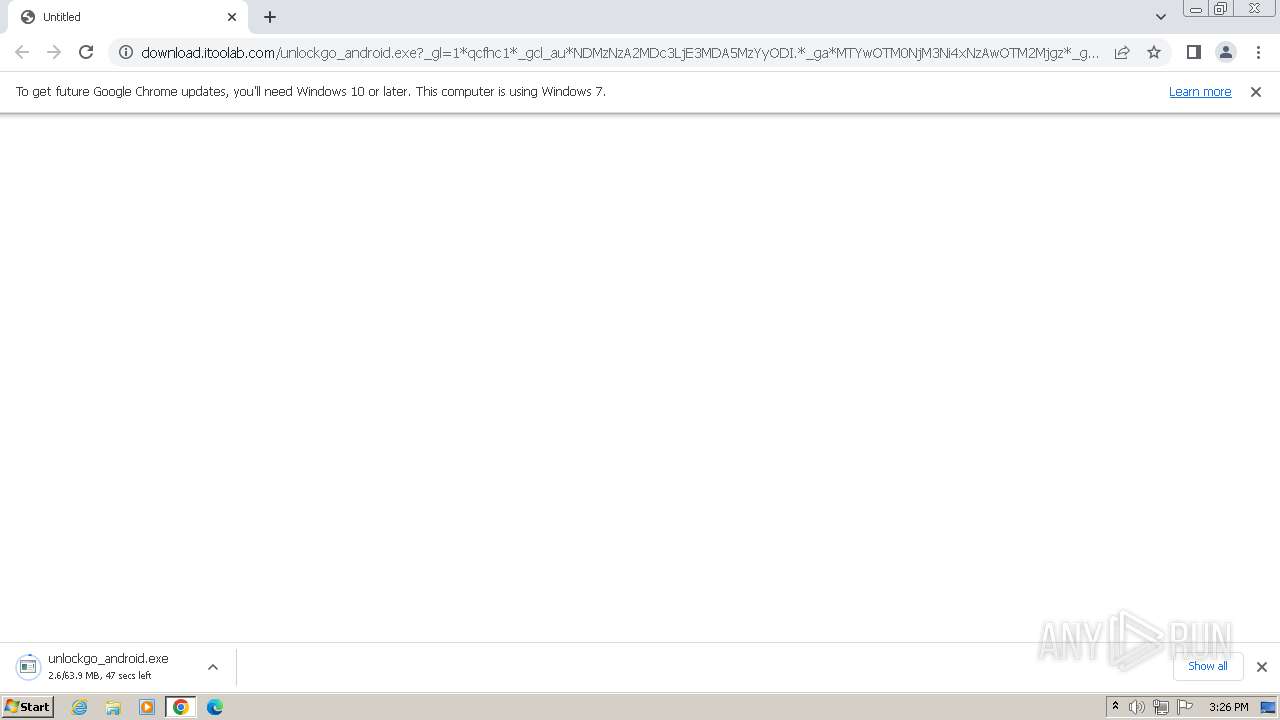
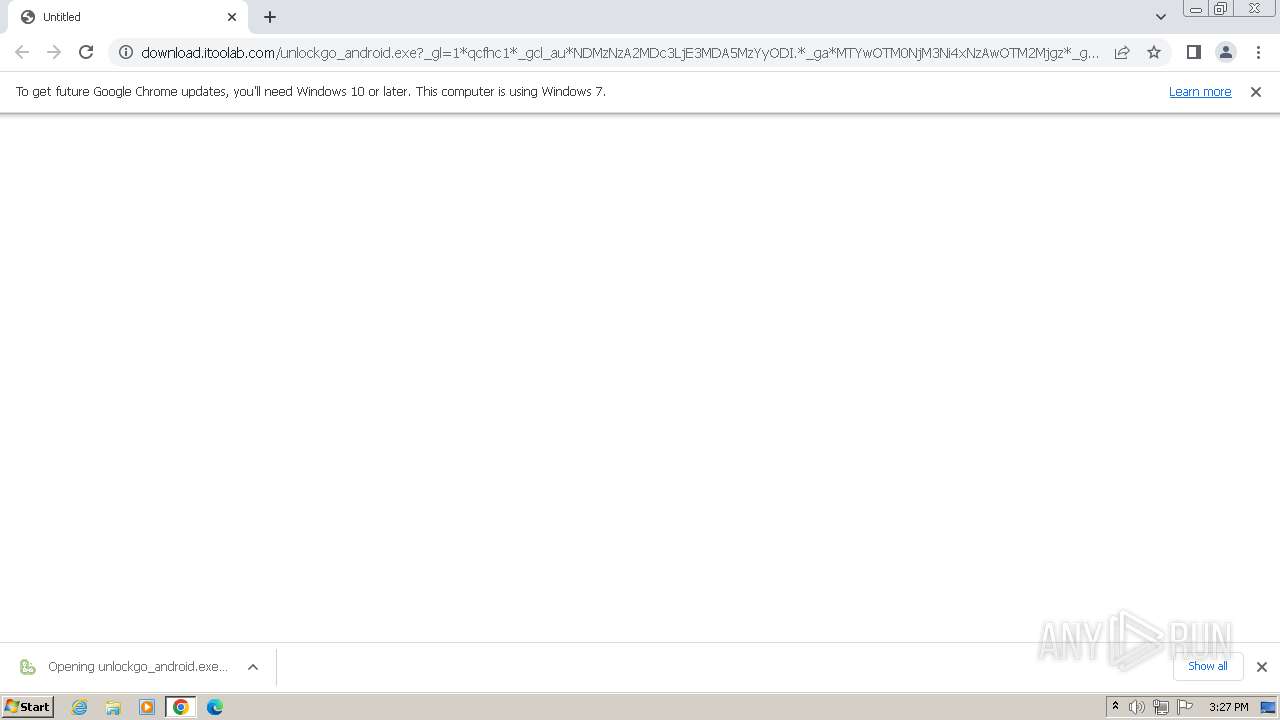
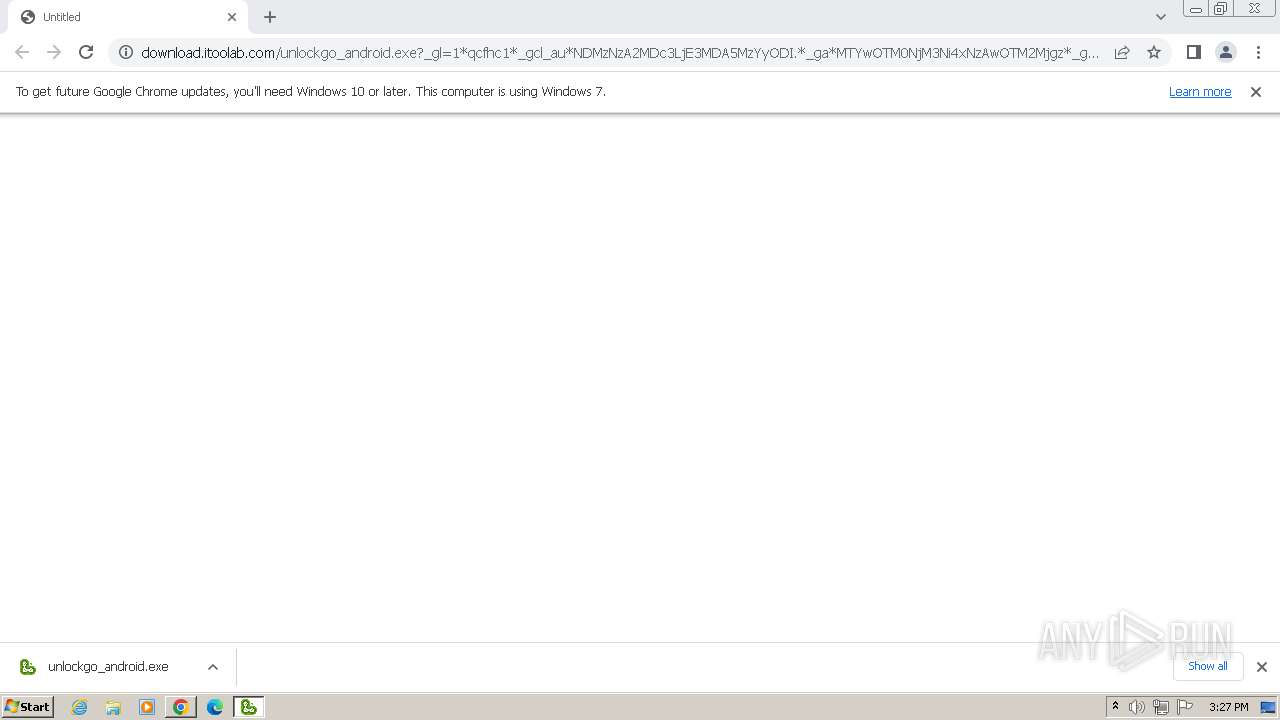
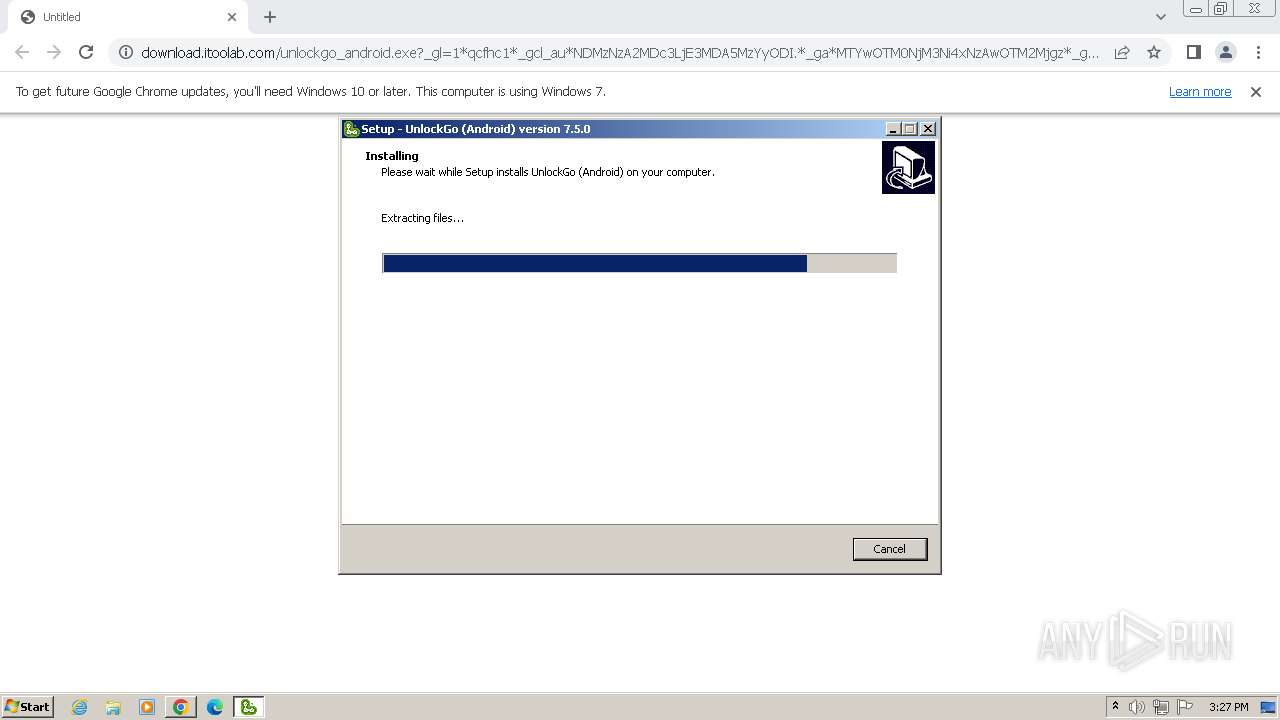
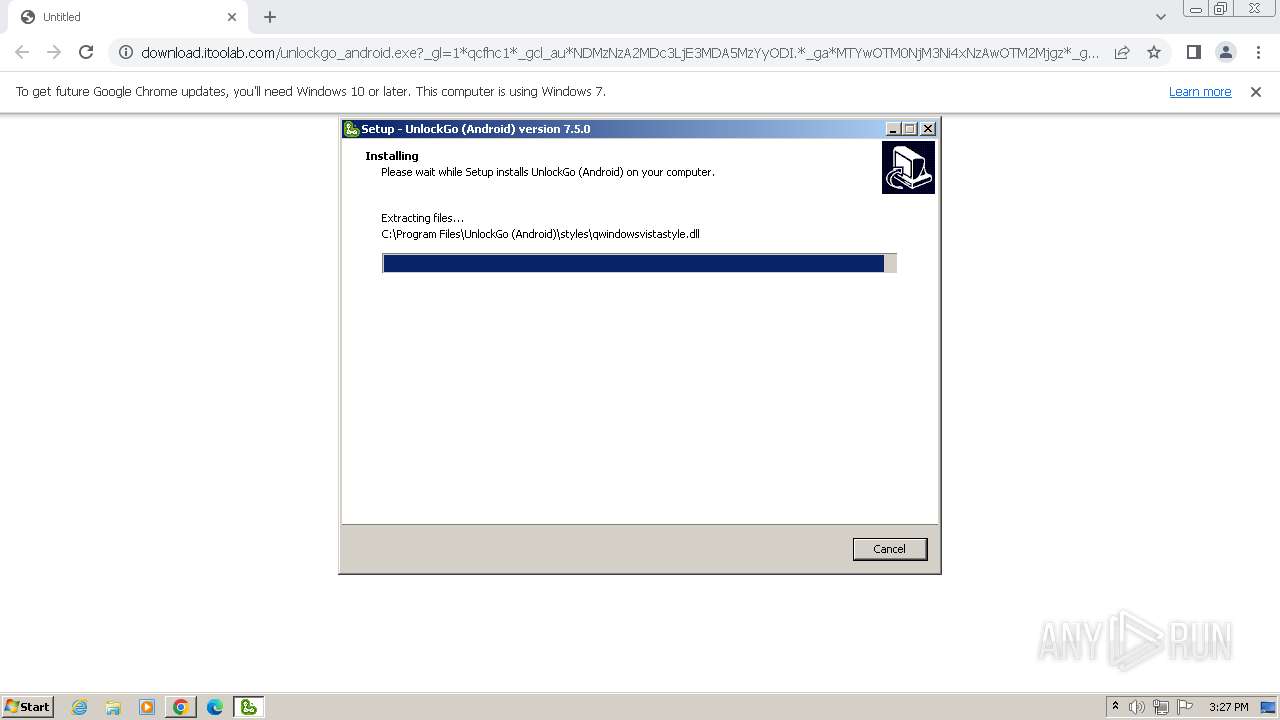
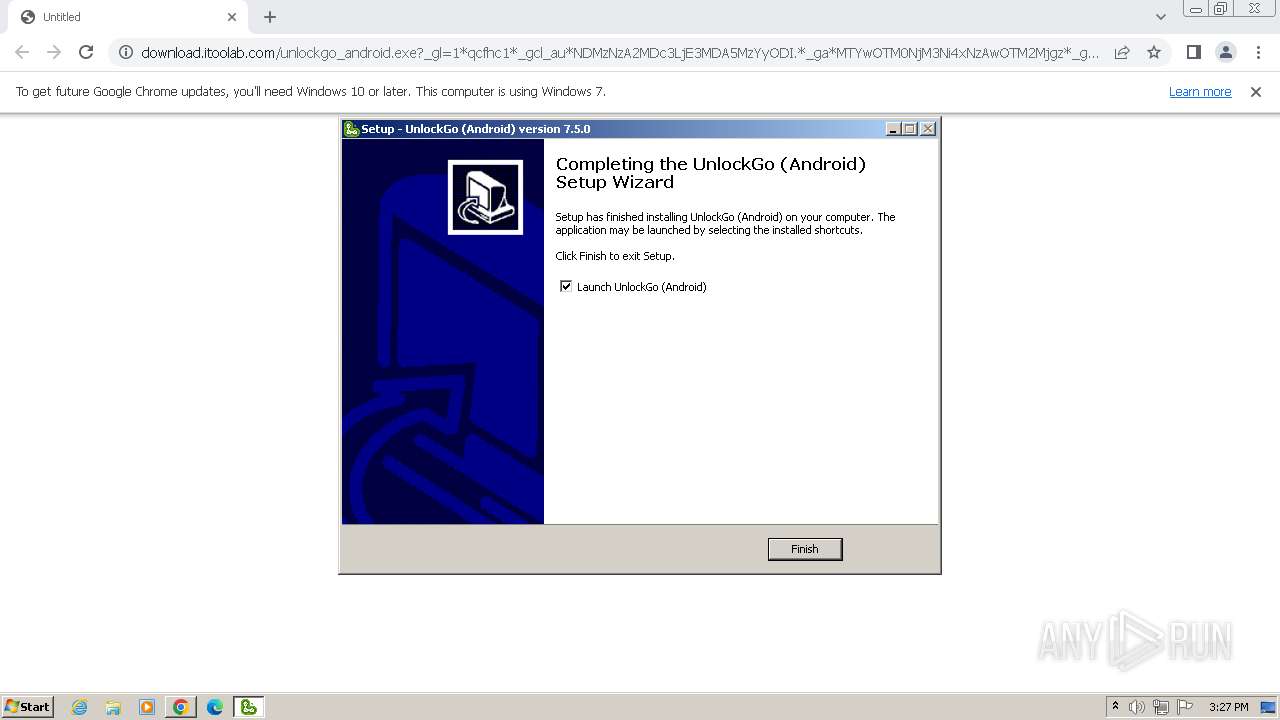
| URL: | https://download.itoolab.com/unlockgo_android.exe?_gl=1*qcfhc1*_gcl_au*NDMzNzA2MDc3LjE3MDA5MzYyODI.*_ga*MTYwOTM0NjM3Ni4xNzAwOTM2Mjgz*_ga_HV4TZRZTZ6*MTcwMDkzNjI4My4xLjEuMTcwMDkzNjczNS41Ny4wLjA. |
| Full analysis: | https://app.any.run/tasks/f25b4d27-bb89-4be6-92ec-5c2cabb41fc6 |
| Verdict: | Malicious activity |
| Analysis date: | November 25, 2023, 15:26:17 |
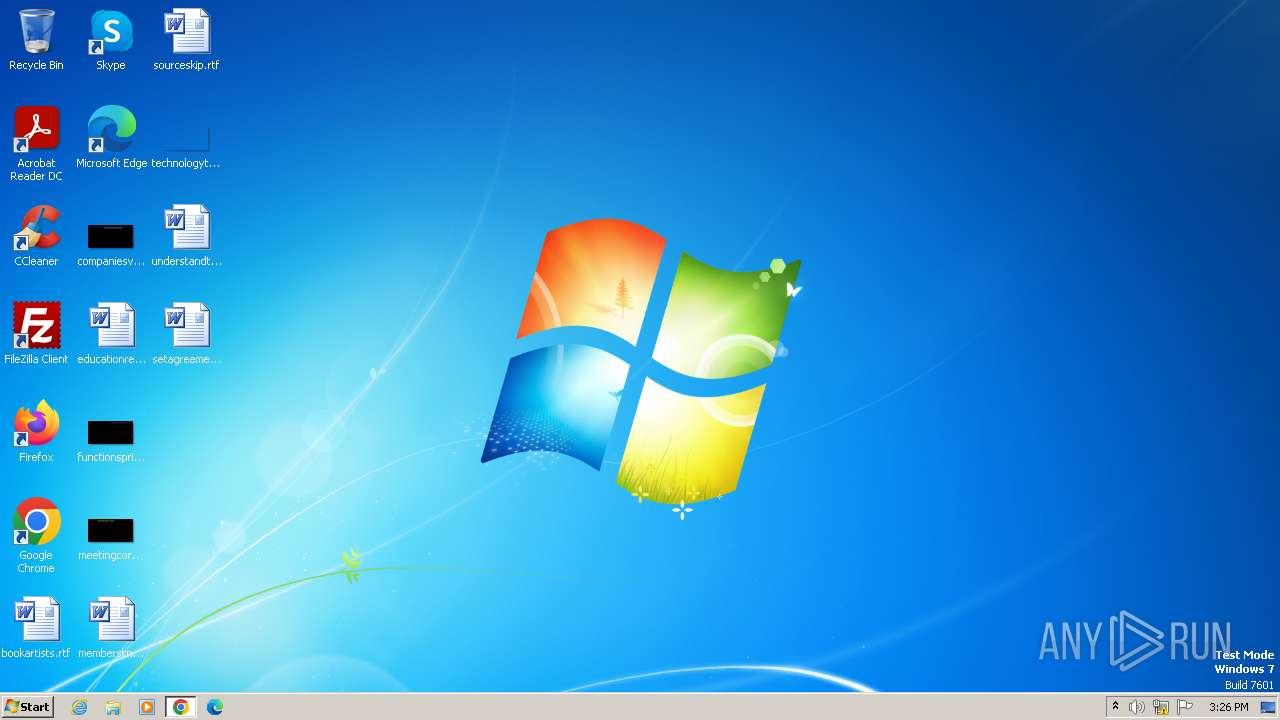
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 79D2930AE7185BCC3F48F0D8598AFD6B07BBA058 |
| SHA256: | 1471A5DD579D1A1F690C14B9C2A44D142B3FA1E242C2A3B988F698A06404FCFE |
| SSDEEP: | 3:N8SEliJuZ3QovhKMBk/6KYUDP36WohBhToLFs9wIfQiSqu3t95x0Y4IETGcu2PRZ:2SKiJOQov9BUYs3CdoRl6C5yrjPPRa6 |
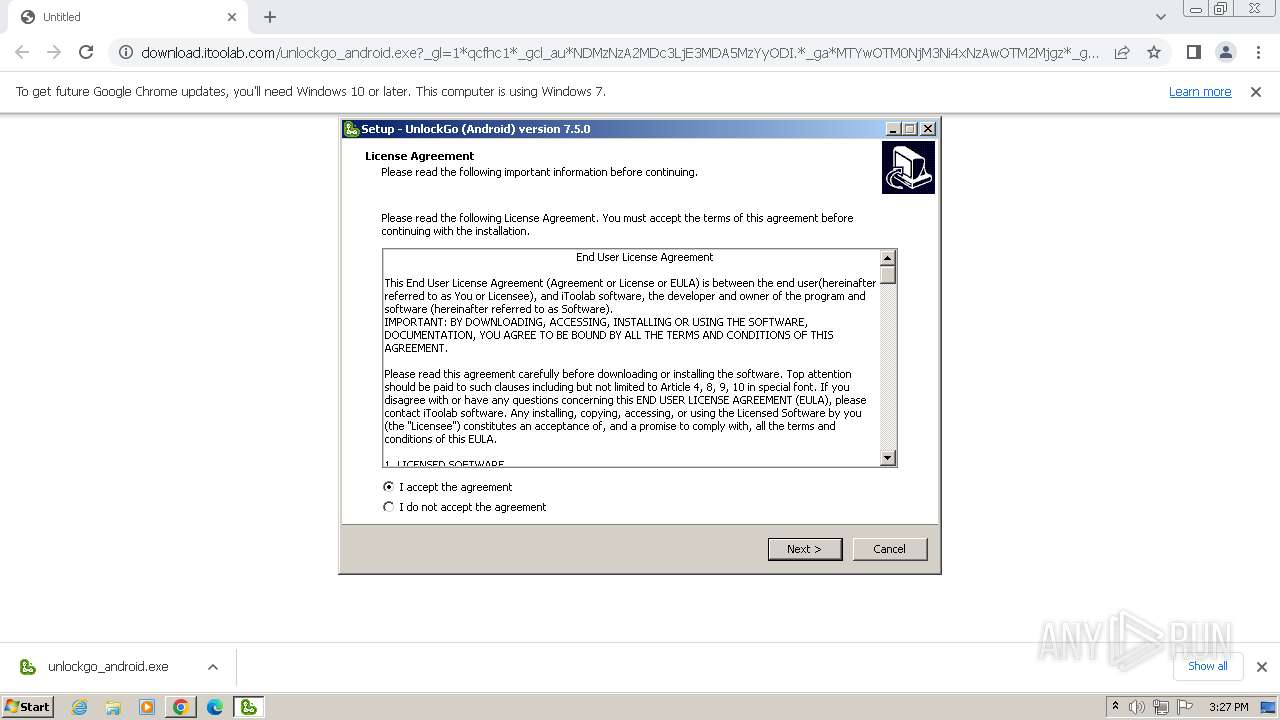
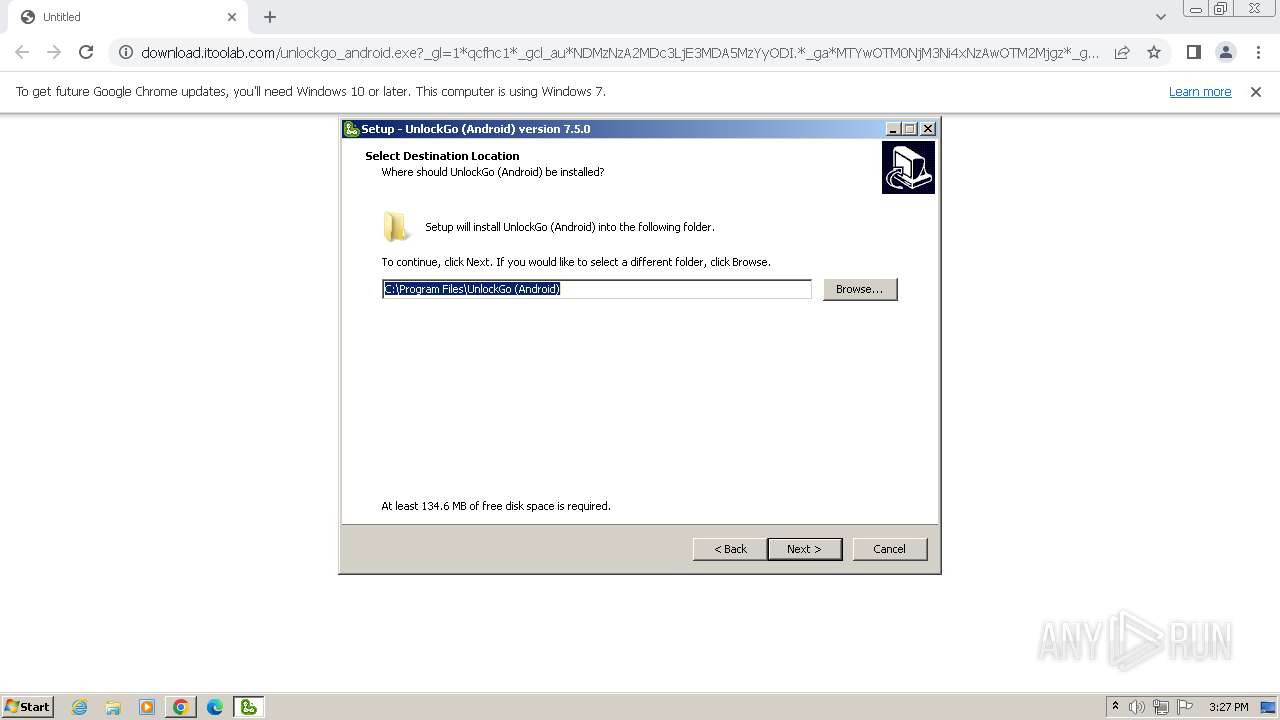
MALICIOUS
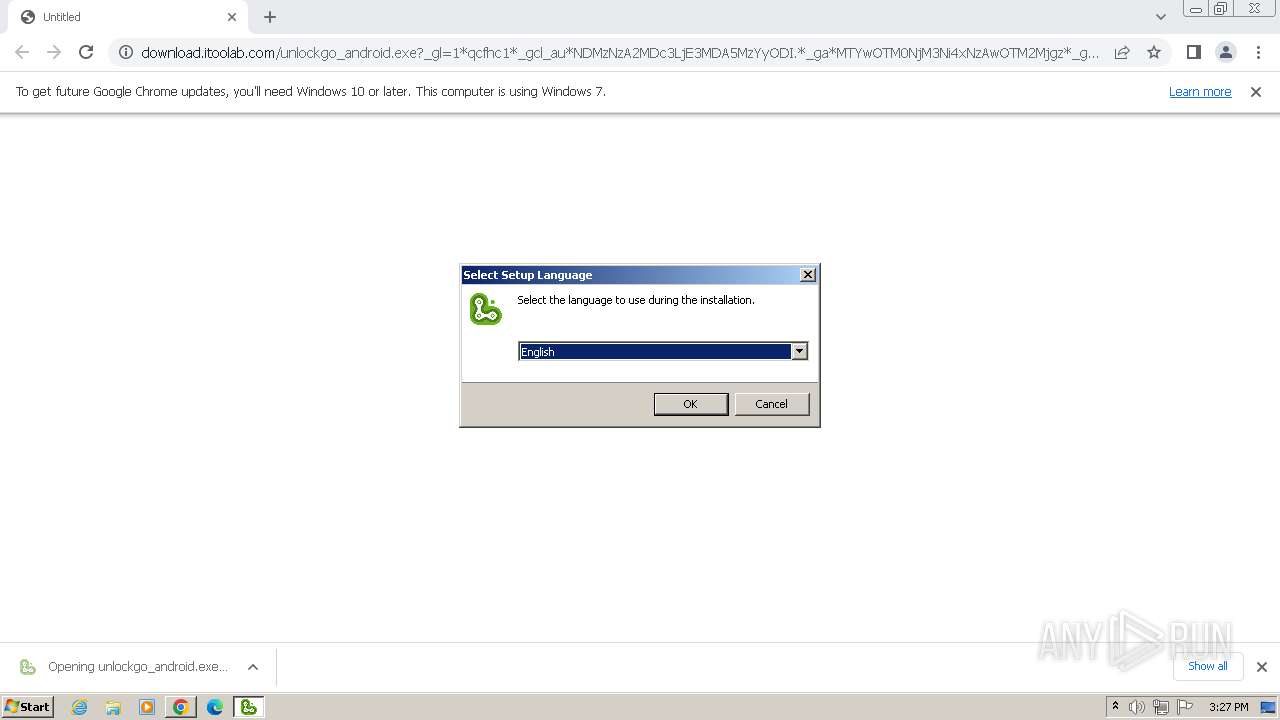
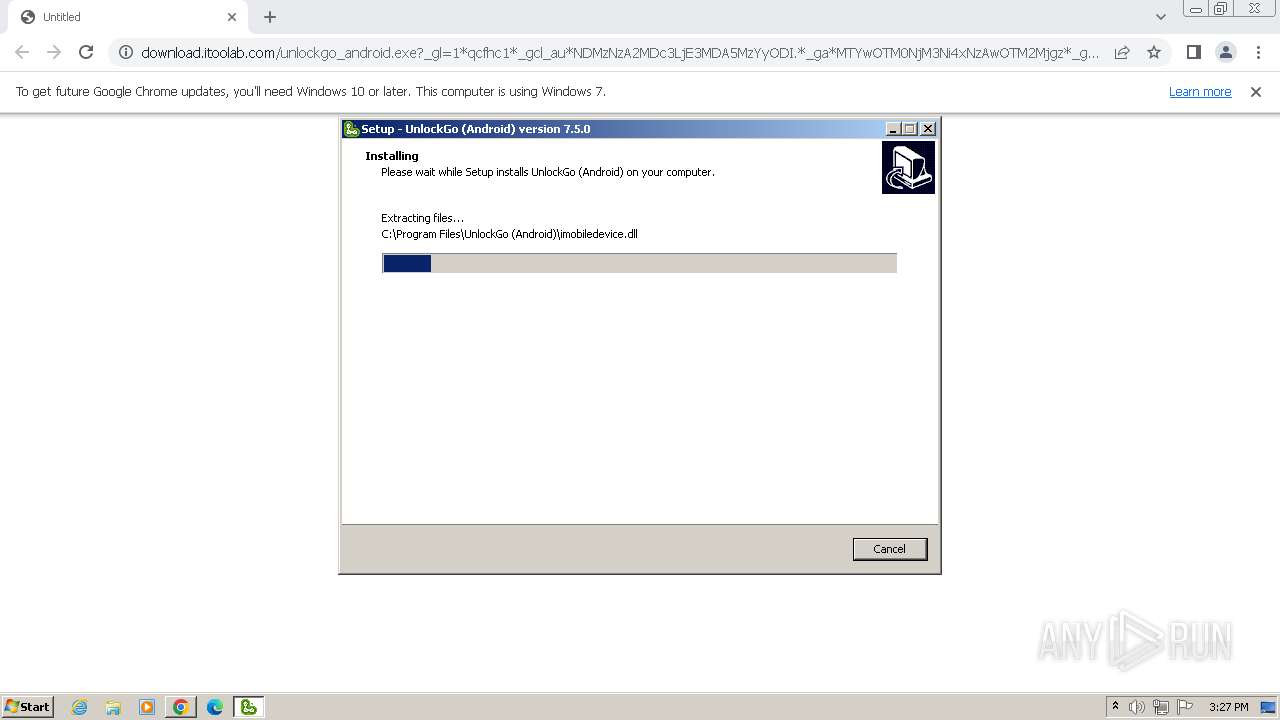
Drops the executable file immediately after the start
- unlockgo_android.exe (PID: 2544)
- DPInst32.exe (PID: 3204)
- drvinst.exe (PID: 3304)
- drvinst.exe (PID: 2088)
- unlockgo_android.tmp (PID: 2268)
Creates a writable file in the system directory
- drvinst.exe (PID: 3304)
SUSPICIOUS
Starts CMD.EXE for commands execution
- unlockgo_android.tmp (PID: 2268)
Reads the Windows owner or organization settings
- unlockgo_android.tmp (PID: 2268)
Get information on the list of running processes
- unlockgo_android.tmp (PID: 2268)
- cmd.exe (PID: 1848)
Reads the Internet Settings
- unlockgo_android.tmp (PID: 2268)
- UnlockGo-Android.exe (PID: 968)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2884)
- cmd.exe (PID: 2788)
Drops a system driver (possible attempt to evade defenses)
- unlockgo_android.tmp (PID: 2268)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 1848)
Process drops legitimate windows executable
- unlockgo_android.tmp (PID: 2268)
- DPInst32.exe (PID: 3204)
- drvinst.exe (PID: 3304)
- drvinst.exe (PID: 2088)
Process drops SQLite DLL files
- unlockgo_android.tmp (PID: 2268)
Reads settings of System Certificates
- UnlockGo-Android.exe (PID: 968)
The process drops C-runtime libraries
- unlockgo_android.tmp (PID: 2268)
Creates files in the driver directory
- drvinst.exe (PID: 3304)
Executes as Windows Service
- VSSVC.exe (PID: 3664)
Checks Windows Trust Settings
- drvinst.exe (PID: 3304)
Application launched itself
- adb.exe (PID: 3340)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 1992)
- unlockgo_android.tmp (PID: 2268)
- UnlockGo-Android.exe (PID: 968)
- DPInst32.exe (PID: 3204)
- drvinst.exe (PID: 3304)
- adb.exe (PID: 3412)
Checks supported languages
- wmpnscfg.exe (PID: 1992)
- unlockgo_android.exe (PID: 2544)
- unlockgo_android.tmp (PID: 2268)
- certmgr.exe (PID: 3156)
- UnlockGo-Android.exe (PID: 968)
- DPInst32.exe (PID: 3204)
- drvinst.exe (PID: 3304)
- adb.exe (PID: 3340)
- adb.exe (PID: 3412)
Manual execution by a user
- wmpnscfg.exe (PID: 1992)
- msedge.exe (PID: 3648)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 1992)
- UnlockGo-Android.exe (PID: 968)
- DPInst32.exe (PID: 3204)
- drvinst.exe (PID: 3304)
The process uses the downloaded file
- chrome.exe (PID: 3664)
- chrome.exe (PID: 900)
- chrome.exe (PID: 3272)
- chrome.exe (PID: 3376)
- chrome.exe (PID: 2128)
Create files in a temporary directory
- unlockgo_android.exe (PID: 2544)
- UnlockGo-Android.exe (PID: 968)
- DPInst32.exe (PID: 3204)
- adb.exe (PID: 3412)
Drops the executable file immediately after the start
- chrome.exe (PID: 3376)
Application launched itself
- chrome.exe (PID: 3376)
- msedge.exe (PID: 3400)
- msedge.exe (PID: 3648)
Creates files in the program directory
- UnlockGo-Android.exe (PID: 968)
- unlockgo_android.tmp (PID: 2268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
109
Monitored processes
63
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4148 --field-trial-handle=1504,i,13259607256190347031,10155921456153604795,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 | |||||||||||||||
| 552 | findstr "UnlockGo-Android.exe" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 888 | taskkill /f /t /im adb.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1296 --field-trial-handle=1120,i,15878638118401334713,6595260796432029949,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 948 | taskkill /f /t /im DeviceServer.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 968 | "C:\Program Files\UnlockGo (Android)\UnlockGo-Android.exe" | C:\Program Files\UnlockGo (Android)\UnlockGo-Android.exe | unlockgo_android.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3344 --field-trial-handle=1120,i,15878638118401334713,6595260796432029949,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1440 --field-trial-handle=1120,i,15878638118401334713,6595260796432029949,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2328 --field-trial-handle=1504,i,13259607256190347031,10155921456153604795,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4140 --field-trial-handle=1504,i,13259607256190347031,10155921456153604795,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 | |||||||||||||||
Total events
16 275
Read events
16 077
Write events
190
Delete events
8
Modification events
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
347
Suspicious files
226
Text files
62
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1bdffc.TMP | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1bdffc.TMP | text | |
MD5:D5C9ECBD2DCA29D89266782824D7AF99 | SHA256:D22D1243ACC064A30823180D0E583C853E9395367C78C2AD9DE59A463904F702 | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF1be403.TMP | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:B806171F9E7C87423595645872D869B0 | SHA256:851A8D533BEBF6A69C5518375396E97463302C1E2031D04F8EB5851C5C82CEB9 | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1be125.TMP | text | |
MD5:99EC94B2503FAD33EDAF99779EBA5BC8 | SHA256:DC554AB7EDCAD375F39ED106CA1EF9A89FB8D9063A4D08F377F2C80D66799D7E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
28
DNS requests
51
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 6.13 Kb | unknown |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | — | — | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 10.1 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 10.1 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 13.8 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 10.1 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 36.3 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 79.3 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 181 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | US | binary | 657 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3376 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2252 | chrome.exe | 188.114.97.3:443 | download.itoolab.com | CLOUDFLARENET | NL | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2252 | chrome.exe | 142.250.181.237:443 | accounts.google.com | GOOGLE | US | unknown |
3376 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
2252 | chrome.exe | 142.250.186.164:443 | www.google.com | GOOGLE | US | whitelisted |
2252 | chrome.exe | 142.250.185.202:443 | optimizationguide-pa.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
download.itoolab.com |
| unknown |
www.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
itoolab.com |
| unknown |
Threats
Process | Message |
|---|---|
UnlockGo-Android.exe | libpng warning: iCCP: known incorrect sRGB profile
|
UnlockGo-Android.exe | libpng warning: iCCP: known incorrect sRGB profile
|
UnlockGo-Android.exe | libpng warning: iCCP: known incorrect sRGB profile
|
UnlockGo-Android.exe | libpng warning: iCCP: known incorrect sRGB profile
|