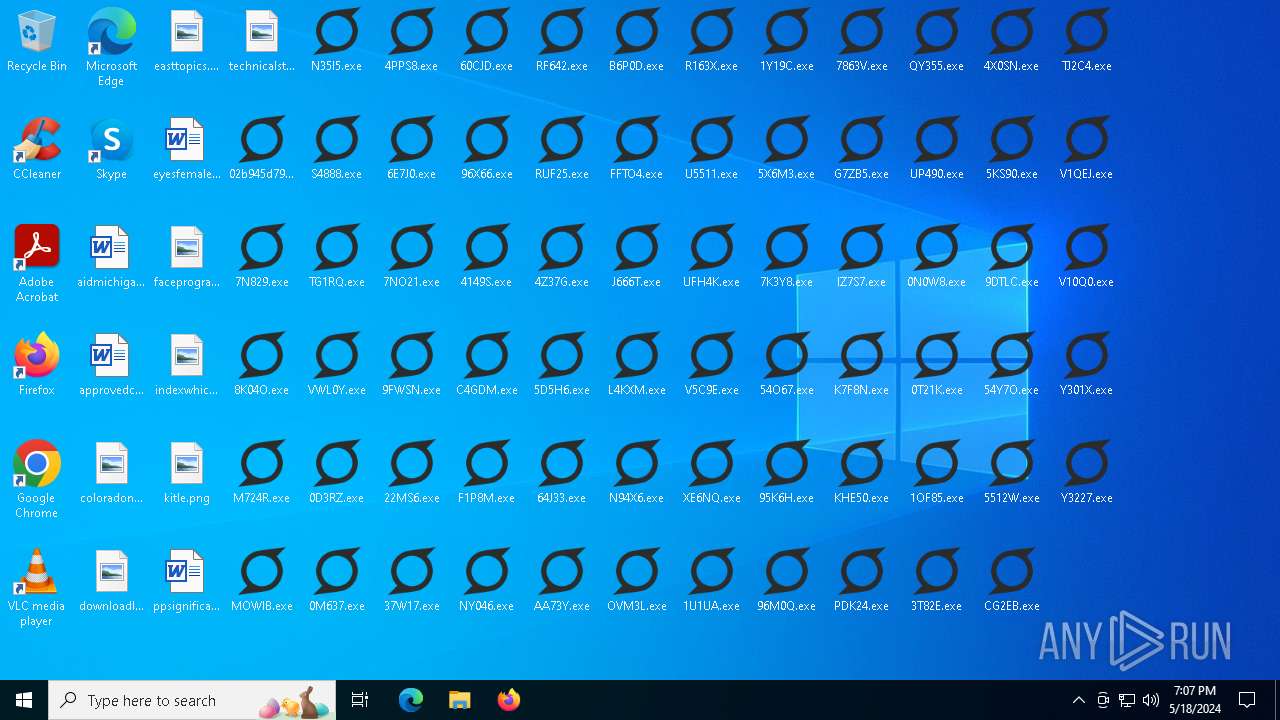
| File name: | 02b945d796fcd22a5d43896a9385f3d0.exe |
| Full analysis: | https://app.any.run/tasks/90155786-b855-44bd-a6e3-2c472cfc9125 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2024, 19:07:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, UPX compressed |
| MD5: | 02B945D796FCD22A5D43896A9385F3D0 |
| SHA1: | 4CF1A499EB163245967BAF43C4537219AD6FF4E4 |
| SHA256: | 141A04CD529DCDC38356796306ED43B3B7DDC579BB7D991ABED989C378948575 |
| SSDEEP: | 49152:lfU00mvij07m88988NtxUaq41JEzw01S2Ss5UZlQ:BU00mvjm2UO1S2Ss58C |
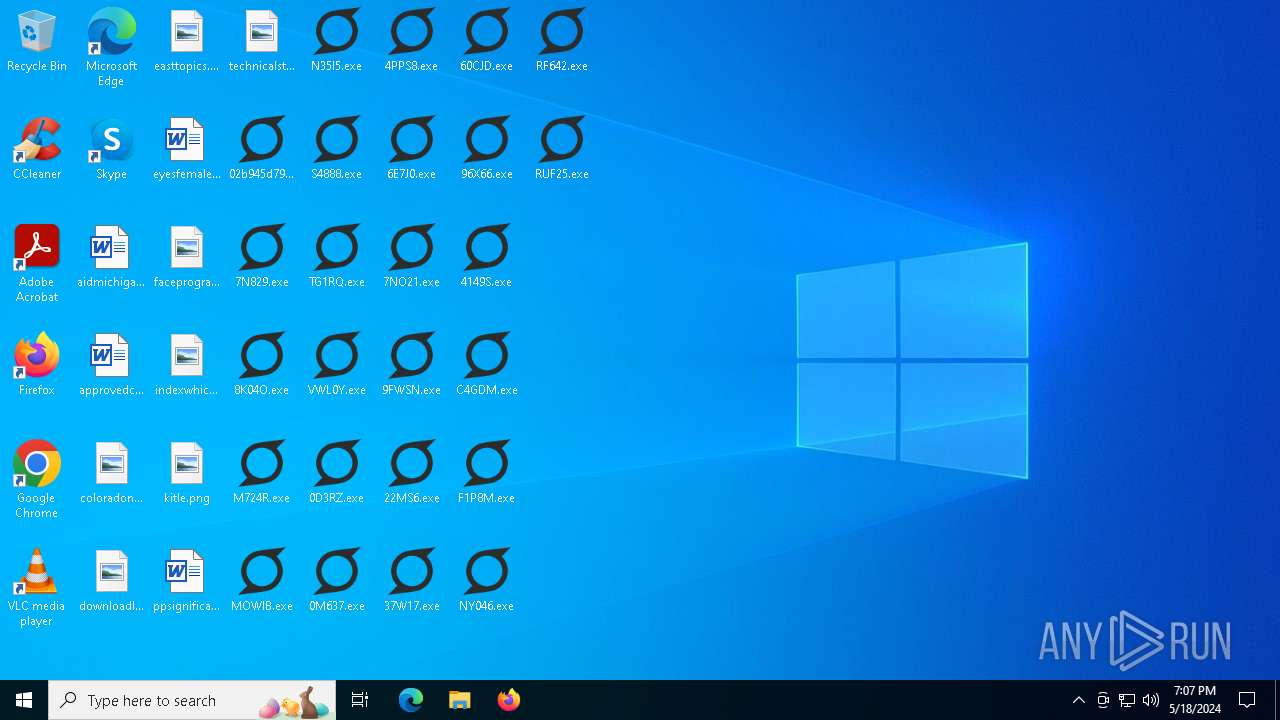
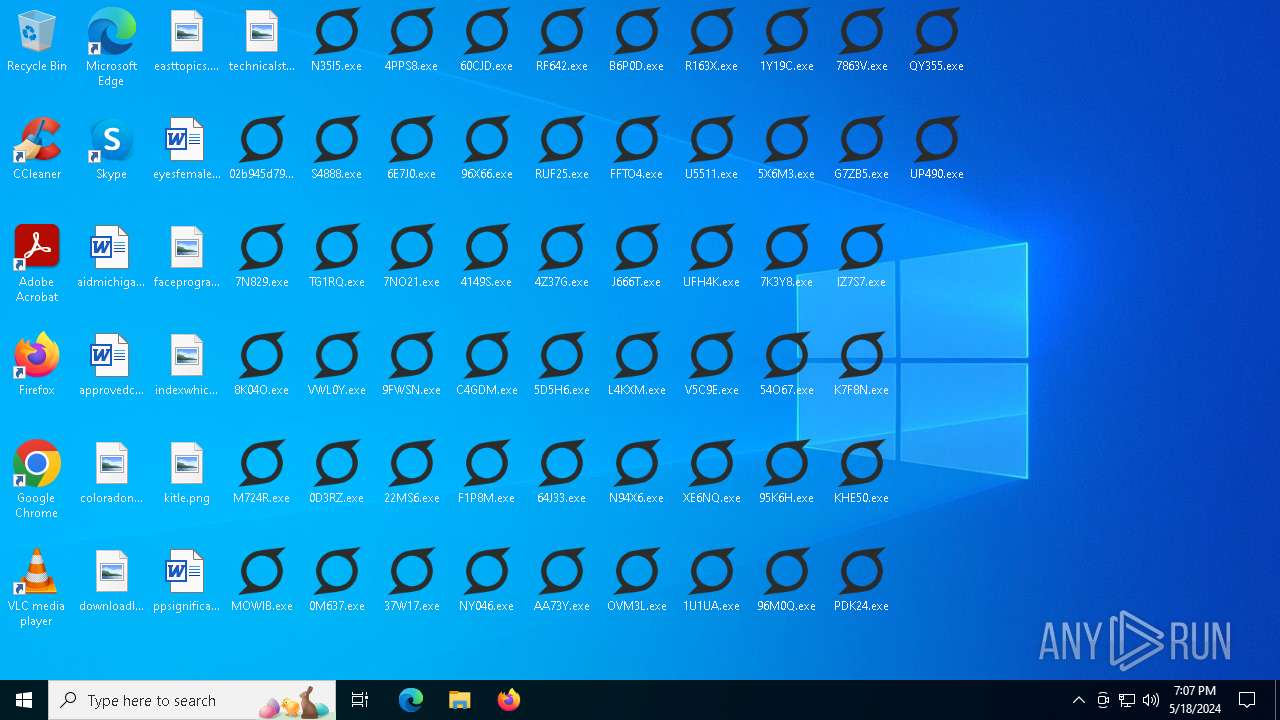
MALICIOUS
Drops the executable file immediately after the start
- powershell.exe (PID: 6292)
- 02b945d796fcd22a5d43896a9385f3d0.exe (PID: 6660)
- 8K04O.exe (PID: 6788)
- M724R.exe (PID: 6852)
- N35I5.exe (PID: 6916)
- VWL0Y.exe (PID: 7040)
- S4888.exe (PID: 7160)
- MOWIB.exe (PID: 6976)
- TG1RQ.exe (PID: 636)
- 7N829.exe (PID: 1752)
- RUF25.exe (PID: 2524)
- 96X66.exe (PID: 1720)
- 60CJD.exe (PID: 5620)
- 6E7J0.exe (PID: 3956)
- 9FWSN.exe (PID: 1712)
- 4149S.exe (PID: 6184)
- 22MS6.exe (PID: 6168)
- 4PPS8.exe (PID: 3712)
- RF642.exe (PID: 6460)
