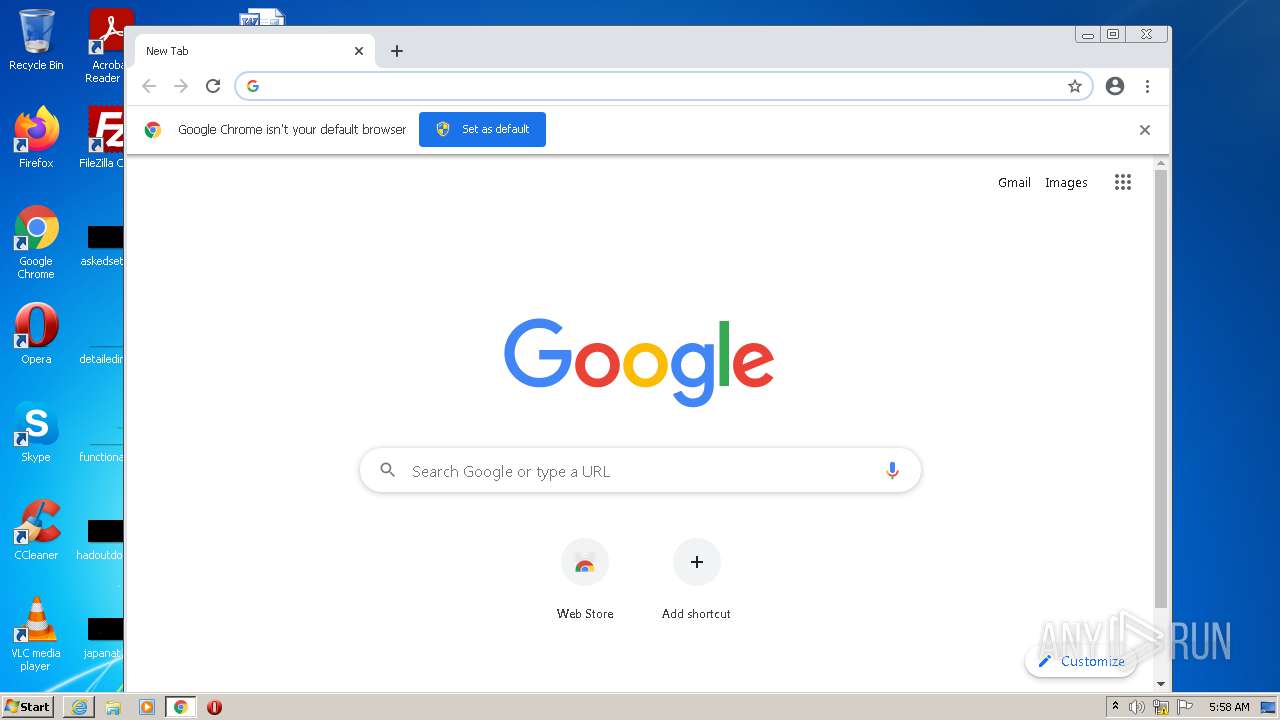
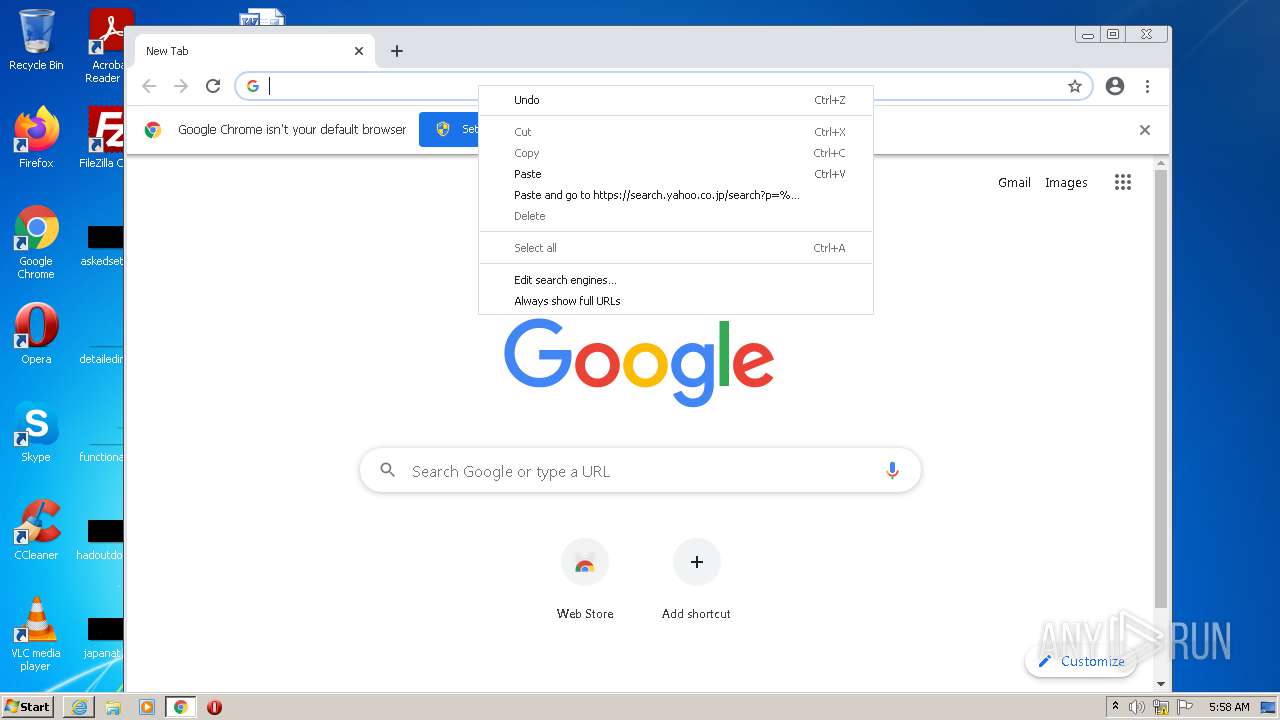
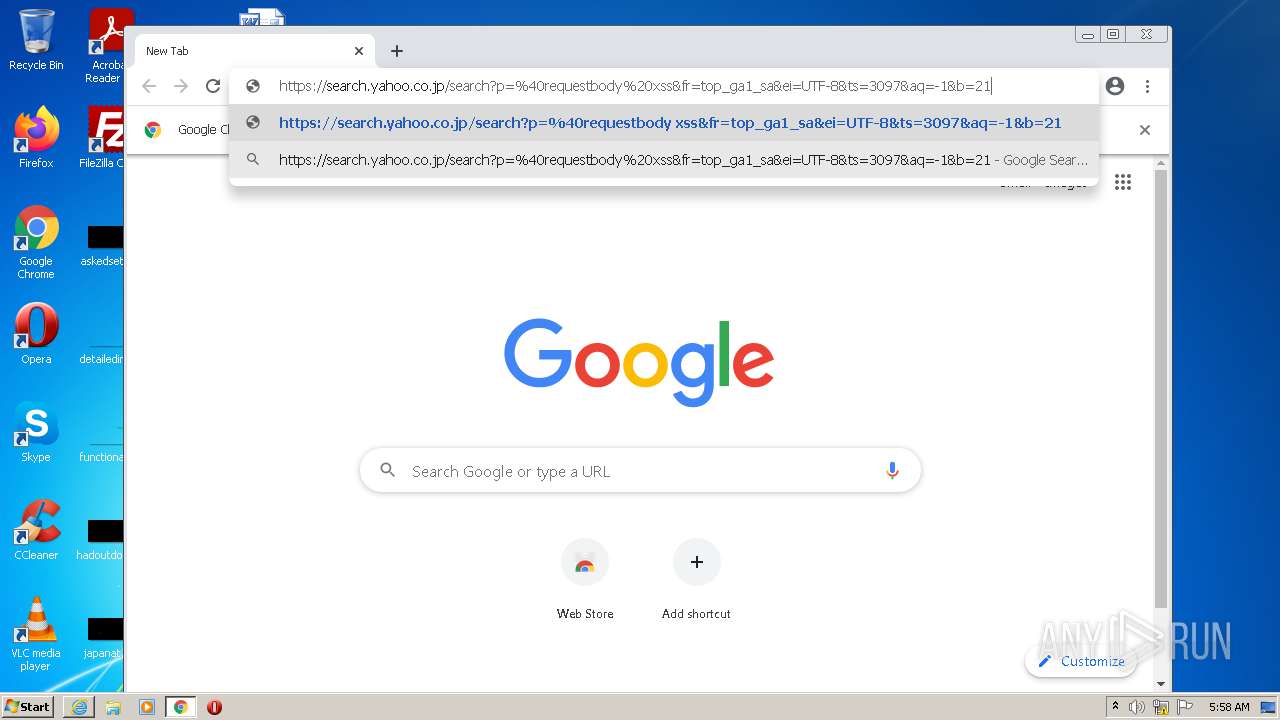
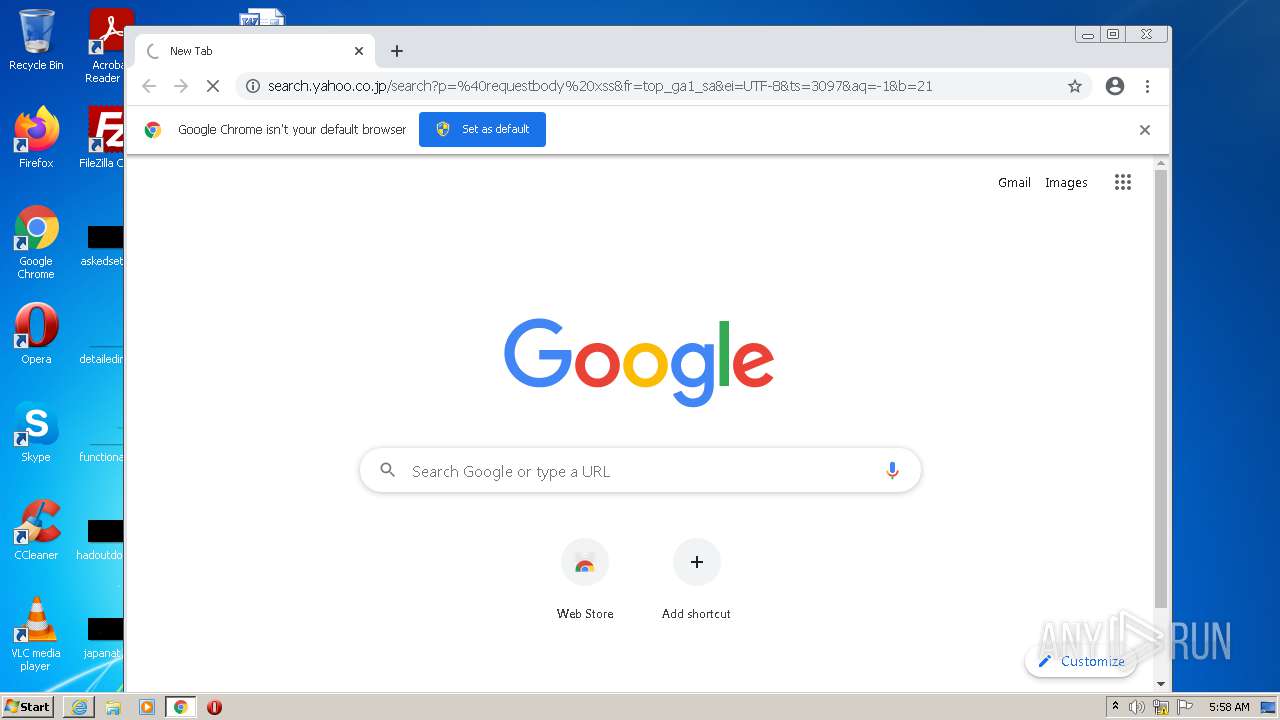
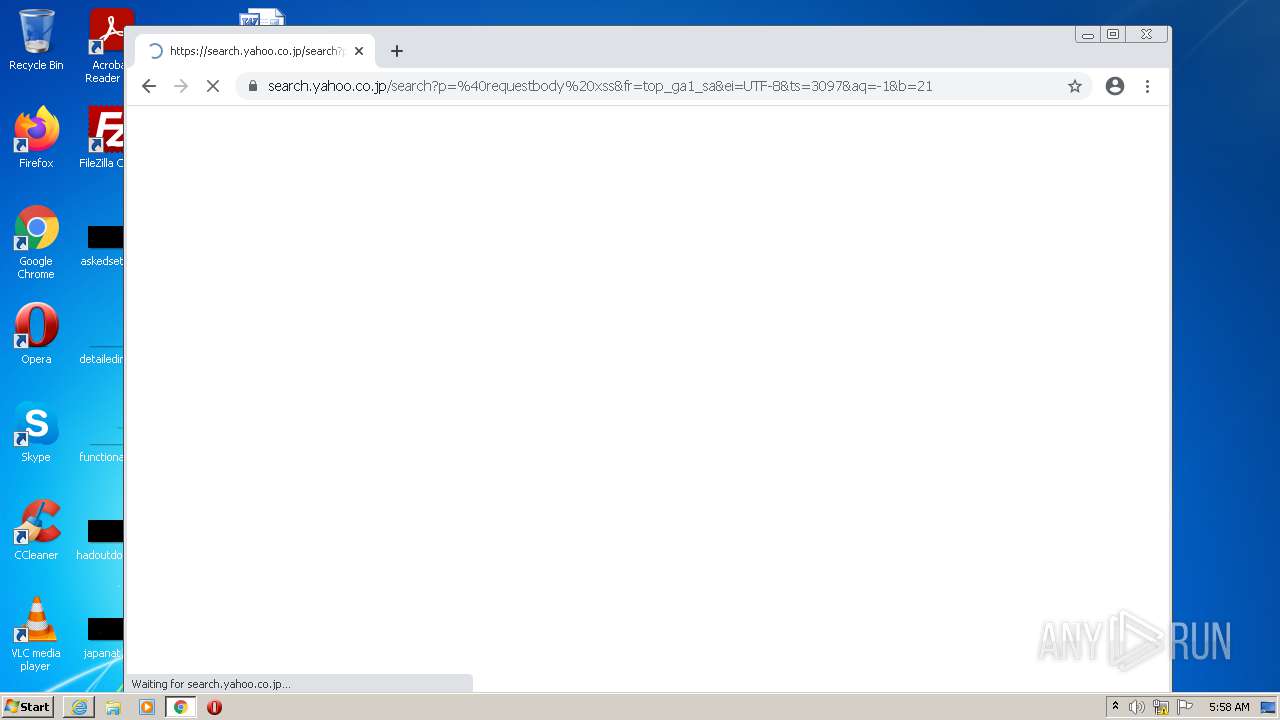
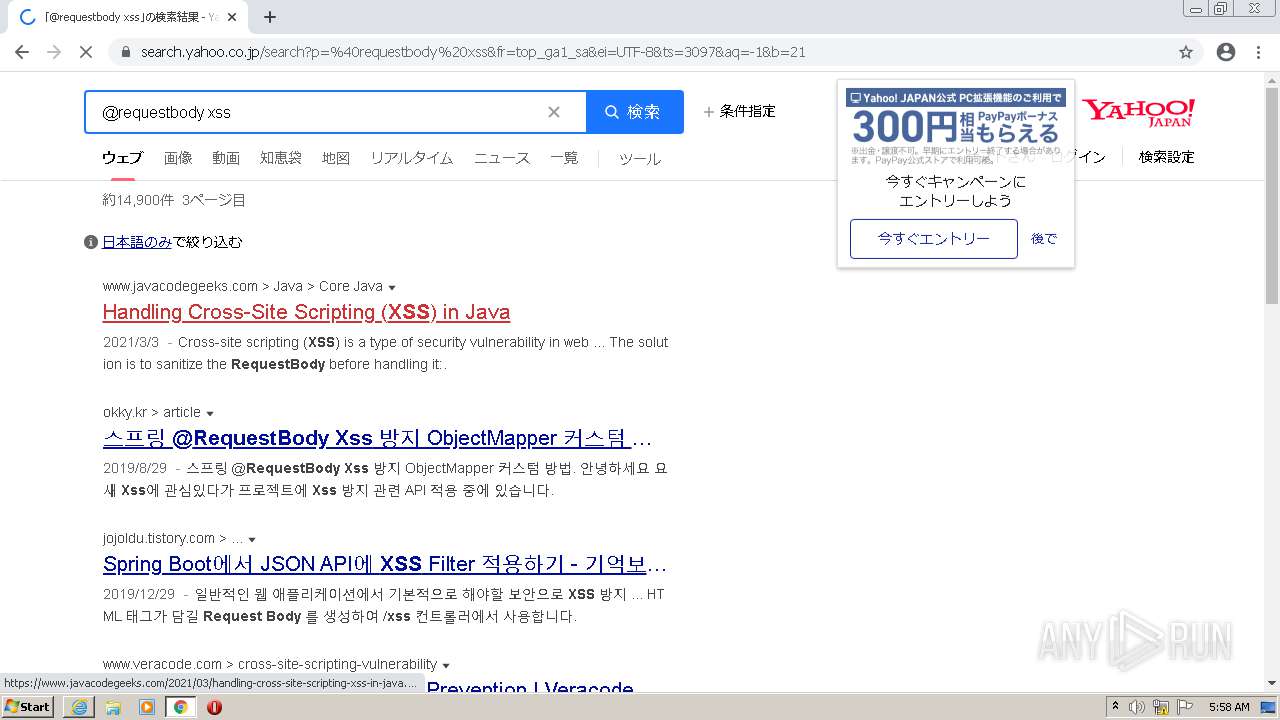
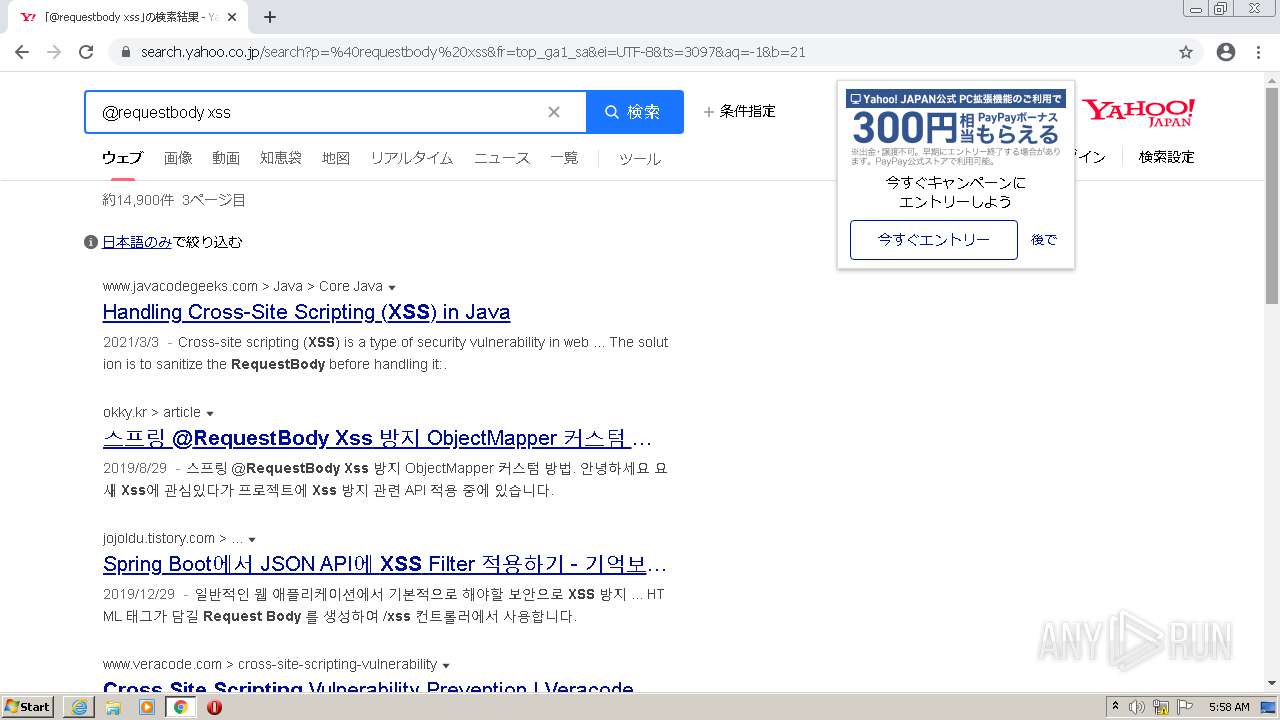
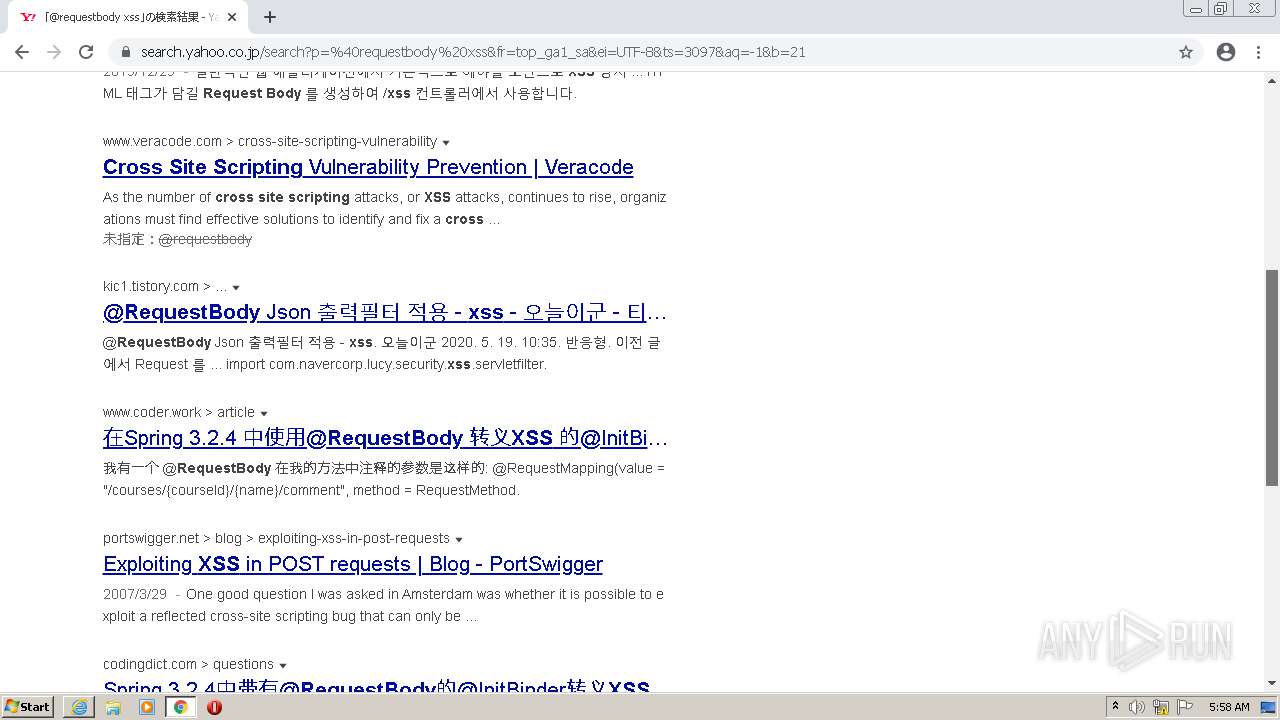
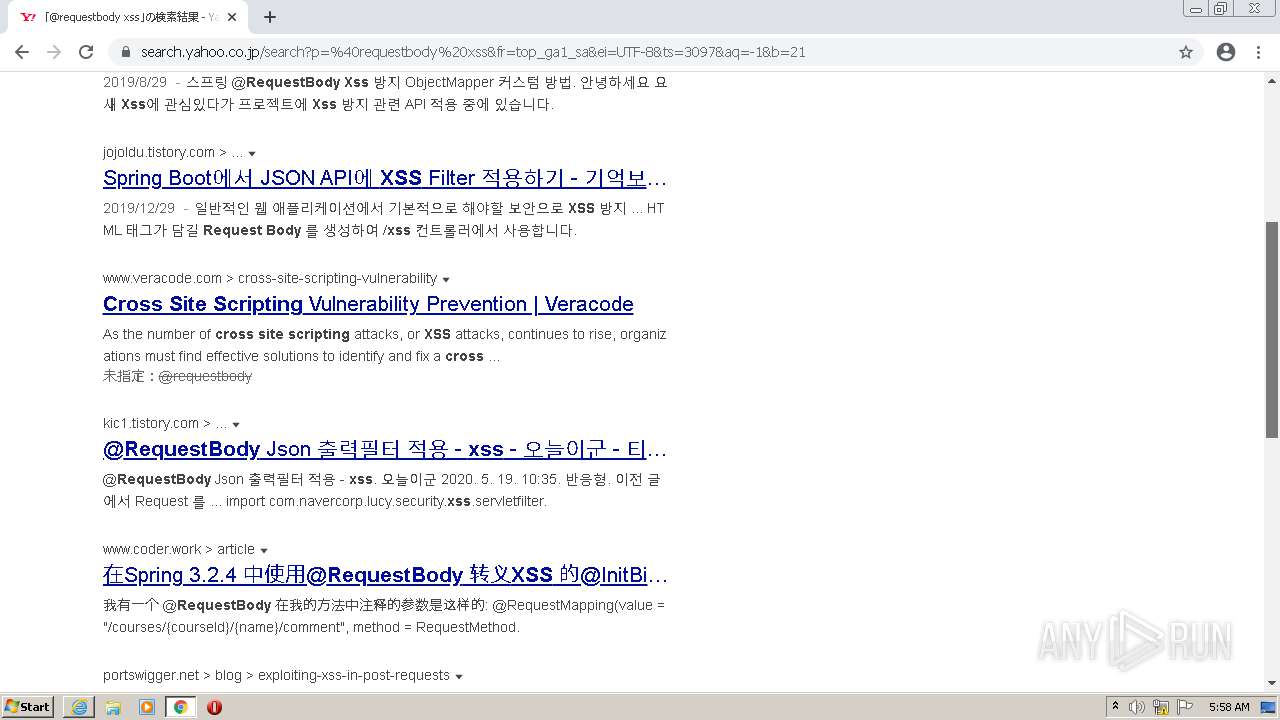
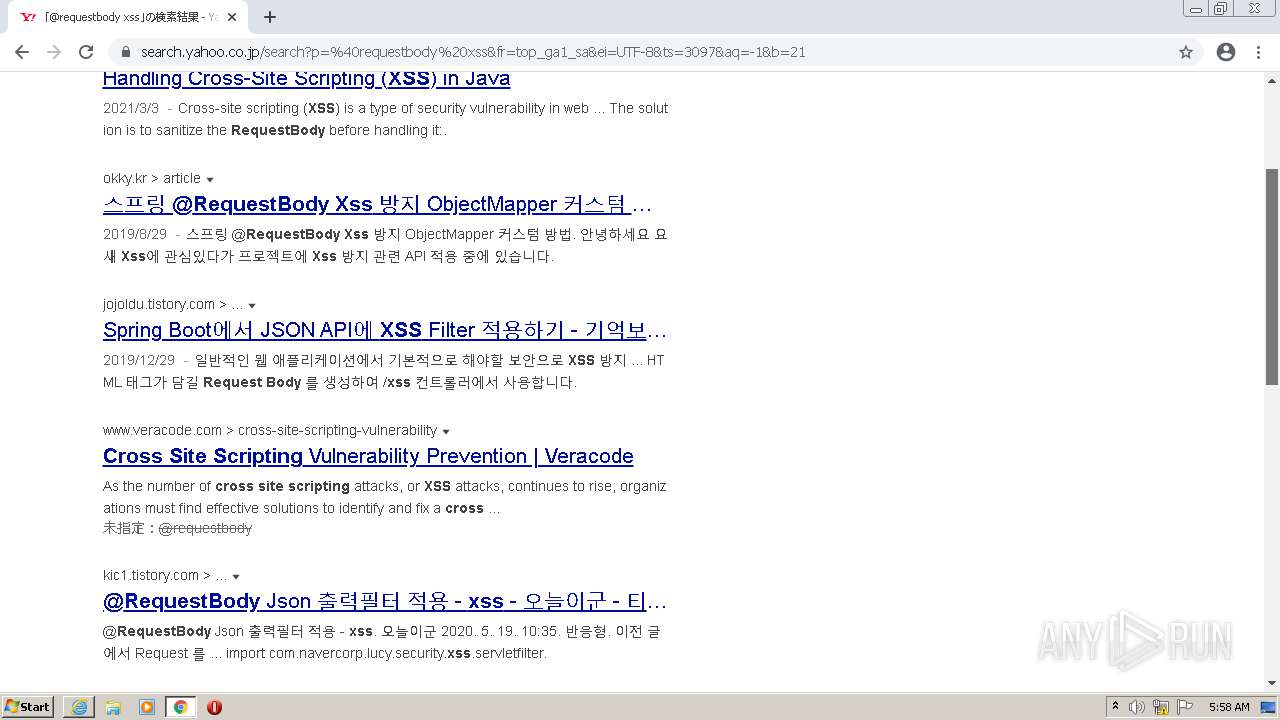
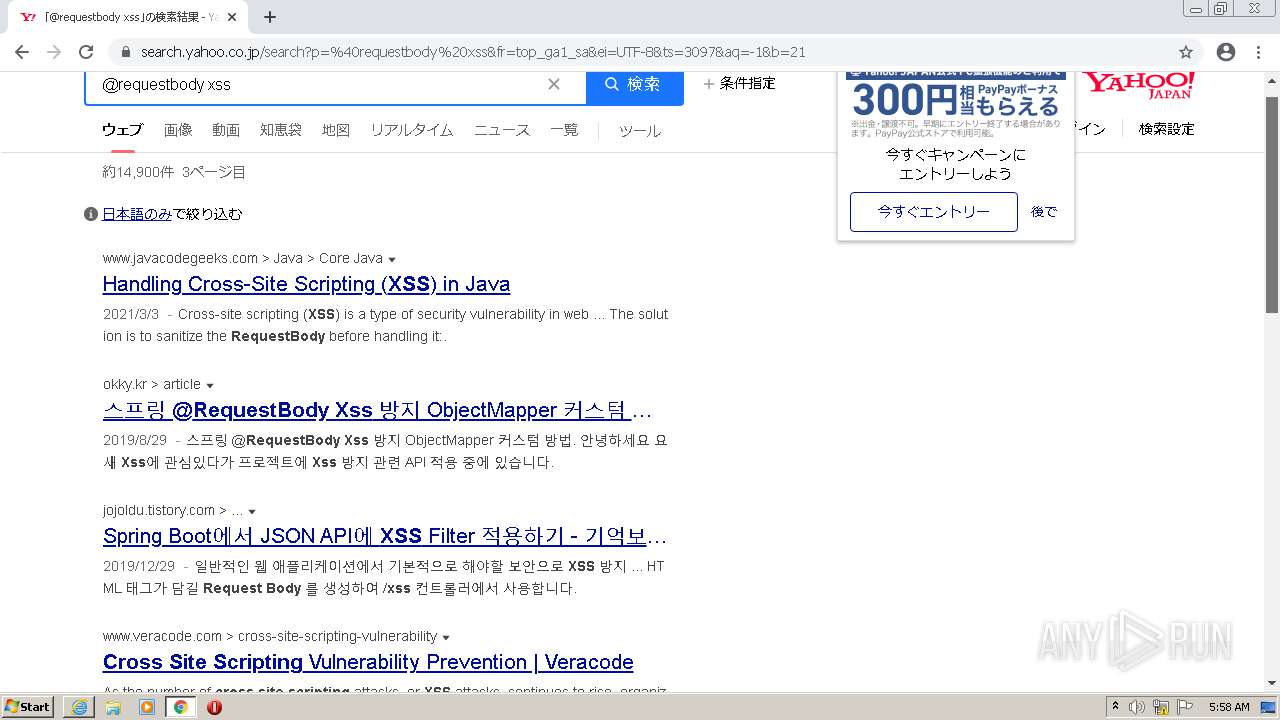
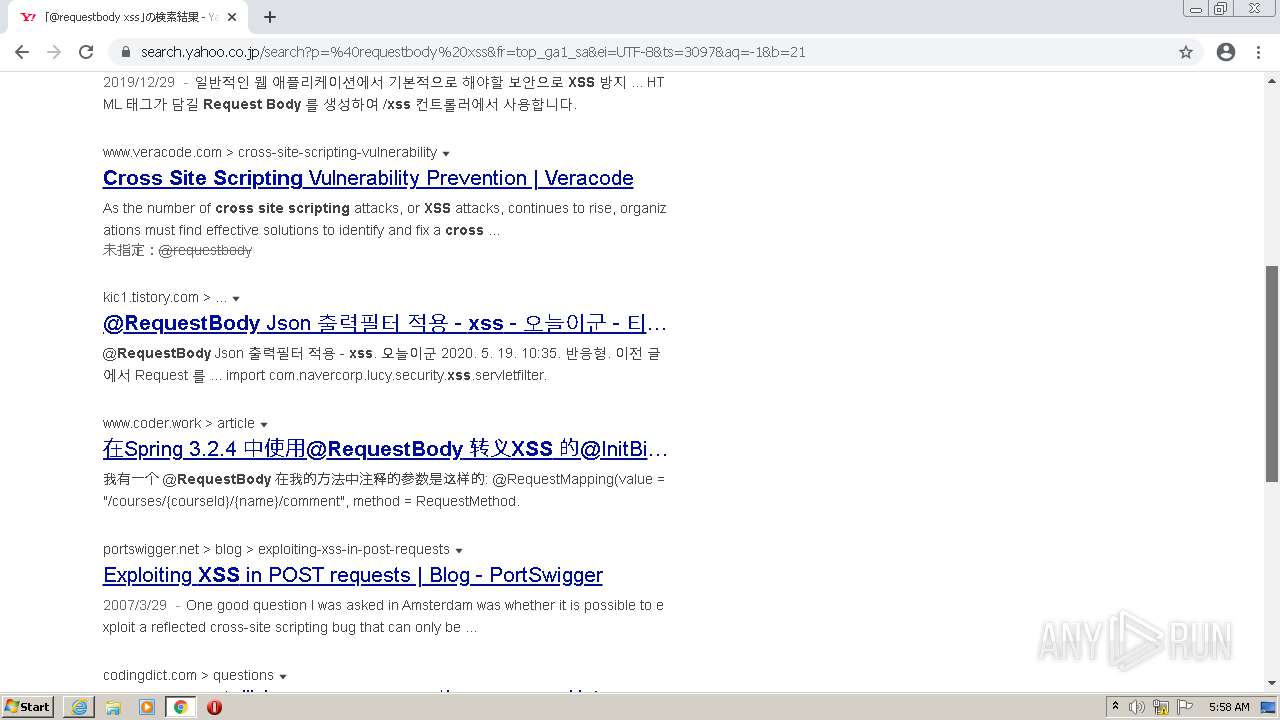
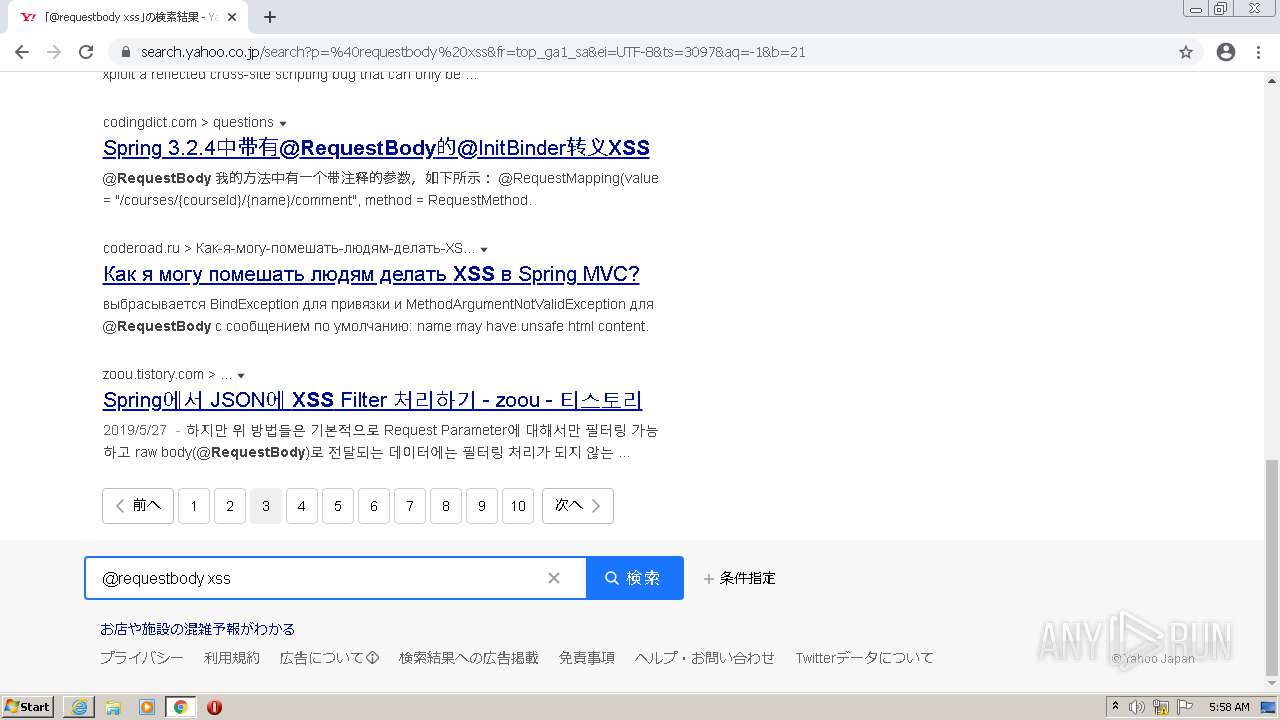
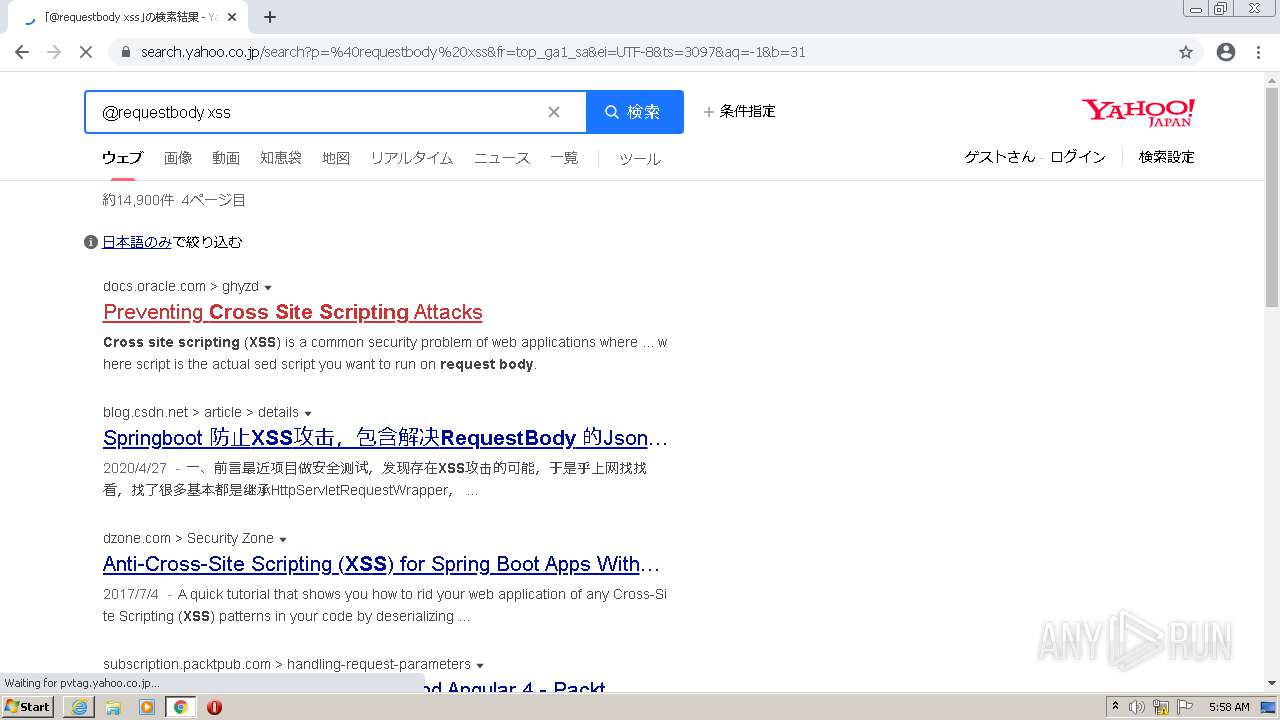
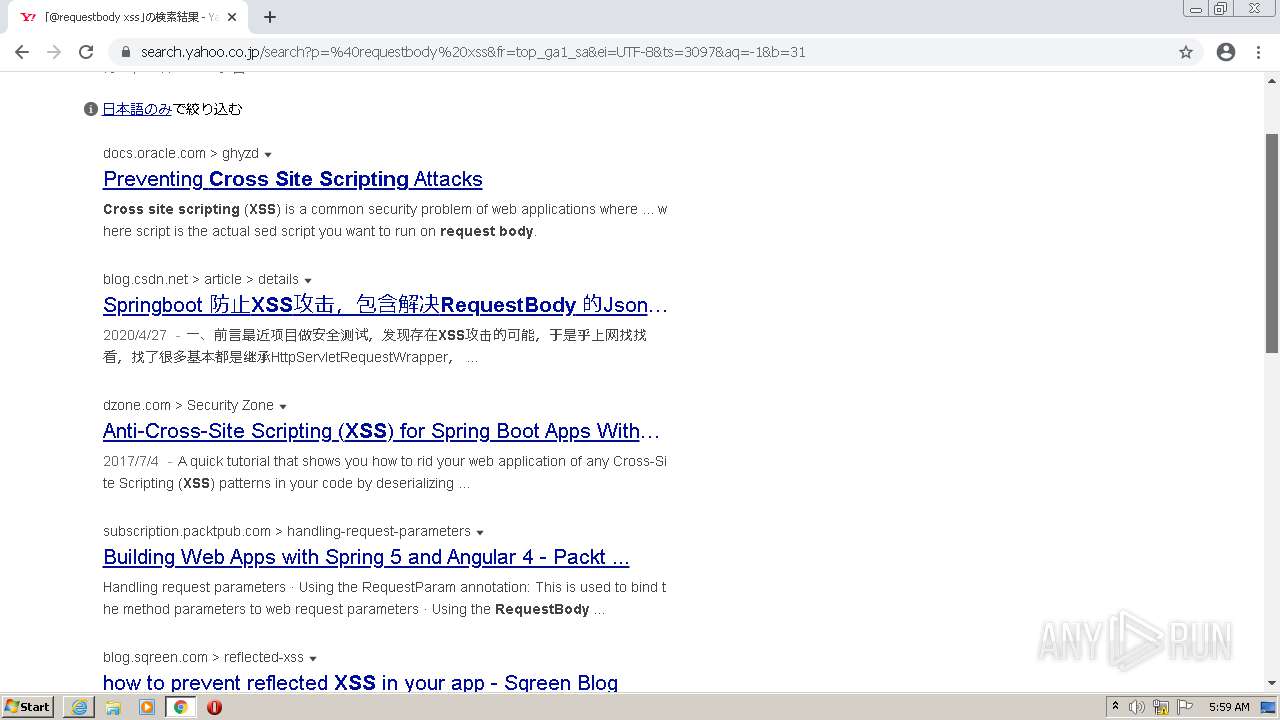
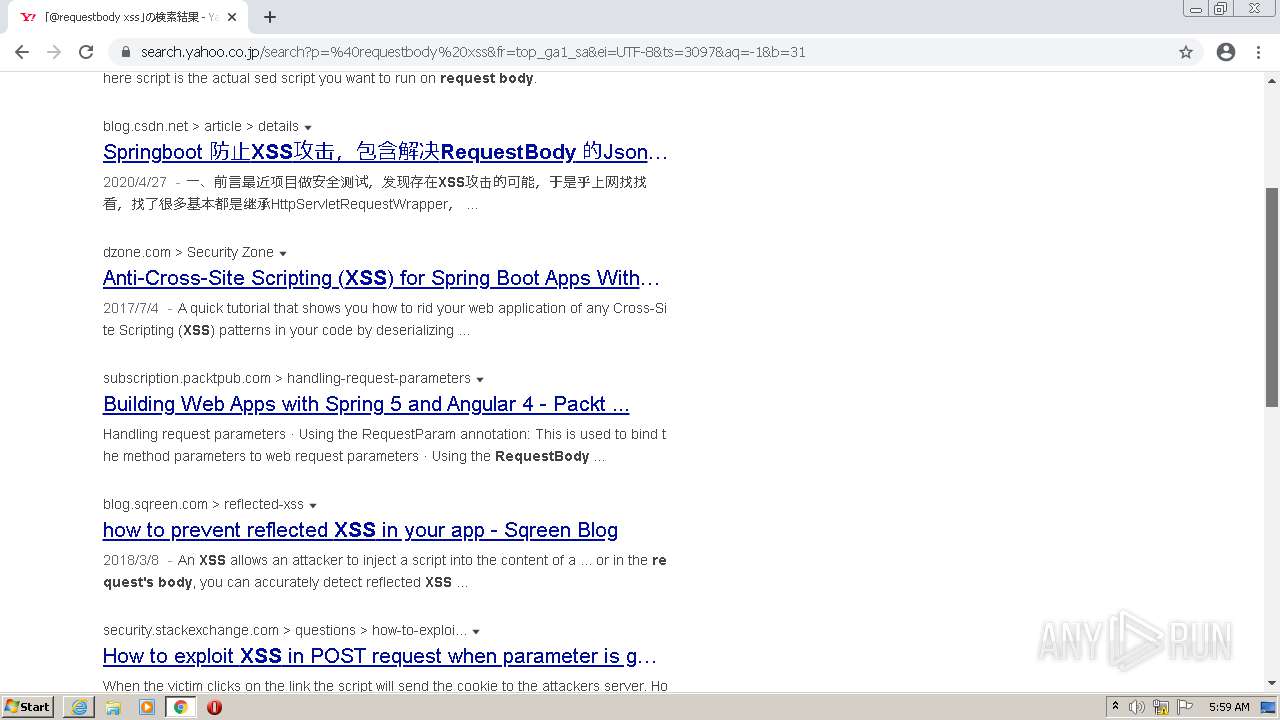
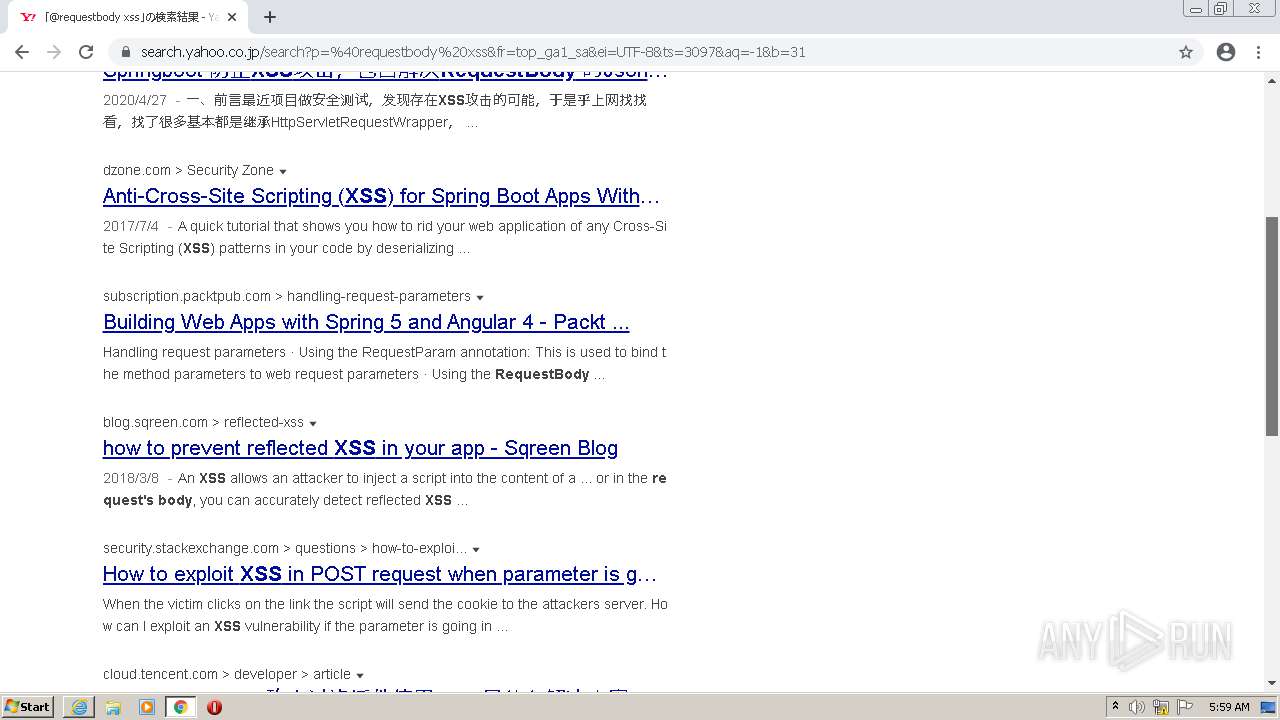
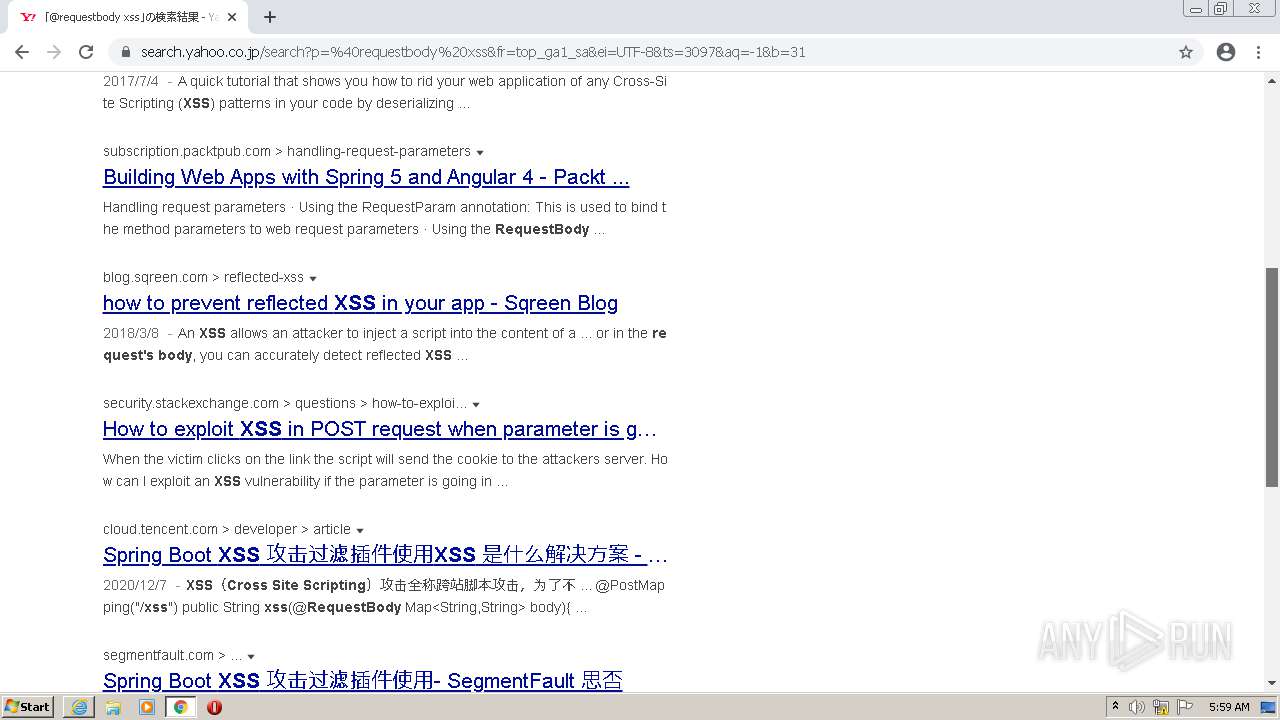
| URL: | https://search.yahoo.co.jp/search?p=%40requestbody%20xss&fr=top_ga1_sa&ei=UTF-8&ts=3097&aq=-1&b=21 |
| Full analysis: | https://app.any.run/tasks/3bc628c7-48c1-428d-86a7-2fa5e78f3b9e |
| Verdict: | Malicious activity |
| Analysis date: | November 11, 2021, 05:54:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C1C8E38279A93A4402BBC70A81522C2E |
| SHA1: | 58E85166A97447AD4E8C1CC4108A5B37EAEBF862 |
| SHA256: | 1437891E990FE735CE950FCF6CEC418123C0FD01DCB54F852AD4D0CE79BBCC63 |
| SSDEEP: | 3:N8N+GtGaMStzQUAqTmEdpEU5ZwxjIfS/EUlaf:2QhQLAqTVfZTfpUsf |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 572)
Modifies files in Chrome extension folder
- chrome.exe (PID: 4020)
INFO
Checks supported languages
- iexplore.exe (PID: 572)
- iexplore.exe (PID: 828)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 1988)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 2232)
- chrome.exe (PID: 1636)
- chrome.exe (PID: 2680)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 3424)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 1932)
- chrome.exe (PID: 3968)
- chrome.exe (PID: 1980)
- chrome.exe (PID: 3608)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 3704)
- chrome.exe (PID: 448)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 3152)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 3860)
- chrome.exe (PID: 2640)
- chrome.exe (PID: 1284)
- chrome.exe (PID: 1876)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 3080)
- chrome.exe (PID: 3828)
- chrome.exe (PID: 2092)
- chrome.exe (PID: 2596)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 3348)
- chrome.exe (PID: 2948)
- chrome.exe (PID: 1132)
- chrome.exe (PID: 564)
- chrome.exe (PID: 896)
- chrome.exe (PID: 1120)
- chrome.exe (PID: 4160)
- chrome.exe (PID: 4208)
- chrome.exe (PID: 4140)
- chrome.exe (PID: 2992)
- chrome.exe (PID: 4604)
Reads the computer name
- iexplore.exe (PID: 828)
- iexplore.exe (PID: 572)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 2688)
- chrome.exe (PID: 3852)
- chrome.exe (PID: 3424)
- chrome.exe (PID: 1980)
Reads settings of System Certificates
- iexplore.exe (PID: 828)
- chrome.exe (PID: 2576)
- iexplore.exe (PID: 572)
Application launched itself
- iexplore.exe (PID: 828)
- chrome.exe (PID: 4020)
Changes internet zones settings
- iexplore.exe (PID: 828)
Creates files in the user directory
- iexplore.exe (PID: 828)
- iexplore.exe (PID: 572)
Changes settings of System certificates
- iexplore.exe (PID: 828)
Manual execution by user
- chrome.exe (PID: 4020)
Reads the hosts file
- chrome.exe (PID: 4020)
- chrome.exe (PID: 2576)
Reads internet explorer settings
- iexplore.exe (PID: 572)
Checks Windows Trust Settings
- iexplore.exe (PID: 828)
- iexplore.exe (PID: 572)
Adds / modifies Windows certificates
- iexplore.exe (PID: 828)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 4020)
Reads the date of Windows installation
- chrome.exe (PID: 3424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
58
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1030815201709424647,15074430205720723313,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1030815201709424647,15074430205720723313,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=48 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6060 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:828 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 828 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://search.yahoo.co.jp/search?p=%40requestbody%20xss&fr=top_ga1_sa&ei=UTF-8&ts=3097&aq=-1&b=21" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1030815201709424647,15074430205720723313,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=49 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1030815201709424647,15074430205720723313,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=50 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1030815201709424647,15074430205720723313,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=47 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1030815201709424647,15074430205720723313,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,1030815201709424647,15074430205720723313,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2568 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,1030815201709424647,15074430205720723313,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
42 483
Read events
42 194
Write events
281
Delete events
8
Modification events
| (PID) Process: | (828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30922432 | |||
| (PID) Process: | (828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30922432 | |||
| (PID) Process: | (828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (828) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
180
Text files
262
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 828 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 828 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 828 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 828 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\KBMO3IY2.txt | text | |
MD5:— | SHA256:— | |||
| 828 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\P5176SLH.txt | text | |
MD5:— | SHA256:— | |||
| 4020 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-618CB0FB-FB4.pma | — | |
MD5:— | SHA256:— | |||
| 828 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\MMGA5ENT.txt | text | |
MD5:— | SHA256:— | |||
| 828 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 828 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 828 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
311
DNS requests
221
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nvkopsnfmtkaxn4annxjego2ca_2021.11.1.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2021.11.1.1143_all_nkp4b43vk3ctkcmicenouveale.crx3 | US | — | — | whitelisted |
— | — | HEAD | 200 | 74.125.173.231:80 | http://r2---sn-4g5ednz7.gvt1.com/edgedl/release2/chrome_component/nvkopsnfmtkaxn4annxjego2ca_2021.11.1.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2021.11.1.1143_all_nkp4b43vk3ctkcmicenouveale.crx3?cms_redirect=yes&mh=4w&mip=194.195.91.19&mm=28&mn=sn-4g5ednz7&ms=nvh&mt=1636609935&mv=m&mvi=2&pl=24&rmhost=r5---sn-4g5ednz7.gvt1.com&shardbypass=yes&smhost=r5---sn-4g5ednsz.gvt1.com | US | — | — | whitelisted |
— | — | HEAD | 302 | 142.250.185.142:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/nvkopsnfmtkaxn4annxjego2ca_2021.11.1.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2021.11.1.1143_all_nkp4b43vk3ctkcmicenouveale.crx3 | US | — | — | whitelisted |
828 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2576 | chrome.exe | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/AAACertificateServices.crl | US | der | 506 b | whitelisted |
828 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
828 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
2576 | chrome.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEChOOcFLOG2InHKZ5YzQWlc%3D | US | der | 727 b | whitelisted |
572 | iexplore.exe | GET | 200 | 23.213.161.88:80 | http://scrootca2.ocsp.secomtrust.net/MEowSDBGMEQwQjAJBgUrDgMCGgUABBTyDvPjcY8Z0TDZzHotwwMWHLKc0AQUCoWpd2UFmHxAgfgPlyw48QrsPM8CCSK5sWMM7LQ8Lg%3D%3D | US | der | 1.50 Kb | whitelisted |
828 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
572 | iexplore.exe | 182.22.16.251:443 | search.yahoo.co.jp | Yahoo Japan Corporation | JP | suspicious |
828 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
828 | iexplore.exe | 8.253.204.249:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
828 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
828 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
828 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
828 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
828 | iexplore.exe | 104.89.38.104:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | malicious |
828 | iexplore.exe | 13.92.246.37:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
2576 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
search.yahoo.co.jp |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |