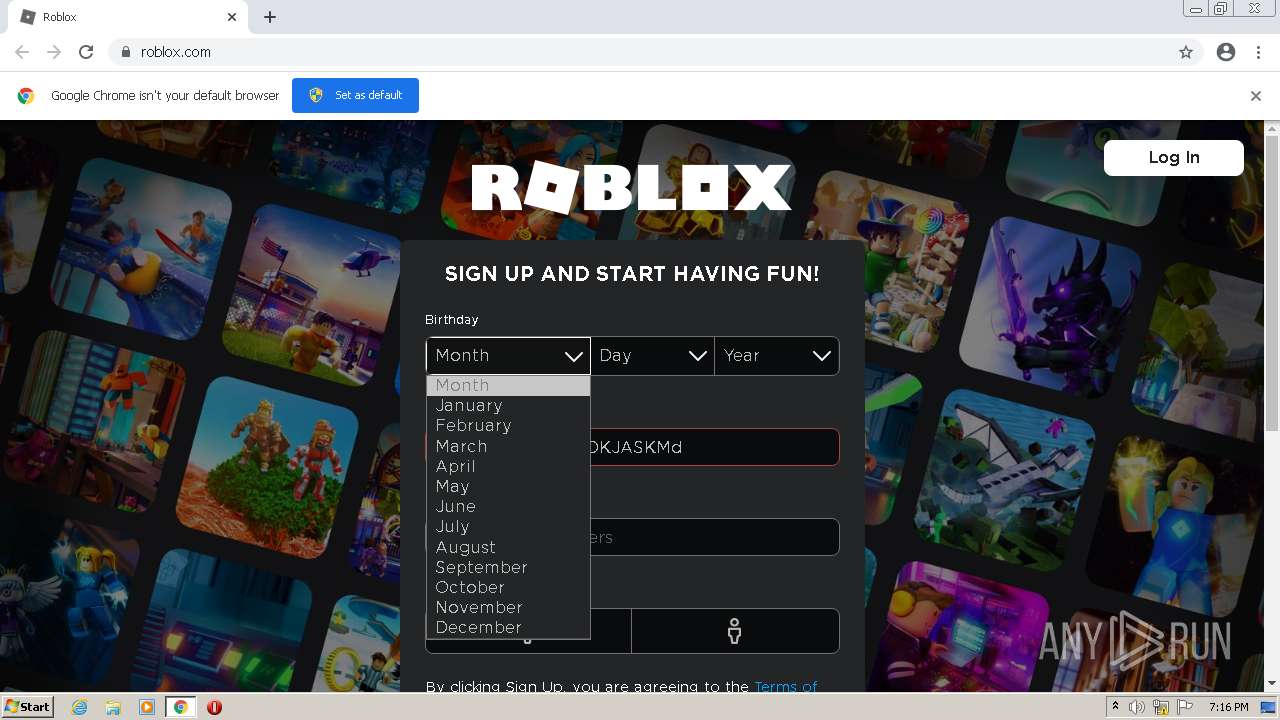
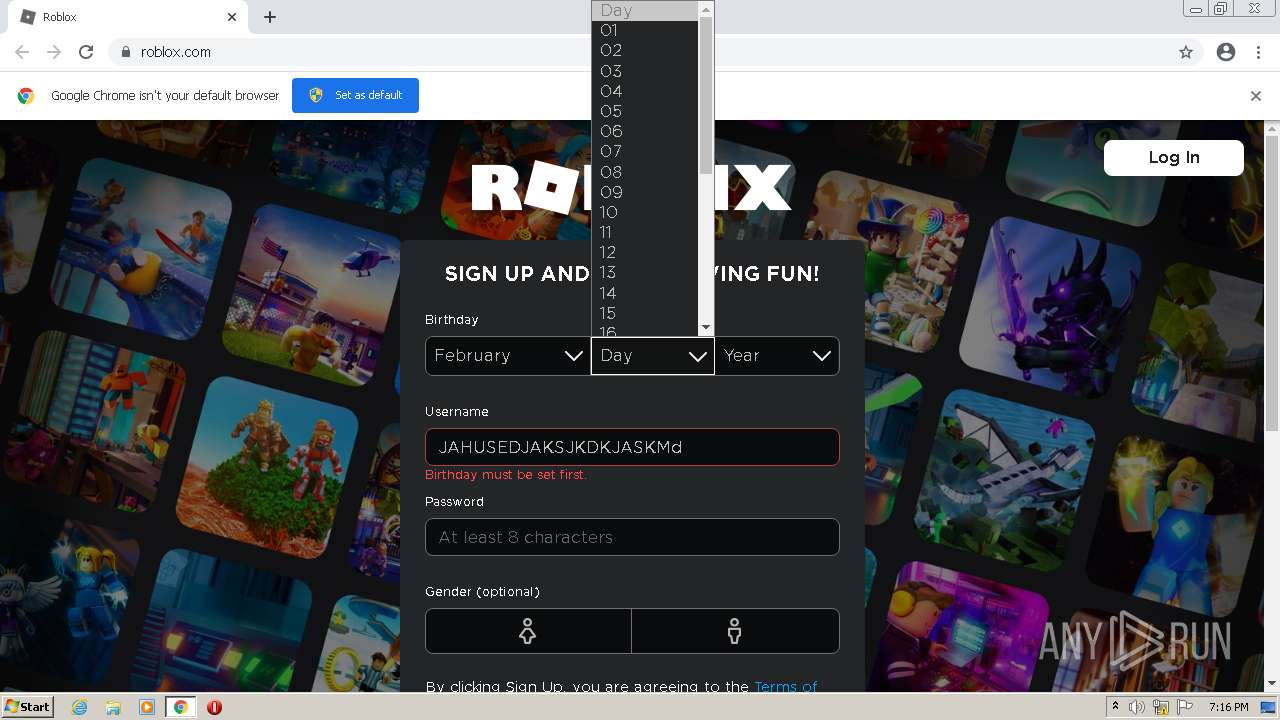
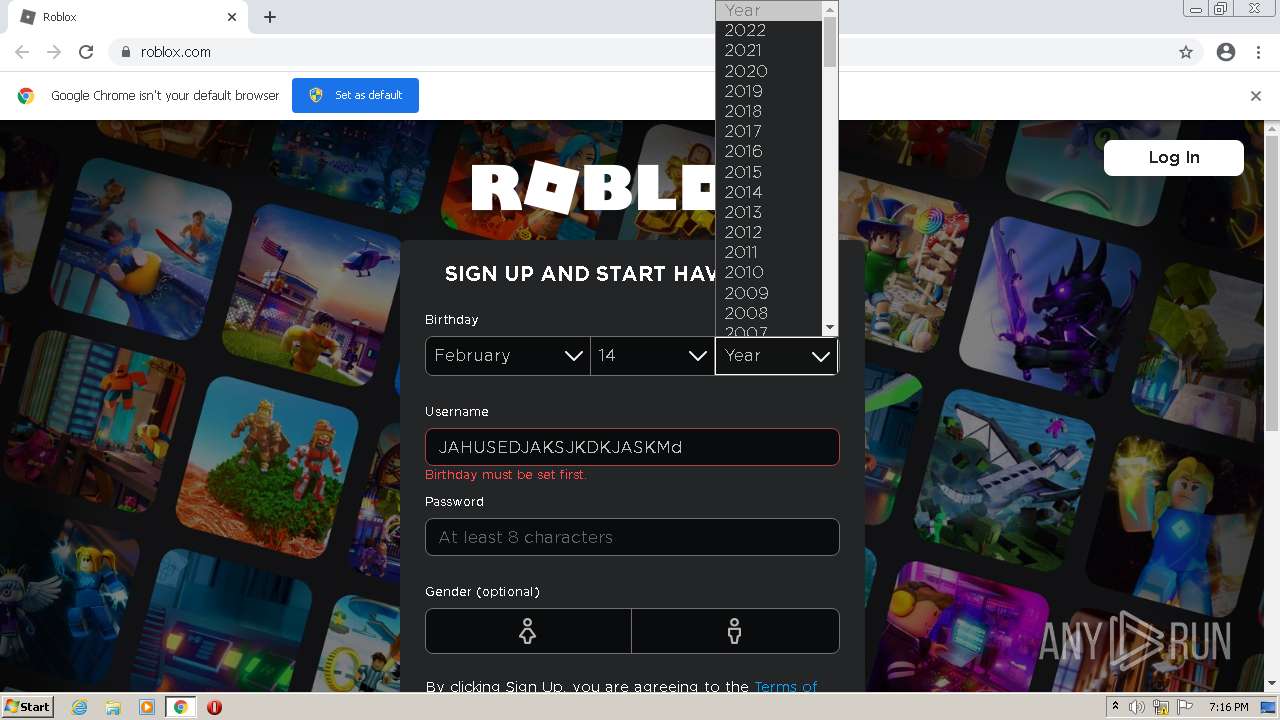
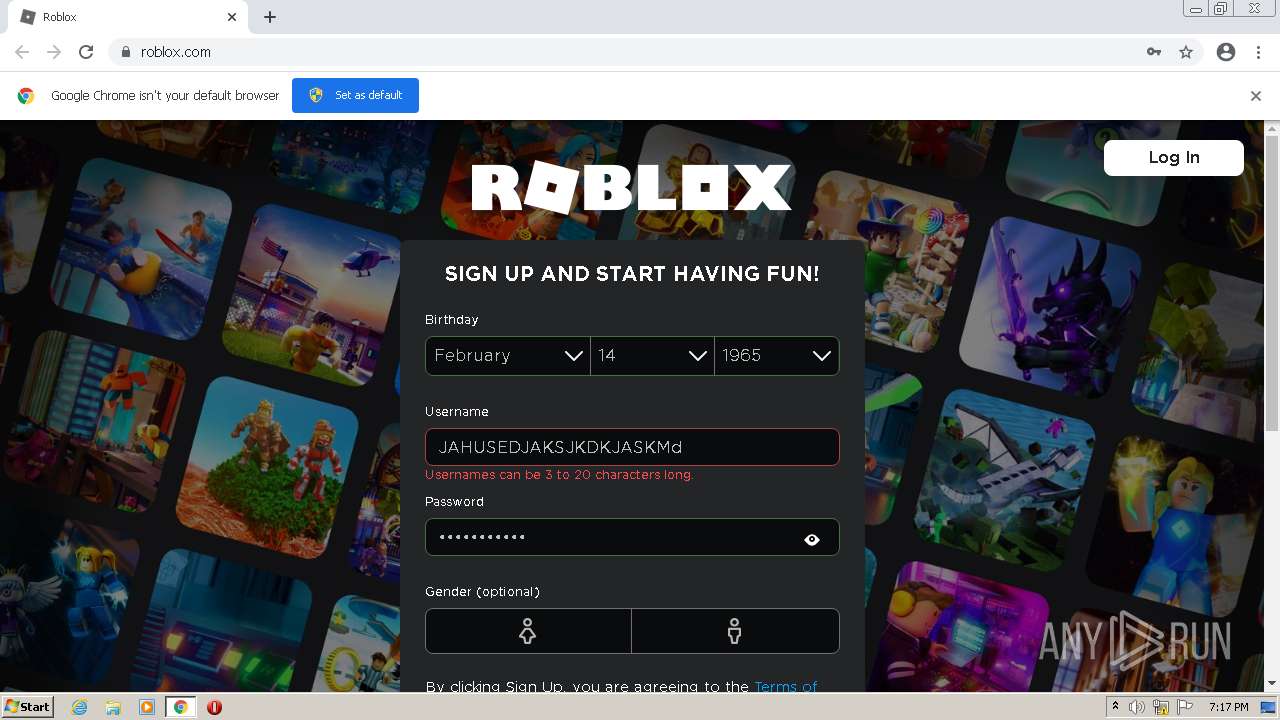
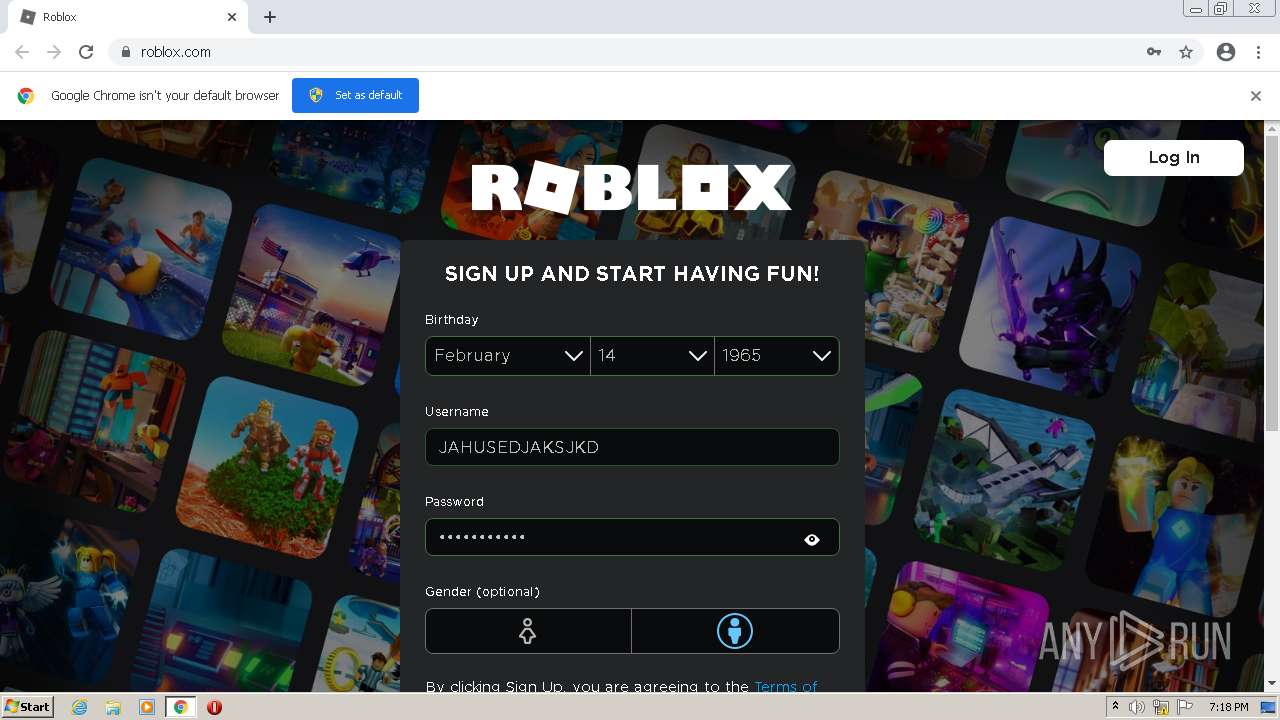
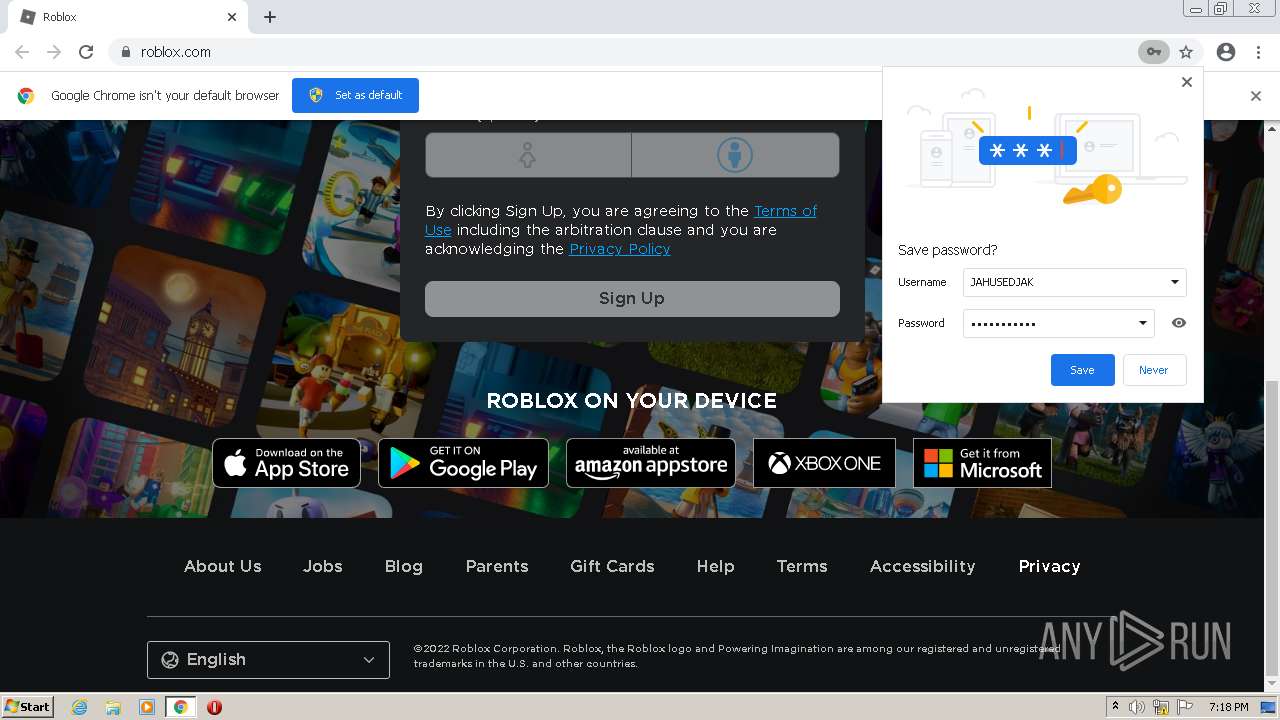
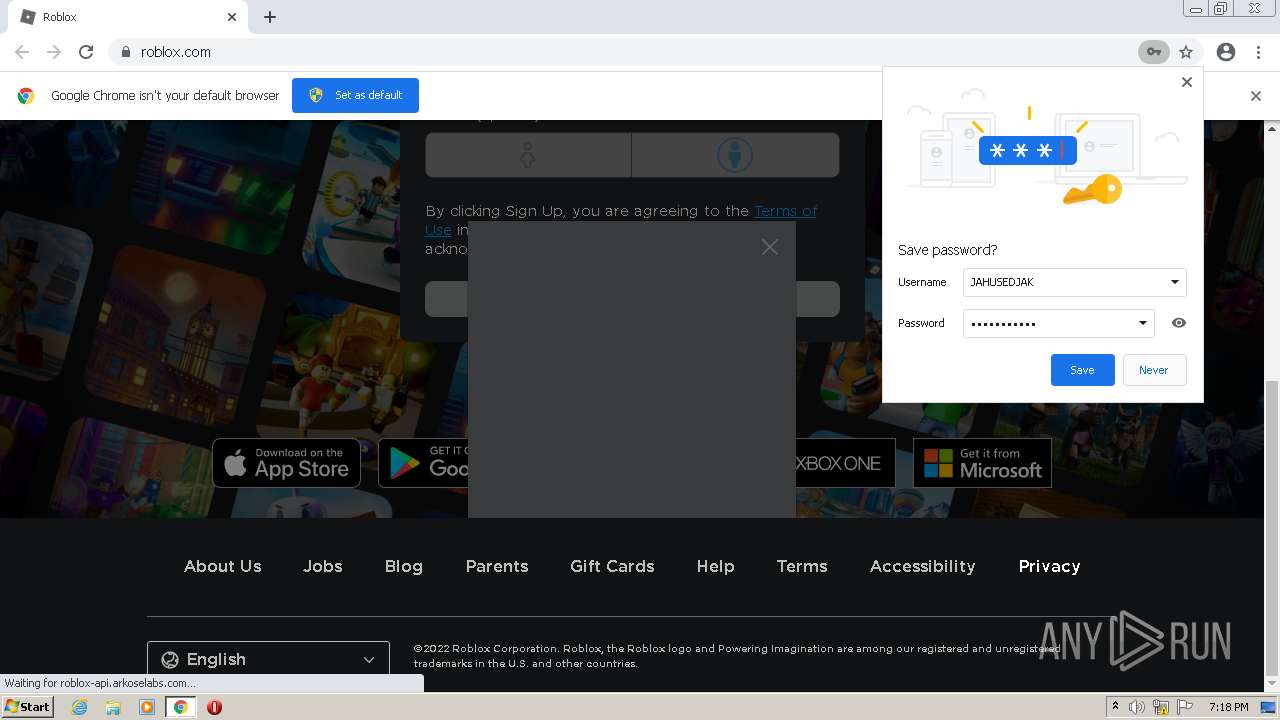
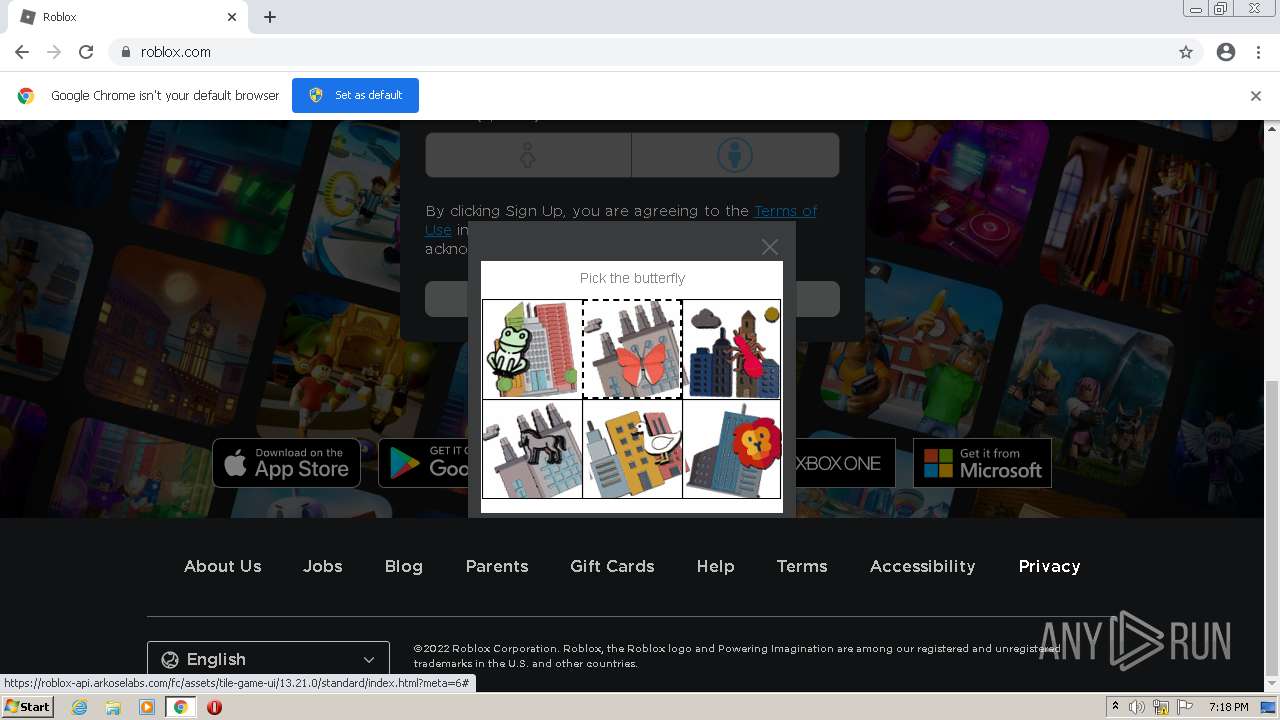
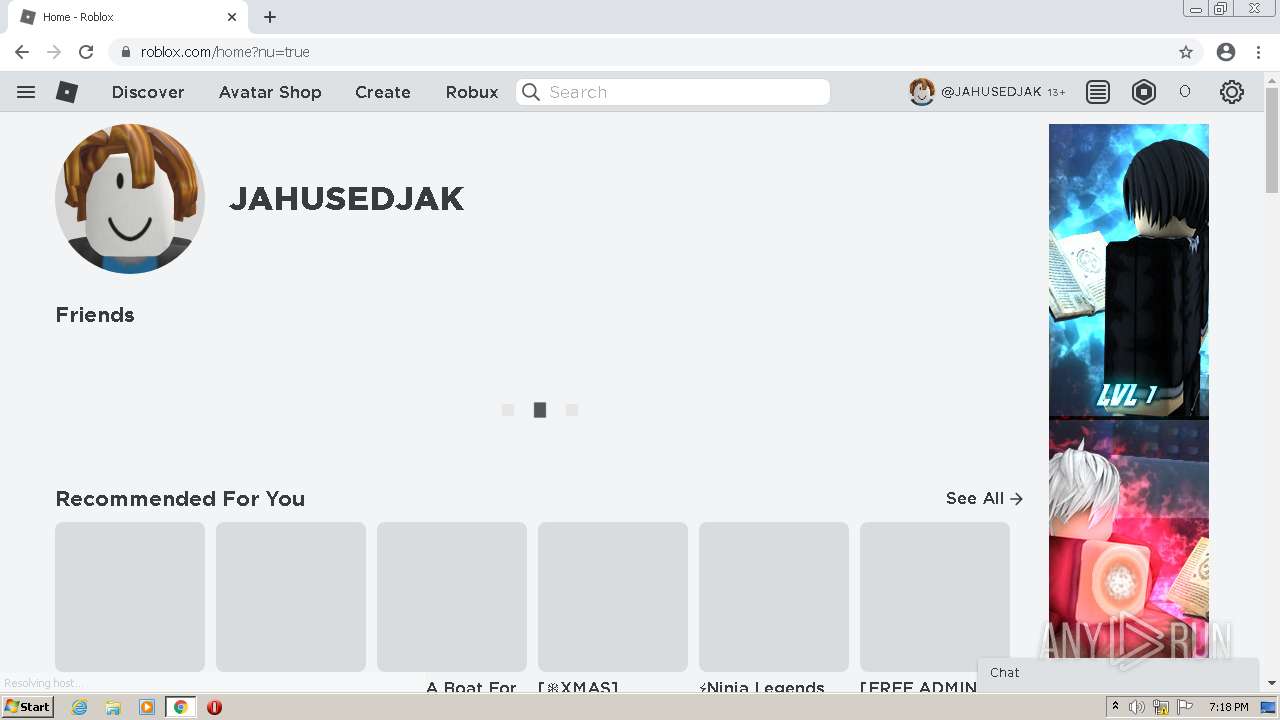
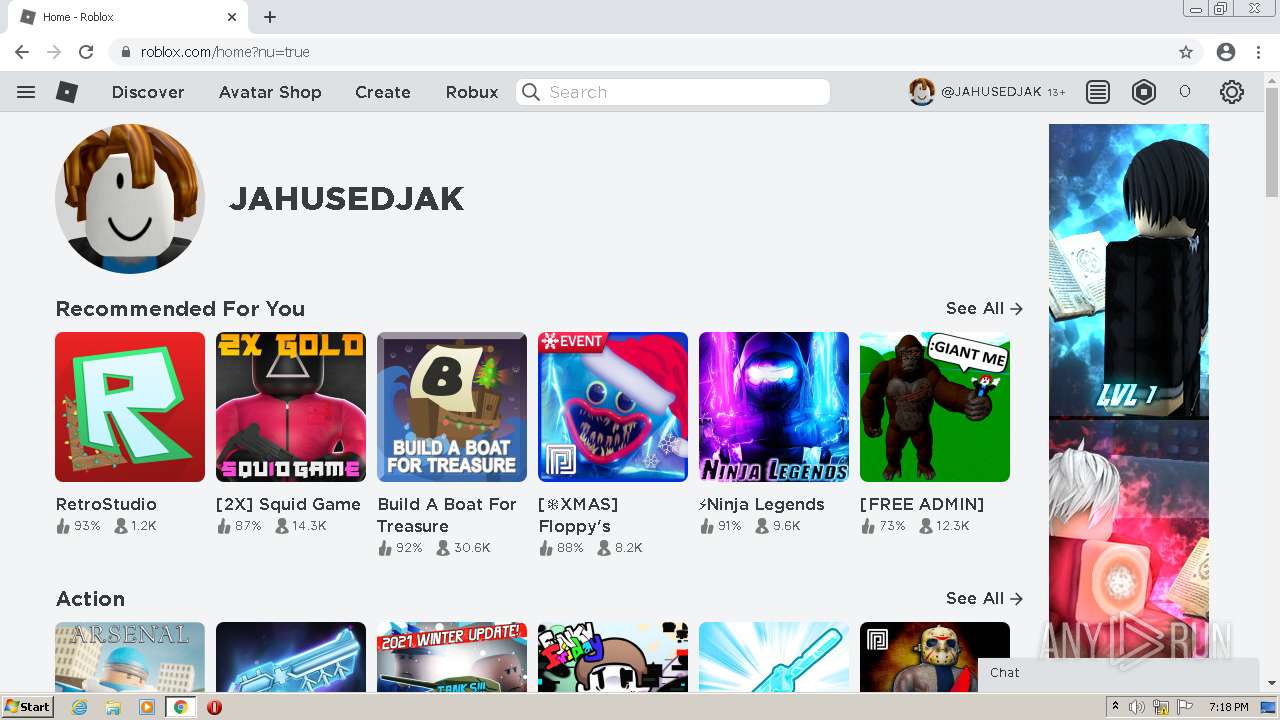
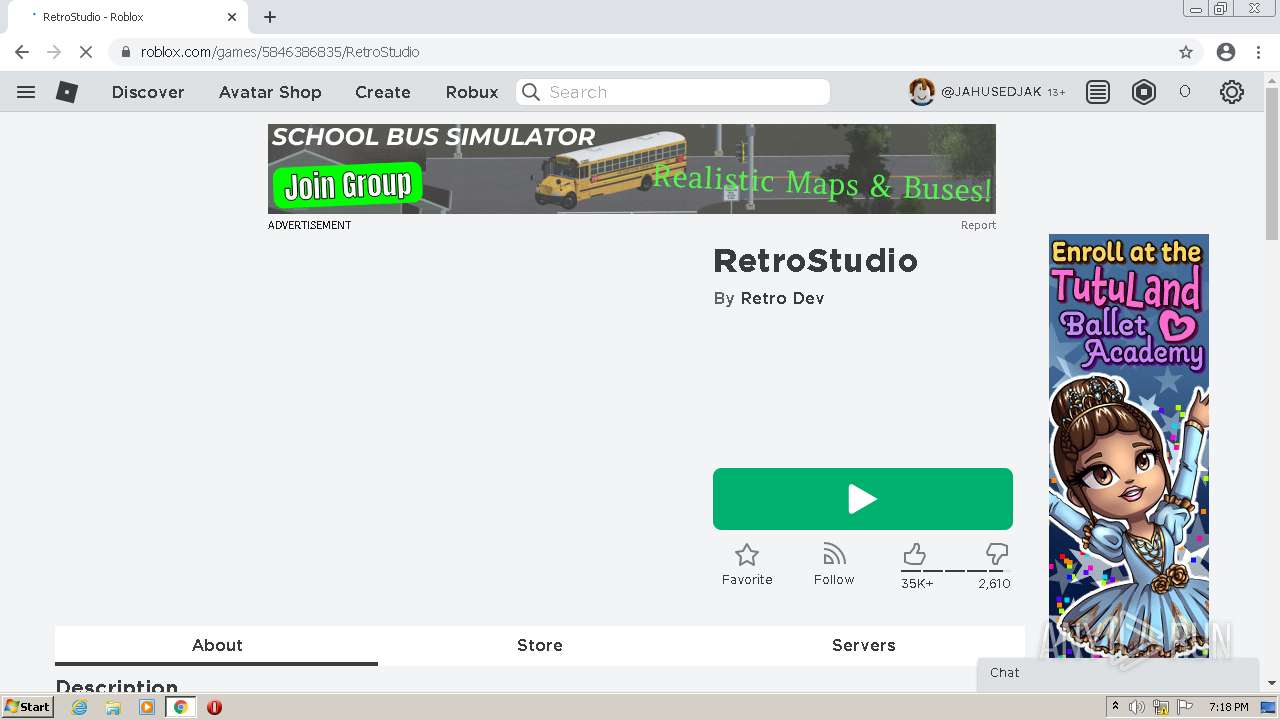
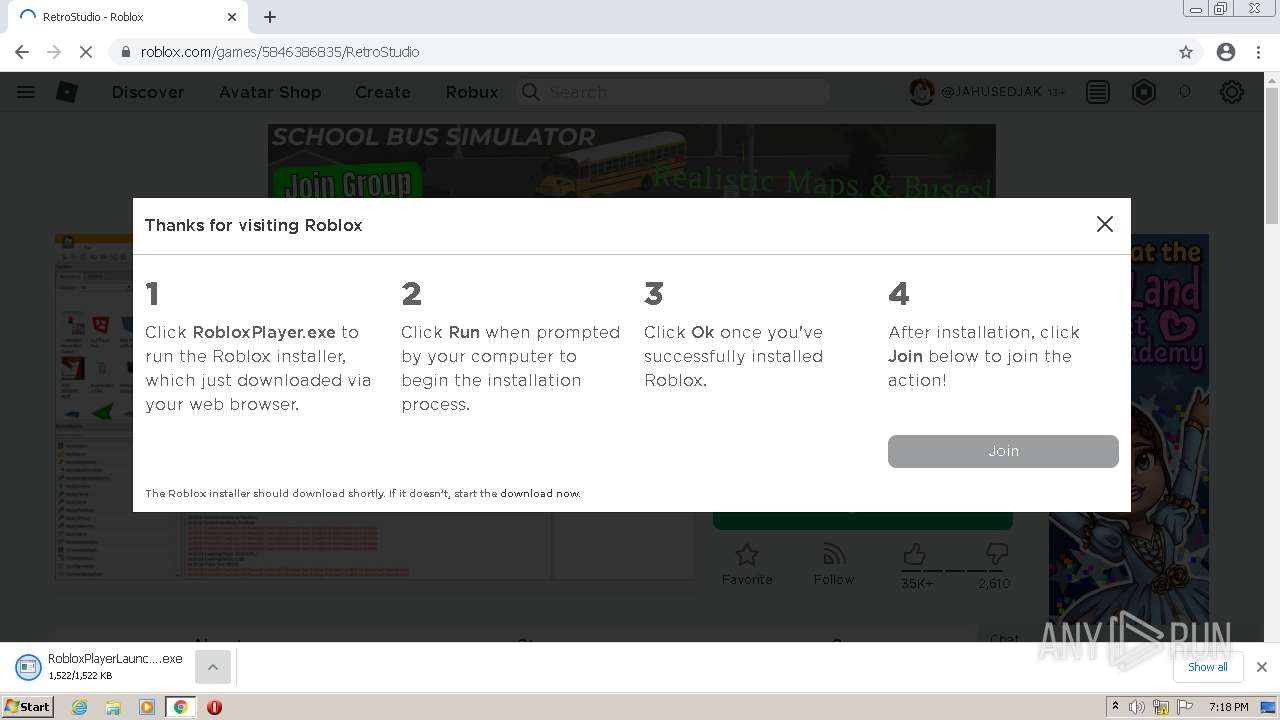
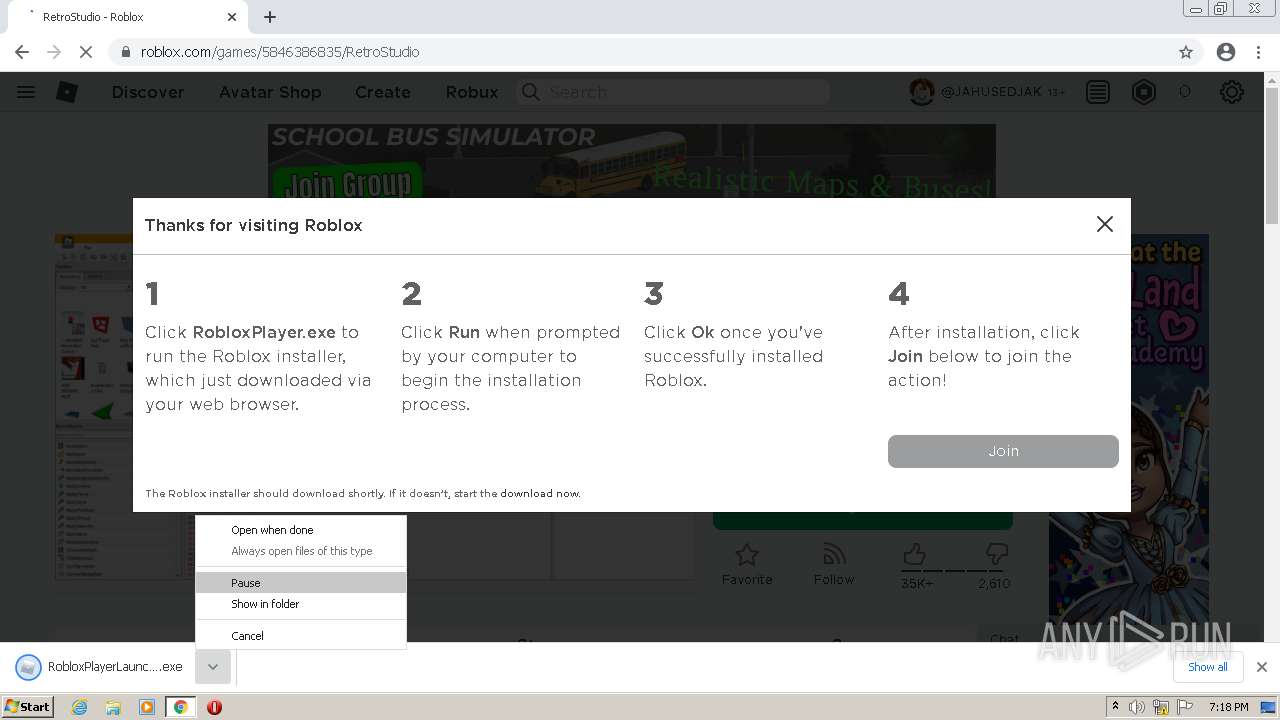
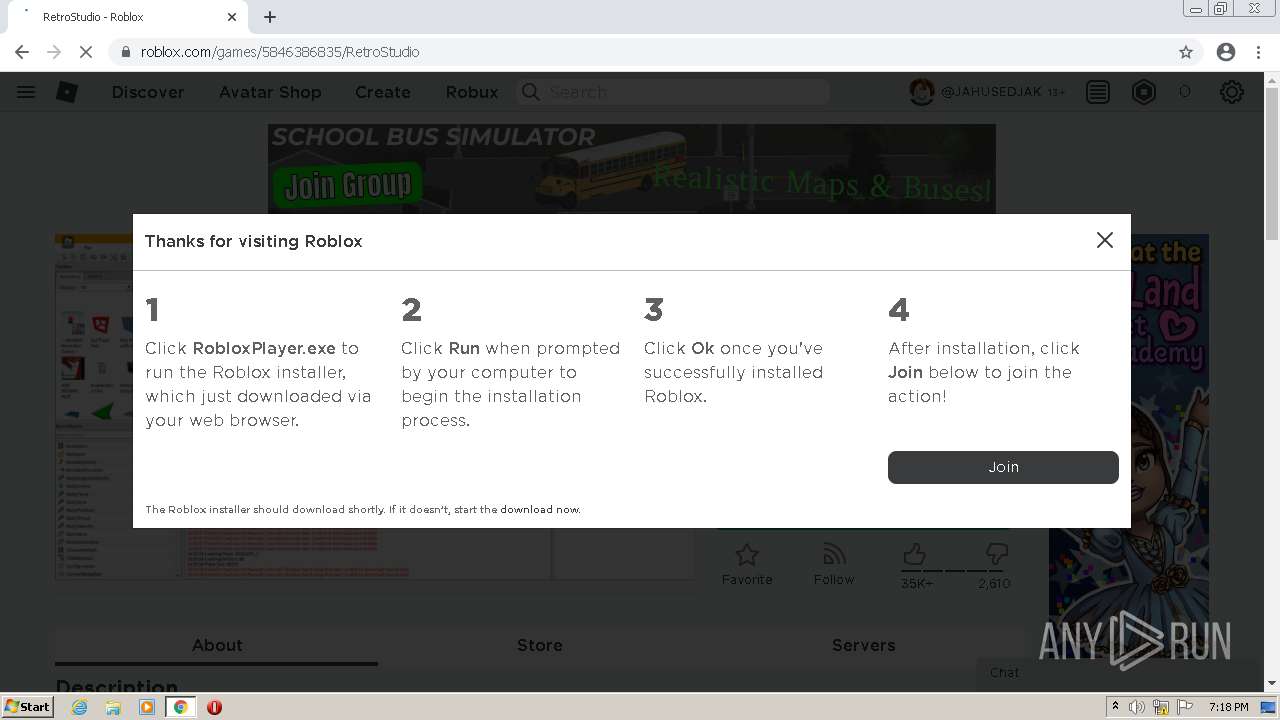
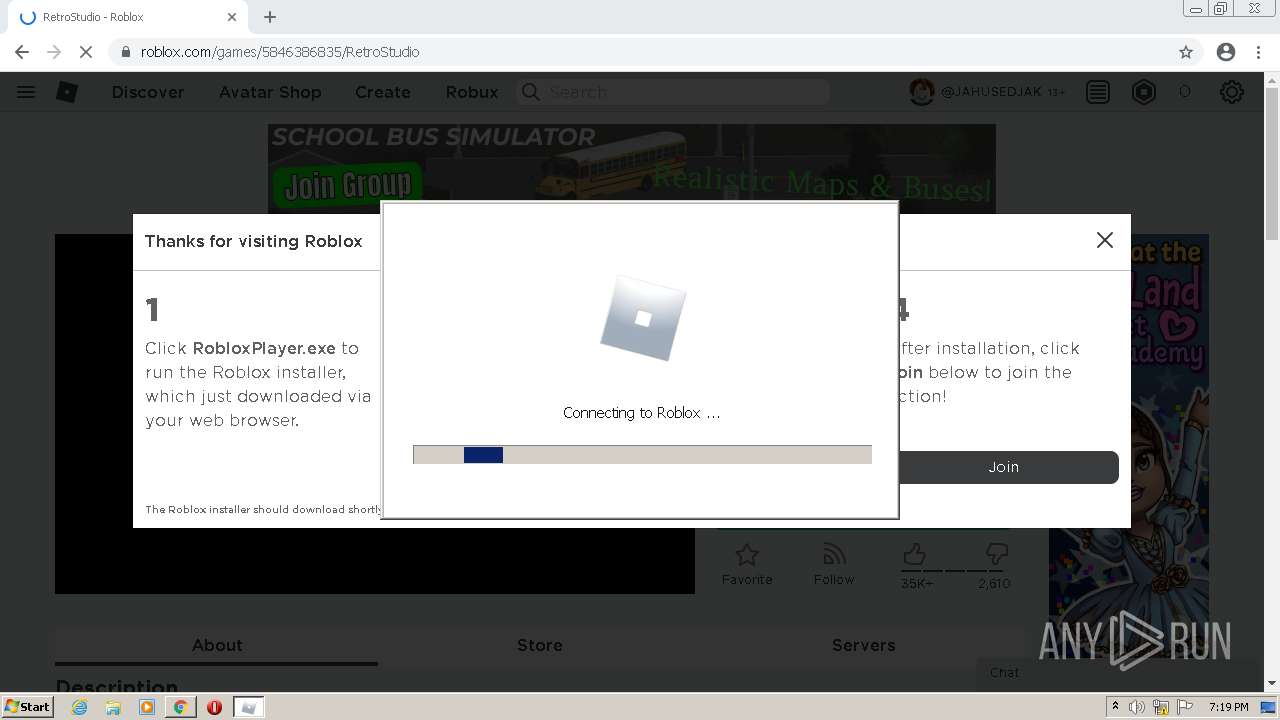
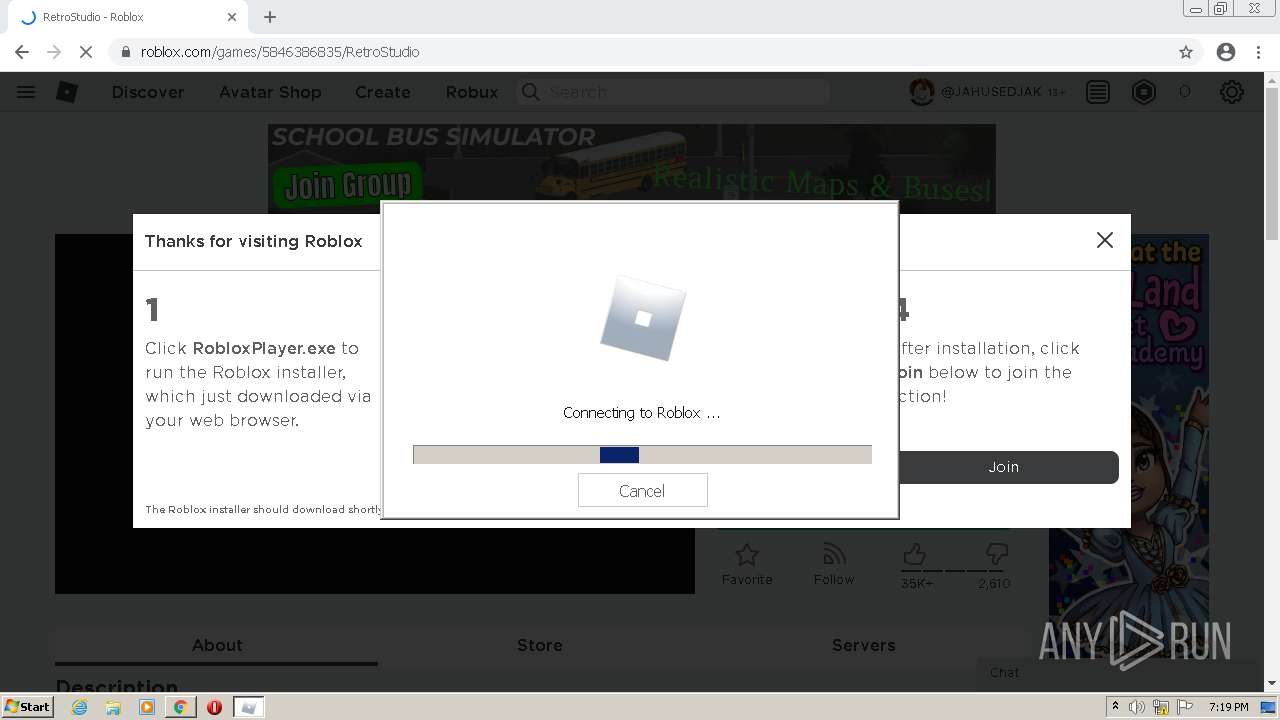
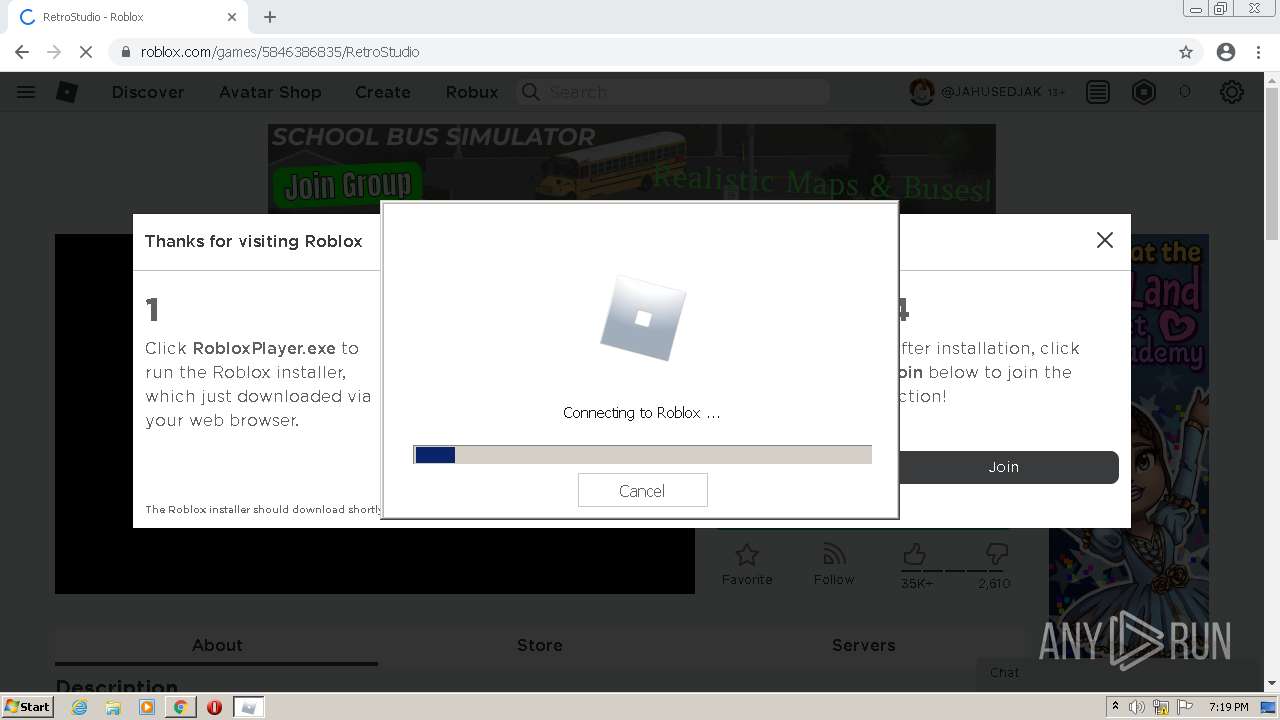
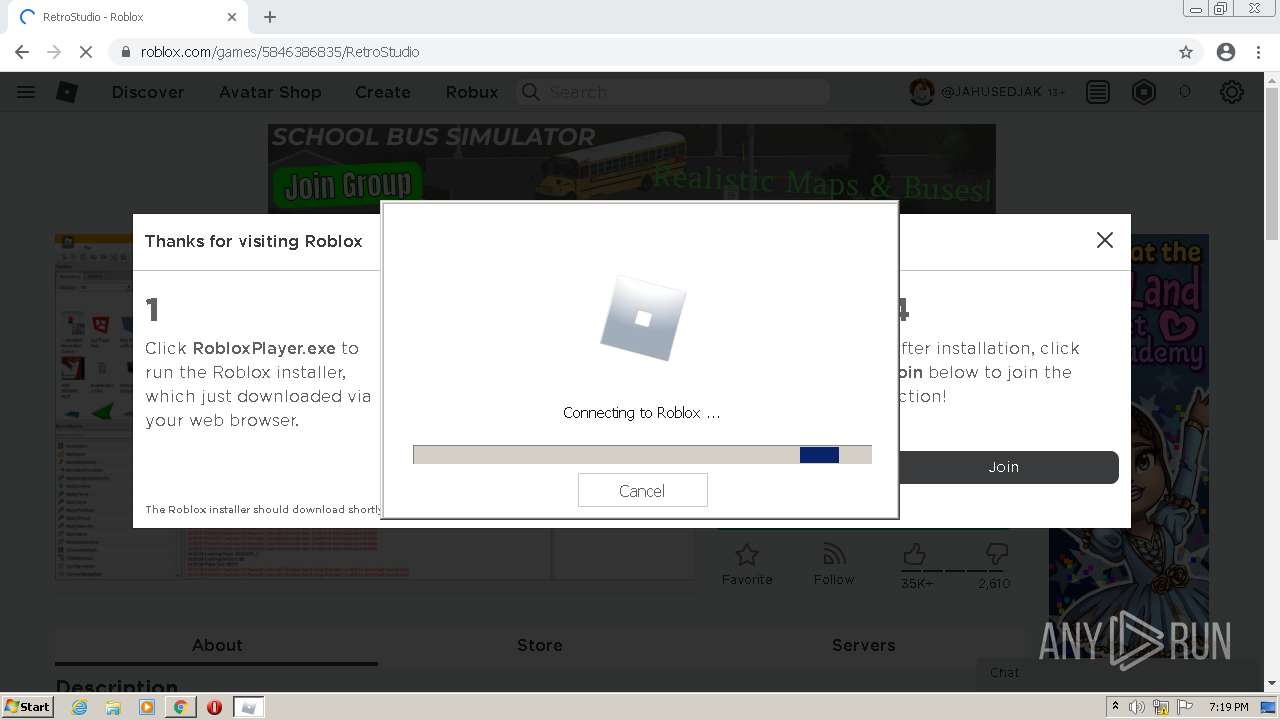
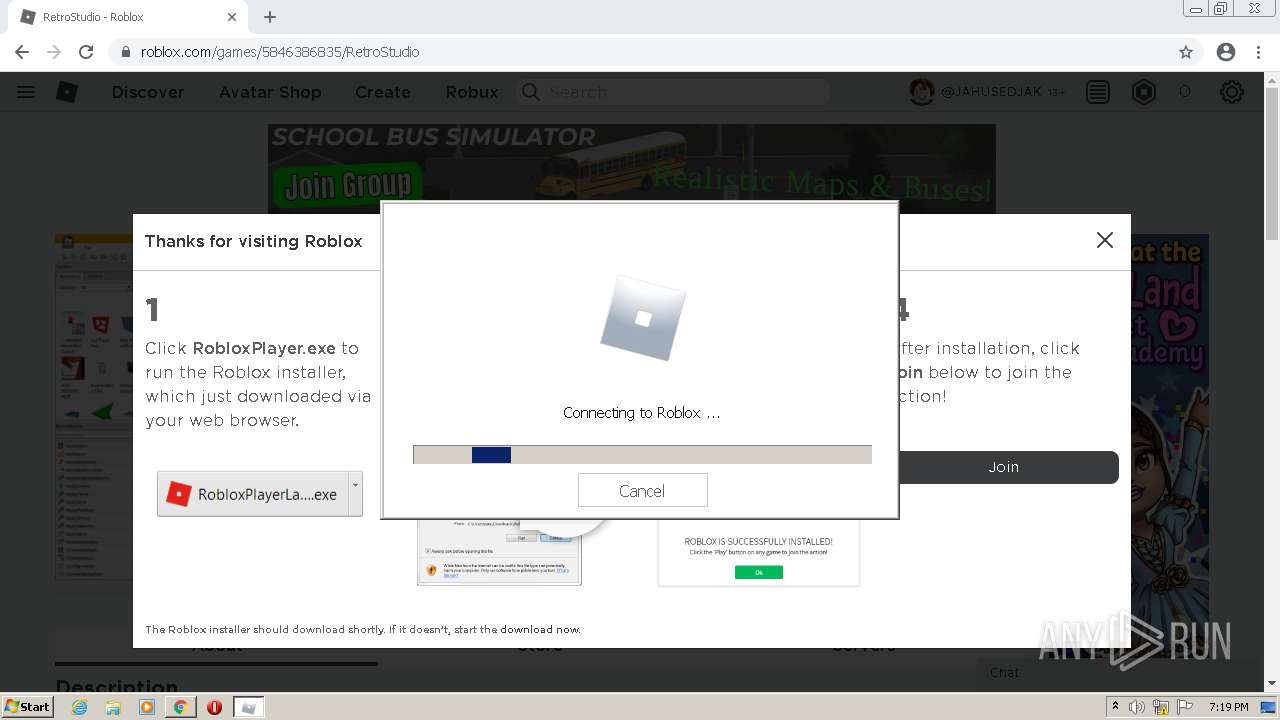
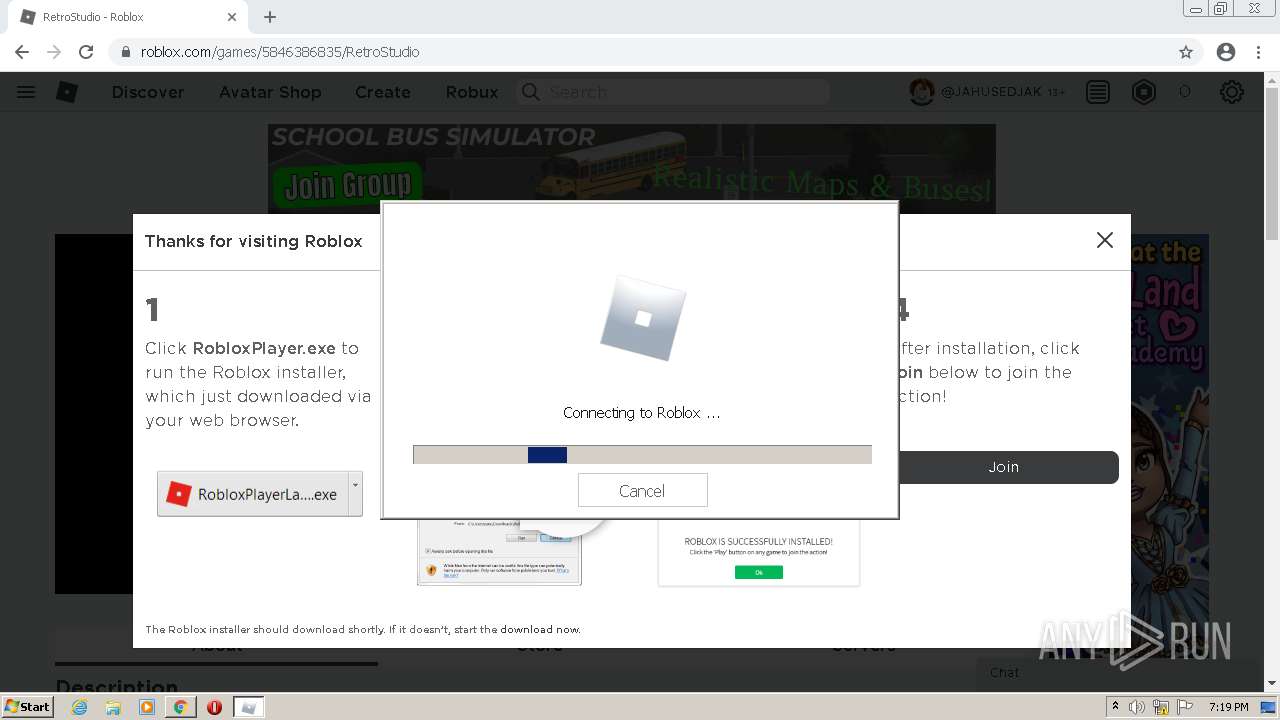
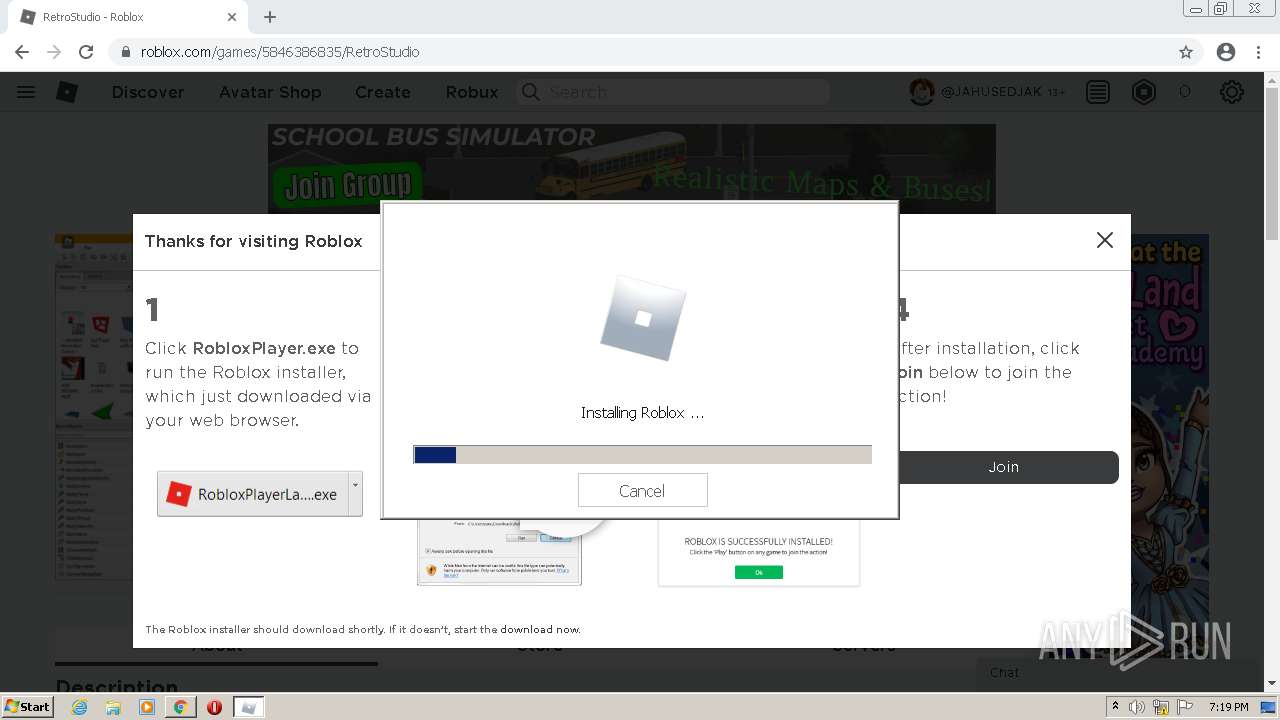
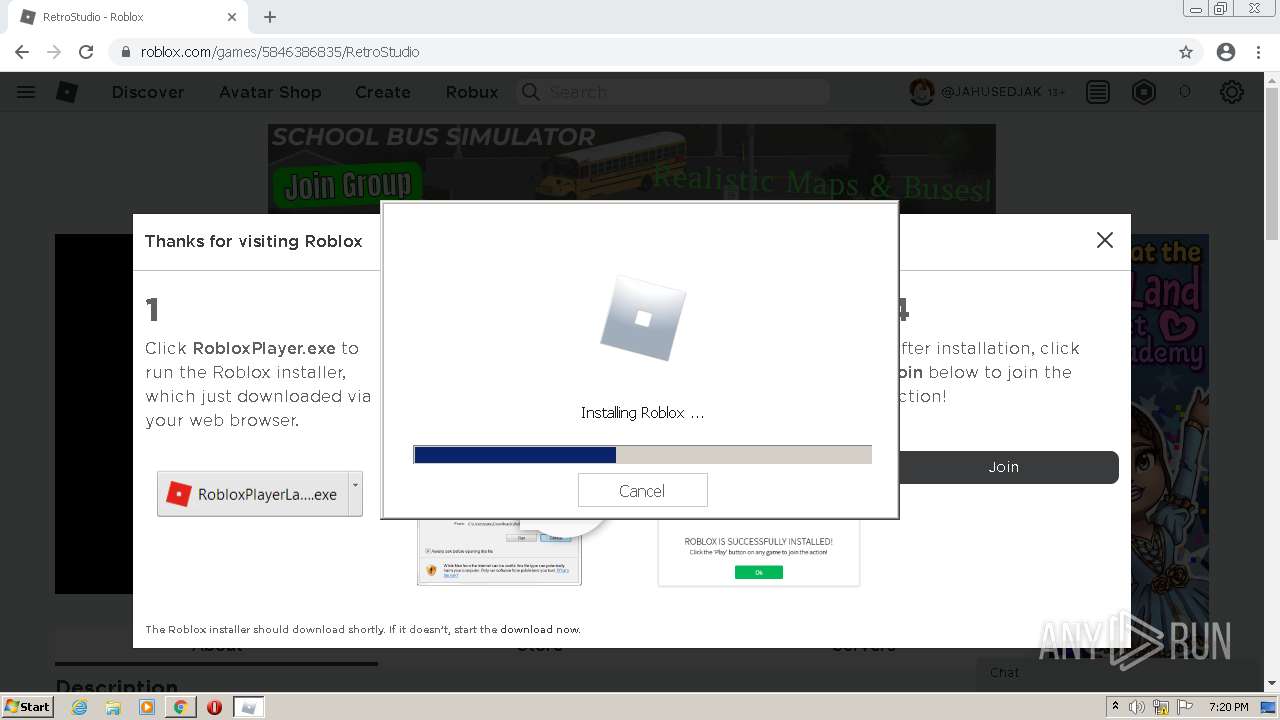
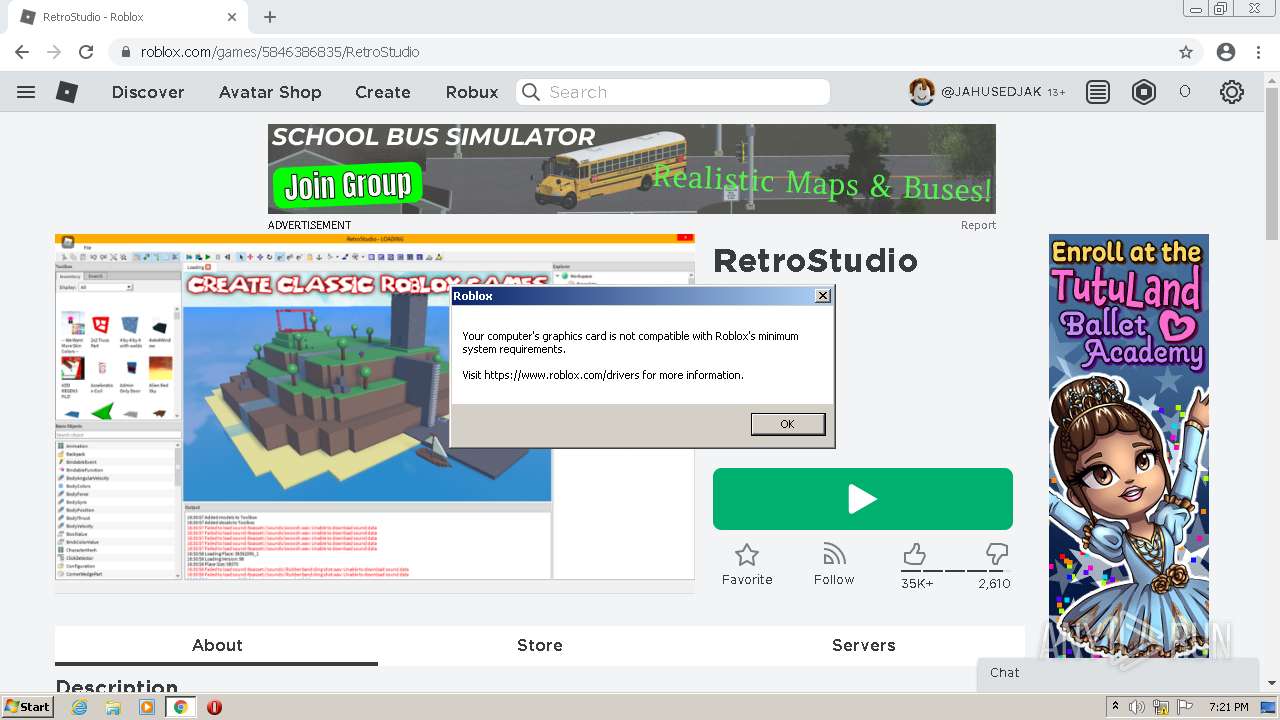
| URL: | https://www.roblox.com |
| Full analysis: | https://app.any.run/tasks/73490cfe-c9ee-43da-863c-4509f5aa4498 |
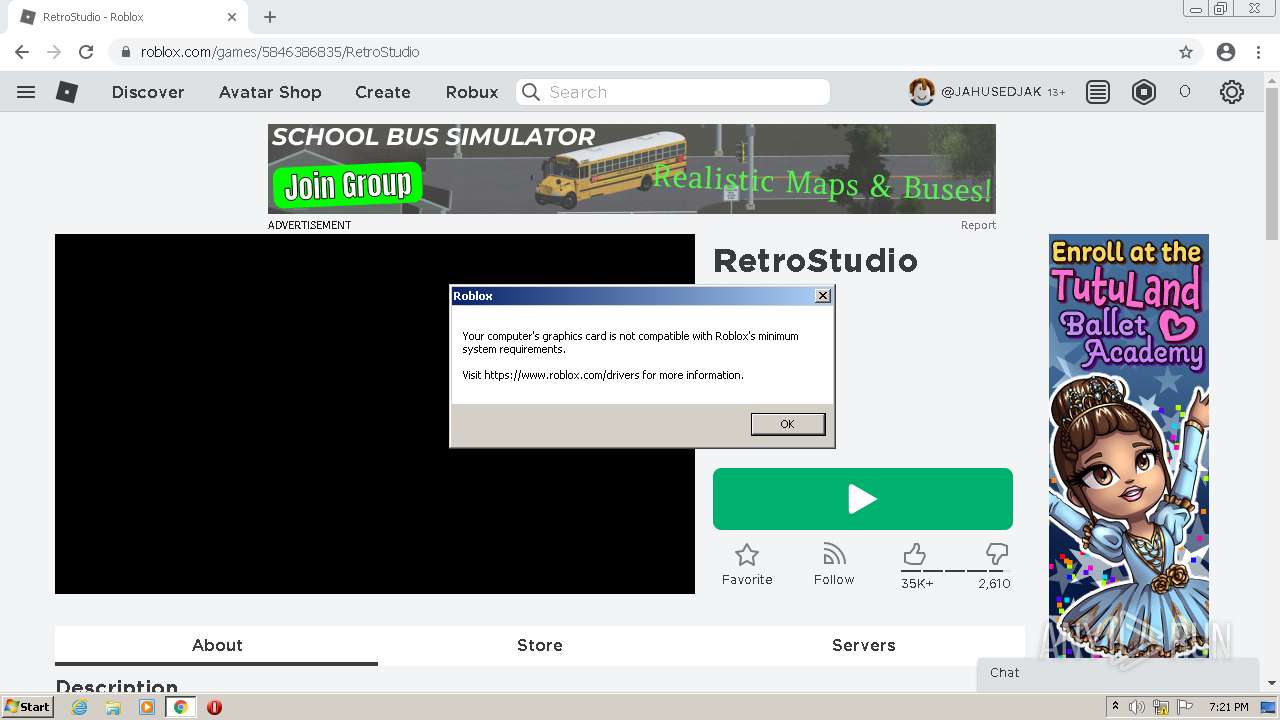
| Verdict: | Malicious activity |
| Analysis date: | January 04, 2022, 19:16:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9ABEFD8D4DB253D3A04A22352B7761EA |
| SHA1: | 975535FE4E006738B3ADC067CD00024B1B3C4296 |
| SHA256: | 14647379C0B84766CD19A0F3CD89F3E40591B98A52ED4C6A2D51E4A5E3B1D5BE |
| SSDEEP: | 3:N8DSLaHE3In:2OLatn |
MALICIOUS
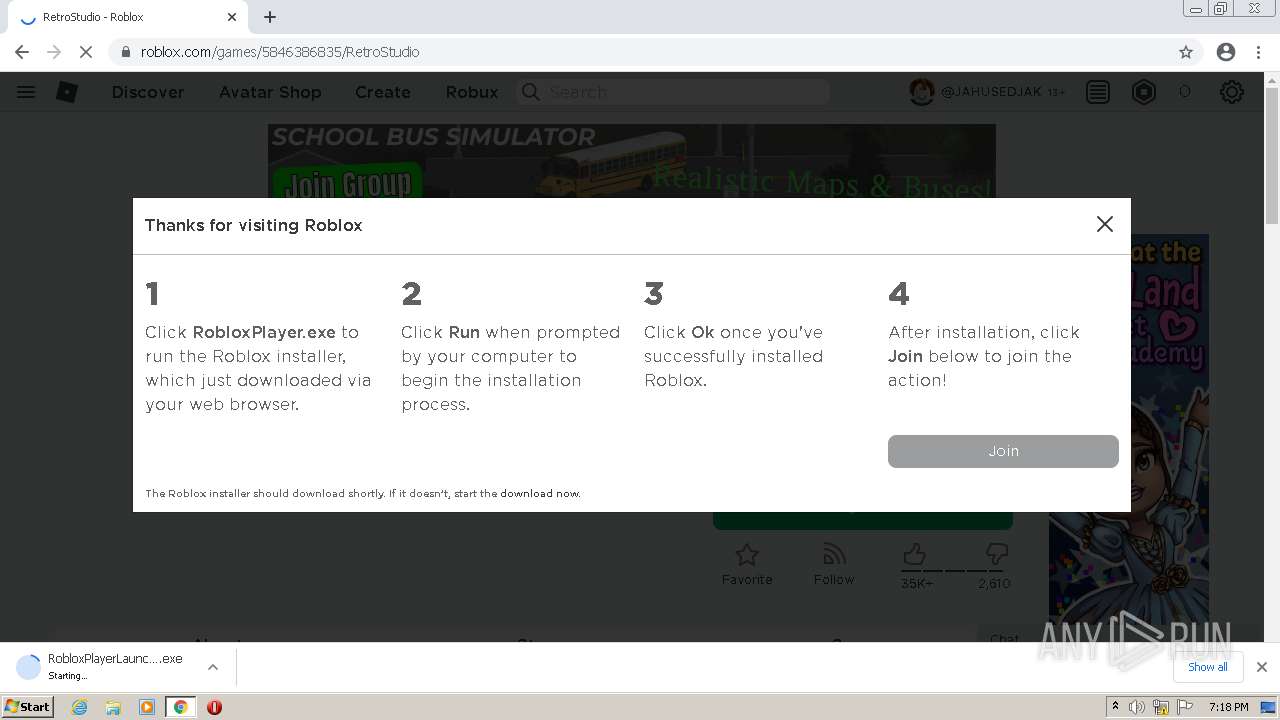
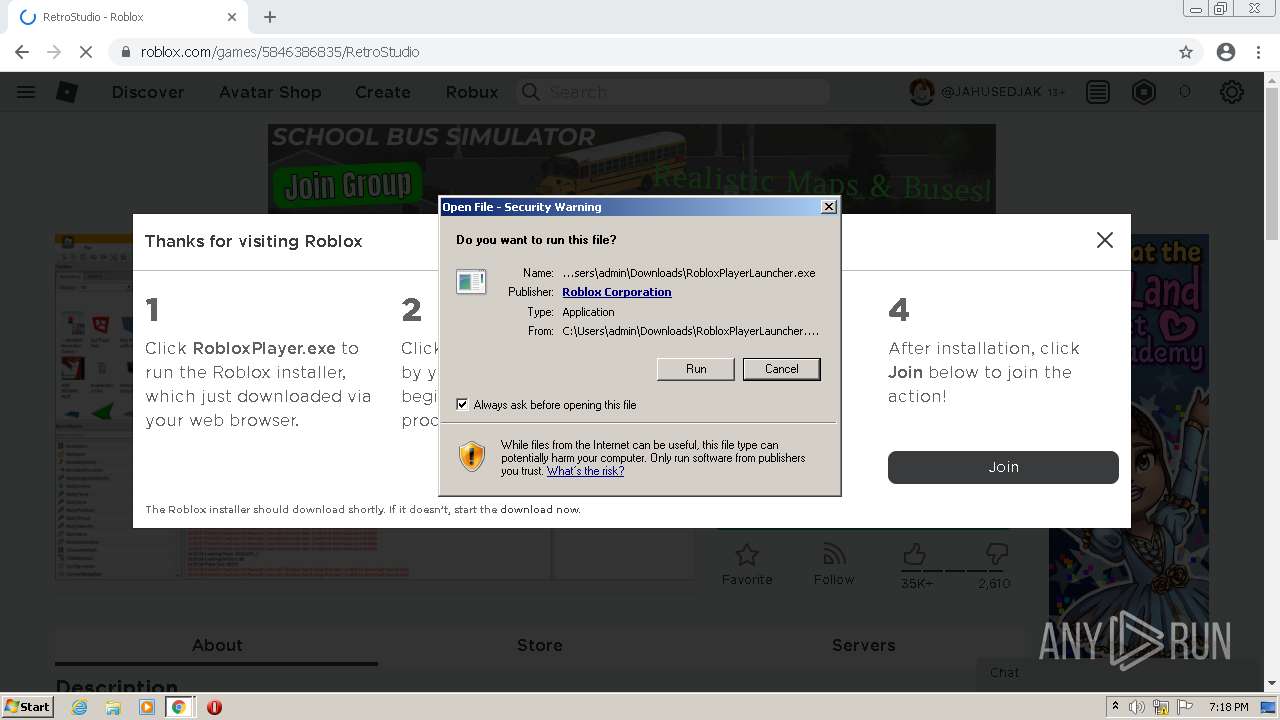
Application was dropped or rewritten from another process
- RobloxPlayerLauncher.exe (PID: 4092)
- RobloxPlayerLauncher.exe (PID: 3052)
- RobloxPlayerLauncher.exe (PID: 2764)
- RobloxPlayerLauncher.exe (PID: 2144)
Drops executable file immediately after starts
- chrome.exe (PID: 3120)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3148)
- RobloxPlayerLauncher.exe (PID: 4092)
- chrome.exe (PID: 3120)
Drops a file with too old compile date
- chrome.exe (PID: 3148)
- RobloxPlayerLauncher.exe (PID: 4092)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3148)
- RobloxPlayerLauncher.exe (PID: 4092)
- chrome.exe (PID: 3120)
Reads Microsoft Outlook installation path
- chrome.exe (PID: 3496)
Reads the computer name
- RobloxPlayerLauncher.exe (PID: 4092)
- RobloxPlayerLauncher.exe (PID: 3052)
- RobloxPlayerLauncher.exe (PID: 2764)
- RobloxPlayerBeta.exe (PID: 2612)
- RobloxPlayerLauncher.exe (PID: 2144)
Application launched itself
- RobloxPlayerLauncher.exe (PID: 4092)
- RobloxPlayerLauncher.exe (PID: 2764)
Checks supported languages
- RobloxPlayerLauncher.exe (PID: 4092)
- RobloxPlayerLauncher.exe (PID: 3052)
- RobloxPlayerLauncher.exe (PID: 2764)
- RobloxPlayerLauncher.exe (PID: 2144)
- RobloxPlayerBeta.exe (PID: 2612)
Creates files in the user directory
- RobloxPlayerLauncher.exe (PID: 4092)
Changes default file association
- RobloxPlayerLauncher.exe (PID: 4092)
Drops a file with a compile date too recent
- RobloxPlayerLauncher.exe (PID: 4092)
Creates a software uninstall entry
- RobloxPlayerLauncher.exe (PID: 4092)
Changes IE settings (feature browser emulation)
- RobloxPlayerBeta.exe (PID: 2612)
INFO
Checks supported languages
- chrome.exe (PID: 3148)
- chrome.exe (PID: 1844)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 1512)
- chrome.exe (PID: 2660)
- chrome.exe (PID: 188)
- chrome.exe (PID: 448)
- chrome.exe (PID: 468)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 1256)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 304)
- chrome.exe (PID: 3540)
- chrome.exe (PID: 1460)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 1896)
- chrome.exe (PID: 416)
- chrome.exe (PID: 2332)
- chrome.exe (PID: 580)
- chrome.exe (PID: 2416)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 3496)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 2452)
- chrome.exe (PID: 3256)
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 3792)
- chrome.exe (PID: 3120)
- chrome.exe (PID: 2936)
- chrome.exe (PID: 2652)
- chrome.exe (PID: 2896)
Reads the hosts file
- chrome.exe (PID: 3148)
- chrome.exe (PID: 4072)
Reads the computer name
- chrome.exe (PID: 3148)
- chrome.exe (PID: 468)
- chrome.exe (PID: 4024)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 448)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 3504)
- chrome.exe (PID: 1256)
- chrome.exe (PID: 3520)
- chrome.exe (PID: 1460)
- chrome.exe (PID: 580)
- chrome.exe (PID: 3496)
- chrome.exe (PID: 2896)
Application launched itself
- chrome.exe (PID: 3148)
Reads settings of System Certificates
- chrome.exe (PID: 4072)
- chrome.exe (PID: 3148)
- RobloxPlayerLauncher.exe (PID: 4092)
- RobloxPlayerLauncher.exe (PID: 3052)
- RobloxPlayerLauncher.exe (PID: 2764)
- RobloxPlayerLauncher.exe (PID: 2144)
- RobloxPlayerBeta.exe (PID: 2612)
Reads the date of Windows installation
- chrome.exe (PID: 3504)
Checks Windows Trust Settings
- chrome.exe (PID: 3148)
- RobloxPlayerLauncher.exe (PID: 4092)
- RobloxPlayerLauncher.exe (PID: 3052)
- RobloxPlayerLauncher.exe (PID: 2764)
- RobloxPlayerBeta.exe (PID: 2612)
- RobloxPlayerLauncher.exe (PID: 2144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
43
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,6706211434926402982,16419567849472596200,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1052,6706211434926402982,16419567849472596200,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3080 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,6706211434926402982,16419567849472596200,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,6706211434926402982,16419567849472596200,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1136 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,6706211434926402982,16419567849472596200,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3104 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,6706211434926402982,16419567849472596200,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2056 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,6706211434926402982,16419567849472596200,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=996 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1052,6706211434926402982,16419567849472596200,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2760 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,6706211434926402982,16419567849472596200,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1820 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e7ed988,0x6e7ed998,0x6e7ed9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
38 995
Read events
38 567
Write events
418
Delete events
10
Modification events
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3148) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
8
Suspicious files
125
Text files
230
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61D49D13-C4C.pma | — | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f108cc58-22b0-4897-afa6-2951428001c2.tmp | text | |
MD5:— | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1844 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF112ce9.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\07e8d474-07bf-4346-924c-759f0c77c2a9.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF112eed.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 3148 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
74
TCP/UDP connections
142
DNS requests
127
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 200 | 74.125.108.201:80 | http://r4---sn-1gi7znek.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.45.13&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1641323556&mv=m&mvi=4&pl=24&rmhost=r3---sn-1gi7znek.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 576 b | whitelisted |
860 | svchost.exe | GET | 206 | 74.125.108.201:80 | http://r4---sn-1gi7znek.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.45.13&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1641323556&mv=m&mvi=4&pl=24&rmhost=r3---sn-1gi7znek.gvt1.com&shardbypass=yes | US | binary | 9.49 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 74.125.108.201:80 | http://r4---sn-1gi7znek.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.45.13&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1641323556&mv=m&mvi=4&pl=24&rmhost=r3---sn-1gi7znek.gvt1.com&shardbypass=yes | US | binary | 9.48 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 74.125.108.201:80 | http://r4---sn-1gi7znek.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.45.13&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1641323556&mv=m&mvi=4&pl=24&rmhost=r3---sn-1gi7znek.gvt1.com&shardbypass=yes | US | binary | 20.7 Kb | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 576 b | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 576 b | whitelisted |
860 | svchost.exe | GET | 206 | 74.125.108.201:80 | http://r4---sn-1gi7znek.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=85.203.45.13&mm=28&mn=sn-1gi7znek&ms=nvh&mt=1641323556&mv=m&mvi=4&pl=24&rmhost=r3---sn-1gi7znek.gvt1.com&shardbypass=yes | US | binary | 5.63 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
860 | svchost.exe | 74.125.108.201:80 | r4---sn-1gi7znek.gvt1.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 142.250.185.173:443 | accounts.google.com | Google Inc. | US | suspicious |
4072 | chrome.exe | 142.250.186.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 142.250.184.232:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
4072 | chrome.exe | 178.79.242.211:443 | css.rbxcdn.com | Limelight Networks, Inc. | DE | suspicious |
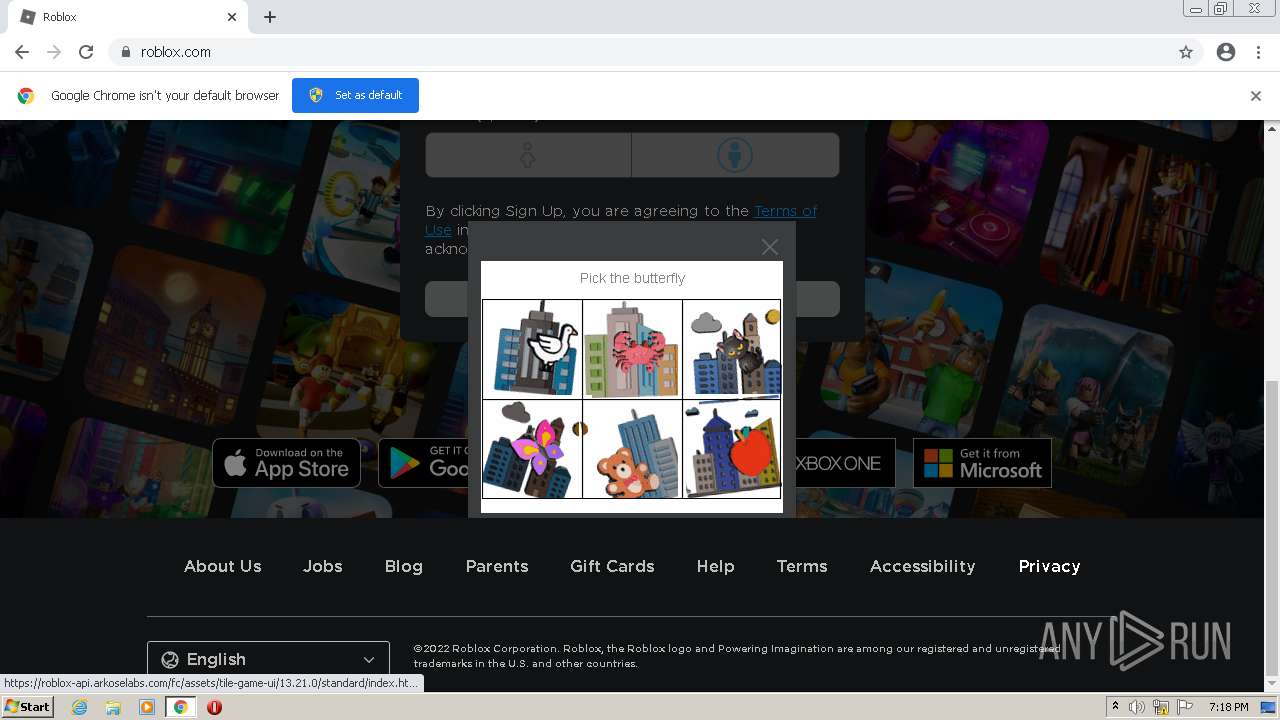
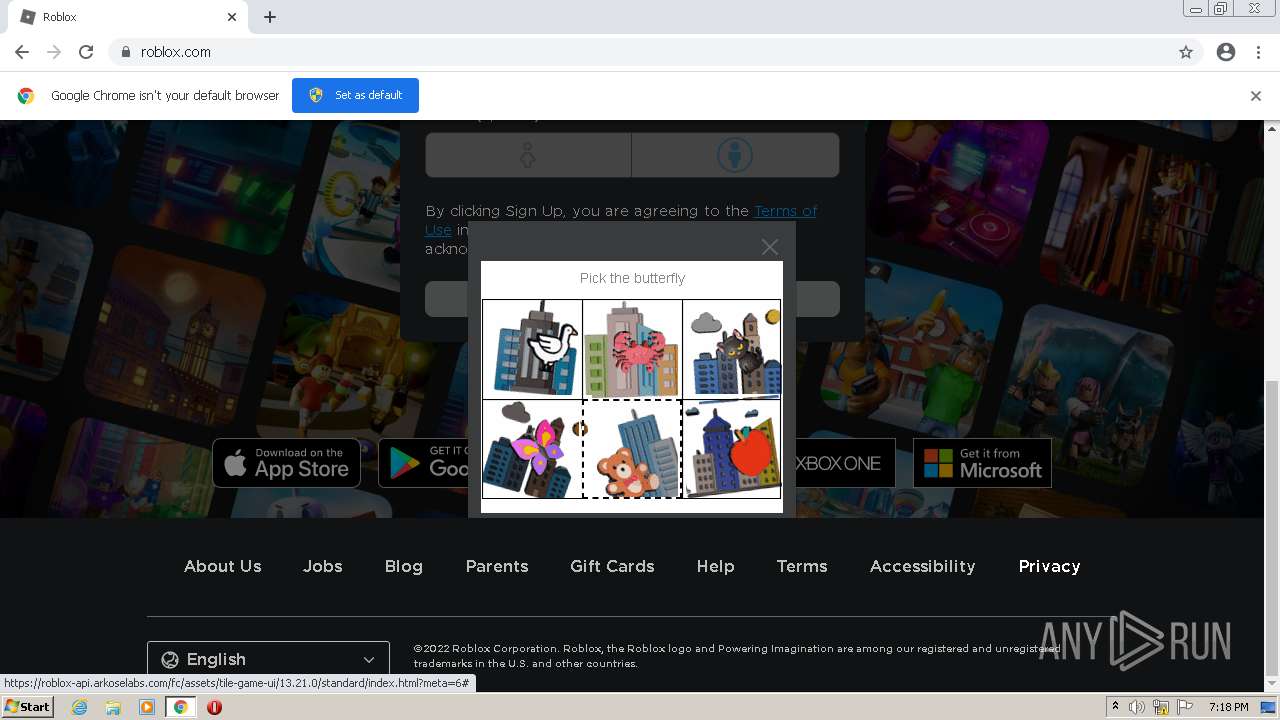
4072 | chrome.exe | 104.18.24.64:443 | roblox-api.arkoselabs.com | Cloudflare Inc | US | suspicious |
4072 | chrome.exe | 178.79.242.48:443 | static.rbxcdn.com | Limelight Networks, Inc. | DE | suspicious |
4072 | chrome.exe | 172.217.18.98:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 142.250.185.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
4072 | chrome.exe | 92.123.194.185:443 | apis.rbxcdn.com | Akamai International B.V. | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.roblox.com |
| whitelisted |
css.rbxcdn.com |
| whitelisted |
static.rbxcdn.com |
| whitelisted |
js.rbxcdn.com |
| whitelisted |
roblox-api.arkoselabs.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
metrics.roblox.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |
Threats
Process | Message |
|---|---|
RobloxPlayerBeta.exe | 2022-01-04T19:21:10.022Z,0.022532,0aa8,6 [FLog::Output] RobloxGitHash: 8e0cd738ec77b371e64e597e21ec55920dcbea1f |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 2022-01-04T19:21:10.025Z,0.025532,0aa8,6 [FLog::Output] The channel is production |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 2022-01-04T19:21:10.103Z,0.103016,0aa8,6 [FLog::Error] Test log: Map check complete and successful! |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 2022-01-04T19:21:10.103Z,0.103016,0aa8,6 [FLog::Error] Dynamic initializer test result: SUCCESS |
RobloxPlayerBeta.exe | |
RobloxPlayerBeta.exe | 2022-01-04T19:21:10.103Z,0.103016,0aa8,6 [FLog::Output] TaskSchedulerMk2::applyAsyncTaskThreadCount( 3 ) <req: 0 active: 0> |
RobloxPlayerBeta.exe | |