| File name: | SAPPHIRE SPOOFER.exe |
| Full analysis: | https://app.any.run/tasks/b644622b-c7bd-4823-8d82-fbd2e1f1e4d7 |
| Verdict: | Malicious activity |
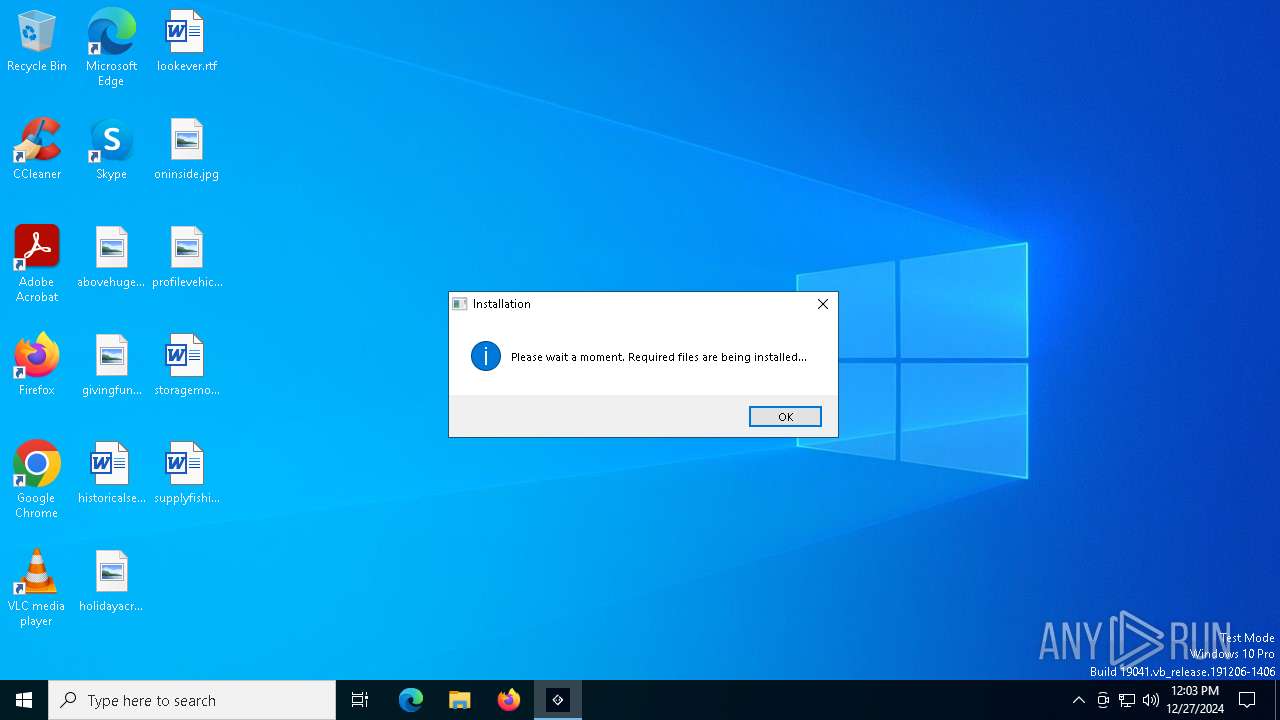
| Analysis date: | December 27, 2024, 12:03:14 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 677CA57390D1B649D3A8584BCEC23E77 |
| SHA1: | 958F276729D21A061AA02CD227F9EC3D91A8A915 |
| SHA256: | 142D4A3FAF5DEFAA7C276E99774C81DADD3DC74DE7A35F0BF85C8FE4E8AD8715 |
| SSDEEP: | 24576:Up+/4UURxUruRrax70p5O9Qx+aAm0vYRO8tf/G:UE/XUraxm5O9QMal0QRO8tf |
MALICIOUS
Connects to the CnC server
- SAPPHIRE SPOOFER.exe (PID: 6828)
Bypass execution policy to execute commands
- powershell.exe (PID: 4444)
Changes powershell execution policy (Bypass)
- SAPPHIRE SPOOFER.exe (PID: 6828)
SUSPICIOUS
Reads security settings of Internet Explorer
- SAPPHIRE SPOOFER.exe (PID: 6828)
Checks Windows Trust Settings
- SAPPHIRE SPOOFER.exe (PID: 6828)
Potential Corporate Privacy Violation
- SAPPHIRE SPOOFER.exe (PID: 6828)
Creates files in the driver directory
- SAPPHIRE SPOOFER.exe (PID: 6828)
Contacting a server suspected of hosting an CnC
- SAPPHIRE SPOOFER.exe (PID: 6828)
Connects to the server without a host name
- SAPPHIRE SPOOFER.exe (PID: 6828)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 4444)
Starts POWERSHELL.EXE for commands execution
- SAPPHIRE SPOOFER.exe (PID: 6828)
INFO
Checks supported languages
- SAPPHIRE SPOOFER.exe (PID: 6828)
The sample compiled with english language support
- SAPPHIRE SPOOFER.exe (PID: 6828)
Reads mouse settings
- SAPPHIRE SPOOFER.exe (PID: 6828)
The process uses AutoIt
- SAPPHIRE SPOOFER.exe (PID: 6828)
Reads the computer name
- SAPPHIRE SPOOFER.exe (PID: 6828)
Creates files or folders in the user directory
- SAPPHIRE SPOOFER.exe (PID: 6828)
Reads the machine GUID from the registry
- SAPPHIRE SPOOFER.exe (PID: 6828)
Checks proxy server information
- SAPPHIRE SPOOFER.exe (PID: 6828)
Reads the software policy settings
- SAPPHIRE SPOOFER.exe (PID: 6828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:12:01 11:15:59+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.16 |
| CodeSize: | 734208 |
| InitializedDataSize: | 325120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2549c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
Total processes
129
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4444 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -Command "Import-Certificate -FilePath 'C:\WINDOWS\server.crt' -CertStoreLocation 'Cert:\LocalMachine\Root' -ErrorAction SilentlyContinue" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | SAPPHIRE SPOOFER.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5460 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6668 | "C:\Users\admin\AppData\Local\Temp\SAPPHIRE SPOOFER.exe" | C:\Users\admin\AppData\Local\Temp\SAPPHIRE SPOOFER.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6828 | "C:\Users\admin\AppData\Local\Temp\SAPPHIRE SPOOFER.exe" | C:\Users\admin\AppData\Local\Temp\SAPPHIRE SPOOFER.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
4 945
Read events
4 942
Write events
3
Delete events
0
Modification events
| (PID) Process: | (6828) SAPPHIRE SPOOFER.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6828) SAPPHIRE SPOOFER.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6828) SAPPHIRE SPOOFER.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
2
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6828 | SAPPHIRE SPOOFER.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\server[1].cer | text | |
MD5:9A757DFC4212AD866330AE2934A297AA | SHA256:9B290CC789B2133E9FD6BE00C2A3AFE0FFC586708FDEF89B9EA024993264D605 | |||
| 6828 | SAPPHIRE SPOOFER.exe | C:\Windows\System32\drivers\etc\hosts.ics | text | |
MD5:74D0DFE9F31C8D10CCF3222D44BDD123 | SHA256:FAC557CAECDC0C36C51BF944B2217ECCB67AE2B816C809FBCD13B0C9CF114F1B | |||
| 6828 | SAPPHIRE SPOOFER.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | binary | |
MD5:7208F91E731475B50B39EFEC9E62AF49 | SHA256:E83B5E14202FFDE067E0C7FF9AF2583326ED19AC0BF5B858878D40D91298D042 | |||
| 6828 | SAPPHIRE SPOOFER.exe | C:\Windows\server.crt | text | |
MD5:9A757DFC4212AD866330AE2934A297AA | SHA256:9B290CC789B2133E9FD6BE00C2A3AFE0FFC586708FDEF89B9EA024993264D605 | |||
| 4444 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0schlg4v.2v5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4444 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tya1sq43.pc4.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6828 | SAPPHIRE SPOOFER.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\hellomyboipy[1].txt | text | |
MD5:31AF0296D89E4FB2E072ED930BD11ED3 | SHA256:F9716D589338162E8FAC7B1E286A7FCE2809F9DE6A8DB7704351E0770F27D9A2 | |||
| 6828 | SAPPHIRE SPOOFER.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_49536AB5156BDD74EFF881D01C36A419 | binary | |
MD5:5FA9302EE263AA7AA759664BA2E9571B | SHA256:0E61DB3E8526E9D9A9DF0289ACA929CC9307ABFC0EB168FC2BCBB9BEAF08D76E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
36
DNS requests
19
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6676 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6372 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6828 | SAPPHIRE SPOOFER.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
6676 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6828 | SAPPHIRE SPOOFER.exe | GET | 200 | 52.66.199.95:80 | http://52.66.199.95/server.crt | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
1752 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 2.23.209.149:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6828 | SAPPHIRE SPOOFER.exe | Potential Corporate Privacy Violation | ET POLICY Autoit Windows Automation tool User-Agent in HTTP Request - Possibly Hostile |
1 ETPRO signatures available at the full report