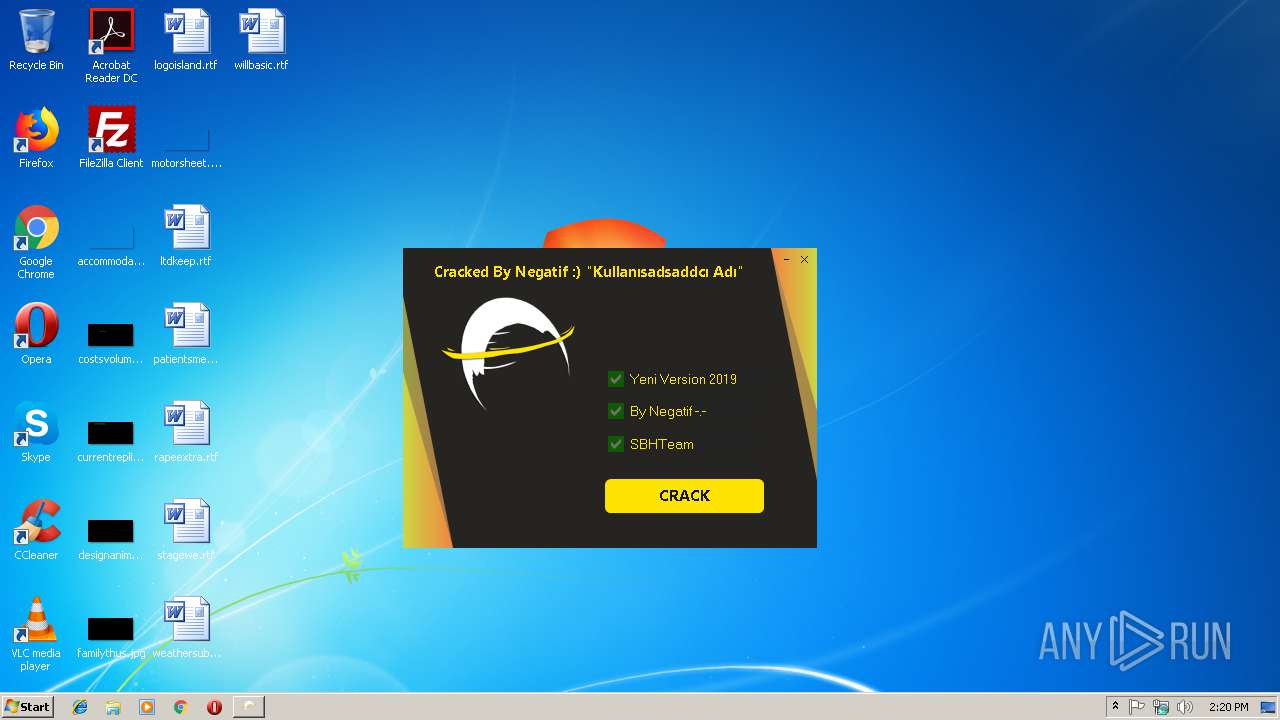
| File name: | EzGlobal Cracked.exe |
| Full analysis: | https://app.any.run/tasks/550d1c6b-c6ff-4fc7-aea4-7cec8c835cac |
| Verdict: | No threats detected |
| Analysis date: | March 12, 2019, 14:20:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9A1BF73E64FA910A6F332A1047AC6FAE |
| SHA1: | AAA70345124CC8532C3344D70E9A2F9057D47923 |
| SHA256: | 148E813A065103719FCA8435EA29CD3928274229F9C03D4E4458A978ACAC6FD5 |
| SSDEEP: | 49152:2EHYURT57eyUFT5Nglus/B5VeIrb9iW3sC8Is5dFHkf1IRSp6MPRcbKzie:jHYQT5OFbc1eCcebsnFkiRSp6MPmbm |
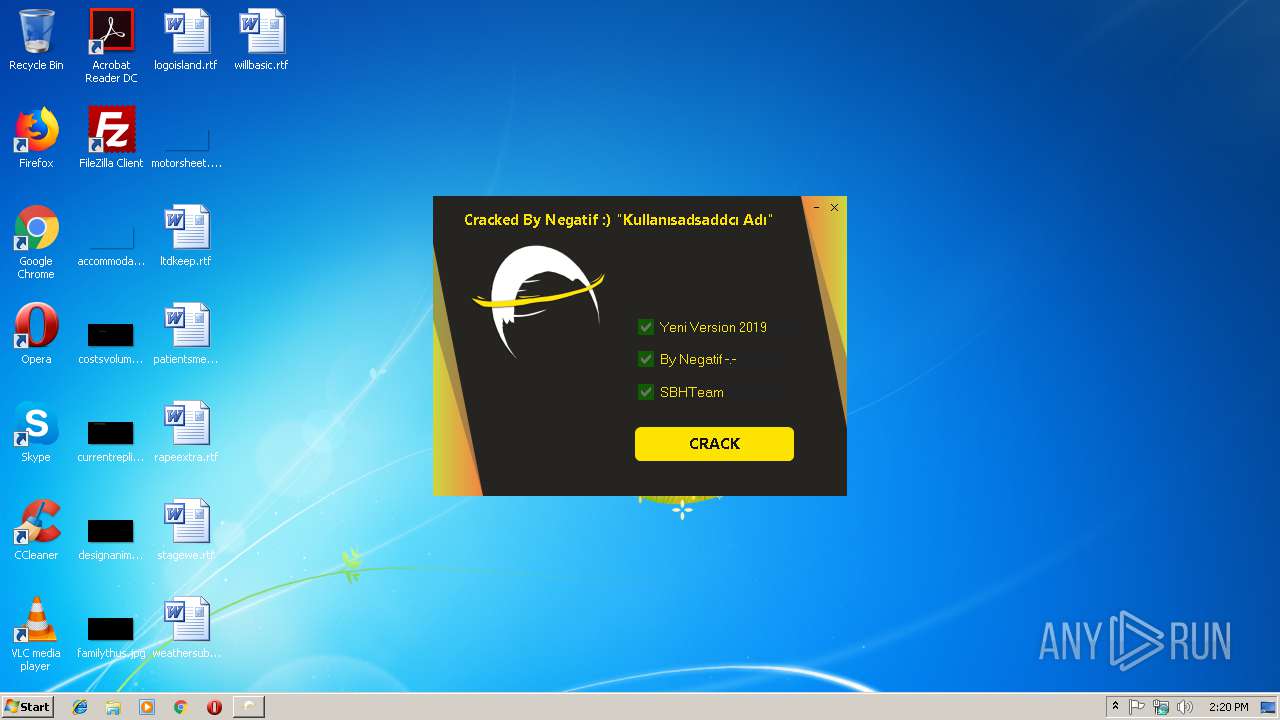
MALICIOUS
Changes settings of System certificates
- EzGlobal Cracked.exe (PID: 3516)
SUSPICIOUS
Reads the machine GUID from the registry
- EzGlobal Cracked.exe (PID: 3516)
Adds / modifies Windows certificates
- EzGlobal Cracked.exe (PID: 3516)
Executable content was dropped or overwritten
- EzGlobal Cracked.exe (PID: 3516)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:10 14:55:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 1928704 |
| InitializedDataSize: | 45568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x63a000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | ezglobalyazilim.com |
| CompanyName: | Ezglobal Yazılım |
| FileDescription: | EzglobalYazılım Loader |
| FileVersion: | 1.0.0.0 |
| InternalName: | ezgoLoader.exe |
| LegalCopyright: | Copyright © 2999 |
| LegalTrademarks: | - |
| OriginalFileName: | ezgoLoader.exe |
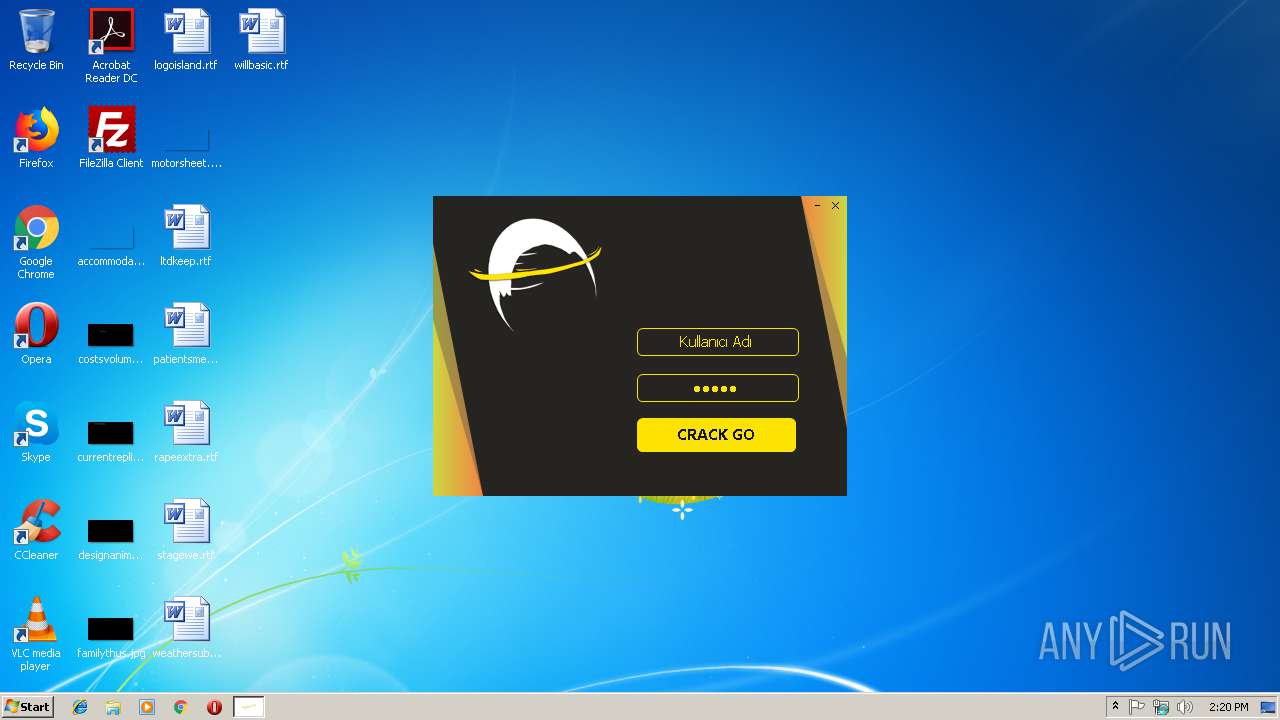
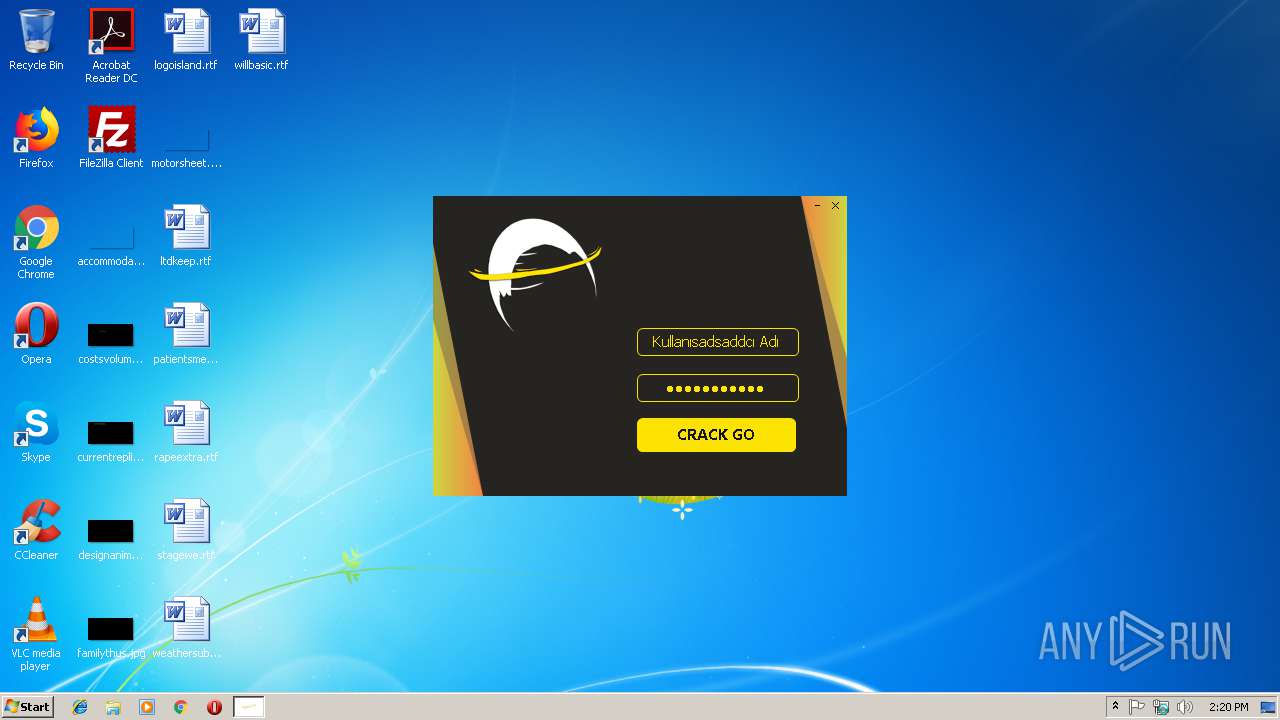
| ProductName: | CSGO LOADER |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Feb-2019 13:55:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x867A |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 10-Feb-2019 13:55:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00002000 | 0x001D8000 | 0x00162C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97346 | |
.rsrc | 0x001DA000 | 0x0000AFFA | 0x00007C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.94826 |
.idata | 0x001E6000 | 0x00002000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.28405 |
0x001E8000 | 0x002A4000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.260771 | |
ojykvqgd | 0x0048C000 | 0x001AE000 | 0x001AD600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.94391 |
kfjrtevj | 0x0063A000 | 0x00002000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.0861 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.0055 | 3174 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.91682 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.48196 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.85526 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 7.96284 | 22927 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.64638 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
comctl32.dll |
kernel32.dll |
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3148 | "C:\Users\admin\AppData\Local\Temp\EzGlobal Cracked.exe" | C:\Users\admin\AppData\Local\Temp\EzGlobal Cracked.exe | — | explorer.exe | |||||||||||
User: admin Company: Ezglobal Yazılım Integrity Level: MEDIUM Description: EzglobalYazılım Loader Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3516 | "C:\Users\admin\AppData\Local\Temp\EzGlobal Cracked.exe" | C:\Users\admin\AppData\Local\Temp\EzGlobal Cracked.exe | explorer.exe | ||||||||||||
User: admin Company: Ezglobal Yazılım Integrity Level: HIGH Description: EzglobalYazılım Loader Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
56
Read events
29
Write events
27
Delete events
0
Modification events
| (PID) Process: | (3516) EzGlobal Cracked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EzGlobal Cracked_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3516) EzGlobal Cracked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EzGlobal Cracked_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3516) EzGlobal Cracked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EzGlobal Cracked_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3516) EzGlobal Cracked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EzGlobal Cracked_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3516) EzGlobal Cracked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EzGlobal Cracked_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3516) EzGlobal Cracked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EzGlobal Cracked_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3516) EzGlobal Cracked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EzGlobal Cracked_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3516) EzGlobal Cracked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EzGlobal Cracked_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3516) EzGlobal Cracked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EzGlobal Cracked_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3516) EzGlobal Cracked.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\EzGlobal Cracked_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3516 | EzGlobal Cracked.exe | C:\Users\admin\AppData\Local\Temp\ezglobal.dll | executable | |
MD5:8F3A43C13DCF363F3ADDB355375EFF5D | SHA256:B69DD6F17F12F19C82C0AF455D43587C6B5B829BBB8A4708C3494D5EBDF04A99 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3516 | EzGlobal Cracked.exe | 104.16.13.231:443 | cdn.discordapp.com | Cloudflare Inc | US | shared |
3516 | EzGlobal Cracked.exe | 94.73.150.152:443 | ezglobalyazilim.com | Cizgi Telekomunikasyon Anonim Sirketi | TR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ezglobalyazilim.com |
| malicious |
cdn.discordapp.com |
| shared |
Threats
Process | Message |
|---|---|
EzGlobal Cracked.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|