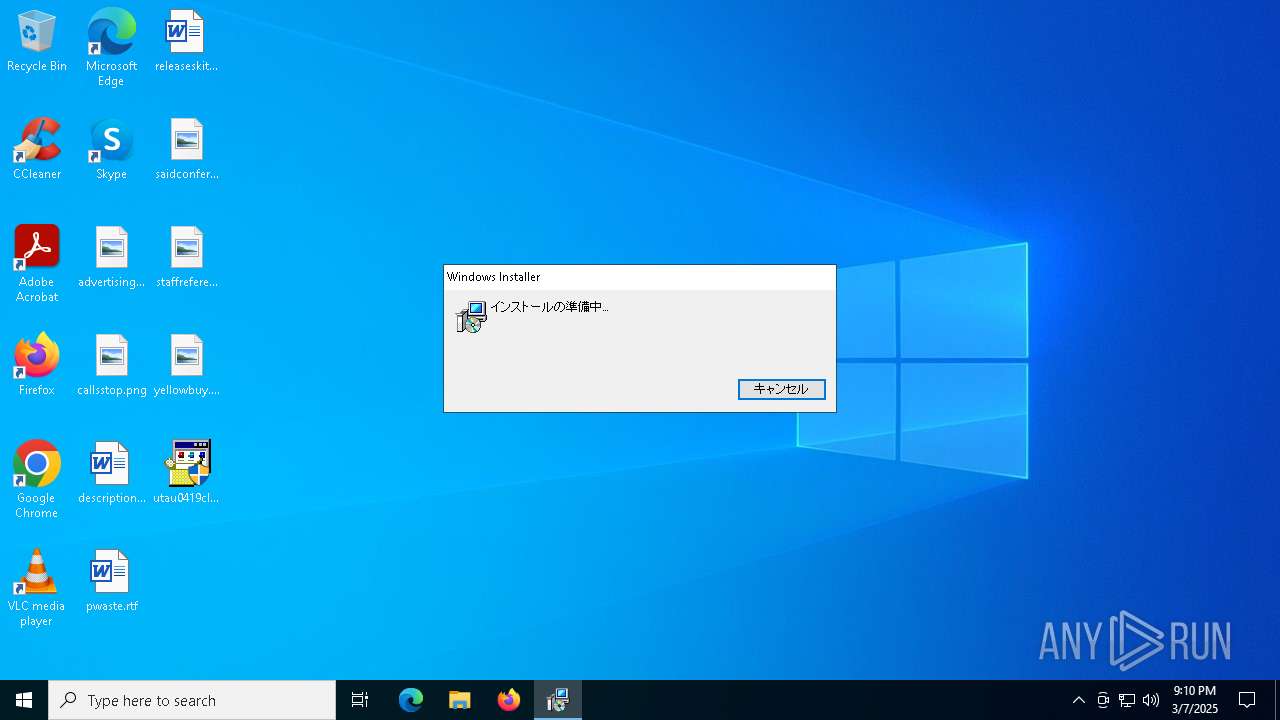
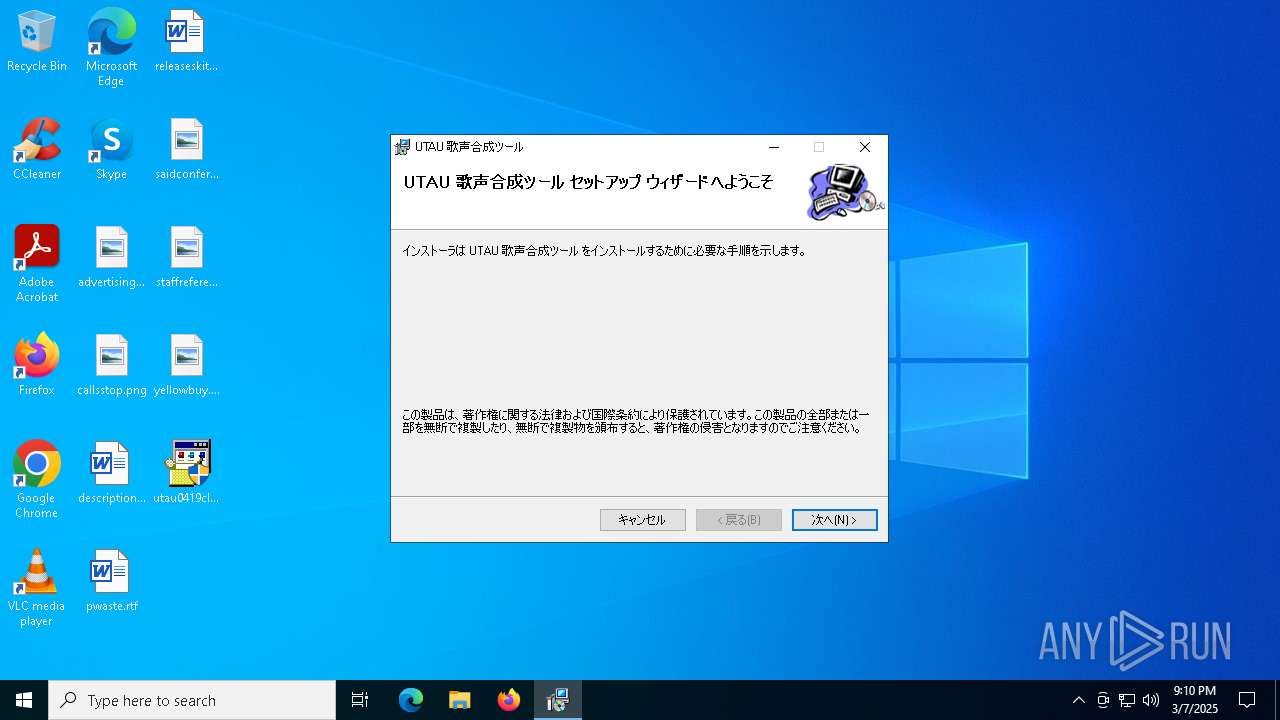
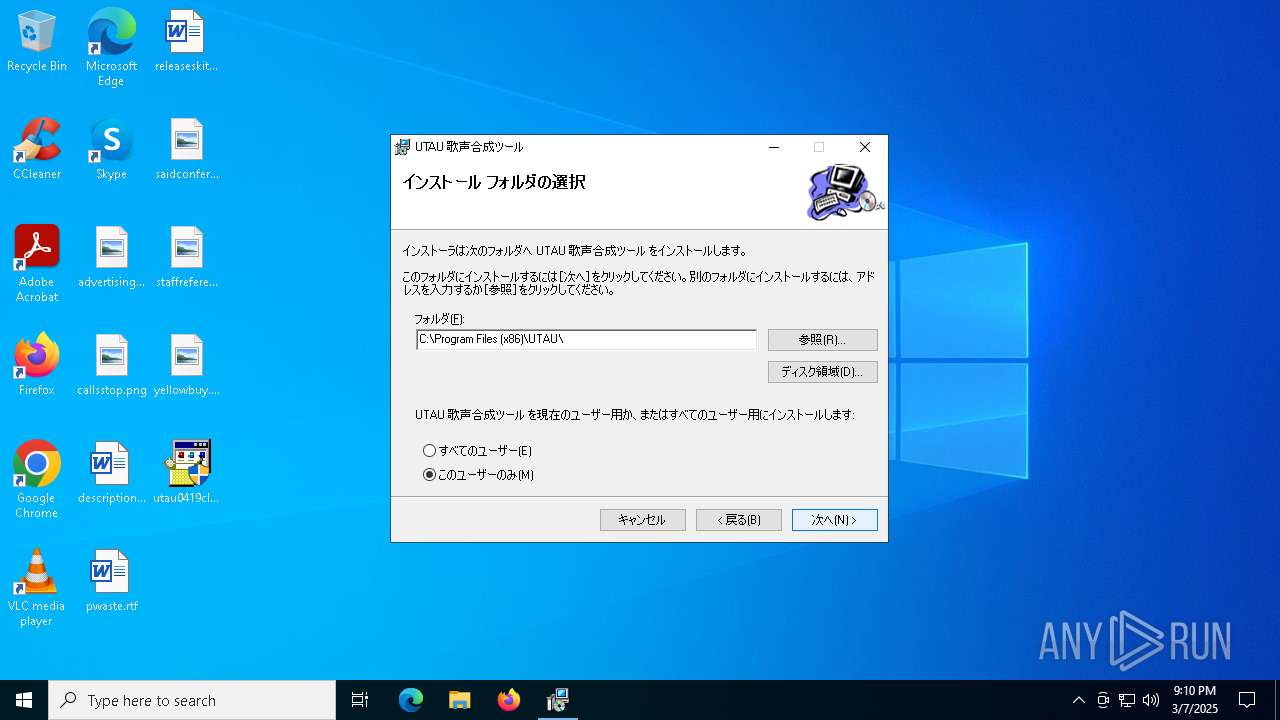
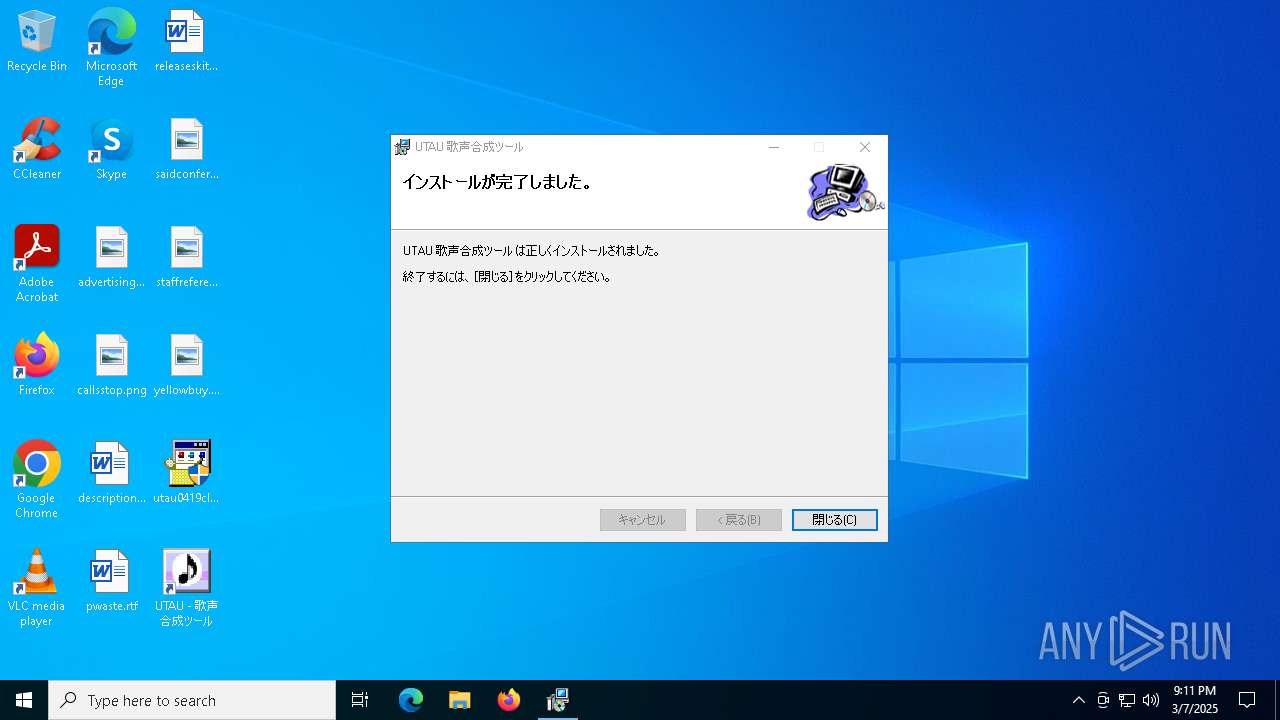
| File name: | utau0419cInstaller.exe |
| Full analysis: | https://app.any.run/tasks/9f567c2a-ef73-4a31-8d1c-3974b326350a |
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2025, 21:10:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, MS CAB-Installer self-extracting archive, 3 sections |
| MD5: | B3FBD653A84017E567D7CFC7C9D14456 |
| SHA1: | A39E627F0D243B21B7F14764F99F8898B2C13F5B |
| SHA256: | 144B853BD7066A736EF8347118CF82C18B7A5BE313F7EDF66571E5D9816828AD |
| SSDEEP: | 98304:NWJHHJ2g4xL/oU2GjYxXfD0Z8mV0C0FW4+VUjsIxHv6Z6XcQnJptnnwwjXaPpUdG:8N2CbSg02 |
MALICIOUS
Changes the autorun value in the registry
- utau0419cInstaller.exe (PID: 7328)
SUSPICIOUS
Process drops legitimate windows executable
- utau0419cInstaller.exe (PID: 7328)
- msiexec.exe (PID: 7492)
Starts a Microsoft application from unusual location
- utau0419cInstaller.exe (PID: 7260)
- utau0419cInstaller.exe (PID: 7328)
Executable content was dropped or overwritten
- utau0419cInstaller.exe (PID: 7328)
Reads the Windows owner or organization settings
- setup.exe (PID: 7396)
Executes as Windows Service
- VSSVC.exe (PID: 5544)
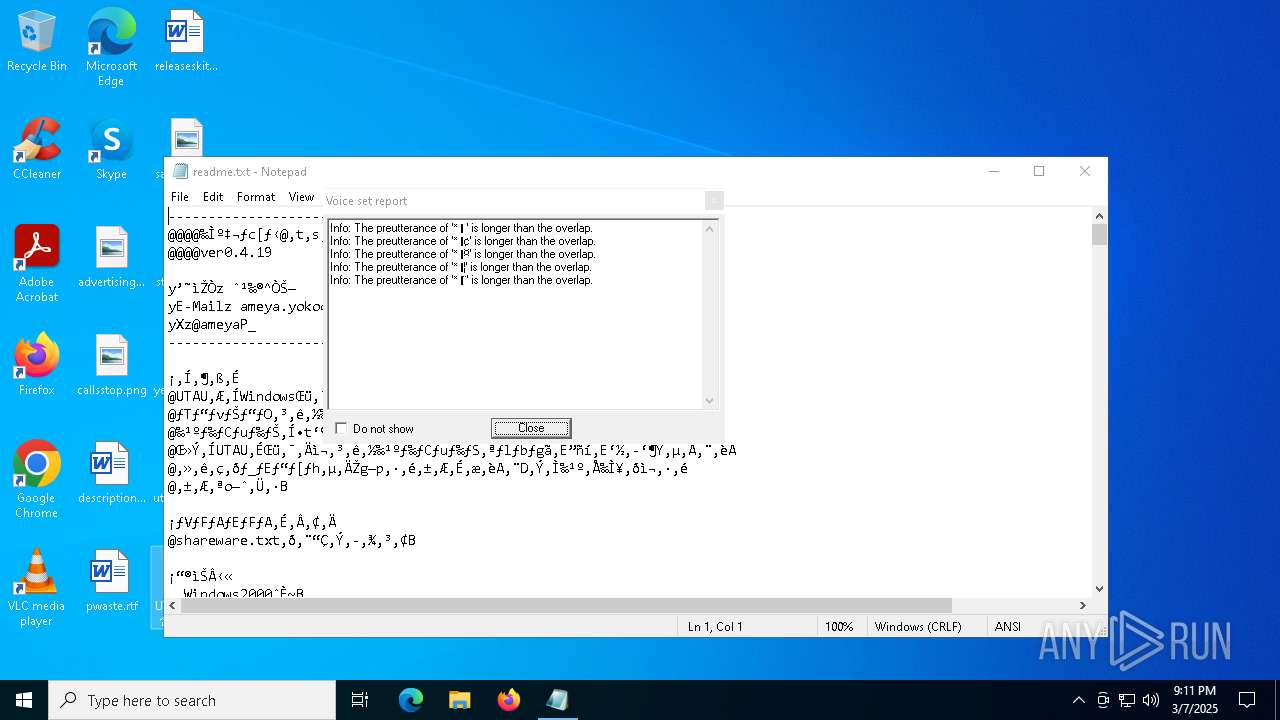
