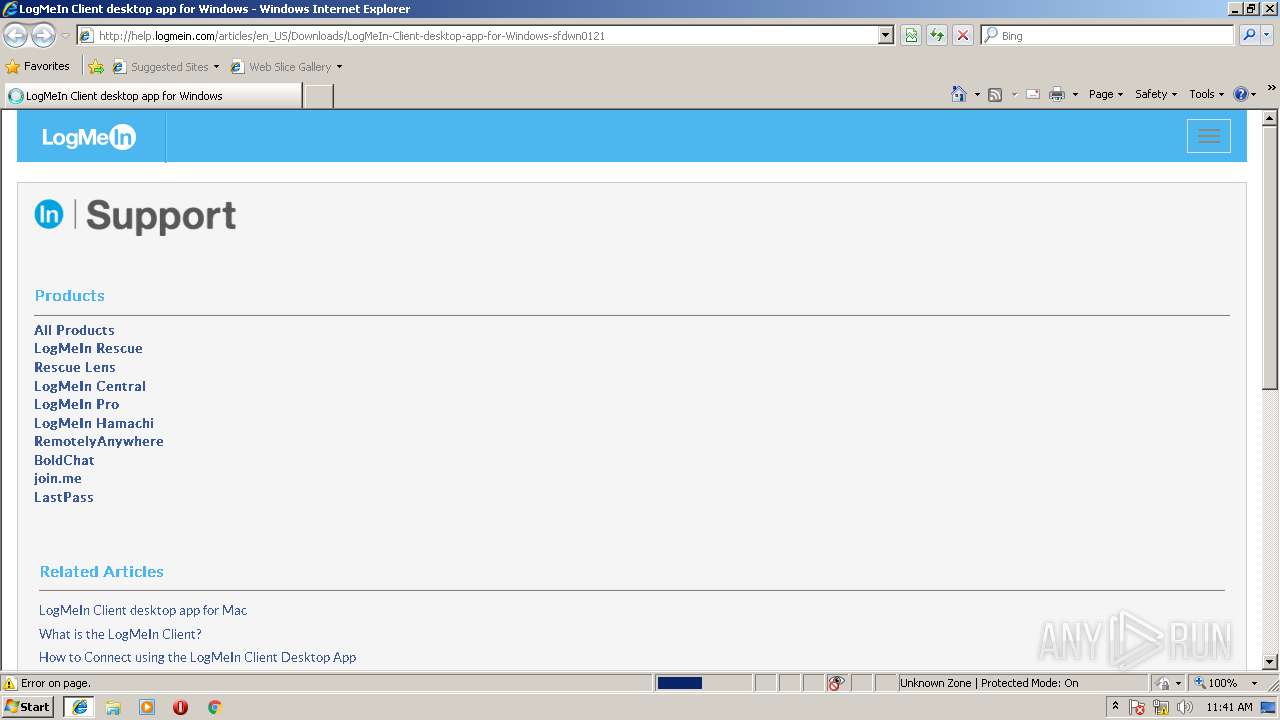
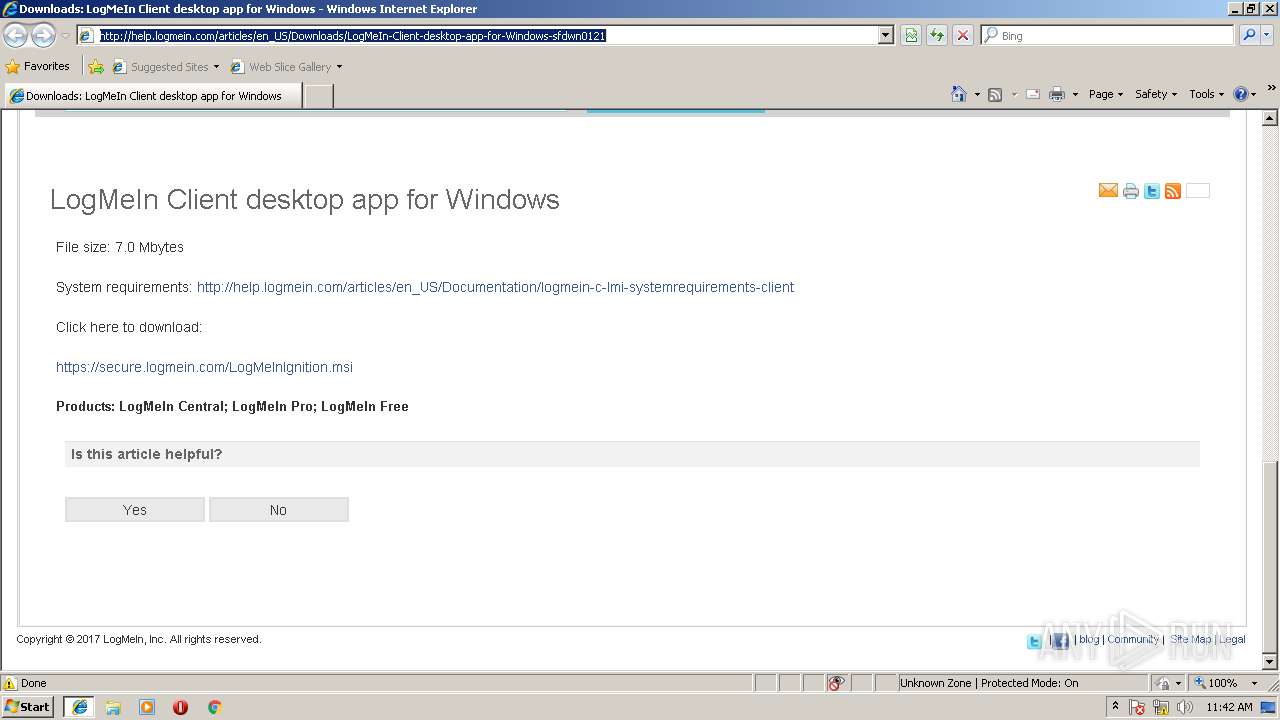
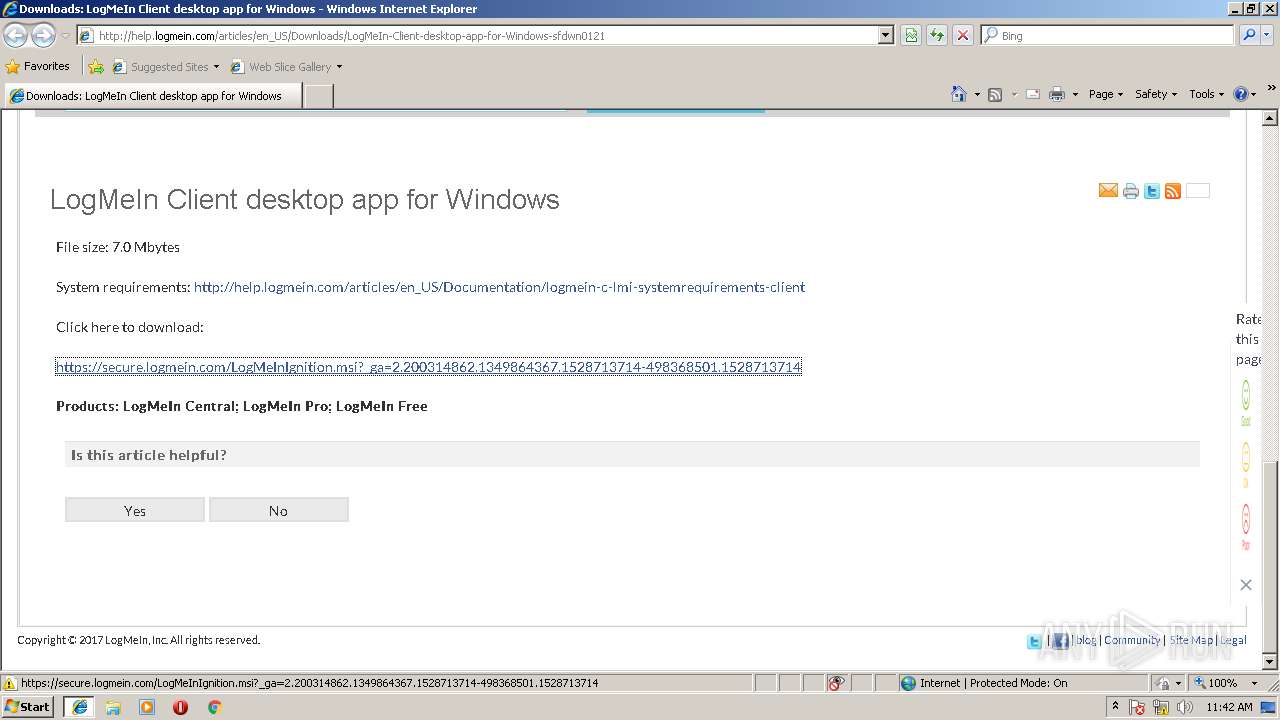
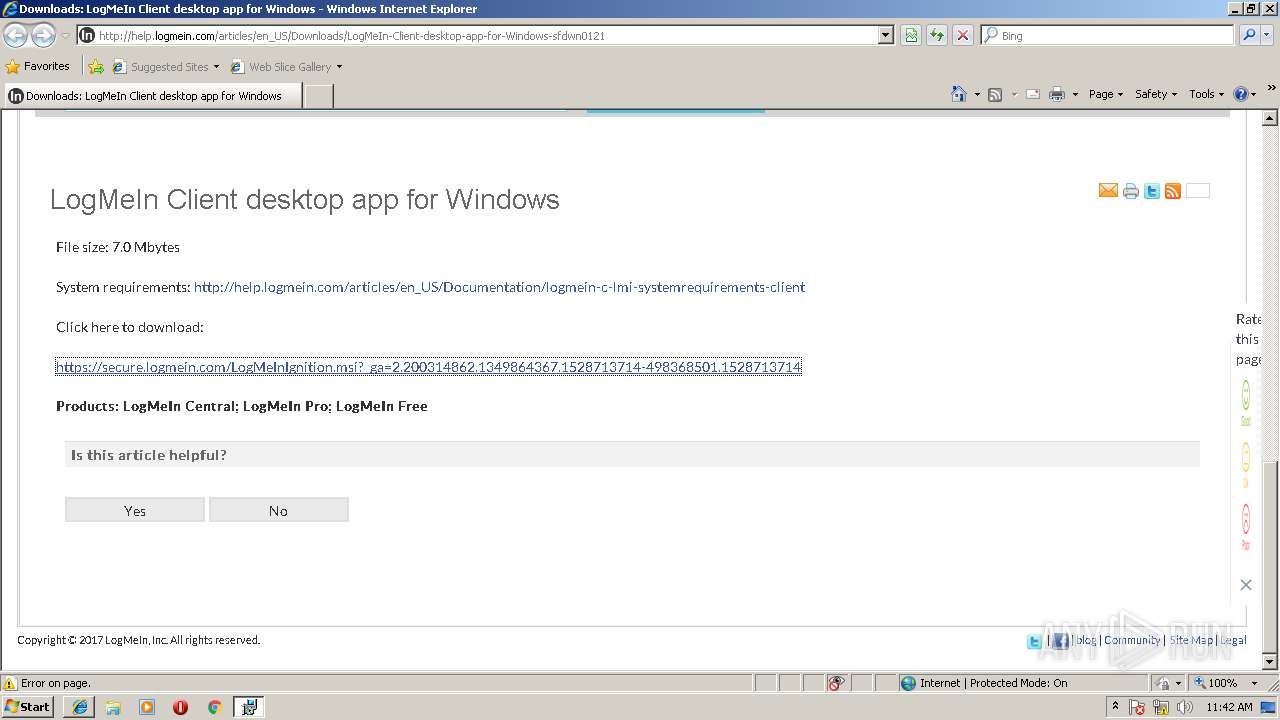
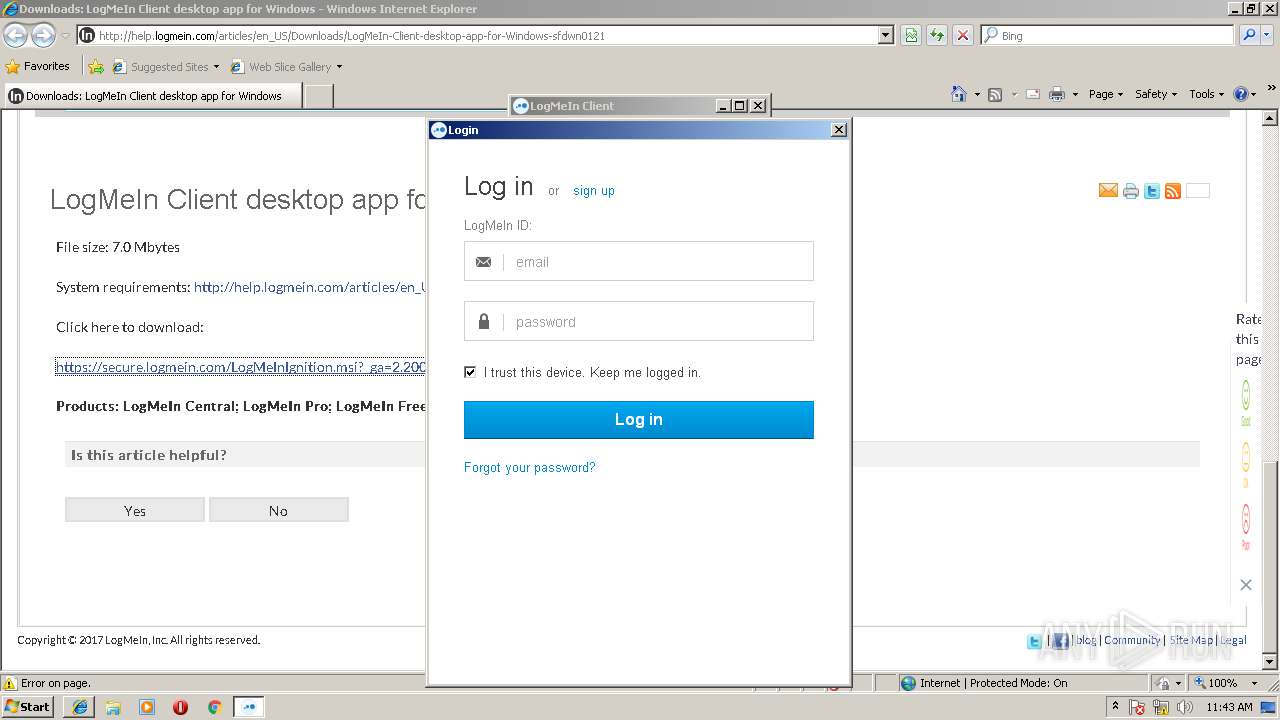
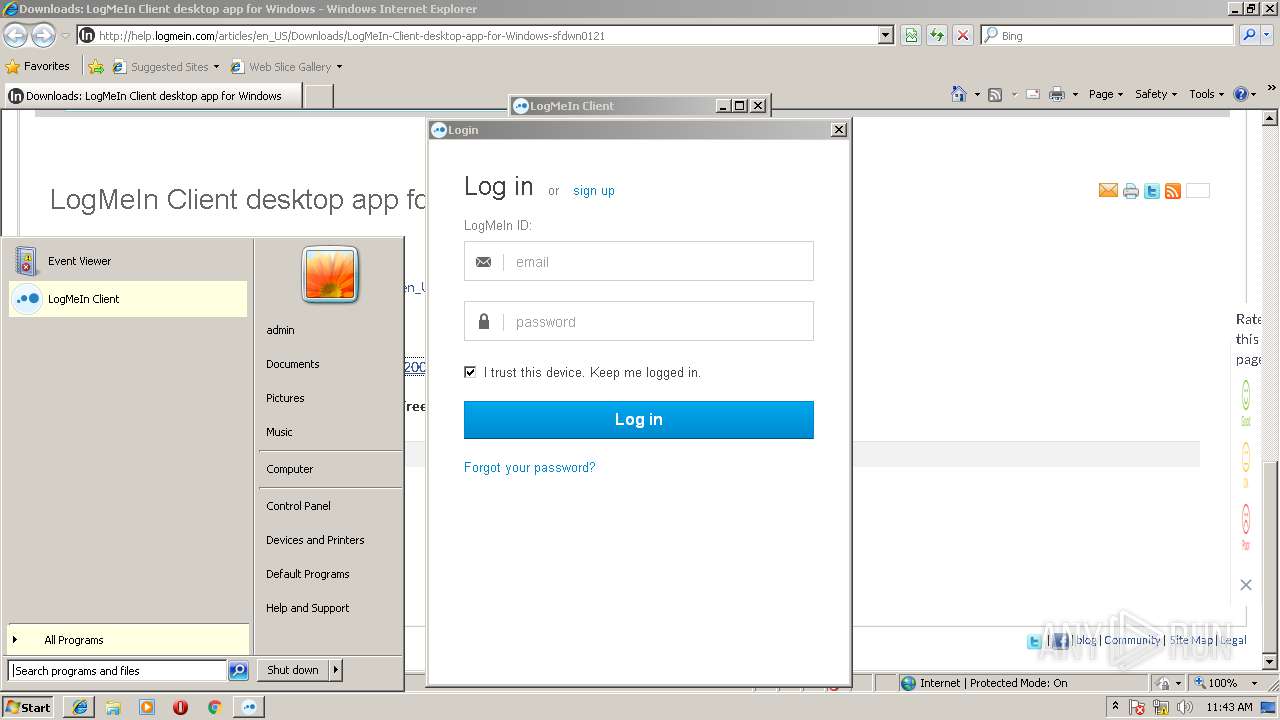
| URL: | http://help.logmein.com/articles/en_US/Downloads/LogMeIn-Client-desktop-app-for-Windows-sfdwn0121 |
| Full analysis: | https://app.any.run/tasks/607792f5-30c9-4f41-943e-0715c35b8272 |
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2018, 10:41:31 |
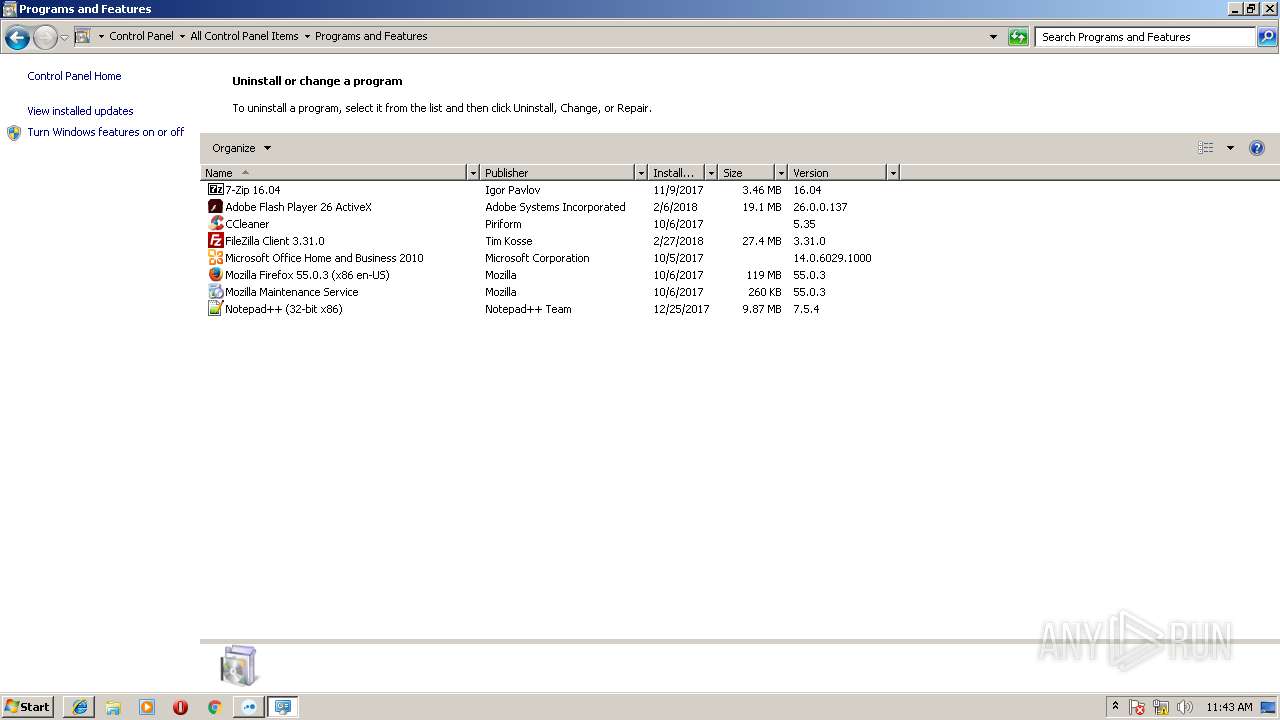
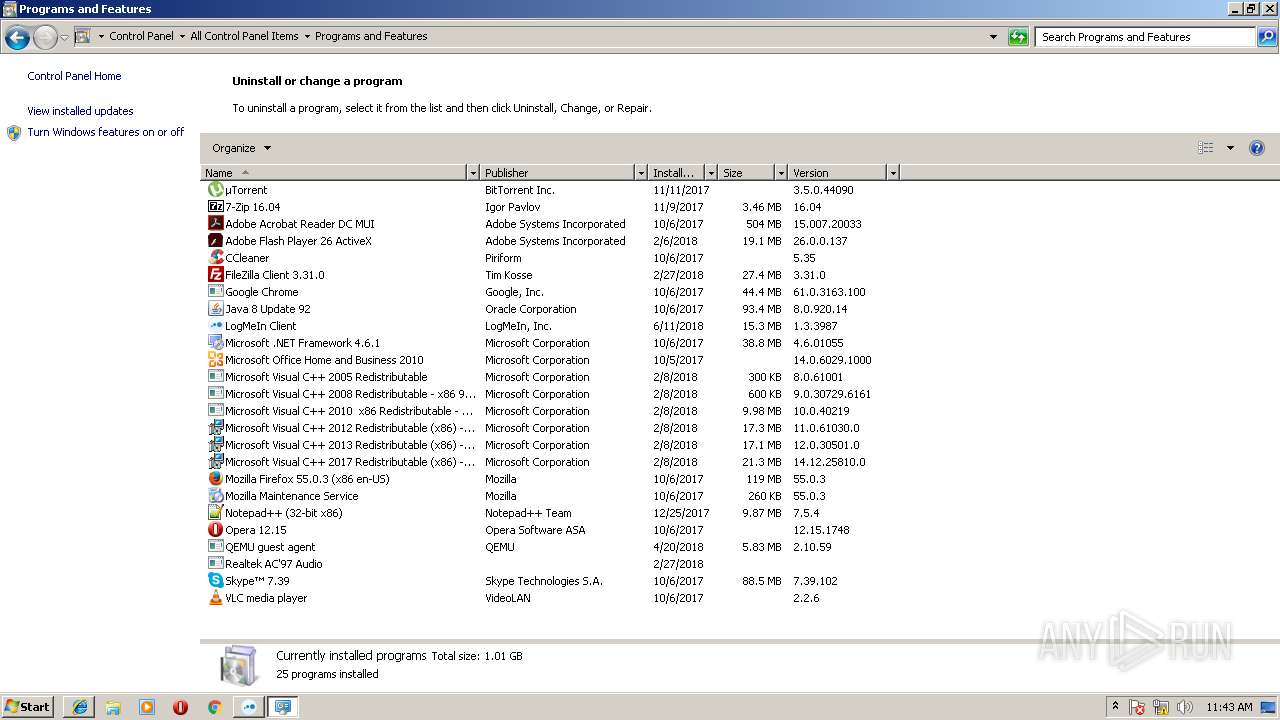
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3E689BF1B9637FC59409591CFEA2BAA4 |
| SHA1: | 70EBBF902526192A0E53204DB8E7A1E53058CFA7 |
| SHA256: | 14951A626A8A787879389B7FAA92C25E5325FC078AC08D8BEF79B9E80066D413 |
| SSDEEP: | 3:N1KWAvE0MSfBuWKAfG4JfgKcF+ALuBAWO0IVKCK/JU:CWGMSf/K74PcF+AafGKBU |
MALICIOUS
Loads dropped or rewritten executable
- LMIGuardianSvc.exe (PID: 1928)
- LMIGuardianSvc.exe (PID: 4052)
- LMIGuardianSvc.exe (PID: 3788)
- LMIGuardianSvc.exe (PID: 1008)
Application was dropped or rewritten from another process
- LMIGuardianSvc.exe (PID: 4052)
- LMIGuardianSvc.exe (PID: 1928)
- LMIGuardianSvc.exe (PID: 1008)
- LMIIgnition.exe (PID: 3740)
- LMIGuardianSvc.exe (PID: 3788)
SUSPICIOUS
Creates files in the user directory
- FlashUtil32_26_0_0_137_ActiveX.exe (PID: 820)
