| File name: | 2.ps1 |
| Full analysis: | https://app.any.run/tasks/1c8c6e68-cb07-4dde-bf93-bc32ea0040dc |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 08:34:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (645), with CRLF line terminators |
| MD5: | A2EC6857B9B92362EE18F1D9166DCE54 |
| SHA1: | EA7753ACC712661E385FA1007CC12C1569140927 |
| SHA256: | 144FBE9CE7785E9604107C0F9B05505EEAAA306394DEF0CEA214954BBCD99BE0 |
| SSDEEP: | 24:K8y6cJtNUcPB7CAV7pN0t2DNtJUzlVwr897XJz2azZFHs3akw:U6cx3Z77V7pG2b6ZhXzxZFHGe |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6972)
- powershell.exe (PID: 4976)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 6972)
Run PowerShell with an invisible window
- powershell.exe (PID: 4976)
Create files in the Startup directory
- powershell.exe (PID: 6972)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 6972)
SUSPICIOUS
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 6972)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 6972)
Connects to the server without a host name
- powershell.exe (PID: 6972)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6972)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 6972)
Application launched itself
- powershell.exe (PID: 6972)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 6972)
Reverses array data (POWERSHELL)
- powershell.exe (PID: 6972)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 6972)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 6972)
The process hide an interactive prompt from the user
- powershell.exe (PID: 6972)
INFO
Disables trace logs
- powershell.exe (PID: 6972)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 6972)
Checks proxy server information
- powershell.exe (PID: 6972)
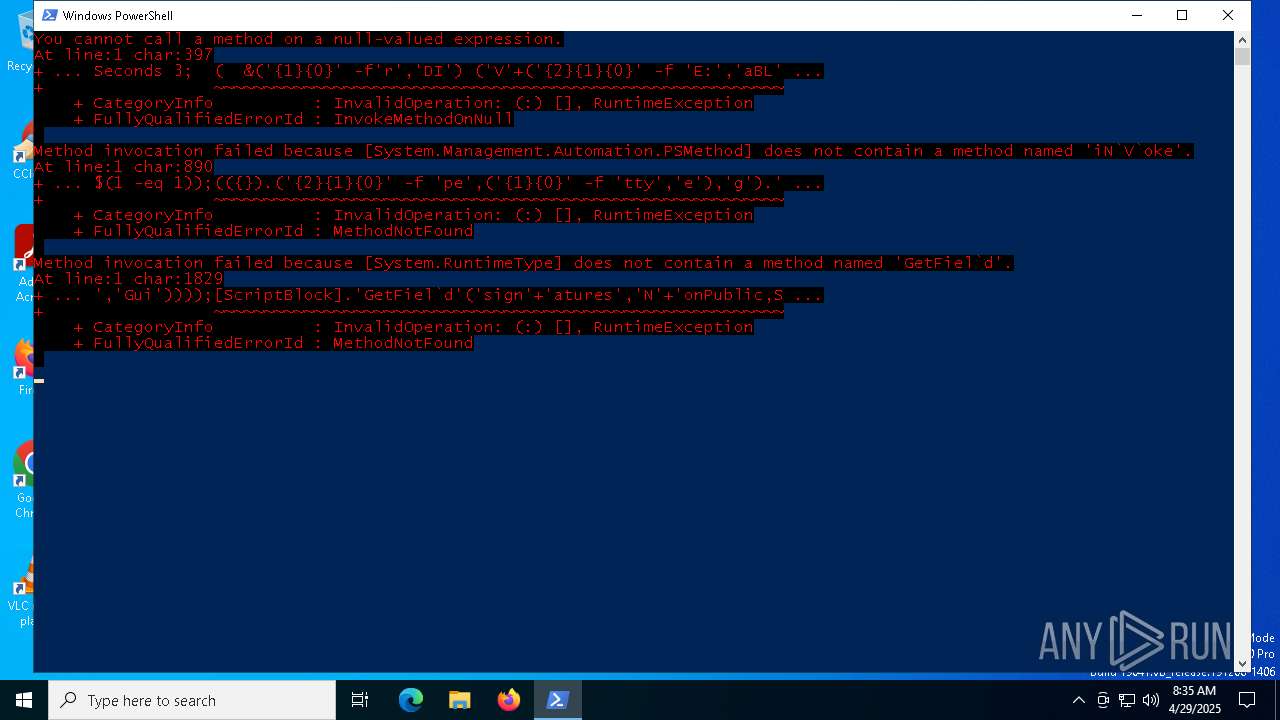
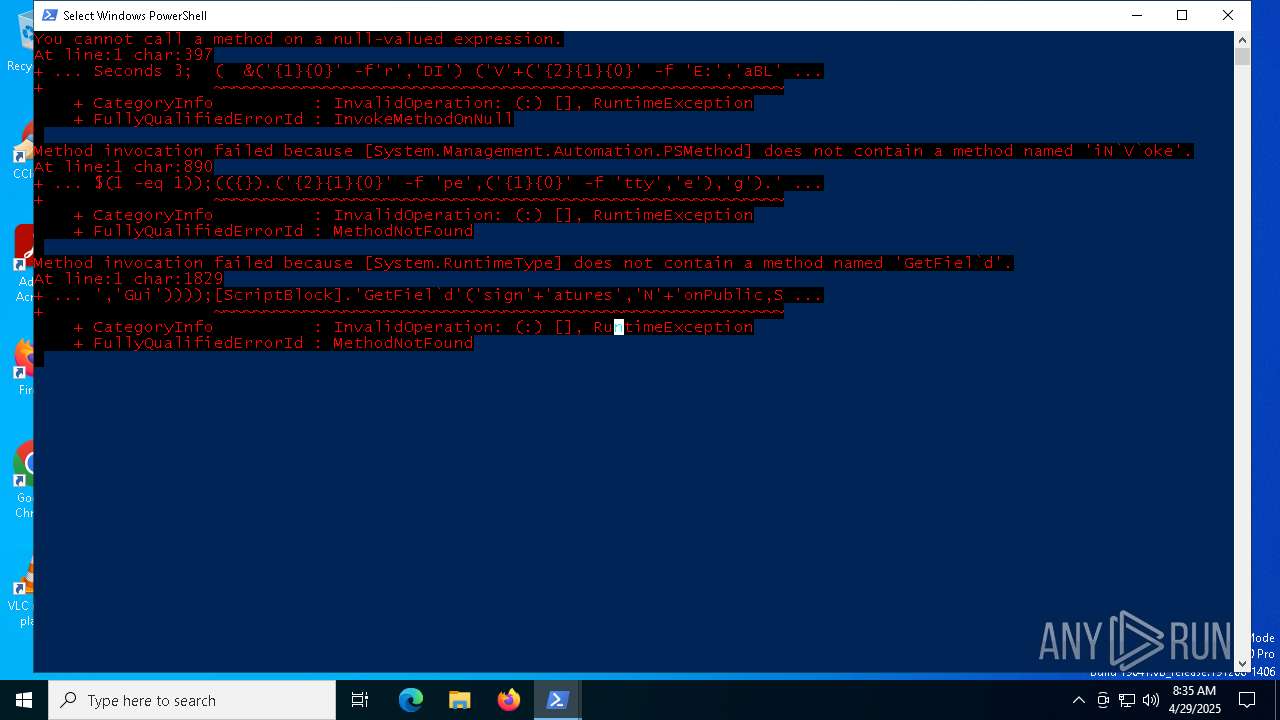
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6972)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 6972)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6972)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 6972)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 6972)
Auto-launch of the file from Startup directory
- powershell.exe (PID: 6972)
Reads the software policy settings
- slui.exe (PID: 6744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
135
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4976 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle hidden -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command Add-Type -AssemblyName System.Windows.Forms;[System.Windows.Forms.MessageBox]::Show('Beim Öffnen dieses Dokuments ist ein Fehler aufgetreten ! Bitte aktualisieren Sie Ihre Version.', 'Adobe PDF Reader Fehlercode: cx91293', [System.Windows.Forms.MessageBoxButtons]::OK, [System.Windows.Forms.MessageBoxIcon]::Exclamation);Exit | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6068 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6744 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6972 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\2.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 055
Read events
11 055
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
7
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4976 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TLF7F18V6O2AYHA0H6RB.temp | binary | |
MD5:5315F04B61DE249336762CB929DF1DF4 | SHA256:8396EDFF2F60405E3BC2A59EE8A5C5170955047EC8FAB29044685100BB13D34E | |||
| 6972 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10b4ea.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6972 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Windows.lnk | binary | |
MD5:F61700B47C8D4C96FA058C12AFDB7B9C | SHA256:34719D524DBD94AEF908ECFB6D6D4272316C6172A215C1E0240AD066FDEAD972 | |||
| 6972 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5otvlkai.ujr.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6972 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_qr3pi1mv.d2t.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6972 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:61507F791928EB3157F3058343F73BDF | SHA256:9456945DFBF266911567941DF4C3433ED95A133B2EFBC5413E3BA0BE2F2970F8 | |||
| 6972 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BNC1OEWM2S2MJ9VDI9LM.temp | binary | |
MD5:61507F791928EB3157F3058343F73BDF | SHA256:9456945DFBF266911567941DF4C3433ED95A133B2EFBC5413E3BA0BE2F2970F8 | |||
| 4976 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yqfmr5lx.1il.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4976 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1107ae.TMP | binary | |
MD5:61507F791928EB3157F3058343F73BDF | SHA256:9456945DFBF266911567941DF4C3433ED95A133B2EFBC5413E3BA0BE2F2970F8 | |||
| 4976 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sbwayrsi.qkn.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
24
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6972 | powershell.exe | GET | 200 | 45.15.162.16:80 | http://45.15.162.16/octopus.txt | unknown | — | — | unknown |
5384 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5384 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.32.238.112:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
pastebin.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |