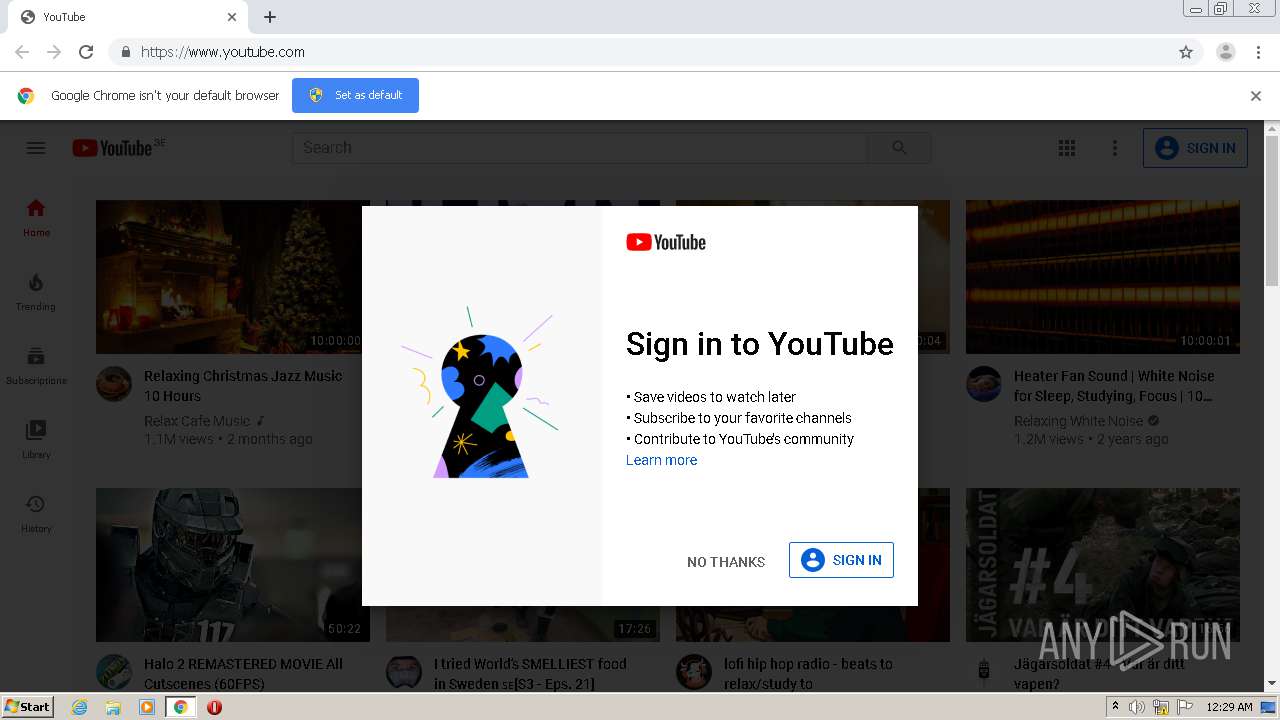
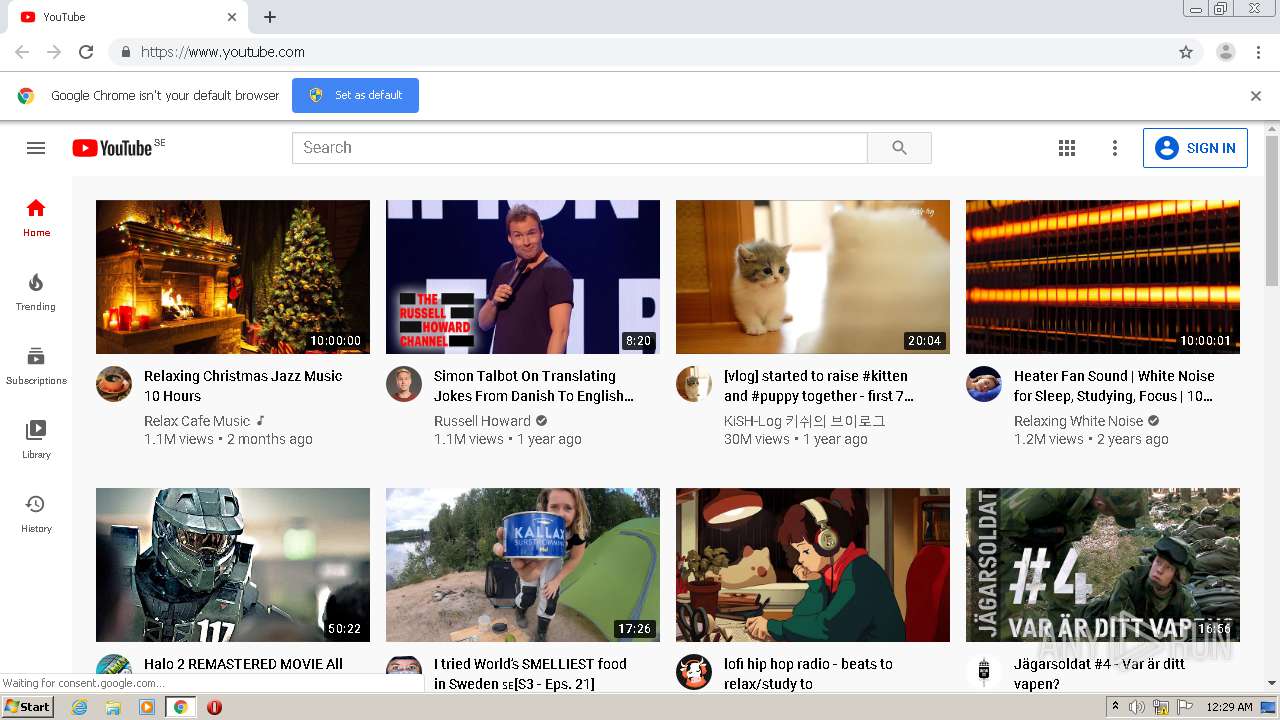
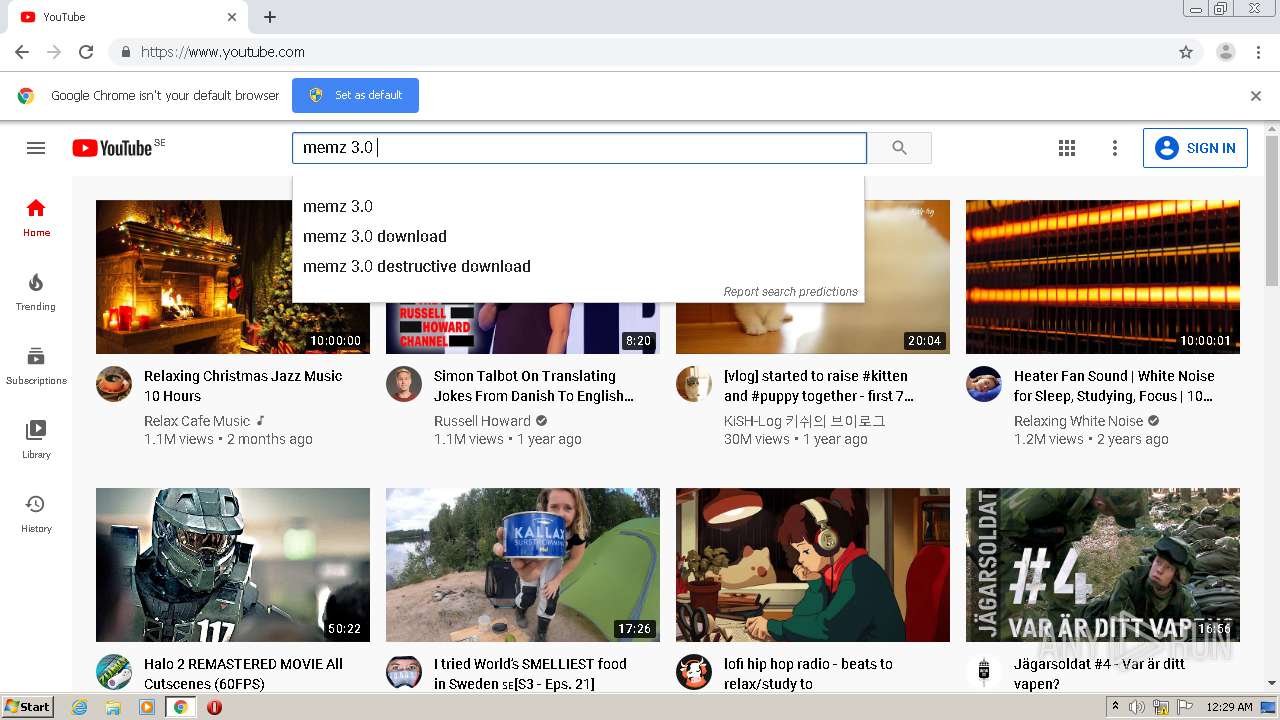
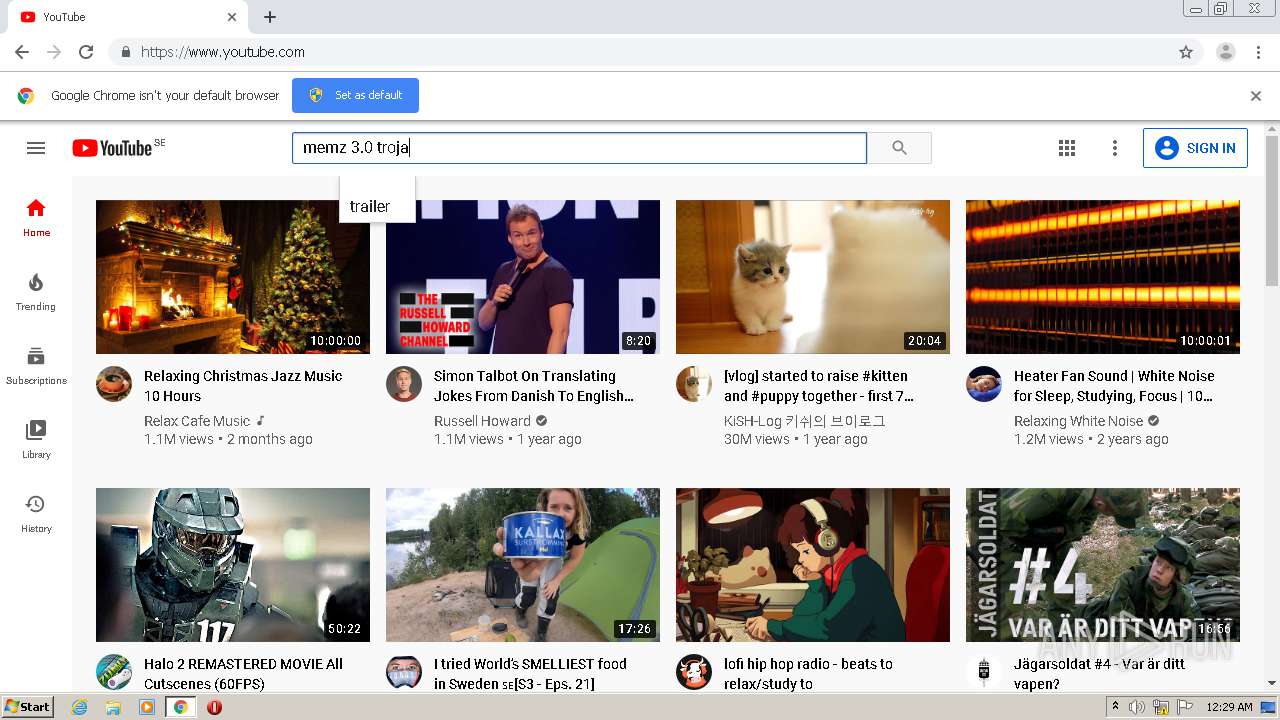
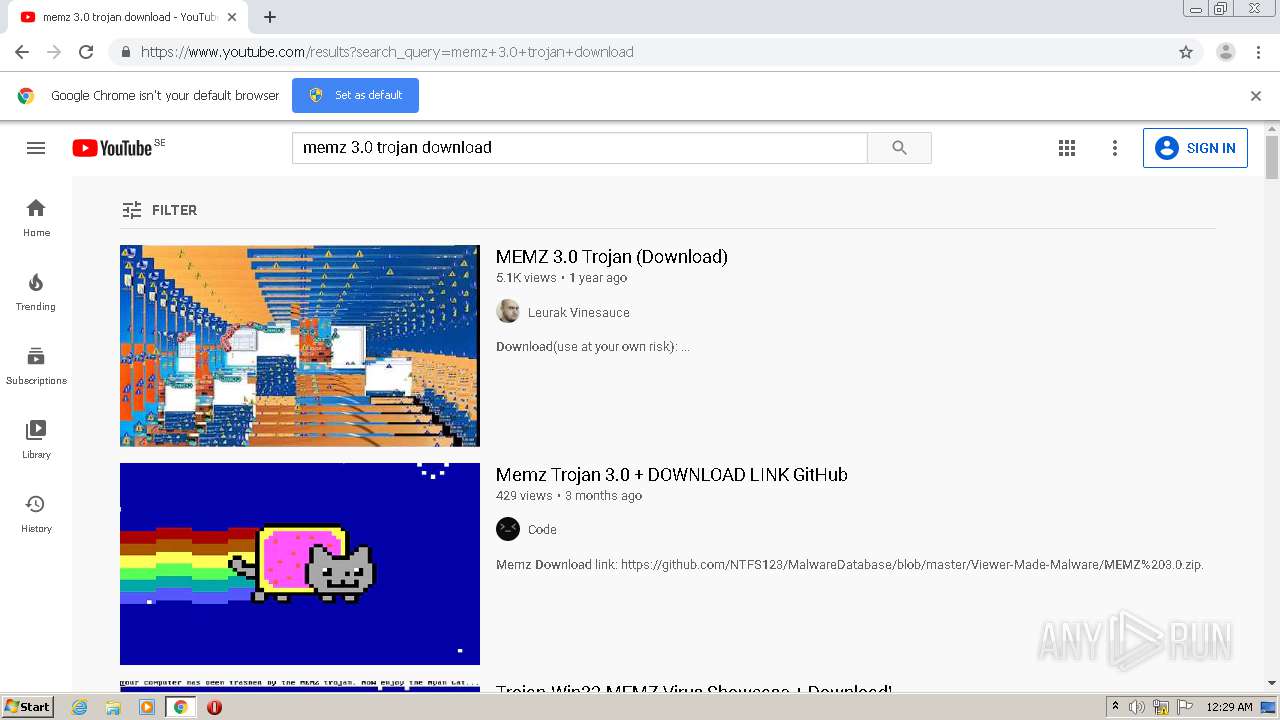
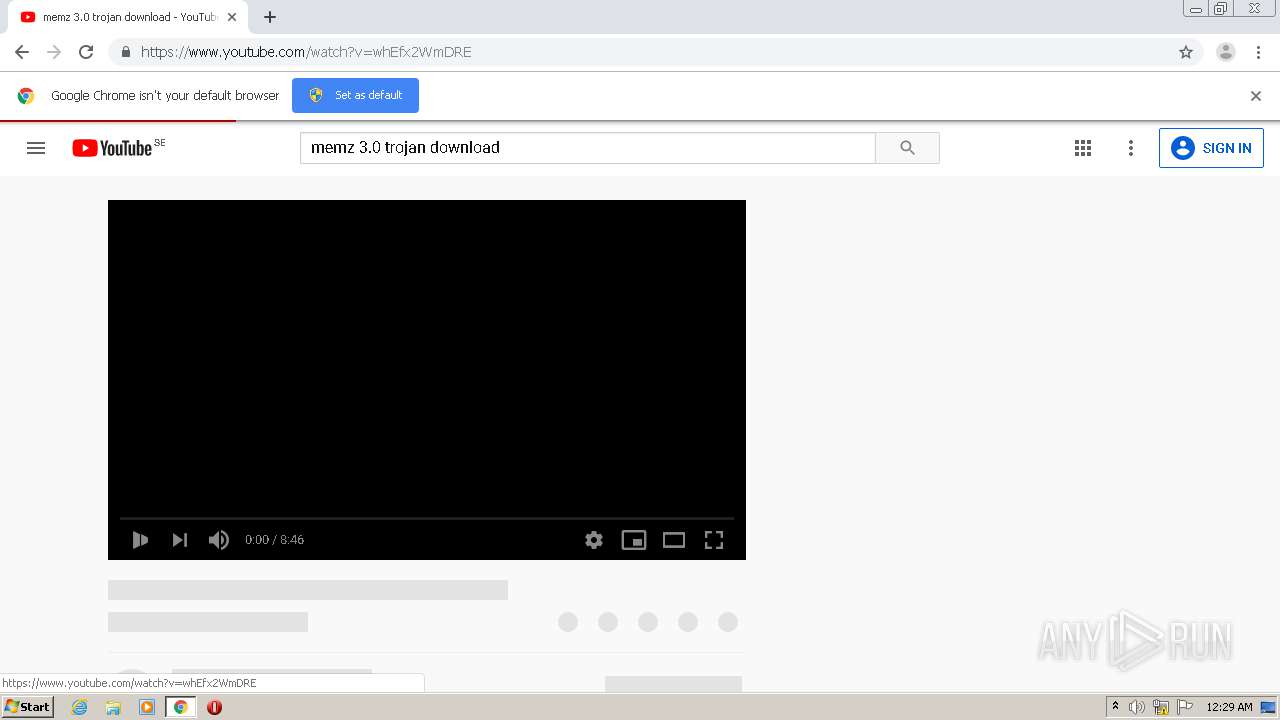
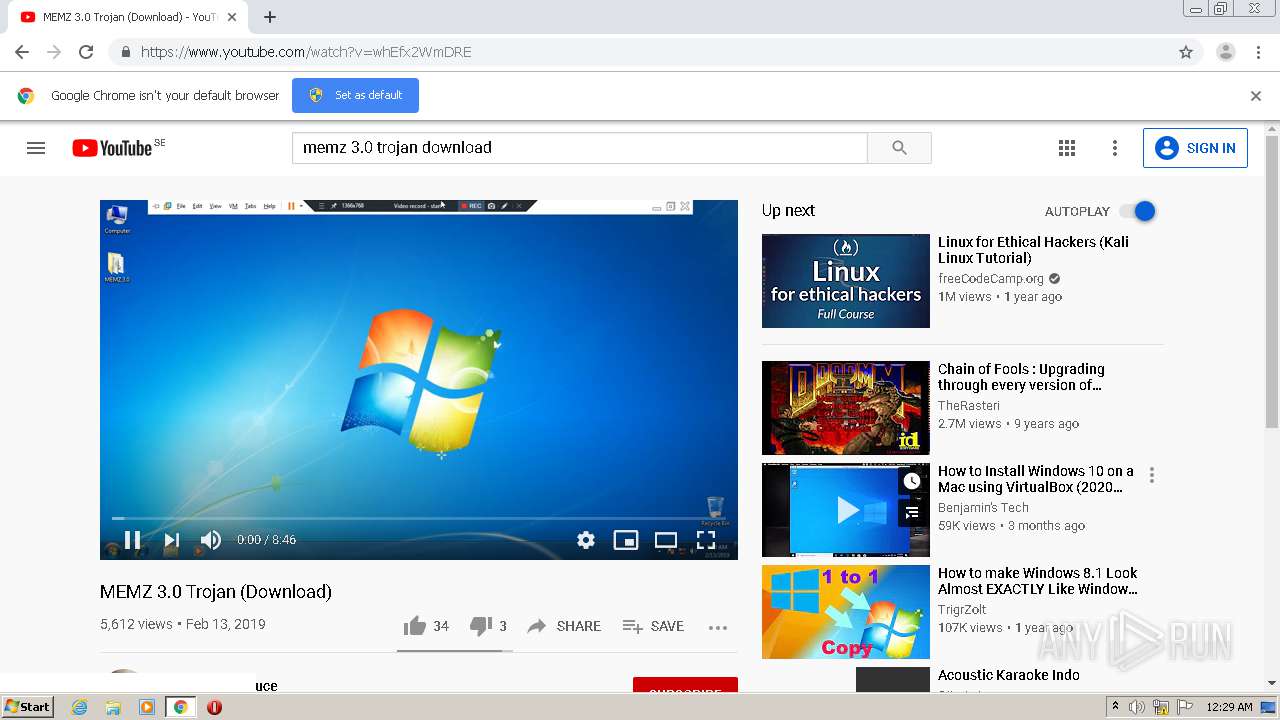
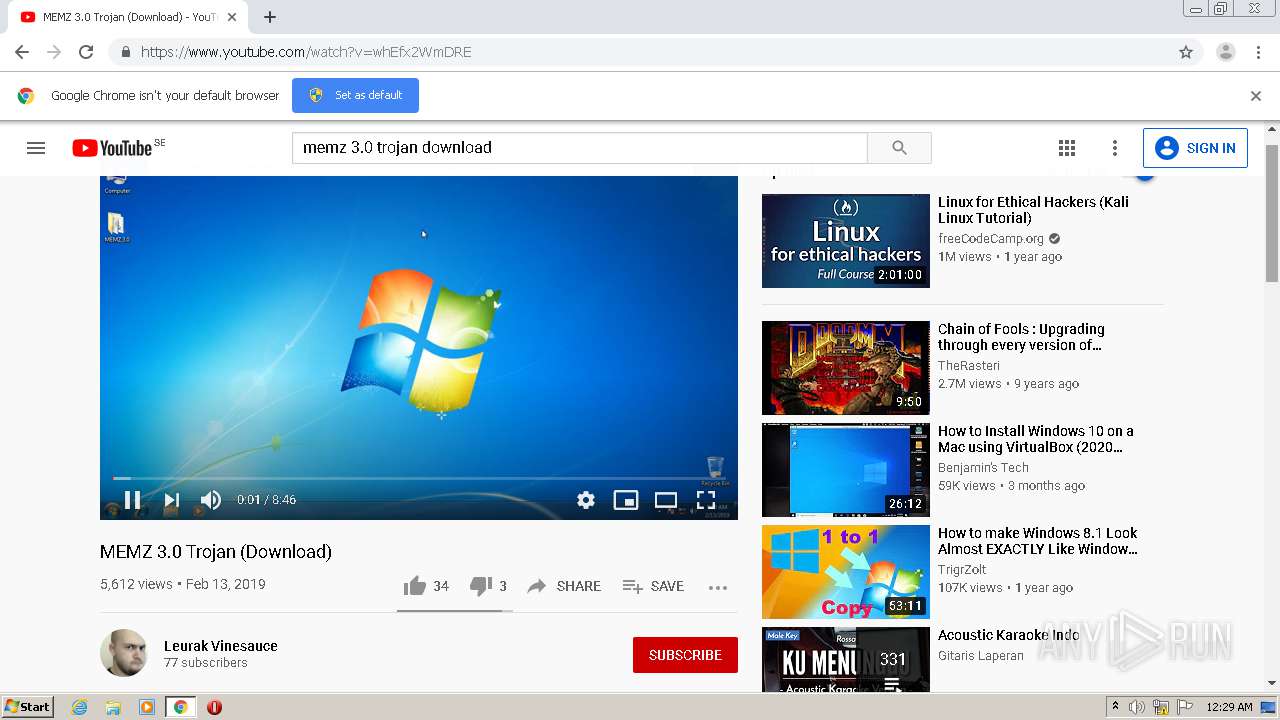
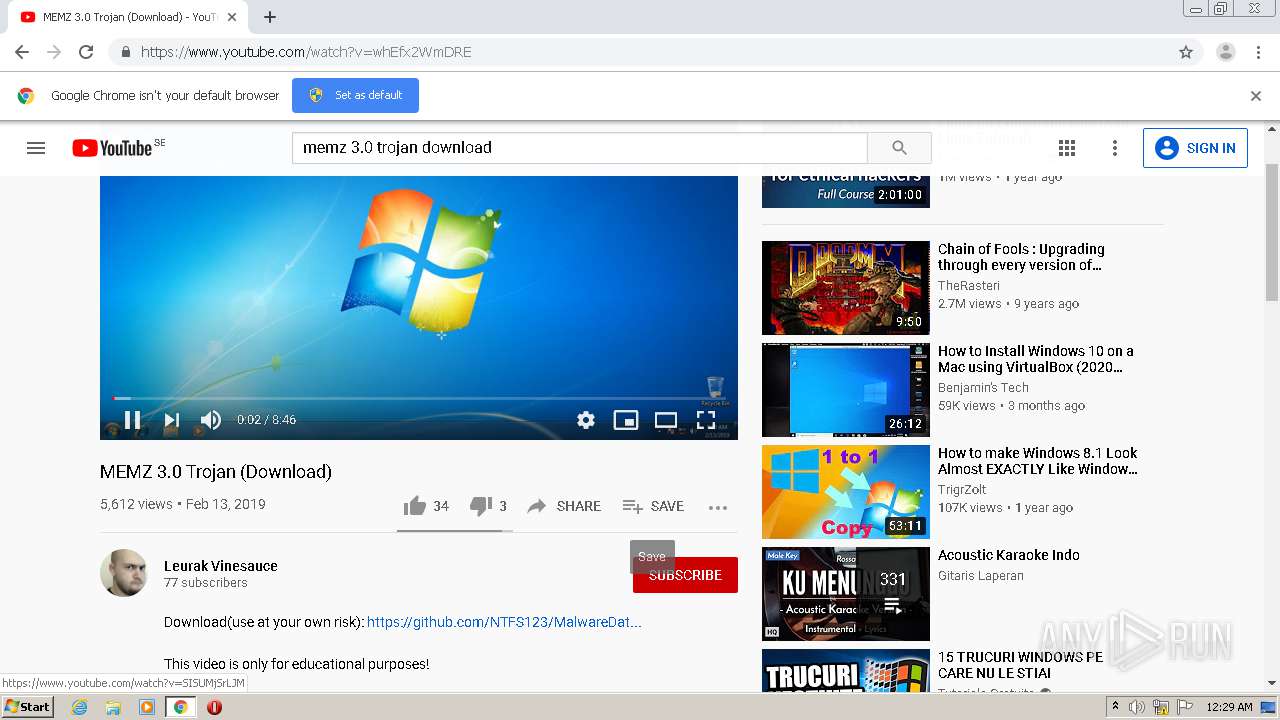
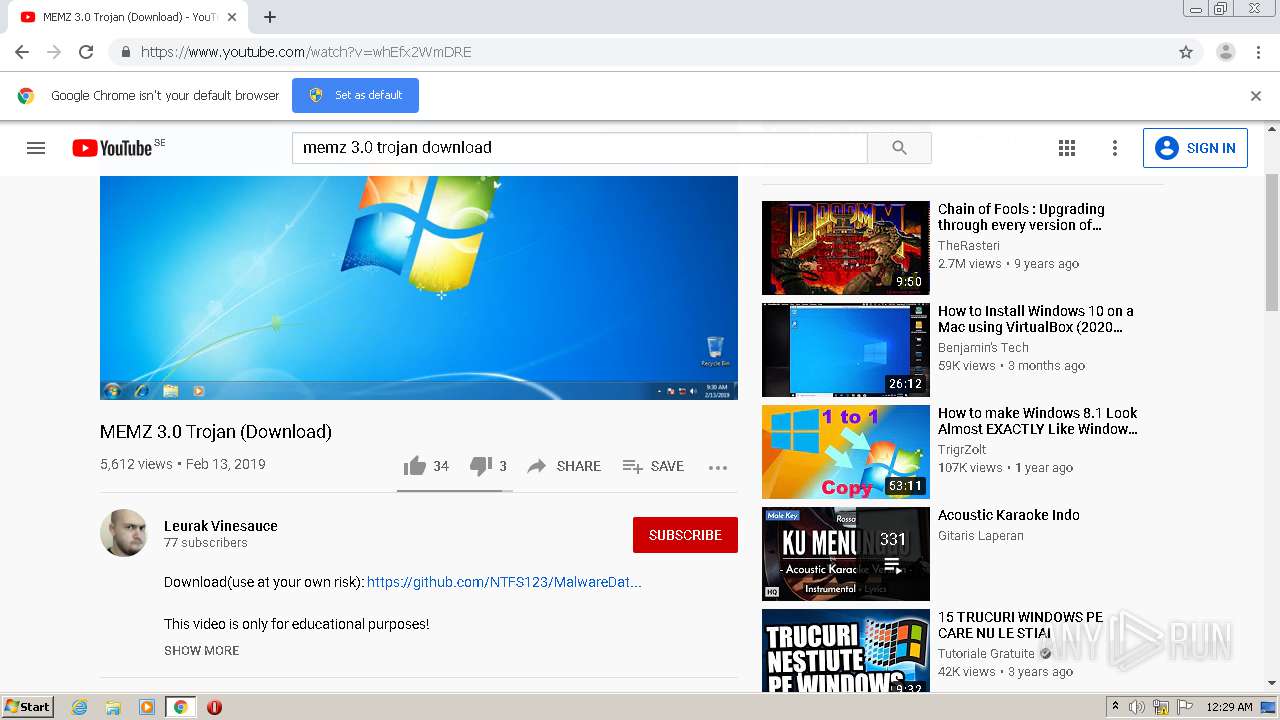
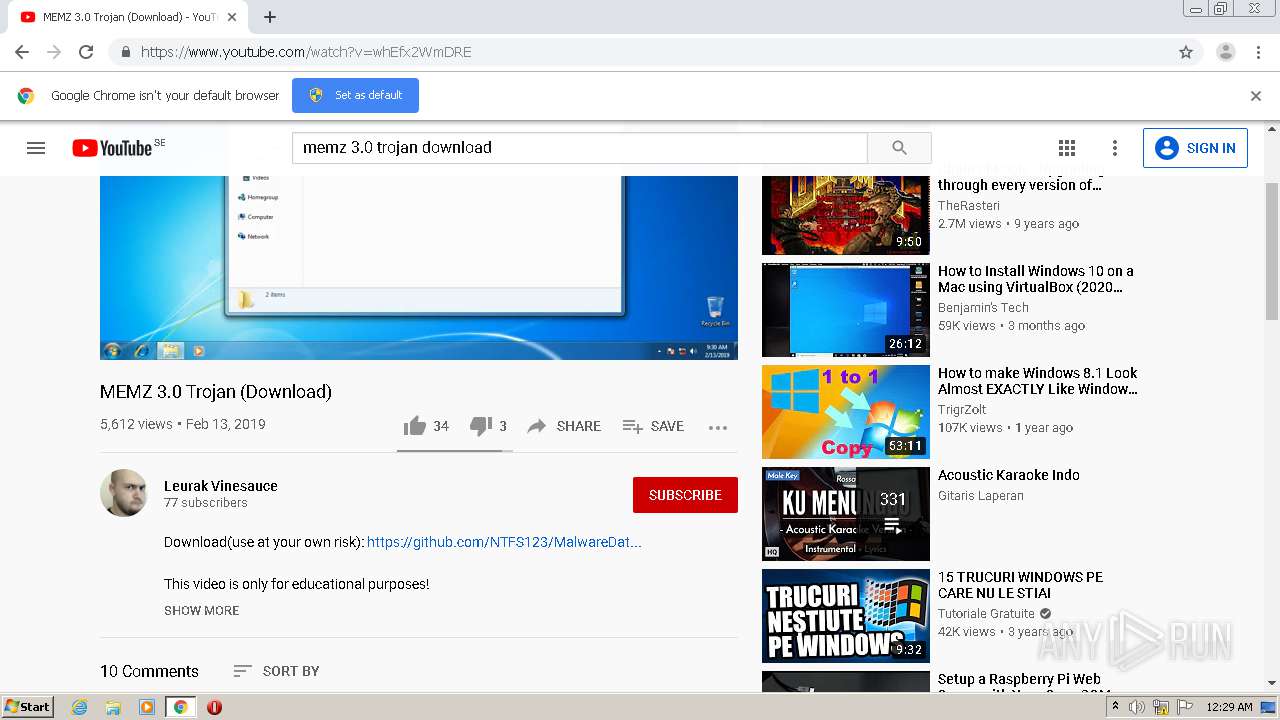
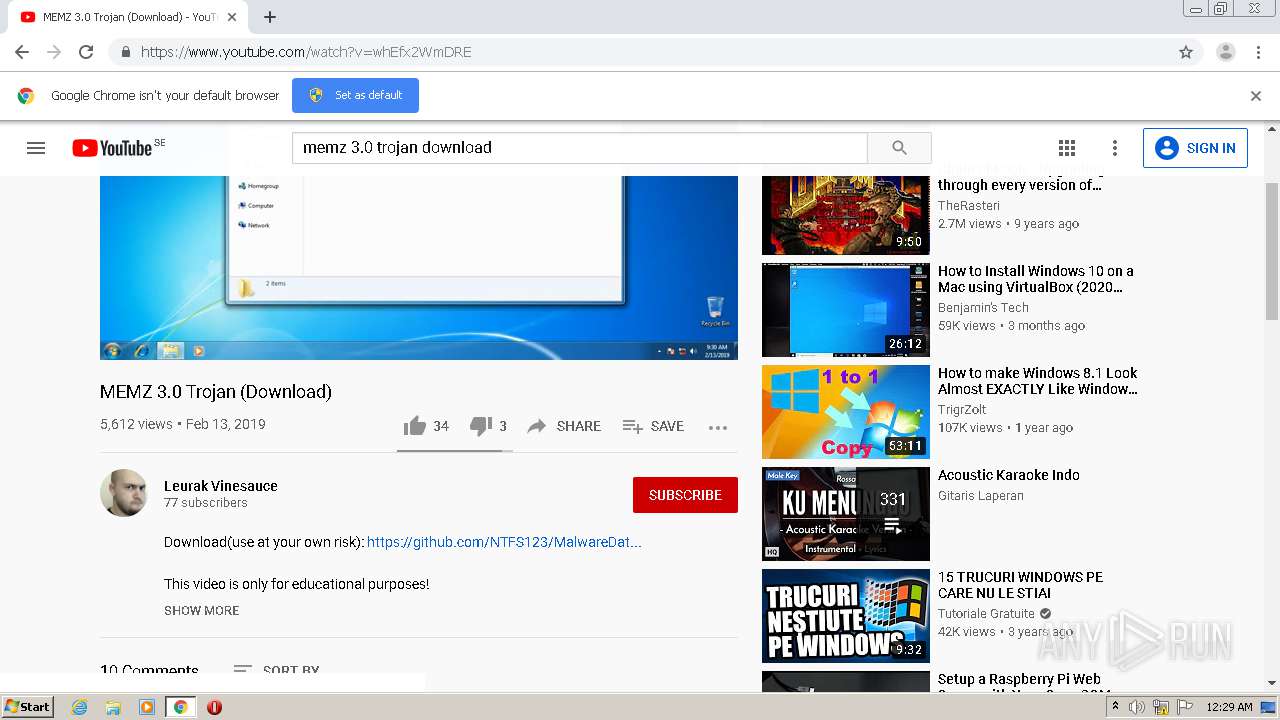
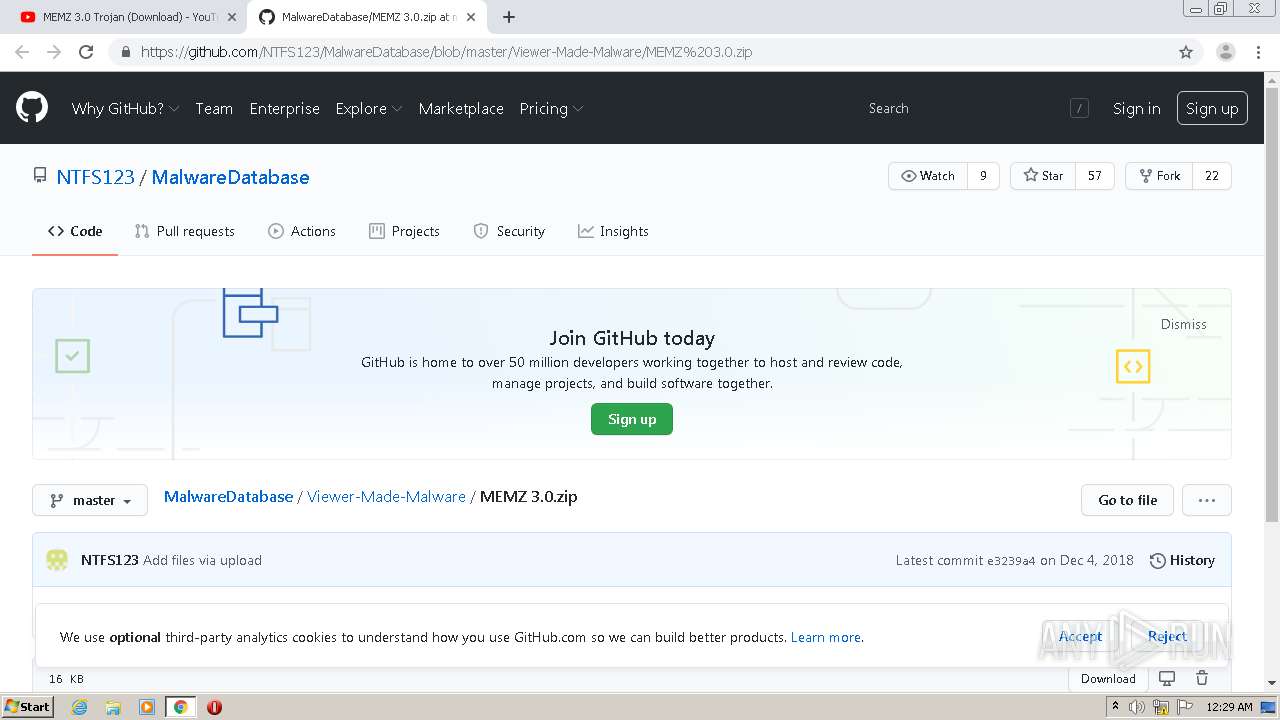
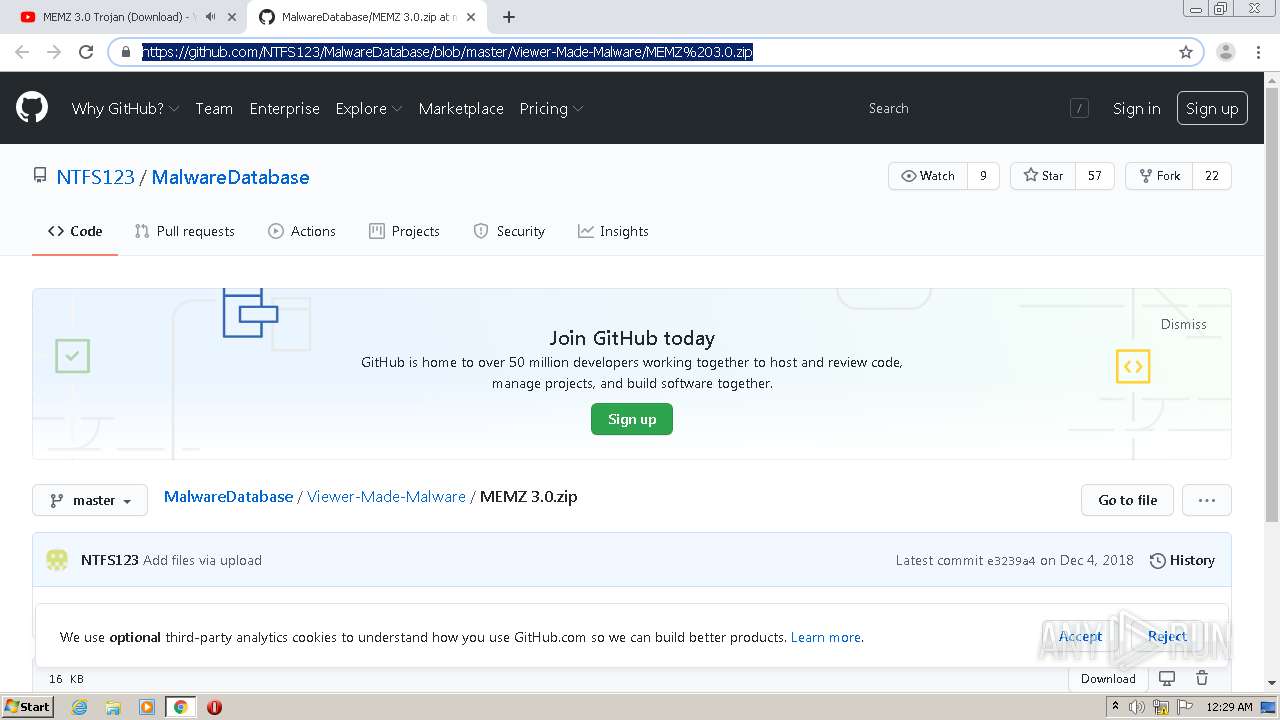
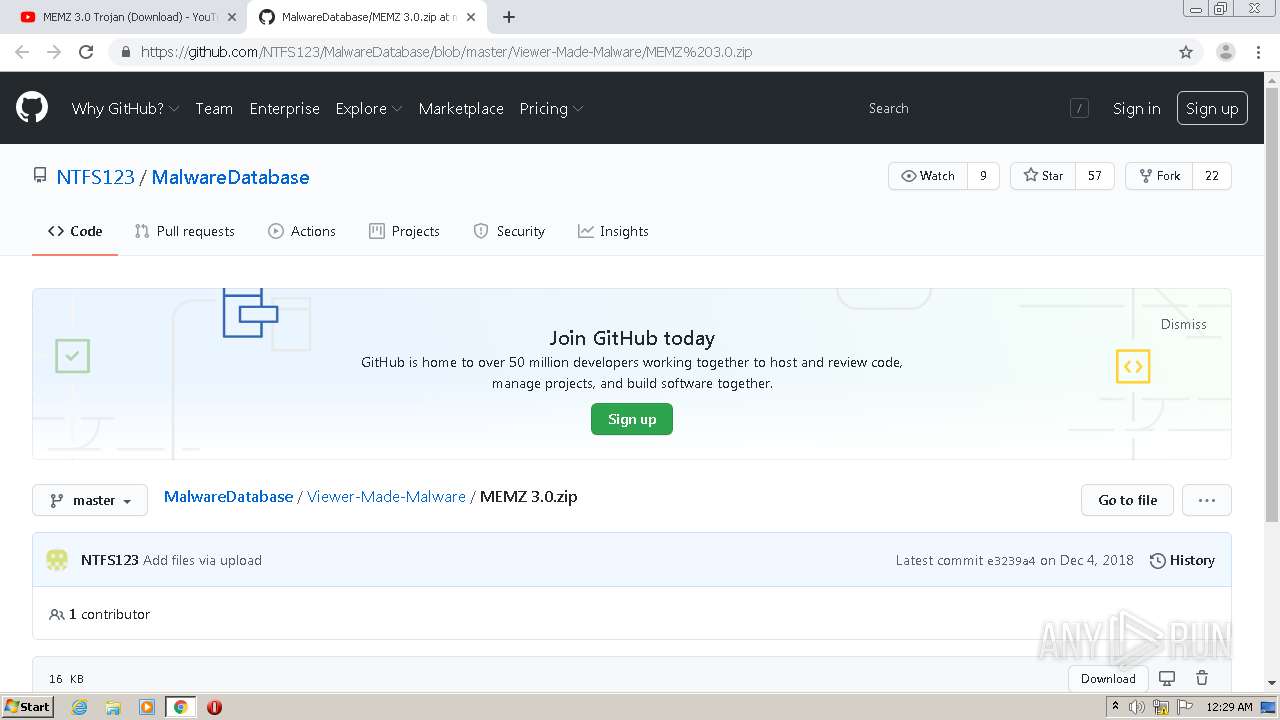
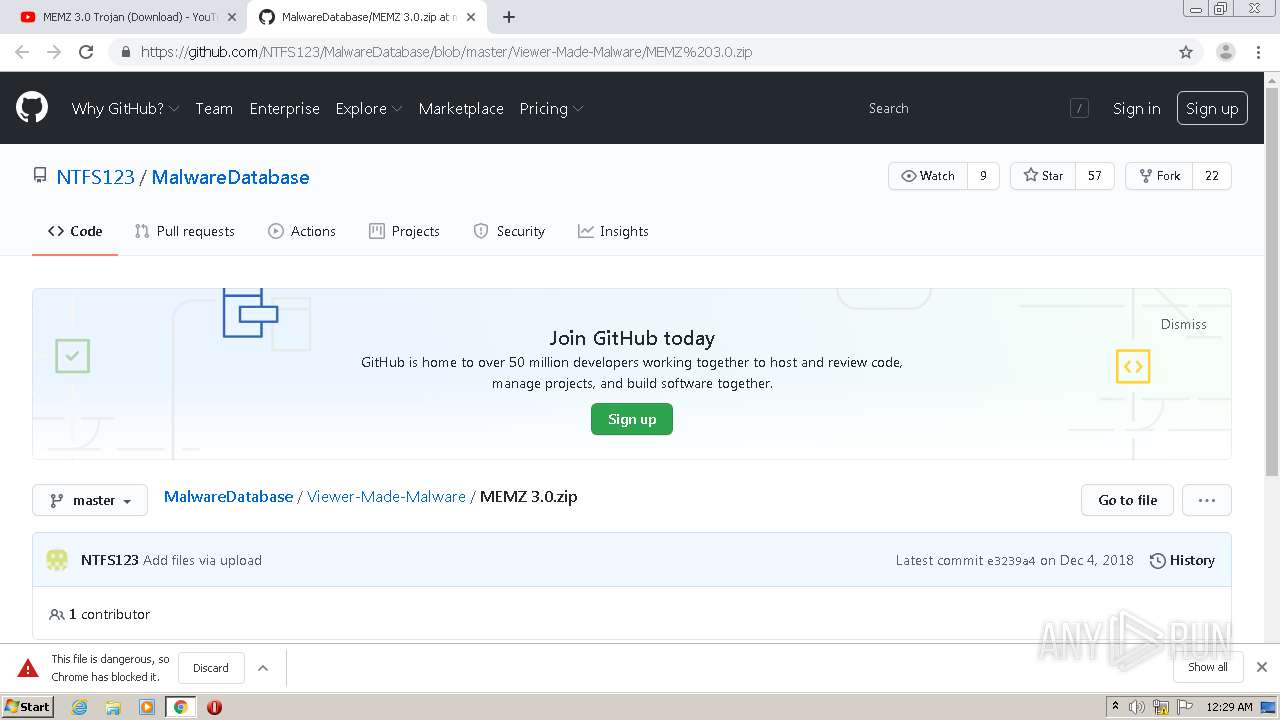
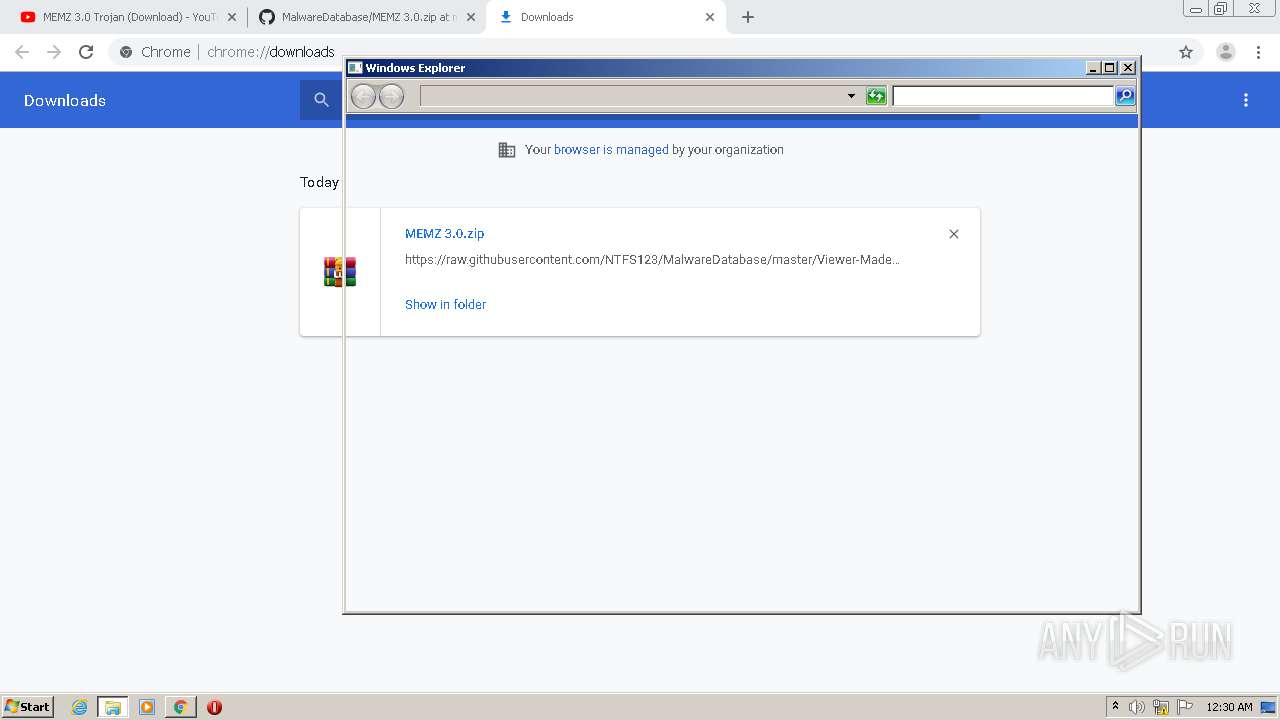
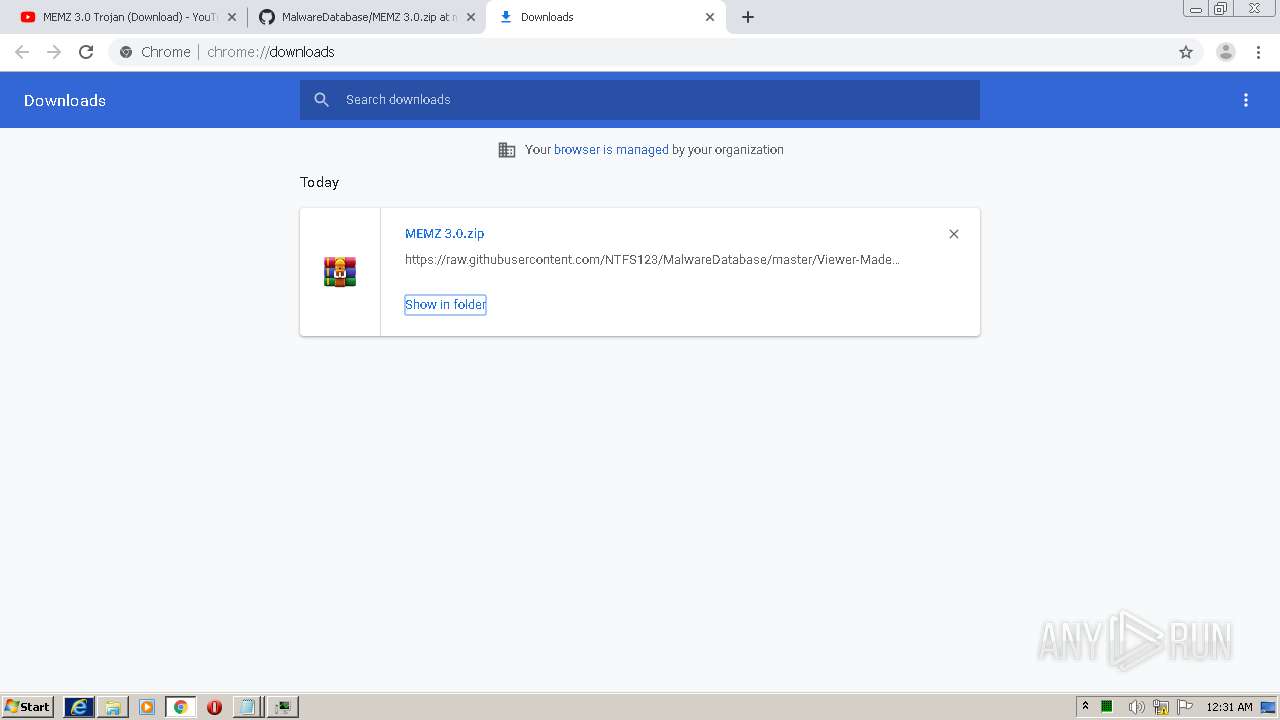
| URL: | https://youtube.com |
| Full analysis: | https://app.any.run/tasks/68c21c8e-1f74-4c4b-978d-d219543e16fd |
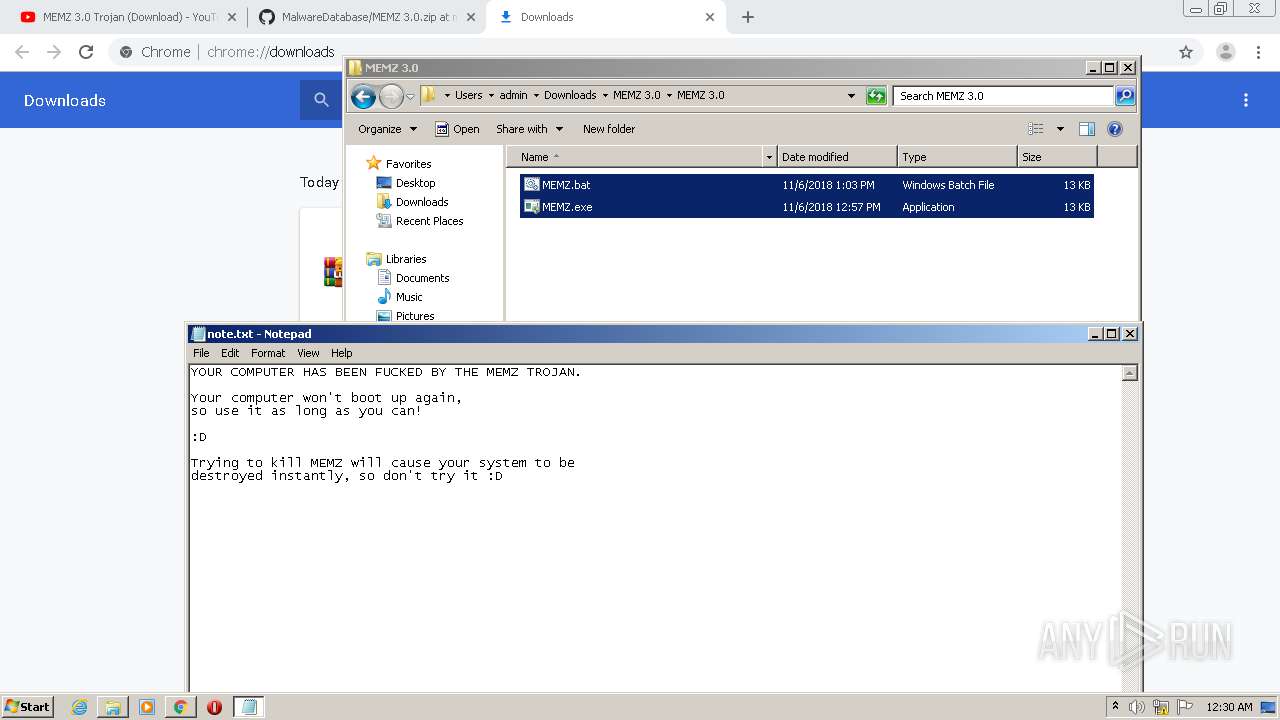
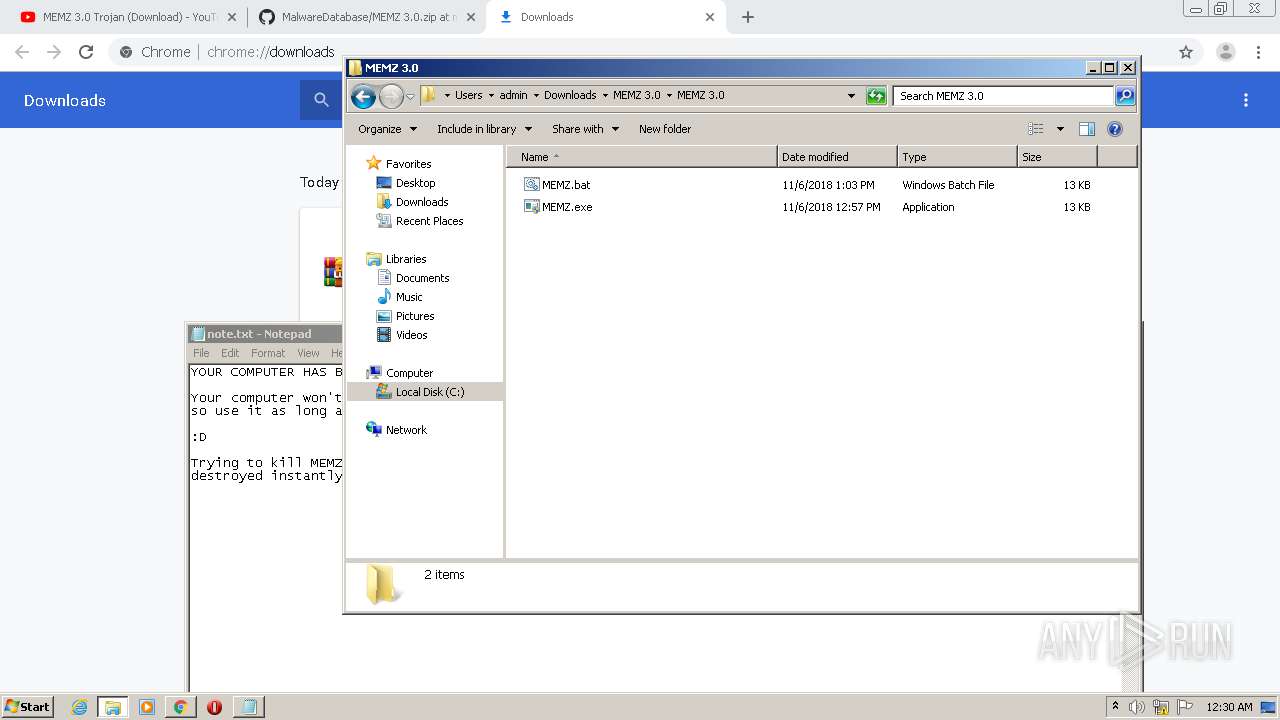
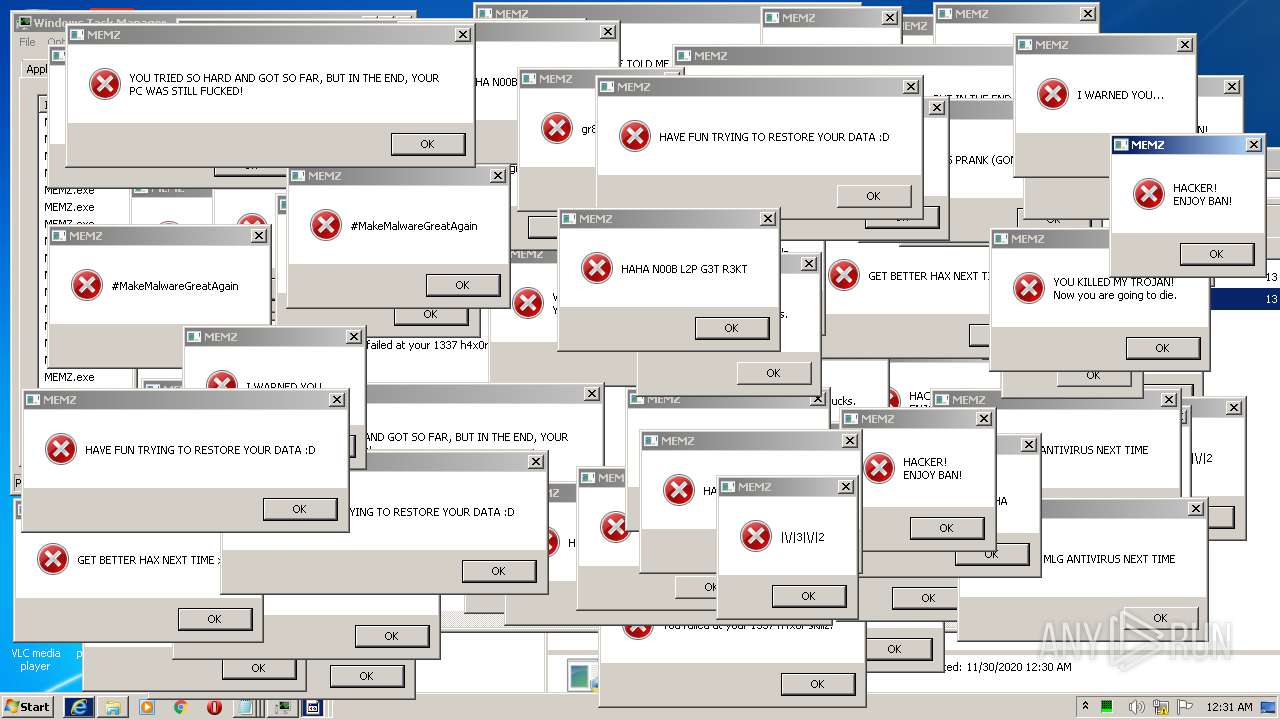
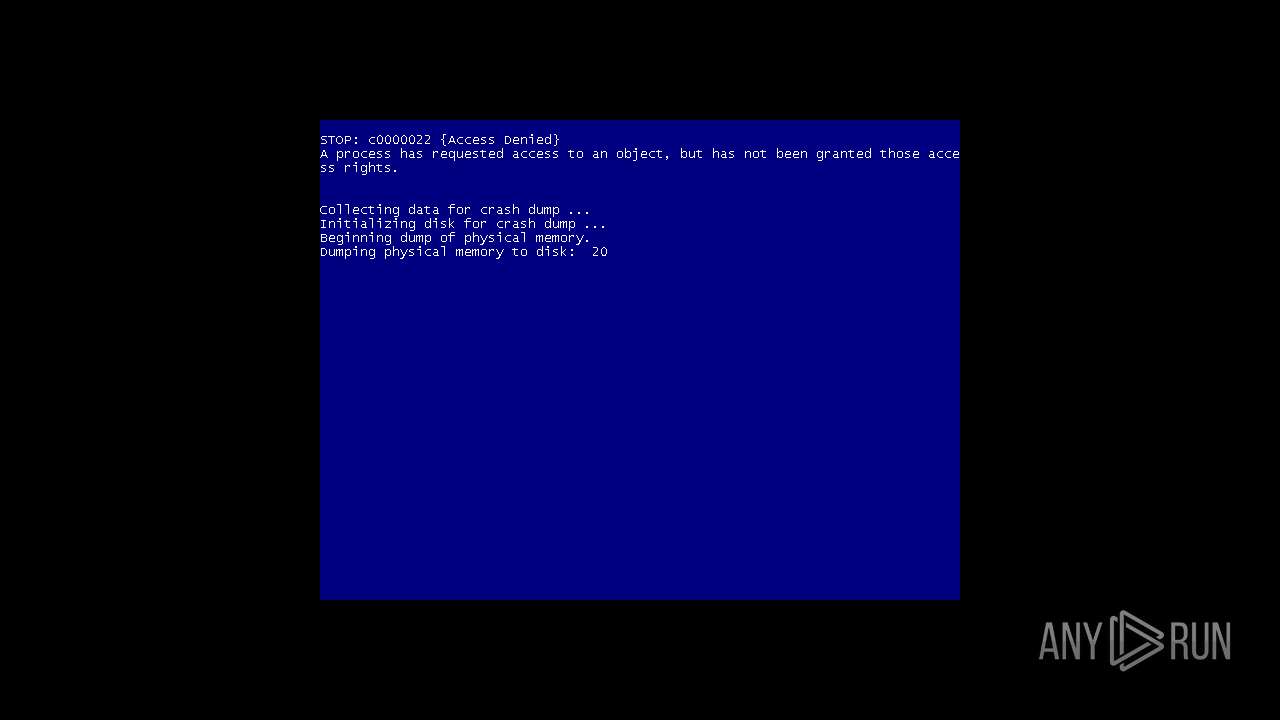
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 00:28:43 |
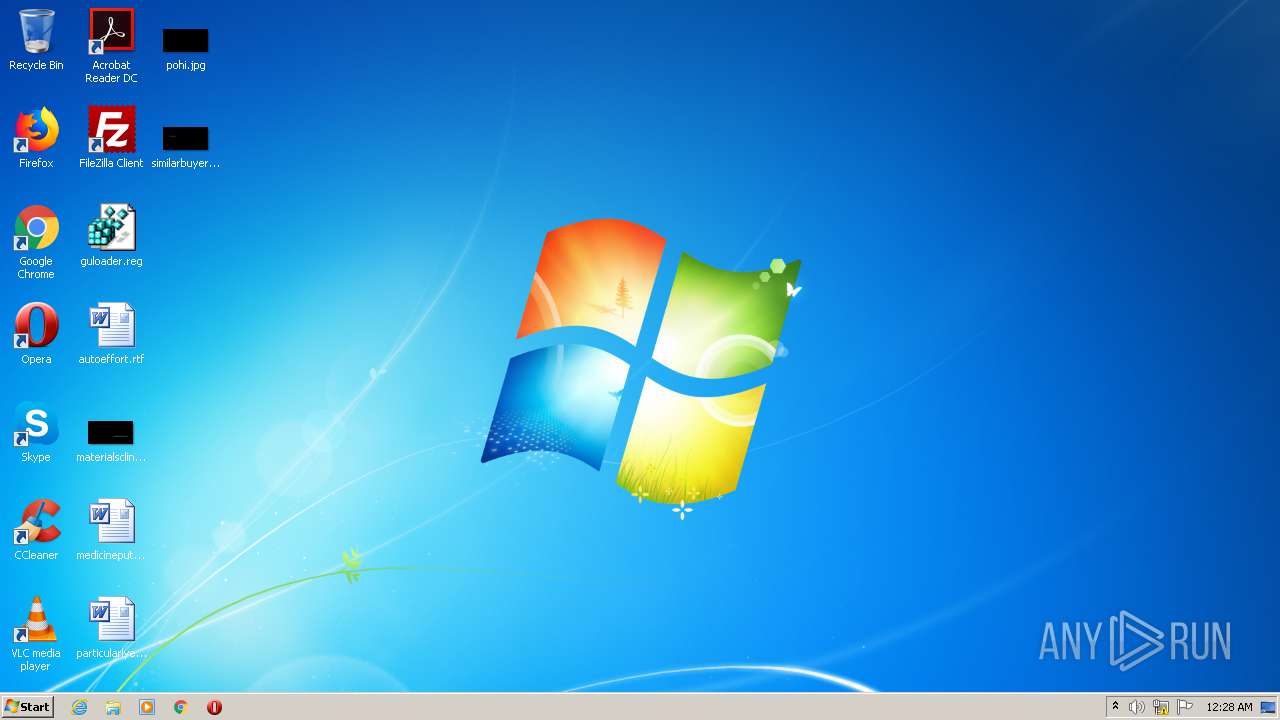
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E62E24467EBDDDF3FE7CC0E6970F01AF |
| SHA1: | BA75BA6B80DD9A217097626443A2F76DB1962697 |
| SHA256: | 1467931A0E8C71B818773F1B3FB9D5031B980753C81C9C135C84C18F38407D5D |
| SSDEEP: | 3:N8uguGTn:2uguGT |
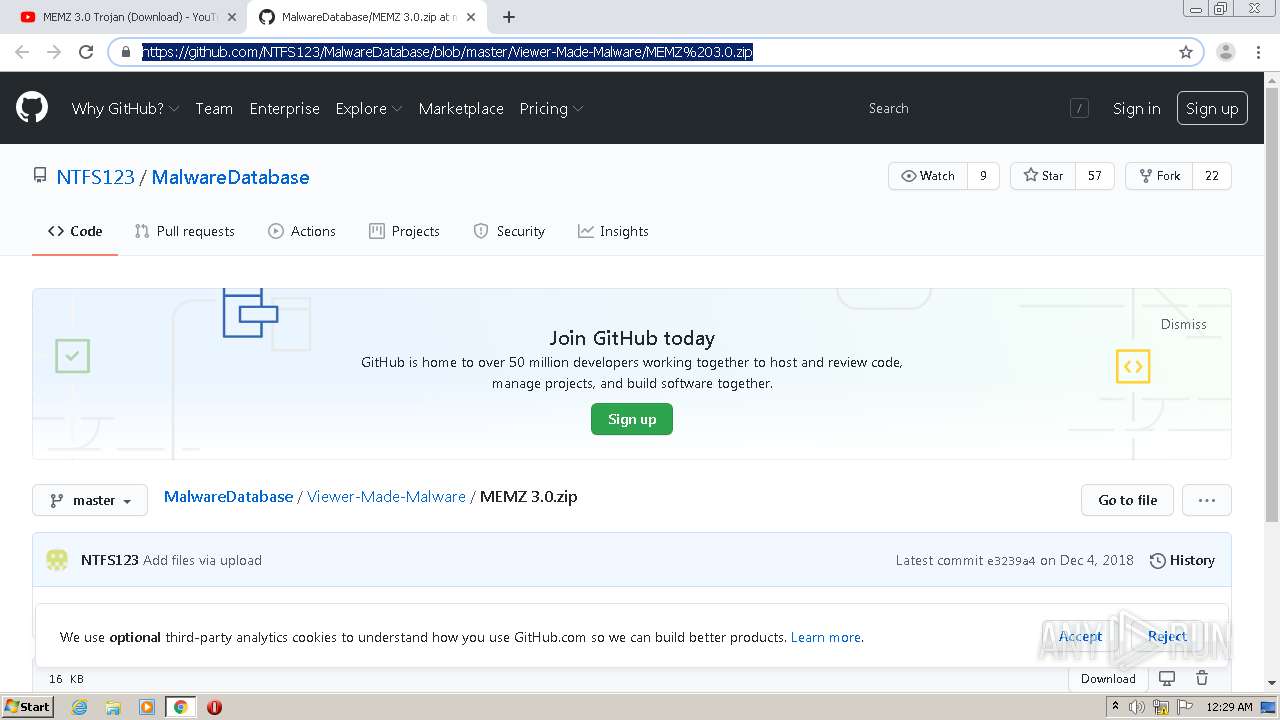
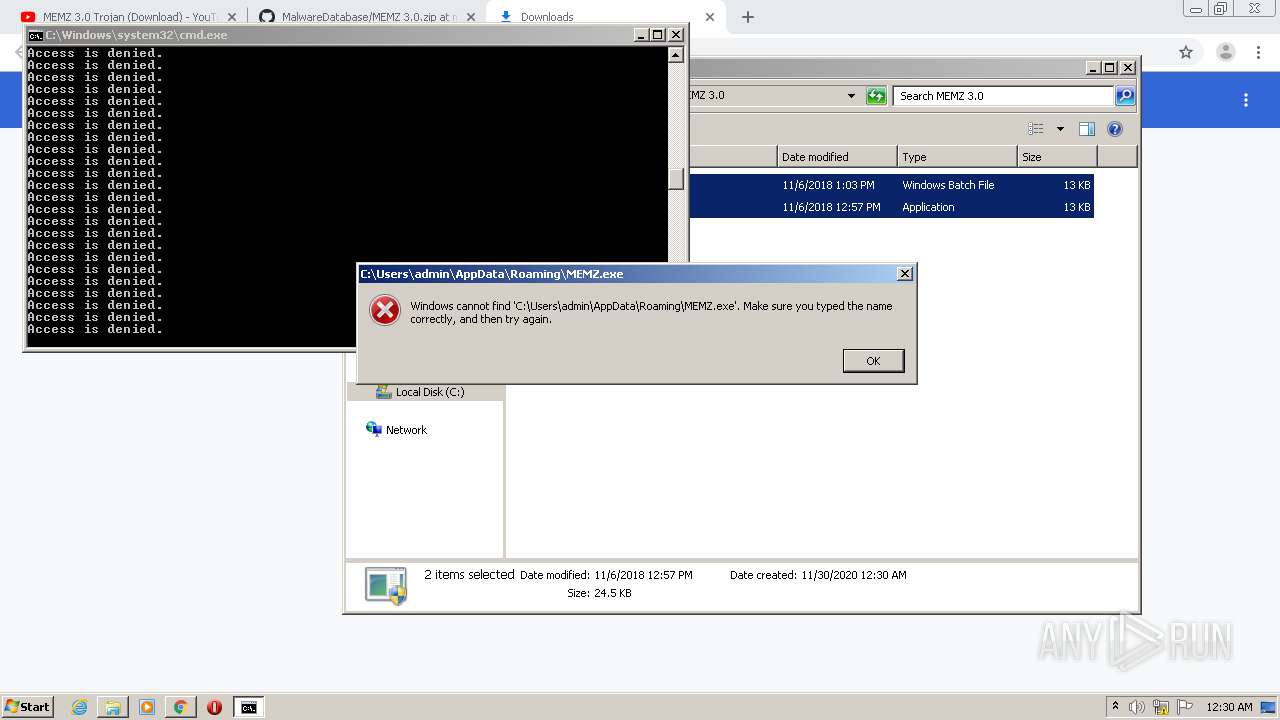
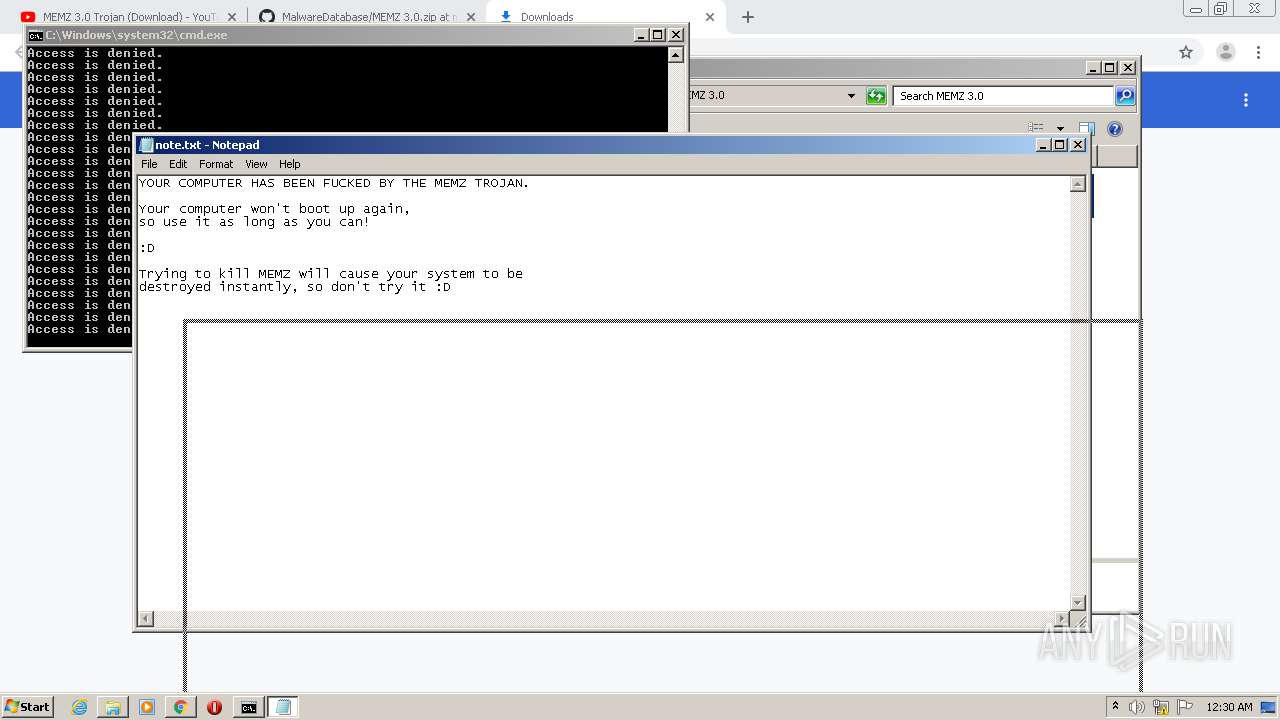
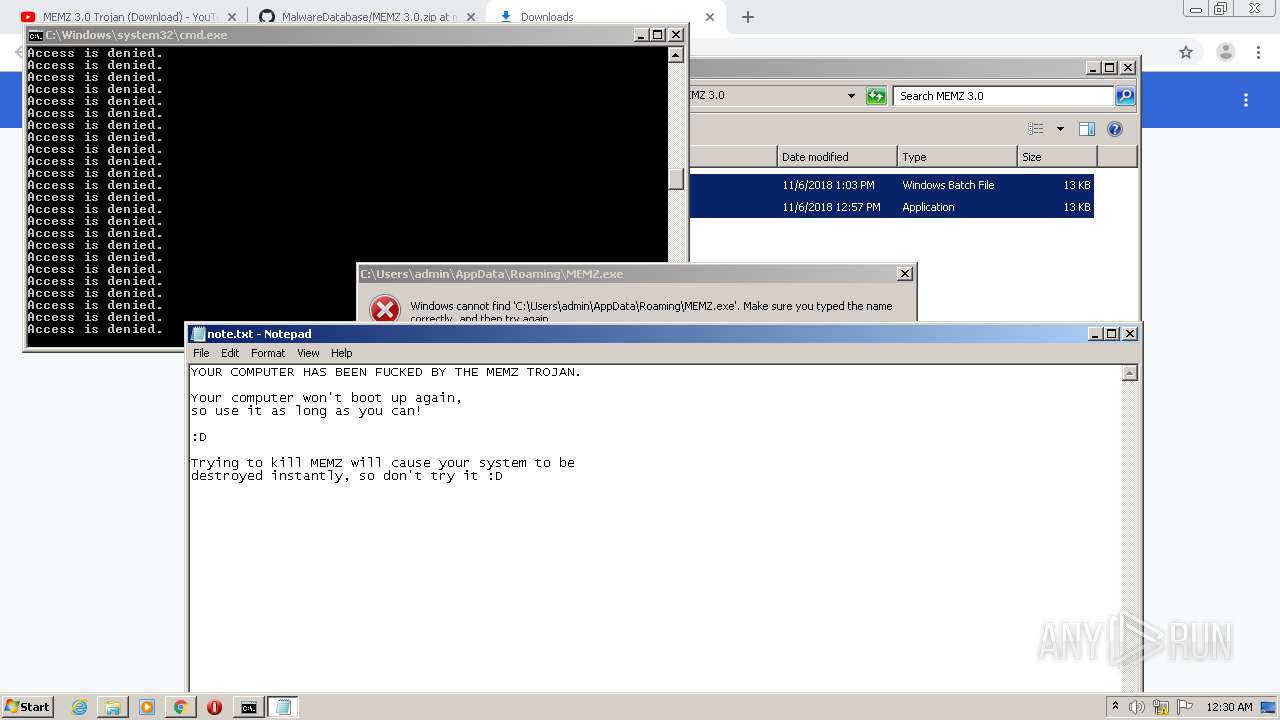
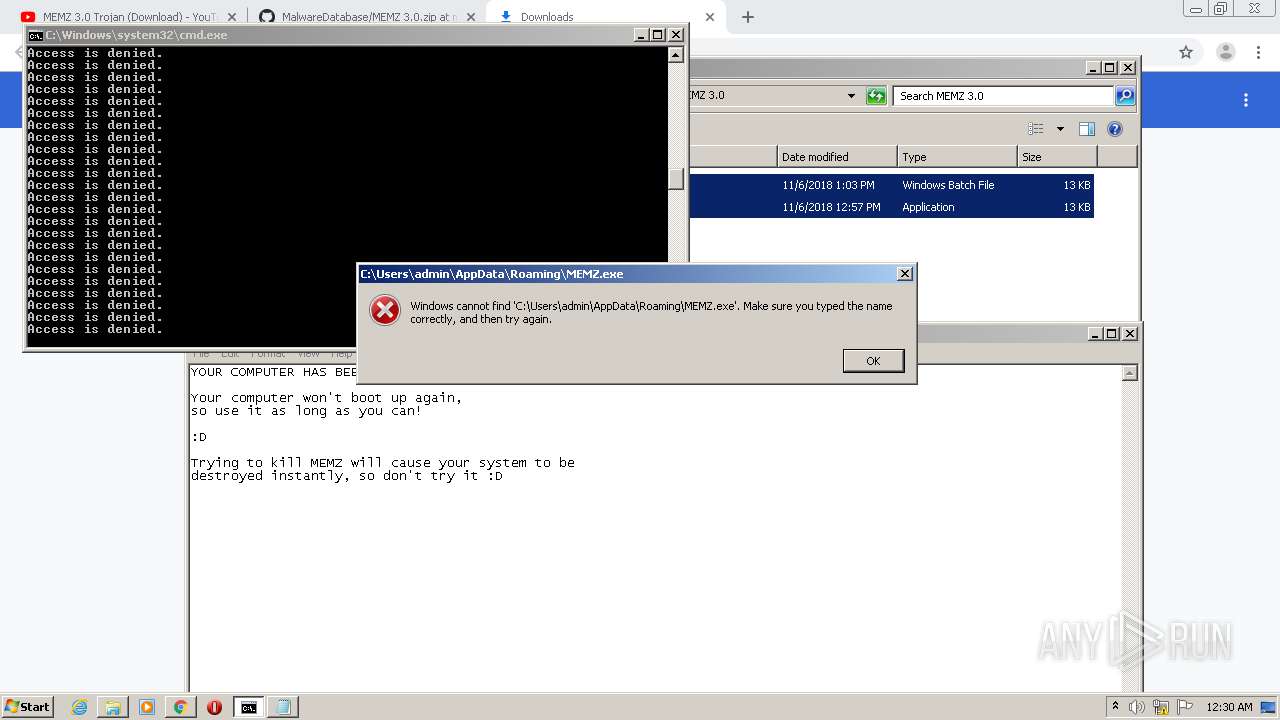
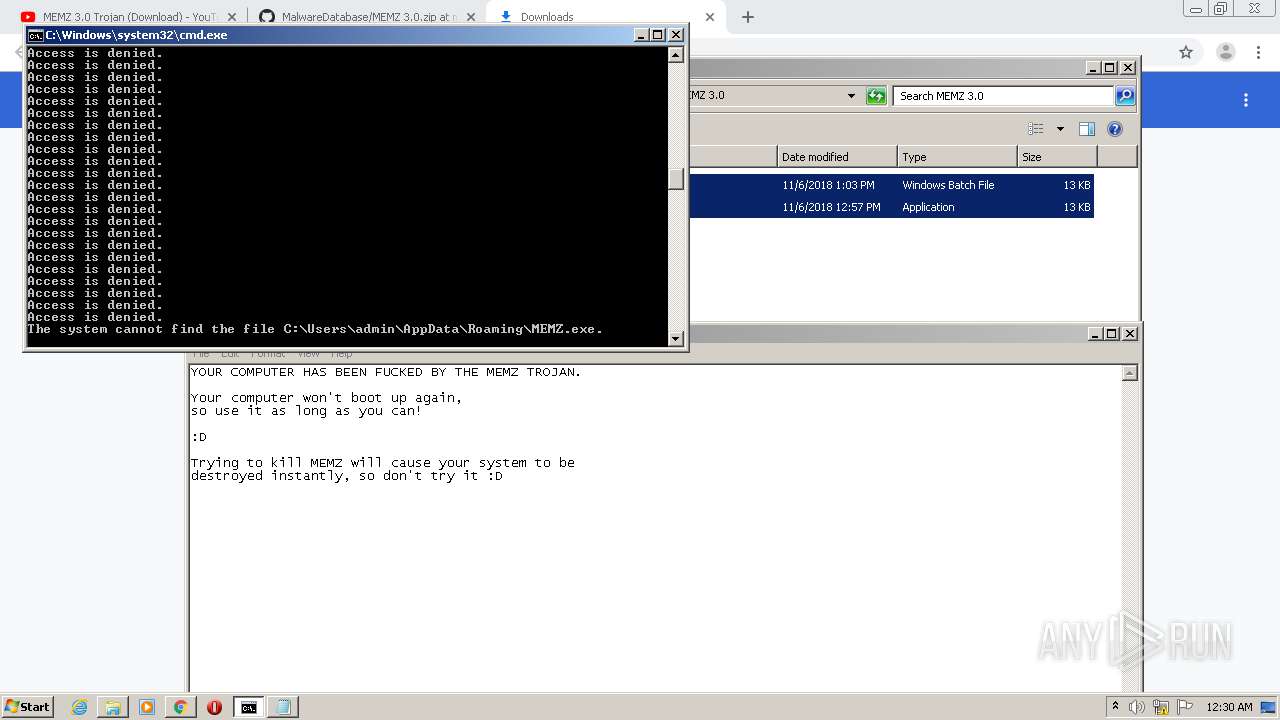
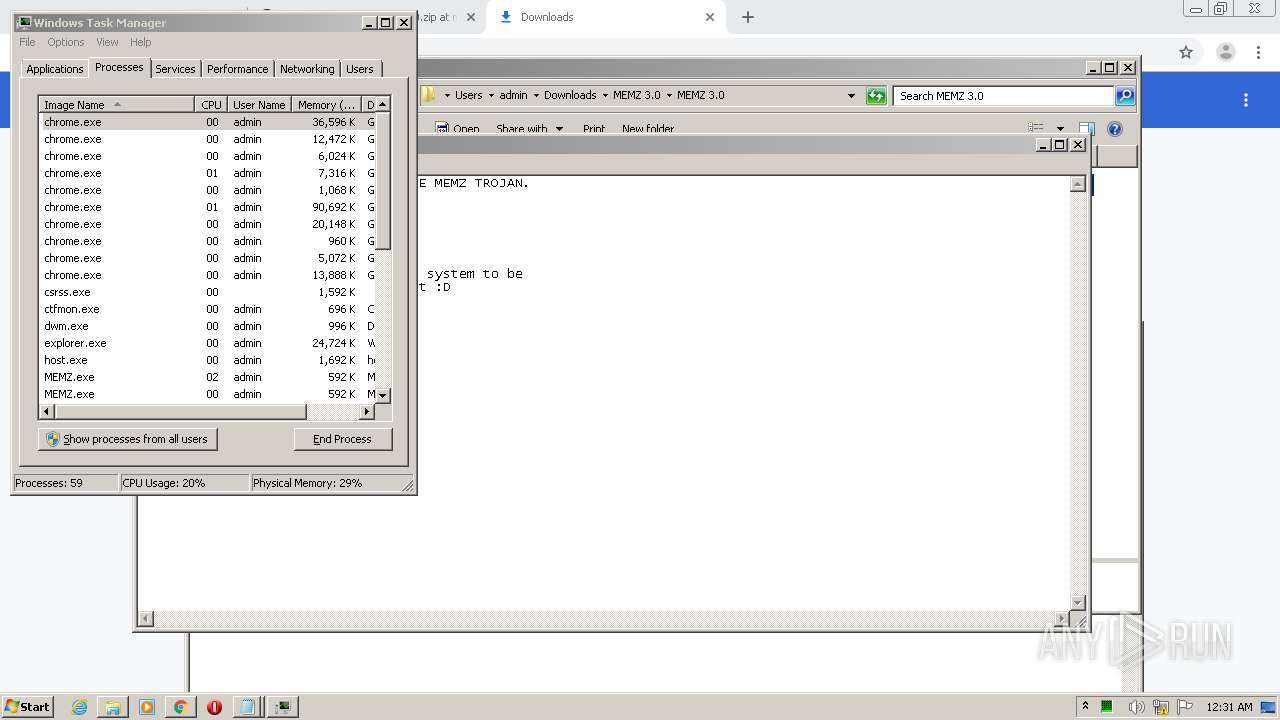
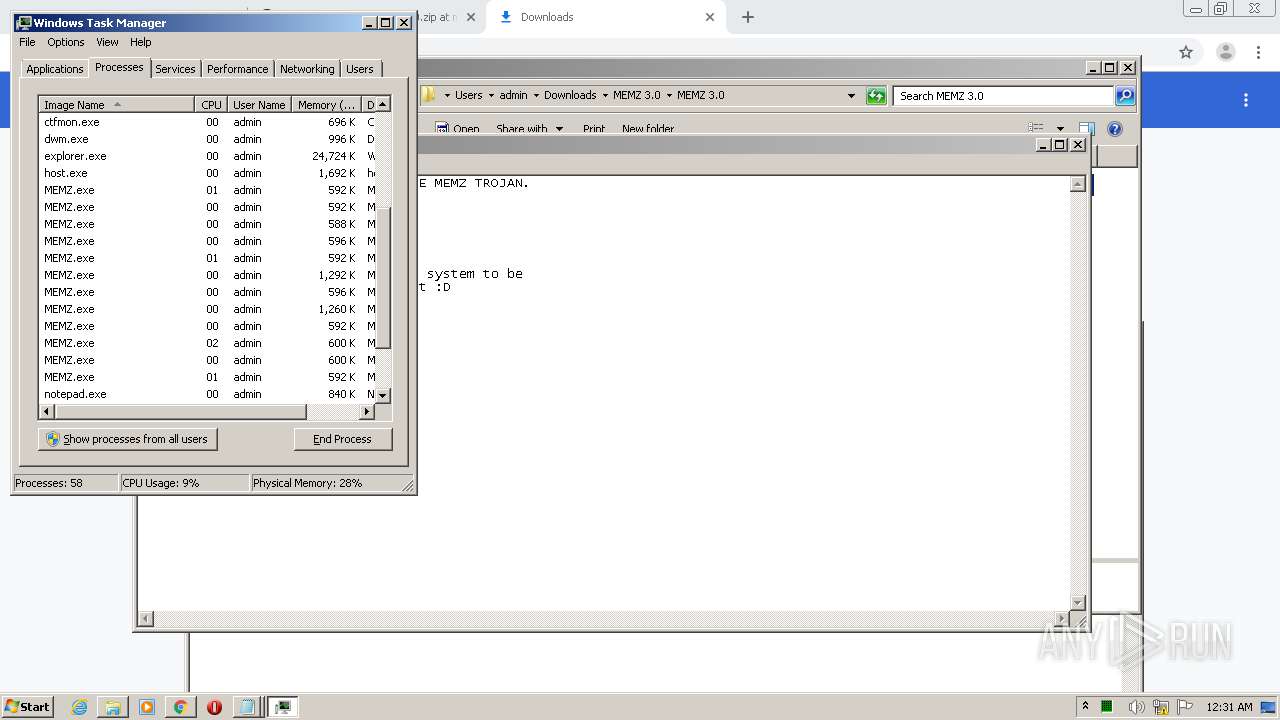
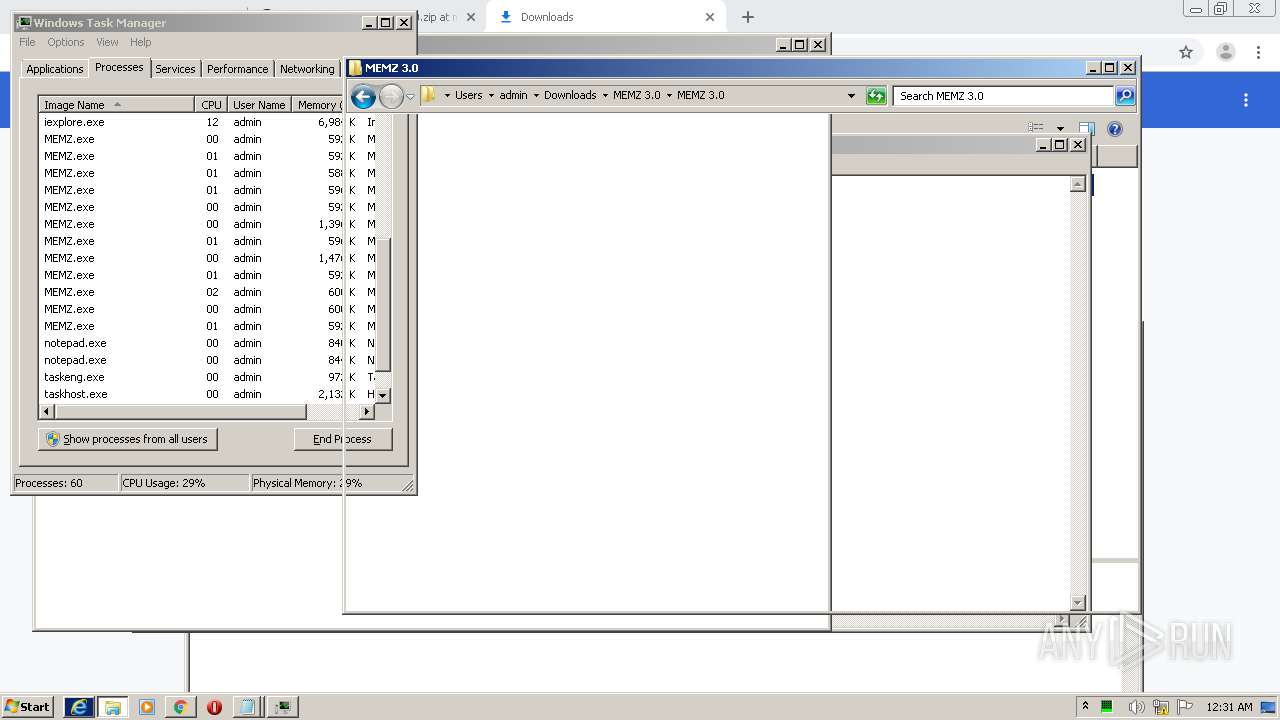
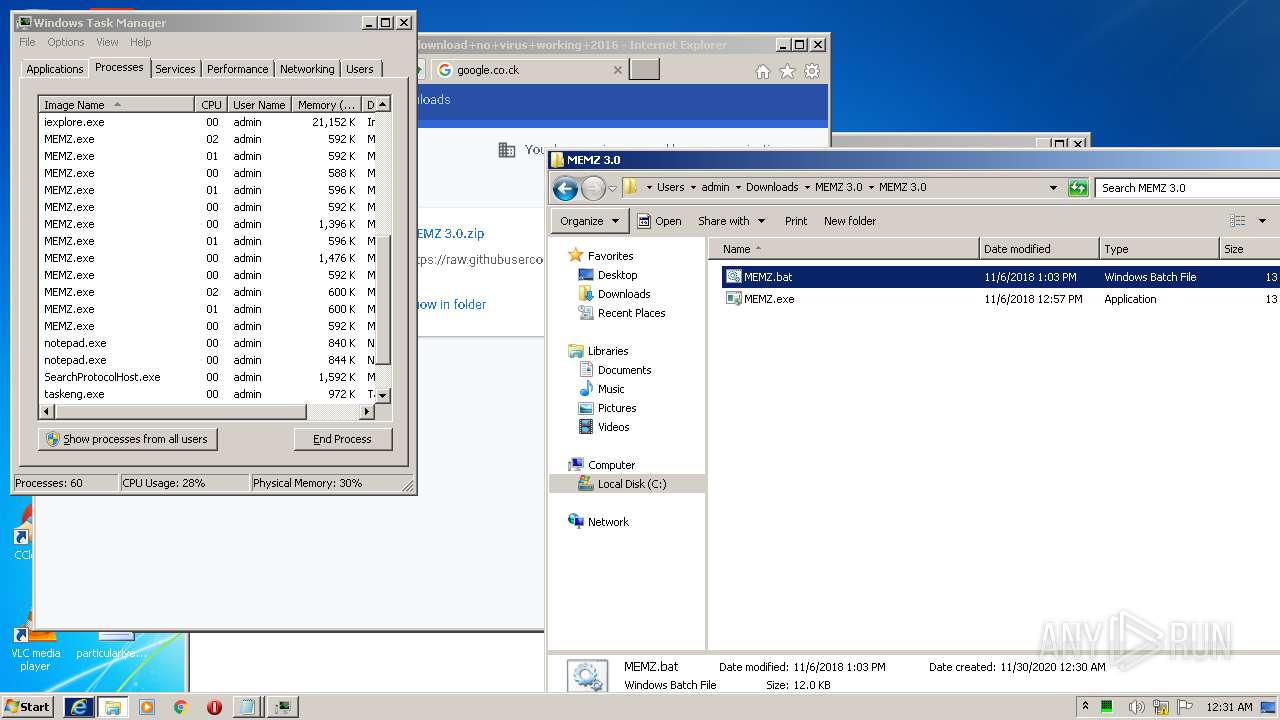
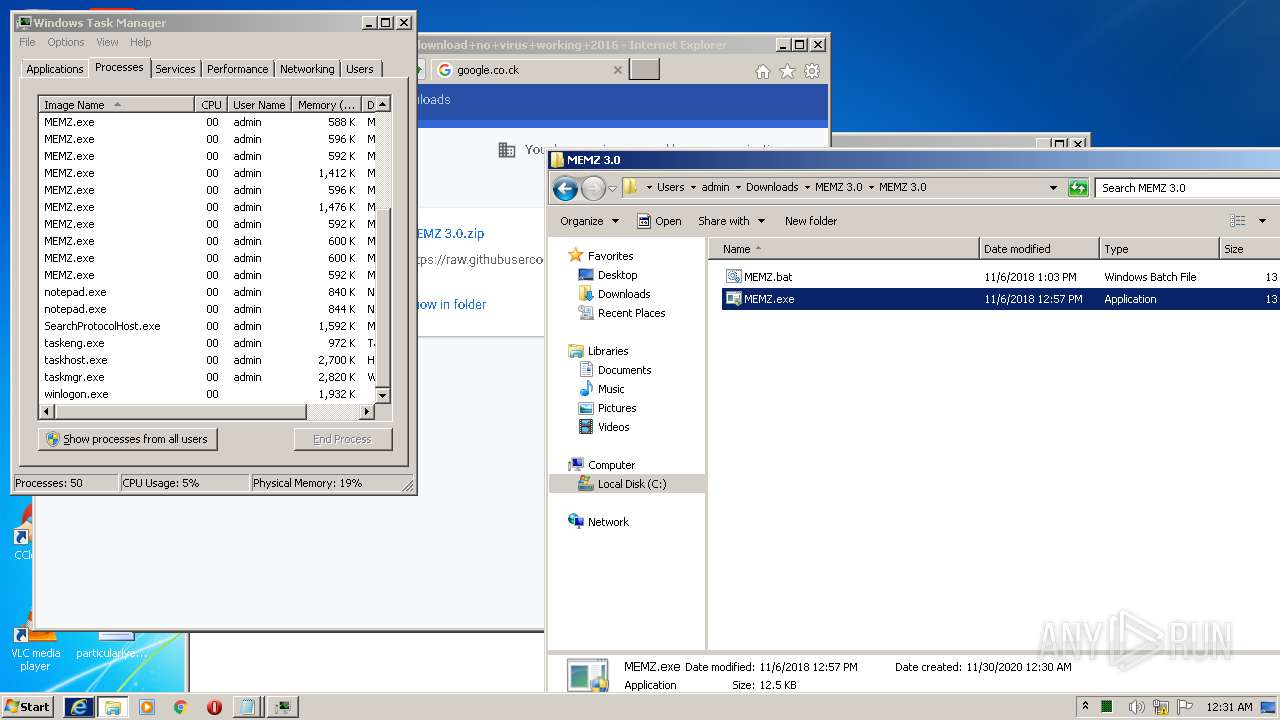
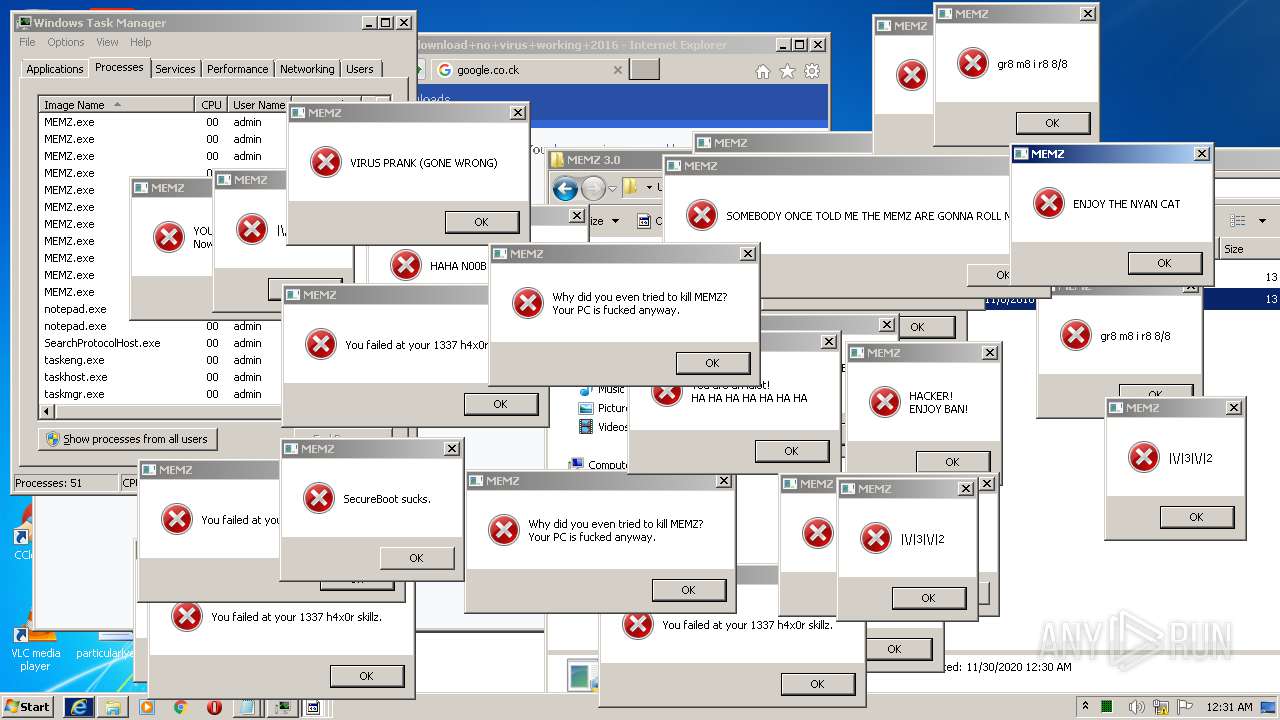
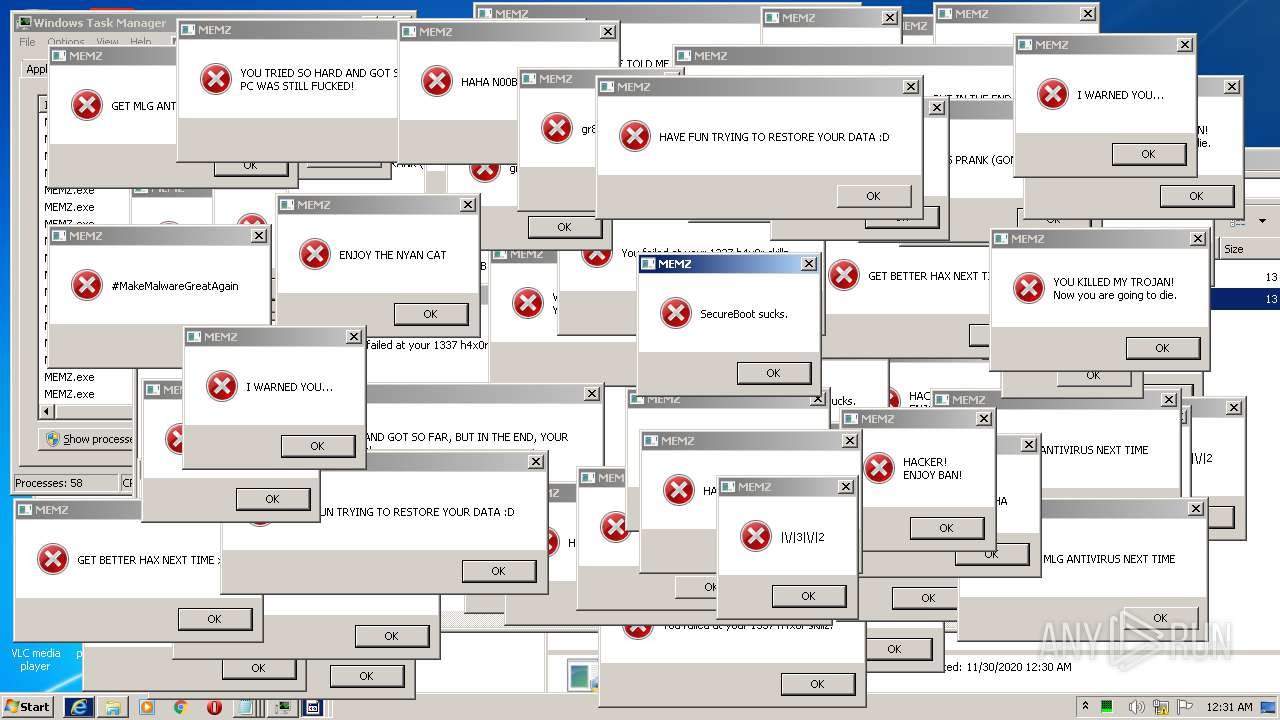
MALICIOUS
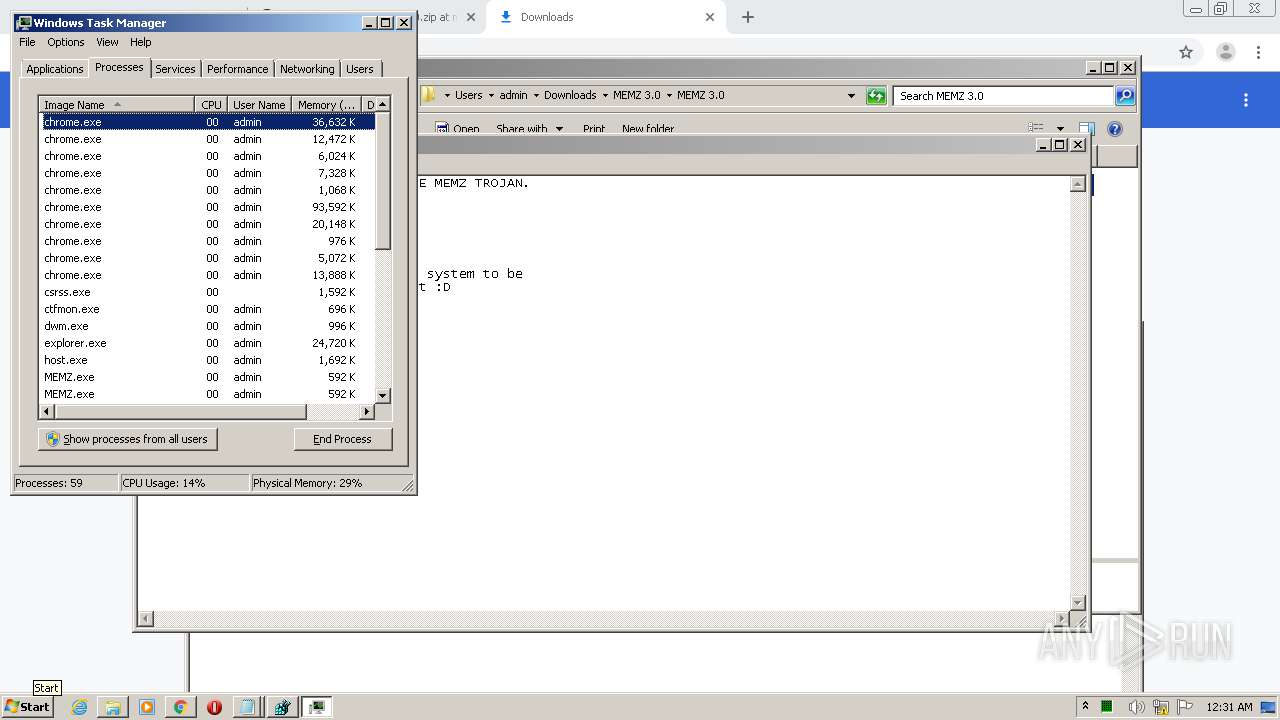
Application was dropped or rewritten from another process
- MEMZ.exe (PID: 2304)
- MEMZ.exe (PID: 1736)
- MEMZ.exe (PID: 1792)
- MEMZ.exe (PID: 1240)
- MEMZ.exe (PID: 2088)
- MEMZ.exe (PID: 3648)
- MEMZ.exe (PID: 2296)
- MEMZ.exe (PID: 2704)
- MEMZ.exe (PID: 2612)
- MEMZ.exe (PID: 3248)
- MEMZ.exe (PID: 2476)
- MEMZ.exe (PID: 3496)
- MEMZ.exe (PID: 2256)
- MEMZ.exe (PID: 1744)
- MEMZ.exe (PID: 2612)
- MEMZ.exe (PID: 2940)
- MEMZ.exe (PID: 2544)
- MEMZ.exe (PID: 2696)
- MEMZ.exe (PID: 3288)
- MEMZ.exe (PID: 3028)
- MEMZ.exe (PID: 2332)
- MEMZ.exe (PID: 2480)
- MEMZ.exe (PID: 2576)
- MEMZ.exe (PID: 480)
- MEMZ.exe (PID: 2176)
Low-level write access rights to disk partition
- MEMZ.exe (PID: 2296)
- MEMZ.exe (PID: 2612)
- MEMZ.exe (PID: 480)
SUSPICIOUS
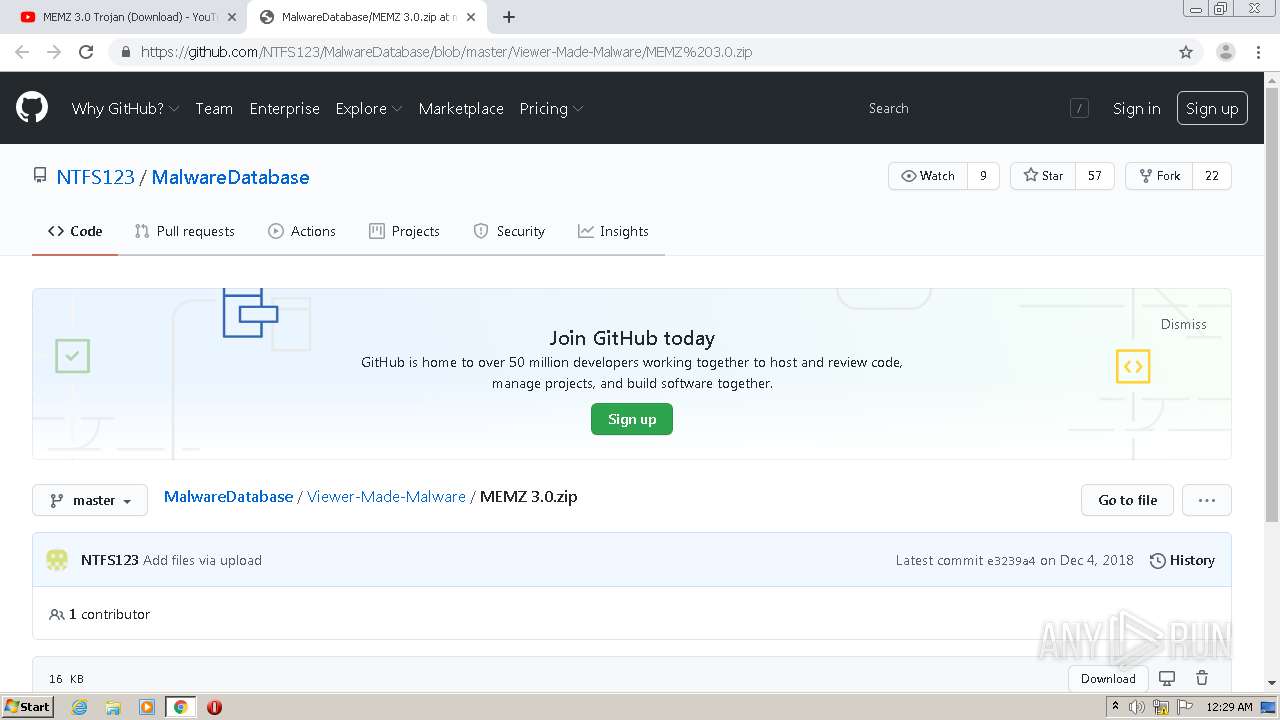
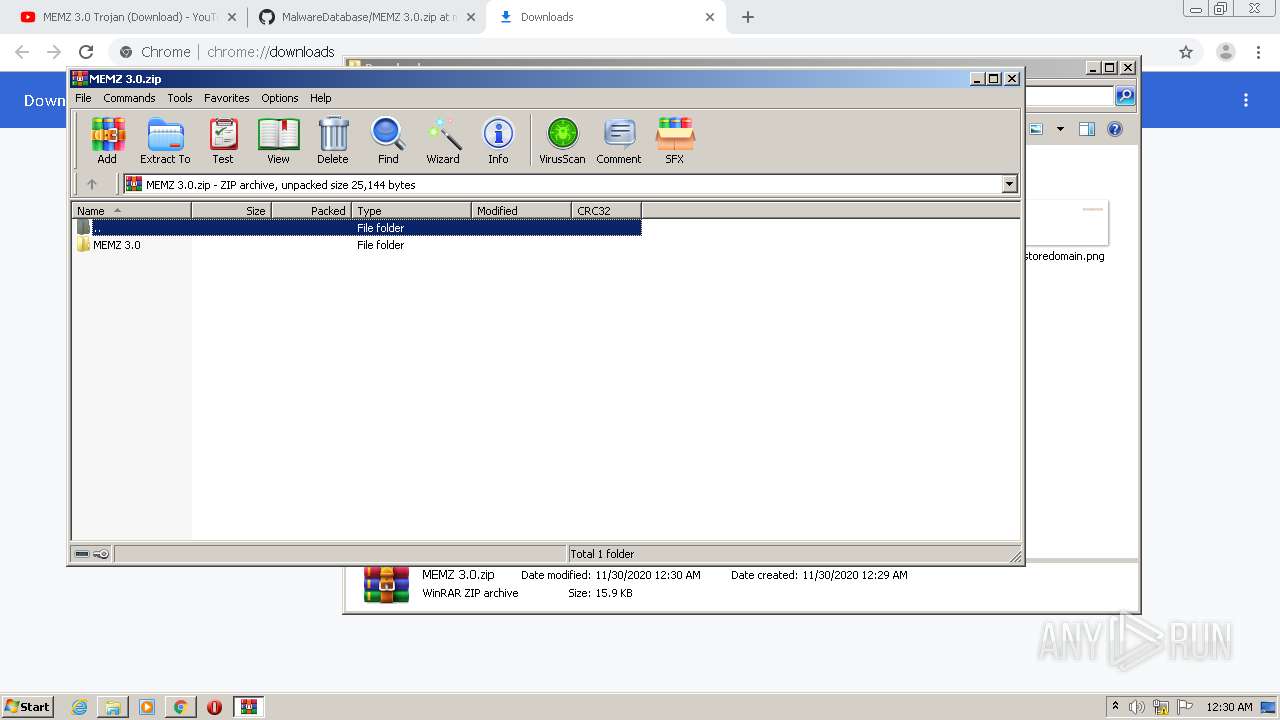
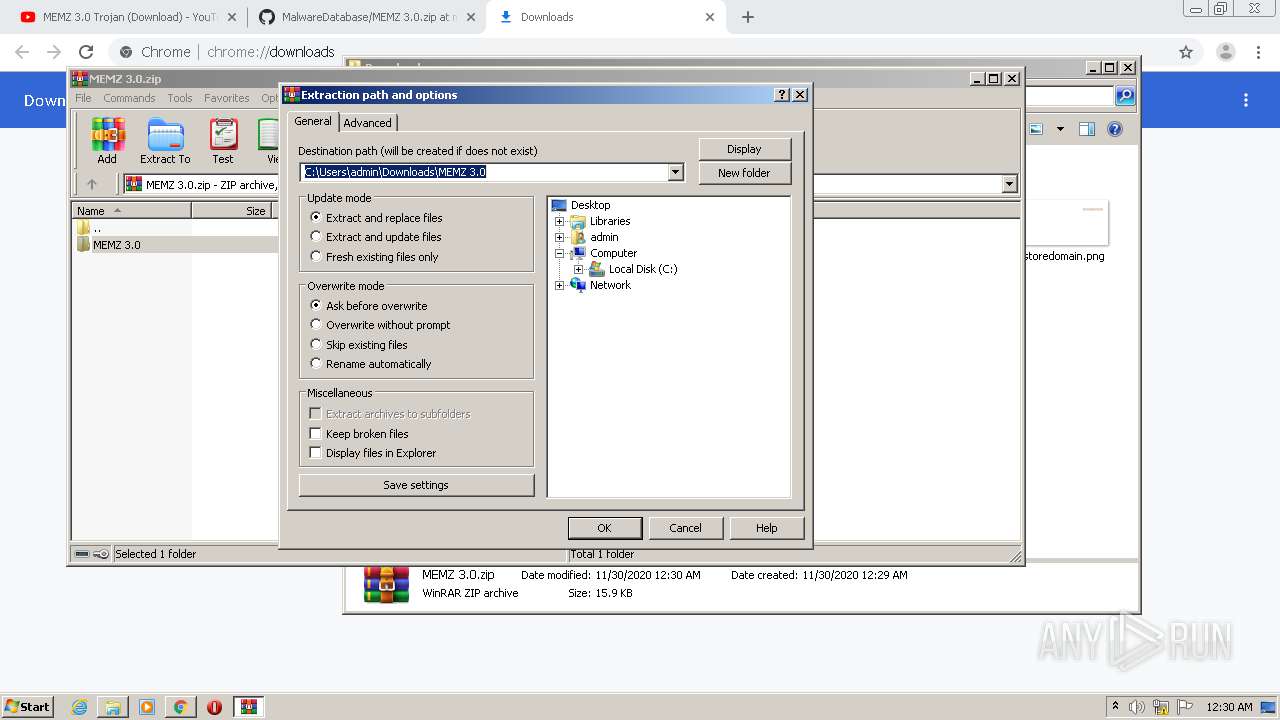
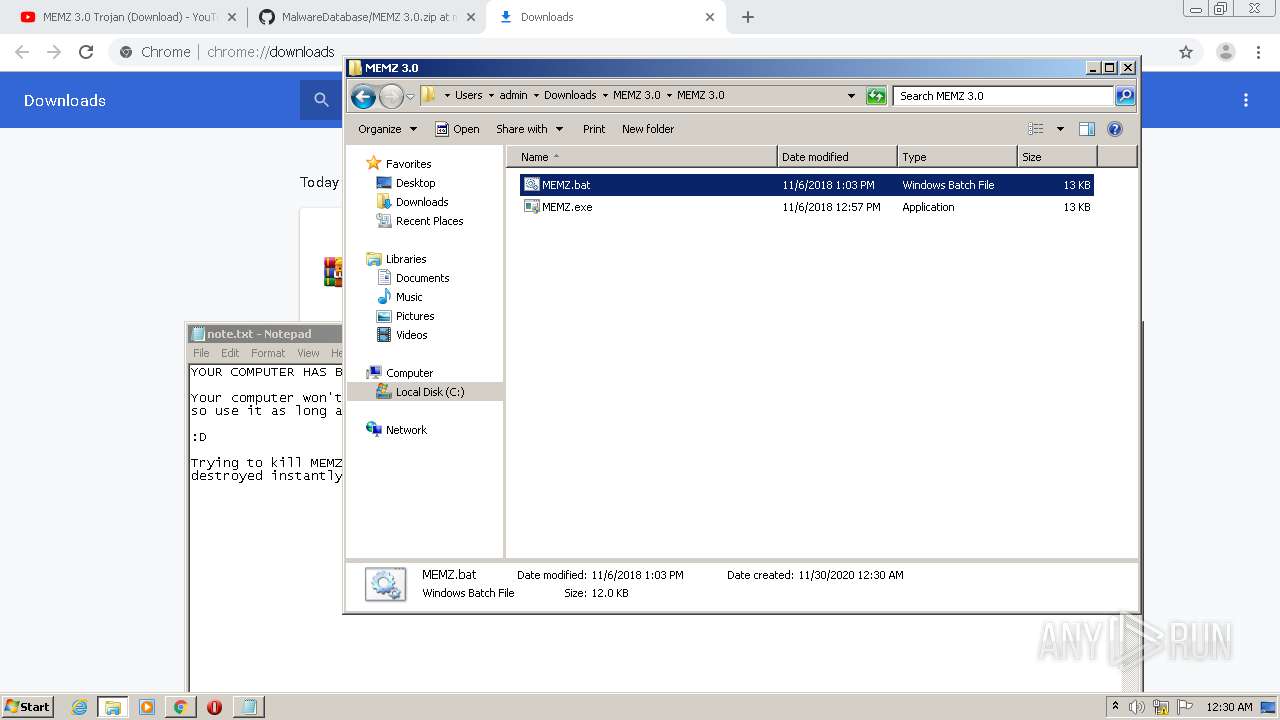
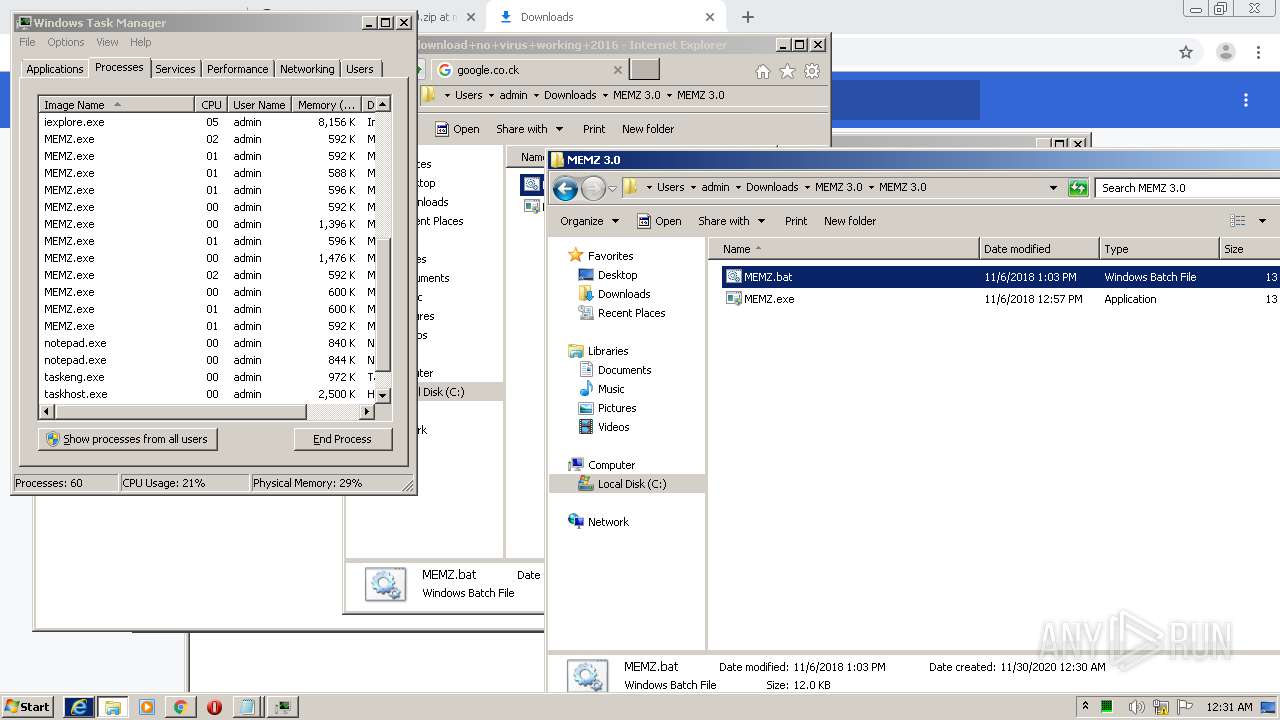
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2920)
- cscript.exe (PID: 3112)
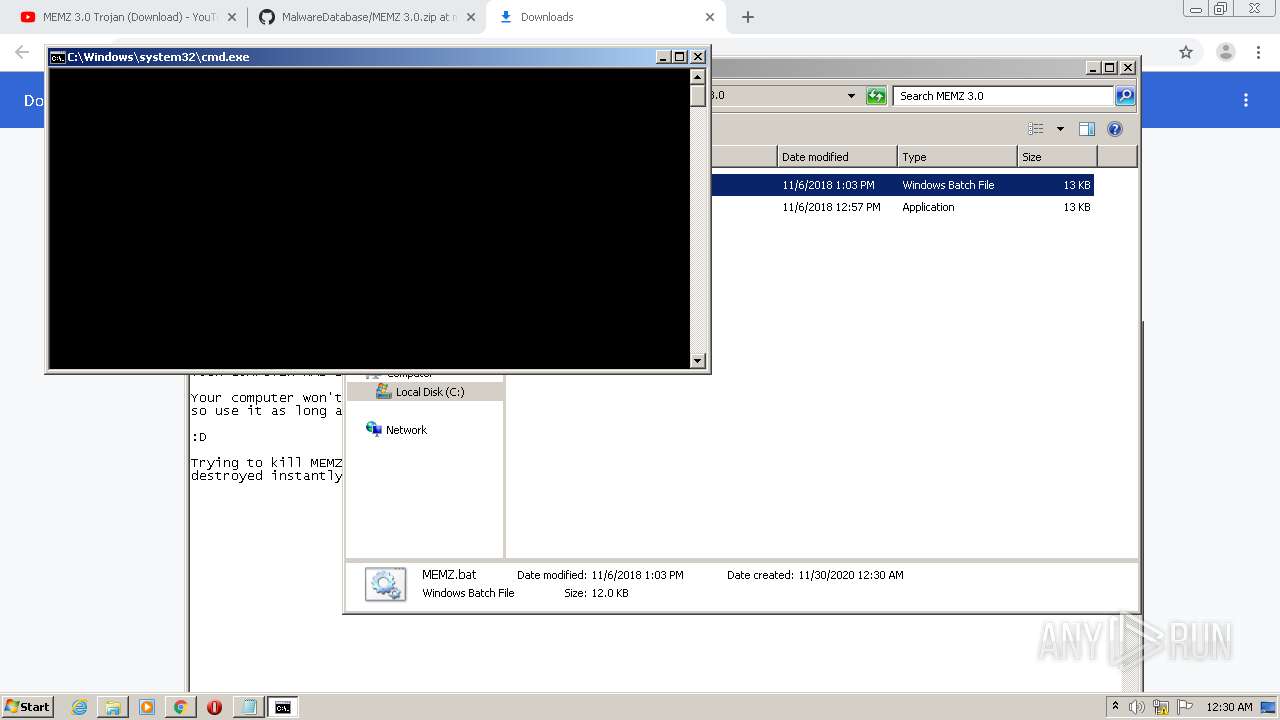
Executes scripts
- cmd.exe (PID: 3376)
- cmd.exe (PID: 2616)
Application launched itself
- MEMZ.exe (PID: 1736)
- MEMZ.exe (PID: 3248)
- MEMZ.exe (PID: 3288)
Low-level read access rights to disk partition
- MEMZ.exe (PID: 2296)
- MEMZ.exe (PID: 2612)
- MEMZ.exe (PID: 480)
Creates files in the user directory
- cscript.exe (PID: 3112)
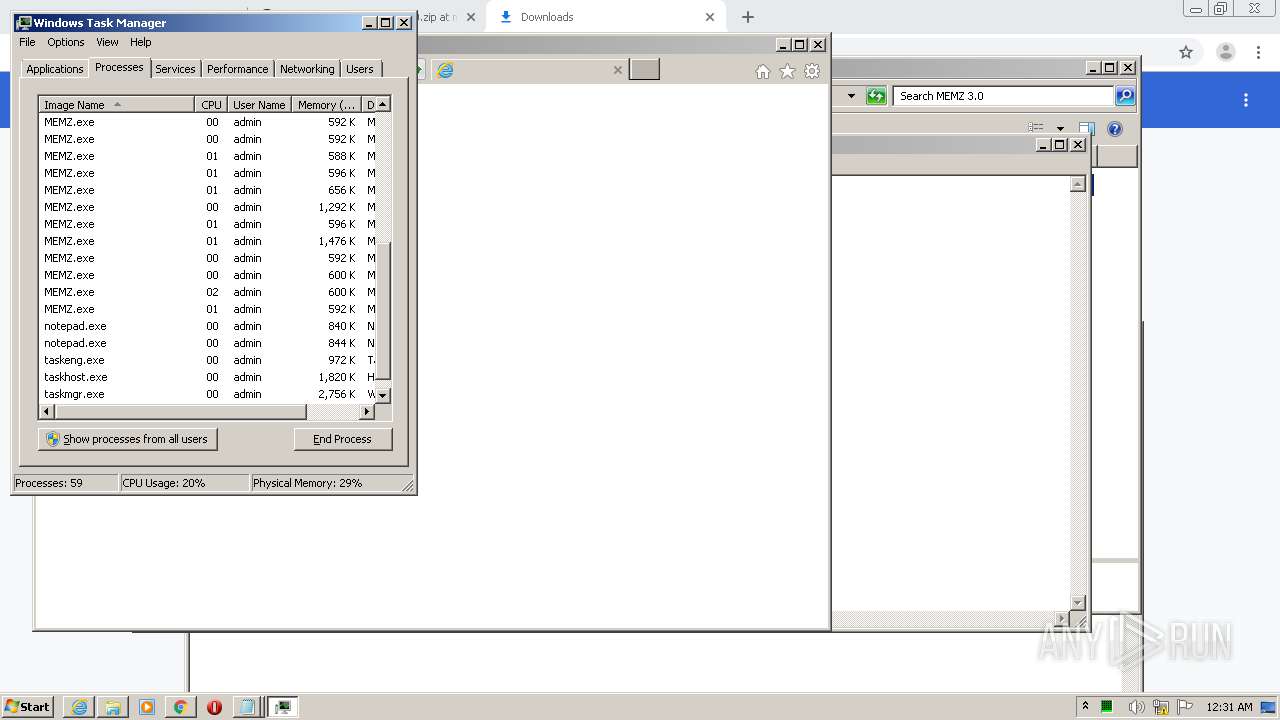
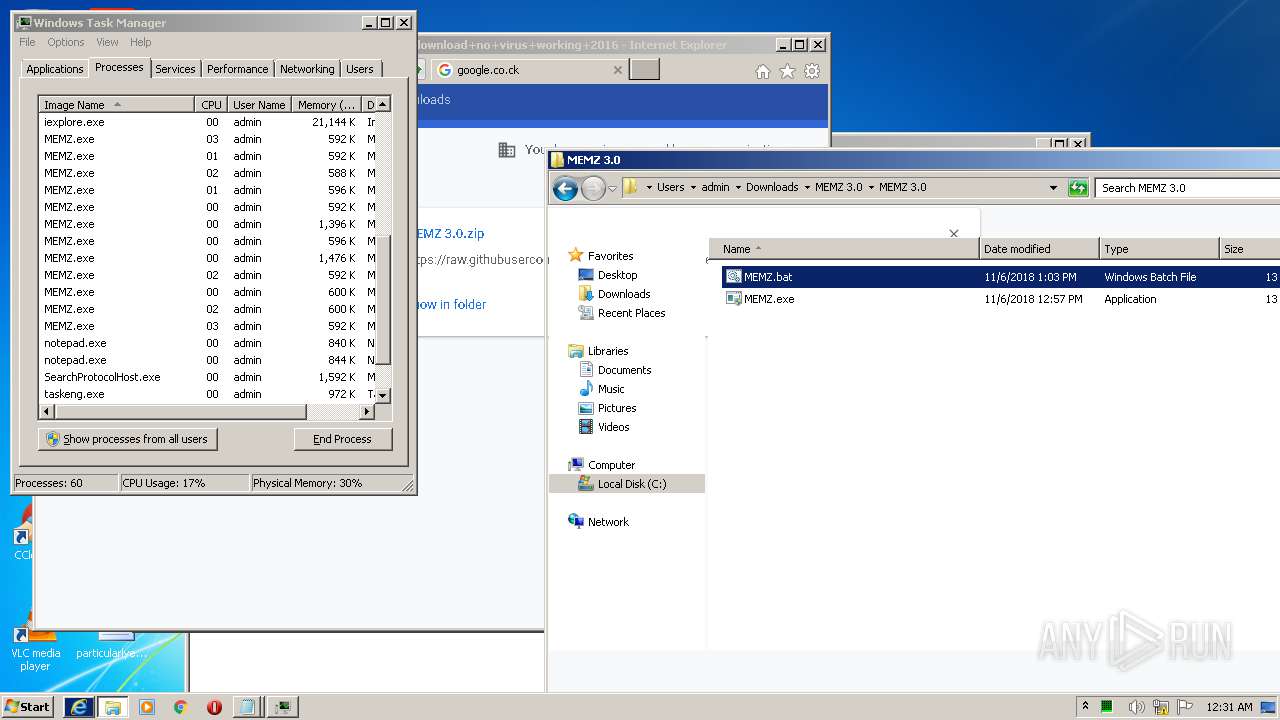
Starts Internet Explorer
- MEMZ.exe (PID: 2612)
INFO
Application launched itself
- chrome.exe (PID: 1096)
- iexplore.exe (PID: 2848)
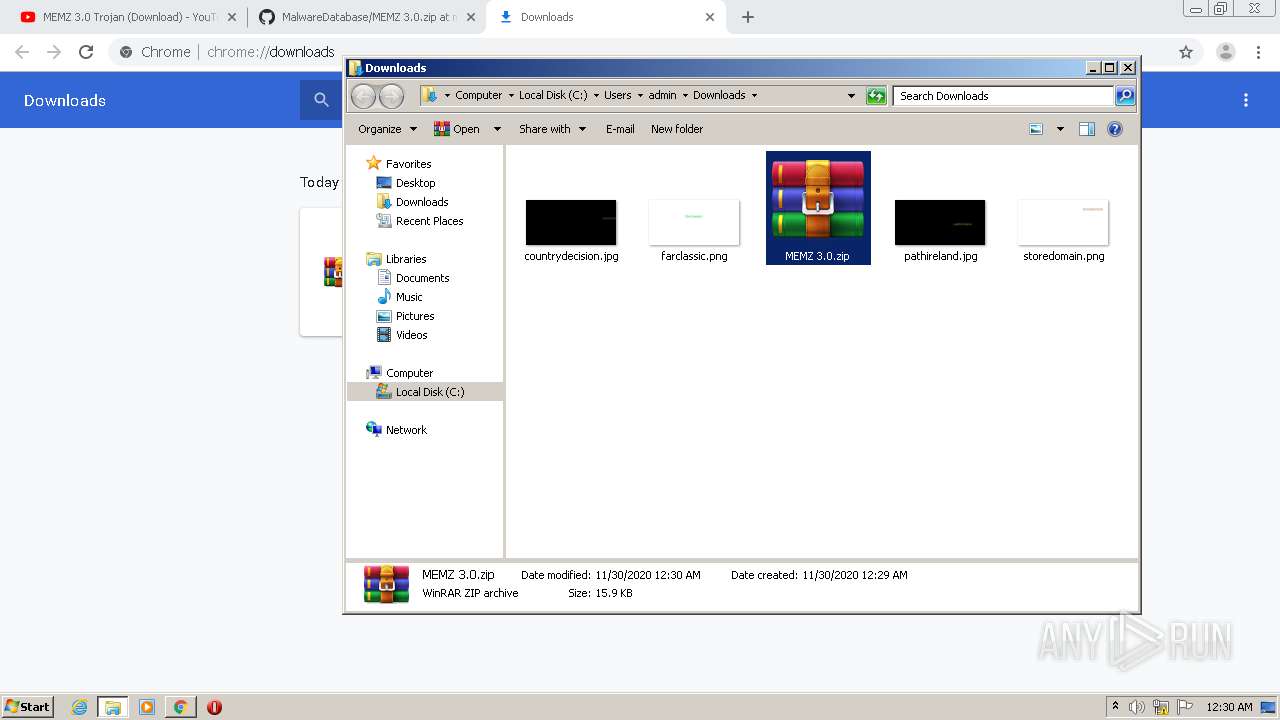
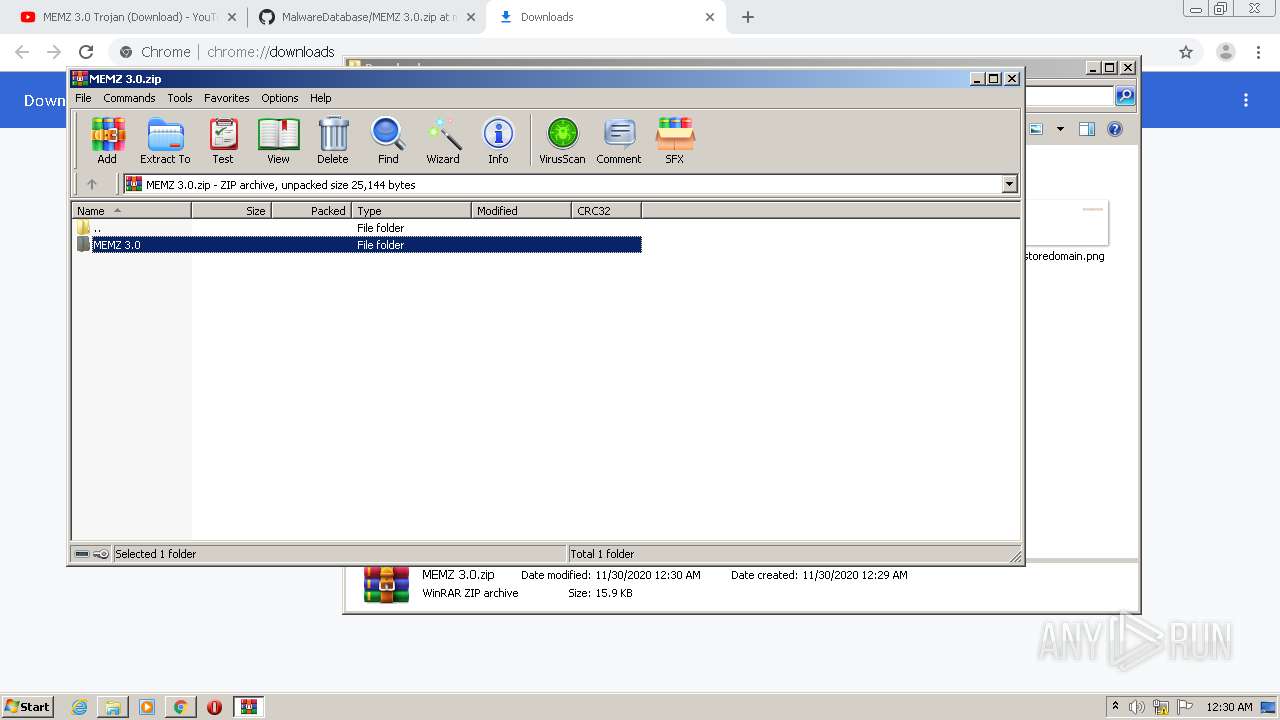
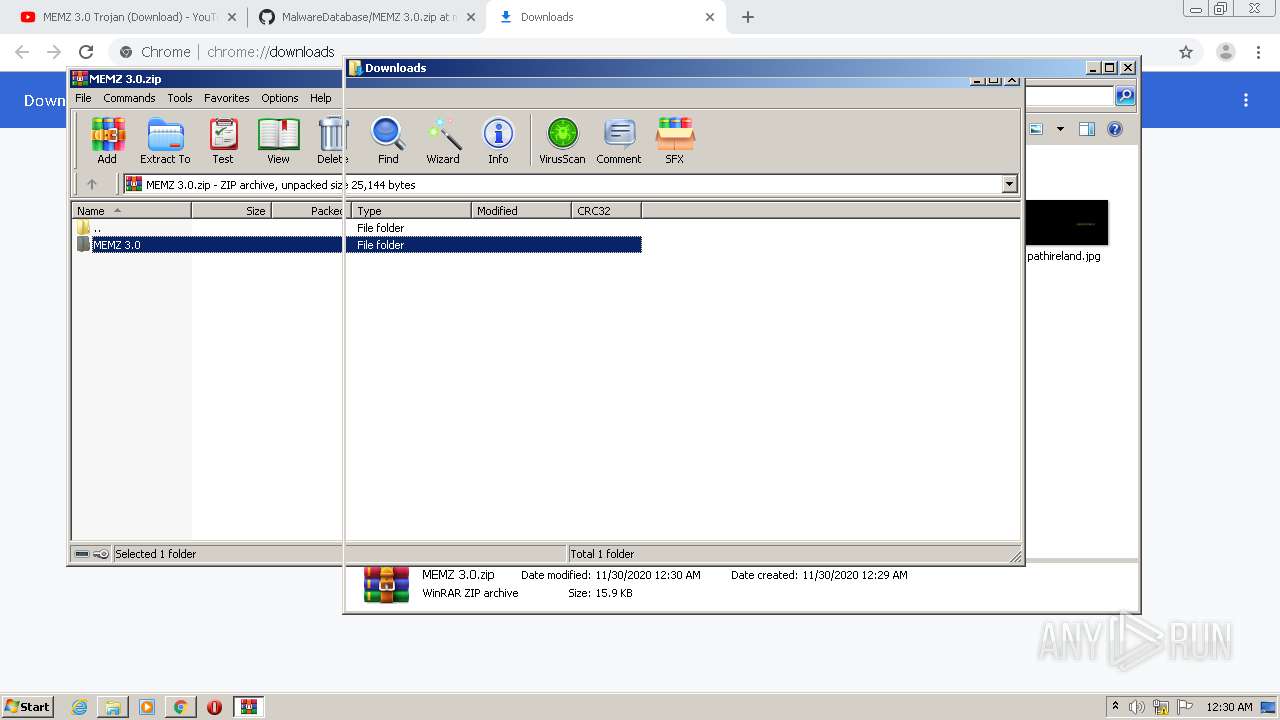
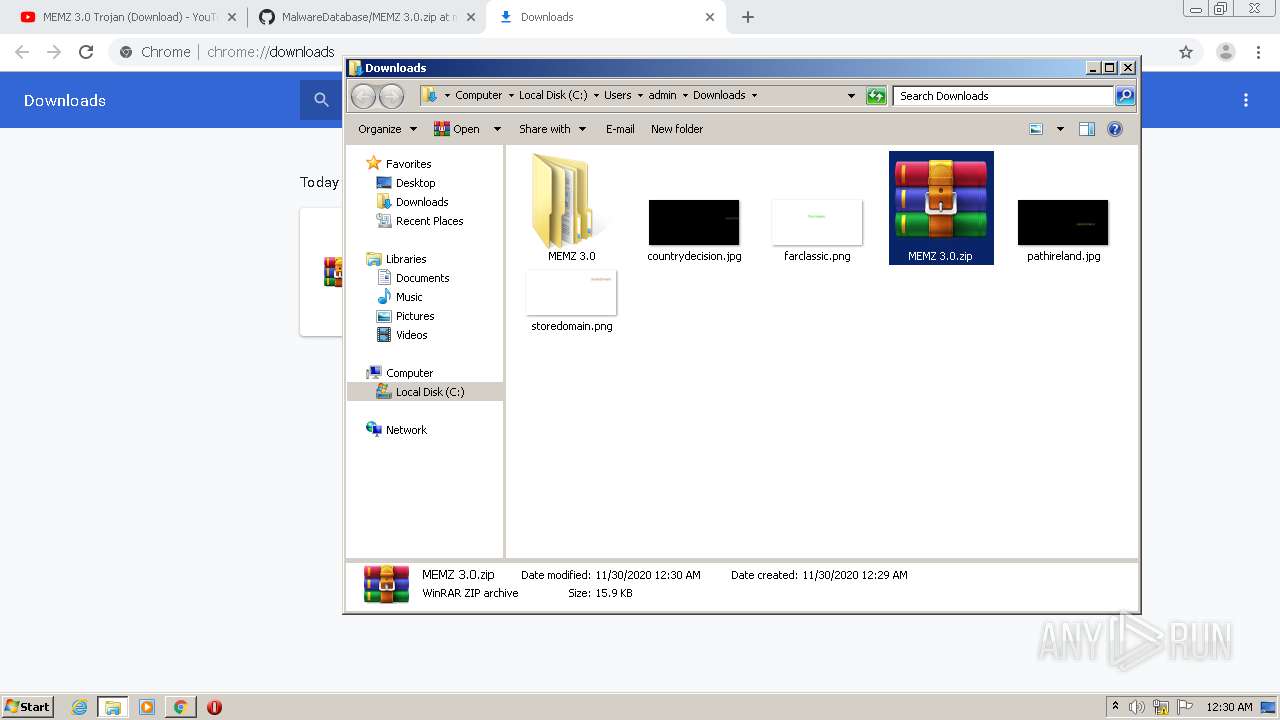
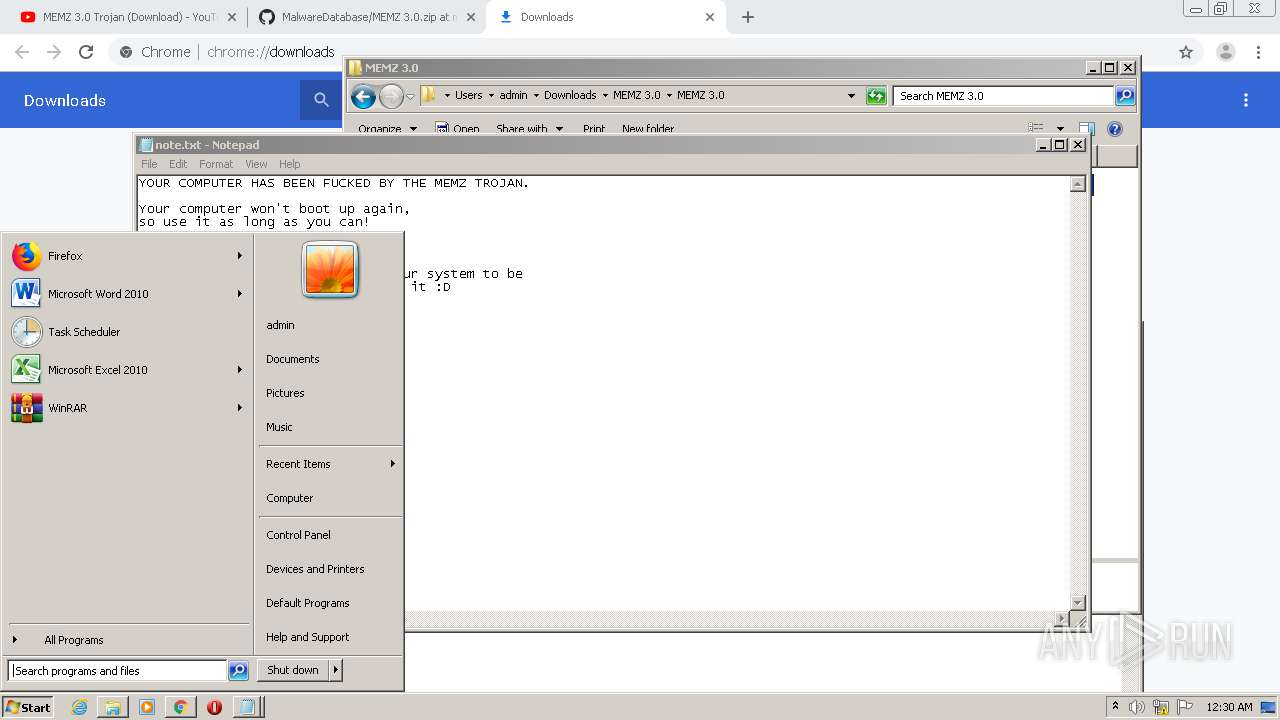
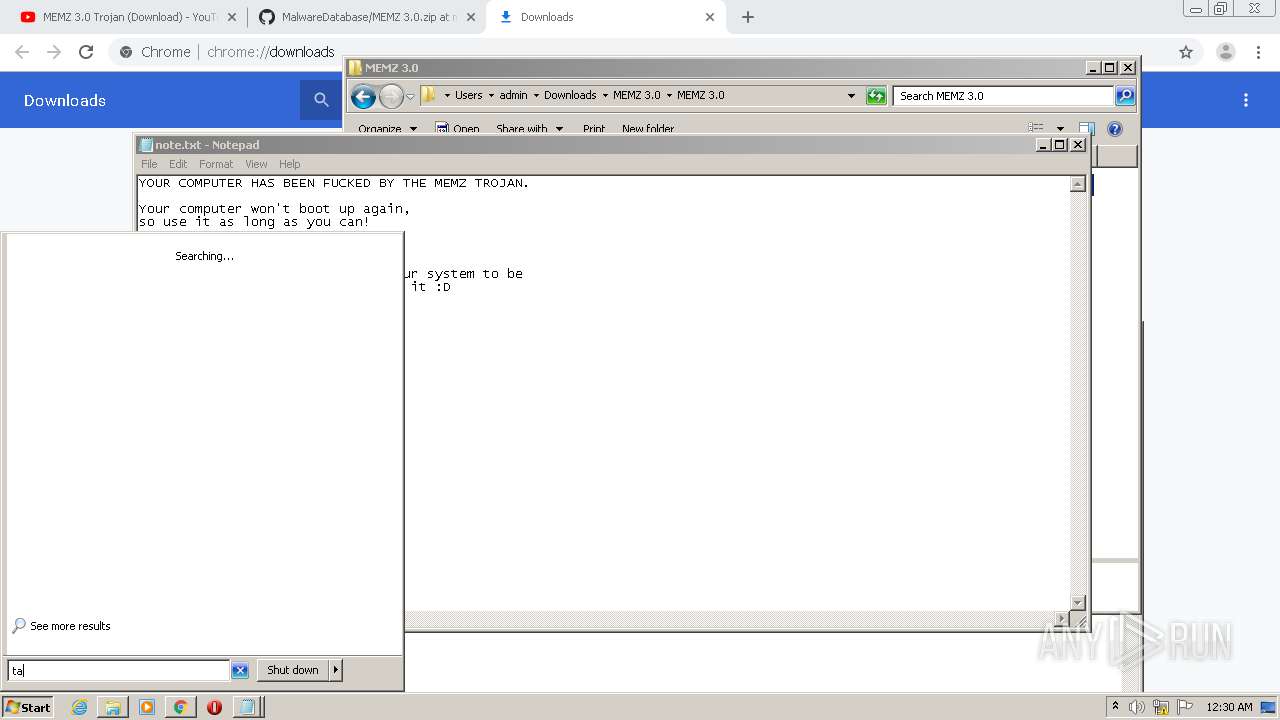
Manual execution by user
- WinRAR.exe (PID: 2920)
- cmd.exe (PID: 3376)
- MEMZ.exe (PID: 2304)
- MEMZ.exe (PID: 1736)
- cmd.exe (PID: 2616)
- taskmgr.exe (PID: 3164)
- MEMZ.exe (PID: 2696)
- MEMZ.exe (PID: 3288)
Reads the hosts file
- chrome.exe (PID: 1872)
- chrome.exe (PID: 1096)
Changes internet zones settings
- iexplore.exe (PID: 2848)
Reads settings of System Certificates
- iexplore.exe (PID: 4080)
Changes settings of System certificates
- iexplore.exe (PID: 4080)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4080)
Creates files in the user directory
- iexplore.exe (PID: 4080)
Reads internet explorer settings
- iexplore.exe (PID: 4080)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
58
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
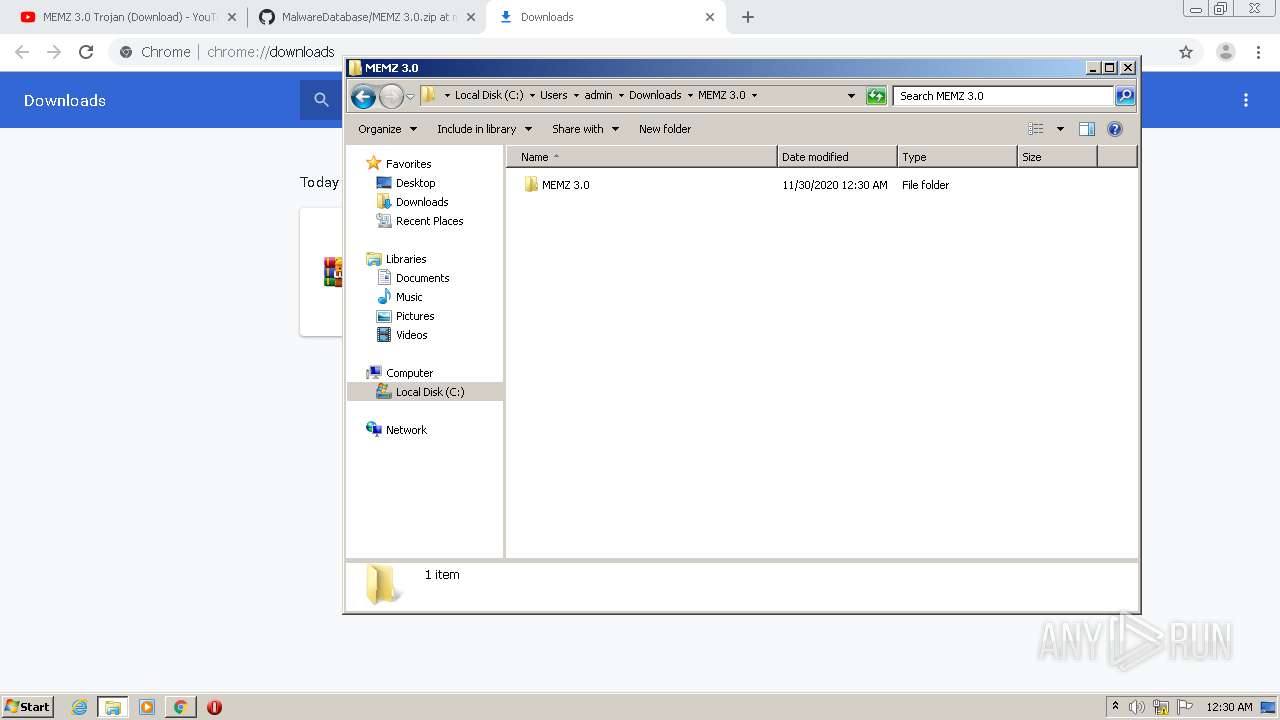
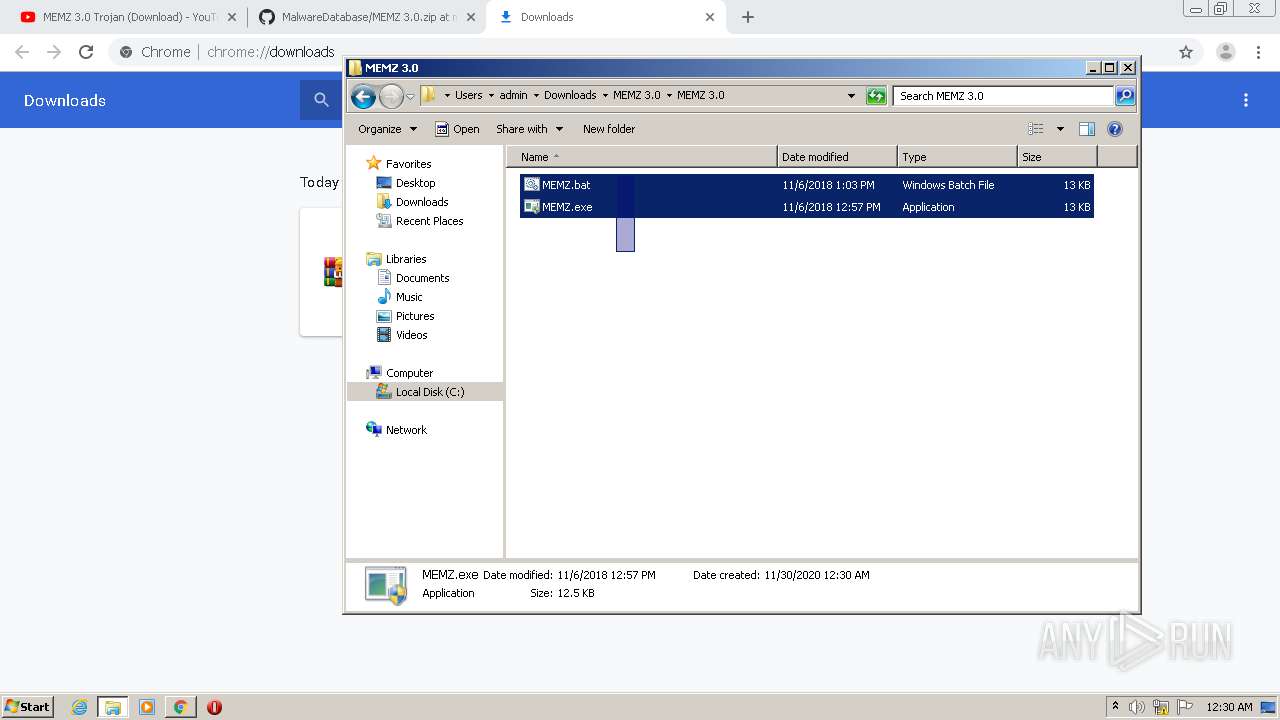
| 480 | "C:\Users\admin\Downloads\MEMZ 3.0\MEMZ 3.0\MEMZ.exe" /main | C:\Users\admin\Downloads\MEMZ 3.0\MEMZ 3.0\MEMZ.exe | MEMZ.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://youtube.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,18076304711630844777,7552877270070508469,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10423532614662576767 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2860 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1240 | "C:\Users\admin\Downloads\MEMZ 3.0\MEMZ 3.0\MEMZ.exe" /watchdog | C:\Users\admin\Downloads\MEMZ 3.0\MEMZ 3.0\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,18076304711630844777,7552877270070508469,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6018223722031239738 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3468 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
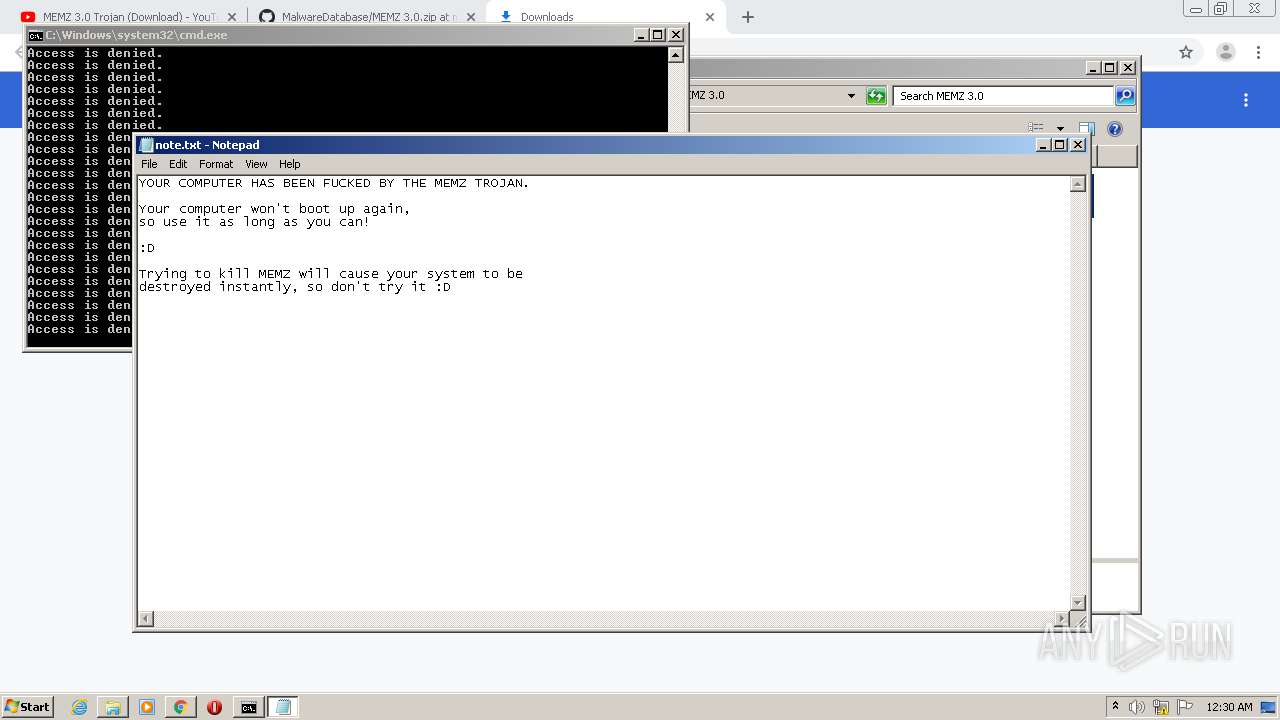
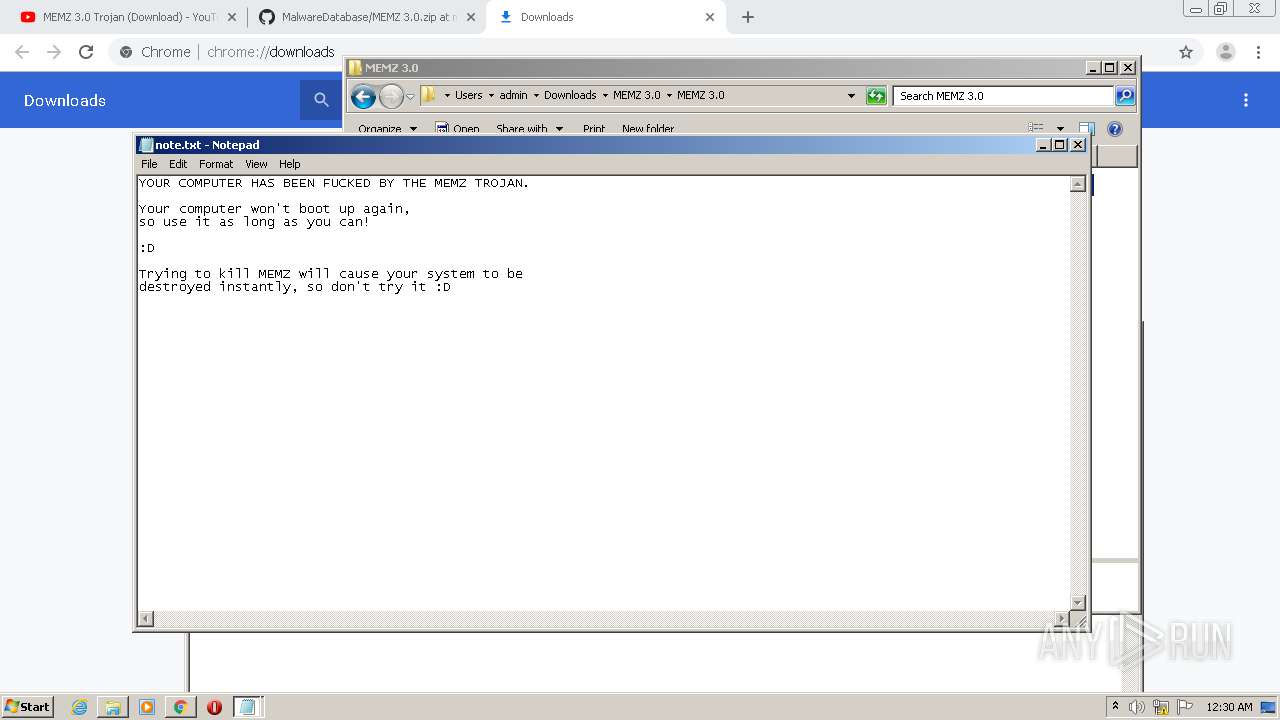
| 1372 | "C:\Windows\System32\notepad.exe" \note.txt | C:\Windows\System32\notepad.exe | — | MEMZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,18076304711630844777,7552877270070508469,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5290353503678900024 