- msiexec.exe (PID: 184)
- LMIIgnition.exe (PID: 3740)
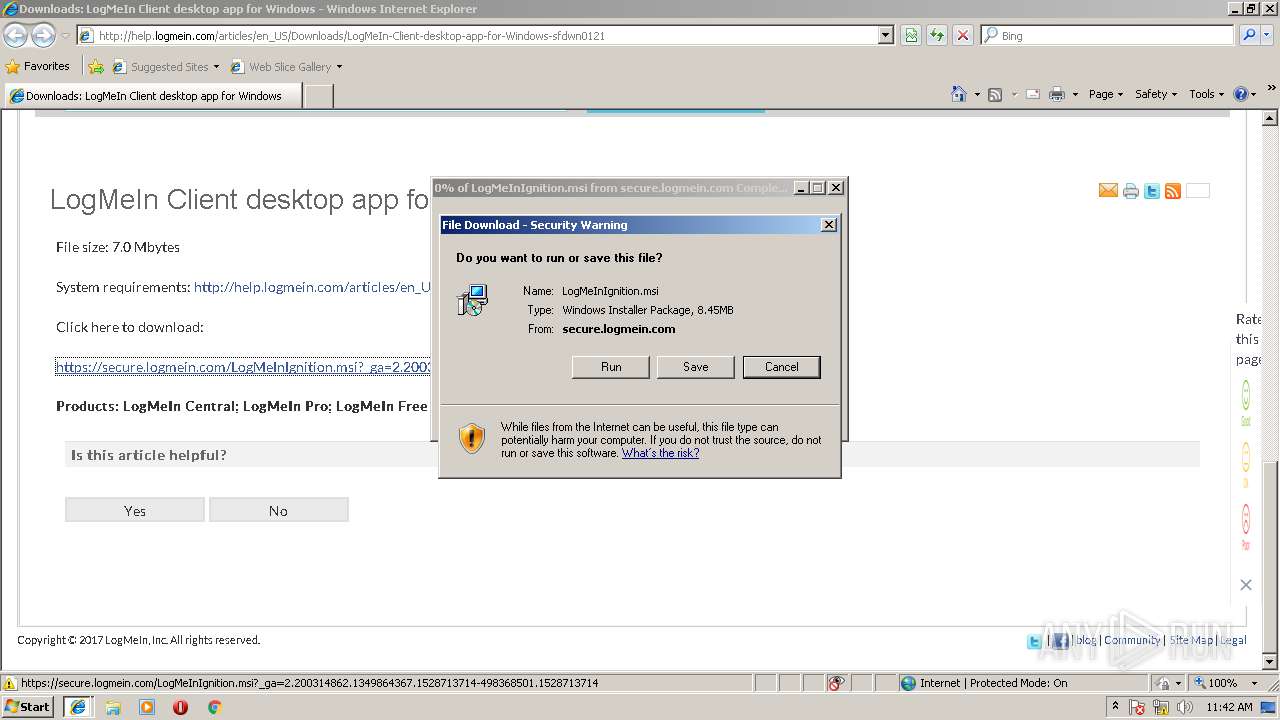
Executable content was dropped or overwritten
- msiexec.exe (PID: 184)
- msiexec.exe (PID: 3452)
Creates or modifies windows services
- LMIGuardianSvc.exe (PID: 3788)
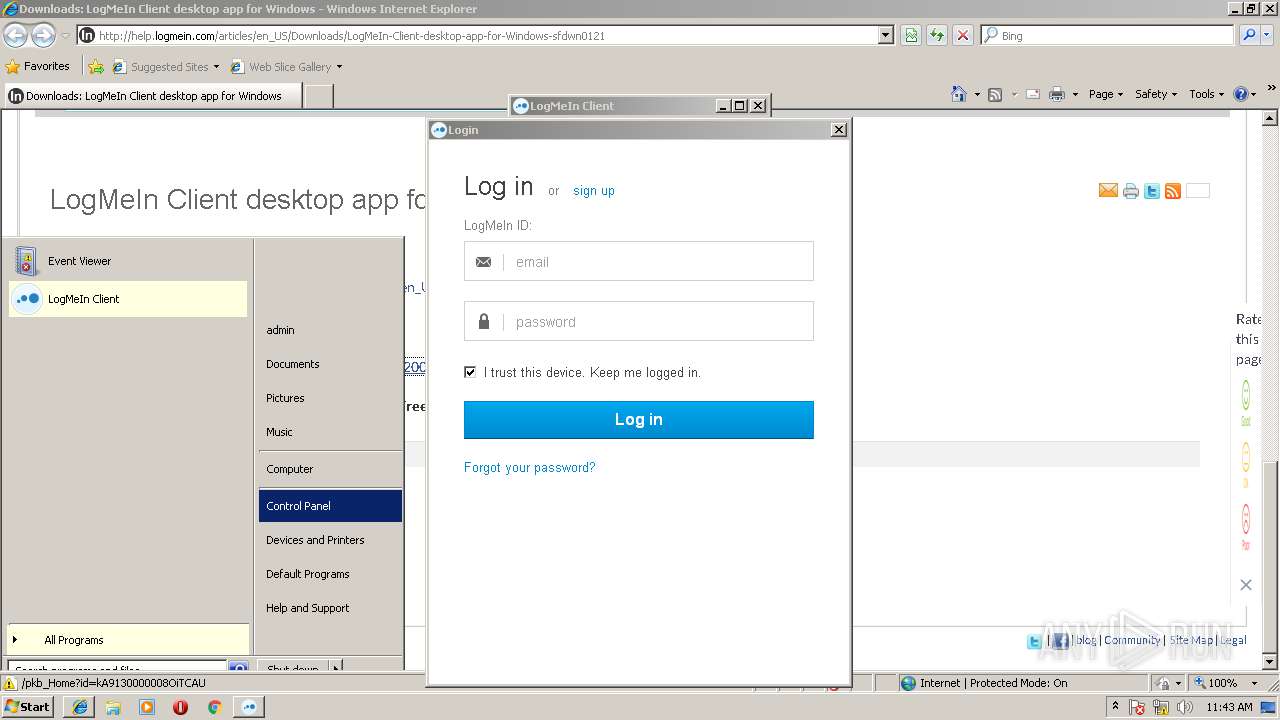
Changes IE settings (feature browser emulation)
- MsiExec.exe (PID: 2936)
Starts Microsoft Installer
- iexplore.exe (PID: 2844)
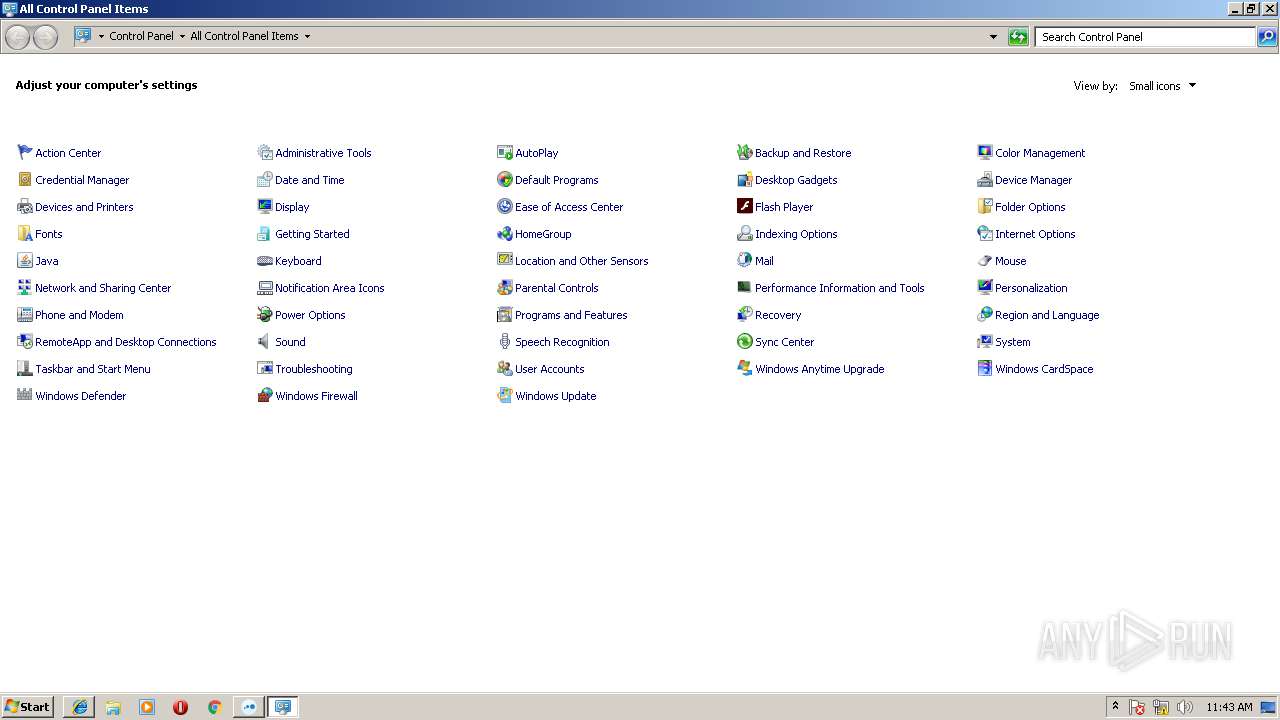
Creates files in the program directory
- LMIGuardianSvc.exe (PID: 1008)
Reads Internet Cache Settings
- rundll32.exe (PID: 3356)
- LMIIgnition.exe (PID: 3740)
Modifies the open verb of a shell class
- LMIIgnition.exe (PID: 3740)
Reads internet explorer settings
- LMIIgnition.exe (PID: 3740)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2844)
Reads settings of System Certificates
- iexplore.exe (PID: 3720)
Dropped object may contain URL's
- iexplore.exe (PID: 2844)
- iexplore.exe (PID: 3720)
- msiexec.exe (PID: 184)
- LMIIgnition.exe (PID: 3740)
Application launched itself
- iexplore.exe (PID: 2844)
- msiexec.exe (PID: 184)
Reads internet explorer settings
- iexplore.exe (PID: 3720)
- iexplore.exe (PID: 2868)
Reads Internet Cache Settings
- iexplore.exe (PID: 2844)
- iexplore.exe (PID: 3720)
- iexplore.exe (PID: 2868)
Creates files in the user directory
- iexplore.exe (PID: 3720)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2804)
- MsiExec.exe (PID: 2040)
- MsiExec.exe (PID: 2936)
Creates or modifies windows services
- msiexec.exe (PID: 184)
- vssvc.exe (PID: 3584)
- MsiExec.exe (PID: 2936)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3584)
Creates files in the program directory
- msiexec.exe (PID: 184)
Creates a software uninstall entry
- msiexec.exe (PID: 184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
16
Malicious processes
2
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
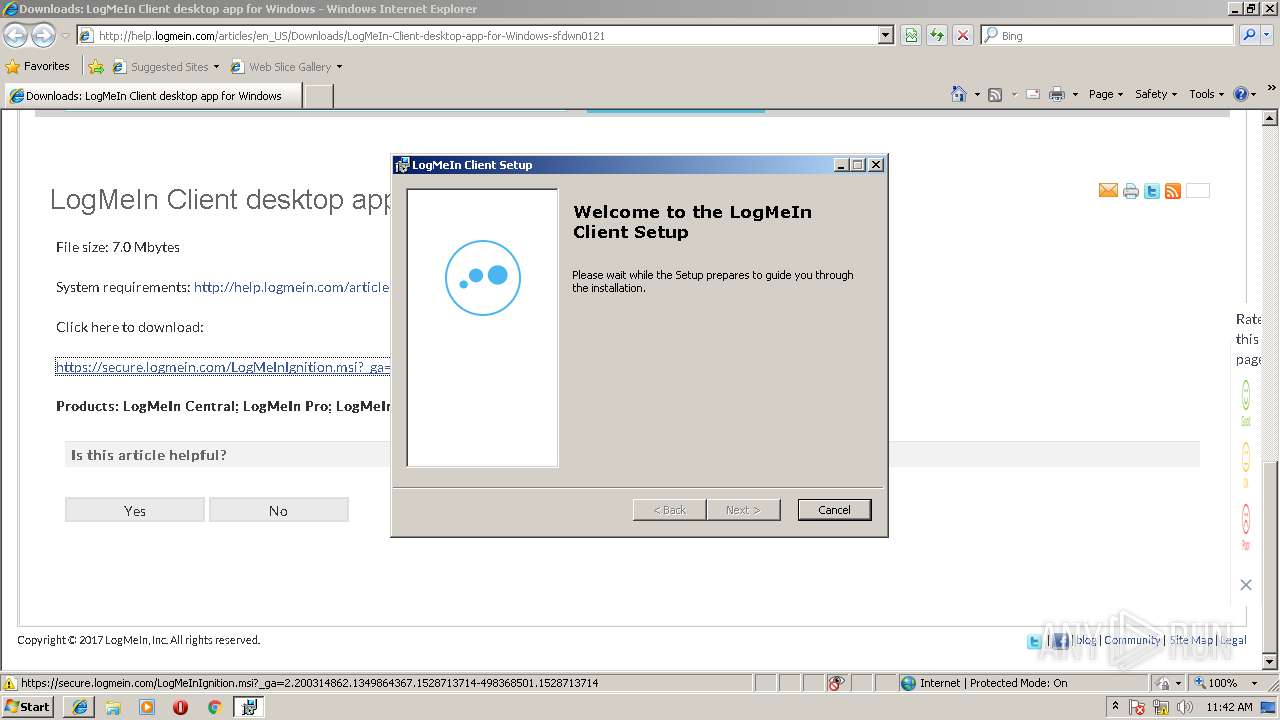
| 184 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 820 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_137_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_137_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,137 Modules
| |||||||||||||||
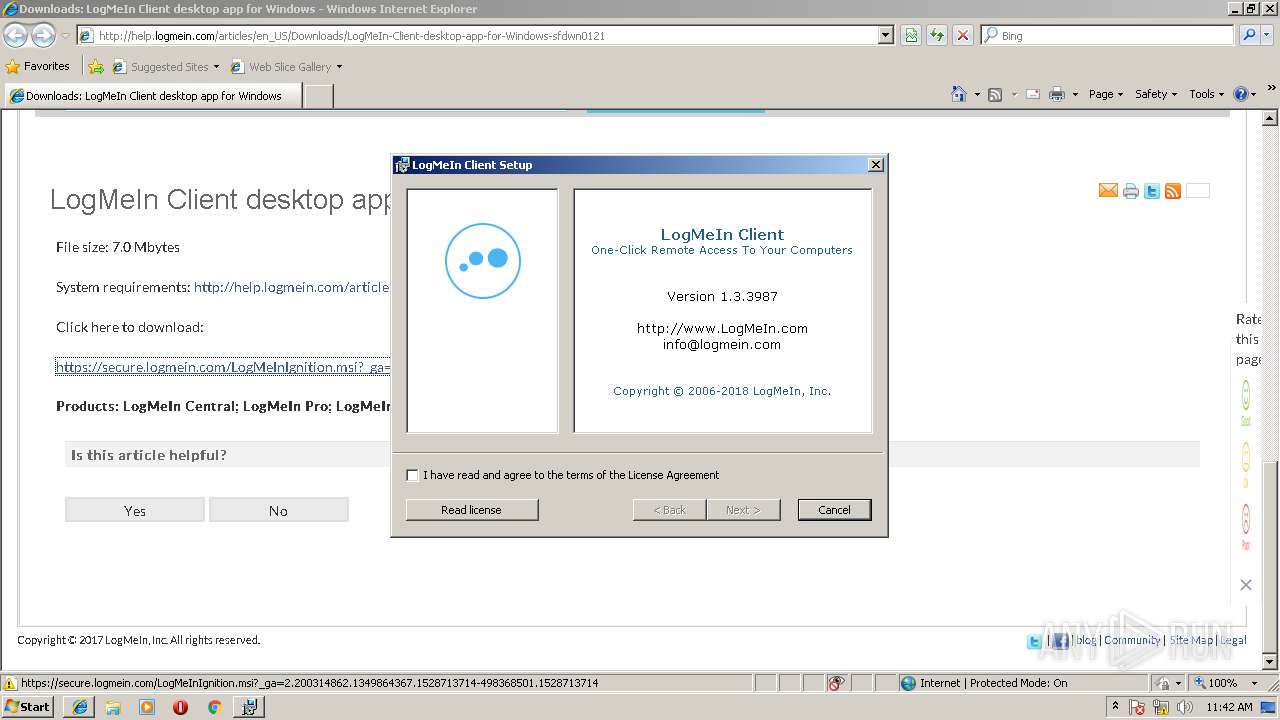
| 1008 | "C:\Program Files\LogMeIn Ignition\LMIGuardianSvc.exe" /escort 3740 | C:\Program Files\LogMeIn Ignition\LMIGuardianSvc.exe | — | LMIIgnition.exe | |||||||||||
User: admin Company: LogMeIn, Inc. Integrity Level: MEDIUM Description: LMIGuardianSvc Exit code: 0 Version: 10.1.1742 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\LogMeIn Ignition\LMIGuardianSvc.exe" -StartSvc | C:\Program Files\LogMeIn Ignition\LMIGuardianSvc.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: LogMeIn, Inc. Integrity Level: SYSTEM Description: LMIGuardianSvc Exit code: 0 Version: 10.1.1742 Modules
| |||||||||||||||
| 2040 | C:\Windows\system32\MsiExec.exe -Embedding AA278924F32B27AD51BBD781C9A8C796 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2804 | C:\Windows\system32\MsiExec.exe -Embedding D9DC96290E71760E99DE3C1CEEFCB4A0 C | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
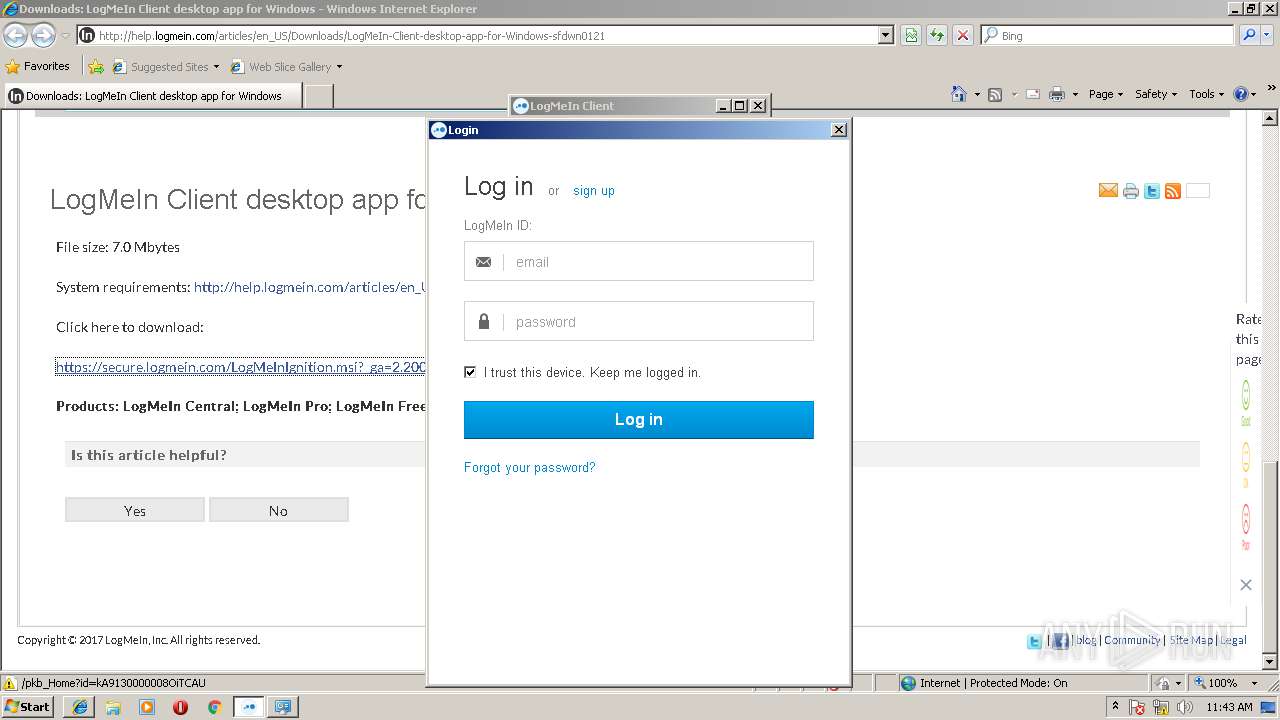
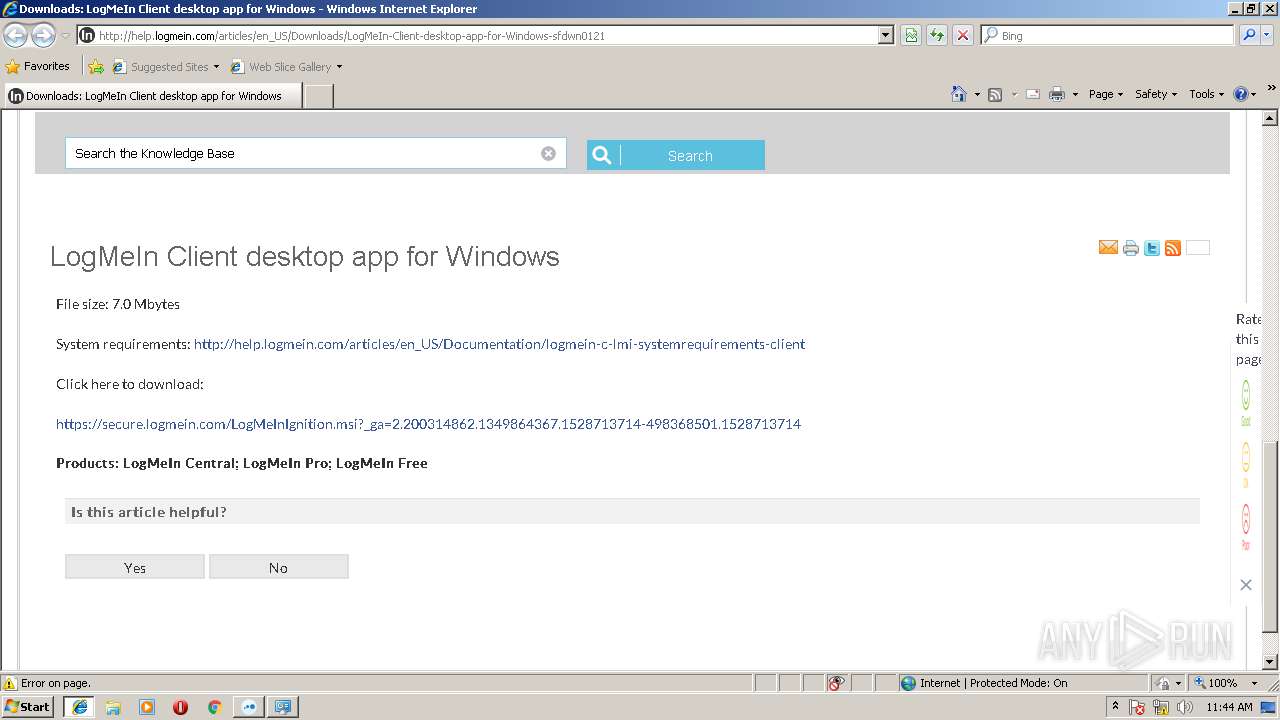
| 2844 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2868 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2844 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2936 | C:\Windows\system32\MsiExec.exe -Embedding 245490B27AA4DE275C49DC88D0228615 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3356 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | LMIIgnition.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 187
Read events
1 627
Write events
518
Delete events
42
Modification events
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006B000000010000000000000000000000000000000000000000000000400C35B347C7D301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A801640000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {09F28FB1-6D64-11E8-B27F-5254004AAD21} |
Value: 0 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 5 | |||
| (PID) Process: | (2844) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207060001000B000A0029002F002303 | |||
Executable files
12
Suspicious files
19
Text files
102
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF2FXMJU\LogMeIn-Client-desktop-app-for-Windows-sfdwn0121[1].txt | — | |
MD5:— | SHA256:— | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF2FXMJU\LogMeIn-Client-desktop-app-for-Windows-sfdwn0121[1].htm | html | |
MD5:— | SHA256:— | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\7W7KPD6U\functions[1].js | text | |
MD5:— | SHA256:— | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\7W7KPD6U\VFState[1].js | text | |
MD5:— | SHA256:— | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\7W7KPD6U\VFRemote[1].js | text | |
MD5:— | SHA256:— | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF2FXMJU\desktopAjax[1].js | html | |
MD5:6EC15500519EAB790AAB648FA1938FA9 | SHA256:2AE9EDDA35D97CBD39D1B0B16C784F37A09D4DA155969B0B6087D41C57579869 | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF2FXMJU\jquery-1.11.1.min[1].js | text | |
MD5:8101D596B2B8FA35FE3A634EA342D7C3 | SHA256:540BC6DEC1DD4B92EA4D3FB903F69EABF6D919AFD48F4E312B163C28CFF0F441 | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YP7LJCLE\bootstrap.min[1].css | text | |
MD5:385B964B68ACB68D23CB43A5218FADE9 | SHA256:B5FD723750763EBB731F9221E413E7D64D58D5192DC040E42292ED3DCCCCA732 | |||
| 3720 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\7W7KPD6U\en_US[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
49
DNS requests
26
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3720 | iexplore.exe | GET | 200 | 195.138.255.9:80 | http://help.logmein.com/jslibrary/jslabels/1528669334000/en_US.js | DE | text | 144 Kb | whitelisted |
3720 | iexplore.exe | GET | 200 | 195.138.255.9:80 | http://help.logmein.com/faces/a4j/g/3_3_3.Finalorg.ajax4jsf.javascript.AjaxScript | DE | text | 18.4 Kb | whitelisted |
3720 | iexplore.exe | GET | 200 | 195.138.255.9:80 | http://help.logmein.com/jslibrary/1526059412000/sfdc/VFState.js | DE | text | 1.81 Kb | whitelisted |
3720 | iexplore.exe | GET | 200 | 195.138.255.9:80 | http://help.logmein.com/jslibrary/1526059412000/sfdc/VFRemote.js | DE | text | 20.1 Kb | whitelisted |
3720 | iexplore.exe | GET | 200 | 195.138.255.9:80 | http://help.logmein.com/jslibrary/1526059412000/sfdc/Knowledge.js | DE | text | 32.6 Kb | whitelisted |
3720 | iexplore.exe | GET | 200 | 195.138.255.9:80 | http://help.logmein.com/static/111213/js/functions.js | DE | text | 10.0 Kb | whitelisted |
3720 | iexplore.exe | GET | 200 | 195.138.255.9:80 | http://help.logmein.com/jslibrary/1526059412000/sfdc/main.js | DE | text | 225 Kb | whitelisted |
3720 | iexplore.exe | GET | 200 | 195.138.255.9:80 | http://help.logmein.com/articles/en_US/Downloads/LogMeIn-Client-desktop-app-for-Windows-sfdwn0121 | DE | html | 124 Kb | whitelisted |
3720 | iexplore.exe | GET | 200 | 195.138.255.9:80 | http://help.logmein.com/resource/1420824334000/pkb_new_css/css/custom.css | DE | text | 1.78 Kb | whitelisted |
3720 | iexplore.exe | GET | 200 | 195.138.255.9:80 | http://help.logmein.com/sCSS/43.0/sprites/1527614538000/Theme3/default/ie8/knowledgeHome.css | DE | text | 2.24 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2844 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3720 | iexplore.exe | 195.138.255.9:80 | help.logmein.com | AS33891 Netzbetrieb GmbH | DE | suspicious |
3720 | iexplore.exe | 172.217.18.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3720 | iexplore.exe | 216.58.214.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3720 | iexplore.exe | 216.58.214.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3720 | iexplore.exe | 172.217.21.232:80 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3720 | iexplore.exe | 52.222.146.254:80 | www.surveygizmo.com | Amazon.com, Inc. | US | whitelisted |
3720 | iexplore.exe | 172.217.23.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3720 | iexplore.exe | 64.95.128.77:443 | secure.logmein.com | LogMeIn, Inc. | US | suspicious |
3720 | iexplore.exe | 216.58.214.42:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
help.logmein.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.surveygizmo.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
secure.logmein.com |
| suspicious |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
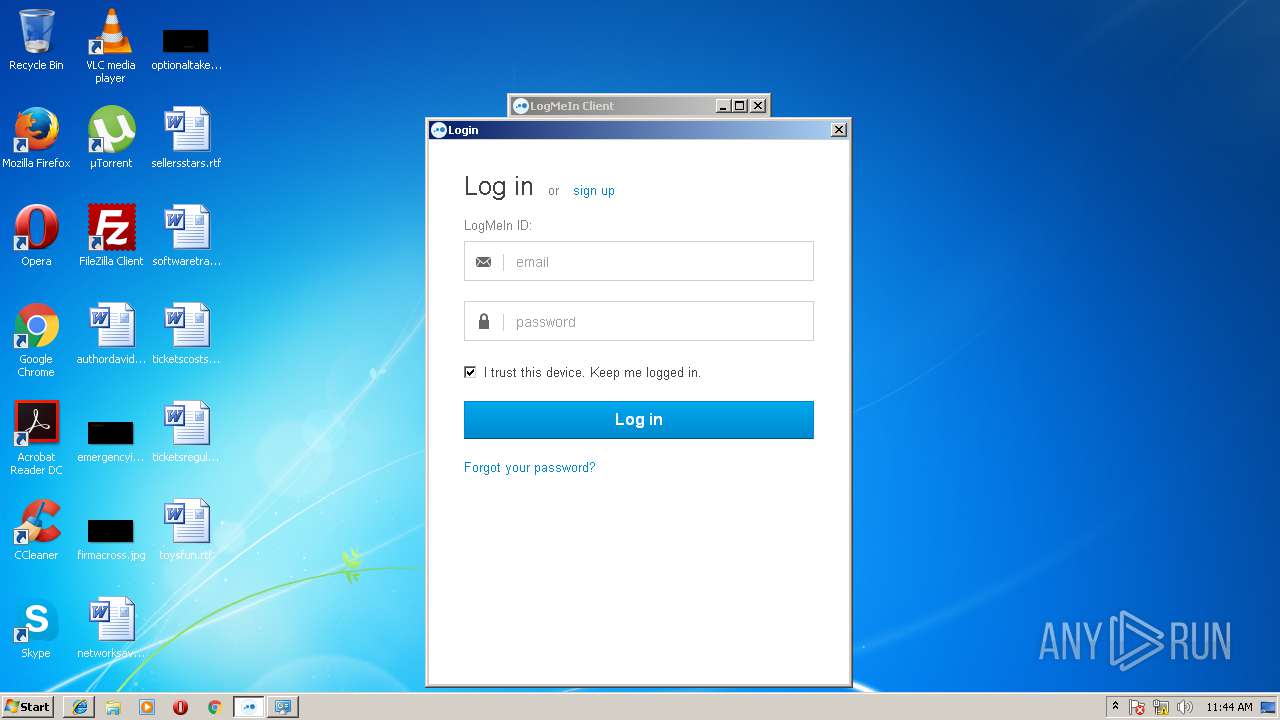
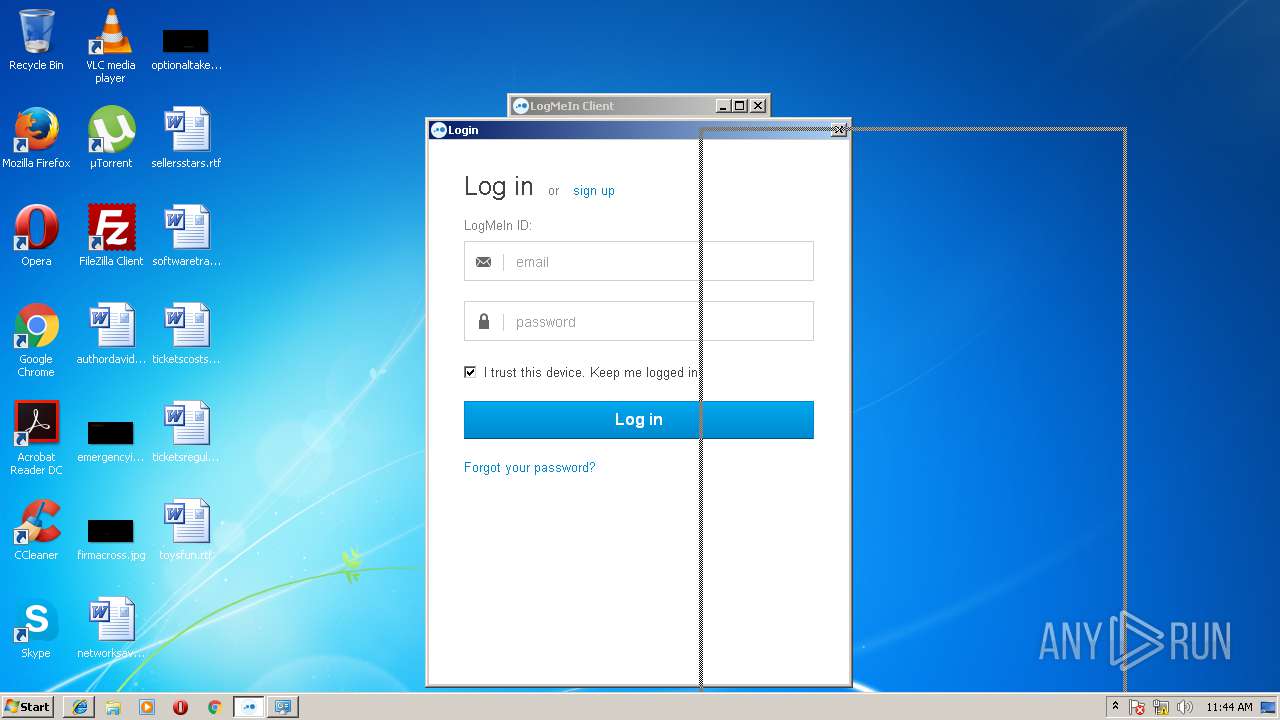
3740 | LMIIgnition.exe | Potential Corporate Privacy Violation | ET POLICY Logmein.com/Join.me SSL Remote Control Access |
3740 | LMIIgnition.exe | Potential Corporate Privacy Violation | ET POLICY Logmein.com/Join.me SSL Remote Control Access |
Process | Message |
|---|---|
MsiExec.exe | GetProperty() - valname: INSTALLEDVERSION |
MsiExec.exe | GetProperty() - valname: ProductVersion |
MsiExec.exe | GetProperty() - valname: INSTALLEDVERSION |
MsiExec.exe | GetProperty() - valname: ProductVersion |
LMIIgnition.exe | BROWSER notification: 0, url:https://asterisk.webservice.logmein.com/ws/api/internal/loginredirect.aspx?buildnumber=3987&ostype=658176&source=1&lang=en&hideautologin=0&autologinchecked=1, text: , 0,0, 0
|
LMIIgnition.exe | BROWSER notification: 2, url:, text: , 0,0, 0
|
LMIIgnition.exe | BROWSER notification: 6, url:, text: Looking up asterisk.webservice.logmein.com, 0,0, 0
|
LMIIgnition.exe | BROWSER notification: 3, url:, text: , 100,10000, 0
|
LMIIgnition.exe | BROWSER notification: 6, url:, text: Connecting to site 64.95.128.116, 0,0, 0
|
LMIIgnition.exe | BROWSER notification: 6, url:, text: Website found. Waiting for reply..., 0,0, 0
|