| download: | setup.exe |
| Full analysis: | https://app.any.run/tasks/0b5e8b50-0eb4-4ed3-a435-e058e8b67ea3 |
| Verdict: | Malicious activity |
| Analysis date: | April 13, 2020, 22:15:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E96DD956BC2159FF1D073876EF5D4E58 |
| SHA1: | A0DA0D7C8394D646EB5A0F64BE14397235F22704 |
| SHA256: | 14636B7FC900E2BE3FEE5ABB409E3B7A3CDF5A99107BF6D7DCBCCE4B26EE0D34 |
| SSDEEP: | 196608:Mem6/gb2N3s9m35DylYLan8CmD5zpX9o38vR/dnG0sb9iMly9ssSGz8EQgCPhtv:MelYyVYm3RLaQ5zpNq8NdnExiMw+P4QD |
MALICIOUS
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2252)
- regsvr32.exe (PID: 3340)
- regsvr32.exe (PID: 3452)
- net_updater32.exe (PID: 2844)
- net_updater32.exe (PID: 2764)
- EGMonitor.exe (PID: 1880)
- EGMonitor.exe (PID: 2952)
- Opera.exe (PID: 1840)
- rundll32.exe (PID: 4048)
- net_updater32.exe (PID: 2740)
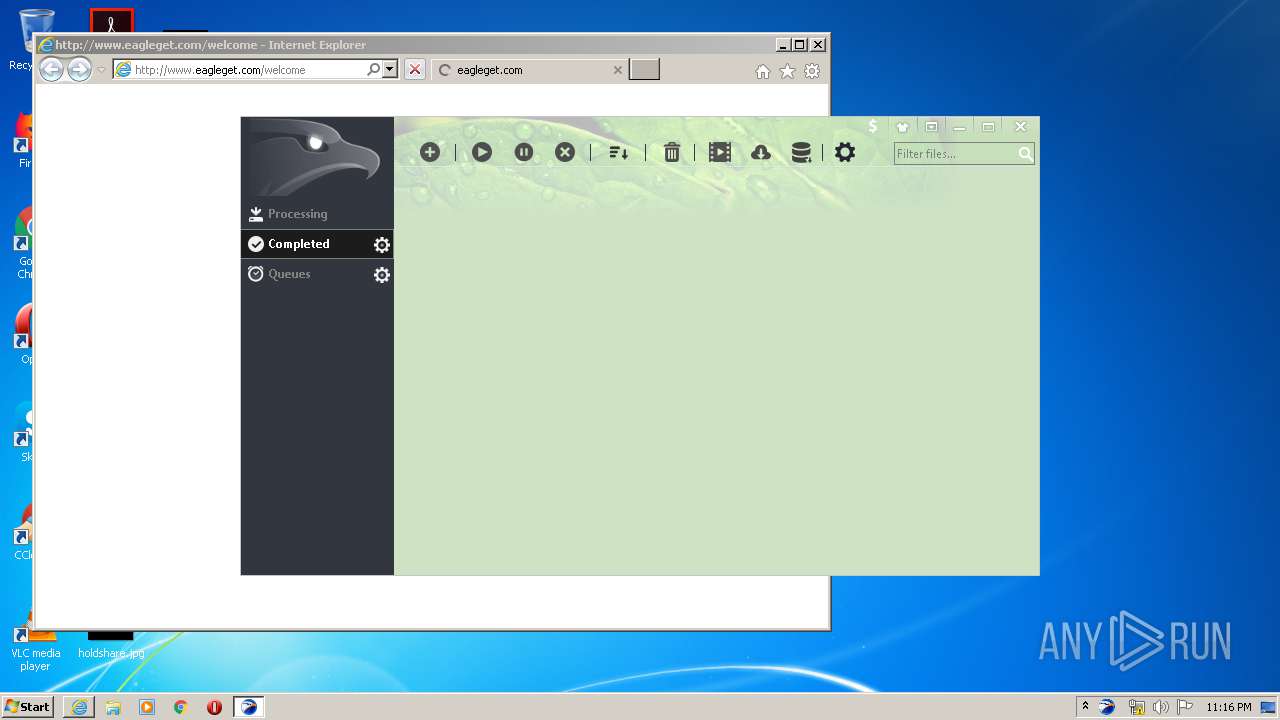
- EagleGet.exe (PID: 2276)
- iexplore.exe (PID: 3128)
- EGMonitor.exe (PID: 2864)
- EGMonitor.exe (PID: 2660)
- EGMonitor.exe (PID: 2720)
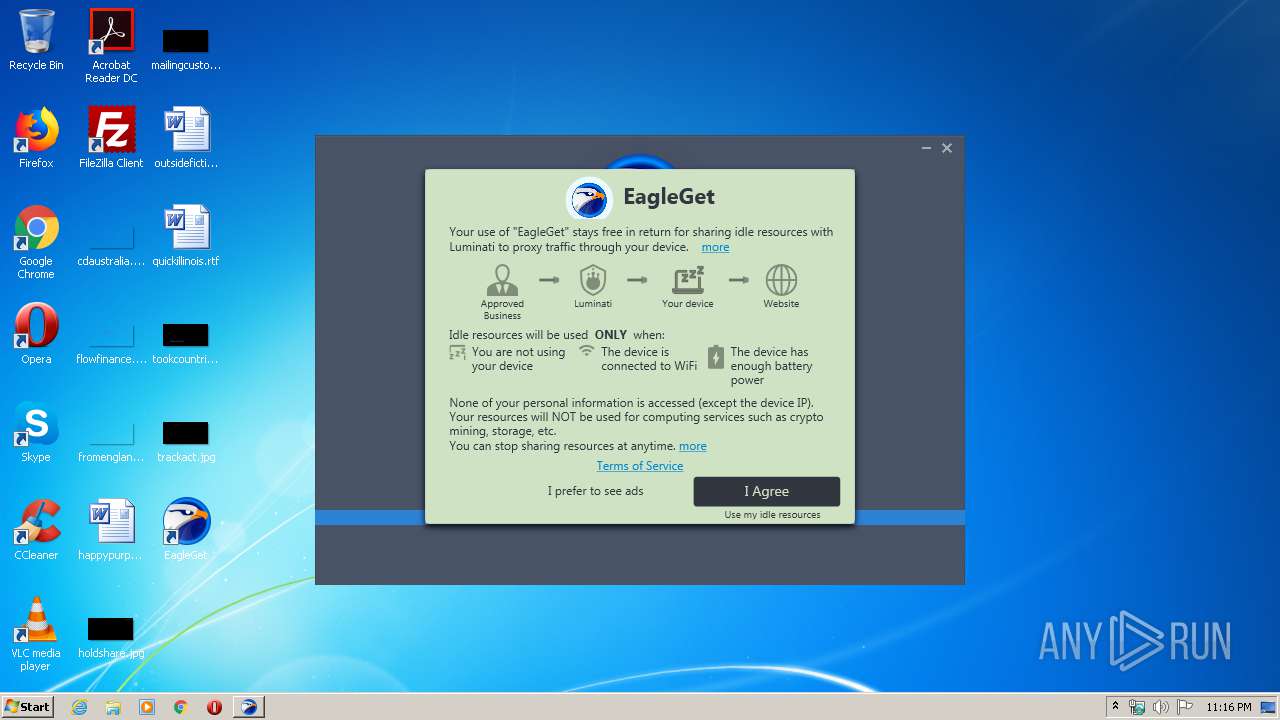
Actions looks like stealing of personal data
- setup.tmp (PID: 1252)
Registers / Runs the DLL via REGSVR32.EXE
- setup.tmp (PID: 1252)
Application was dropped or rewritten from another process
- test_wpf.exe (PID: 1492)
- net_updater32.exe (PID: 2764)
- EGMonitor.exe (PID: 1880)
- EGMonitor.exe (PID: 2952)
- EGMonitor.exe (PID: 2720)
- net_updater32.exe (PID: 2740)
- test_wpf.exe (PID: 3584)
- EagleGet.exe (PID: 2276)
- test_wpf.exe (PID: 3040)
- EGMonitor.exe (PID: 2864)
- EGMonitor.exe (PID: 2660)
- net_updater32.exe (PID: 2844)
Changes settings of System certificates
- net_updater32.exe (PID: 2764)
SUSPICIOUS
Reads Windows owner or organization settings
- setup.tmp (PID: 1252)
Reads the Windows organization settings
- setup.tmp (PID: 1252)
Uses TASKKILL.EXE to kill process
- setup.tmp (PID: 1252)
Creates files in the user directory
- setup.tmp (PID: 1252)
- EagleGet.exe (PID: 2276)
Executable content was dropped or overwritten
- setup.tmp (PID: 1252)
- setup.exe (PID: 3052)
- setup.exe (PID: 2140)
- net_updater32.exe (PID: 2764)
- EGMonitor.exe (PID: 1880)
- EGMonitor.exe (PID: 2720)
- net_updater32.exe (PID: 2740)
Creates COM task schedule object
- regsvr32.exe (PID: 3452)
- regsvr32.exe (PID: 2252)
- regsvr32.exe (PID: 3340)
Reads Environment values
- net_updater32.exe (PID: 2764)
- net_updater32.exe (PID: 2740)
Creates files in the program directory
- net_updater32.exe (PID: 2844)
- net_updater32.exe (PID: 2764)
- EagleGet.exe (PID: 2276)
- net_updater32.exe (PID: 2740)
Application launched itself
- net_updater32.exe (PID: 2764)
- EGMonitor.exe (PID: 1880)
Reads Internet Cache Settings
- net_updater32.exe (PID: 2764)
Executed as Windows Service
- EGMonitor.exe (PID: 1880)
- net_updater32.exe (PID: 2740)
Creates files in the driver directory
- EGMonitor.exe (PID: 1880)
Creates files in the Windows directory
- EGMonitor.exe (PID: 1880)
- net_updater32.exe (PID: 2740)
Creates or modifies windows services
- EGMonitor.exe (PID: 1880)
Uses RUNDLL32.EXE to load library
- setup.tmp (PID: 1252)
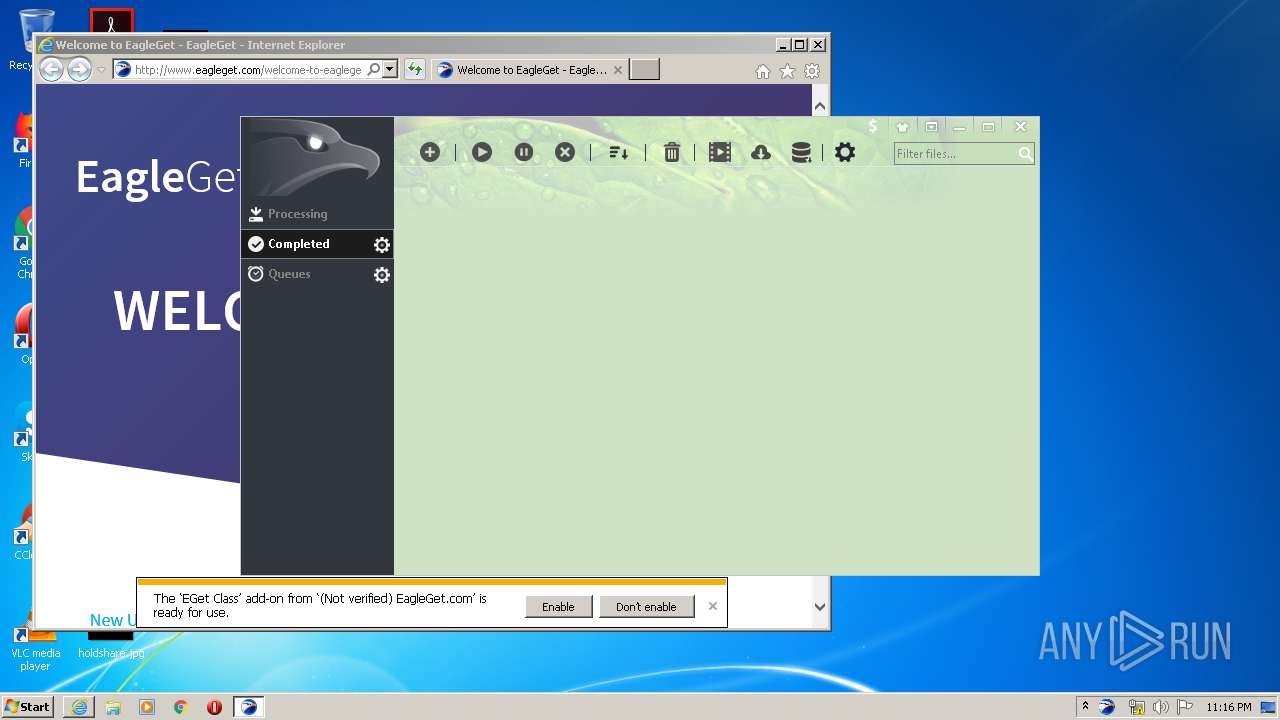
Starts Internet Explorer
- setup.tmp (PID: 1252)
Adds / modifies Windows certificates
- net_updater32.exe (PID: 2764)
INFO
Application was dropped or rewritten from another process
- setup.tmp (PID: 3788)
- setup.tmp (PID: 1252)
Loads dropped or rewritten executable
- setup.tmp (PID: 1252)
Creates a software uninstall entry
- setup.tmp (PID: 1252)
Creates files in the program directory
- setup.tmp (PID: 1252)
Reads settings of System Certificates
- net_updater32.exe (PID: 2764)
- iexplore.exe (PID: 1016)
Dropped object may contain Bitcoin addresses
- net_updater32.exe (PID: 2764)
Creates files in the user directory
- Opera.exe (PID: 1840)
- iexplore.exe (PID: 1016)
Application launched itself
- iexplore.exe (PID: 3128)
Reads Internet Cache Settings
- iexplore.exe (PID: 3128)
- iexplore.exe (PID: 1016)
Changes internet zones settings
- iexplore.exe (PID: 3128)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1016)
Changes settings of System certificates
- iexplore.exe (PID: 1016)
Reads internet explorer settings
- iexplore.exe (PID: 1016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:08 14:51:37+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 69120 |
| InitializedDataSize: | 104960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117e4 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.6.50 |
| ProductVersionNumber: | 2.1.6.50 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | ASCII |
| Comments: | 此安装程序由 Inno Setup 构建。 |
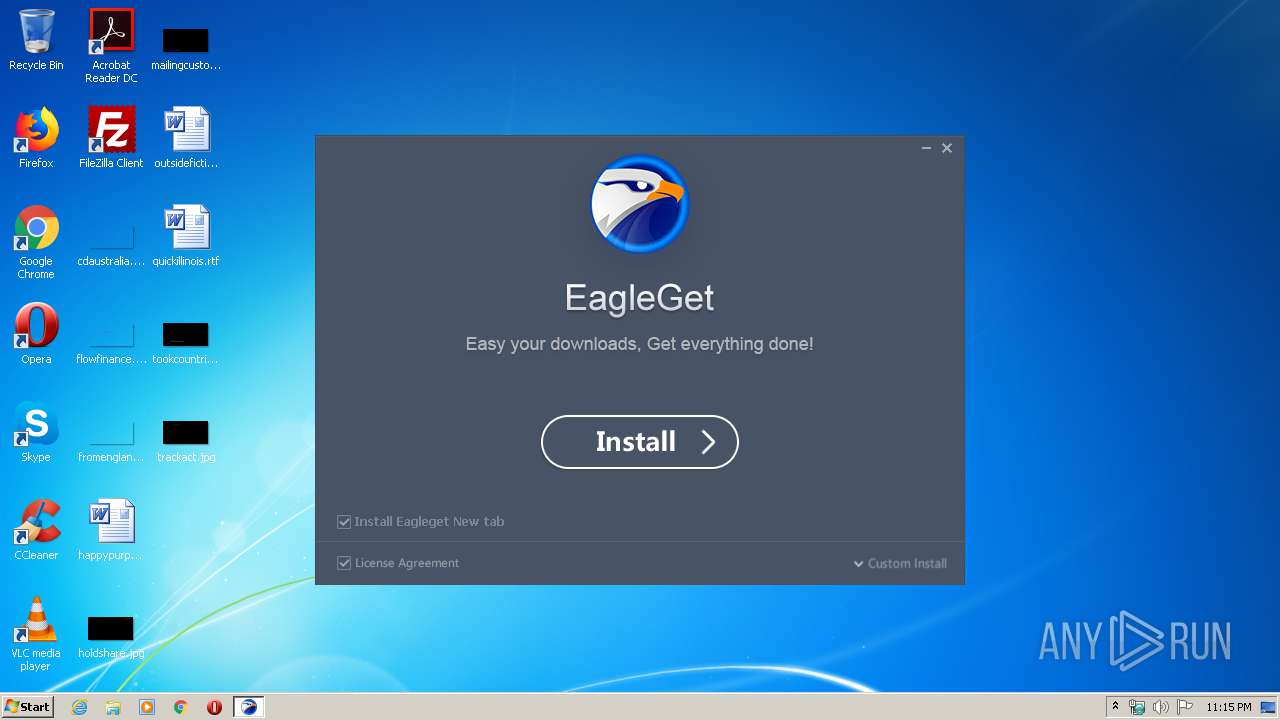
| CompanyName: | EagleGet |
| FileDescription: | EagleGet Setup |
| FileVersion: | 2.1.6.50 |
| LegalCopyright: | |
| ProductName: | EagleGet |
| ProductVersion: | 2.1.6.50 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Apr-2016 12:51:37 |
| Detected languages: |
|
| Comments: | 此安装程序由 Inno Setup 构建。 |
| CompanyName: | EagleGet |
| FileDescription: | EagleGet Setup |
| FileVersion: | 2.1.6.50 |
| LegalCopyright: | - |
| ProductName: | EagleGet |
| ProductVersion: | 2.1.6.50 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 08-Apr-2016 12:51:37 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000FD10 | 0x0000FE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.38464 |
.itext | 0x00011000 | 0x00000F6C | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.74547 |
.data | 0x00012000 | 0x00000CB4 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.35781 |
.bss | 0x00013000 | 0x000056C0 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.reloc | 0x0001C000 | 0x0000137C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0 |
.rsrc | 0x0001E000 | 0x00017988 | 0x00017A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.50148 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08452 | 1444 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 5.68272 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 5.71503 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 5.90552 | 2440 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 5.84275 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
68
Monitored processes
24
Malicious processes
12
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1016 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3128 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1252 | "C:\Users\admin\AppData\Local\Temp\is-6DMNO.tmp\setup.tmp" /SL5="$A0204,9993427,175104,C:\Users\admin\AppData\Local\Temp\setup.exe" /SPAWNWND=$701CA /NOTIFYWND=$C0202 | C:\Users\admin\AppData\Local\Temp\is-6DMNO.tmp\setup.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 安装/卸载 Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1492 | C:\Program Files\EagleGet\test_wpf.exe | C:\Program Files\EagleGet\test_wpf.exe | — | net_updater32.exe | |||||||||||
User: admin Company: Luminati Networks Ltd. Integrity Level: HIGH Description: test_wpf Exit code: 0 Version: 1.172.289 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Opera\Opera.exe" "C:\Program Files\EagleGet\addon\eagleget_cext@eagleget.com.crx" | C:\Program Files\Opera\Opera.exe | setup.tmp | ||||||||||||
User: admin Company: Opera Software Integrity Level: HIGH Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 1880 | "C:\Program Files\EagleGet\EGMonitor.exe" /svc | C:\Program Files\EagleGet\EGMonitor.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: EGMonitor Exit code: 4294967286 Version: 2, 0, 3, 6 Modules
| |||||||||||||||
| 2140 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Company: EagleGet Integrity Level: MEDIUM Description: EagleGet Setup Exit code: 0 Version: 2.1.6.50 Modules
| |||||||||||||||
| 2252 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\EagleGet\eagleSniffer.dll" | C:\Windows\system32\regsvr32.exe | — | setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2276 | "C:\Program Files\EagleGet\EagleGet.exe" | C:\Program Files\EagleGet\EagleGet.exe | setup.tmp | ||||||||||||
User: admin Company: EagleGet.com Integrity Level: HIGH Description: EagleGet Free Downloader Exit code: 0 Version: 2.1.6.50 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\EagleGet\EGMonitor.exe" /installnewtab | C:\Program Files\EagleGet\EGMonitor.exe | — | setup.tmp | |||||||||||
User: admin Integrity Level: HIGH Description: EGMonitor Exit code: 0 Version: 2, 0, 3, 6 Modules
| |||||||||||||||
| 2720 | "C:\Program Files\EagleGet\EGMonitor.exe" /install | C:\Program Files\EagleGet\EGMonitor.exe | setup.tmp | ||||||||||||
User: admin Integrity Level: HIGH Description: EGMonitor Exit code: 0 Version: 2, 0, 3, 6 Modules
| |||||||||||||||
Total events
3 478
Read events
1 853
Write events
1 615
Delete events
10
Modification events
| (PID) Process: | (1252) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: E40400003664C714E111D601 | |||
| (PID) Process: | (1252) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 1D336523094D24CD937F8315E1C212E7E2F47AFF2DC4E3C887375D209A70168E | |||
| (PID) Process: | (1252) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1252) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | delete value | Name: | Enable Browser Extensions |
Value: yes | |||
| (PID) Process: | (1252) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | Enable Browser Extensions |
Value: ye뼀栣Ą | |||
| (PID) Process: | (1252) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Mozilla\NativeMessagingHosts\eagleget |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp\is-BP9P5.tmp\firefox.json | |||
| (PID) Process: | (1252) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Mozilla\NativeMessagingHosts\eagleget |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp\is-BP9P5.tmp\firefox.json | |||
| (PID) Process: | (1252) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Mozilla\Mozilla Firefox 68.0.1\extensions |
| Operation: | write | Name: | eagleget_ffext@eagleget.com |
Value: C:\Users\admin\AppData\Local\Temp\is-BP9P5.tmp\addon\eagleget_ffext@eagleget.com.xpi | |||
| (PID) Process: | (1252) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\EagleGet\CallbackCtrl.dll | |||
| (PID) Process: | (1252) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 5F8C230472066AFB2ACC12ED926711060B68270FEA84129F539D755A78D76E50 | |||
Executable files
45
Suspicious files
62
Text files
148
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-7A0RJ.tmp\setup.tmp | executable | |
MD5:EB42E5720E09CD014694A22C86929F5E | SHA256:4DC2D414277E497490D2009F370051298BCCAA649D0A335B064269A0BB9BBBF3 | |||
| 1252 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-BP9P5.tmp\util.dll | executable | |
MD5:192C98CB51F39BE053AD5C7E029E75F8 | SHA256:A2EF6B8FBF44BC77631D5635B8ABEDF90DB5903B94618753168F5A904EBC5F60 | |||
| 3052 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-6DMNO.tmp\setup.tmp | executable | |
MD5:EB42E5720E09CD014694A22C86929F5E | SHA256:4DC2D414277E497490D2009F370051298BCCAA649D0A335B064269A0BB9BBBF3 | |||
| 1252 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-BP9P5.tmp\btn_n.png | image | |
MD5:66DEFF37283BCA24EA963AE3A3963B38 | SHA256:D9F0859F6A5648B0A9060200CC9A7534161E1B22844F631766E4E3540090790A | |||
| 1252 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-BP9P5.tmp\loading.png | image | |
MD5:589AC6FFE91A177AFF97DABE25689011 | SHA256:2313BD947E407CCEE25C6BCBA3C7D45F5C92159950D9D1277D258A293760A732 | |||
| 1252 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-BP9P5.tmp\btn_browser.png | image | |
MD5:8DD4F9F2C22073544694ECA39C4F305D | SHA256:0F6E9827EF681B88722D2013AE44FE5F8EEEAF22B6FE64904ECD0852DE8197C8 | |||
| 1252 | setup.tmp | C:\Users\admin\AppData\Roaming\EagleGet\configs\data.db-journal | — | |
MD5:— | SHA256:— | |||
| 1252 | setup.tmp | C:\Program Files\EagleGet\is-7UR3L.tmp | — | |
MD5:— | SHA256:— | |||
| 1252 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-BP9P5.tmp\xy.png | image | |
MD5:E92F3FBF3876C4044722FD975281B3FF | SHA256:31137AD0EF19381E1778EB89B6CB9F70A9EE5244AD943AD494E1E57B18B48AB7 | |||
| 1252 | setup.tmp | C:\Program Files\EagleGet\is-Q1UOH.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
97
DNS requests
27
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1016 | iexplore.exe | GET | 301 | 104.28.1.36:80 | http://www.eagleget.com/welcome | US | — | — | malicious |
1016 | iexplore.exe | GET | 200 | 104.28.1.36:80 | http://www.eagleget.com/wp-content/themes/one-page-express/customizer/kirki/assets/css/kirki-styles.css | US | — | — | malicious |
2764 | net_updater32.exe | GET | 200 | 104.28.1.36:80 | http://admin.eagleget.com/latest/EagleGet-Icon.png | US | image | 35.4 Kb | malicious |
2276 | EagleGet.exe | GET | 200 | 104.28.1.36:80 | http://admin.eagleget.com/update/autoup.php?version=2.1.6.50 | US | text | 18 b | malicious |
1840 | Opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 564 b | whitelisted |
1252 | setup.tmp | POST | 200 | 104.28.1.36:80 | http://admin.eagleget.com/analytics/lg.php? | US | — | — | malicious |
2276 | EagleGet.exe | GET | 200 | 167.114.35.160:80 | http://dl.eagleget.com/report/check.php?md5= | CA | text | 141 b | malicious |
2276 | EagleGet.exe | GET | 200 | 104.28.1.36:80 | http://admin.eagleget.com/update/filehosting.php?md5=643ad317ba9d4a015b89087d701bafac | US | text | 831 b | malicious |
1016 | iexplore.exe | GET | 200 | 212.124.124.178:80 | http://www.1-1ads.com/js/show_ads_supp.js?pubId=1105 | US | compressed | 9.17 Kb | whitelisted |
1016 | iexplore.exe | GET | 200 | 212.124.124.178:80 | http://www.1-1ads.com/js/show_ads_supp.js?pubId=3004 | US | compressed | 9.17 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2764 | net_updater32.exe | 34.206.78.88:443 | perr.lum-sdk.io | Amazon.com, Inc. | US | suspicious |
2764 | net_updater32.exe | 23.21.154.58:443 | perr.lum-sdk.io | Amazon.com, Inc. | US | suspicious |
2764 | net_updater32.exe | 138.68.222.242:80 | 138-68-222-242.l-cdn.com | Digital Ocean, Inc. | US | unknown |
2764 | net_updater32.exe | 104.28.1.36:80 | admin.eagleget.com | Cloudflare Inc | US | shared |
2844 | net_updater32.exe | 162.125.66.1:443 | www.dropbox.com | Dropbox, Inc. | DE | shared |
2764 | net_updater32.exe | 68.183.153.117:80 | 68-183-153-117.l-cdn.com | DSL Extreme | US | unknown |
2844 | net_updater32.exe | 162.125.66.6:443 | ucb2e8fcf774f4e8904d450befd7.dl.dropboxusercontent.com | Dropbox, Inc. | DE | shared |
2844 | net_updater32.exe | 23.21.154.58:443 | perr.lum-sdk.io | Amazon.com, Inc. | US | suspicious |
2844 | net_updater32.exe | 34.206.78.88:443 | perr.lum-sdk.io | Amazon.com, Inc. | US | suspicious |
2844 | net_updater32.exe | 104.248.53.74:80 | 104-248-53-74.l-cdn.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dropbox.com |
| shared |
perr.lum-sdk.io |
| suspicious |
perr.l-err.biz |
| suspicious |
perr.l-agent.me |
| suspicious |
138-68-222-242.l-cdn.com |
| unknown |
admin.eagleget.com |
| malicious |
68-183-153-117.l-cdn.com |
| unknown |
ucb2e8fcf774f4e8904d450befd7.dl.dropboxusercontent.com |
| suspicious |
104-248-53-74.l-cdn.com |
| unknown |
certs.opera.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2764 | net_updater32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2764 | net_updater32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2764 | net_updater32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2844 | net_updater32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2844 | net_updater32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2844 | net_updater32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2740 | net_updater32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2740 | net_updater32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2740 | net_updater32.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |