| URL: | https://urldefense.com/v3/__https://a.insgly.net/api/trk?id=emailclick&i=728539&eid=136254895&url=http:**Afmtrack.s2mtraining.com*v1*clk*rDxCyCxeQc2N451FGA-XnA,69pDe2NrTb2BBhvNfbKJnw,0,aHR0cHM6Ly9vZmZpY2UtbWVzc2FnZXMuaW5mby8*ZT1mZXJuaWFueUB1YWIuZWR1__;Ly8vLy8v!!NoSwA-eRAg!UAYxuMWWSPCElw9Iw3Z70rUcuQJB6Wi00xo0gQlT181VBVWP-iAttOlyKapDiKLdRw$ |
| Full analysis: | https://app.any.run/tasks/e632374a-9df5-4ba3-af97-90485c6479ee |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 19:40:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 377FCDAB41749227C893F609771A06E0 |
| SHA1: | ECDD44A609A905EDAC128125DF9FC3F99EFDA629 |
| SHA256: | 1429E161A96EA8EFAA1F9A50847269EAD6590B52E225421C6A852C741EC332E8 |
| SSDEEP: | 6:2UJtIrhVTznMwKTUWTXQ7xRfIGsRRhL47RsjL1bX/rwI1sdla9lDdXYBy:2U0Pz27TkoRhs7W3NXsXdILdoI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3584)
INFO
Reads the computer name
- iexplore.exe (PID: 1968)
- iexplore.exe (PID: 3584)
Changes internet zones settings
- iexplore.exe (PID: 1968)
Application launched itself
- iexplore.exe (PID: 1968)
Checks Windows Trust Settings
- iexplore.exe (PID: 1968)
- iexplore.exe (PID: 3584)
Reads internet explorer settings
- iexplore.exe (PID: 3584)
Creates files in the user directory
- iexplore.exe (PID: 3584)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1968)
Checks supported languages
- iexplore.exe (PID: 1968)
- iexplore.exe (PID: 3584)
Reads settings of System Certificates
- iexplore.exe (PID: 1968)
- iexplore.exe (PID: 3584)
Changes settings of System certificates
- iexplore.exe (PID: 1968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1968 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://urldefense.com/v3/__https://a.insgly.net/api/trk?id=emailclick&i=728539&eid=136254895&url=http:**Afmtrack.s2mtraining.com*v1*clk*rDxCyCxeQc2N451FGA-XnA,69pDe2NrTb2BBhvNfbKJnw,0,aHR0cHM6Ly9vZmZpY2UtbWVzc2FnZXMuaW5mby8*ZT1mZXJuaWFueUB1YWIuZWR1__;Ly8vLy8v!!NoSwA-eRAg!UAYxuMWWSPCElw9Iw3Z70rUcuQJB6Wi00xo0gQlT181VBVWP-iAttOlyKapDiKLdRwf7f81a39-5f63-5b42-9efd-1f13b5431005quot; | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3584 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1968 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
15 367
Read events
15 246
Write events
119
Delete events
2
Modification events
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 702571616 | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30988329 | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30988329 | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1968) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
14
Text files
11
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 1968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\72BA427A91F50409B9EAC87F2B59B951_F0B960C3B1E522BB9772662759982F90 | binary | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | binary | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | binary | |
MD5:— | SHA256:— | |||
| 1968 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_BACC6CD2B29F18349081C9FD2343833B | der | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | der | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:— | SHA256:— | |||
| 3584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B66240B0F6C84BD4857ABA60CF5CE4A0_5043E0F5DF723415C9EECC201C838A62 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
39
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3584 | iexplore.exe | GET | 200 | 13.225.84.175:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3584 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCEA2KFitLH9n0LY9WTWFSpcE%3D | US | der | 471 b | whitelisted |
3584 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 2.18 Kb | whitelisted |
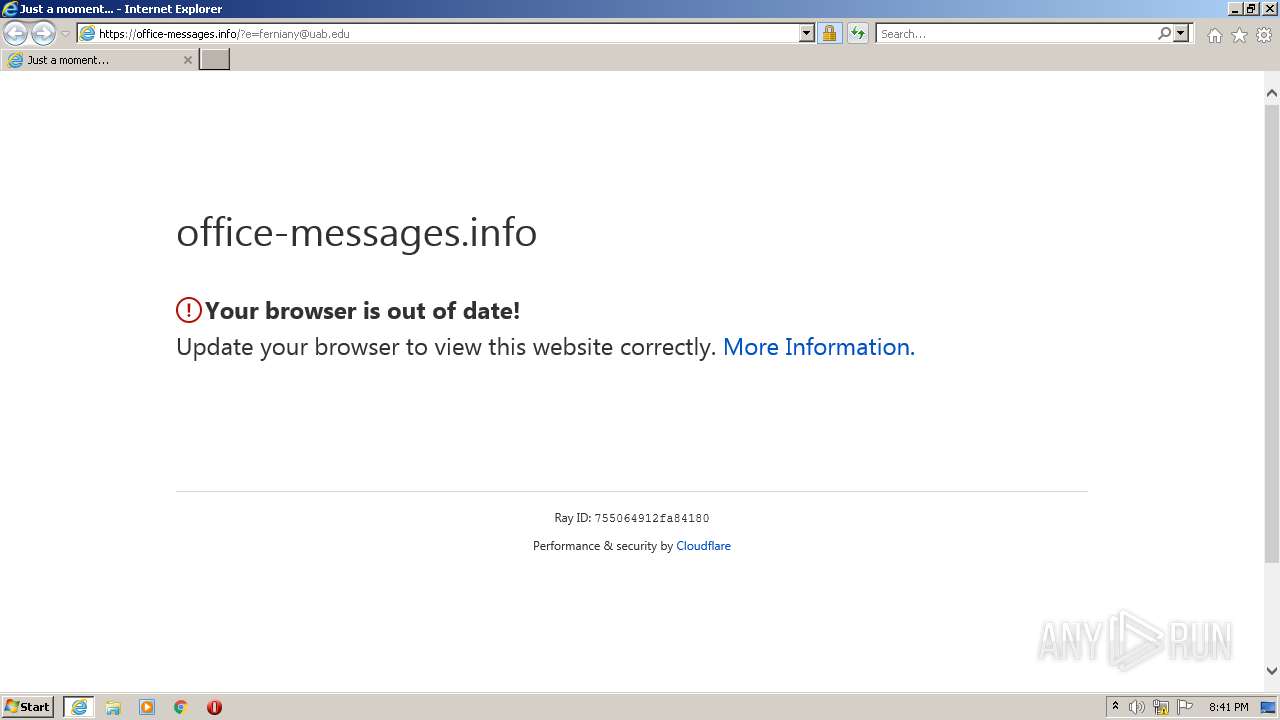
3584 | iexplore.exe | GET | 302 | 13.234.200.109:80 | http://fmtrack.s2mtraining.com/v1/clk/rDxCyCxeQc2N451FGA-XnA,69pDe2NrTb2BBhvNfbKJnw,0,aHR0cHM6Ly9vZmZpY2UtbWVzc2FnZXMuaW5mby8/ZT1mZXJuaWFueUB1YWIuZWR1 | IN | html | 140 b | unknown |
3584 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3584 | iexplore.exe | GET | 200 | 13.225.84.97:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3584 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | US | der | 724 b | whitelisted |
3584 | iexplore.exe | GET | 200 | 13.225.84.88:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAJLG6jYk19jZUe48j76mSc%3D | US | der | 471 b | whitelisted |
1968 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3584 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 1.42 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3584 | iexplore.exe | 52.6.56.188:443 | urldefense.com | AMAZON-AES | US | suspicious |
1968 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
3584 | iexplore.exe | 52.204.90.22:443 | urldefense.com | AMAZON-AES | US | suspicious |
1968 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
1968 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3584 | iexplore.exe | 13.225.84.88:80 | ocsp.sca1b.amazontrust.com | AMAZON-02 | US | whitelisted |
— | — | 13.225.84.13:80 | ocsp.rootg2.amazontrust.com | AMAZON-02 | US | whitelisted |
3584 | iexplore.exe | 188.114.97.3:443 | office-messages.info | CLOUDFLARENET | NL | malicious |
3584 | iexplore.exe | 13.225.78.98:443 | a.insgly.net | AMAZON-02 | US | malicious |
3584 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | CLOUDFLARENET | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
urldefense.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
a.insgly.net |
| shared |
o.ss2.us |
| whitelisted |