Start notepad (likely ransomware note)
- utau.exe (PID: 7472)
INFO
The sample compiled with japanese language support
- utau0419cInstaller.exe (PID: 7328)
- msiexec.exe (PID: 7492)
Reads the computer name
- utau0419cInstaller.exe (PID: 7328)
- setup.exe (PID: 7396)
- msiexec.exe (PID: 7492)
Checks supported languages
- utau0419cInstaller.exe (PID: 7328)
- setup.exe (PID: 7396)
- msiexec.exe (PID: 7492)
Create files in a temporary directory
- utau0419cInstaller.exe (PID: 7328)
- setup.exe (PID: 7396)
The sample compiled with english language support
- utau0419cInstaller.exe (PID: 7328)
- msiexec.exe (PID: 7492)
Manages system restore points
- SrTasks.exe (PID: 7592)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7492)
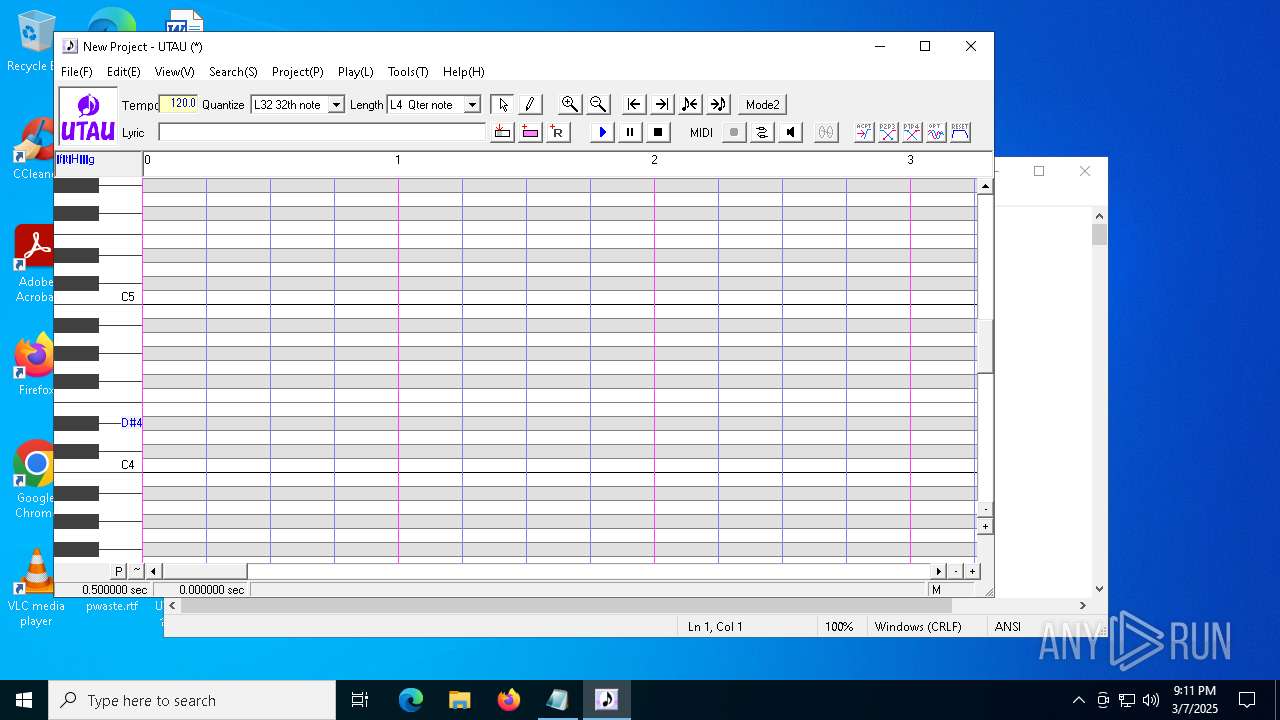
Manual execution by a user
- utau.exe (PID: 7472)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5936)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 5936)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 5936)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1999:09:25 11:18:31+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 5.12 |
| CodeSize: | 34304 |
| InitializedDataSize: | 6825472 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x283d |
| OSVersion: | 5 |
| ImageVersion: | 5 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.2920.0 |
| ProductVersionNumber: | 5.0.2920.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Japanese |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 キャビネット自己展開ツール |
| FileVersion: | 5.00.2920.0000 |
| InternalName: | Wextract |
| LegalCopyright: | Copyright (C) Microsoft Corp. 1981-1999 |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Microsoft(R) Windows (R) 2000 Operating System |
| ProductVersion: | 5.00.2920.0000 |
Total processes
158
Monitored processes
19
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Windows\syswow64\MsiExec.exe" /Y "C:\WINDOWS\SysWOW64\COMDLG32.OCX" | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | "C:\Windows\syswow64\MsiExec.exe" /Y "C:\WINDOWS\SysWOW64\msinet.ocx" | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3784 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4920 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5544 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5936 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7176 | "C:\Windows\syswow64\MsiExec.exe" /Y "C:\WINDOWS\SysWOW64\MSCOMCTL.OCX" | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7200 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7260 | "C:\Users\admin\Desktop\utau0419cInstaller.exe" | C:\Users\admin\Desktop\utau0419cInstaller.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 キャビネット自己展開ツール Exit code: 3221226540 Version: 5.00.2920.0000 Modules
| |||||||||||||||
| 7328 | "C:\Users\admin\Desktop\utau0419cInstaller.exe" | C:\Users\admin\Desktop\utau0419cInstaller.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 キャビネット自己展開ツール Exit code: 0 Version: 5.00.2920.0000 Modules
| |||||||||||||||
Total events
9 955
Read events
9 054
Write events
813
Delete events
88
Modification events
| (PID) Process: | (7328) utau0419cInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\WINDOWS\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (7396) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{618736E0-3C3D-11CF-810C-00AA00389B71}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7396) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{618736E0-3C3D-11CF-810C-00AA00389B71}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7396) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Volatile\00\MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{03022430-ABC4-11D0-BDE2-00AA001A1953}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7396) setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Volatile\00\MACHINE\SOFTWARE\Classes\Interface\{03022430-ABC4-11D0-BDE2-00AA001A1953}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7200) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7200) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7200) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3784) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3784) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
22
Suspicious files
309
Text files
39
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7328 | utau0419cInstaller.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\utaustup.msi | — | |
MD5:— | SHA256:— | |||
| 5936 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\d8a51b0a-6138-423e-895c-768397a8720e.down_data | — | |
MD5:— | SHA256:— | |||
| 7492 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7492 | msiexec.exe | C:\Windows\Installer\1122d7.msi | — | |
MD5:— | SHA256:— | |||
| 5936 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:7C48C30BA63B689902BB426C7A0DDC09 | SHA256:32716D5FC0139B83464450DC3B8550672E5530480DCA1050D2606F95DFDF67EB | |||
| 7328 | utau0419cInstaller.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\setup.exe | executable | |
MD5:D60900A7B0FFF3BD9F109B3CC00F7804 | SHA256:8F1B93D05B2CD046F87F10ED5C11430BDE70439CAF34DC6BB81B12AE2D25EB9F | |||
| 7492 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:B329ED52DD0BFBEC026CB0C048AC60B3 | SHA256:4DE8890C216BB723D128DB403F6FF3A4DA1BF6048FDBC9A3FBA3F12C36090955 | |||
| 5936 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\d8a51b0a-6138-423e-895c-768397a8720e.7796483d-092d-4bd1-8284-5c253cc379cf.down_meta | binary | |
MD5:91934B47D225048A461FA9007477EC6F | SHA256:F5C876E594F32E54319AFC51B5F2387A5FCF0B88A9493781FC8EAA236510D7B5 | |||
| 5936 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:E694690FBBCF757B7EEDCC9E56E802CD | SHA256:F99A1DBEB7D18CA69D22FEA08EDA34139FA508237375FD2A0F64FD1D31FD0C7E | |||
| 7492 | msiexec.exe | C:\Windows\Installer\MSI2671.tmp | binary | |
MD5:EEA148F1BDB16C4EA8EAD2D3F42F9CD1 | SHA256:4204E73354518785CECF034A32CF10AD7A2D856485E284C81DC9D3EAD493B3C5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
34
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5360 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7576 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5936 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5360 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
7576 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7576 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5936 | BackgroundTransferHost.exe | 184.86.251.21:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |