| File name: | Pantheon V2 HVNCnls.scr |
| Full analysis: | https://app.any.run/tasks/34dc84d9-6aa0-4088-b0de-3f968560756a |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 03:29:50 |
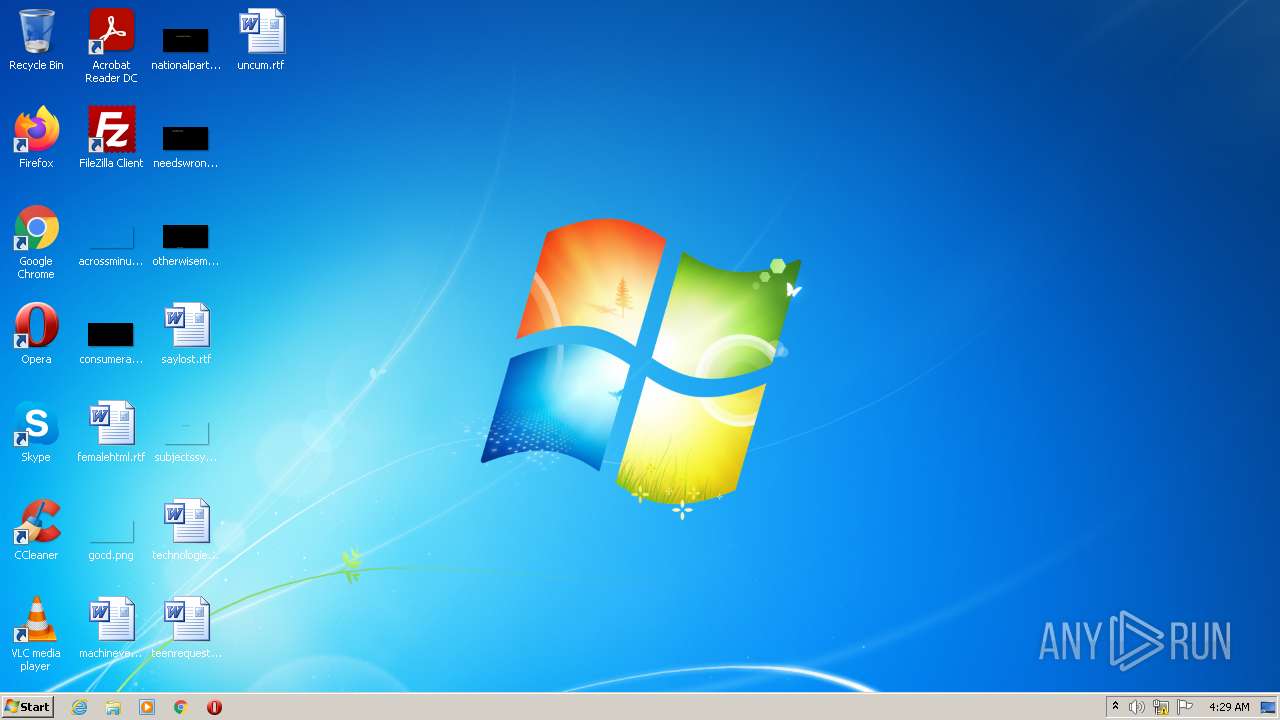
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 98D7999986D63FBD914BDDC3D7B7ECF9 |
| SHA1: | 7C528FB3CC427791482F7A84923A21621CFB9675 |
| SHA256: | 144A026BB63A29B36A3437094C4F53CF1CB135EDCBE15AB06E35FB8759129BFC |
| SSDEEP: | 12288:v41SrH22qla5w/yXbxixFcRMFQIkeNCSo9mbX8:v0SrH0MW/IbxiYCQIkeNCSBQ |
MALICIOUS
Drops executable file immediately after starts
- Pantheon V2 HVNCnls.scr.exe (PID: 2272)
Application was dropped or rewritten from another process
- REALFINAL.EXE (PID: 1648)
SUSPICIOUS
Reads the computer name
- Pantheon V2 HVNCnls.scr.exe (PID: 2272)
- REALFINAL.EXE (PID: 1648)
Checks supported languages
- Pantheon V2 HVNCnls.scr.exe (PID: 2272)
- REALFINAL.EXE (PID: 1648)
- cmd.exe (PID: 3452)
- cmd.exe (PID: 3860)
Creates files in the user directory
- Pantheon V2 HVNCnls.scr.exe (PID: 2272)
Drops a file with a compile date too recent
- Pantheon V2 HVNCnls.scr.exe (PID: 2272)
Executable content was dropped or overwritten
- Pantheon V2 HVNCnls.scr.exe (PID: 2272)
Starts CMD.EXE for commands execution
- REALFINAL.EXE (PID: 1648)
INFO
Checks supported languages
- timeout.exe (PID: 3816)
- timeout.exe (PID: 3140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x3248 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 786432 |
| CodeSize: | 31232 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| TimeStamp: | 2011:07:03 11:05:04+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jul-2011 09:05:04 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 03-Jul-2011 09:05:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00007842 | 0x00007A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48777 |
.rdata | 0x00009000 | 0x0000319E | 0x00003200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92389 |
.data | 0x0000D000 | 0x00001A84 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.57332 |
.rsrc | 0x0000F000 | 0x000BAB5C | 0x000BAC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.44333 |
.reloc | 0x000CA000 | 0x000013AA | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.12103 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.01924 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
CURLLOADER.SLN | 5.50676 | 1440 | Latin 1 / Western European | UNKNOWN | RBIND |
REALFINAL.EXE | 7.56922 | 513536 | Latin 1 / Western European | UNKNOWN | RBIND |
DROPIN | 2.19716 | 9 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
EXEC | 0 | 1 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.dll |
SHELL32.dll |
Total processes
40
Monitored processes
6
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1648 | "C:\Users\admin\AppData\Roaming\REALFINAL.EXE" | C:\Users\admin\AppData\Roaming\REALFINAL.EXE | — | Pantheon V2 HVNCnls.scr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Rights Management Services Activation for Server Security Processor Exit code: 0 Version: 10.0.19041.1682 Modules
| |||||||||||||||
| 2272 | "C:\Users\admin\AppData\Local\Temp\Pantheon V2 HVNCnls.scr.exe" | C:\Users\admin\AppData\Local\Temp\Pantheon V2 HVNCnls.scr.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 3140 | timeout 40 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3452 | "C:\Windows\System32\cmd.exe" /c timeout /nobreak /t 20 | C:\Windows\System32\cmd.exe | — | REALFINAL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3816 | timeout /nobreak /t 20 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3860 | "C:\Windows\System32\cmd.exe" /c timeout 40 | C:\Windows\System32\cmd.exe | — | REALFINAL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
985
Read events
969
Write events
16
Delete events
0
Modification events
| (PID) Process: | (2272) Pantheon V2 HVNCnls.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2272) Pantheon V2 HVNCnls.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2272) Pantheon V2 HVNCnls.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2272) Pantheon V2 HVNCnls.scr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1648) REALFINAL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1648) REALFINAL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1648) REALFINAL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1648) REALFINAL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2272 | Pantheon V2 HVNCnls.scr.exe | C:\Users\admin\AppData\Roaming\CURLLOADER.SLN | text | |
MD5:BC5A8C18FC6C44756CDE51EF471A9A1F | SHA256:280E88A726F3288028975A8851415EEB1A716F72D8650110B86D5E2DDD346D18 | |||
| 2272 | Pantheon V2 HVNCnls.scr.exe | C:\Users\admin\AppData\Roaming\REALFINAL.EXE | executable | |
MD5:8B662719E44AB11419FE3E1D7E96CC03 | SHA256:0E3BE9658E97E3EA844E0D818A0F4731573EC5AFFE4F42E8D244E0C91717DF68 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
Pantheon V2 HVNCnls.scr.exe | C:\Users\admin\AppData\Roaming\CURLLOADER.SLN |
Pantheon V2 HVNCnls.scr.exe | C:\Users\admin\AppData\Roaming\REALFINAL.EXE |