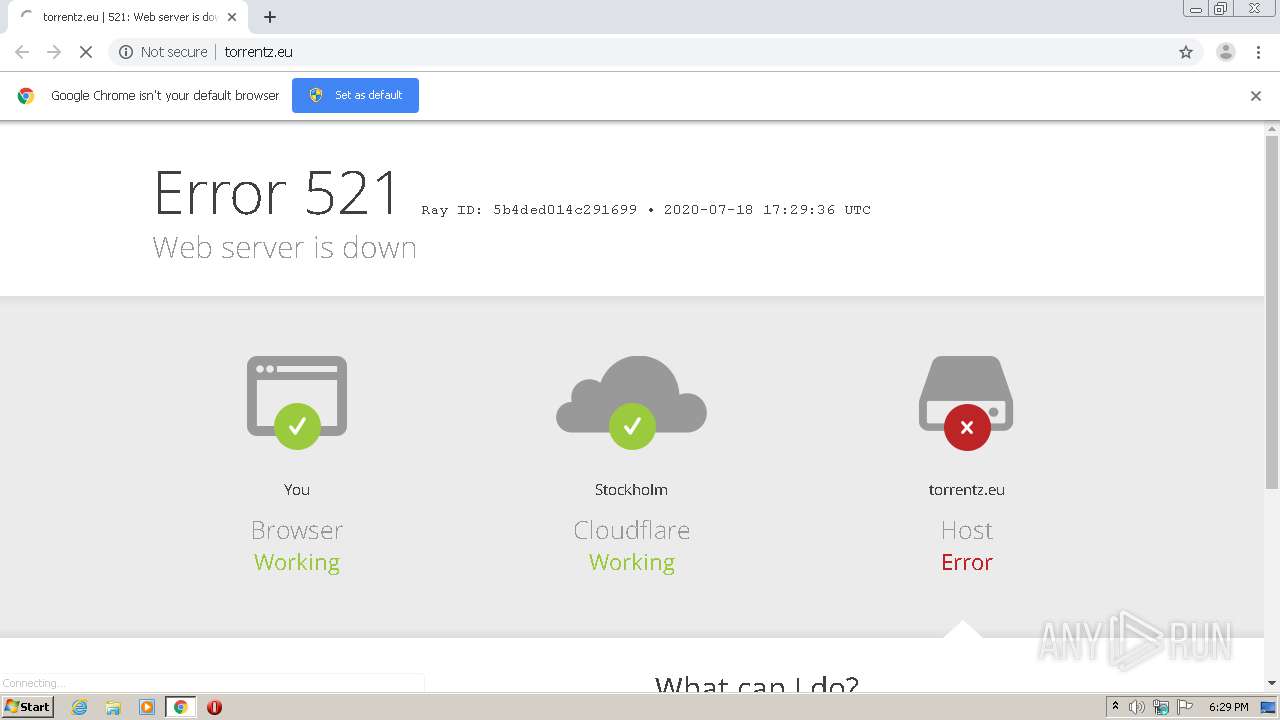
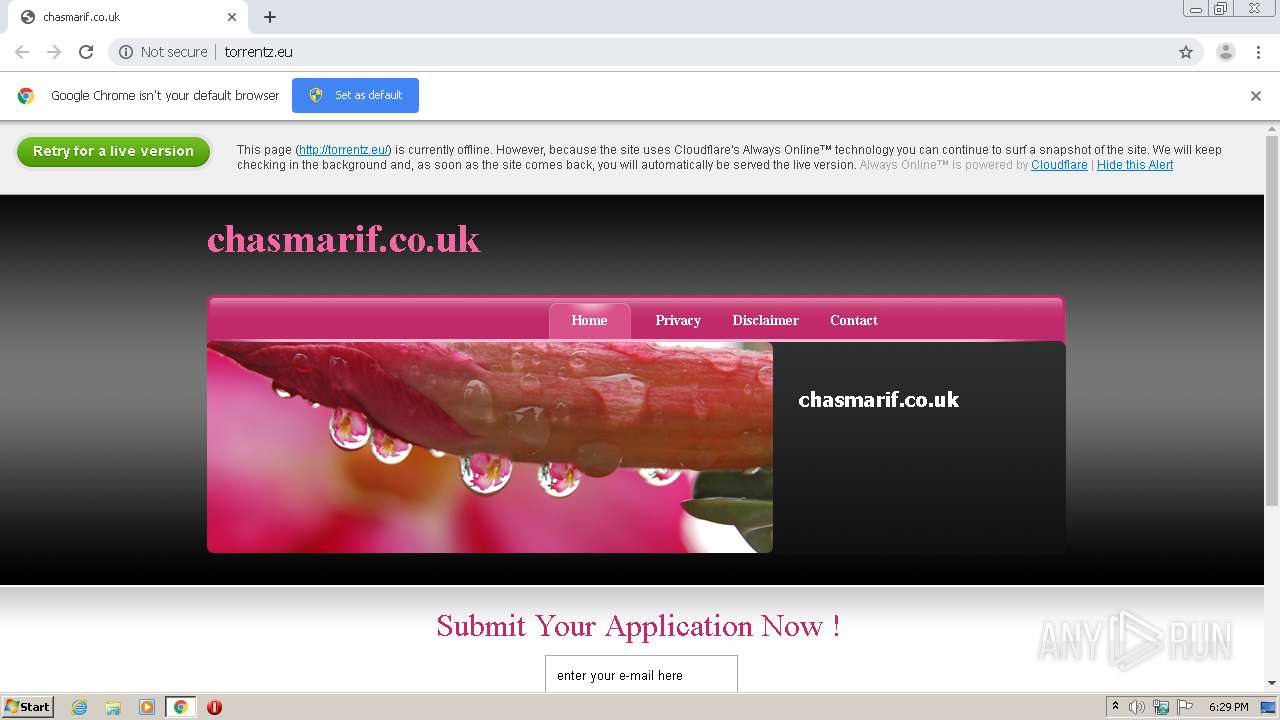
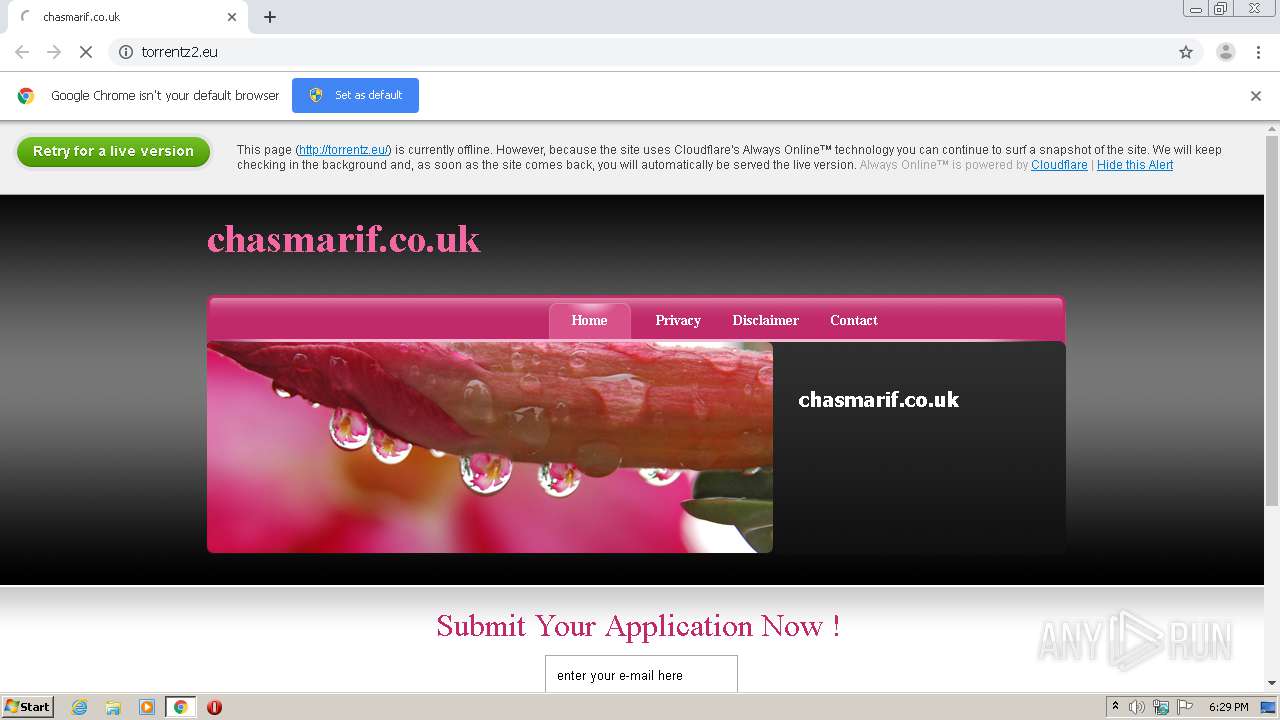
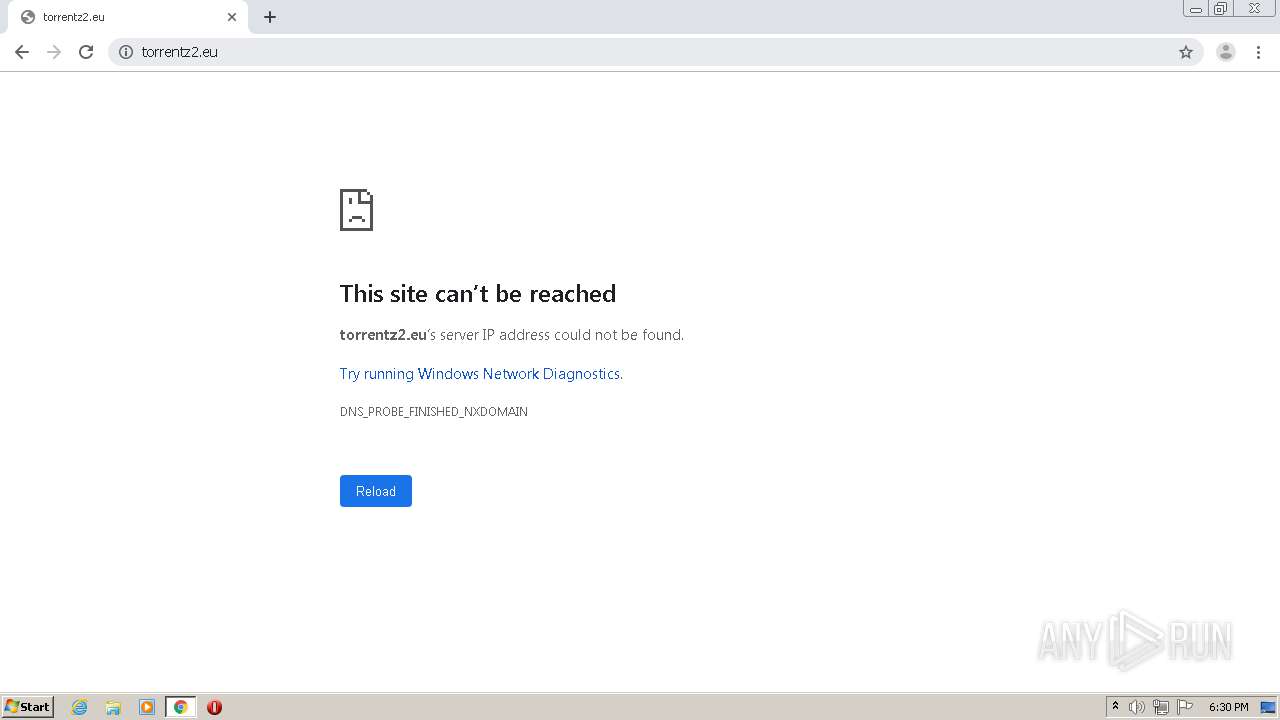
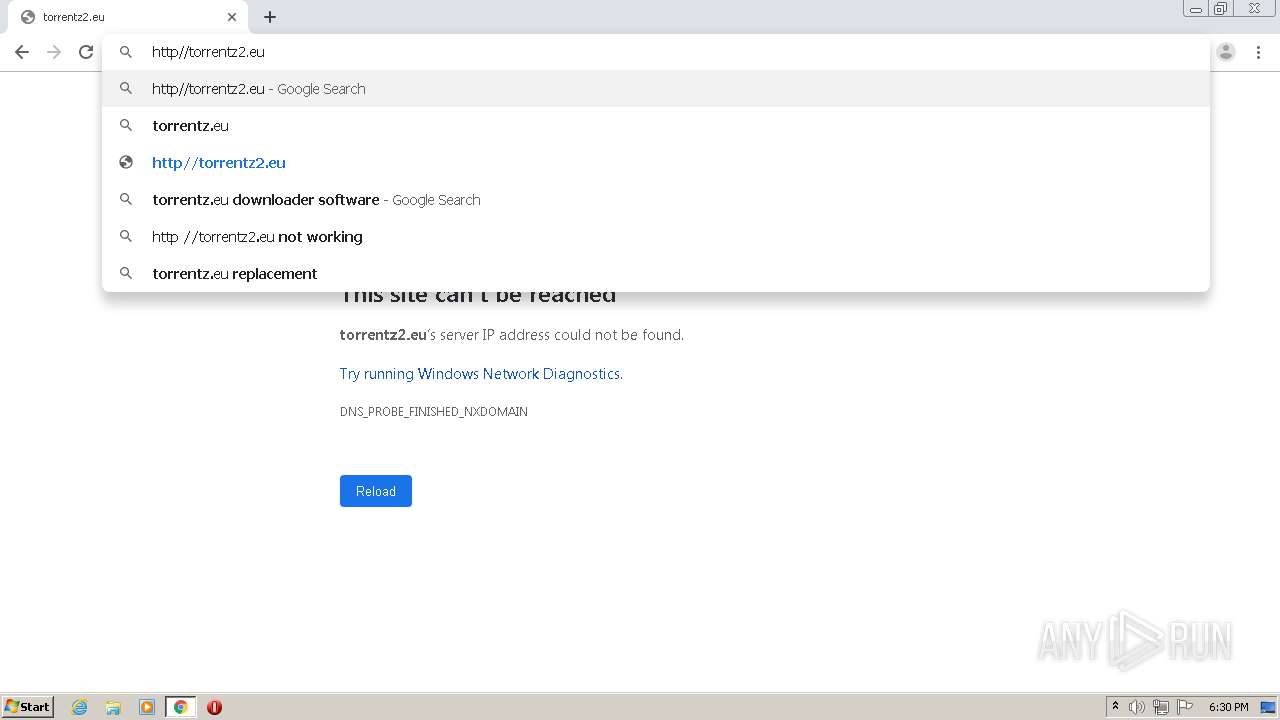
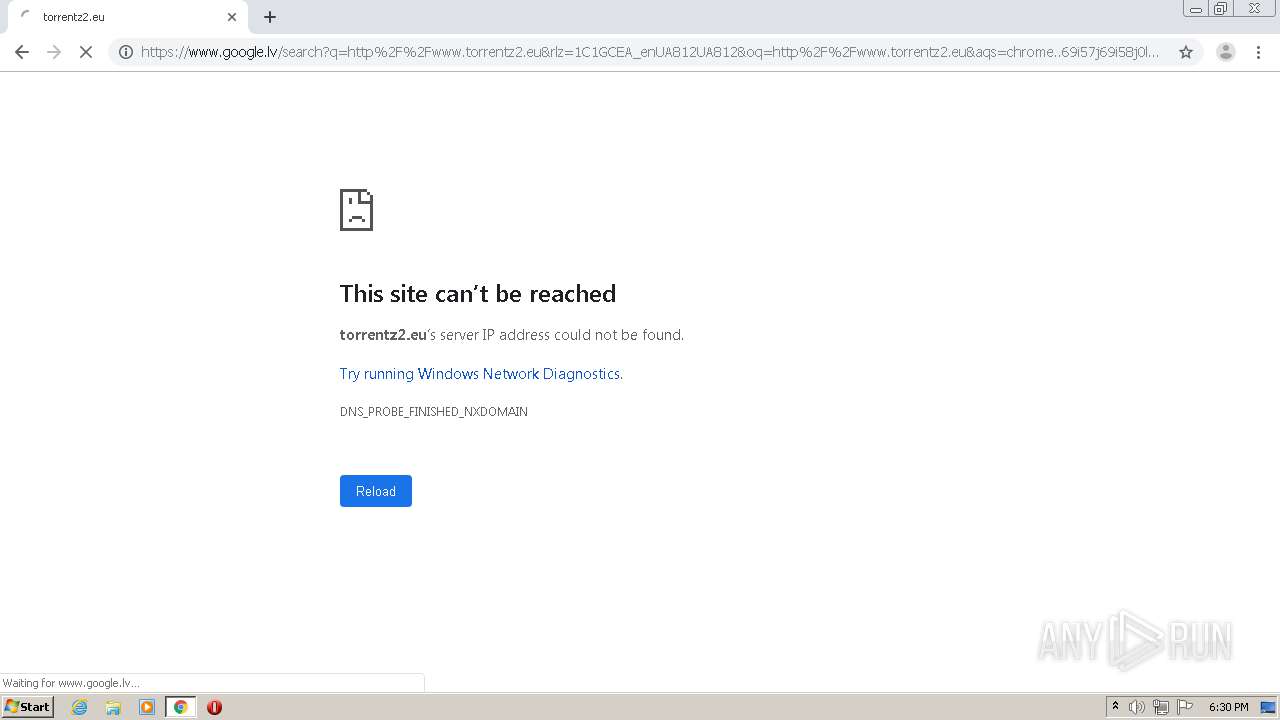
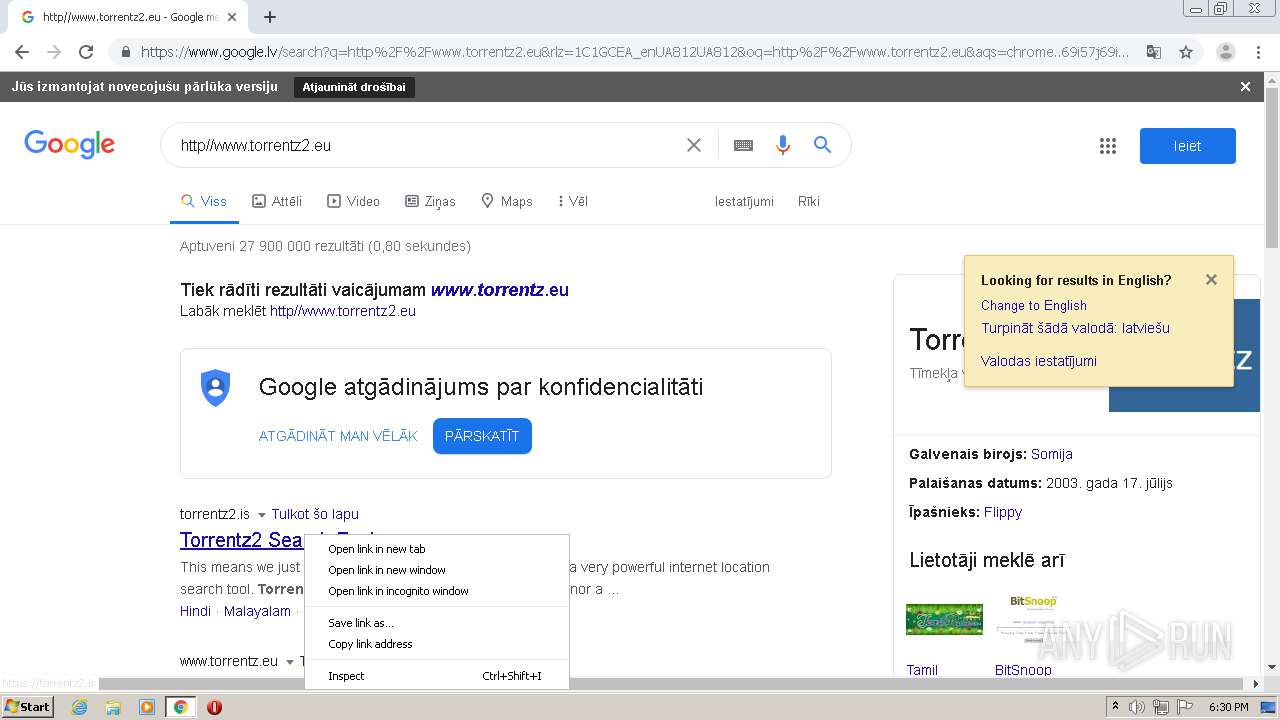
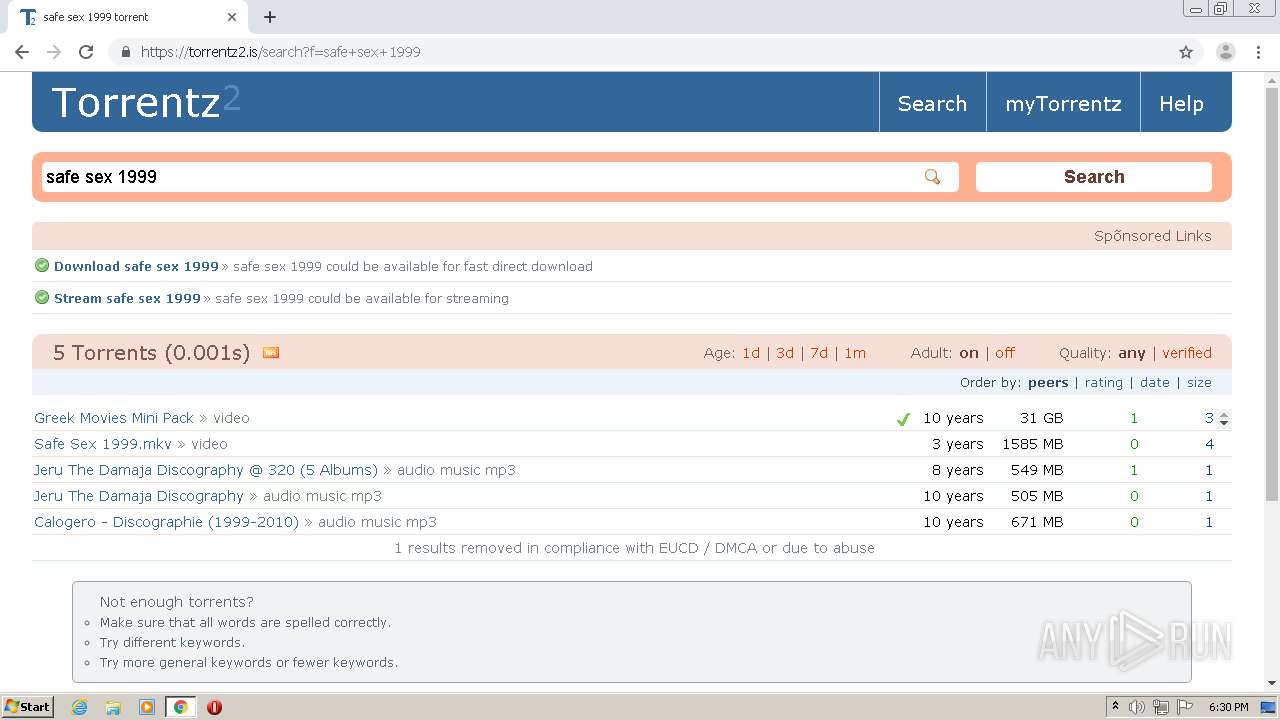
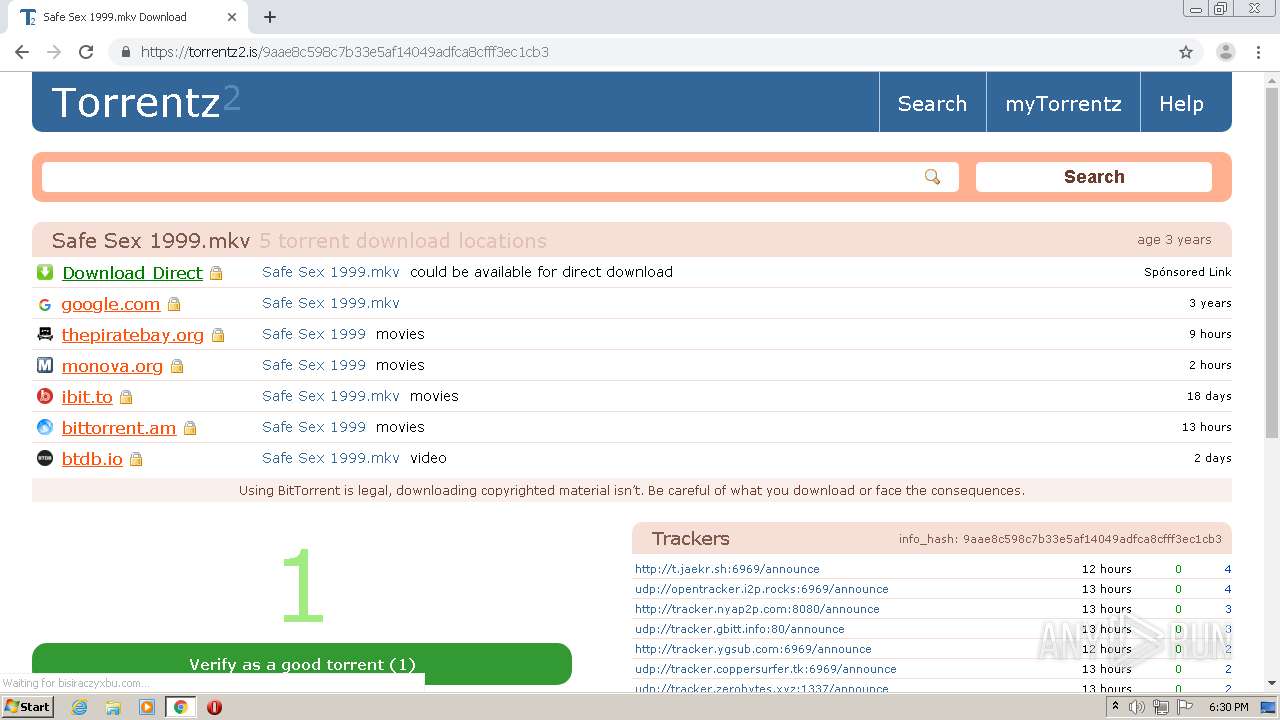
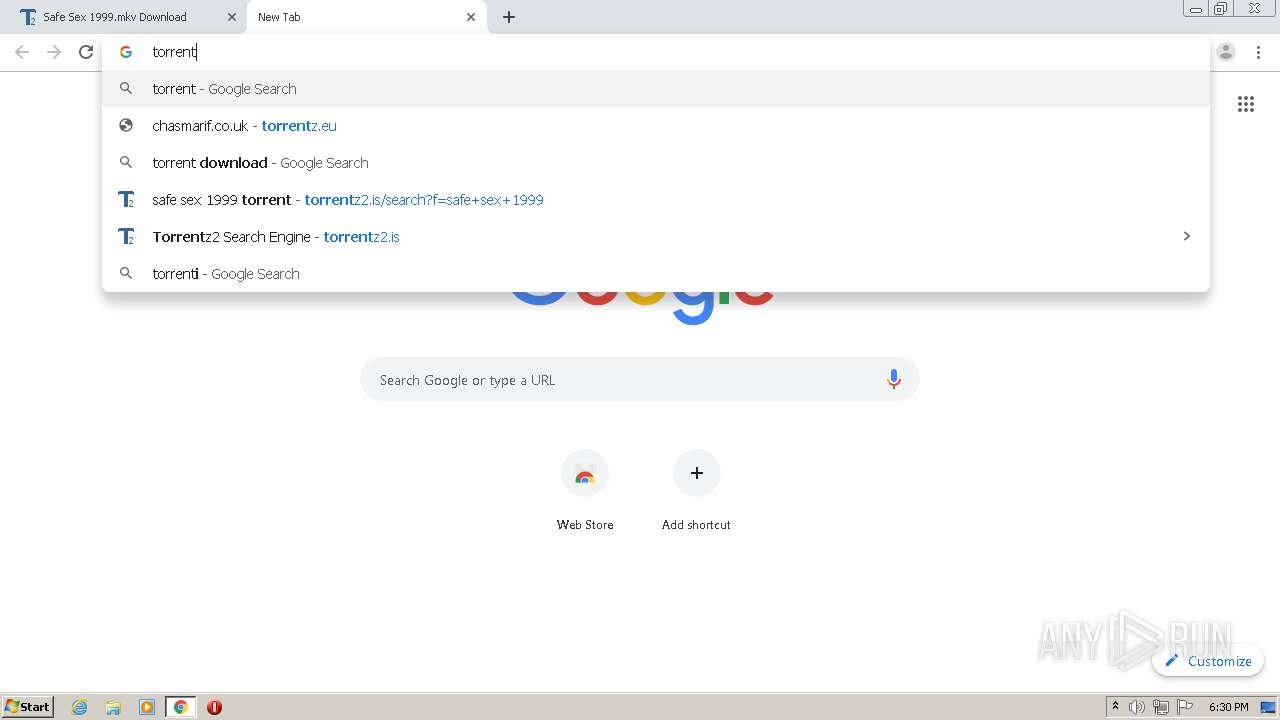
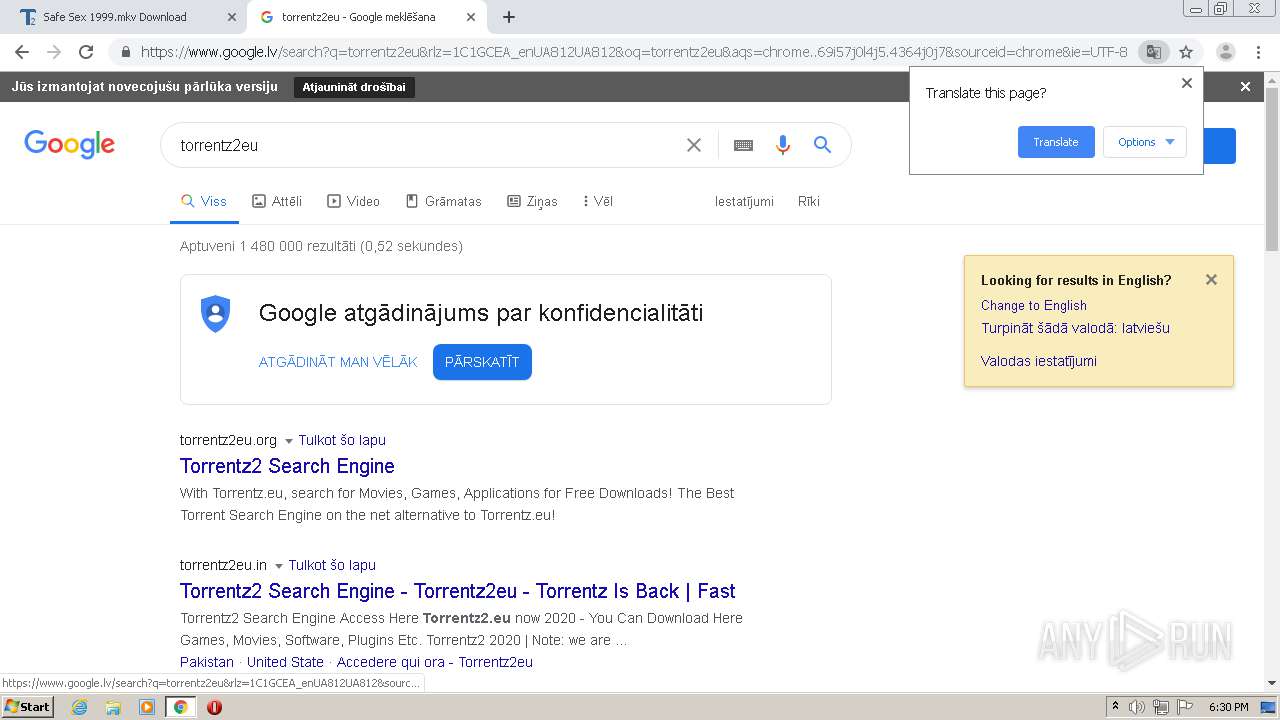
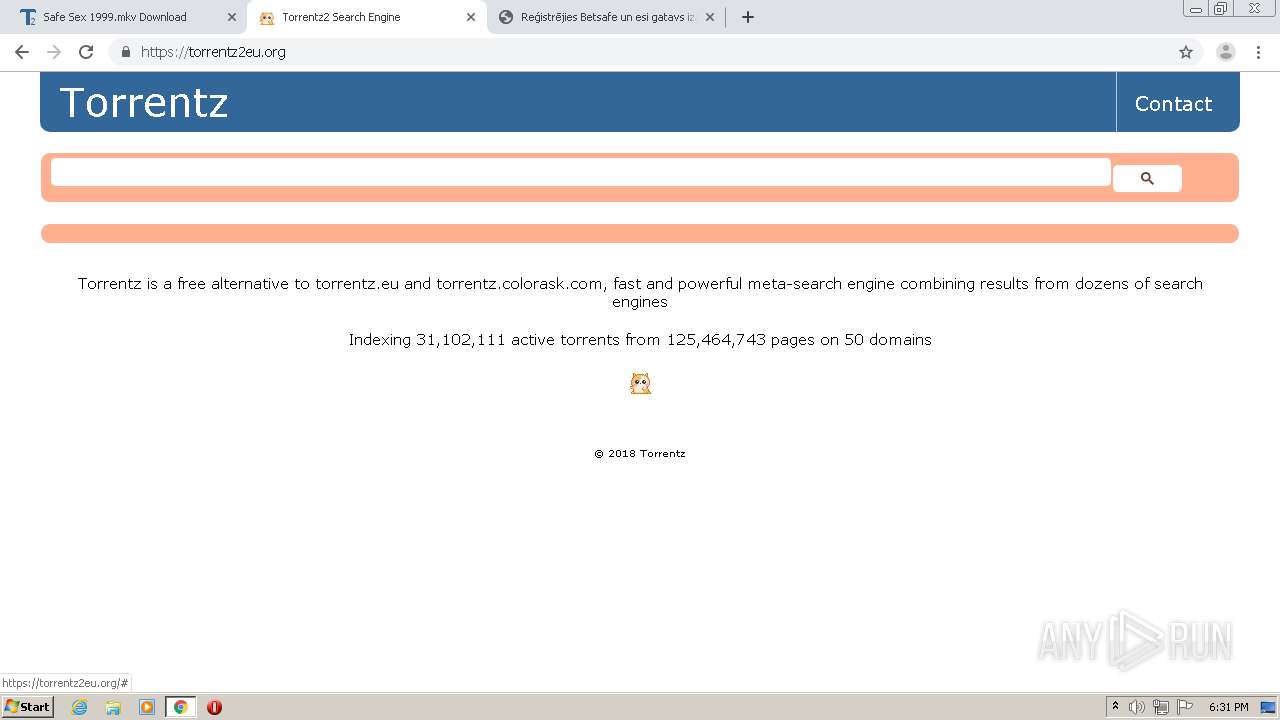
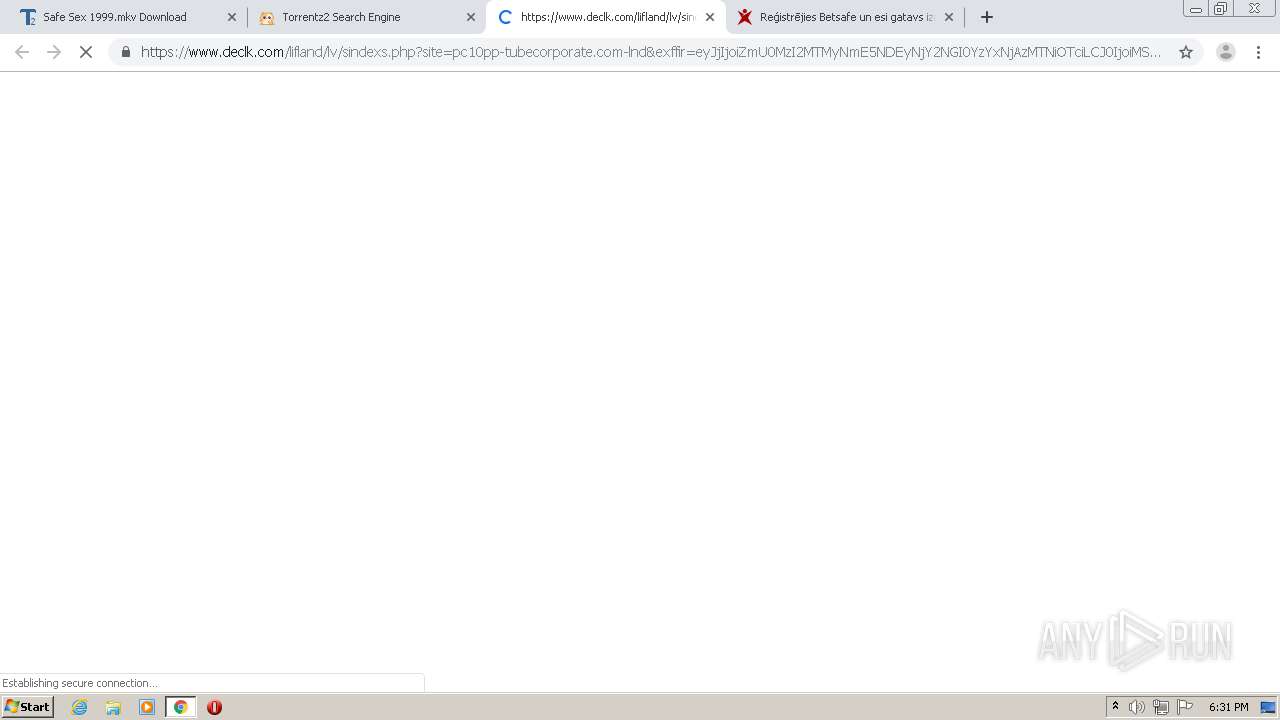
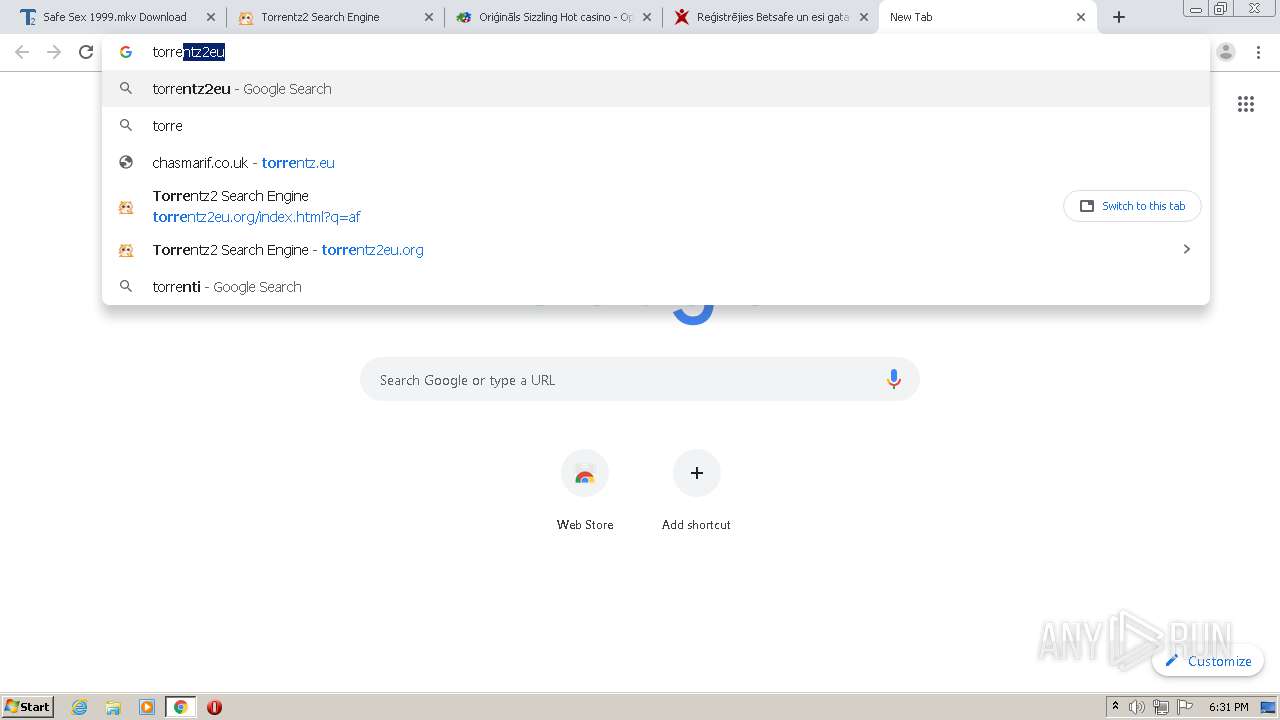
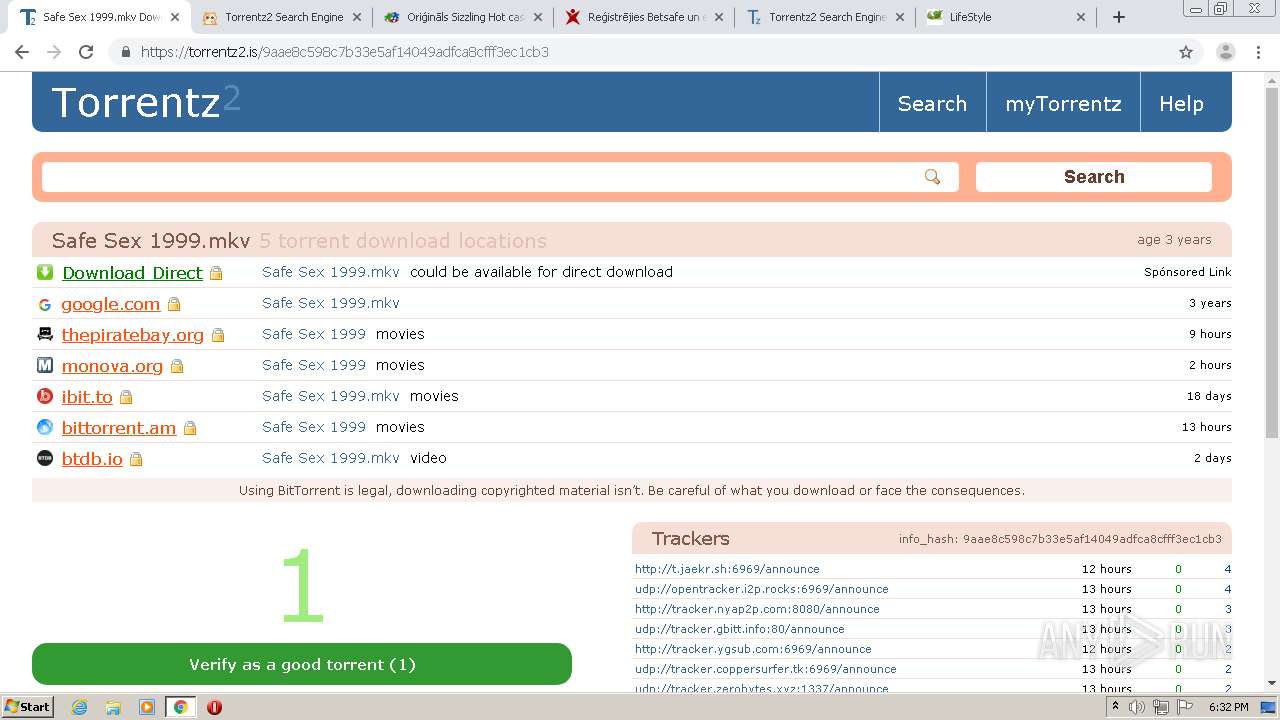
| URL: | http://torrentz.eu |
| Full analysis: | https://app.any.run/tasks/d9087b0c-9daf-4aaf-9230-a273f0abc756 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2020, 17:29:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0ACAF51B6DFEF20293F997C775CE653A |
| SHA1: | B5749D8B3E5AFE9DDEEA6B75E924F204A09A10AA |
