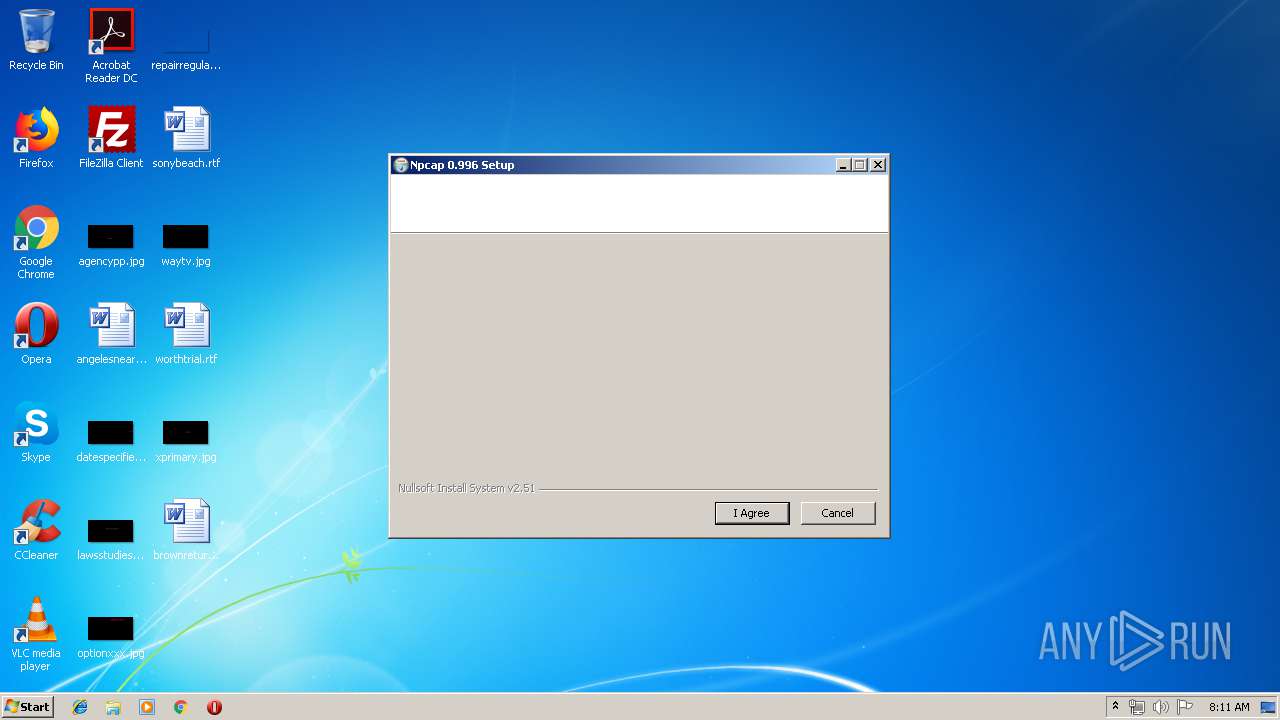
| File name: | npcap-0.996.exe |
| Full analysis: | https://app.any.run/tasks/ab5c4af4-bd8a-4230-b527-e9328b0eef79 |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2019, 07:11:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 402DA3B59AB6C1E239DAAA6BAF6F1997 |
| SHA1: | 5C7259A18BA69289B650FE38AE1BFA558834AC2D |
| SHA256: | 1493E5CDEFB5D7F9BAC8C38F0B1DC33AF02F3F54F8C536E5713ACDAEEDA0DAFD |
| SSDEEP: | 12288:KAC1KgYTjse6p+XklAZVbirgKyPz2WKwlT/yuxo9/l1GmuTXFr2drfYO2CNlcsyM:KAC1ez6p+XkQi0Pzj9/yvwVaYO2oaDj0 |
MALICIOUS
Loads dropped or rewritten executable
- npcap-0.996.exe (PID: 2252)
Application was dropped or rewritten from another process
- ns41E6.tmp (PID: 2032)
- NPFInstall.exe (PID: 948)
- ns46EB.tmp (PID: 3248)
- ns44B7.tmp (PID: 3028)
- NPFInstall.exe (PID: 1768)
- ns434F.tmp (PID: 2728)
- ns4600.tmp (PID: 1100)
- NPFInstall.exe (PID: 3900)
- ns88C8.tmp (PID: 1344)
- NPFInstall.exe (PID: 2976)
- nsA25C.tmp (PID: 2912)
Changes settings of System certificates
- certutil.exe (PID: 3652)
- certutil.exe (PID: 3540)
Loads the Task Scheduler COM API
- SCHTASKS.EXE (PID: 1424)
Uses Task Scheduler to run other applications
- nsA25C.tmp (PID: 2912)
SUSPICIOUS
Creates files in the Windows directory
- certutil.exe (PID: 3652)
- NPFInstall.exe (PID: 3900)
- certutil.exe (PID: 3540)
- pnputil.exe (PID: 3968)
- npcap-0.996.exe (PID: 2252)
- NPFInstall.exe (PID: 948)
- DrvInst.exe (PID: 1064)
- DrvInst.exe (PID: 3744)
Creates files in the program directory
- NPFInstall.exe (PID: 1768)
- npcap-0.996.exe (PID: 2252)
- NPFInstall.exe (PID: 2976)
Removes files from Windows directory
- certutil.exe (PID: 3652)
- certutil.exe (PID: 3540)
- DrvInst.exe (PID: 1064)
- DrvInst.exe (PID: 3744)
- NPFInstall.exe (PID: 948)
Executable content was dropped or overwritten
- npcap-0.996.exe (PID: 2252)
- DrvInst.exe (PID: 1064)
- NPFInstall.exe (PID: 948)
- DrvInst.exe (PID: 3744)
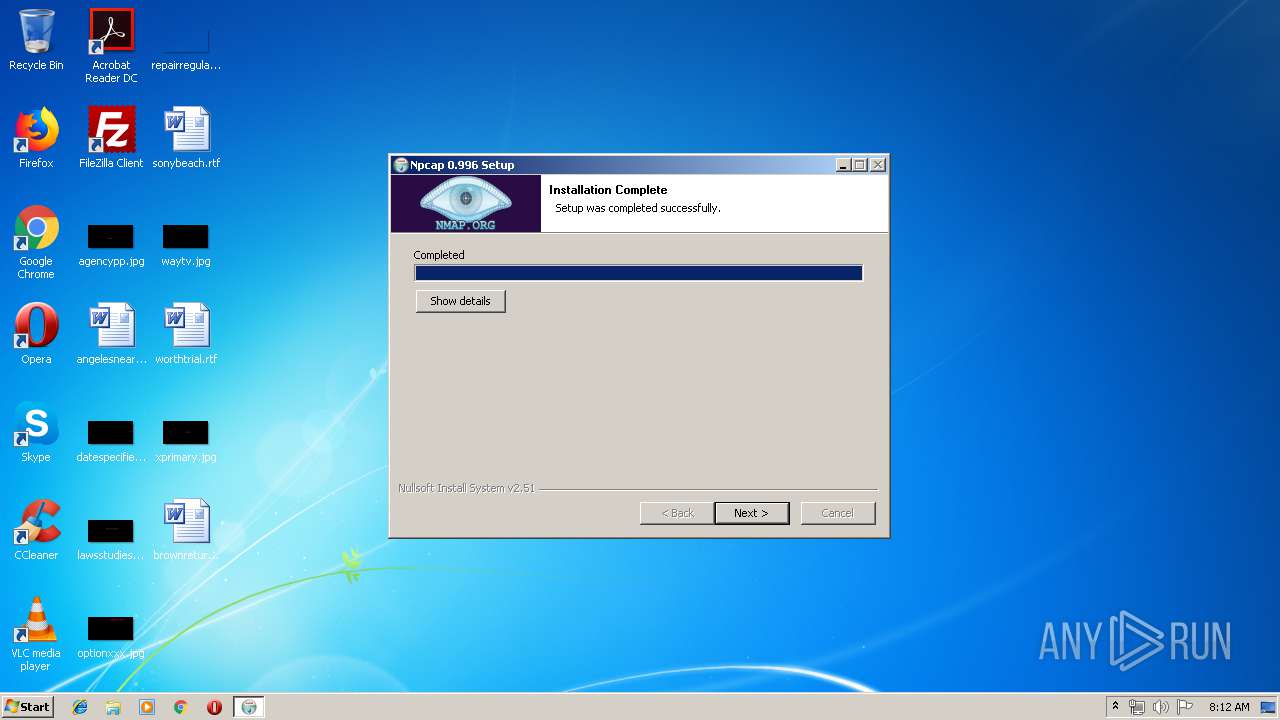
Creates a software uninstall entry
- npcap-0.996.exe (PID: 2252)
Starts application with an unusual extension
- npcap-0.996.exe (PID: 2252)
Creates files in the driver directory
- DrvInst.exe (PID: 1064)
- NPFInstall.exe (PID: 948)
- DrvInst.exe (PID: 3744)
Searches for installed software
- DrvInst.exe (PID: 1064)
Executed as Windows Service
- vssvc.exe (PID: 2480)
Executed via COM
- DrvInst.exe (PID: 3448)
- DrvInst.exe (PID: 3744)
- DrvInst.exe (PID: 1064)
Creates or modifies windows services
- npcap-0.996.exe (PID: 2252)
- DrvInst.exe (PID: 3744)
INFO
Changes settings of System certificates
- DrvInst.exe (PID: 1064)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 1064)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:02 05:21:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 125440 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x36e7 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.996.611 |
| ProductVersionNumber: | 5.0.996.611 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
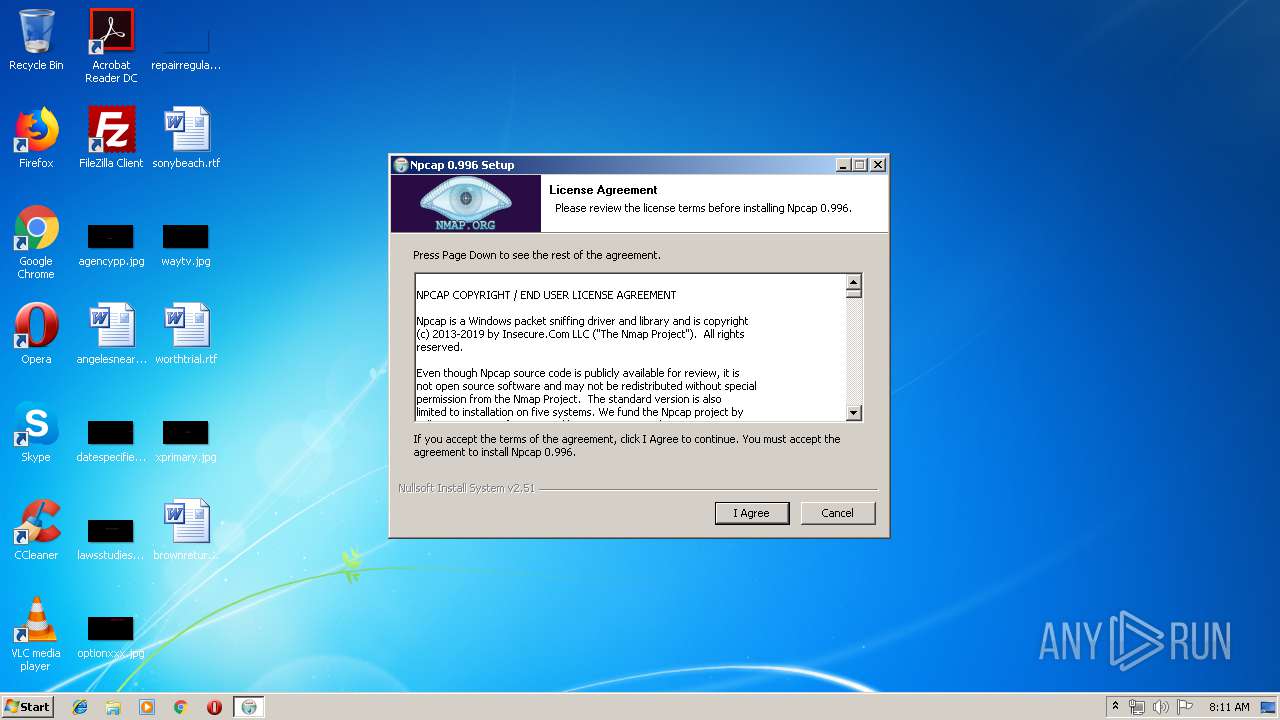
| FileDescription: | Npcap 0.996 installer |
| FileVersion: | 0.996 |
| LegalCopyright: | Copyright 2016 Insecure.Com LLC ("The Nmap Project") |
| ProductName: | Npcap |
| ProductVersion: | 0.996 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Apr-2016 03:21:39 |
| Detected languages: |
|
| FileDescription: | Npcap 0.996 installer |
| FileVersion: | 0.996 |
| LegalCopyright: | Copyright 2016 Insecure.Com LLC ("The Nmap Project") |
| ProductName: | Npcap |
| ProductVersion: | 0.996 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 02-Apr-2016 03:21:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000063CD | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4551 |
.rdata | 0x00008000 | 0x000011E2 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.30938 |
.data | 0x0000A000 | 0x0001C4F8 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96324 |
.ndata | 0x00027000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00037000 | 0x000044E0 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.87015 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21417 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
64
Monitored processes
21
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | "C:\Users\admin\AppData\Local\Temp\npcap-0.996.exe" | C:\Users\admin\AppData\Local\Temp\npcap-0.996.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Npcap 0.996 installer Exit code: 3221226540 Version: 0.996 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Npcap\NPFInstall.exe" -n -i | C:\Program Files\Npcap\NPFInstall.exe | ns46EB.tmp | ||||||||||||
User: admin Company: Insecure.Com LLC. Integrity Level: HIGH Description: A LWF & WFP driver installation tool Exit code: 0 Version: 0.996 Modules
| |||||||||||||||
| 1064 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{26b22dac-dedc-28de-bede-da3920b3b36f}\NPCAP.inf" "0" "605306be3" "00000544" "WinSta0\Default" "0000032C" "208" "C:\Program Files\Npcap" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1100 | "C:\Users\admin\AppData\Local\Temp\nsw10F2.tmp\ns4600.tmp" "C:\Program Files\Npcap\NPFInstall.exe" -n -iw | C:\Users\admin\AppData\Local\Temp\nsw10F2.tmp\ns4600.tmp | — | npcap-0.996.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1344 | "C:\Users\admin\AppData\Local\Temp\nsw10F2.tmp\ns88C8.tmp" "C:\Program Files\Npcap\NPFInstall.exe" -n -il | C:\Users\admin\AppData\Local\Temp\nsw10F2.tmp\ns88C8.tmp | — | npcap-0.996.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1424 | SCHTASKS.EXE /Create /F /RU SYSTEM /SC ONSTART /TN npcapwatchdog /TR "'C:\Program Files\Npcap\CheckStatus.bat'" /NP | C:\Windows\system32\SCHTASKS.EXE | — | nsA25C.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Npcap\NPFInstall.exe" -n -c | C:\Program Files\Npcap\NPFInstall.exe | — | ns44B7.tmp | |||||||||||
User: admin Company: Insecure.Com LLC. Integrity Level: HIGH Description: A LWF & WFP driver installation tool Exit code: 0 Version: 0.996 Modules
| |||||||||||||||
| 2032 | "C:\Users\admin\AppData\Local\Temp\nsw10F2.tmp\ns41E6.tmp" certutil -addstore -f "TrustedPublisher" "C:\Users\admin\AppData\Local\Temp\nsw10F2.tmp\Insecure-SHA1.cer" | C:\Users\admin\AppData\Local\Temp\nsw10F2.tmp\ns41E6.tmp | — | npcap-0.996.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2252 | "C:\Users\admin\AppData\Local\Temp\npcap-0.996.exe" | C:\Users\admin\AppData\Local\Temp\npcap-0.996.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Npcap 0.996 installer Exit code: 0 Version: 0.996 Modules
| |||||||||||||||
| 2480 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 477
Read events
815
Write events
615
Delete events
47
Modification events
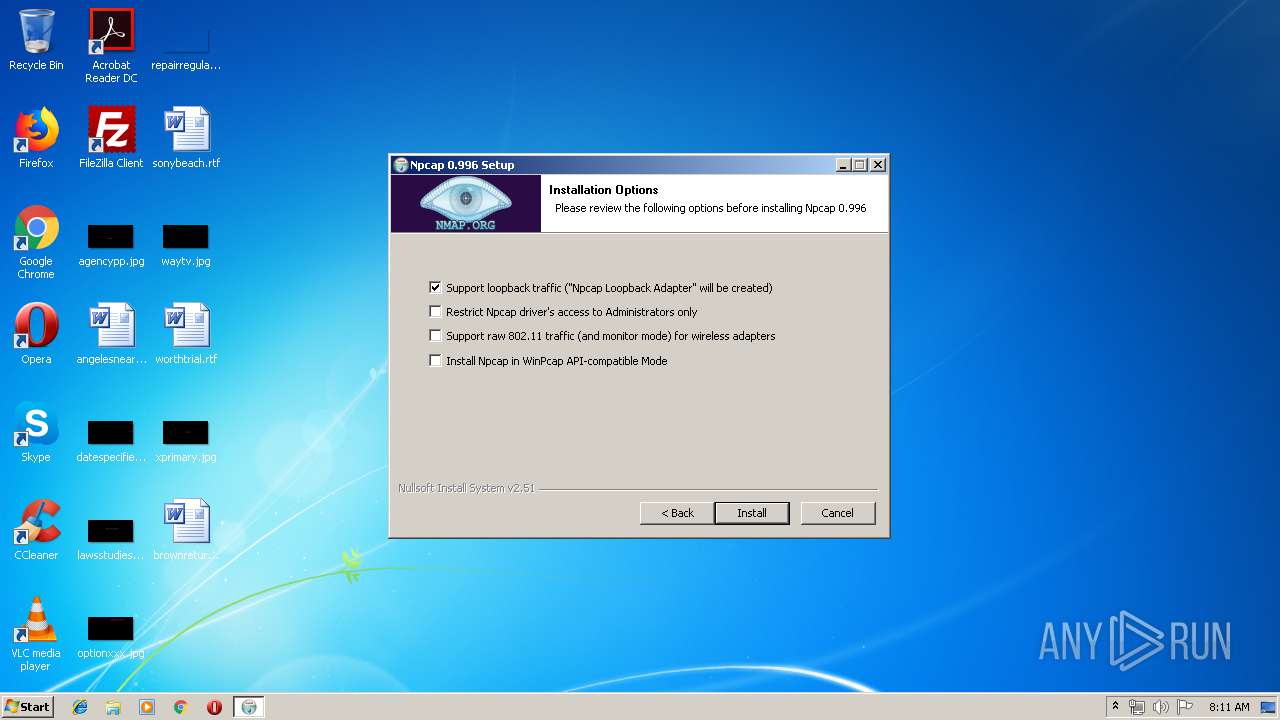
| (PID) Process: | (2252) npcap-0.996.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Npcap |
| Operation: | write | Name: | AdminOnly |
Value: 0 | |||
| (PID) Process: | (2252) npcap-0.996.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Npcap |
| Operation: | write | Name: | WinPcapCompatible |
Value: 0 | |||
| (PID) Process: | (2252) npcap-0.996.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Npcap |
| Operation: | write | Name: | |
Value: C:\Program Files\Npcap | |||
| (PID) Process: | (2252) npcap-0.996.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Npcap\uninstall.exe" | |||
| (PID) Process: | (2252) npcap-0.996.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\Npcap\uninstall.exe" /S | |||
| (PID) Process: | (2252) npcap-0.996.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Npcap\uninstall.exe | |||
| (PID) Process: | (2252) npcap-0.996.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NpcapInst |
| Operation: | write | Name: | UninstallPath |
Value: C:\Program Files\Npcap | |||
| (PID) Process: | (3652) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\EC2AE51775F3252541B266C40528DAA77BAA072F |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000EC2AE51775F3252541B266C40528DAA77BAA072F2000000001000000F6050000308205F2308204DAA0030201020210033B0A4DC1797373E6EFEC07FC63BA34300D06092A864886F70D01010B0500306C310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312B302906035504031322446967694365727420455620436F6465205369676E696E6720434120285348413229301E170D3136313130333030303030305A170D3139313130373132303030305A30820100311D301B060355040F0C1450726976617465204F7267616E697A6174696F6E31133011060B2B0601040182373C02010313025553311B3019060B2B0601040182373C020102130A43616C69666F726E6961311530130603550405130C323030303130333130303133311C301A06035504090C1331313320436865727279205374202331333337310E300C060355041113053938313034310B3009060355040613025553311330110603550408130A57617368696E67746F6E3110300E0603550407130753656174746C6531193017060355040A1310496E7365637572652E436F6D204C4C433119301706035504031310496E7365637572652E436F6D204C4C4330820122300D06092A864886F70D01010105000382010F003082010A0282010100A0089EFFAA2F88551E4CF8AFF76D6F17E5E7B2D06C53D2215E627343BB434641B40057EE3ED721F03FDAE2FFA5C68BD62C7F31B40E3938AA9FA99C2918047742392D60D9355596DF4569A71C33D7C5243D0F2A140CD00C691D6CF5E0D17CDF831F7BF4C07D2A394583C84F3440B4364622EC050D140D38A5C30A99EF73418B215C09B59513BA0A617CF0CD0AD833A1F0D92E483E1C525A380ECC208763EC6E596E65137C95C8C01350D7CE32729E1499DE5CECBEF1E42700EA19AEEBB504F60B05D877E71538B5E4BCB23E950929668BE0F0CB5DC4E7C29FF5E821FF803F5FDD5F406DC133F674DF9FE7C7EBC1A43DC36F433BEC55B0987953A2B4B8A08F9B390203010001A38201F8308201F4301F0603551D230418301680148FE87EF06D326A000523C770976A3A90FF6BEAD4301D0603551D0E041604142007C07AE17734CD83F10275B3B5EE932A11D54530350603551D11042E302CA02A06082B06010505070803A01E301C0C1A55532D43414C49464F524E49412D323030303130333130303133300E0603551D0F0101FF04040302078030130603551D25040C300A06082B06010505070303307B0603551D1F047430723037A035A0338631687474703A2F2F63726C332E64696769636572742E636F6D2F4556436F64655369676E696E67534841322D67312E63726C3037A035A0338631687474703A2F2F63726C342E64696769636572742E636F6D2F4556436F64655369676E696E67534841322D67312E63726C304B0603551D2004443042303706096086480186FD6C0302302A302806082B06010505070201161C68747470733A2F2F7777772E64696769636572742E636F6D2F4350533007060567810C0103307E06082B0601050507010104723070302406082B060105050730018618687474703A2F2F6F6373702E64696769636572742E636F6D304806082B06010505073002863C687474703A2F2F636163657274732E64696769636572742E636F6D2F44696769436572744556436F64655369676E696E6743412D534841322E637274300C0603551D130101FF04023000300D06092A864886F70D01010B0500038201010006854D3607AB988CCFE8A3A7CD99A29BC1A004B142053ECFC43CD9BCC5F4A290B7867FB44AF912A0448EAD4F83487072B140805106B440857EF6CF268CDD7DCE83FCE75470233DF6F9B4CFE3F433A2634ED4587DDDA1D527B2A32EE968FF2CADD6AD525E8434C7BB6672E56D2315E026879BC4ADC25889478CC30161A8B49E9A9262A70D63BBCB6F5FC04CB8C7FE3701573CC902652DB62E86748874D4C1E5F6C6E3948DDA7BB56E945411D22A9945015E82165F67F93FFE355E574DEDA8C90BAF498612AD42A520FEDED46F8A2E3075599E78F64D50CAB29B7ED740FCE4F8537C5CC031C33127569D166589141FD5FA4CA6C7357B24AE79F9D2C54272FB02C6 | |||
| (PID) Process: | (3652) certutil.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3540) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\83B2DDFEF9F7004438D7AA66C524344F71A70B48 |
| Operation: | write | Name: | Blob |
Value: 03000000010000001400000083B2DDFEF9F7004438D7AA66C524344F71A70B482000000001000000B3050000308205AF30820497A003020102021009A62D3BEC2C603652D5CB46A1A1EBAB300D06092A864886F70D01010505003065310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312430220603550403131B446967694365727420455620436F6465205369676E696E67204341301E170D3138303431313030303030305A170D3139313130373132303030305A3081D231133011060B2B0601040182373C02010313025553311B3019060B2B0601040182373C020102130A43616C69666F726E6961311D301B060355040F0C1450726976617465204F7267616E697A6174696F6E311530130603550405130C323030303130333130303133310B3009060355040613025553311330110603550408130A57617368696E67746F6E3110300E0603550407130753656174746C6531193017060355040A1310496E7365637572652E436F6D204C4C433119301706035504031310496E7365637572652E436F6D204C4C4330820122300D06092A864886F70D01010105000382010F003082010A02820101009B0E903FE2AD256783DA91DF1EEB4AE0C76BC89B880066763A306C619D0CB3FEAB8F695B798F1DB039A1A49A90C234A56C58CA7A5C21B176A7EA5BE2404139273E2617A3391B49593EB162EBD6F86D8D4AEDDABB475E156917A104B4C077CBAAD3390A48588CC523F985BED6B63CA3AF529BE545B2F1B9316EDD3A9805A21B8FCC3DED6F2185426229BD99F620B5D4E8D21002FC2CF3B9397DFE2222ABFFAFD9FBB3510D151E11E1EAB8DF312EF846F549202559099077A72F81DFACBC650E42CCC9D6885CEAB9F63CA613AB385038CE9C56F690B484023AF99E6C483C6E8675240ACCEF420BD511321A97BA3728C3D9B9AC99BF9C087C2B1248518DD01935150203010001A38201EB308201E7301F0603551D23041830168014AD690670FC801B16B3A918946B9402865EF7278C301D0603551D0E0416041434990289D1C96EE5E07D3326D2C2EC6A20005CE130350603551D11042E302CA02A06082B06010505070803A01E301C0C1A55532D43414C49464F524E49412D323030303130333130303133300E0603551D0F0101FF04040302078030130603551D25040C300A06082B0601050507030330730603551D1F046C306A3033A031A02F862D687474703A2F2F63726C332E64696769636572742E636F6D2F4556436F64655369676E696E672D67312E63726C3033A031A02F862D687474703A2F2F63726C342E64696769636572742E636F6D2F4556436F64655369676E696E672D67312E63726C304B0603551D2004443042303706096086480186FD6C0302302A302806082B06010505070201161C68747470733A2F2F7777772E64696769636572742E636F6D2F4350533007060567810C0103307906082B06010505070101046D306B302406082B060105050730018618687474703A2F2F6F6373702E64696769636572742E636F6D304306082B060105050730028637687474703A2F2F636163657274732E64696769636572742E636F6D2F44696769436572744556436F64655369676E696E6743412E637274300C0603551D130101FF04023000300D06092A864886F70D010105050003820101005810375C2836B0D444D1709338DD4B3E419215208D3A0BB5CA67FB678103D7A30FFAA5E09AEBE0B22ACBD08941990863FE4DCA43C0E48EAAE877998B5E6DEE22A56E53A06F48D62DDFB59D2CE4F07C8AB6D5BA6C19F475F891DB3FF906A445B04E4F5740F1E98D59514B70A0AFBB3212175CB469851067D381A4D27FB861BBE5830C424890E07106290BC6C01EC610AB814BEE74EDA9214A41B108A0D0B9BC14D64743FCD37E952EFF61F0835259C82F6F9DA8540F2482130AD8F40684567BA29A04E6B0D1D7411EF285CD8E9F7AFECB514DC5EE80FBDE693952F08EAB6521267D520CECF3FC90B5D71D2220E124AAC3A8140433A8850D29EDE119CEE398DC0C | |||
Executable files
20
Suspicious files
25
Text files
628
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2252 | npcap-0.996.exe | C:\Users\admin\AppData\Local\Temp\nsw10F2.tmp\options.ini | text | |
MD5:— | SHA256:— | |||
| 2252 | npcap-0.996.exe | C:\Users\admin\AppData\Local\Temp\nsw10F2.tmp\final.ini | text | |
MD5:— | SHA256:— | |||
| 2252 | npcap-0.996.exe | C:\Program Files\Npcap\FixInstall.bat | text | |
MD5:16E01C918EB101B6D3A66EAACA9EA211 | SHA256:E0A4DF26C530BAEDE1D1ACB452E76338D0748521DC2AE378DF1A87BB1D556846 | |||
| 2252 | npcap-0.996.exe | C:\Program Files\Npcap\npcap.sys | executable | |
MD5:1E152ED6AABBB756F768D320D6FBAE54 | SHA256:75BED432F8B92CAE369236FC43106D36F27AFF9F46EA9E40F6C596412CE320D7 | |||
| 2252 | npcap-0.996.exe | C:\Program Files\Npcap\LICENSE | text | |
MD5:043E3F337A269643FA4A6BCB5C17EA55 | SHA256:8ED32F19CFB6A16C595965DF6293A4711D171B616916D87CE4B2DEDED911CE88 | |||
| 2252 | npcap-0.996.exe | C:\Program Files\Npcap\NPFInstall.exe | executable | |
MD5:7CF75CD87E469E24EB6900ACD0457A6B | SHA256:1D2C84E5043F3D01B8556E61192128FCC6045A72DF306DF39FA98281DBE3A6B5 | |||
| 2252 | npcap-0.996.exe | C:\Users\admin\AppData\Local\Temp\nsw10F2.tmp\ns44B7.tmp | — | |
MD5:— | SHA256:— | |||
| 2252 | npcap-0.996.exe | C:\Program Files\Npcap\npcap.cat | cat | |
MD5:3E1A6928E8D5F4162F61ED3C16B9B4BC | SHA256:DE433F43E0B1D2BC5E329573020CC6A95CE0C9B1A7DDDA0225420E3D1D9787E6 | |||
| 2252 | npcap-0.996.exe | C:\Program Files\Npcap\npcap_wfp.inf | binary | |
MD5:06DCA144646BBEDA00437809D679D019 | SHA256:66847839B1A5B13C4C2E58975CF9F887A3550BC7978B61B0572CA1B04584E49E | |||
| 2252 | npcap-0.996.exe | C:\Program Files\Npcap\npcap.inf | binary | |
MD5:98E3B869584F5DC14CBD2C4E8C2E7767 | SHA256:4897E00724A3DBFFFBCCC2CE3993995B75FBE4EA5DFD17E4E2EFCE3F7983801A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report