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,18076304711630844777,7552877270070508469,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3503888761721241569 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2168 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1736 | "C:\Users\admin\Downloads\MEMZ 3.0\MEMZ 3.0\MEMZ.exe" | C:\Users\admin\Downloads\MEMZ 3.0\MEMZ 3.0\MEMZ.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1744 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /watchdog | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
3 993
Read events
3 743
Write events
247
Delete events
3
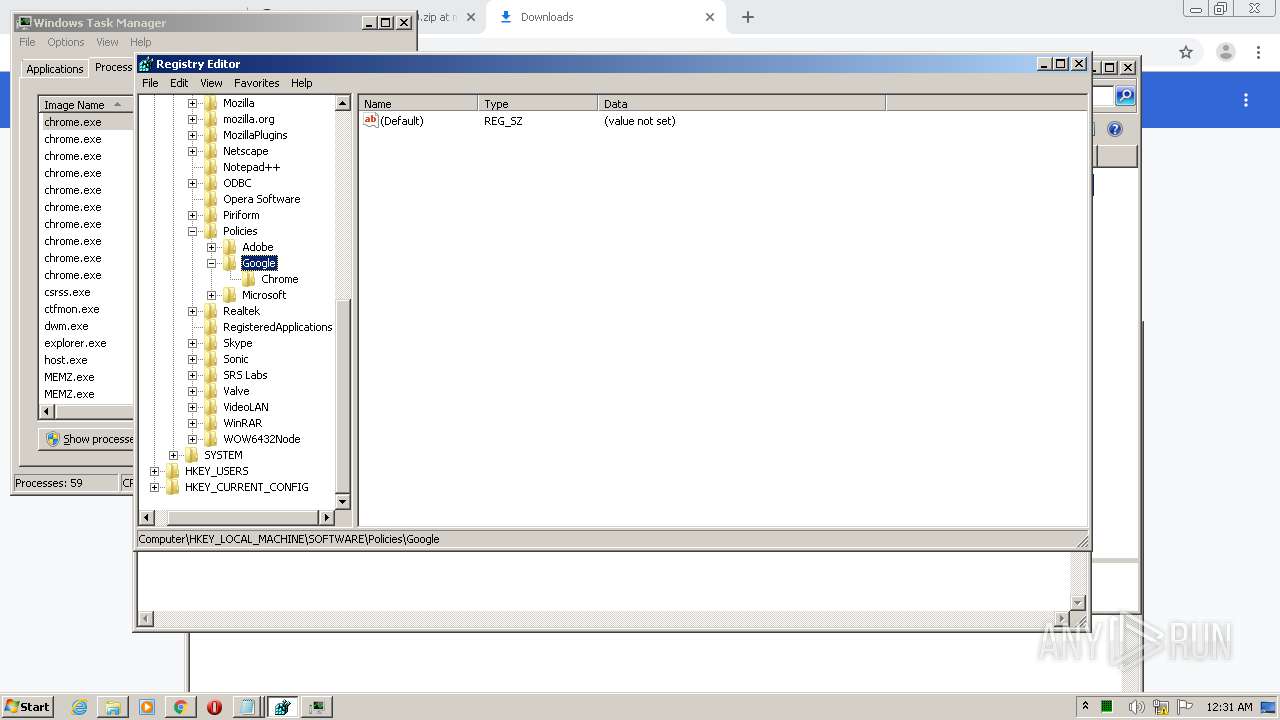
Modification events
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1096-13251169734472750 |
Value: 259 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
79
Text files
211
Unknown types
20
Dropped files
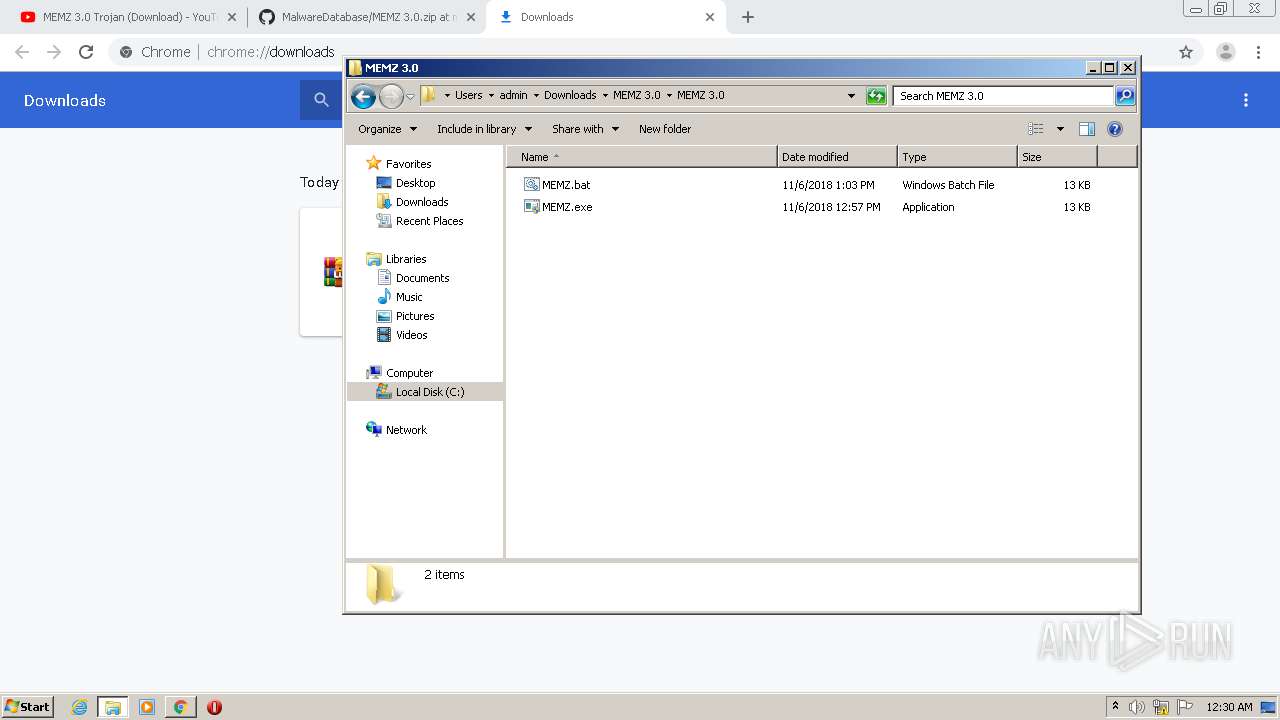
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC43CC7-448.pma | — | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2a44cc81-9ebb-47e0-9ef1-3e6779988a2a.tmp | — | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF13f02f.TMP | text | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF13f06e.TMP | text | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF13f04f.TMP | text | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF13f204.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
64
DNS requests
46
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4080 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDliVAU%2F6ZWzwIAAAAAgFX%2B | US | der | 472 b | whitelisted |
4080 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEB8qXupijjEMAgAAAACAViQ%3D | US | der | 471 b | whitelisted |
4080 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDliVAU%2F6ZWzwIAAAAAgFX%2B | US | der | 472 b | whitelisted |
4080 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDgM%2F2Oalb9SggAAAAAYth0 | US | der | 472 b | whitelisted |
4080 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
4080 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDgM%2F2Oalb9SggAAAAAYth0 | US | der | 472 b | whitelisted |
4080 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEB8qXupijjEMAgAAAACAViQ%3D | US | der | 471 b | whitelisted |
2848 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
4080 | iexplore.exe | GET | 200 | 216.58.207.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1872 | chrome.exe | 64.233.168.93:443 | youtube.com | Google Inc. | US | unknown |
1872 | chrome.exe | 142.250.28.136:443 | www.youtube.com | Google Inc. | US | unknown |
1872 | chrome.exe | 172.217.12.205:443 | accounts.google.com | Google Inc. | US | suspicious |
1872 | chrome.exe | 172.217.21.214:443 | i.ytimg.com | Google Inc. | US | whitelisted |
1872 | chrome.exe | 216.58.212.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1872 | chrome.exe | 172.217.11.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1872 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1872 | chrome.exe | 142.250.80.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1872 | chrome.exe | 64.233.179.139:443 | consent.youtube.com | Google Inc. | US | whitelisted |
1872 | chrome.exe | 172.217.12.206:443 | play.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
youtube.com |
| whitelisted |
accounts.google.com |
| shared |
www.youtube.com |
| whitelisted |
i.ytimg.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
yt3.ggpht.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.se |
| whitelisted |