| SHA256: | 149649022D946EE1730C3D54F6742B4DC0BB28582B1E523B52C8D65C26BD9680 |
| SSDEEP: | 3:N1KKKHefp:CKWefp |
MALICIOUS
No malicious indicators.SUSPICIOUS
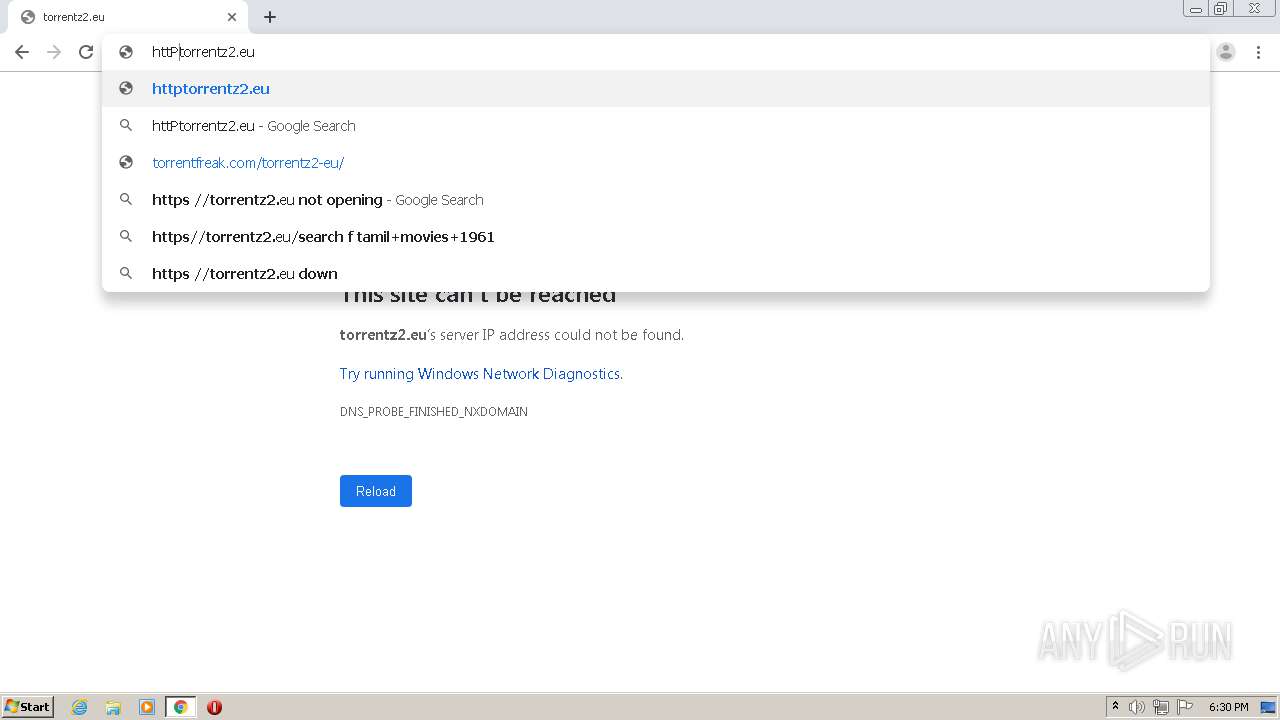
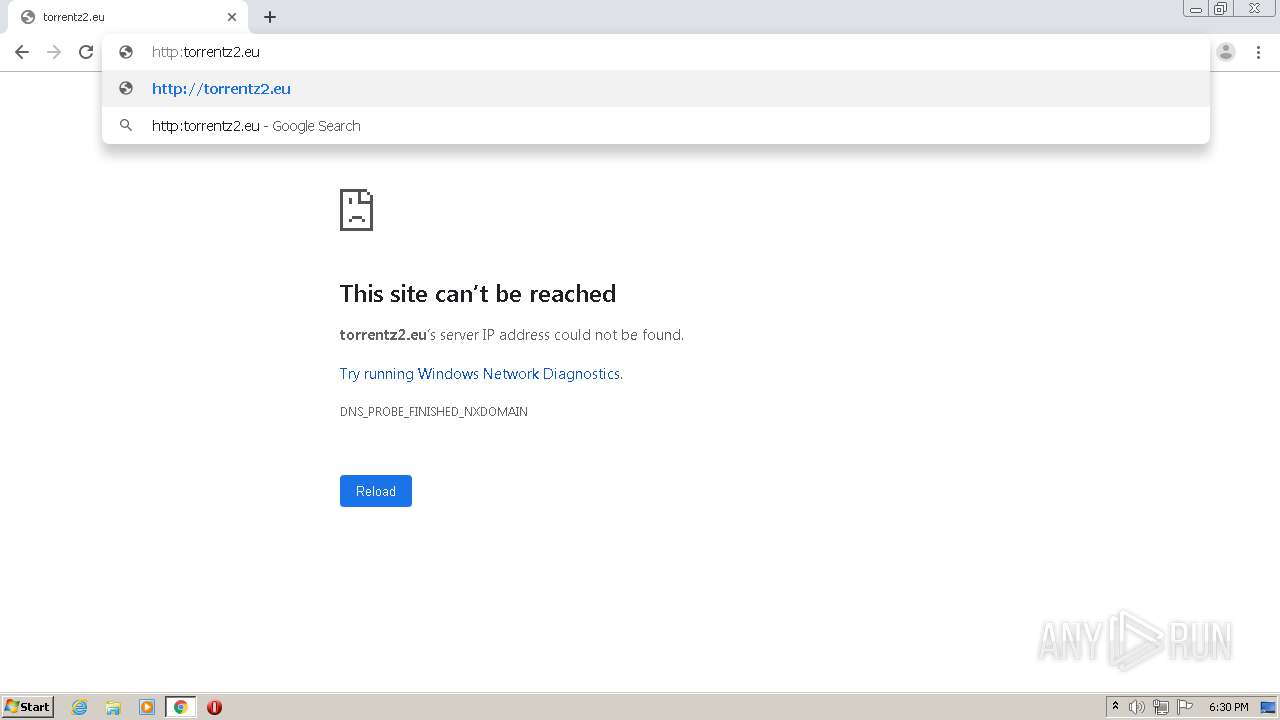
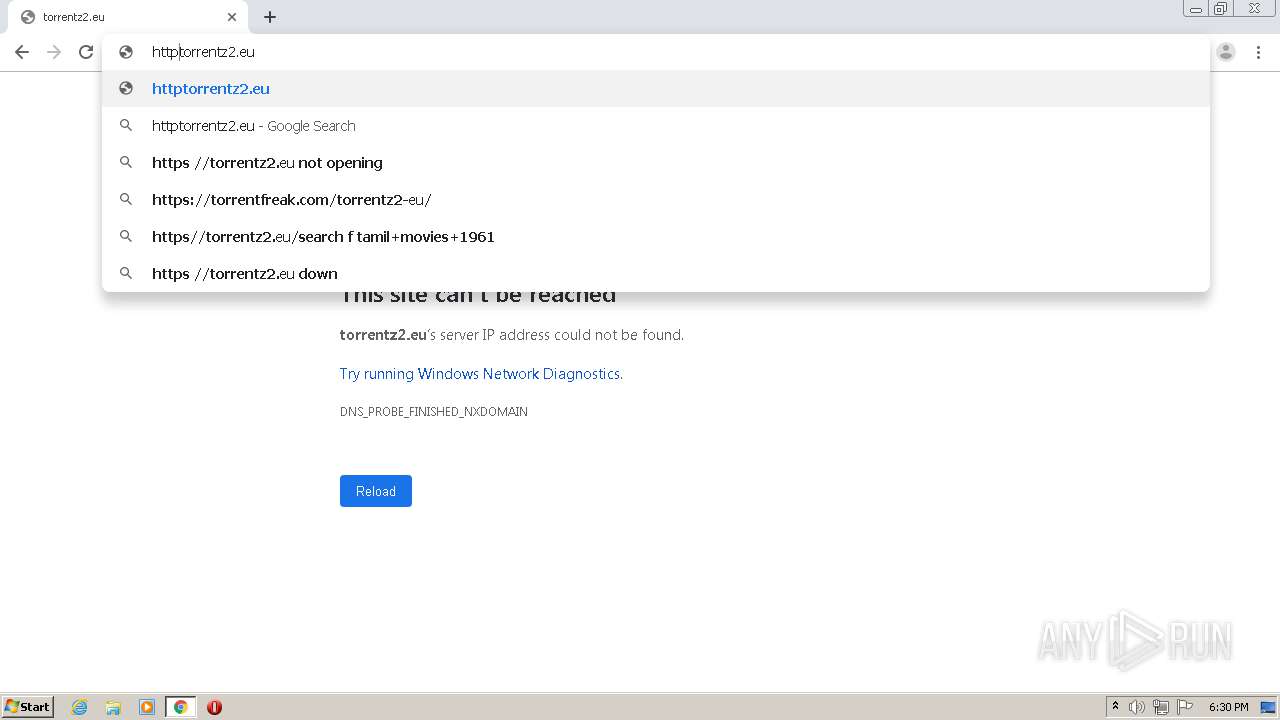
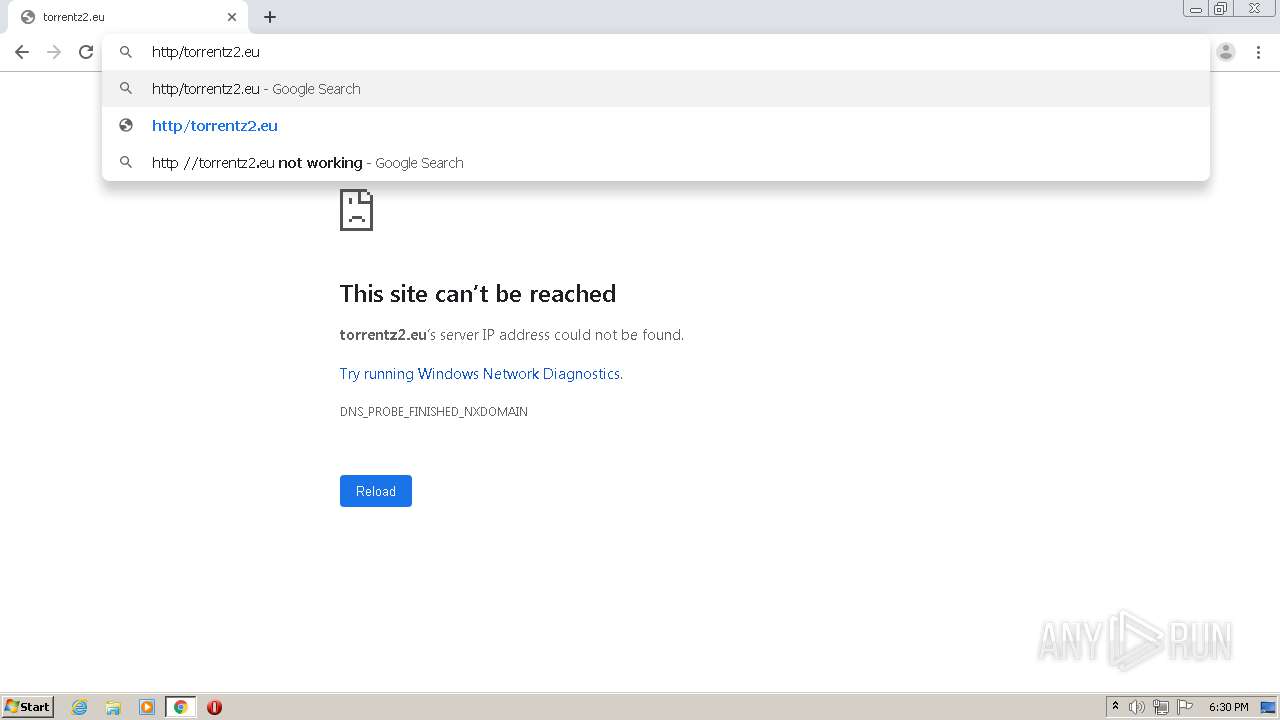
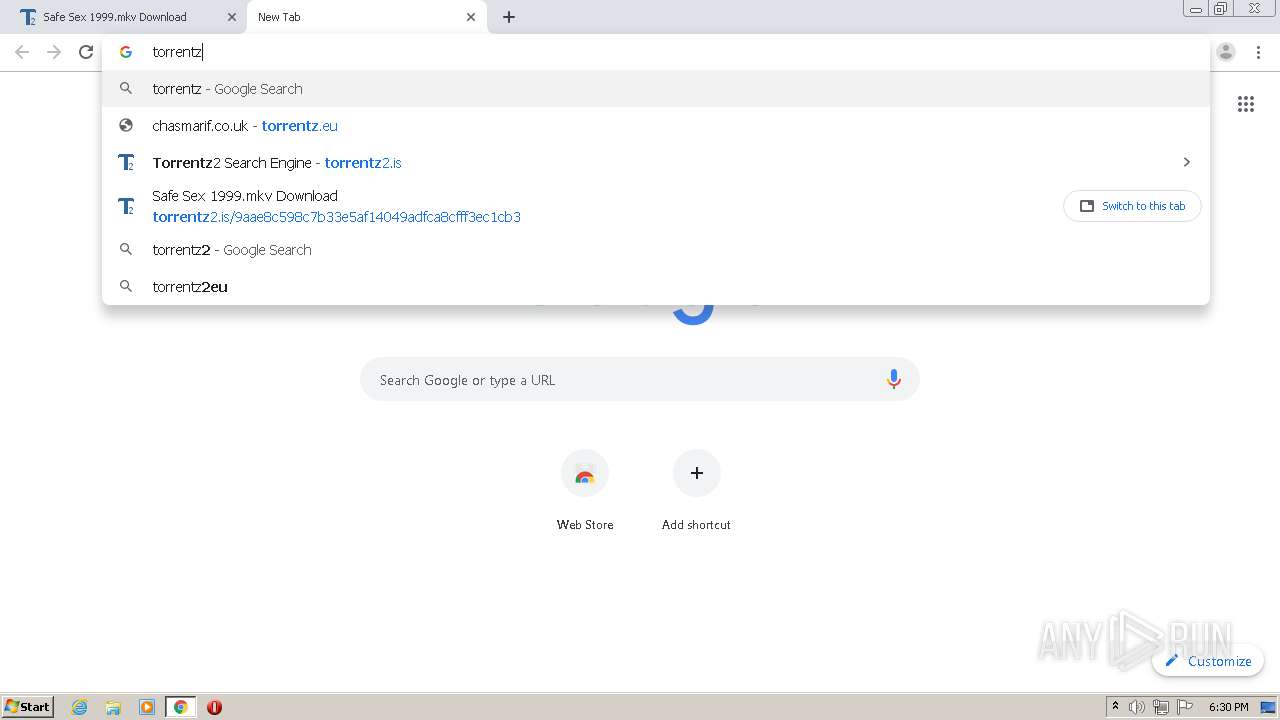
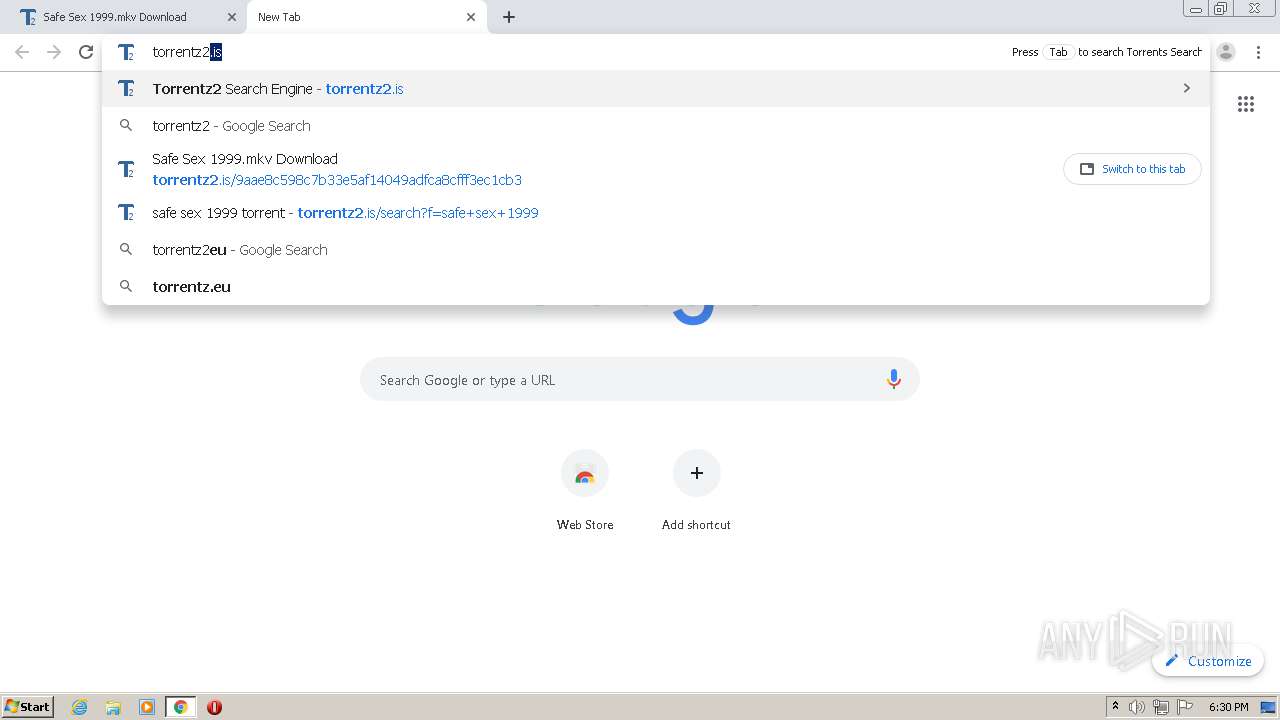
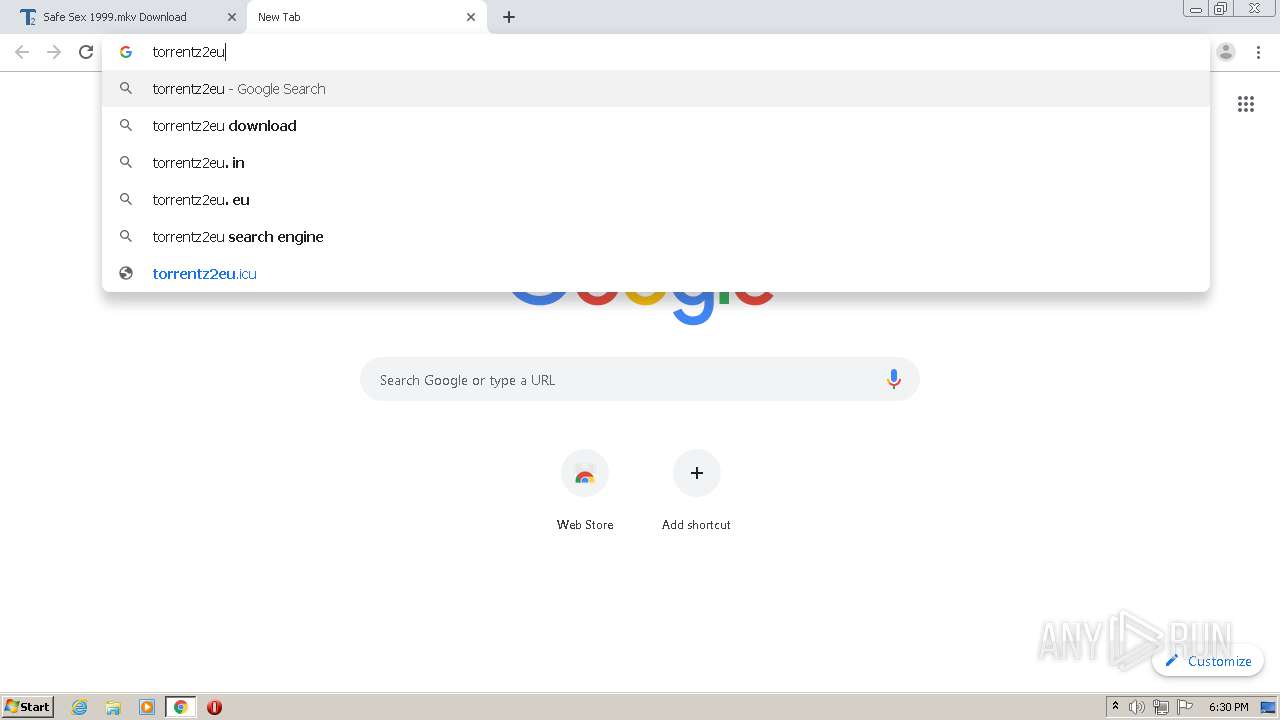
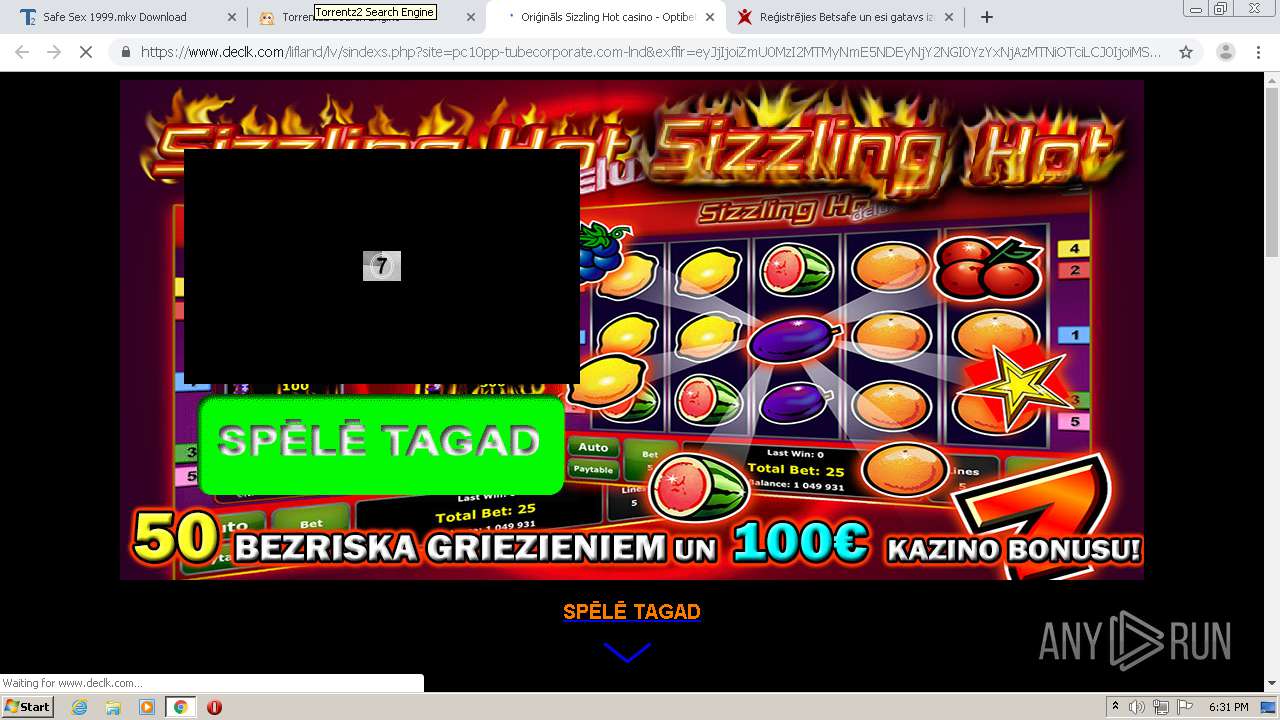
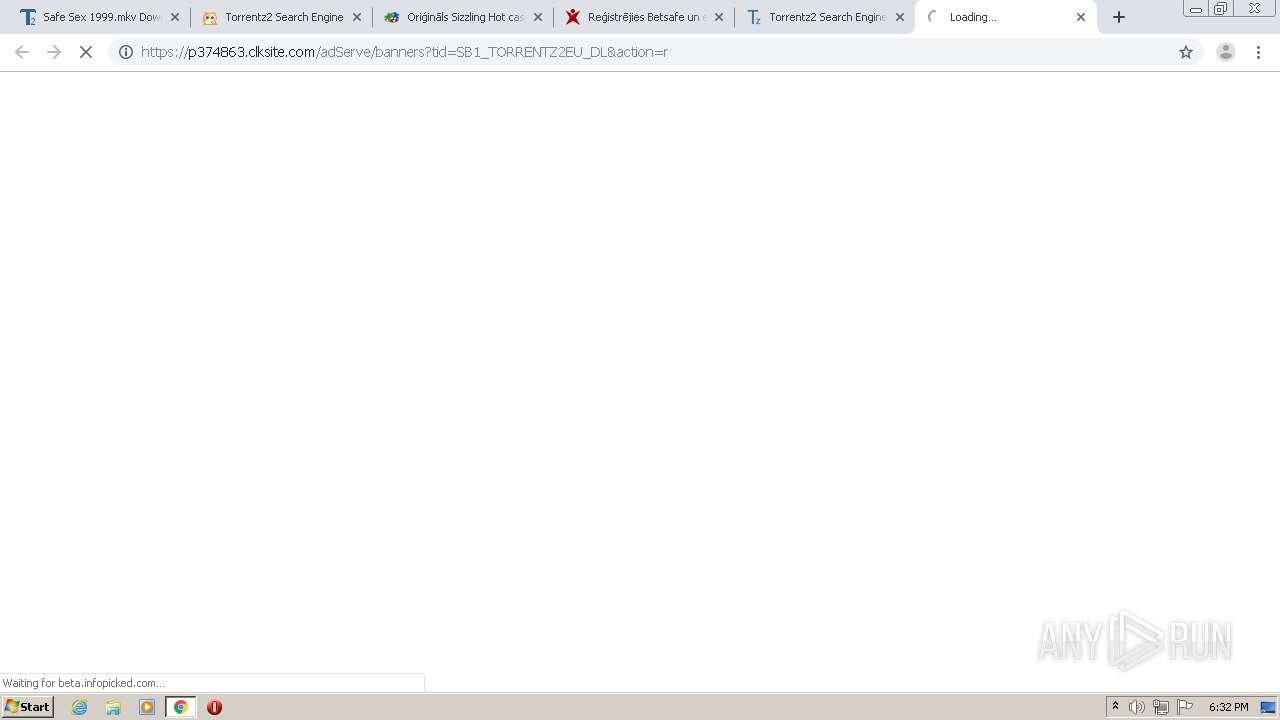
Modifies files in Chrome extension folder
- chrome.exe (PID: 2792)
INFO
Reads the hosts file
- chrome.exe (PID: 2792)
- chrome.exe (PID: 2460)
Application launched itself
- chrome.exe (PID: 2792)
Reads settings of System Certificates
- chrome.exe (PID: 2460)
Dropped object may contain TOR URL's
- chrome.exe (PID: 2792)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
111
Monitored processes
75
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15229805828131942164,12846341228042139814,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8380251750839440025 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3696 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15229805828131942164,12846341228042139814,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1536624497550611235 --renderer-client-id=71 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15229805828131942164,12846341228042139814,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12925517345089237149 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15229805828131942164,12846341228042139814,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12801801522529810094 --renderer-client-id=45 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15229805828131942164,12846341228042139814,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14050252669371234730 --renderer-client-id=52 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15229805828131942164,12846341228042139814,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2936601315447560351 --renderer-client-id=67 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15229805828131942164,12846341228042139814,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17618962684864308001 --mojo-platform-channel-handle=3604 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,15229805828131942164,12846341228042139814,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4870101422166088004 --renderer-client-id=55 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4396 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,15229805828131942164,12846341228042139814,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10426389327422147737 --mojo-platform-channel-handle=1032 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,15229805828131942164,12846341228042139814,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=758991228658770317 --mojo-platform-channel-handle=4148 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
850
Read events
712
Write events
133
Delete events
5
Modification events
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2792-13239566973808000 |
Value: 259 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2792) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
224
Text files
329
Unknown types
48
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F13317E-AE8.pma | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f4eaff2d-f854-492c-9095-eb4b19afbb4b.tmp | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF13c41e.TMP | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2792 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF13c603.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
174
DNS requests
110
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
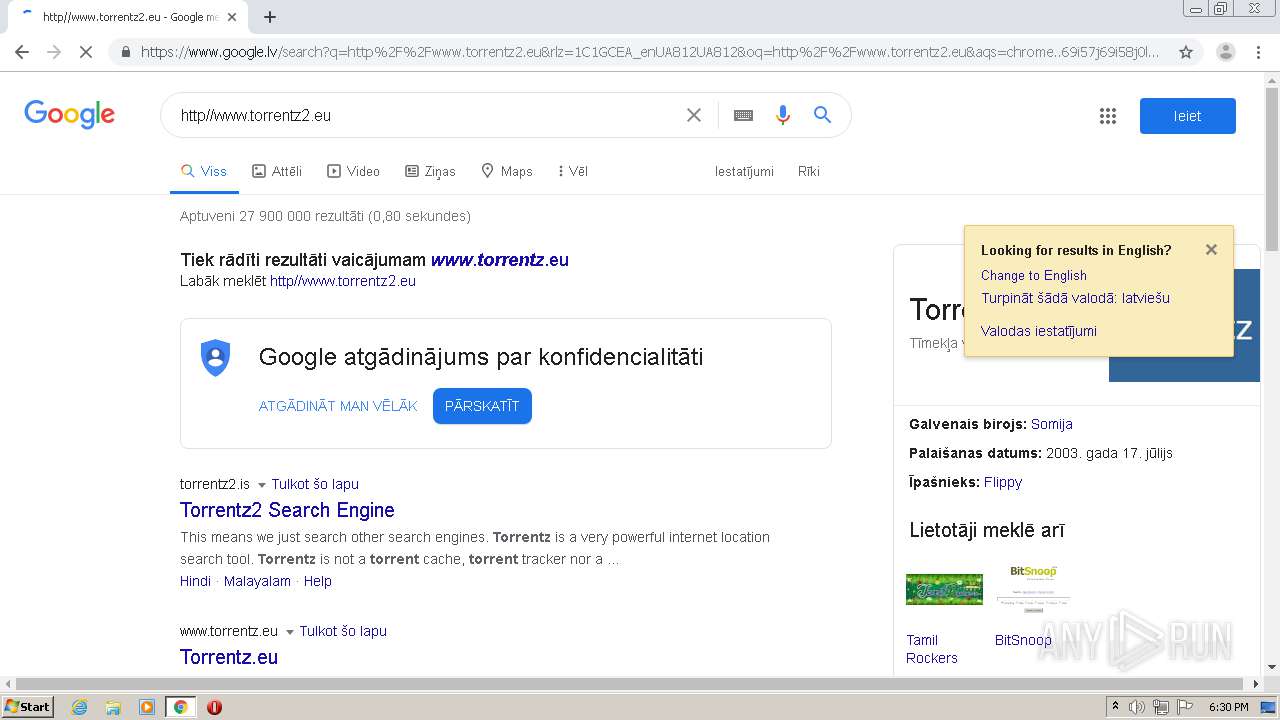
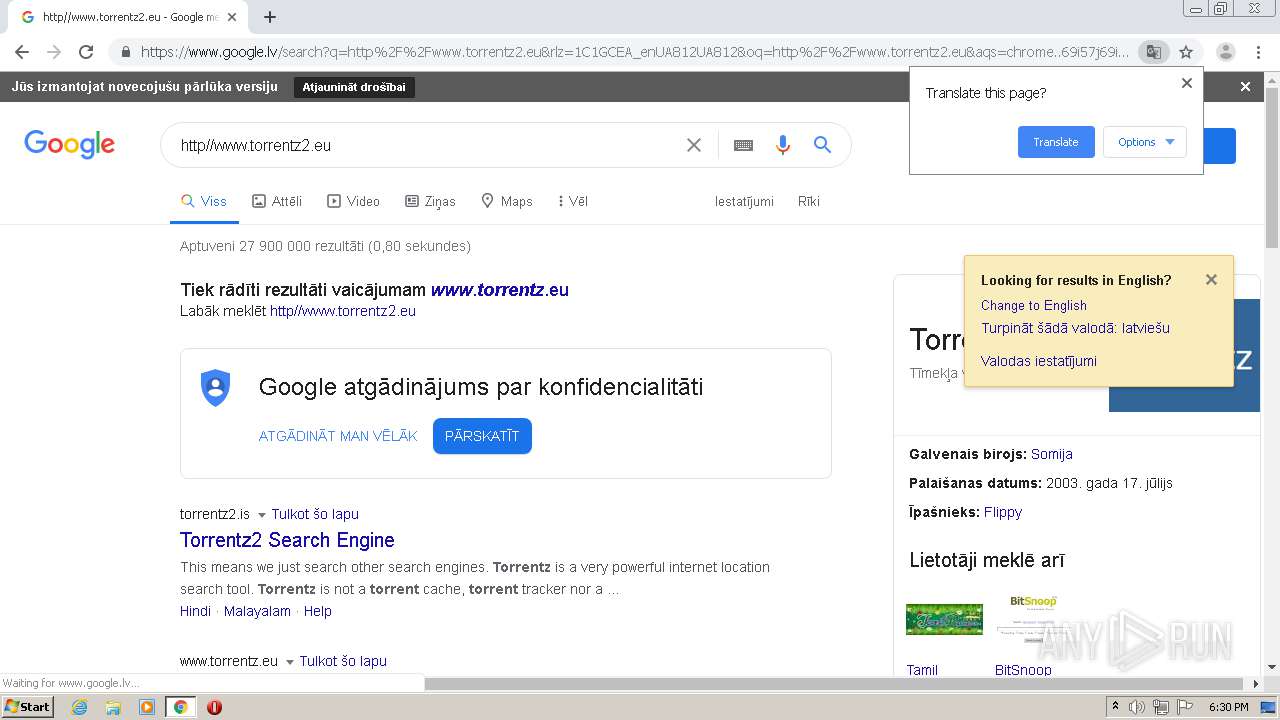
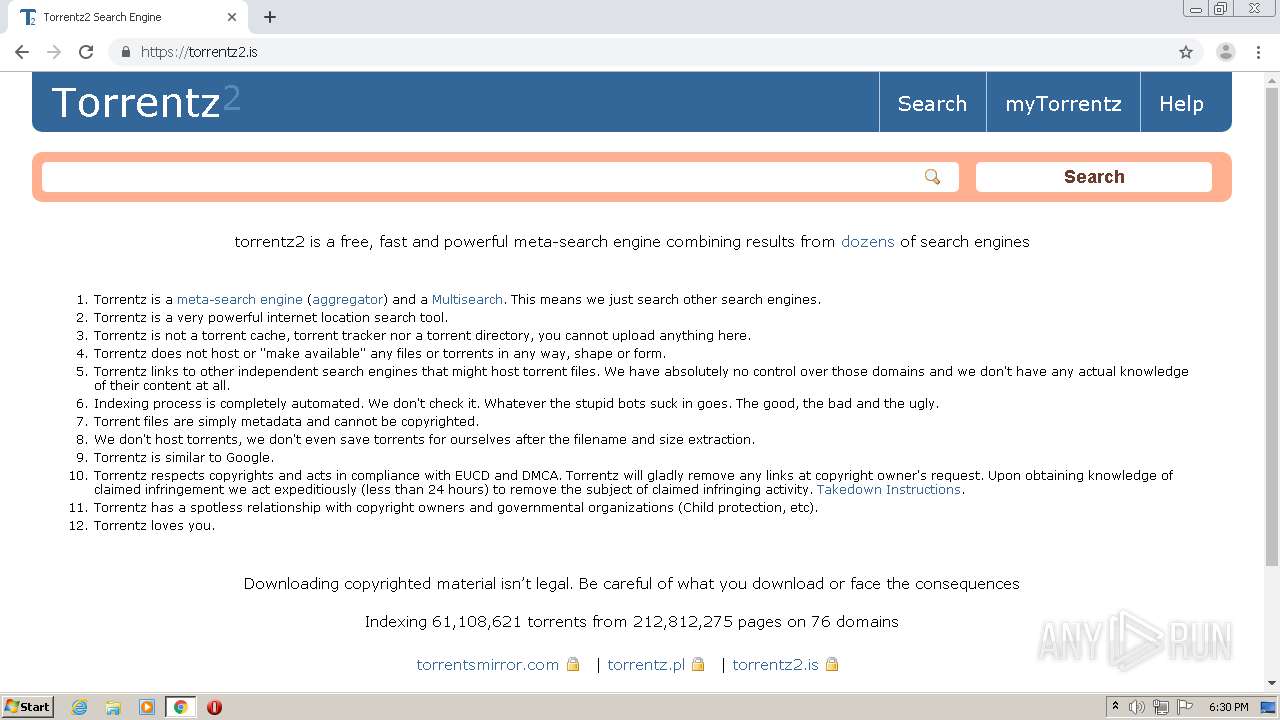
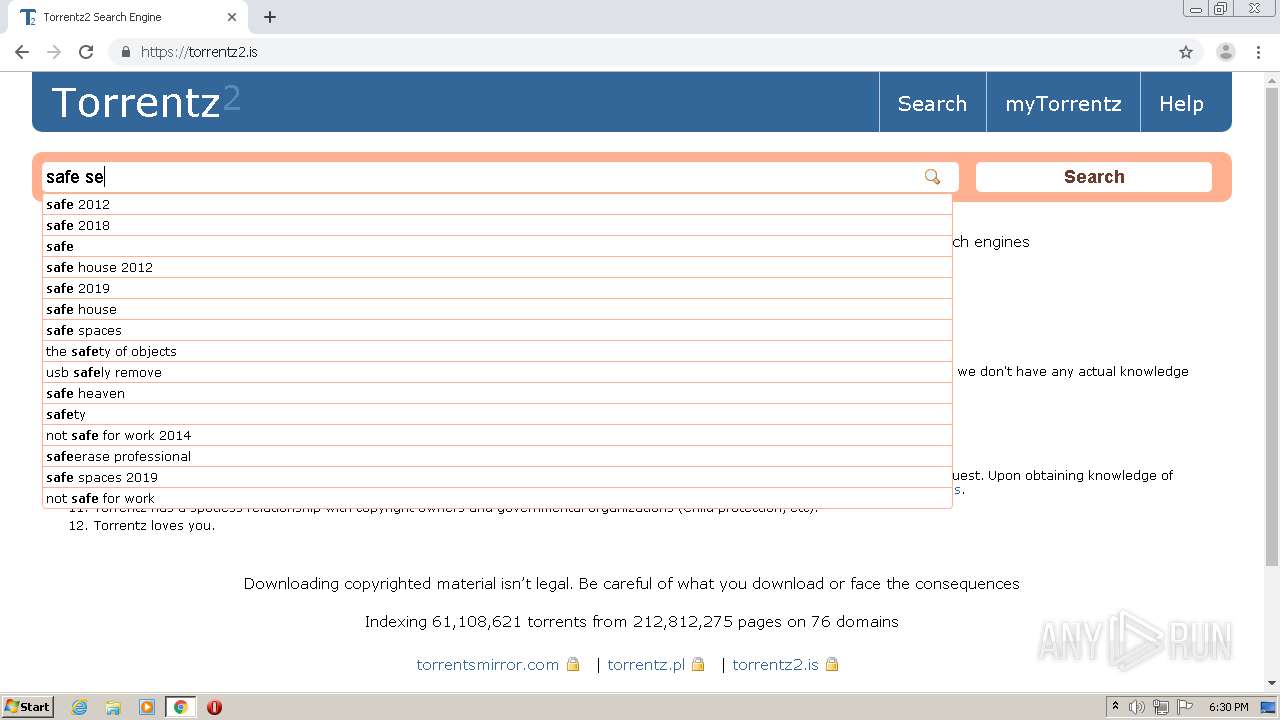
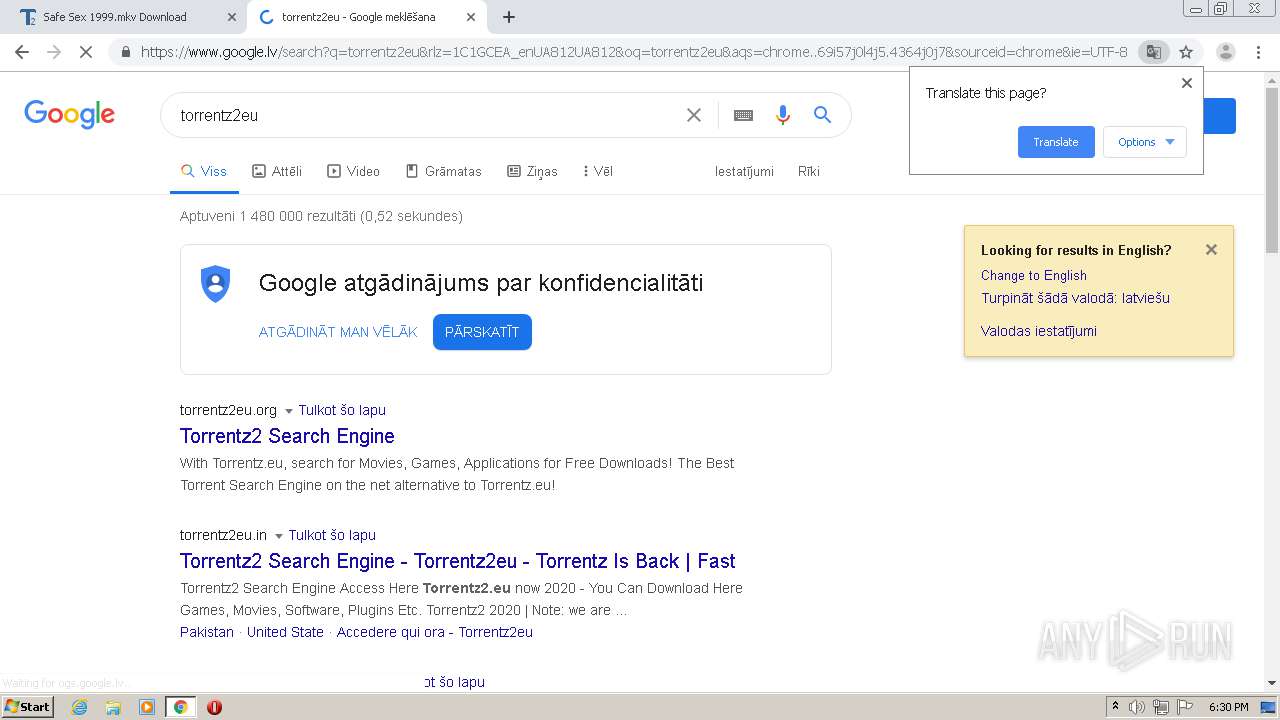
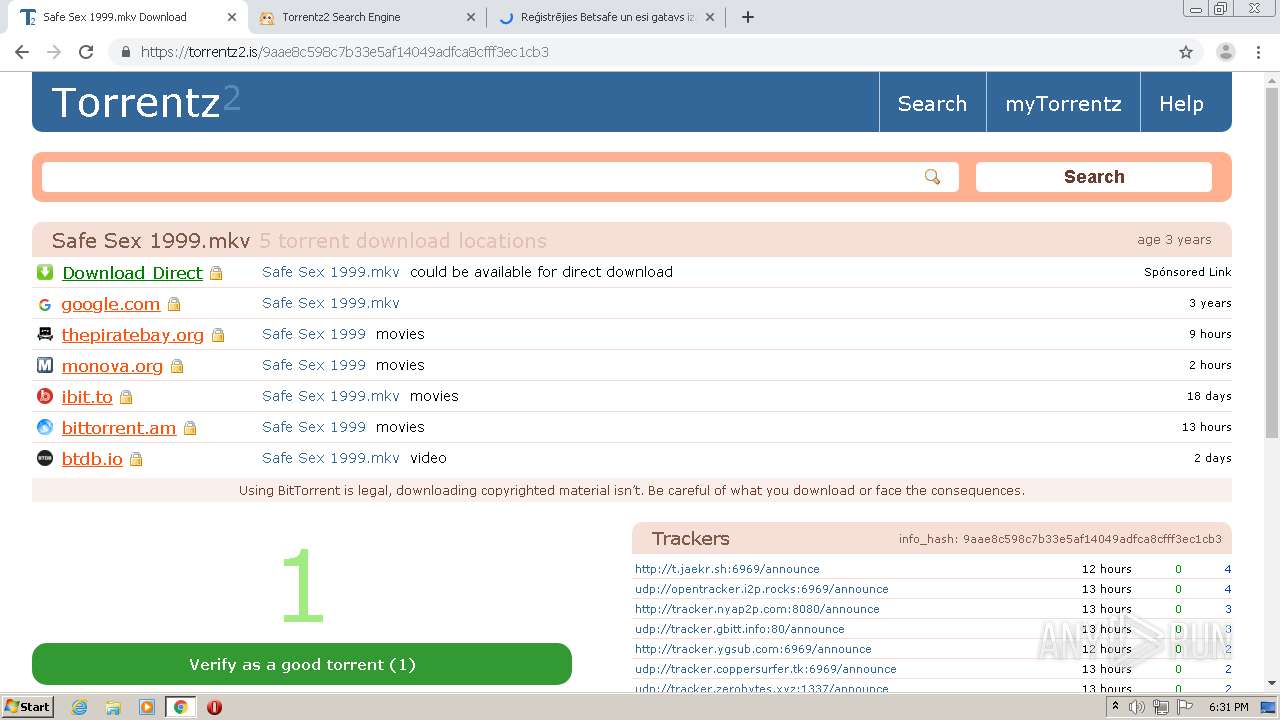
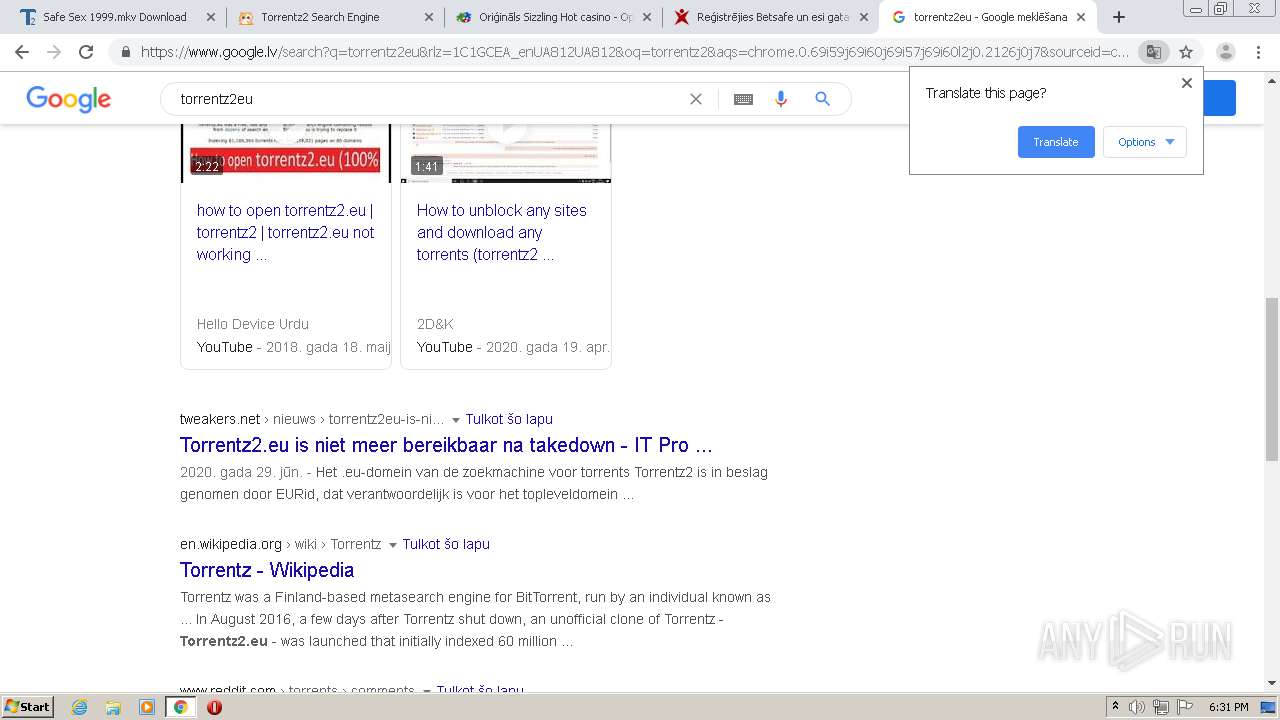
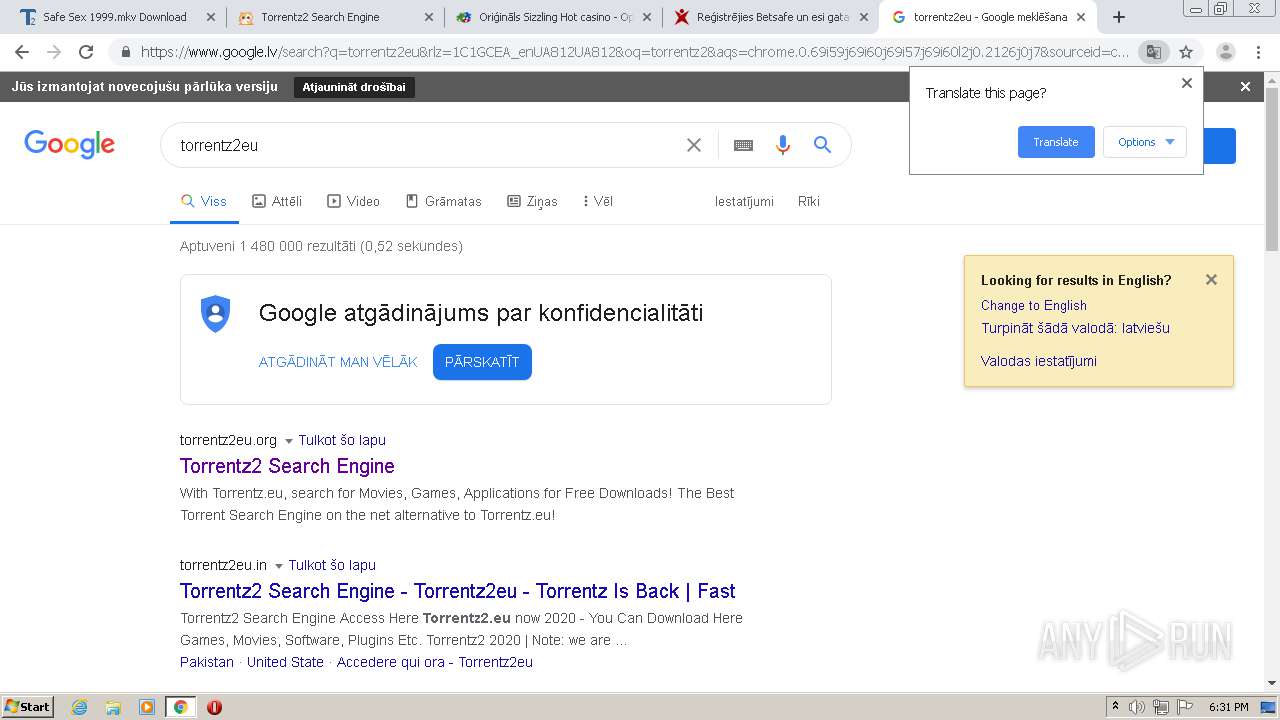
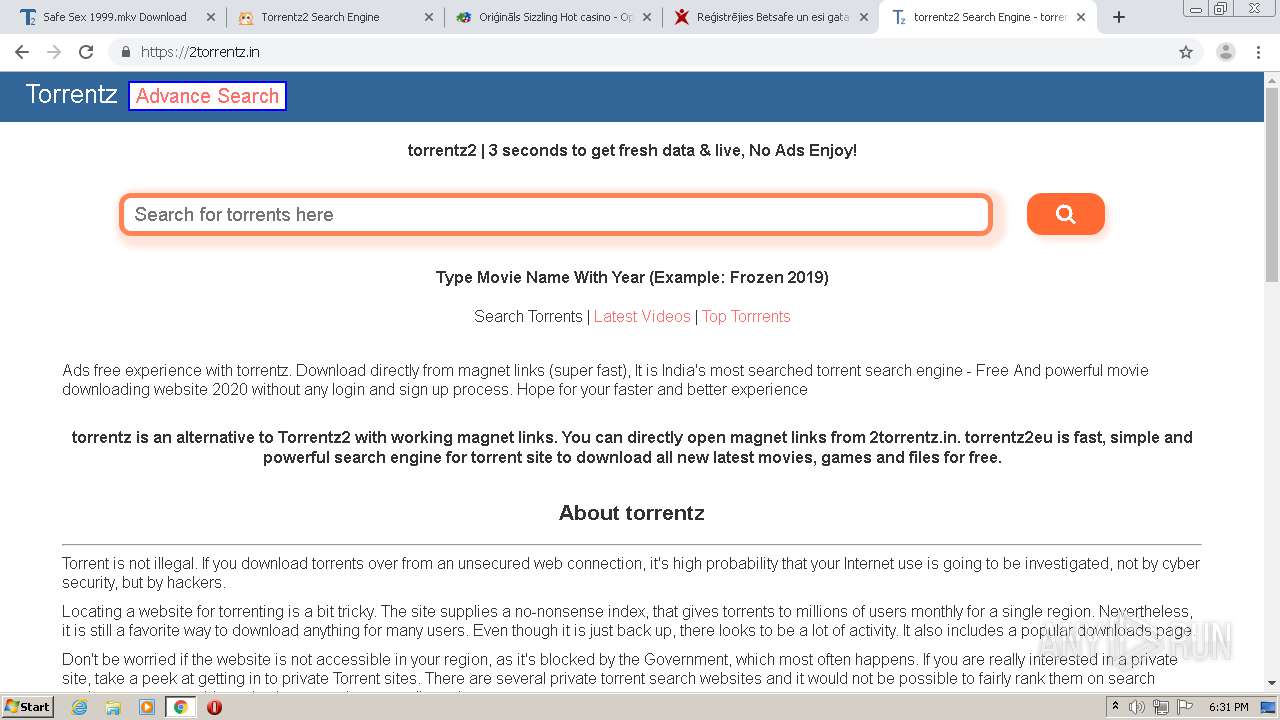
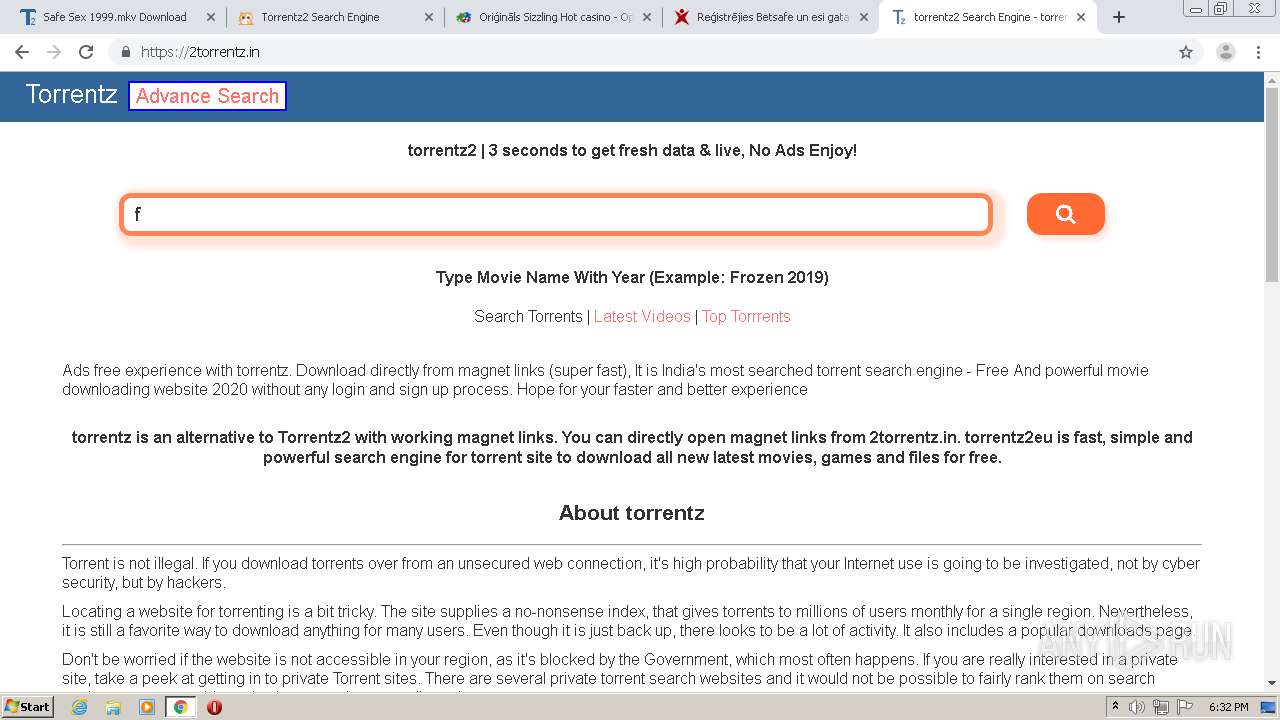
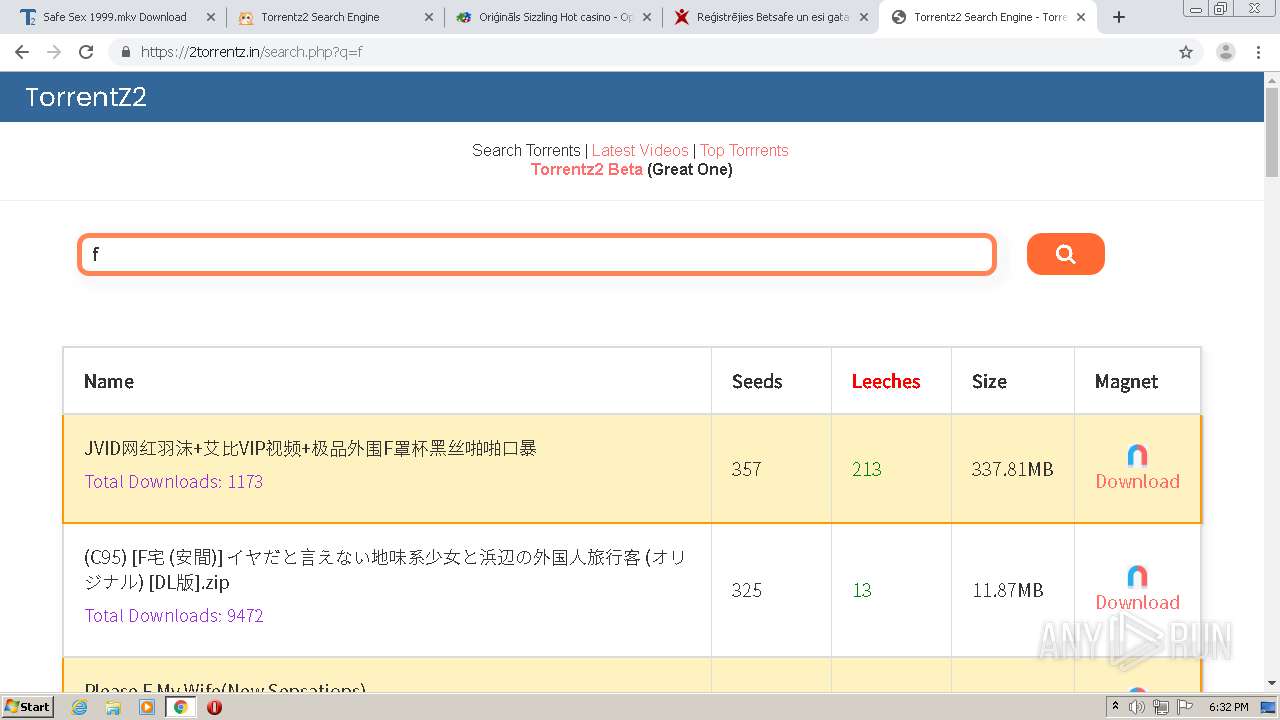
2460 | chrome.exe | GET | — | 172.67.211.249:80 | http://torrentz.eu/favicon.ico | US | — | — | suspicious |
2460 | chrome.exe | GET | 521 | 172.67.211.249:80 | http://torrentz.eu/ | US | html | 4.42 Kb | suspicious |
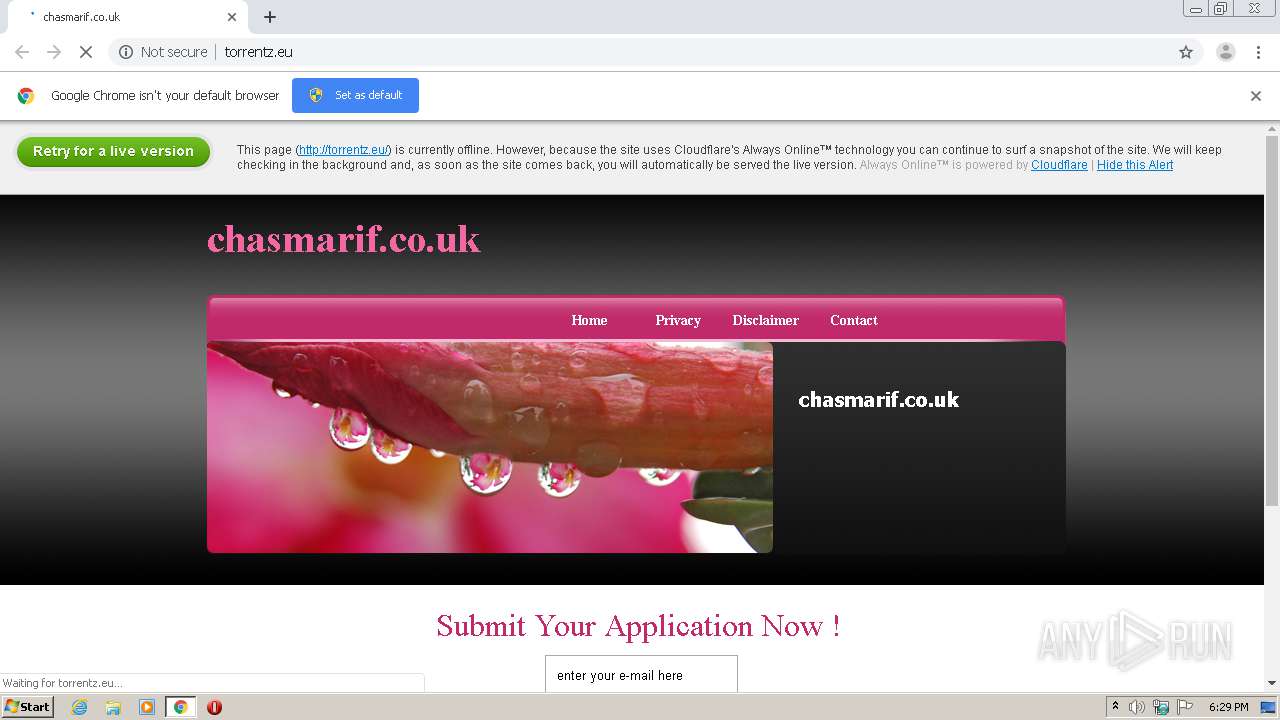
2460 | chrome.exe | GET | 200 | 172.67.211.249:80 | http://torrentz.eu/cdn-cgi/styles/cf.errors.css | US | text | 4.70 Kb | suspicious |
2460 | chrome.exe | GET | 200 | 172.67.211.249:80 | http://torrentz.eu/images/style.css | US | text | 1.51 Kb | suspicious |
2460 | chrome.exe | GET | 200 | 172.67.211.249:80 | http://torrentz.eu/images/templatemo_top_bg.jpg | US | image | 2.04 Kb | suspicious |
2460 | chrome.exe | GET | 200 | 172.67.211.249:80 | http://torrentz.eu/images/templatemo_middle_bg.jpg | US | image | 348 b | suspicious |
2460 | chrome.exe | GET | 404 | 172.67.211.249:80 | http://torrentz.eu/favicon.ico | US | html | 1.10 Kb | suspicious |
2460 | chrome.exe | GET | 200 | 172.67.211.249:80 | http://torrentz.eu/images/templatemo_header.jpg | US | image | 111 Kb | suspicious |
2460 | chrome.exe | GET | 200 | 172.67.211.249:80 | http://torrentz.eu/images/templatemo_menu_current.jpg | US | image | 1.20 Kb | suspicious |
2460 | chrome.exe | GET | 200 | 172.67.211.249:80 | http://torrentz.eu/ | US | html | 1.83 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2460 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 172.67.211.249:80 | torrentz.eu | — | US | suspicious |
2460 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2460 | chrome.exe | 216.58.206.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 172.217.21.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 172.217.18.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 159.148.69.142:80 | r3---sn-a5uoxu-gpme.gvt1.com | LATNET SERVISS Ltd. | LV | whitelisted |
2460 | chrome.exe | 172.217.18.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 159.148.69.143:80 | r4---sn-a5uoxu-gpme.gvt1.com | LATNET SERVISS Ltd. | LV | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
torrentz.eu |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
support.cloudflare.com |
| whitelisted |
www.cloudflare.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2460 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2460 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2460 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |