| File name: | Kronos.exe |
| Full analysis: | https://app.any.run/tasks/74569293-9fb4-4cc4-a9f5-d27ec1490c22 |
| Verdict: | Malicious activity |
| Analysis date: | October 21, 2024, 11:45:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 0157784B7E0543AC7FC8C8DEE148E606 |
| SHA1: | F6F83903B4E52BF9532E0CBA4C888F636EB39758 |
| SHA256: | 147C1ED89DD953DA36D35DD5D6CC612FAE5FA91D1AFD1E405347376E9745C4E5 |
| SSDEEP: | 49152:1+URbLDF/dNn6C+5QCbi0PqRyIKINVBOjYfHyVv91FZ8eea0OjO+N12vTyprlYnV:1+URbLB3nj+ri8qUGNn4Y/6rHEvyQGpM |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes application which crashes
- Kronos.exe (PID: 764)
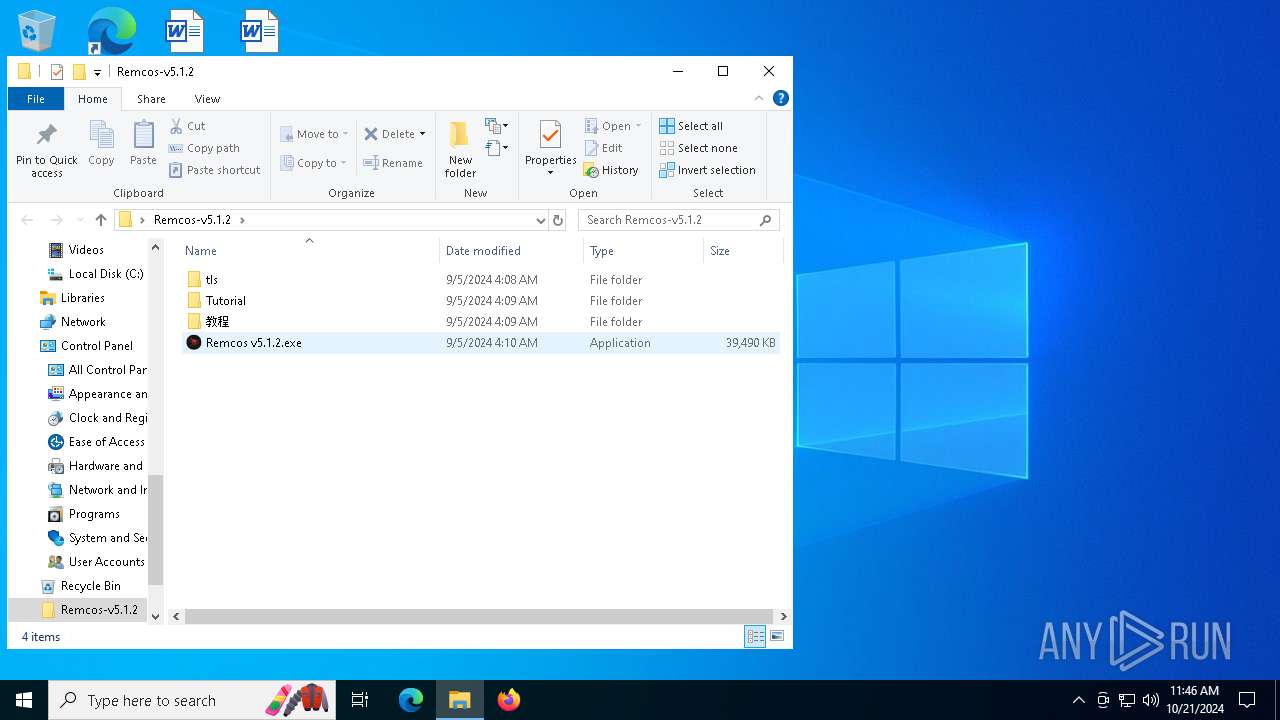
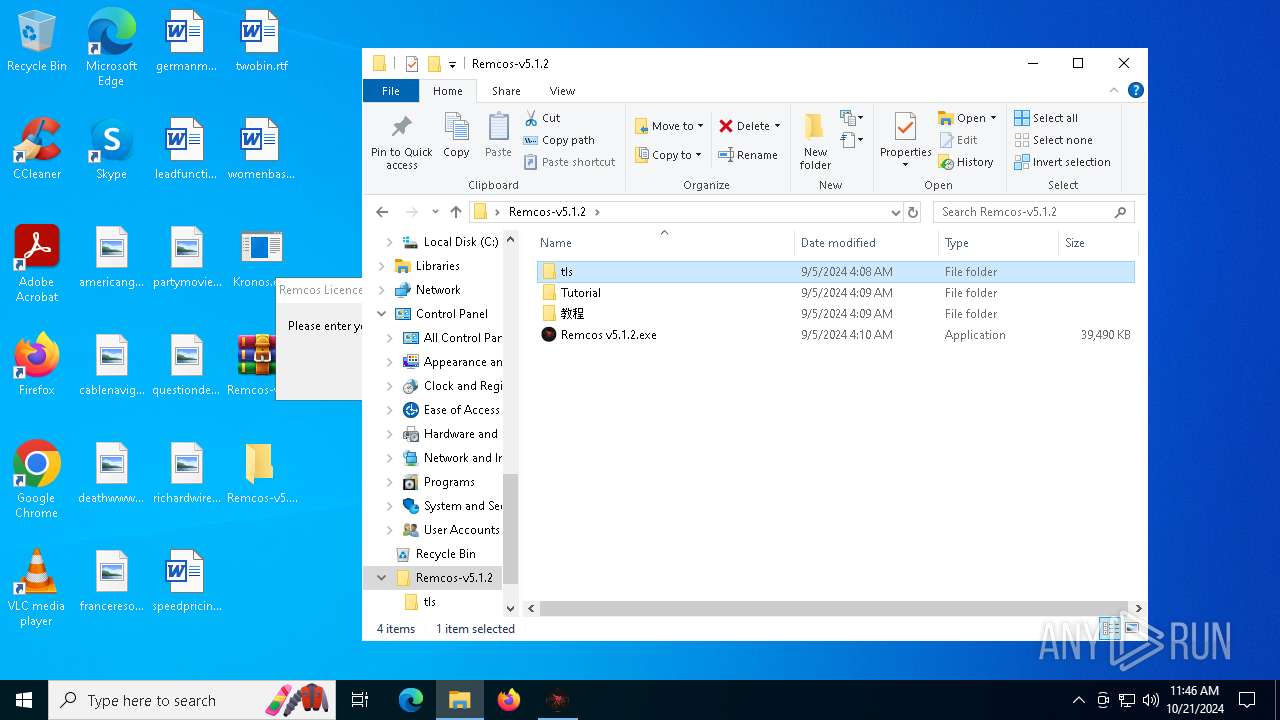
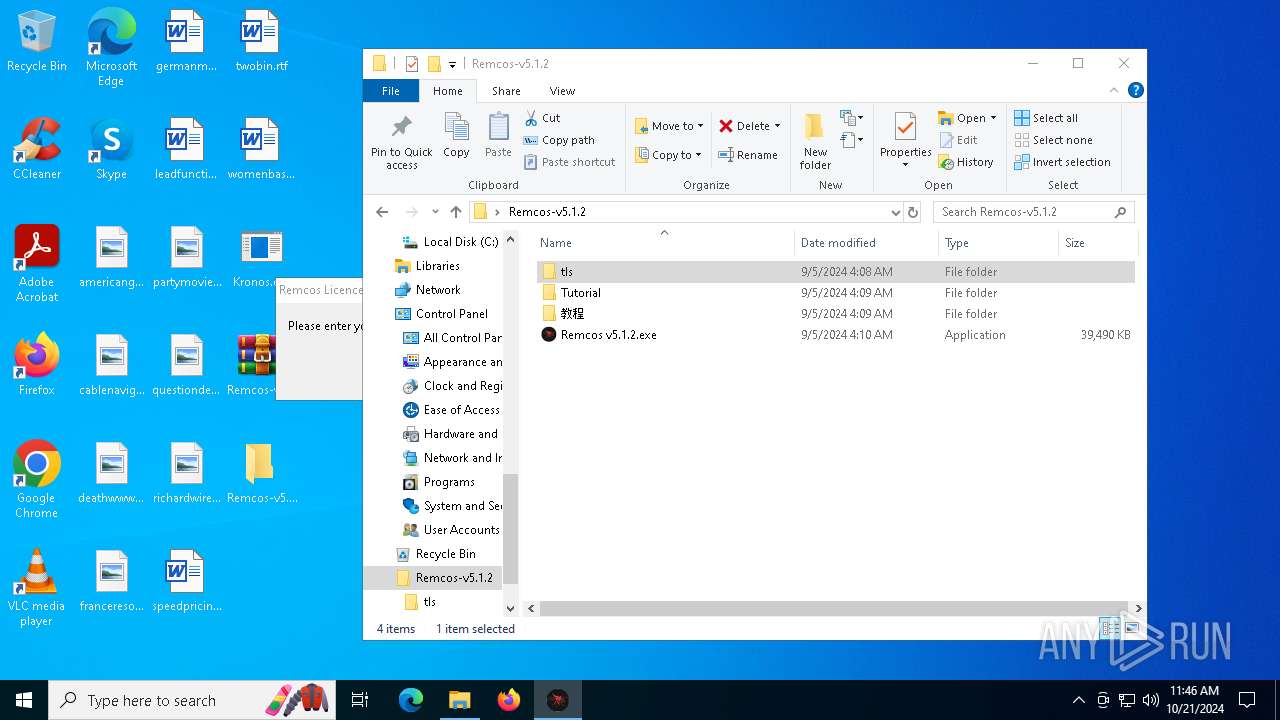
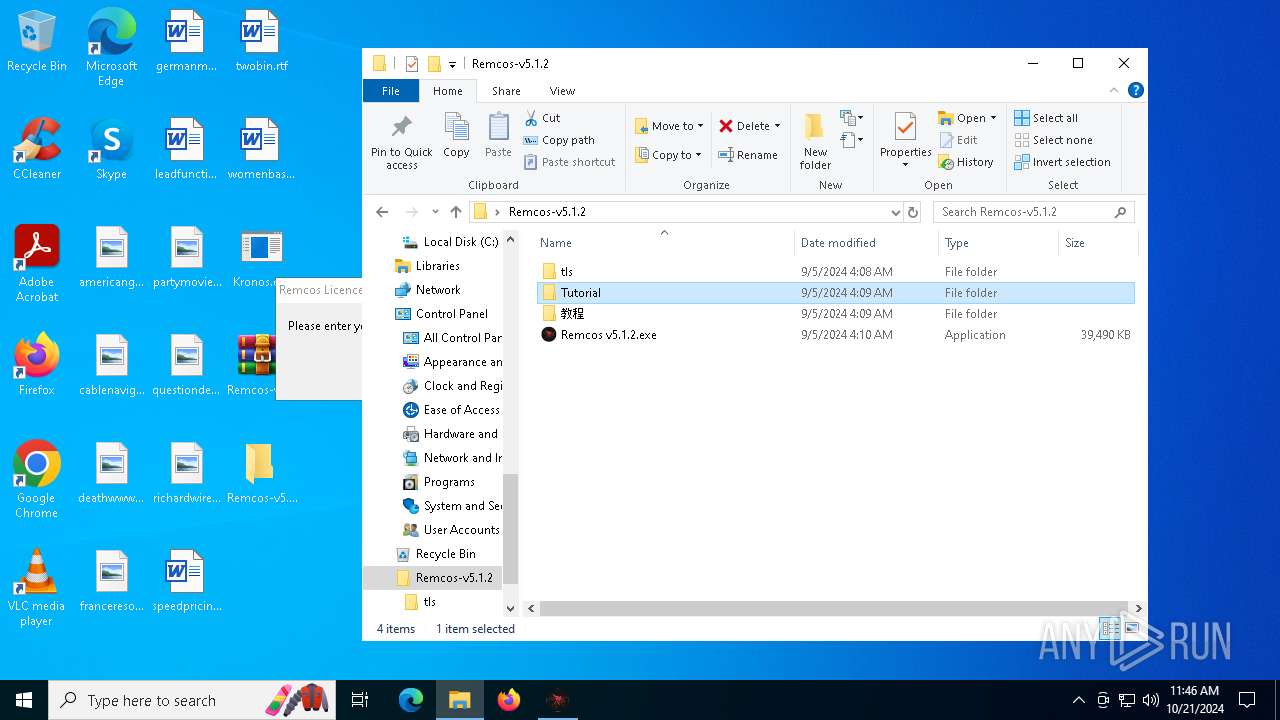
Executable content was dropped or overwritten
- Kronos.exe (PID: 764)
- Remcos v5.1.2.exe (PID: 7756)
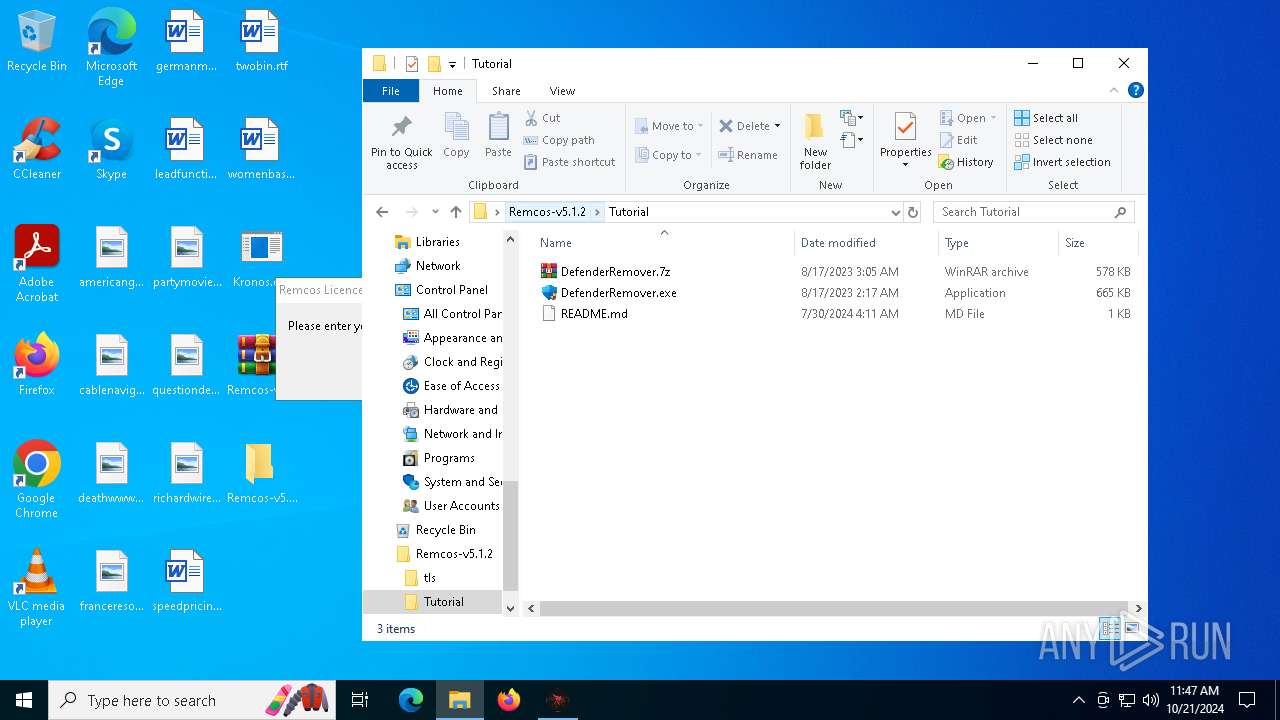
- DefenderRemover.exe (PID: 6992)
Process drops legitimate windows executable
- Remcos v5.1.2.exe (PID: 7756)
- DefenderRemover.exe (PID: 6992)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- svchost.exe (PID: 7844)
Connects to unusual port
- svchost.exe (PID: 7844)
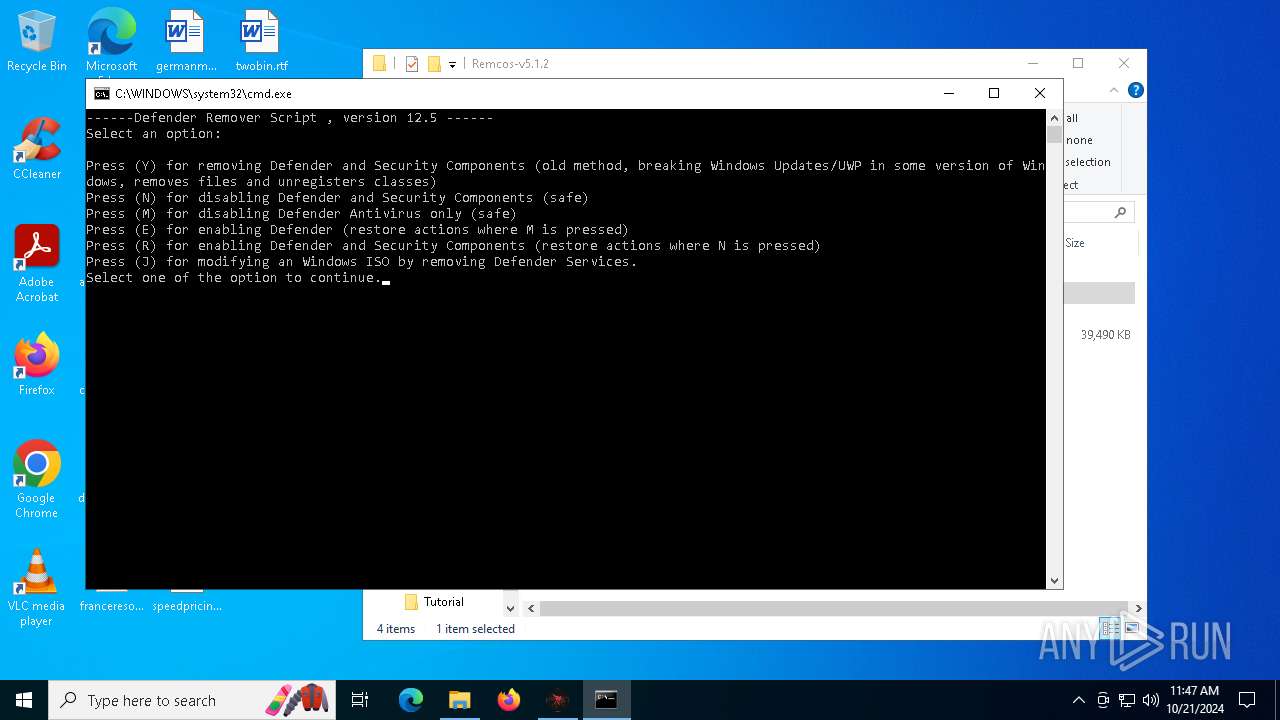
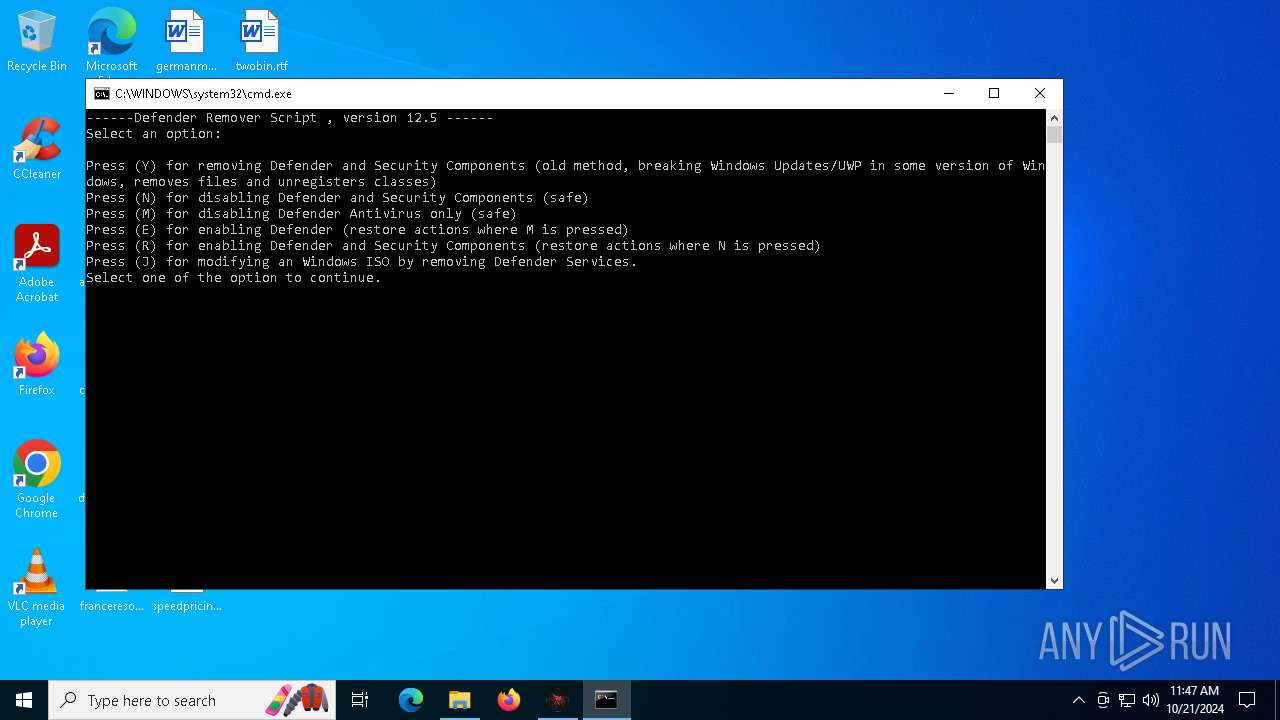
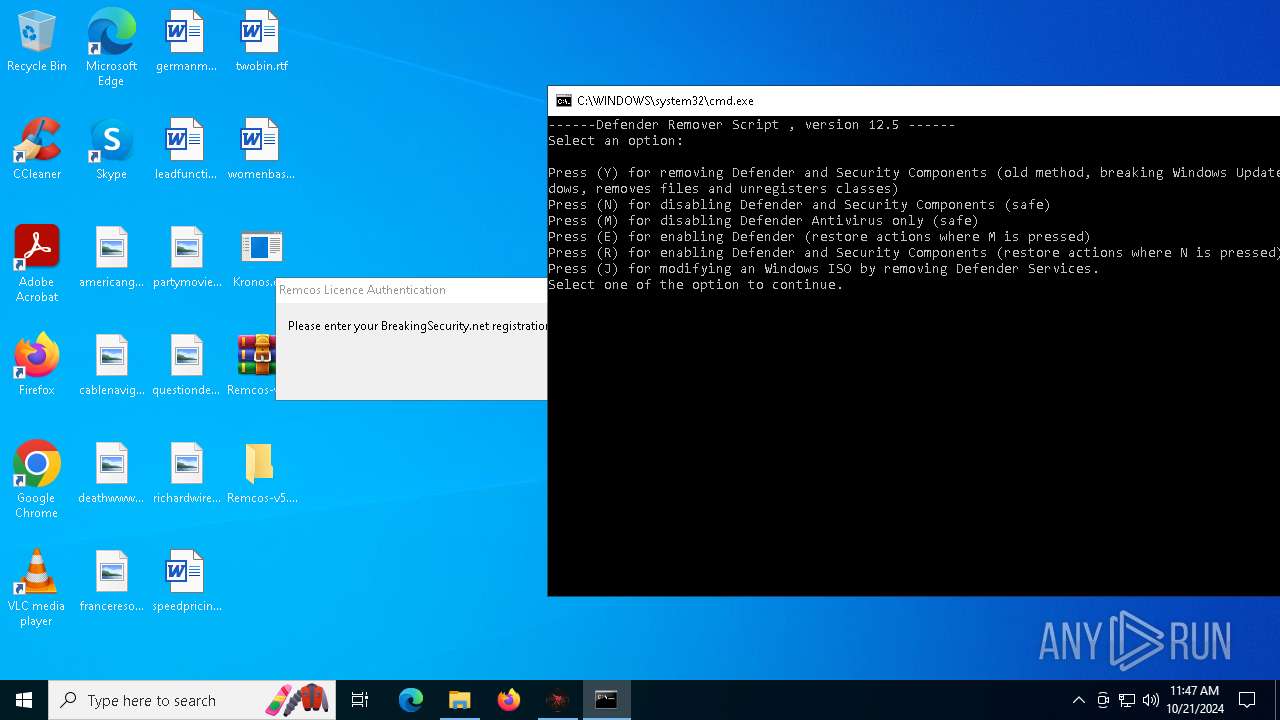
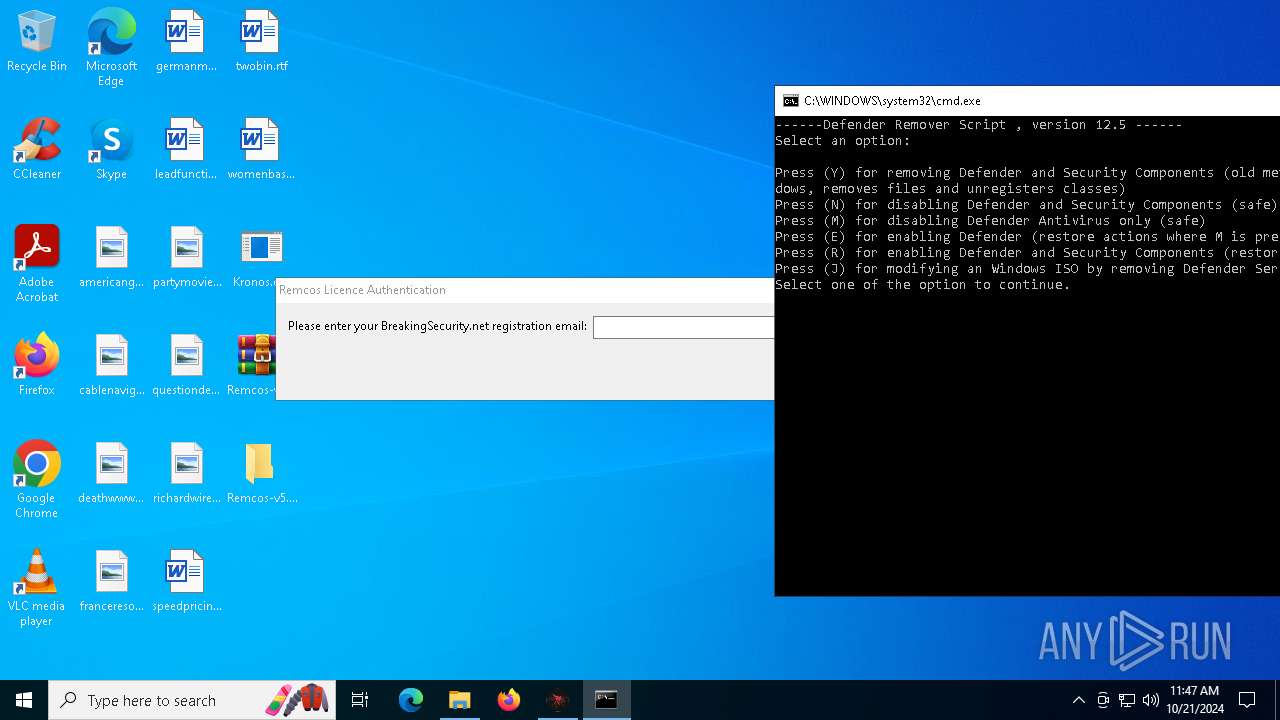
Executing commands from a ".bat" file
- DefenderRemover.exe (PID: 6992)
Starts CMD.EXE for commands execution
- DefenderRemover.exe (PID: 6992)
INFO
Reads the computer name
- Kronos.exe (PID: 764)
Checks supported languages
- Kronos.exe (PID: 764)
Reads the machine GUID from the registry
- Kronos.exe (PID: 764)
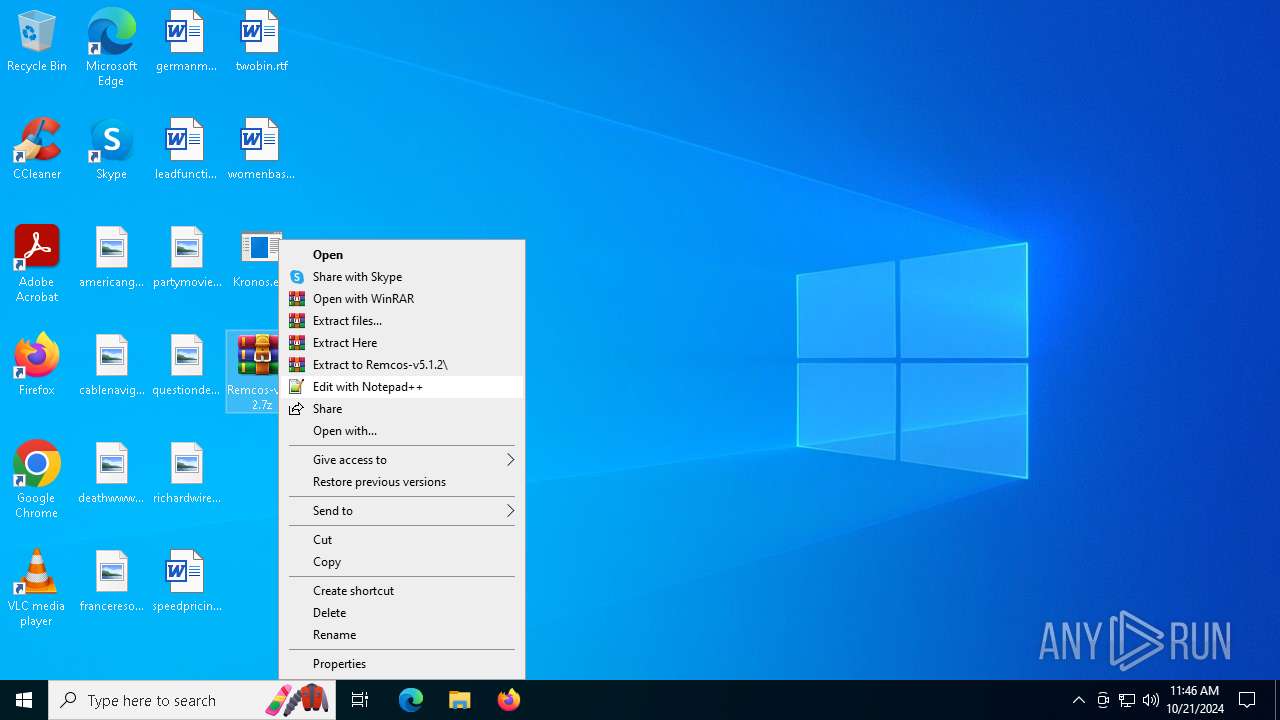
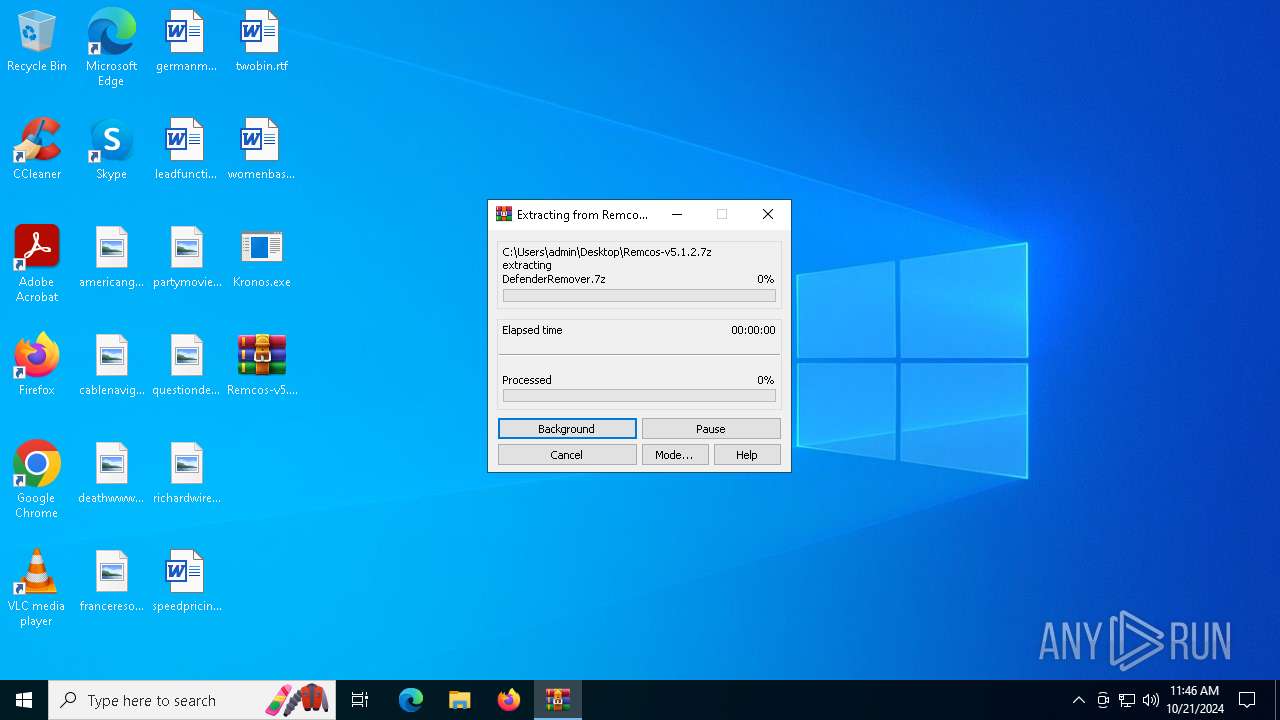
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7624)
Manual execution by a user
- WinRAR.exe (PID: 7624)
- Remcos v5.1.2.exe (PID: 7756)
- DefenderRemover.exe (PID: 8172)
- DefenderRemover.exe (PID: 6992)
Create files in a temporary directory
- Kronos.exe (PID: 764)
Attempting to use instant messaging service
- svchost.exe (PID: 7844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2102:01:07 12:28:57+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 1298432 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x13ef0e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Kronos |
| FileVersion: | 1.0.0.0 |
| InternalName: | Kronos.exe |
| LegalCopyright: | Copyright © 2022 |
| LegalTrademarks: | - |
| OriginalFileName: | Kronos.exe |
| ProductName: | Kronos |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
144
Monitored processes
12
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | C:\WINDOWS\system32\cmd.exe /c .\Script_Run.bat | C:\Windows\SysWOW64\cmd.exe | — | DefenderRemover.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 764 | "C:\Users\admin\Desktop\Kronos.exe" | C:\Users\admin\Desktop\Kronos.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Kronos Exit code: 3221225477 Version: 1.0.0.0 Modules
| |||||||||||||||
| 5616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6716 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 764 -s 1280 | C:\Windows\SysWOW64\WerFault.exe | Kronos.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
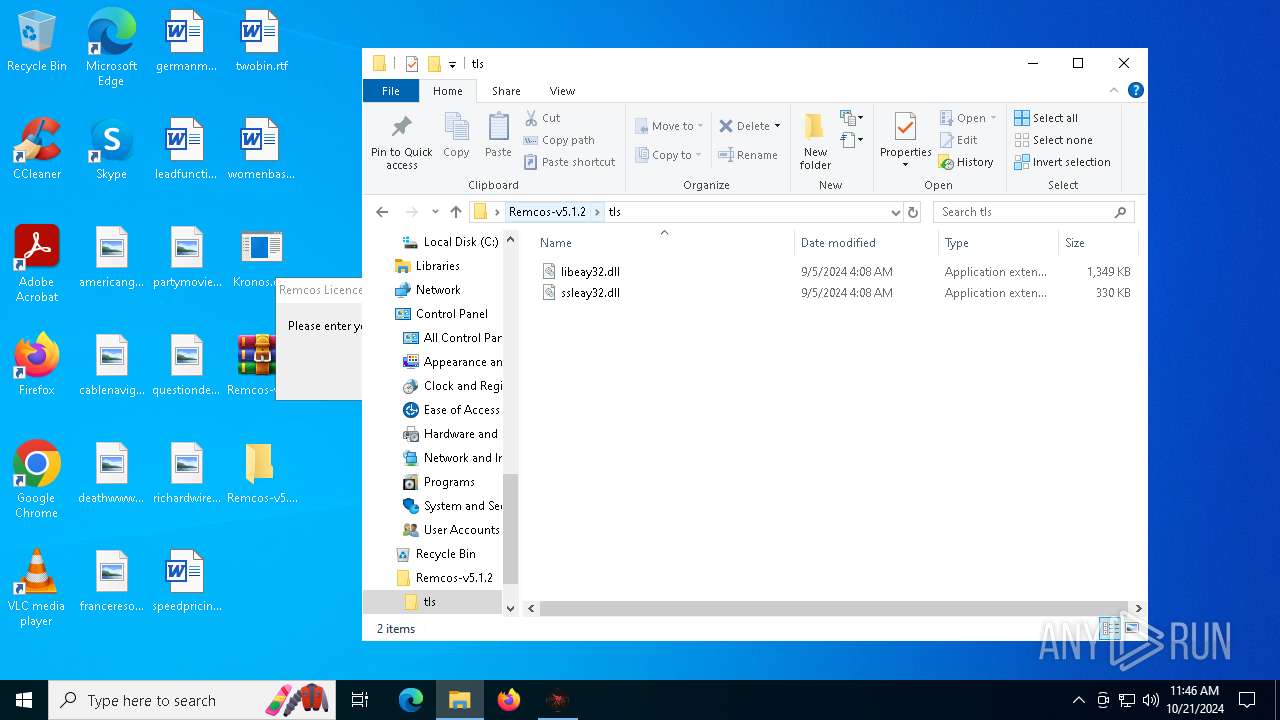
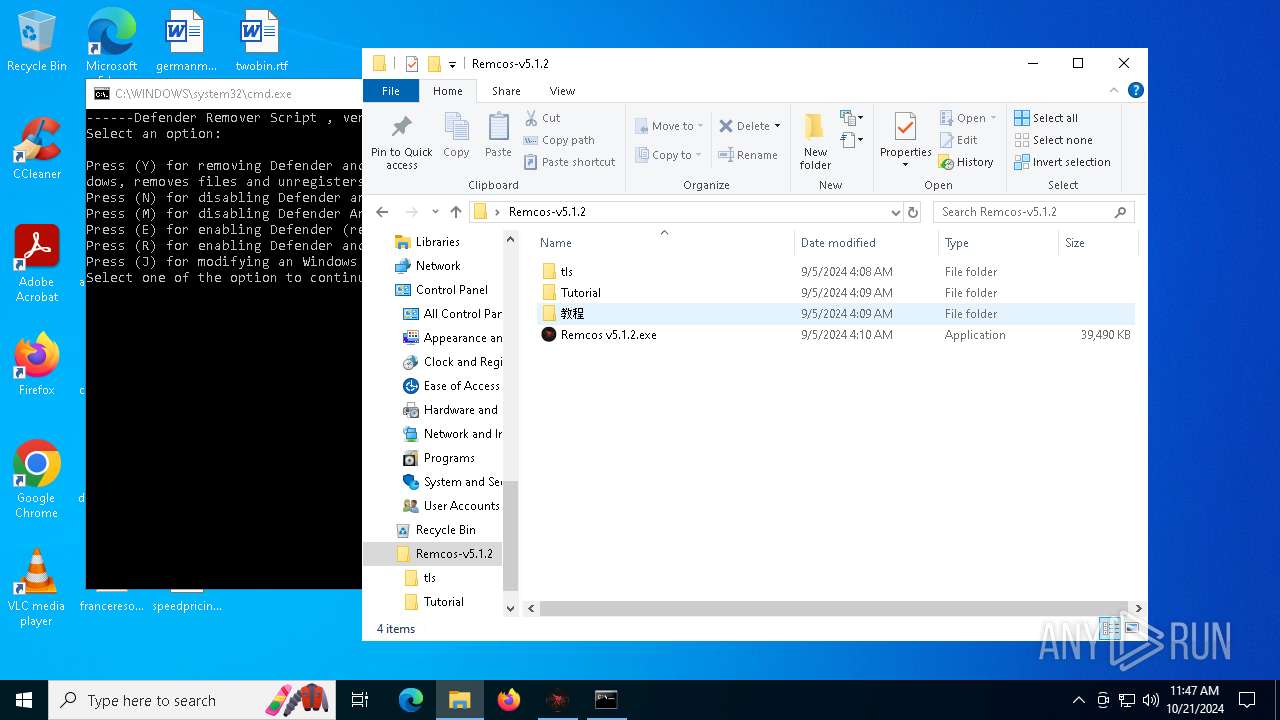
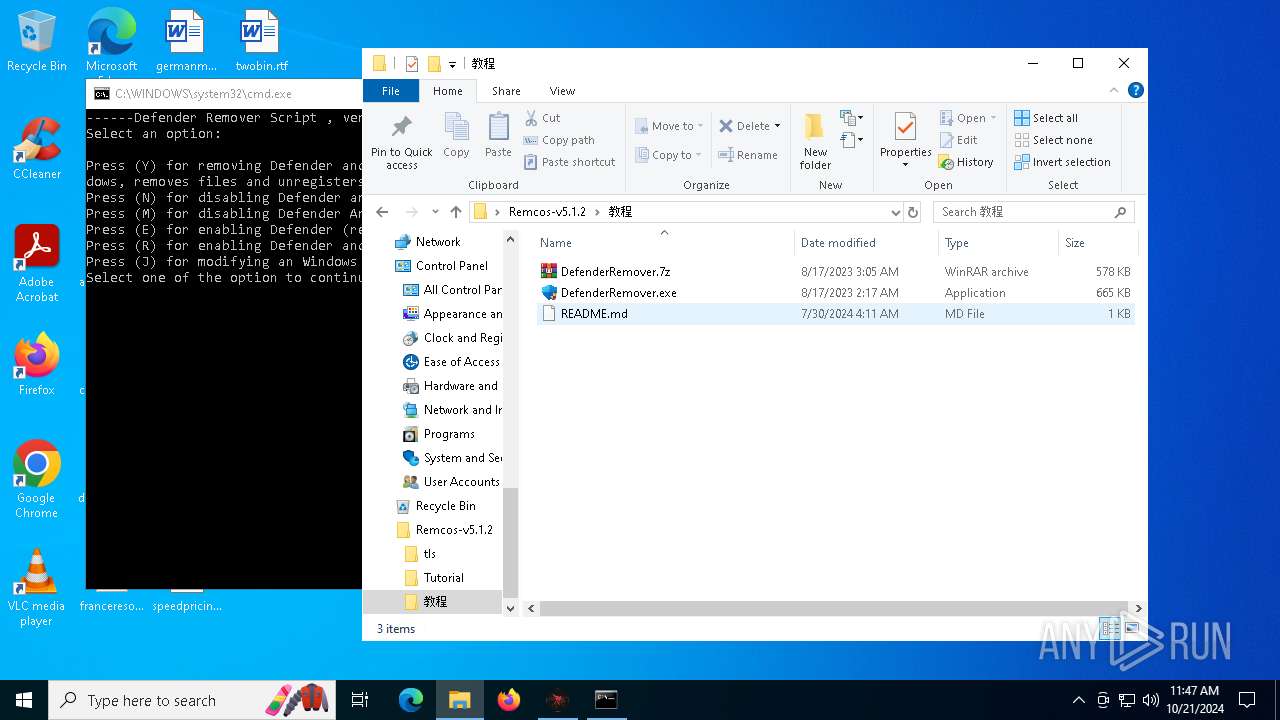
| 6992 | "C:\Users\admin\Desktop\Remcos-v5.1.2\Tutorial\DefenderRemover.exe" | C:\Users\admin\Desktop\Remcos-v5.1.2\Tutorial\DefenderRemover.exe | explorer.exe | ||||||||||||
User: admin Company: Gallery Inc Integrity Level: HIGH Description: Defender Remover Version: 12.5.2 Modules
| |||||||||||||||
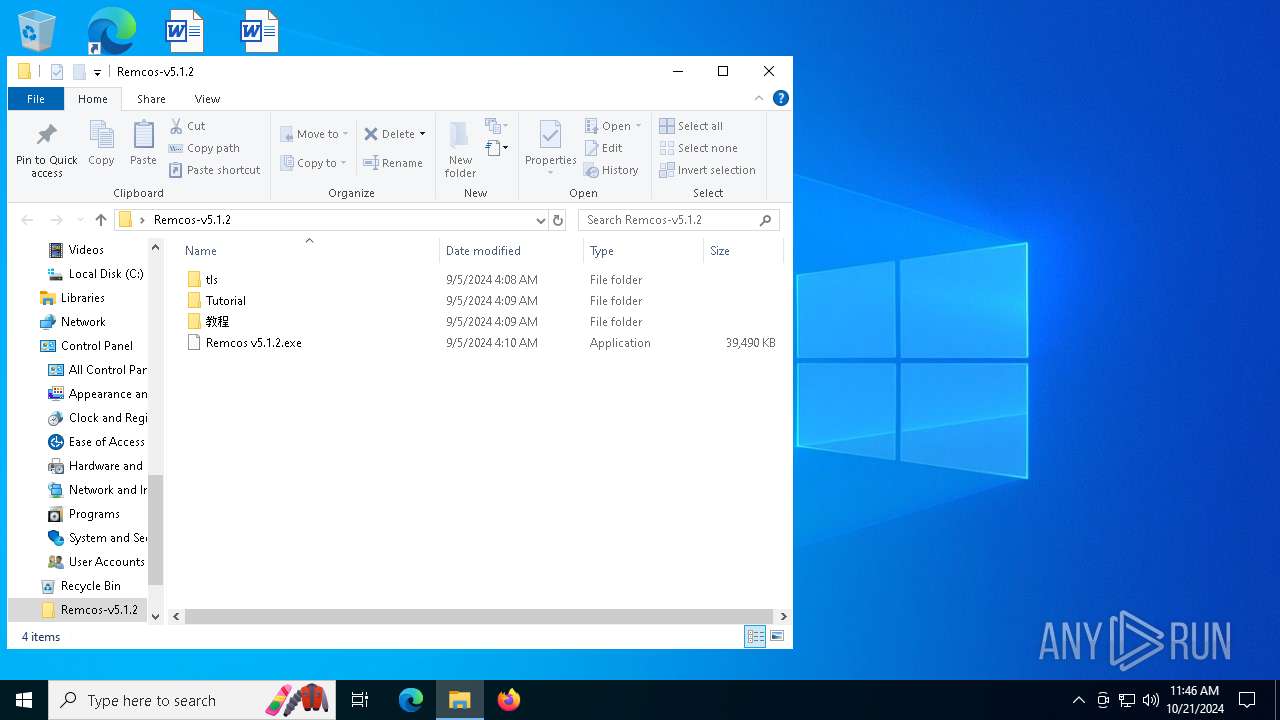
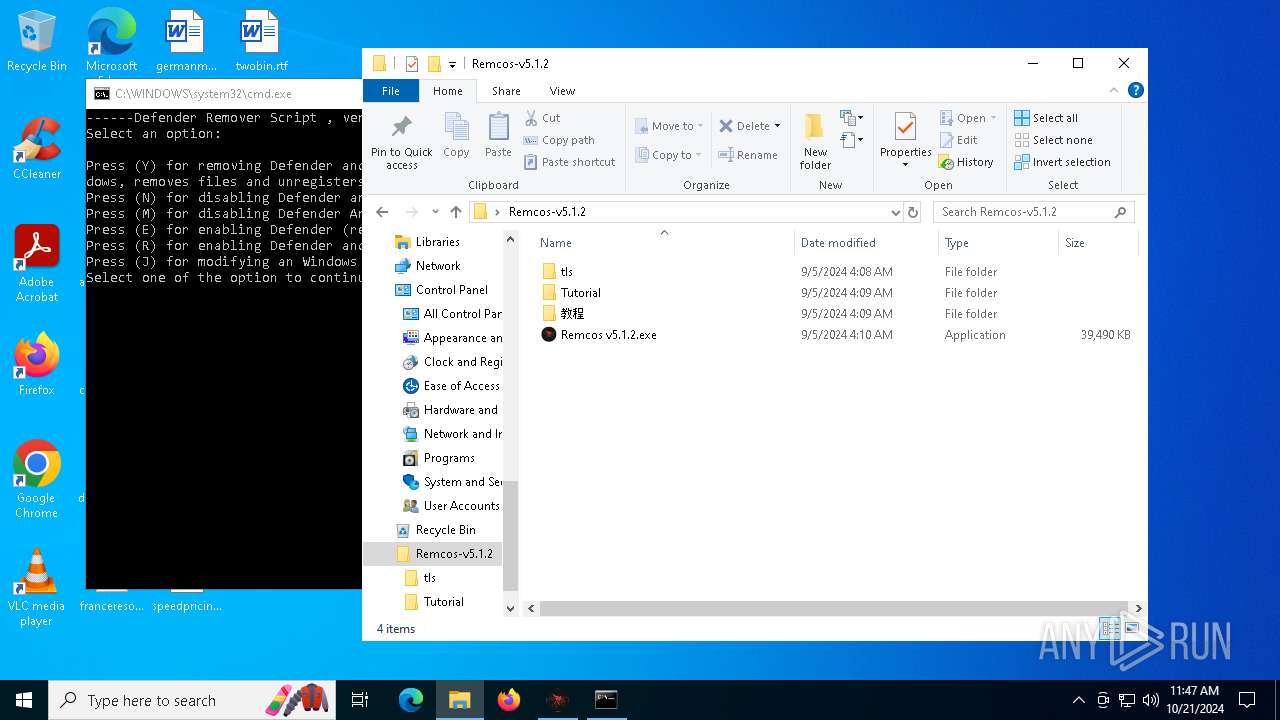
| 7624 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\Remcos-v5.1.2.7z" C:\Users\admin\Desktop\Remcos-v5.1.2\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7720 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
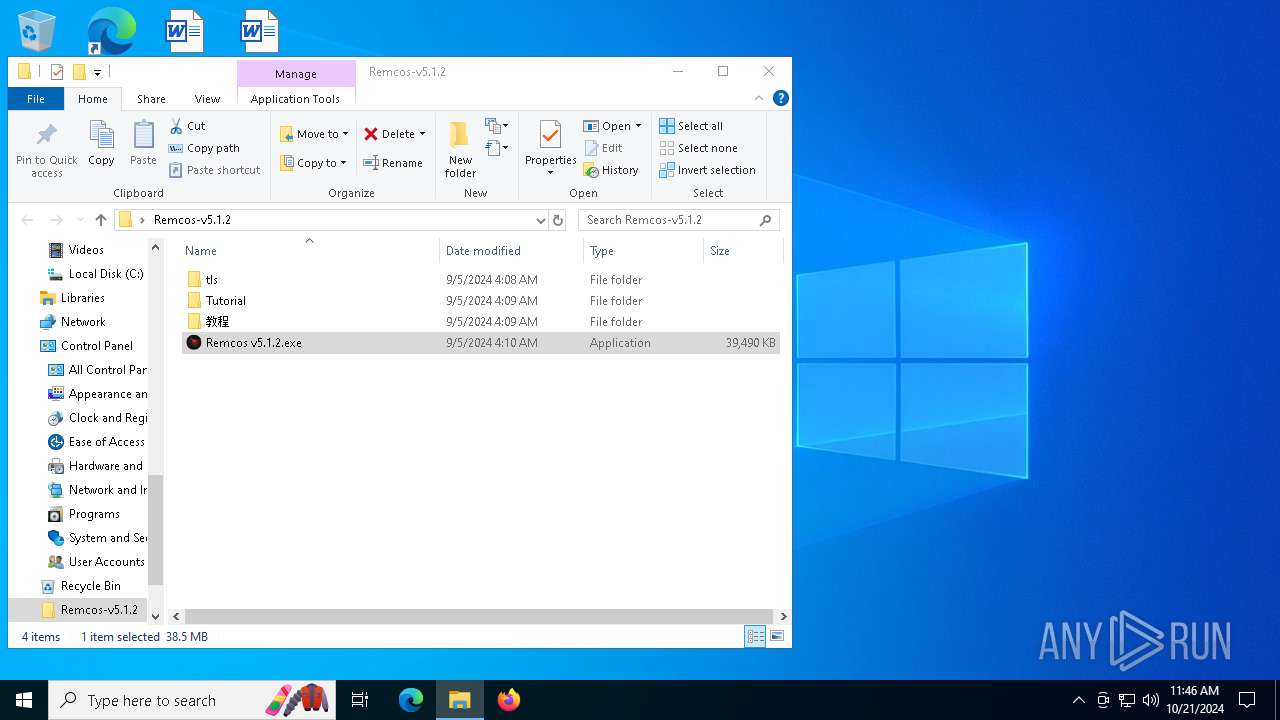
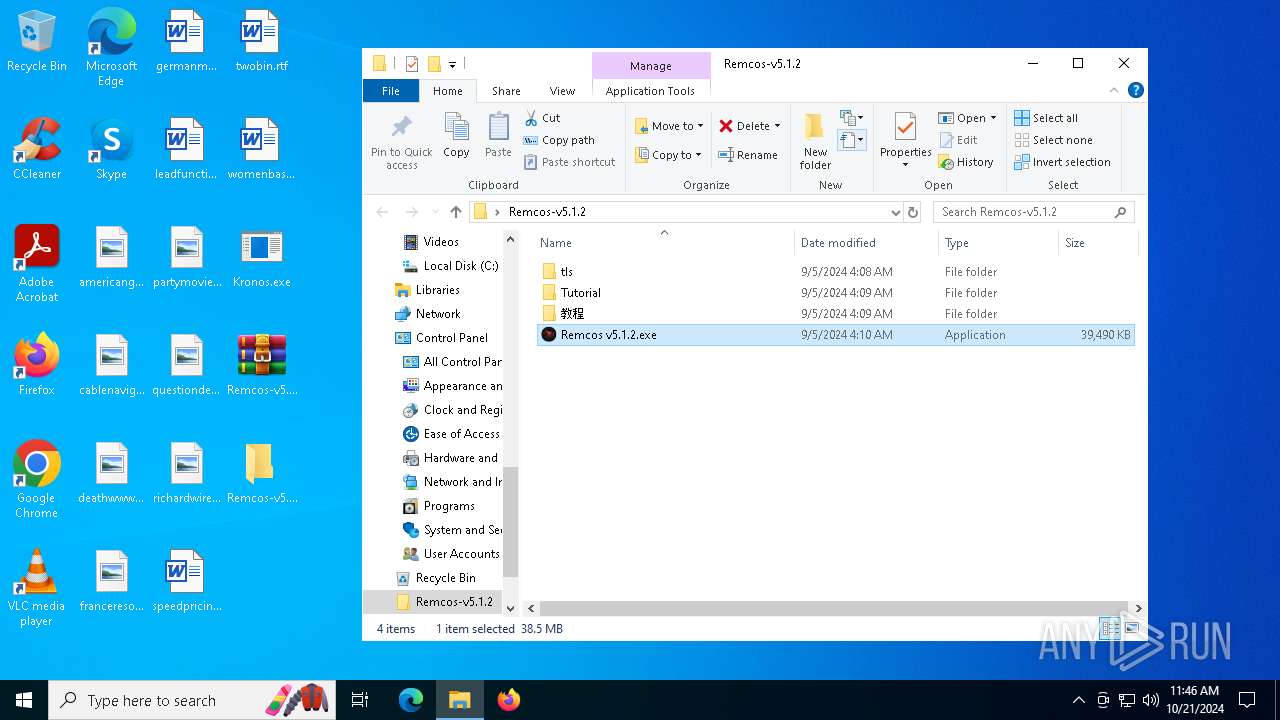
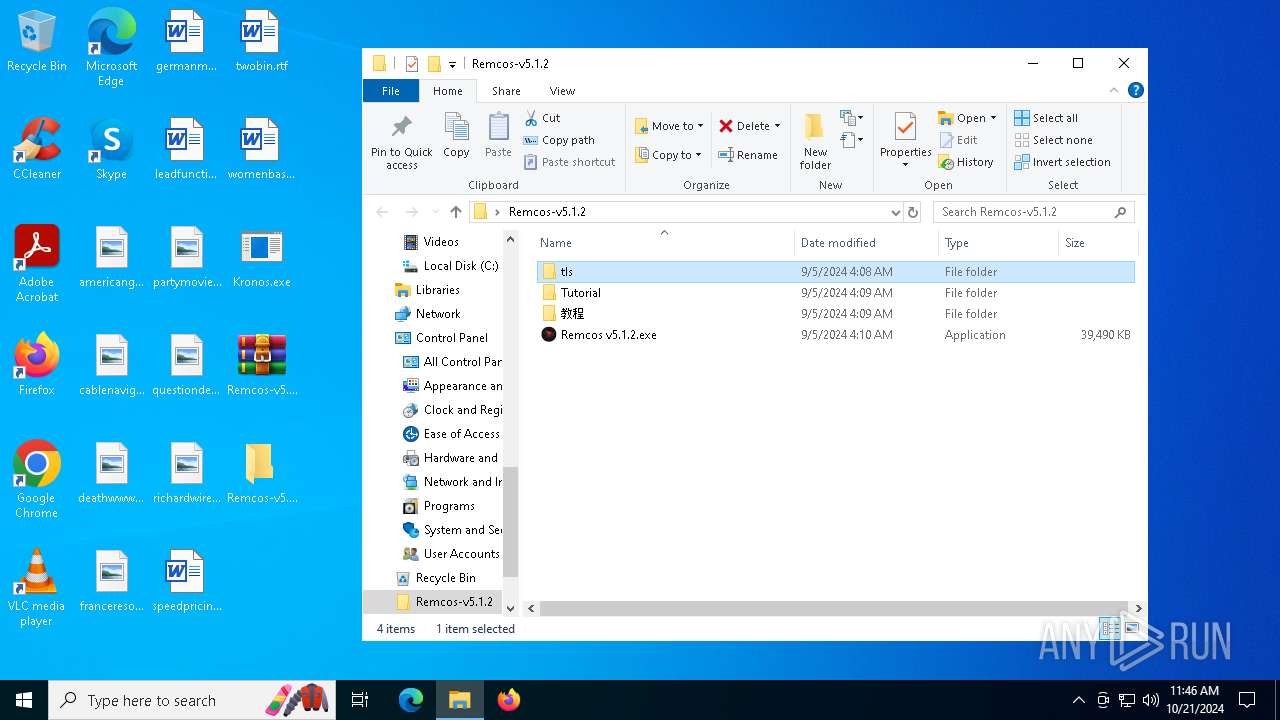
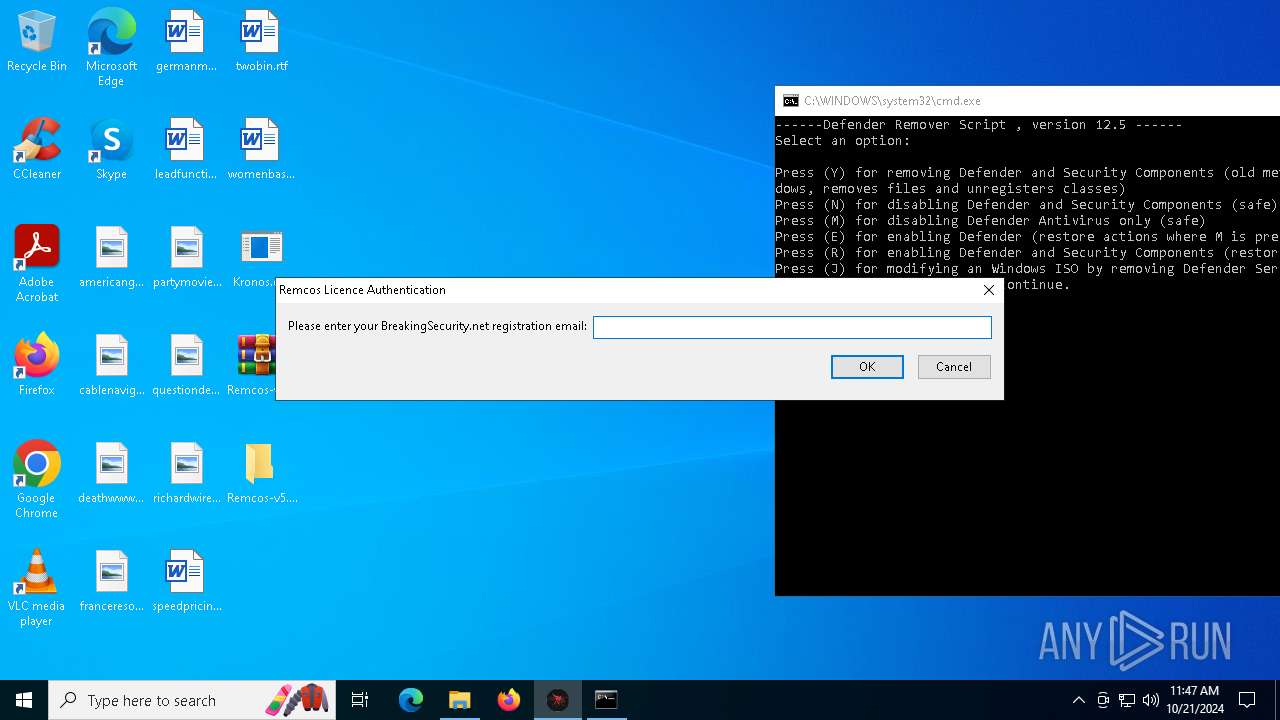
| 7756 | "C:\Users\admin\Desktop\Remcos-v5.1.2\Remcos v5.1.2.exe" | C:\Users\admin\Desktop\Remcos-v5.1.2\Remcos v5.1.2.exe | explorer.exe | ||||||||||||
User: admin Company: BreakingSecurity.net Integrity Level: MEDIUM Description: REMCOS Remote Control & Surveillance Exit code: 0 Version: 5.1.2.0 Modules
| |||||||||||||||
| 7824 | "C:\Users\admin\Desktop\Remcos-v5.1.2\Remcos v5.1.2.exe" | C:\Users\admin\Desktop\Remcos-v5.1.2\Remcos v5.1.2.exe | — | Remcos v5.1.2.exe | |||||||||||
User: admin Company: BreakingSecurity.net Integrity Level: MEDIUM Description: REMCOS Remote Control & Surveillance Exit code: 0 Version: 5.1.2.0 Modules
| |||||||||||||||
| 7844 | "C:\Users\admin\AppData\Roaming\svchost.exe" | C:\Users\admin\AppData\Roaming\svchost.exe | Remcos v5.1.2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Version: 6.2.22621.1 Modules
| |||||||||||||||
Total events
6 150
Read events
6 145
Write events
5
Delete events
0
Modification events
| (PID) Process: | (7624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7624) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7756) Remcos v5.1.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
Executable files
9
Suspicious files
9
Text files
43
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6716 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_Kronos.exe_2f2824fd7a1205ea4c4b5ece8e1c8698ea16_161d4087_b0d8f385-02f0-4c53-bd81-aada70e4b3e8\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6716 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\Kronos.exe.764.dmp | — | |
MD5:— | SHA256:— | |||
| 7624 | WinRAR.exe | C:\Users\admin\Desktop\Remcos-v5.1.2\Remcos v5.1.2.exe | — | |
MD5:— | SHA256:— | |||
| 7756 | Remcos v5.1.2.exe | C:\Users\admin\Desktop\Remcos-v5.1.2\Remcos v5.1.2.exe | — | |
MD5:— | SHA256:— | |||
| 6716 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERC452.tmp.dmp | binary | |
MD5:9928C1442C3AAB4624CF65B78F36F1EB | SHA256:1C308BA20A95FC555C144A9BF109383DD96C811E7D87A33F76AF2F6D9FF0F873 | |||
| 6716 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | der | |
MD5:F0CF5B1794ECA7CD73F9C020DAAB8EF2 | SHA256:2AF00EDCE7EF3266897E52DC81E8DE3B7A079028C0F1F96EAFF9E38AD342F617 | |||
| 764 | Kronos.exe | C:\Users\admin\AppData\Local\Temp\71ca6684-c388-4e5d-bf7c-156dde04d7d5\awalsenin.dll | executable | |
MD5:14FF402962AD21B78AE0B4C43CD1F194 | SHA256:FB9646CB956945BDC503E69645F6B5316D3826B780D3C36738D6B944E884D15B | |||
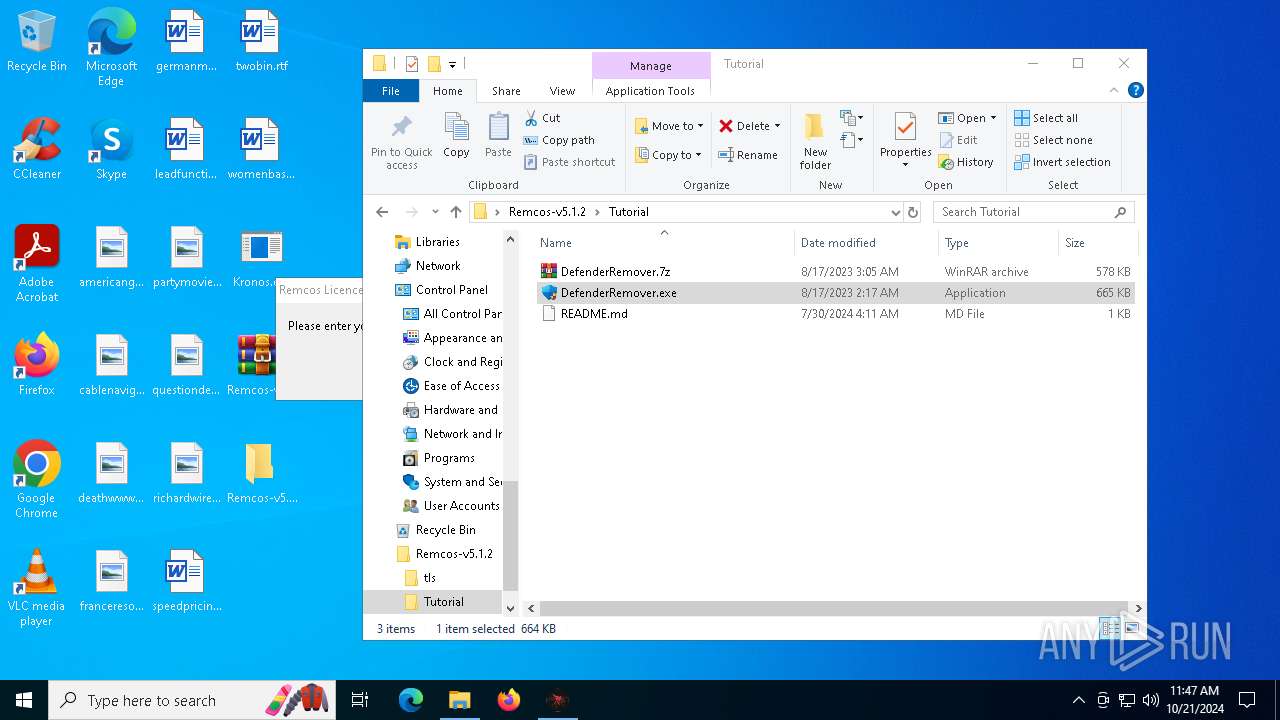
| 7624 | WinRAR.exe | C:\Users\admin\Desktop\Remcos-v5.1.2\教程\DefenderRemover.7z | compressed | |
MD5:DD1DE9B2F3FD46946DCF7C0E5D3F3AB7 | SHA256:B751A0A4536BB9E5D454AB74B021650479AB1A46792B2616968183589DD8ABD5 | |||
| 7624 | WinRAR.exe | C:\Users\admin\Desktop\Remcos-v5.1.2\Tutorial\README.md | text | |
MD5:9461A7E1BEBAB36162E2AFD2263A5BC8 | SHA256:41EE272268648DEBA3D883C3F6CAA429C140135CF3F6D6194664F86159FF9381 | |||
| 7624 | WinRAR.exe | C:\Users\admin\Desktop\Remcos-v5.1.2\Tutorial\DefenderRemover.exe | executable | |
MD5:7A3E43C2971746C84D32F8A448823673 | SHA256:C7BDCEBE60356900DC4B4F8BC8B75ACC1536DF33AE7A1049BFA27192B8C62D0A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
60
DNS requests
22
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.36.225.233:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6716 | WerFault.exe | GET | 200 | 23.33.233.193:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6716 | WerFault.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3604 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7284 | SIHClient.exe | GET | 200 | 23.33.233.193:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1552 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7284 | SIHClient.exe | GET | 200 | 23.33.233.193:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4996 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.36.225.233:80 | www.microsoft.com | AKAMAI-AS | CH | whitelisted |
4360 | SearchApp.exe | 2.23.209.141:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7844 | svchost.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
7844 | svchost.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |