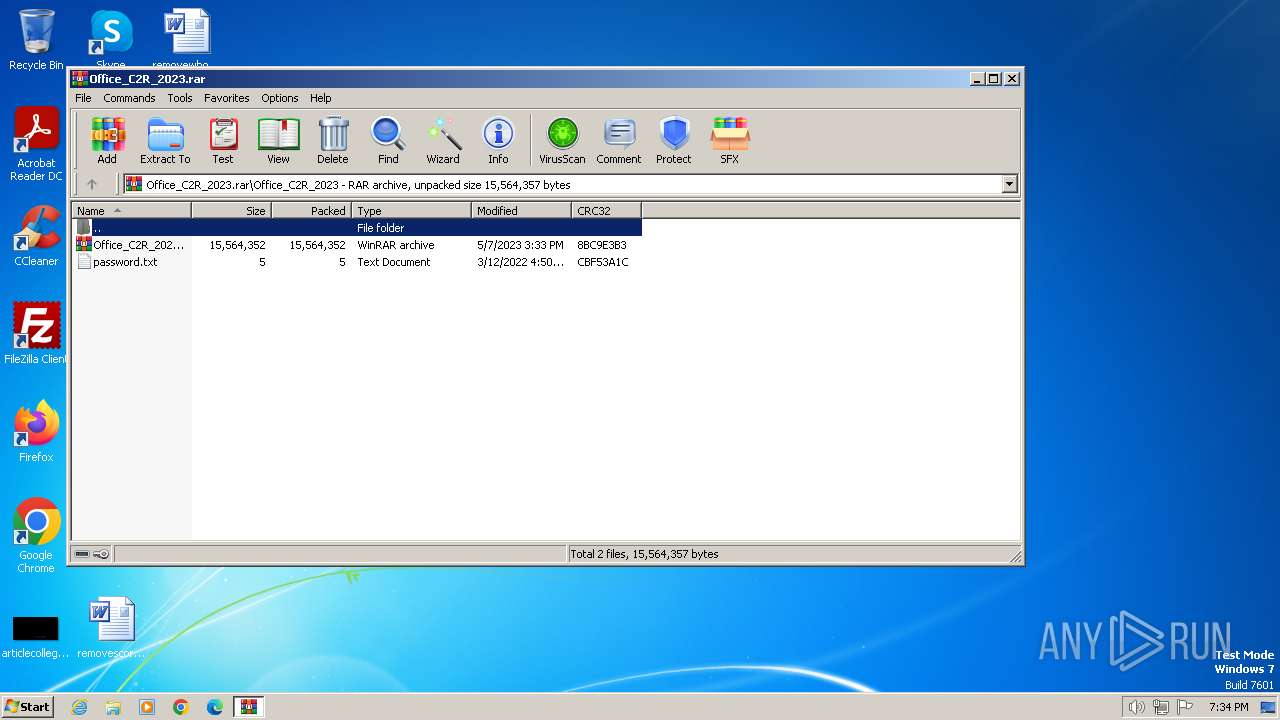
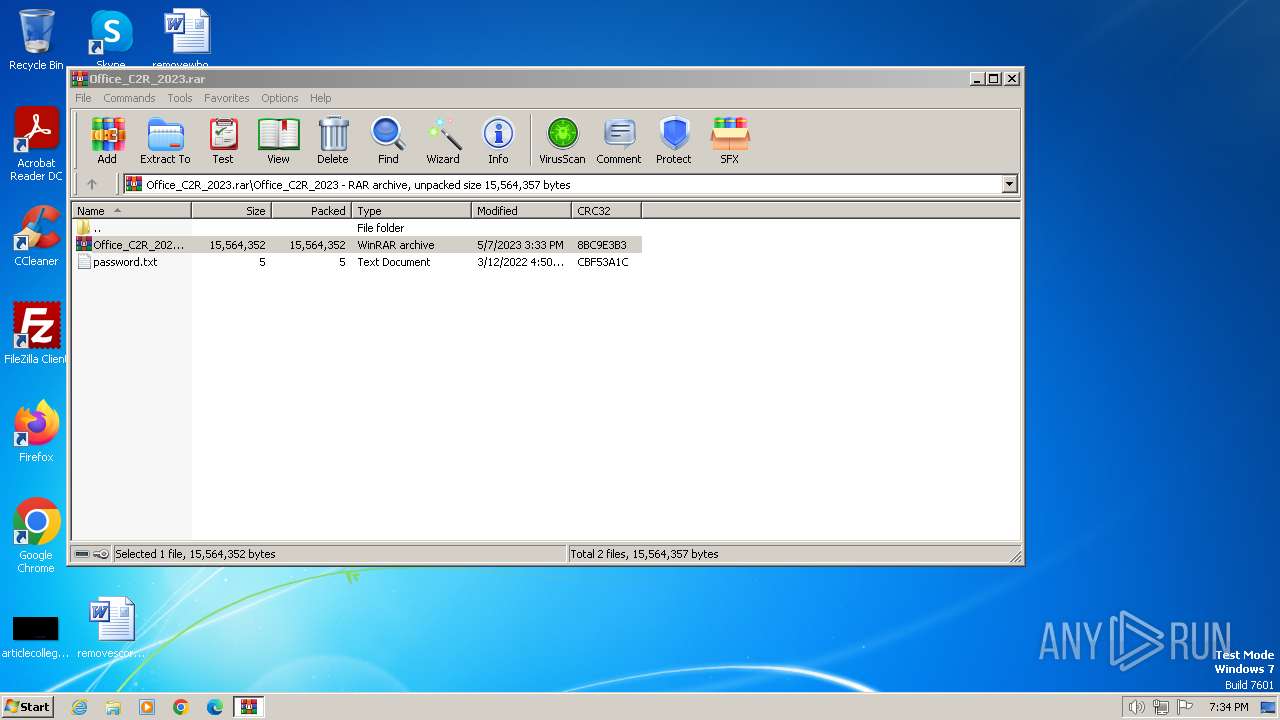
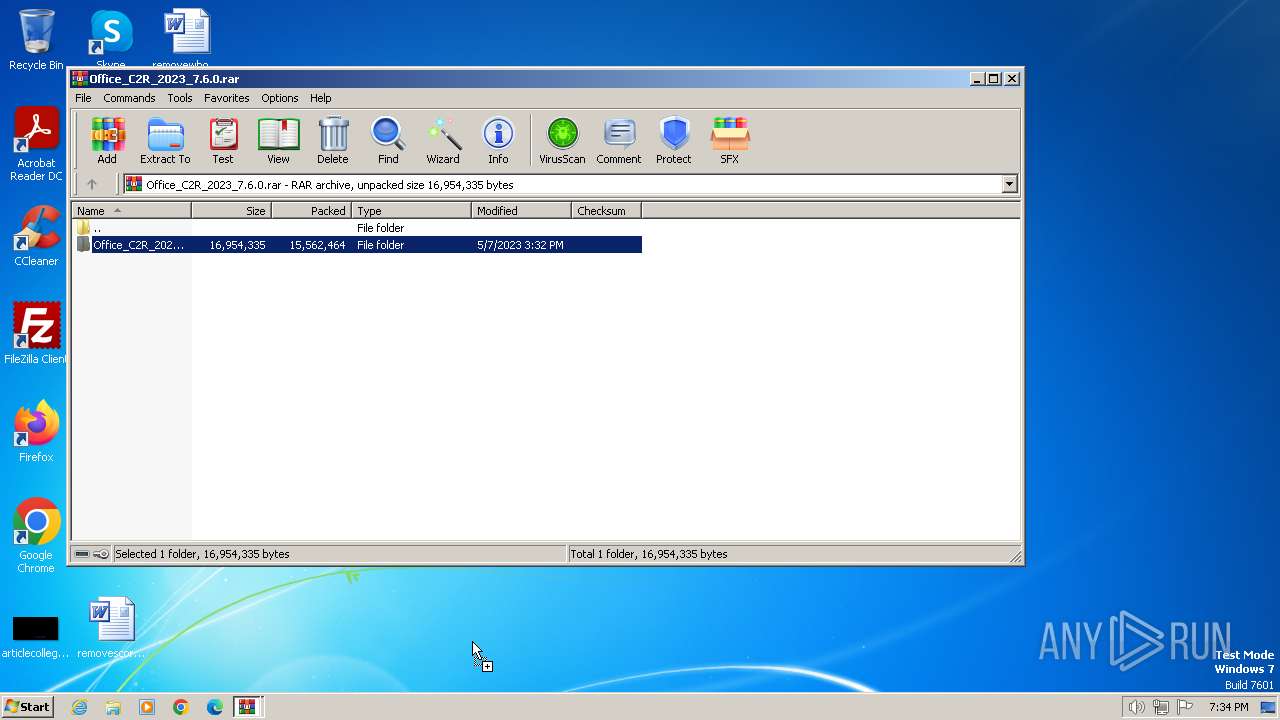
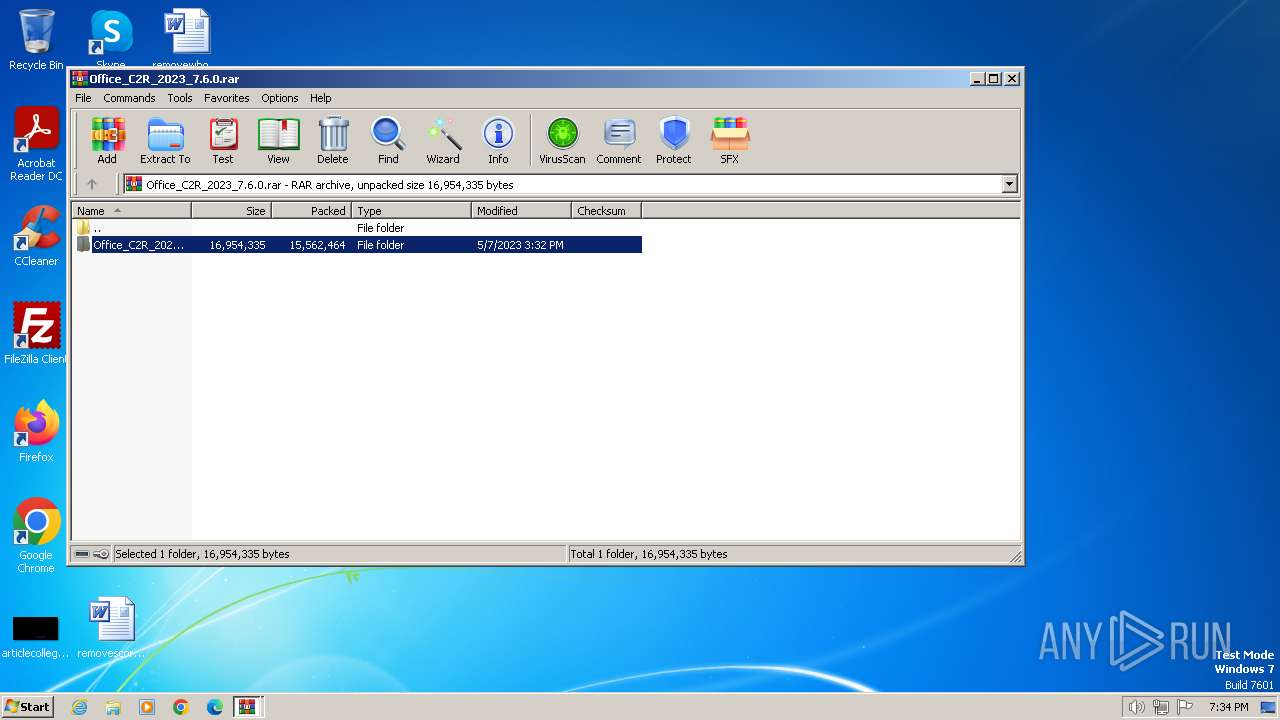
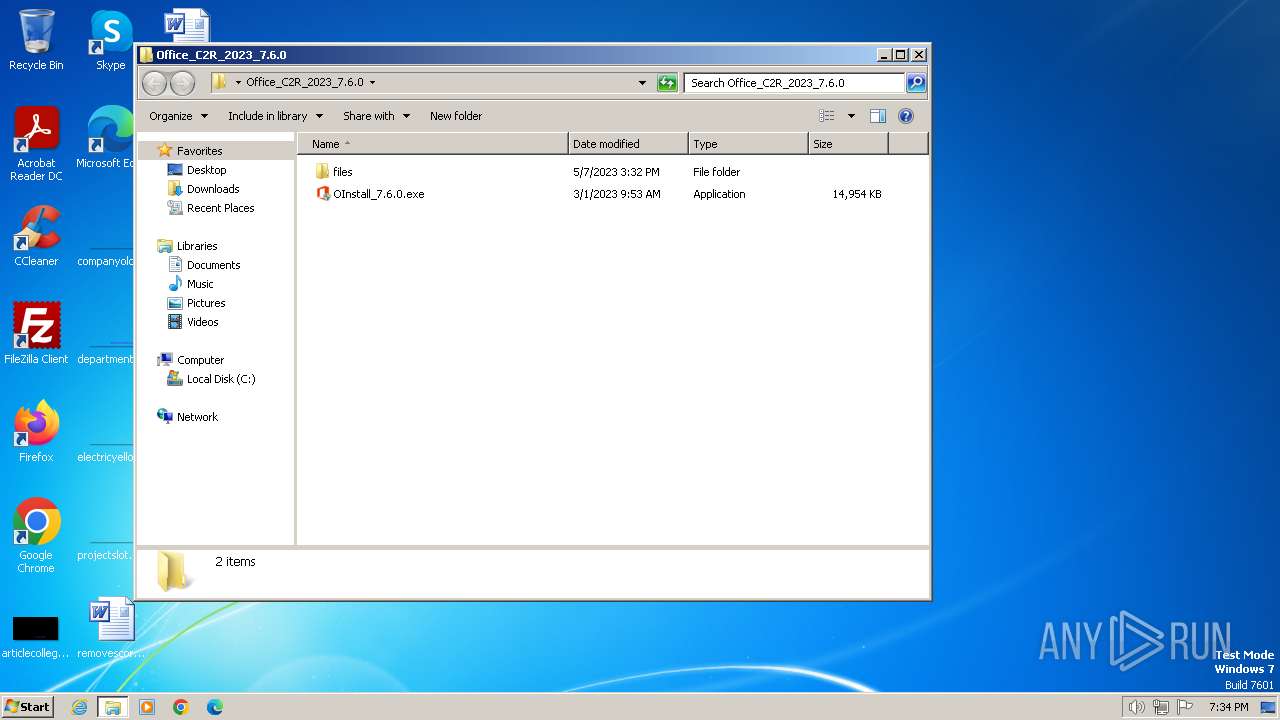
| File name: | Office_C2R_2023.rar |
| Full analysis: | https://app.any.run/tasks/f8c9a233-0f77-42ec-a555-c77ac1bf6ecd |
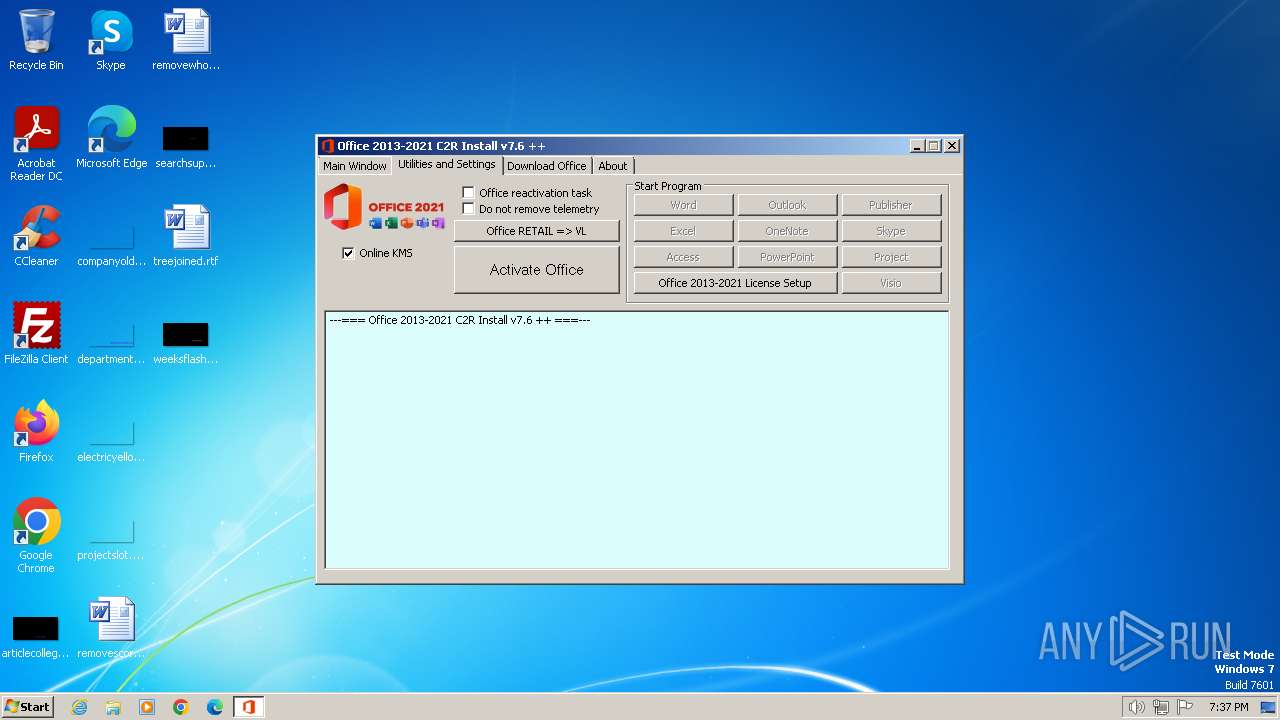
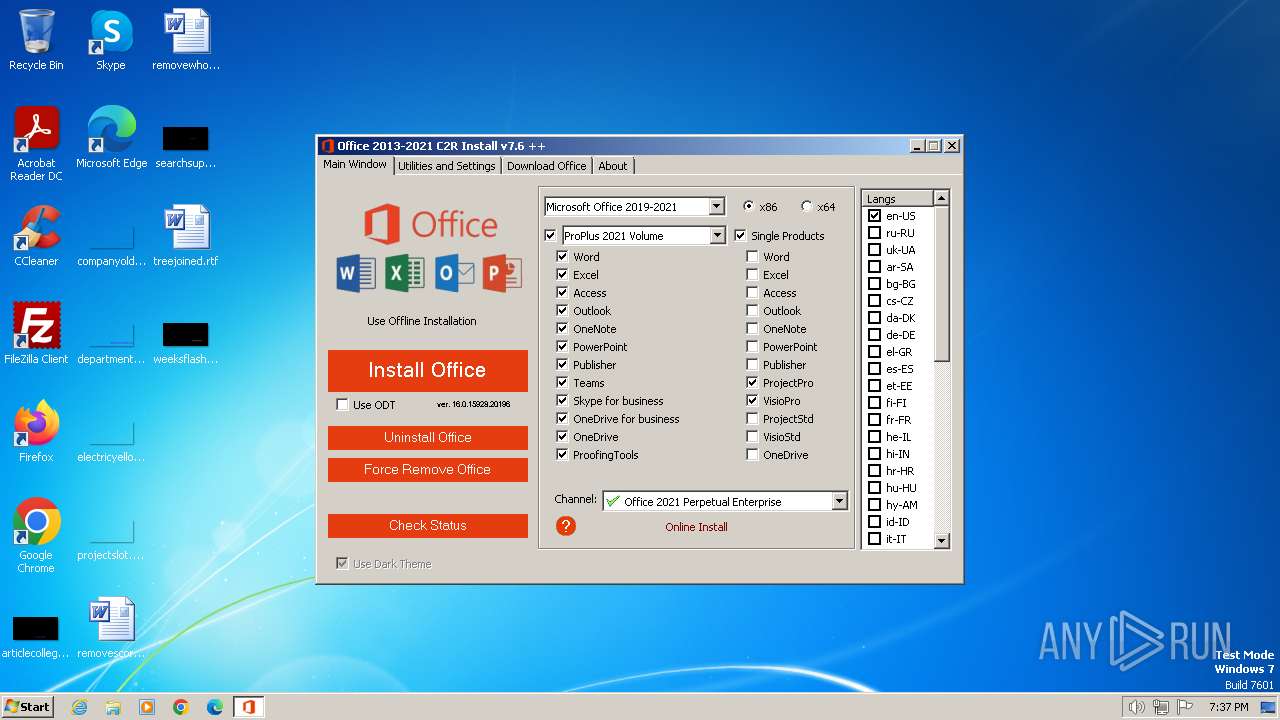
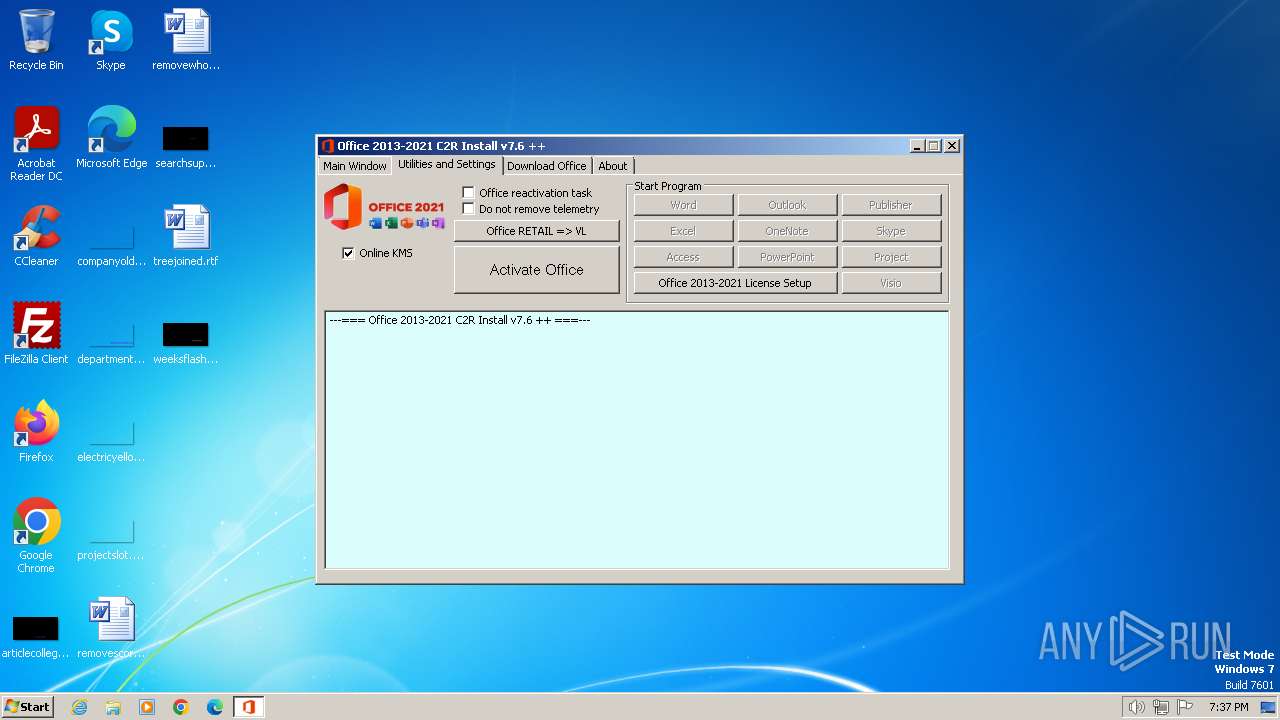
| Verdict: | Malicious activity |
| Analysis date: | January 29, 2024, 19:33:39 |
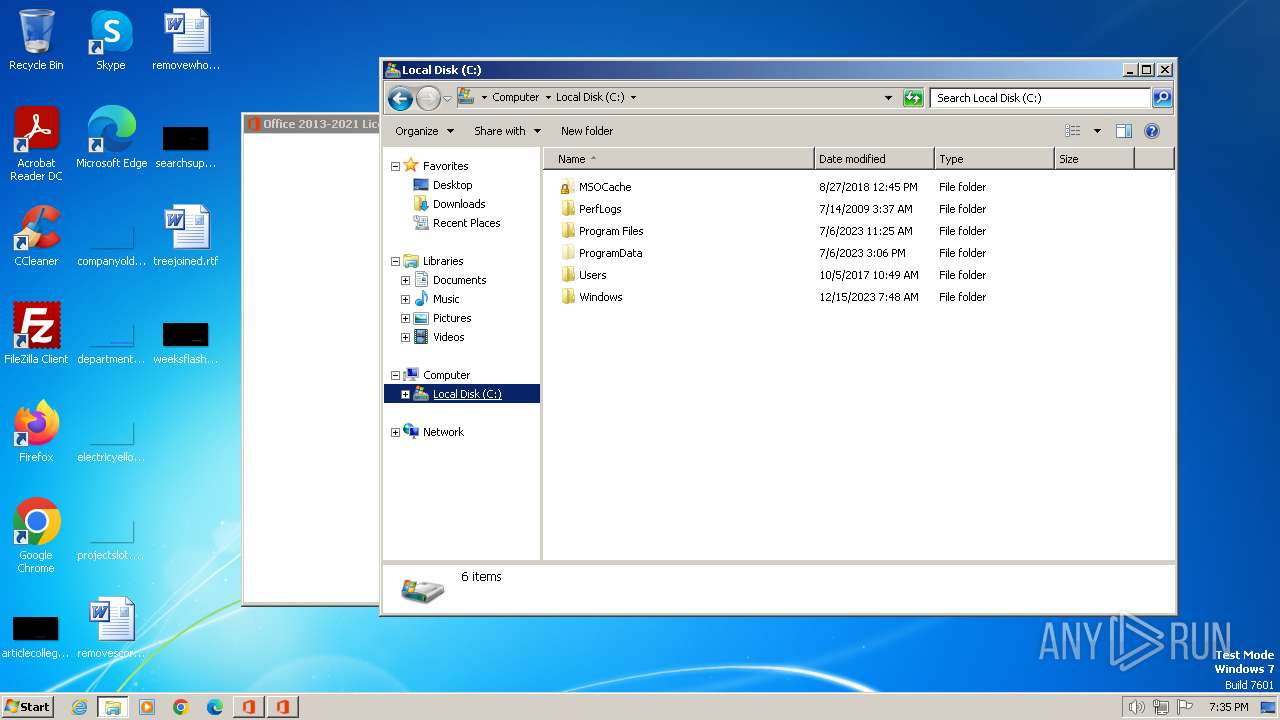
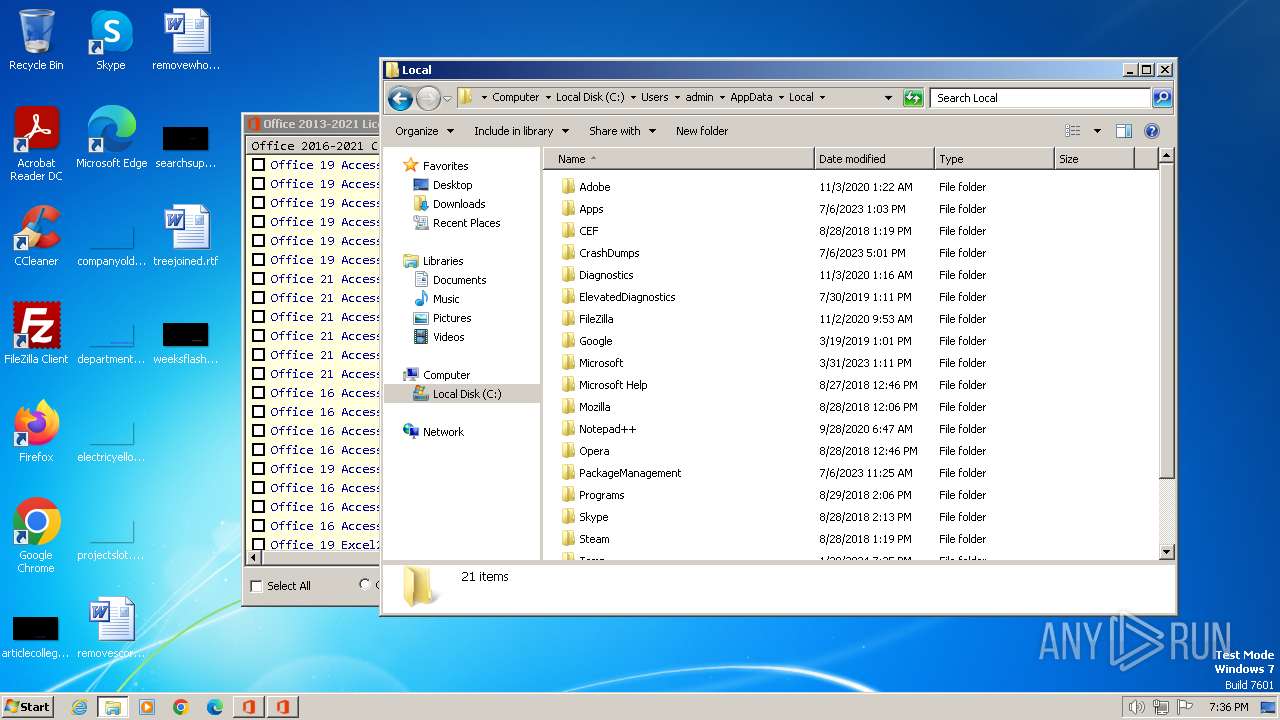
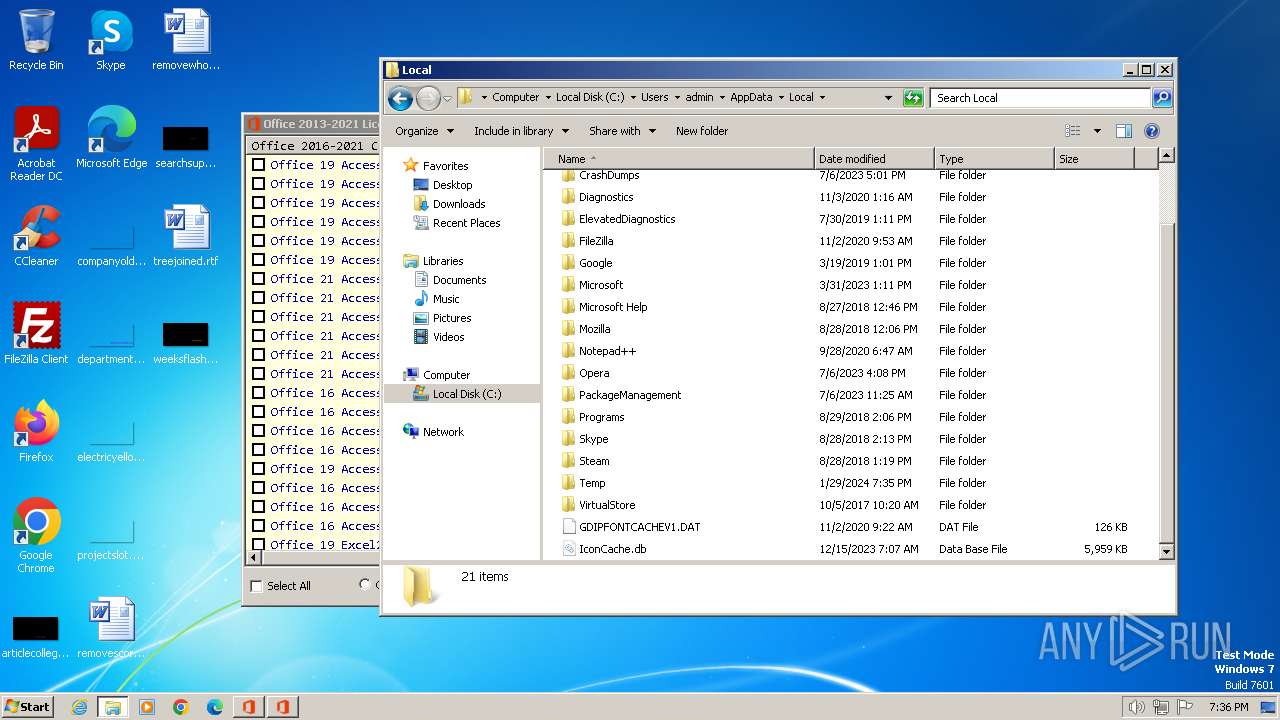
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 9C6EA80DD89D68A4F8FB39D11CAADC64 |
| SHA1: | C380DFE70ADDE4A23601D597FC862C4A2E79D750 |
| SHA256: | 149FC381395801B5AD1C79DECF52AA93B8B81161CE71441446252A41BCF6BEFE |
| SSDEEP: | 196608:vJJQlOmGFWWRXPq2WDTkY9/wPCP4nTIeE:vPQlOmGUudWDwY5wZng |
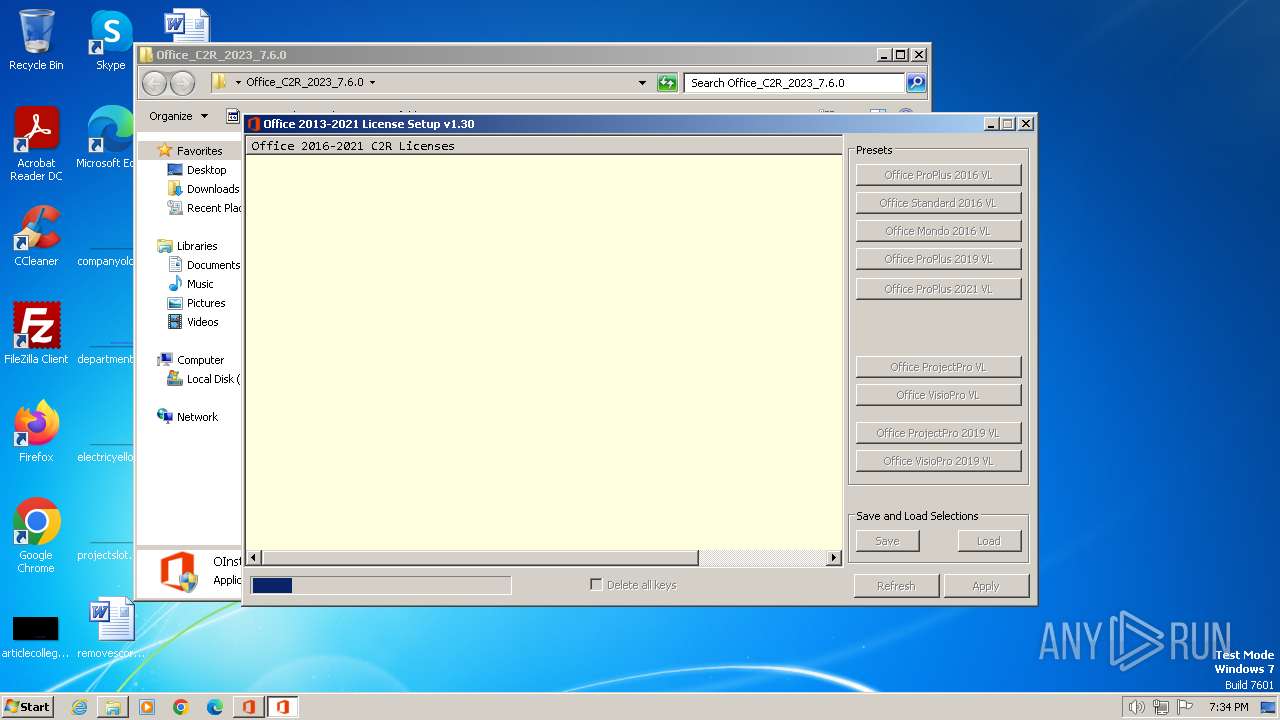
MALICIOUS
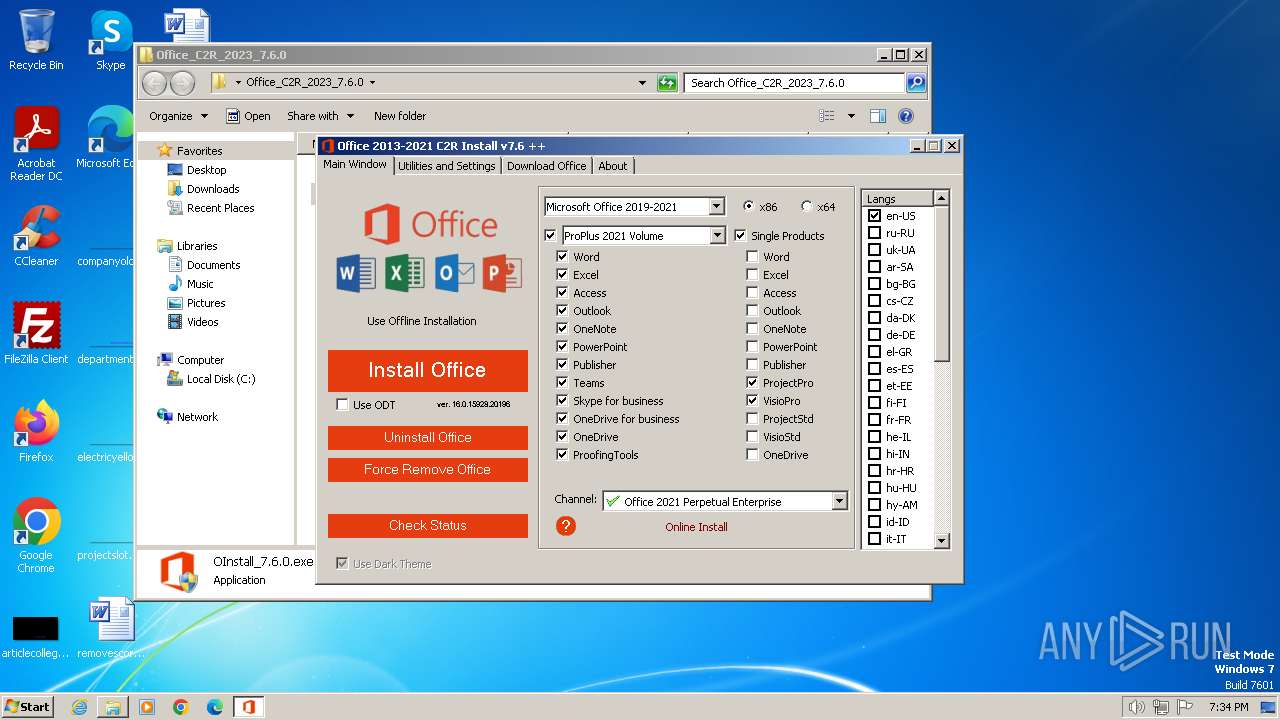
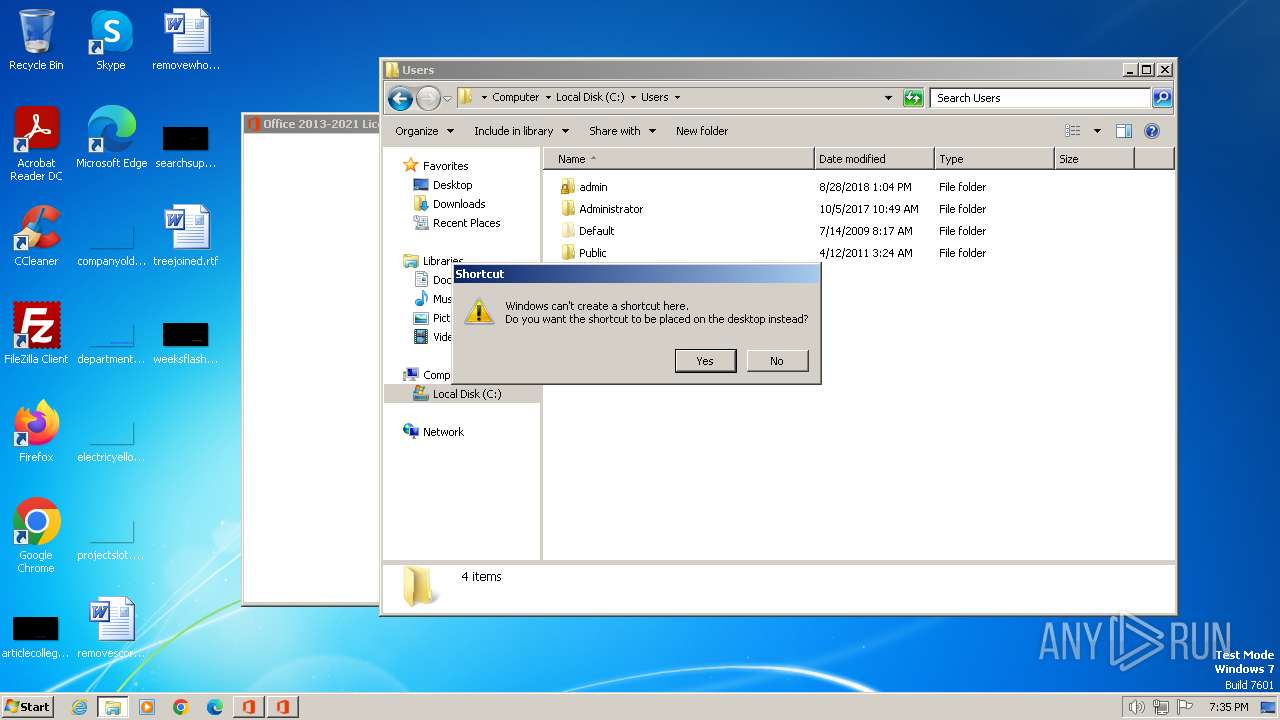
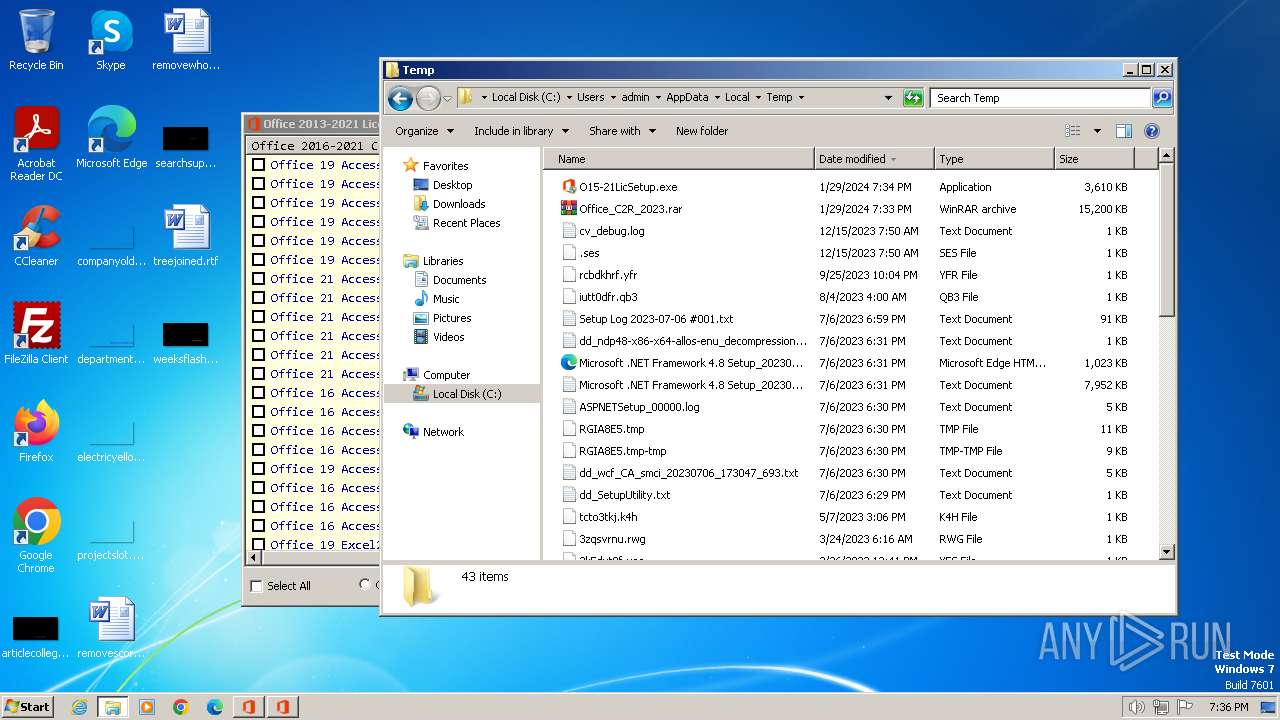
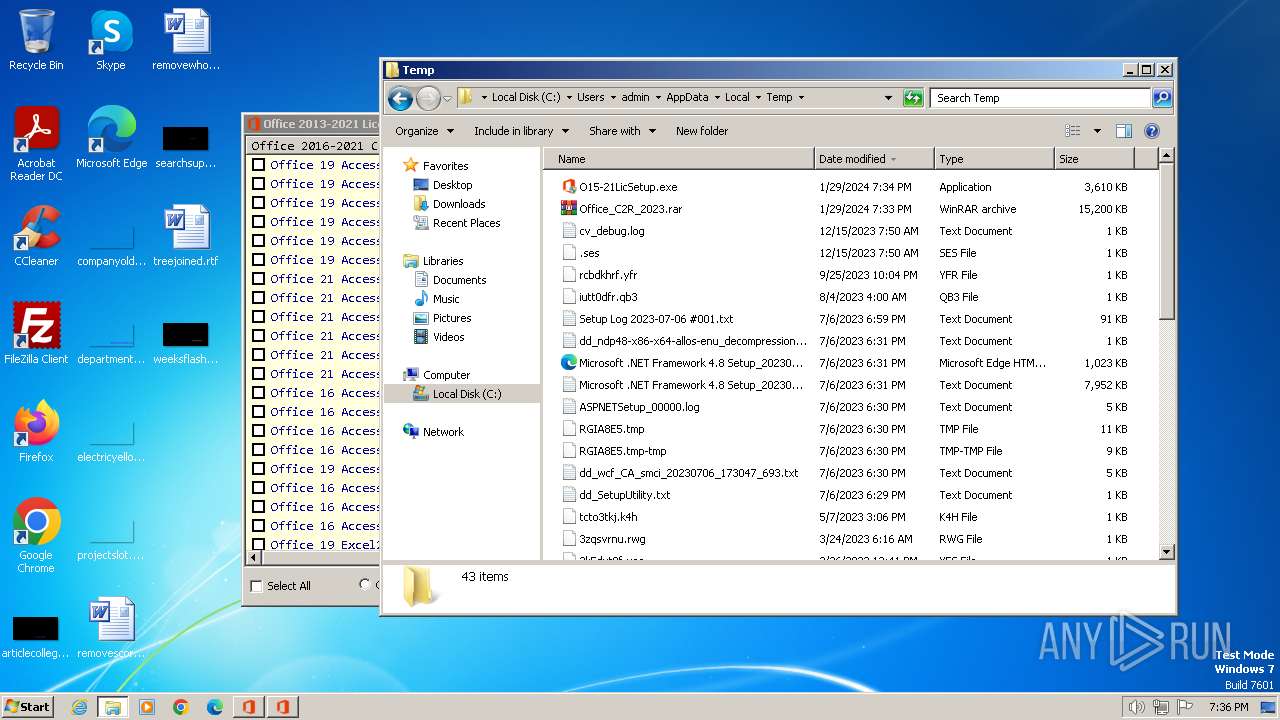
Drops the executable file immediately after the start
- OInstall_7.6.0.exe (PID: 2824)
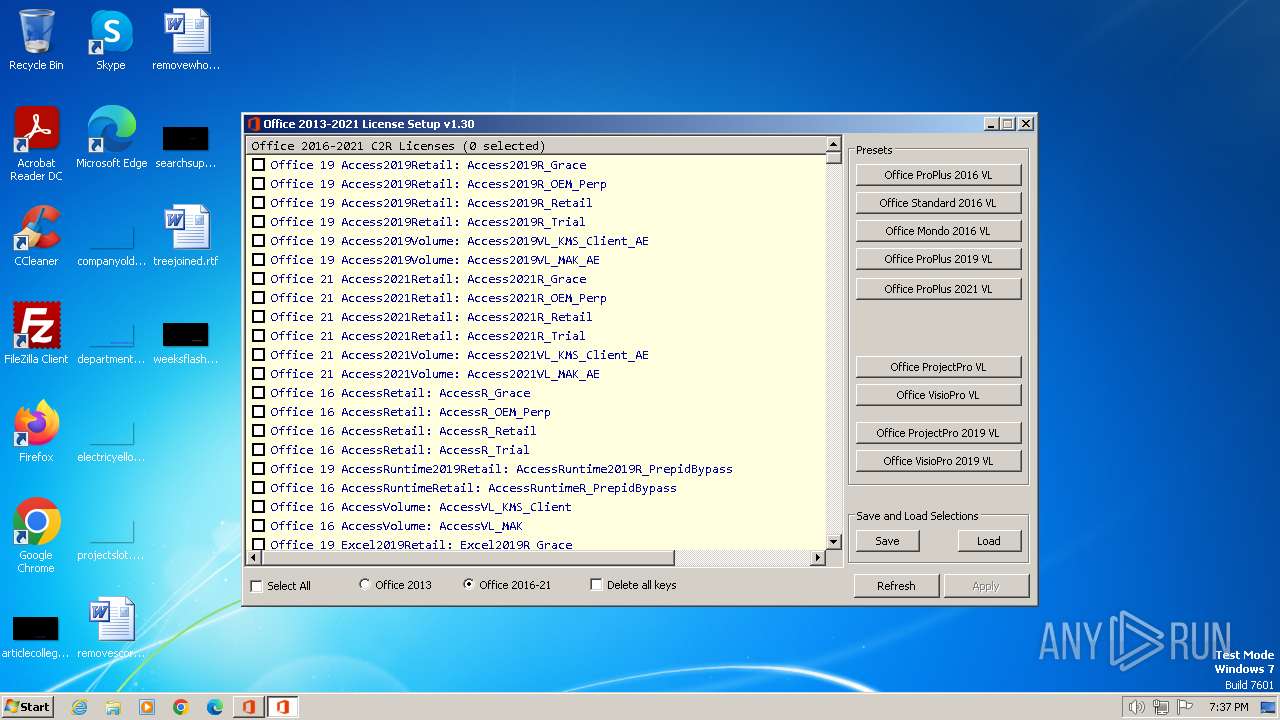
- O15-21LicSetup.exe (PID: 3600)
- files.dat (PID: 3560)
- files.dat (PID: 2932)
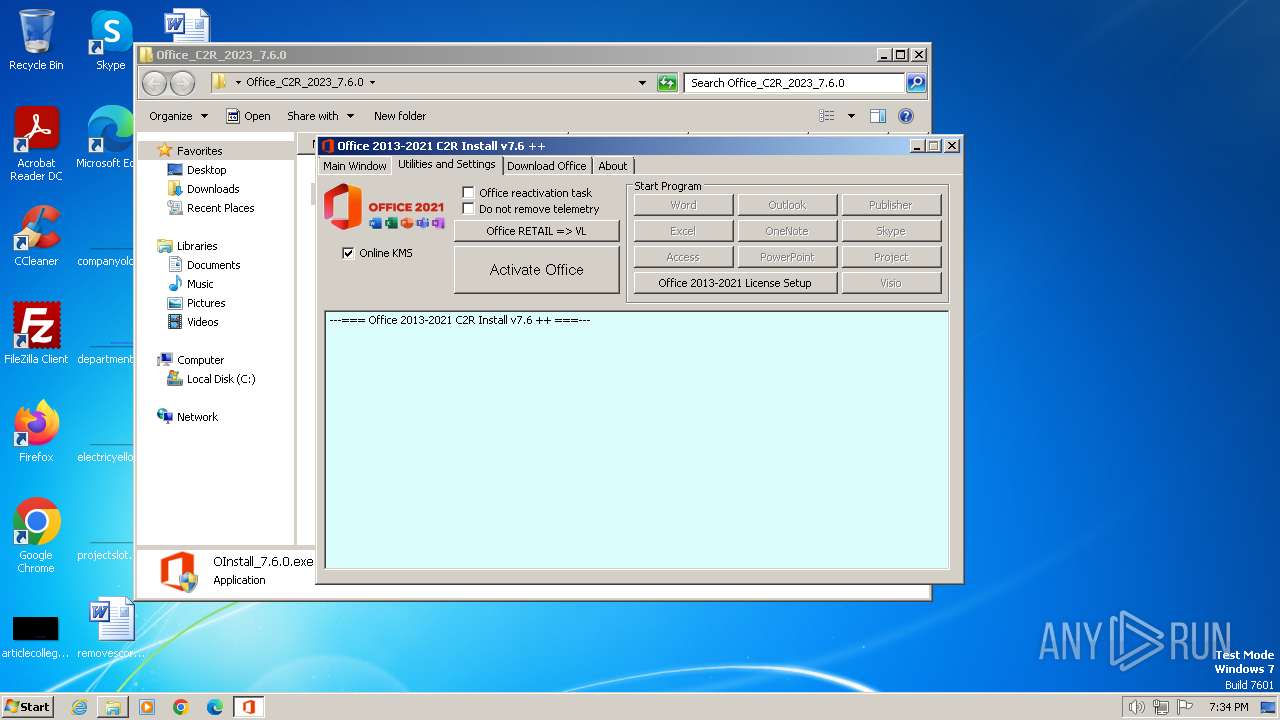
Accesses system services(Win32_Service) via WMI (SCRIPT)
- cscript.exe (PID: 3844)
- cscript.exe (PID: 2636)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 1632)
- OInstall_7.6.0.exe (PID: 2824)
- files.dat (PID: 3560)
- files.dat (PID: 2932)
Application launched itself
- WinRAR.exe (PID: 268)
Uses REG/REGEDIT.EXE to modify registry
- OInstall_7.6.0.exe (PID: 2824)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 3040)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 3316)
Executable content was dropped or overwritten
- OInstall_7.6.0.exe (PID: 2824)
- O15-21LicSetup.exe (PID: 3600)
- files.dat (PID: 3560)
- files.dat (PID: 2932)
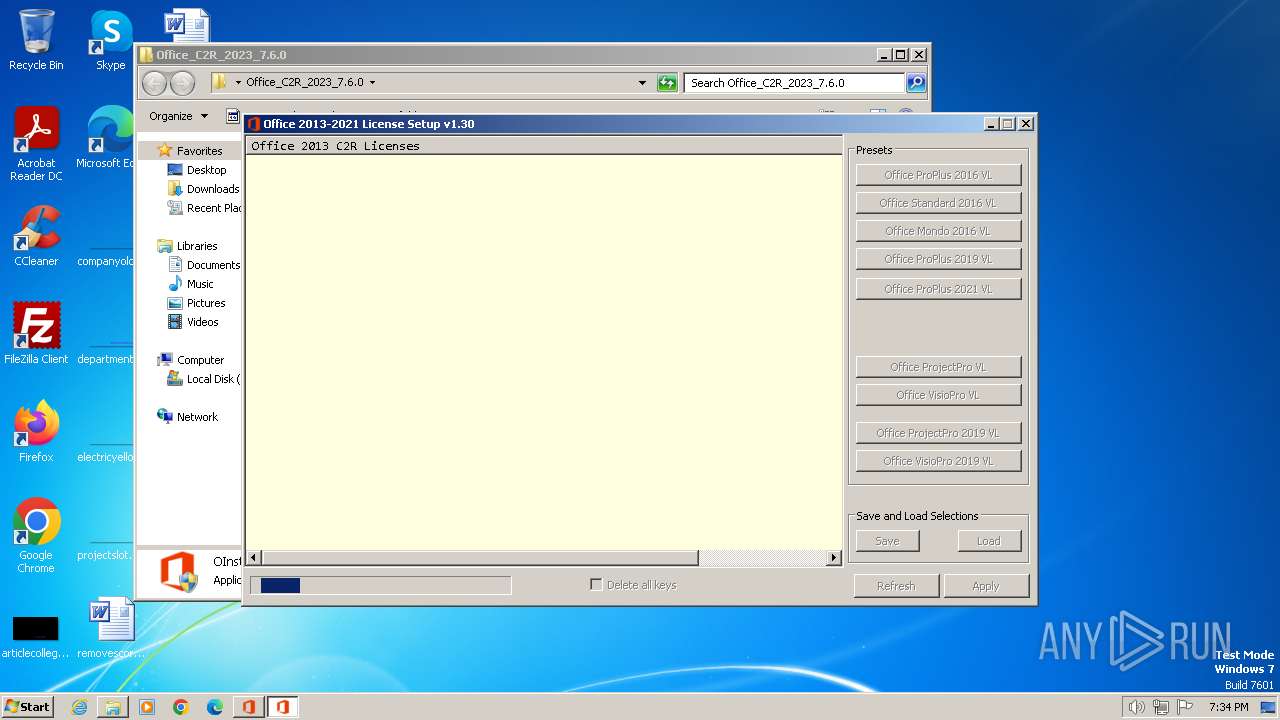
Drops 7-zip archiver for unpacking
- O15-21LicSetup.exe (PID: 3600)
Starts CMD.EXE for commands execution
- O15-21LicSetup.exe (PID: 3600)
- OInstall_7.6.0.exe (PID: 2824)
Starts application with an unusual extension
- cmd.exe (PID: 3588)
- cmd.exe (PID: 3904)
Reads settings of System Certificates
- cscript.exe (PID: 3844)
- cscript.exe (PID: 2636)
The process drops C-runtime libraries
- files.dat (PID: 3560)
- files.dat (PID: 2932)
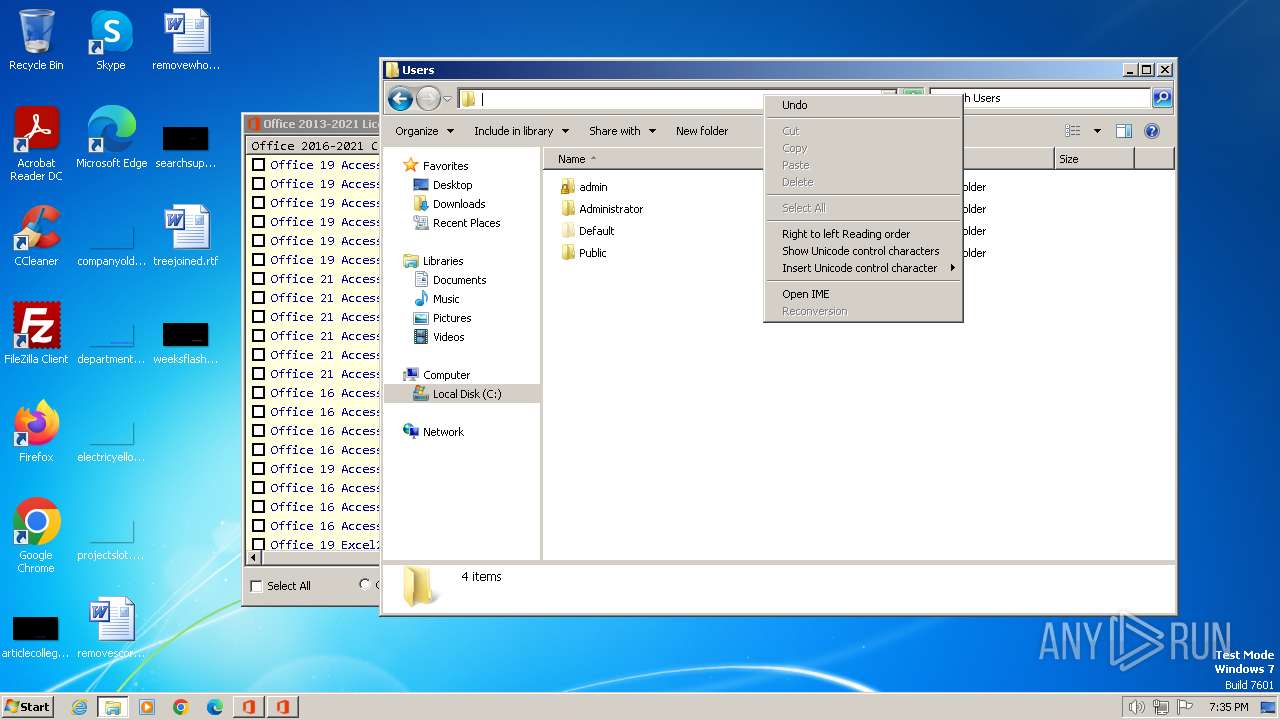
The process executes VB scripts
- cmd.exe (PID: 3884)
- cmd.exe (PID: 2332)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 3844)
- cscript.exe (PID: 2636)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 3844)
- cscript.exe (PID: 2636)
Gets a collection of all available drive names (SCRIPT)
- cscript.exe (PID: 3844)
- cscript.exe (PID: 2636)
Gets the drive type (SCRIPT)
- cscript.exe (PID: 3844)
- cscript.exe (PID: 2636)
Checks whether a specific file exists (SCRIPT)
- cscript.exe (PID: 3844)
- cscript.exe (PID: 2636)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- cscript.exe (PID: 3844)
- cscript.exe (PID: 2636)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- cscript.exe (PID: 3844)
- cscript.exe (PID: 2636)
Executes WMI query (SCRIPT)
- cscript.exe (PID: 3844)
- cscript.exe (PID: 2636)
The executable file from the user directory is run by the CMD process
- files.dat (PID: 3560)
- files.dat (PID: 2932)
- test.exe (PID: 3248)
Accesses computer name via WMI (SCRIPT)
- cscript.exe (PID: 3844)
- cscript.exe (PID: 2636)
Reads the Internet Settings
- cscript.exe (PID: 2636)
Connects to unusual port
- test.exe (PID: 3248)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1632)
Checks supported languages
- OInstall_7.6.0.exe (PID: 2824)
- O15-21LicSetup.exe (PID: 3600)
- files.dat (PID: 3560)
- files.dat (PID: 2932)
- test.exe (PID: 3248)
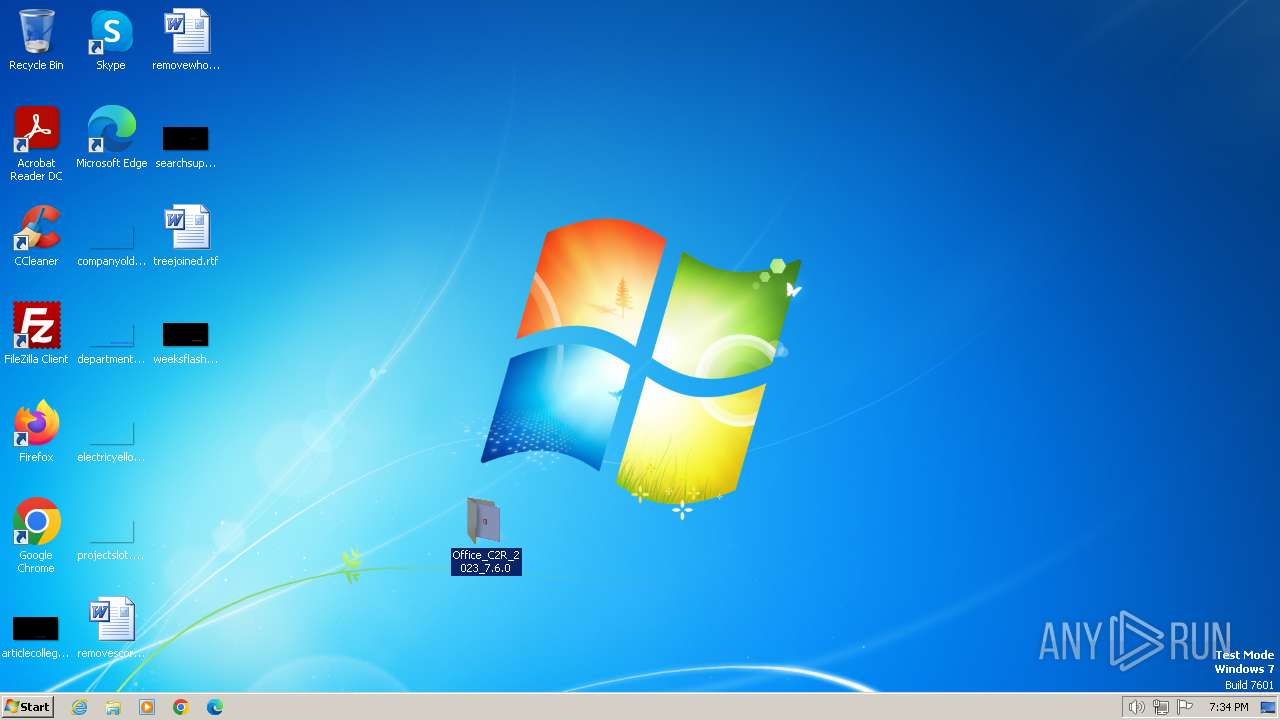
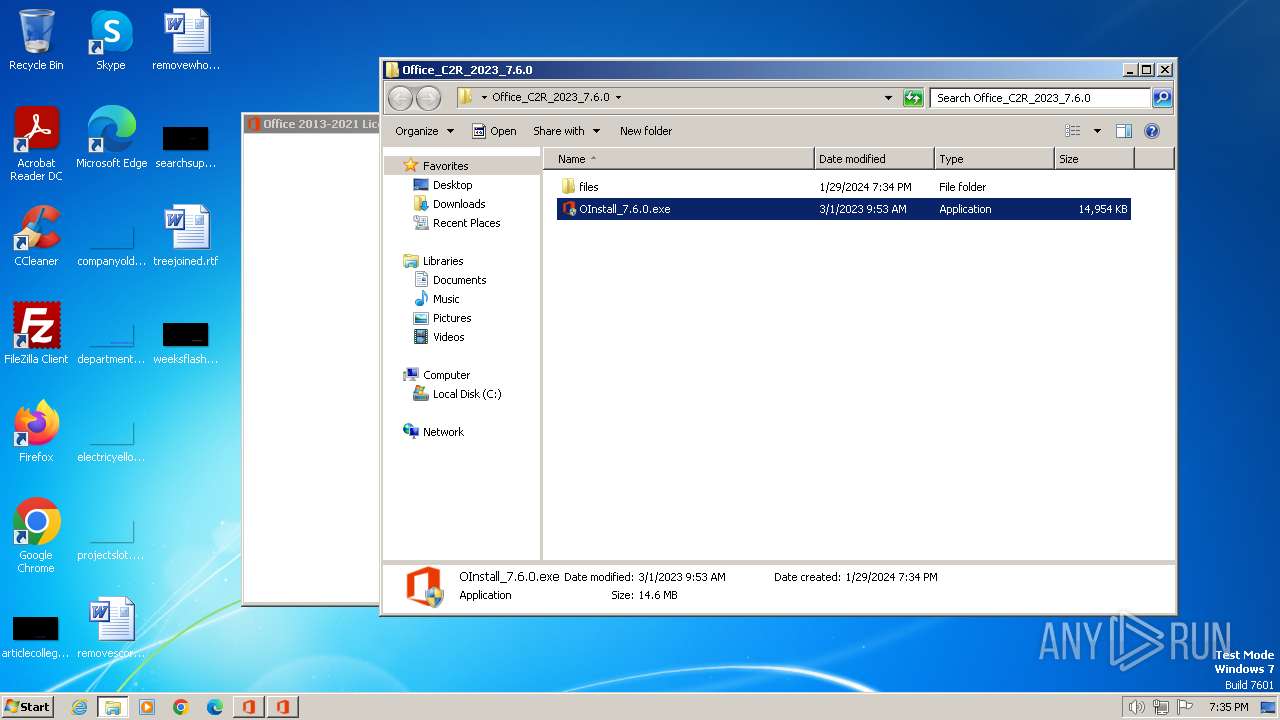
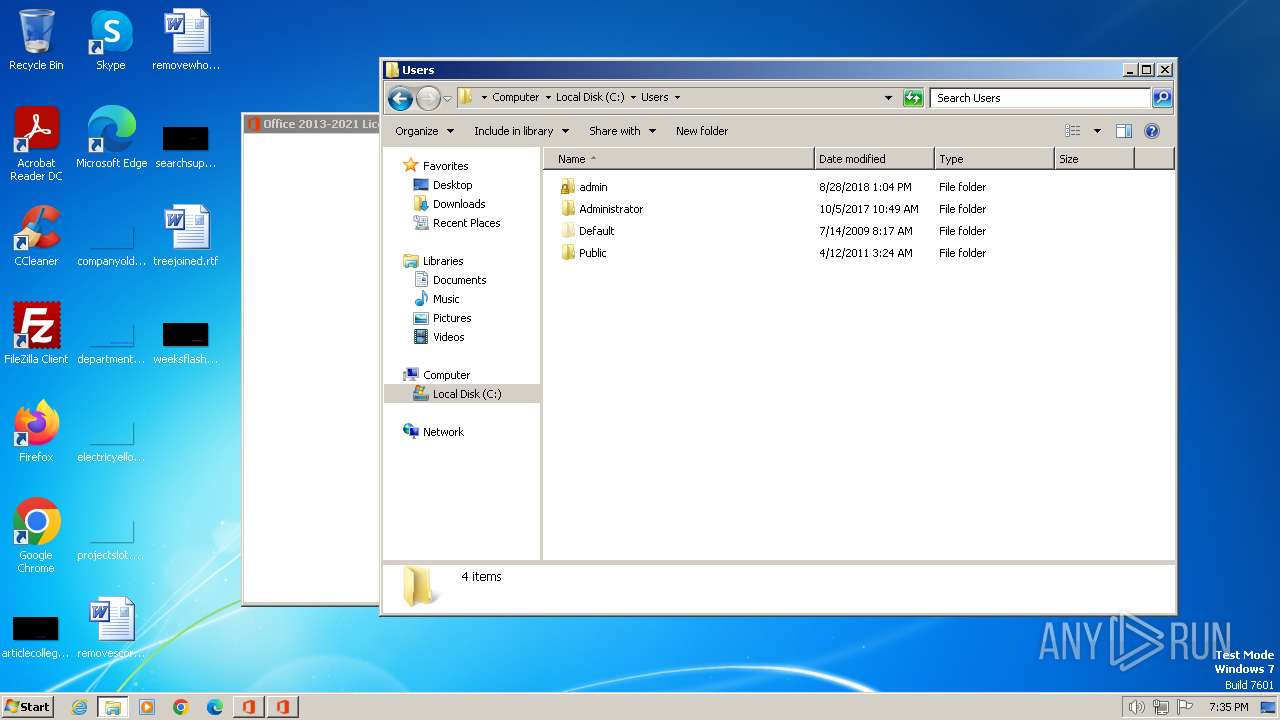
Manual execution by a user
- OInstall_7.6.0.exe (PID: 2868)
- OInstall_7.6.0.exe (PID: 2824)
Reads Environment values
- OInstall_7.6.0.exe (PID: 2824)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1632)
Reads the computer name
- OInstall_7.6.0.exe (PID: 2824)
- test.exe (PID: 3248)
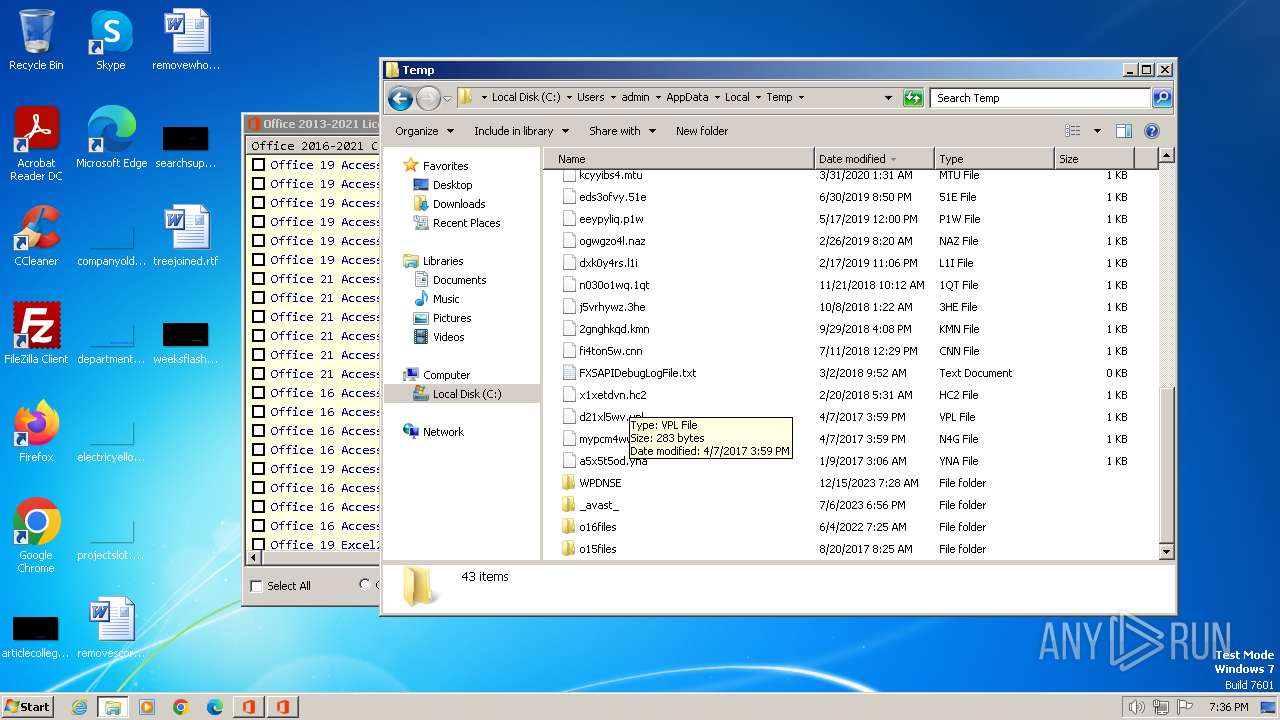
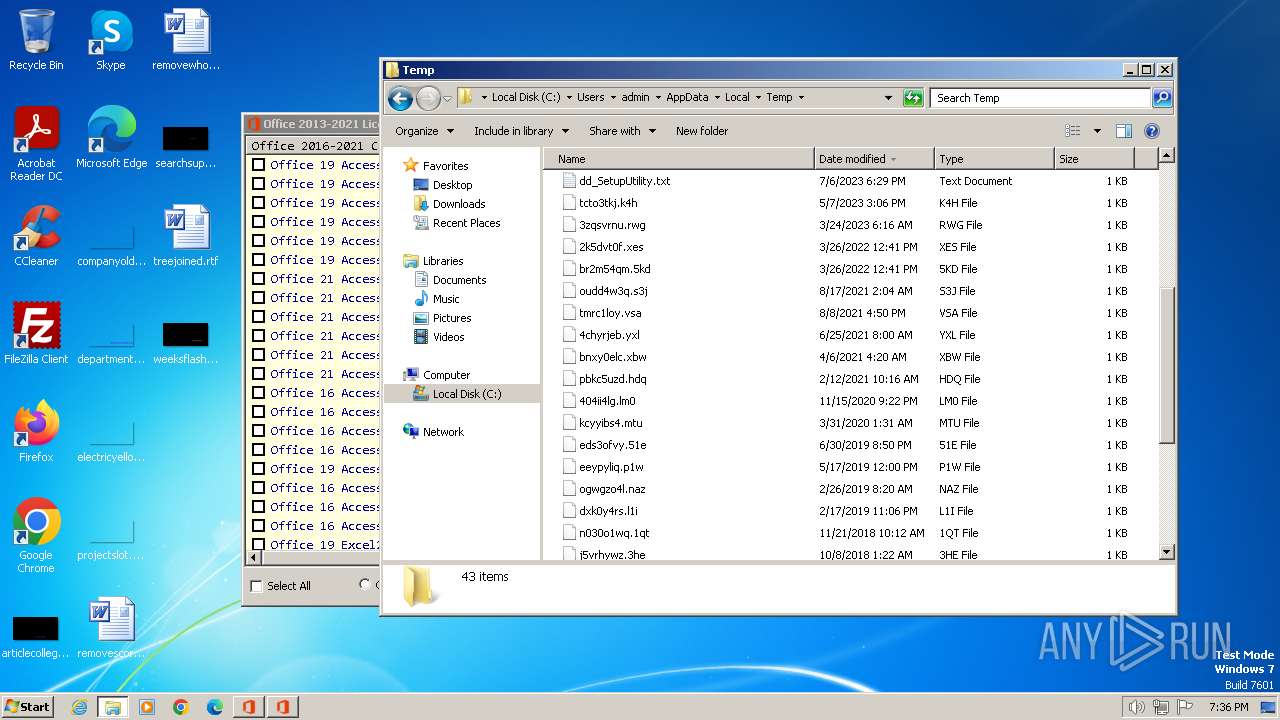
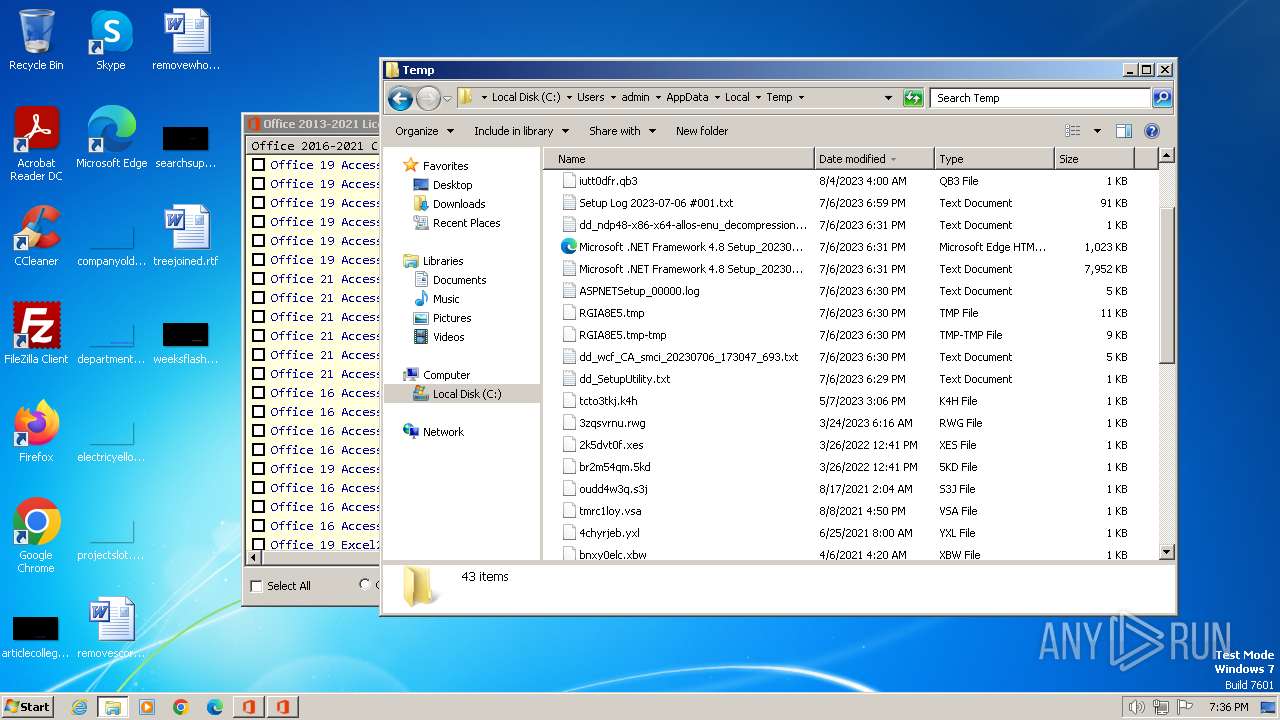
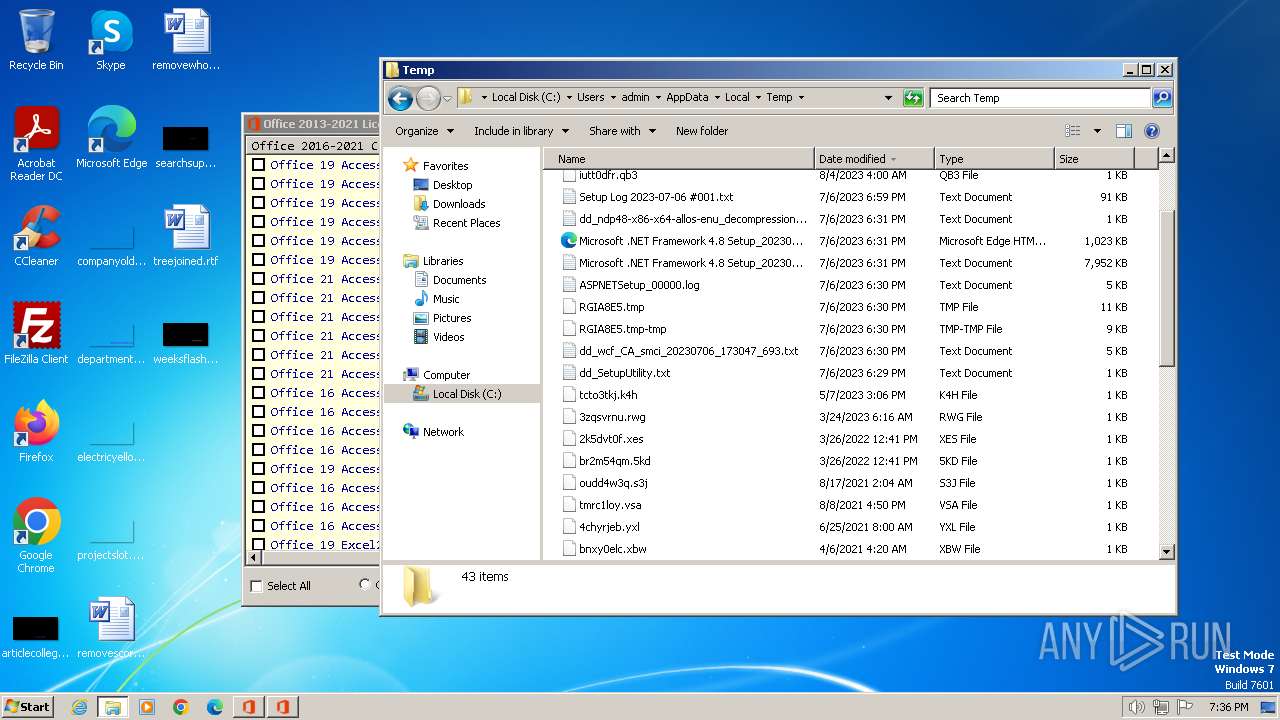
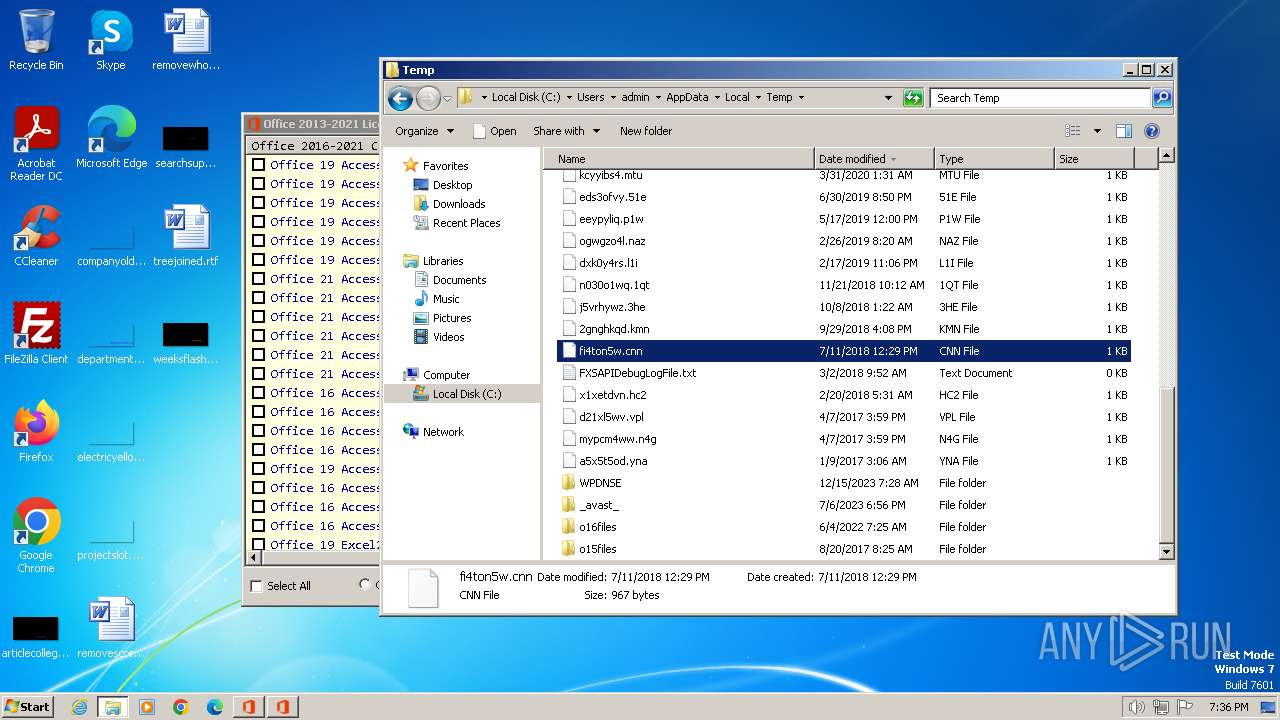
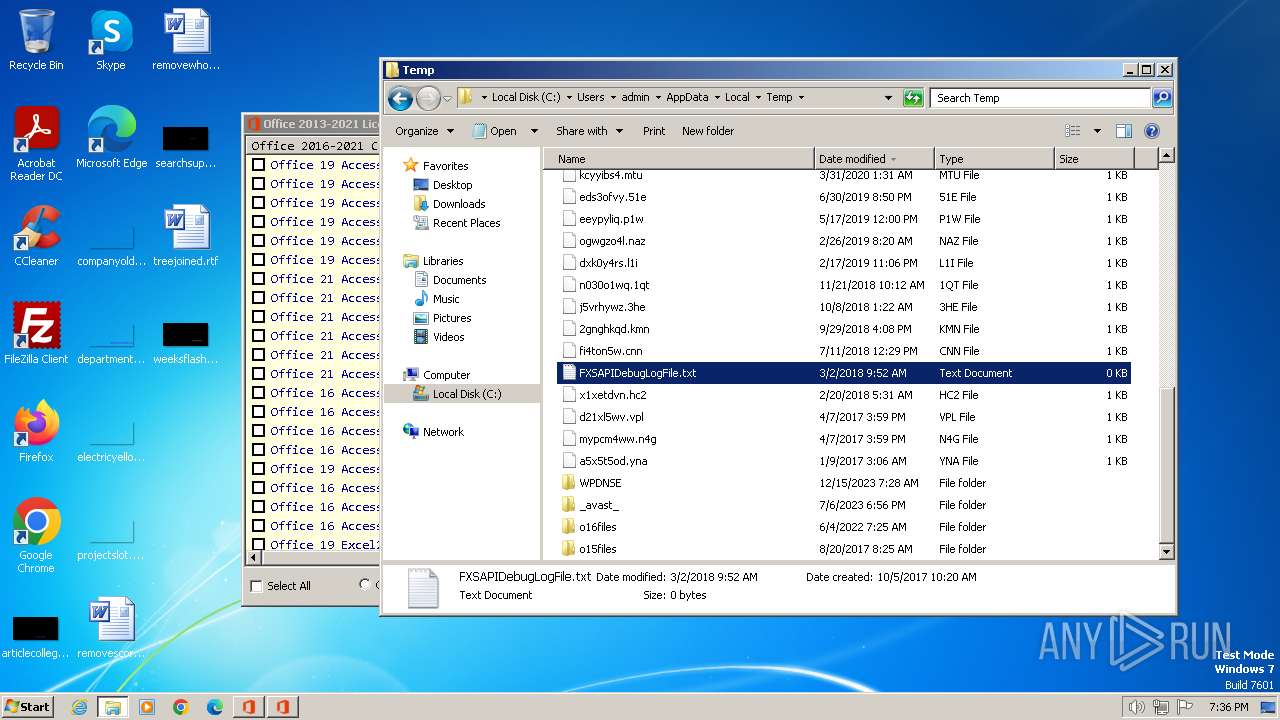
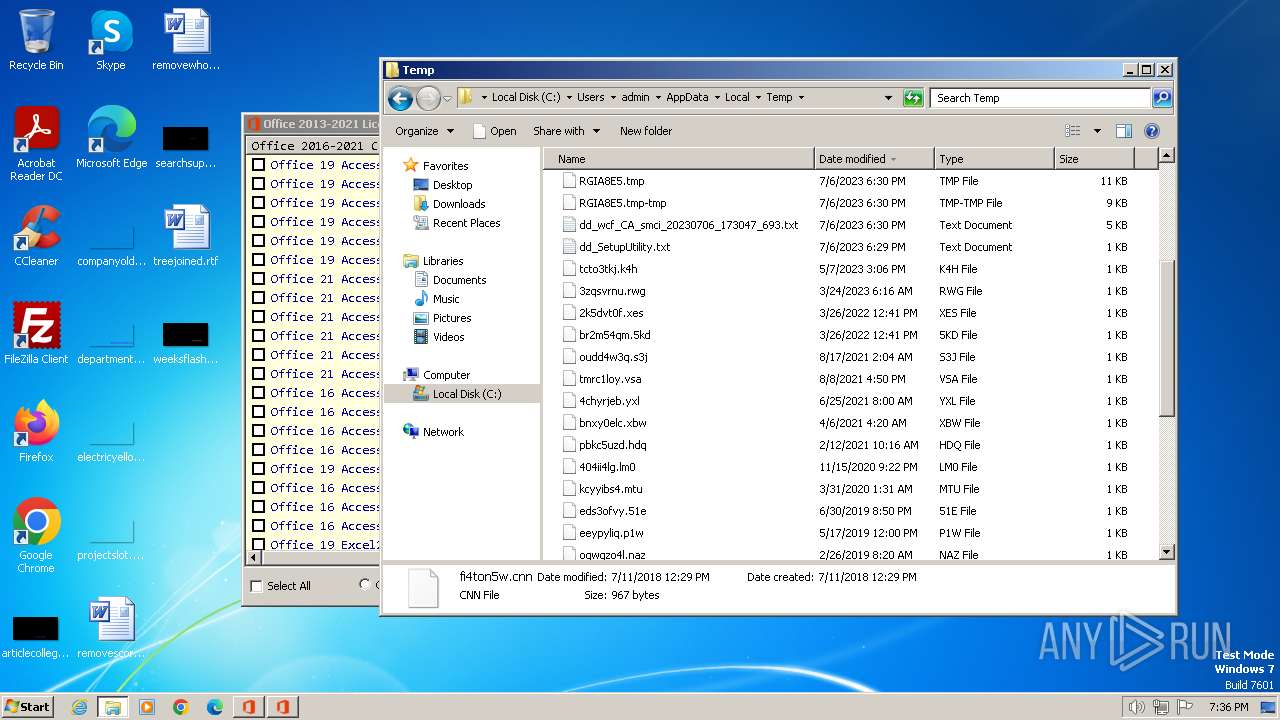
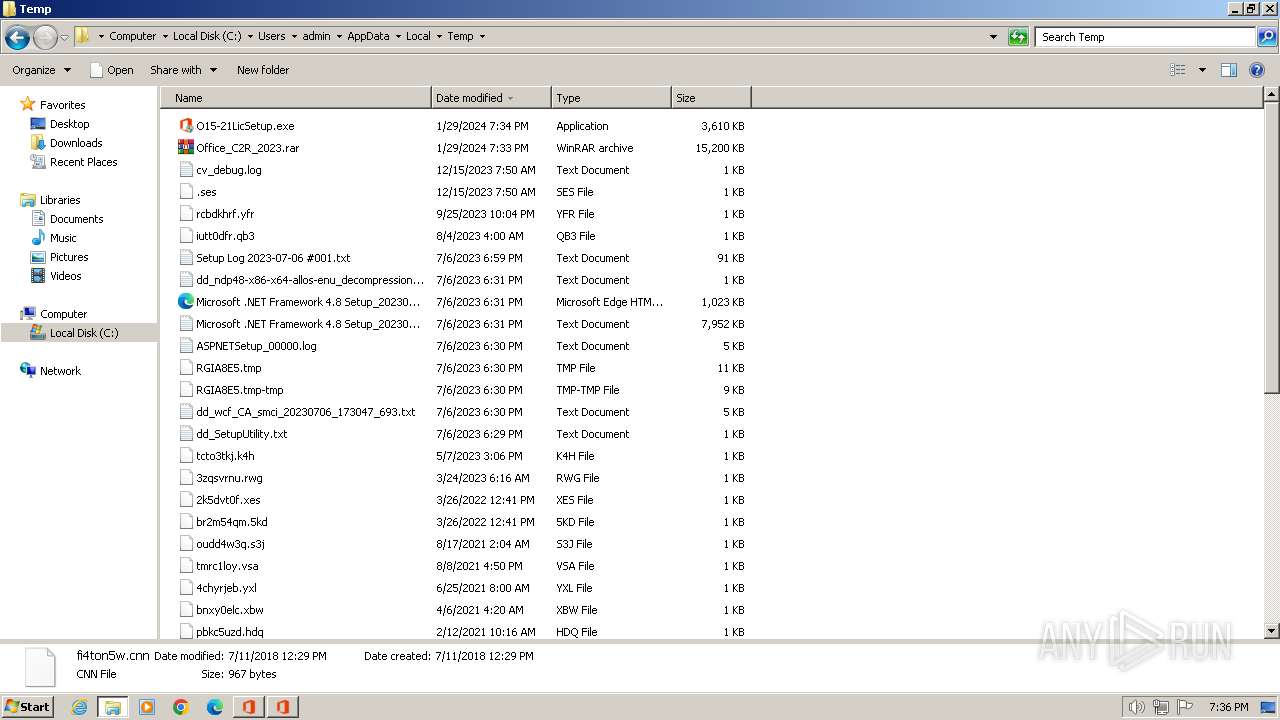
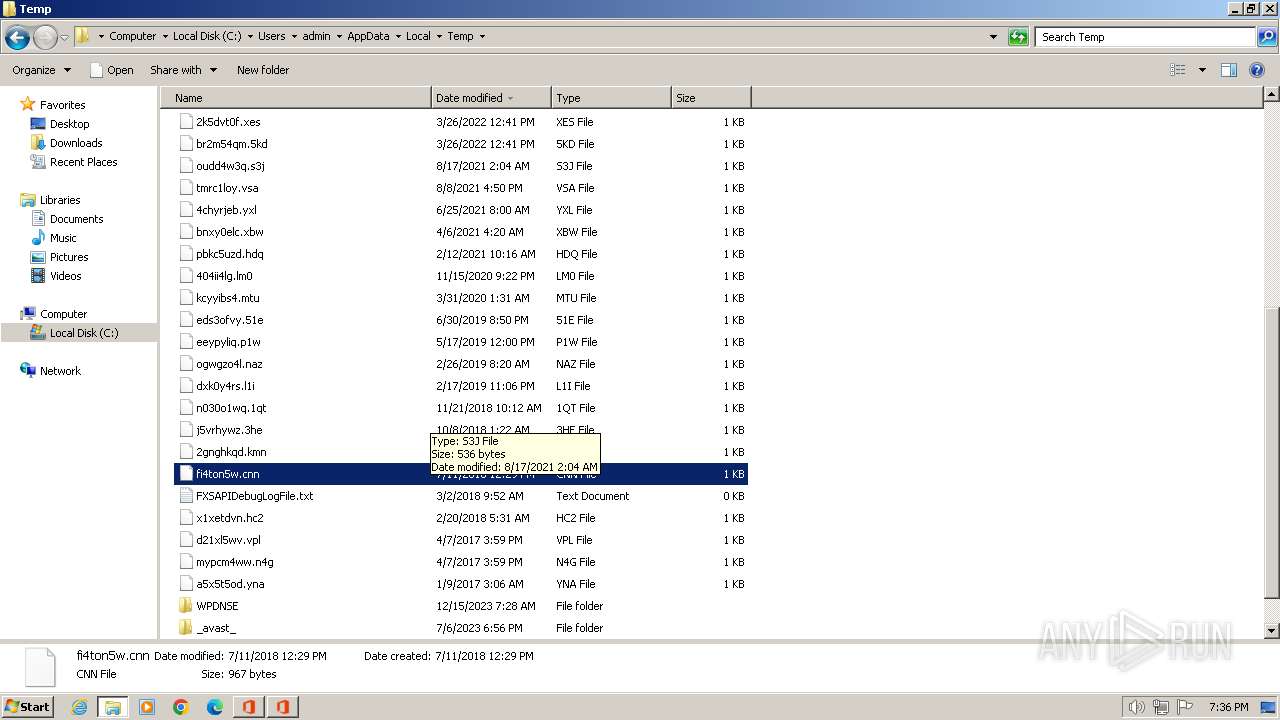
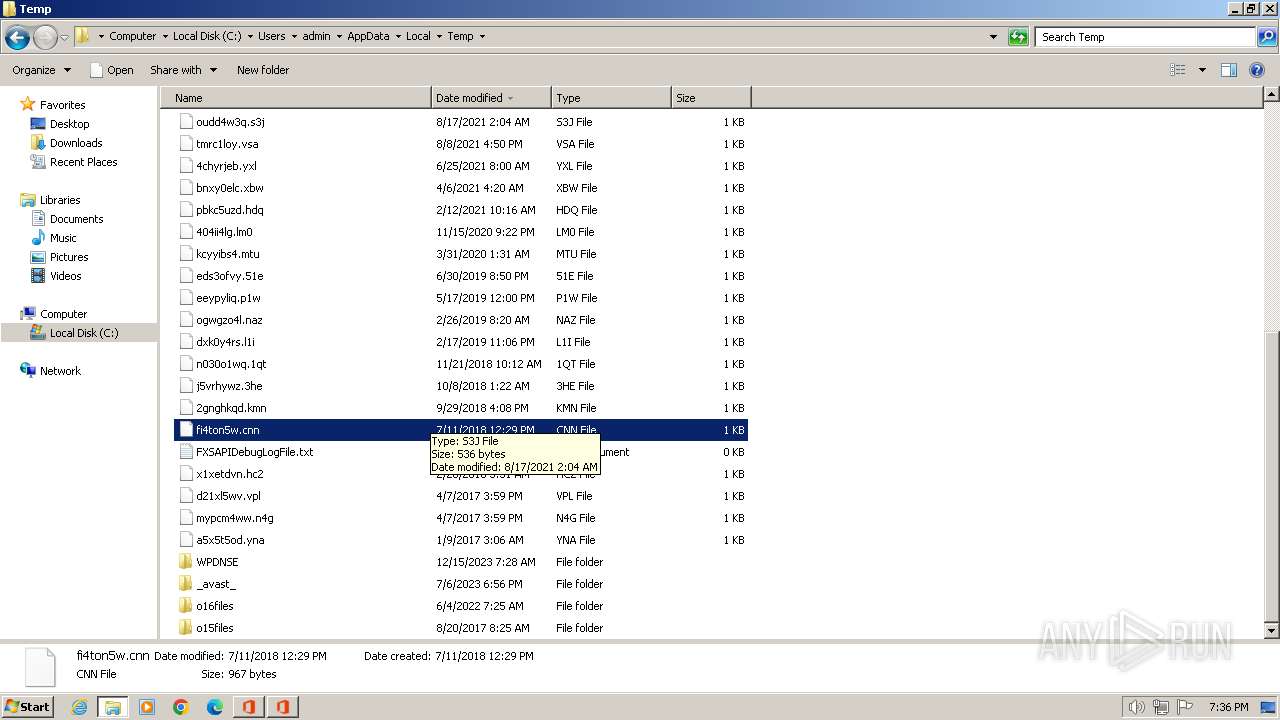
Create files in a temporary directory
- OInstall_7.6.0.exe (PID: 2824)
- O15-21LicSetup.exe (PID: 3600)
- files.dat (PID: 3560)
- files.dat (PID: 2932)
Reads security settings of Internet Explorer
- cscript.exe (PID: 3844)
- cscript.exe (PID: 2636)
Reads the machine GUID from the registry
- test.exe (PID: 3248)
Reads Microsoft Office registry keys
- reg.exe (PID: 3380)
- reg.exe (PID: 1604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
97
Monitored processes
34
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 268 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Office_C2R_2023.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 908 | "C:\Windows\System32\reg.exe" add "HKLM\SOFTWARE\Microsoft\Windows Script Host\Settings" /v Enabled /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | OInstall_7.6.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | "C:\Windows\System32\cmd.exe" /c REG QUERY HKLM\Software\WOW6432Node\Microsoft\Office /s /v Path | C:\Windows\System32\cmd.exe | — | OInstall_7.6.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1604 | REG QUERY HKLM\Software\Microsoft\Office /s /v Path /reg:64 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1632 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa268.32882\Office_C2R_2023_7.6.0.rar | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1652 | REG QUERY HKLM\Software\WOW6432Node\Microsoft\Office /s /v Path | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2088 | "C:\Windows\System32\cmd.exe" /c REG QUERY HKLM\Software\Microsoft\Office /s /v Path /reg:64 | C:\Windows\System32\cmd.exe | — | OInstall_7.6.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
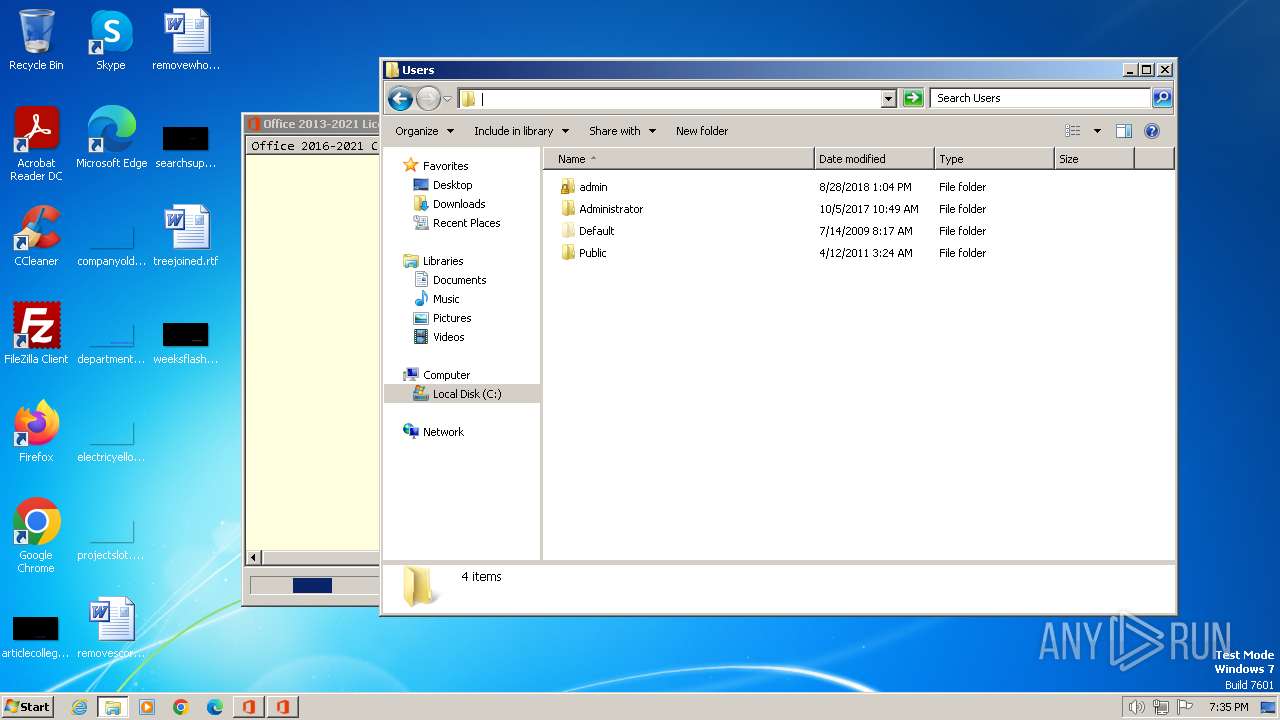
| 2204 | "C:\Windows\System32\cmd.exe" /D /c C:\Users\admin\AppData\Local\Temp\test.exe kms.loli.beer:1688 -l Windows -6 | C:\Windows\System32\cmd.exe | — | OInstall_7.6.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2228 | "C:\Windows\System32\cmd.exe" /D /c cscript.exe "" //NoLogo /act | C:\Windows\System32\cmd.exe | — | OInstall_7.6.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2332 | "C:\Windows\System32\cmd.exe" /c cscript.exe ospp.vbs /dstatusall | C:\Windows\System32\cmd.exe | — | O15-21LicSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
9 841
Read events
9 753
Write events
88
Delete events
0
Modification events
| (PID) Process: | (268) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (268) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
18
Suspicious files
0
Text files
2 310
Unknown types
0
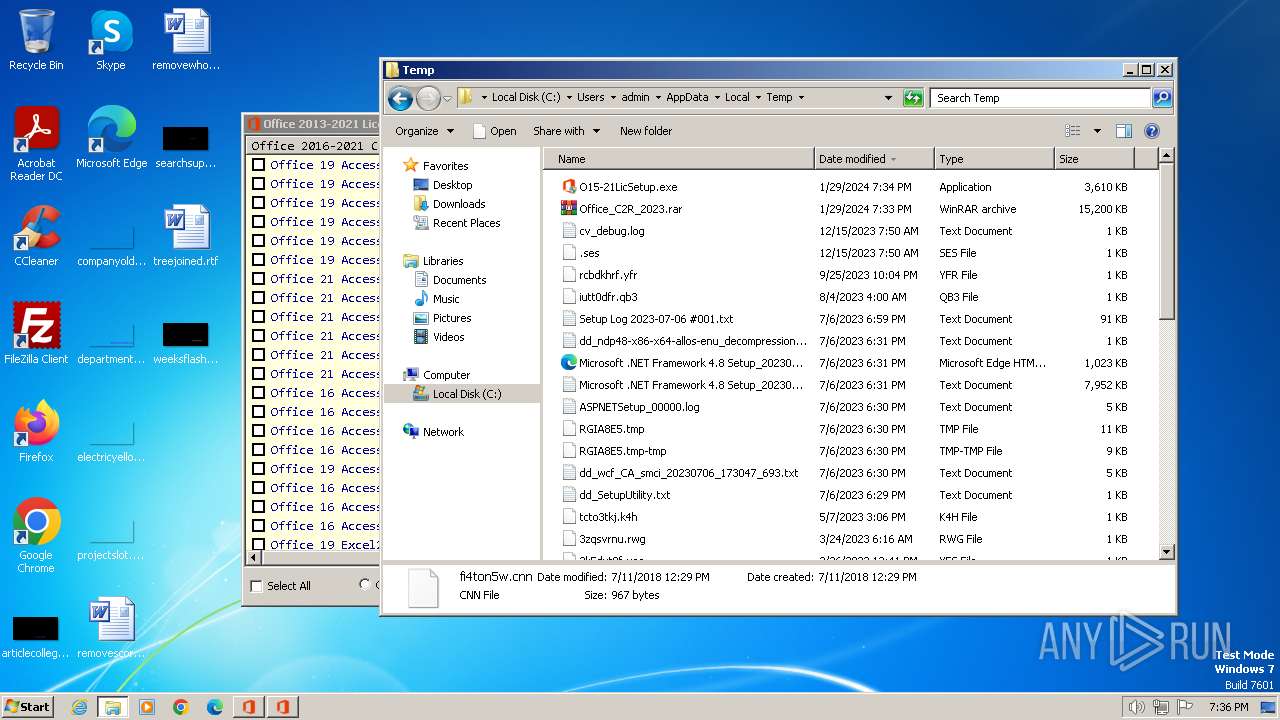
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
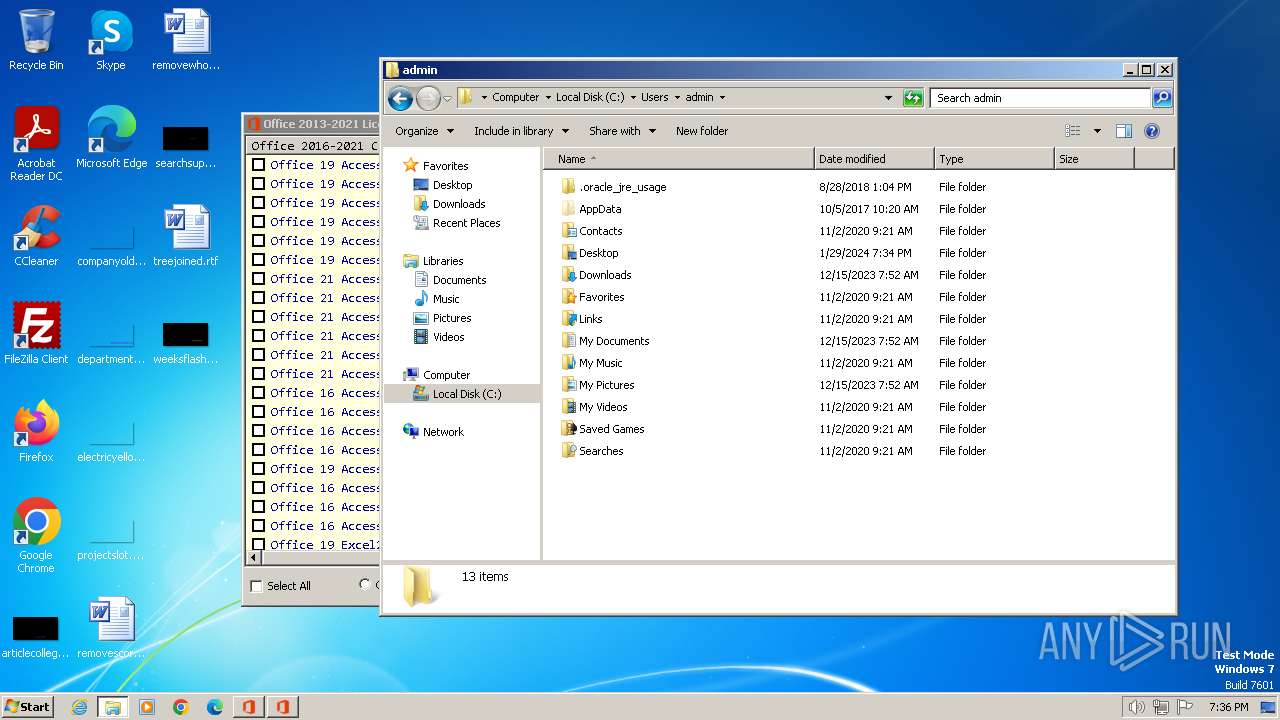
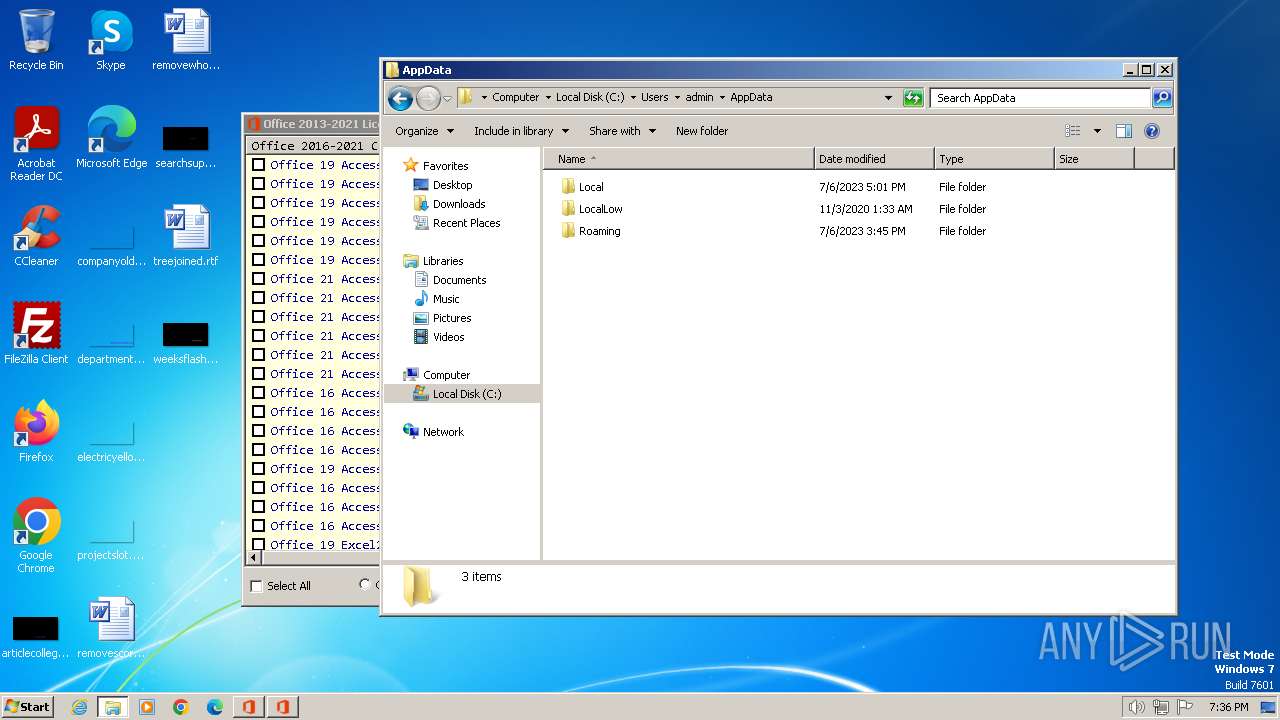
| 268 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa268.32882\Office_C2R_2023_7.6.0.rar | — | |
MD5:— | SHA256:— | |||
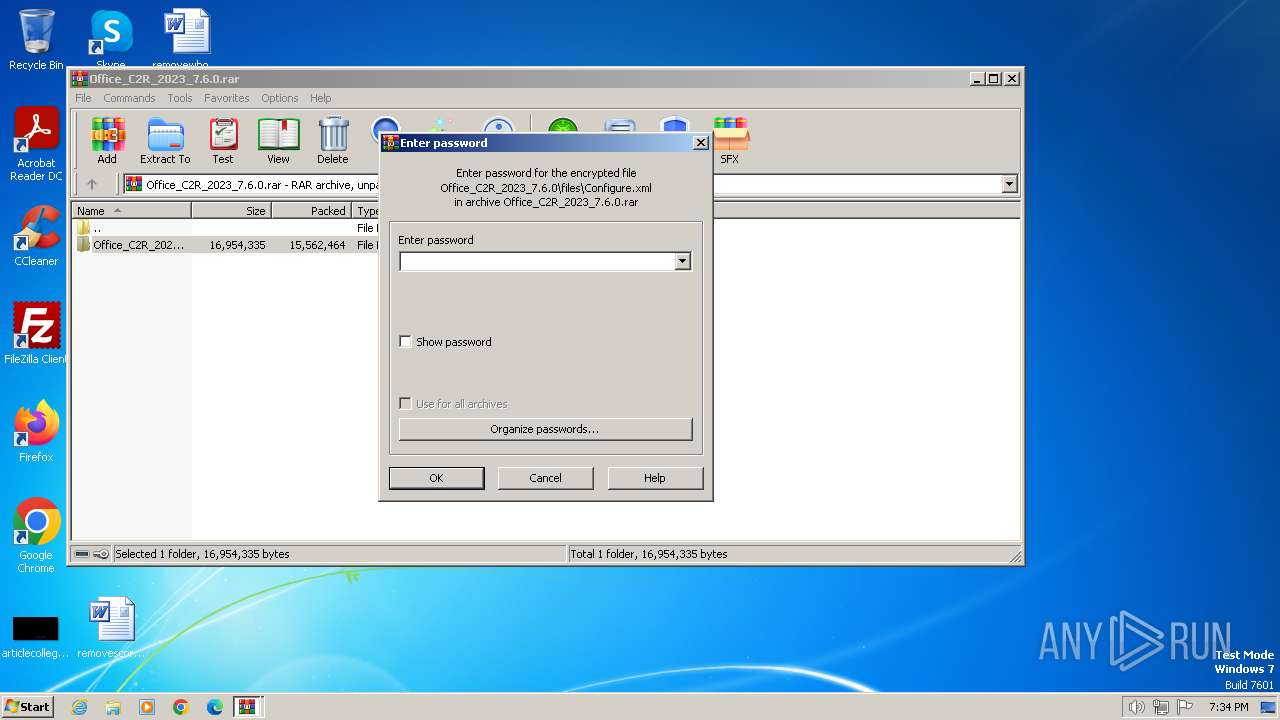
| 1632 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1632.33232\Office_C2R_2023_7.6.0\files\Configure.xml | text | |
MD5:62ED85E5A45666AD7999DB9F19AE0454 | SHA256:E0C5B4921562D8162FFC0D1B4EE70C804EAD5C1569E56A027C504CFD8C2E831F | |||
| 1632 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1632.33232\Office_C2R_2023_7.6.0\files\x86\msvcr100.dll | executable | |
MD5:BF38660A9125935658CFA3E53FDC7D65 | SHA256:60C06E0FA4449314DA3A0A87C1A9D9577DF99226F943637E06F61188E5862EFA | |||
| 1632 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1632.33232\Office_C2R_2023_7.6.0\files\Uninstall.xml | text | |
MD5:364F86F97324EA82FE0D142CD01CF6DD | SHA256:09D5B42140BAB13165BA97FBD0E77792304C3C93555BE02C3DCE21A7A69C66DD | |||
| 3560 | files.dat | C:\Users\admin\AppData\Local\Temp\o15files\AccessR_Grace-ppd.xrm-ms | xml | |
MD5:A7511730CE3F5CF512224DF650ECCF4C | SHA256:2E0B336C45DCC7FA1902C21CE9D3C59A0AAF0653E7F1EFAAC73DFF0C5BCC138B | |||
| 3560 | files.dat | C:\Users\admin\AppData\Local\Temp\o15files\AccessR_Grace-ul-oob.xrm-ms | xml | |
MD5:9602E7CC4CB46F3B6E4FA33E158AB0D7 | SHA256:6B14E4026FEF6E824E07310F570E4C820E18AF35849A9037777EA46DBF2B4FFC | |||
| 3600 | O15-21LicSetup.exe | C:\Users\admin\AppData\Local\Temp\files.dat | executable | |
MD5:DC2D0D6E8B2D38B3456DACD9D4FCF392 | SHA256:6CCC6BB1569067BFCC579AB0A432987638EB37F3675AADE0388467E232D97EF9 | |||
| 1632 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1632.33232\Office_C2R_2023_7.6.0\files\x86\cleanospp.exe | executable | |
MD5:5FD363D52D04AC200CD24F3BCC903200 | SHA256:3FDEFE2AD092A9A7FE0EDF0AC4DC2DE7E5B9CE6A0804F6511C06564194966CF9 | |||
| 3560 | files.dat | C:\Users\admin\AppData\Local\Temp\o15files\AccessR_OEM_Perp-pl.xrm-ms | xml | |
MD5:2DBFB475049A649A07512E6BE8D5E1B4 | SHA256:C34A77B0F5573B303ECEE1038E5B8AADFA7A2088BA8B8B64669B18723CD54046 | |||
| 3560 | files.dat | C:\Users\admin\AppData\Local\Temp\o15files\AccessR_OEM_Perp-ppd.xrm-ms | xml | |
MD5:2BDA339E2BD24A4BD6AD9A014BD6ECB2 | SHA256:1B480130EE98D24041C6F223CEF3CCB4EA51009FCC53E6AED055DAEE91B62ADB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3248 | test.exe | 104.208.72.228:1688 | kms.loli.beer | MICROSOFT-CORP-MSN-AS-BLOCK | HK | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kms.loli.beer |
| unknown |