- C4GDM.exe (PID: 3652)
- 37W17.exe (PID: 1572)
- F1P8M.exe (PID: 6556)
- NY046.exe (PID: 6604)
- 0D3RZ.exe (PID: 6656)
- 0M637.exe (PID: 6432)
- 7NO21.exe (PID: 6348)
- V5C9E.exe (PID: 6564)
- L4KXM.exe (PID: 6544)
- FFTO4.exe (PID: 6800)
- J666T.exe (PID: 6876)
- AA73Y.exe (PID: 6932)
- OVM3L.exe (PID: 6980)
- 64J33.exe (PID: 4708)
- 4Z37G.exe (PID: 7116)
- XE6NQ.exe (PID: 1012)
- U5511.exe (PID: 7052)
- B6P0D.exe (PID: 5840)
- N94X6.exe (PID: 1636)
- 5D5H6.exe (PID: 920)
- UFH4K.exe (PID: 4548)
- R163X.exe (PID: 428)
- IZ7S7.exe (PID: 3500)
- 54O67.exe (PID: 3956)
- G7ZB5.exe (PID: 1712)
- 7K3Y8.exe (PID: 4360)
- 1U1UA.exe (PID: 6184)
- KHE50.exe (PID: 3712)
- 5X6M3.exe (PID: 6168)
- K7F8N.exe (PID: 3652)
- 1Y19C.exe (PID: 1572)
- QY355.exe (PID: 6460)
- PDK24.exe (PID: 6356)
- 95K6H.exe (PID: 6620)
- 7863V.exe (PID: 6704)
- UP490.exe (PID: 6332)
- 96M0Q.exe (PID: 6568)
- 1OF85.exe (PID: 6680)
- V1QEJ.exe (PID: 6544)
- 9DTLC.exe (PID: 6856)
- 3T82E.exe (PID: 5552)
- Y3227.exe (PID: 7016)
- 54Y7O.exe (PID: 7136)
- CG2EB.exe (PID: 4232)
- TJ2C4.exe (PID: 7112)
- V10Q0.exe (PID: 1016)
- 5512W.exe (PID: 1412)
- 0N0W8.exe (PID: 3740)
- 5KS90.exe (PID: 5012)
- 4X0SN.exe (PID: 2084)
- 0T21K.exe (PID: 624)
- Y301X.exe (PID: 1428)
- 984K3.exe (PID: 4752)
- TJ1QY.exe (PID: 4148)
- 1D62T.exe (PID: 3692)
- NB0TV.exe (PID: 6148)
- 5V5IZ.exe (PID: 4988)
- Y8U72.exe (PID: 4072)
- E5LC4.exe (PID: 1616)
- 025VG.exe (PID: 6512)
- BZQD7.exe (PID: 6036)
- 6810I.exe (PID: 6364)
- EEO8S.exe (PID: 6408)
- G9V27.exe (PID: 1788)
- O9WE2.exe (PID: 6344)
- 99ZL1.exe (PID: 6688)
- 77712.exe (PID: 6652)
- 711V7.exe (PID: 6888)
- 9V3PZ.exe (PID: 6968)
- QB88D.exe (PID: 6956)
- NHU4R.exe (PID: 7124)
- TX9MD.exe (PID: 7000)
- AEM4R.exe (PID: 7164)
- 4P82A.exe (PID: 7052)
- T7LZ7.exe (PID: 2920)
- SFASV.exe (PID: 1444)
- 986B7.exe (PID: 5924)
- KS0I5.exe (PID: 2084)
- X2726.exe (PID: 5196)
- NPS64.exe (PID: 2484)
- 4O9T8.exe (PID: 4960)
- 6AE1C.exe (PID: 4148)
- HZR1Y.exe (PID: 4752)
- 44WJS.exe (PID: 3724)
- N7R0N.exe (PID: 6220)
- 3BZAL.exe (PID: 5076)
- 16LFW.exe (PID: 6508)
- 87U7P.exe (PID: 6380)
- Z9Z56.exe (PID: 6036)
- 01V42.exe (PID: 324)
- WQ418.exe (PID: 6364)
- 3O9X3.exe (PID: 6404)
- ZM1H7.exe (PID: 6708)
- YM3X2.exe (PID: 6644)
- CI071.exe (PID: 6832)
- 42EZ1.exe (PID: 2600)
- 56SEV.exe (PID: 6960)
- K46TA.exe (PID: 5036)
- 9954Z.exe (PID: 7016)
- 4W0IT.exe (PID: 6996)
- 4WS91.exe (PID: 6740)
- 04076.exe (PID: 4920)
- ZM2KN.exe (PID: 6780)
- G1CB2.exe (PID: 5056)
- 18OM7.exe (PID: 4196)
- 6VN2K.exe (PID: 5904)
- AWJEF.exe (PID: 5196)
- TOI8L.exe (PID: 3688)
- 22OGZ.exe (PID: 5092)
- 0NMLH.exe (PID: 1720)
- 0654P.exe (PID: 5956)
- KL948.exe (PID: 6208)
- 4F4X6.exe (PID: 4160)
- 4B305.exe (PID: 3692)
- A5ZI9.exe (PID: 6244)
- 6T8NY.exe (PID: 5004)
- 5EJSO.exe (PID: 6508)
- TOY05.exe (PID: 5076)
- 9IU9X.exe (PID: 6428)
- 5556W.exe (PID: 6036)
- EV7AO.exe (PID: 6372)
- 8X41S.exe (PID: 6756)
- WE52B.exe (PID: 6348)
- XU9T1.exe (PID: 6716)
- 70O52.exe (PID: 6856)
- FGRMG.exe (PID: 4288)
- J7661.exe (PID: 6544)
- ICQ0E.exe (PID: 5036)
- HJB1G.exe (PID: 6984)
- LXSLE.exe (PID: 6980)
- 1I18S.exe (PID: 4024)
- 3FFMR.exe (PID: 6740)
- DZB8M.exe (PID: 3740)
- 80EQ4.exe (PID: 4384)
- 57D53.exe (PID: 4704)
- I7G22.exe (PID: 1944)
- 85007.exe (PID: 3820)
- 01CH8.exe (PID: 5196)
- 2E1Y3.exe (PID: 3956)
- IL366.exe (PID: 2480)
- 4VB81.exe (PID: 2084)
- C605X.exe (PID: 6188)
- D64AQ.exe (PID: 1120)
- N991U.exe (PID: 6288)
- 9031Q.exe (PID: 3104)
- HF7S5.exe (PID: 6448)
- K3VR8.exe (PID: 6560)
- 03553.exe (PID: 2916)
- K3YNW.exe (PID: 6396)
- 7UEBK.exe (PID: 364)
- B30WC.exe (PID: 6364)
- 8OA0O.exe (PID: 1788)
- DN635.exe (PID: 6528)
- 927G1.exe (PID: 6860)
- R0OE4.exe (PID: 6660)
- SSN20.exe (PID: 2396)
- 6IY2Z.exe (PID: 6788)
- U7JAA.exe (PID: 7020)
- 10W8W.exe (PID: 6996)
- S9403.exe (PID: 7140)
- B4YQ1.exe (PID: 7120)
- OYH7Y.exe (PID: 7032)
- R3G15.exe (PID: 7164)
- 74C91.exe (PID: 4928)
- DNFUA.exe (PID: 1100)
- 56ISU.exe (PID: 6108)
- H7221.exe (PID: 712)
- 907V7.exe (PID: 1428)
- 73875.exe (PID: 5372)
- O624I.exe (PID: 4484)
- AC1C4.exe (PID: 3500)
- 4T6WK.exe (PID: 6216)
- PQ12M.exe (PID: 4160)
- 365H2.exe (PID: 3960)
- OA72T.exe (PID: 4416)
- S60O0.exe (PID: 7072)
- 79476.exe (PID: 1604)
- LP845.exe (PID: 5396)
- PL6GL.exe (PID: 4500)
- 29X1Z.exe (PID: 6360)
- 04OHX.exe (PID: 6368)
- 58N6V.exe (PID: 6804)
- L4ZXZ.exe (PID: 6420)
- 9TMG1.exe (PID: 6908)
- Q1BAQ.exe (PID: 6540)
- H3VN5.exe (PID: 6880)
- WG1B7.exe (PID: 6972)
- 218P8.exe (PID: 1364)
- H1062.exe (PID: 1684)
- 657LD.exe (PID: 2684)
- 440KC.exe (PID: 6968)
- 4550G.exe (PID: 7000)
- Q0D99.exe (PID: 6784)
- 88OC4.exe (PID: 4024)
- X45W2.exe (PID: 5840)
- E28H6.exe (PID: 628)
- 54676.exe (PID: 1360)
- Z04H5.exe (PID: 1412)
- 900FK.exe (PID: 5720)
- D3Z0L.exe (PID: 6016)
- 24N9H.exe (PID: 2524)
- ITBP2.exe (PID: 5716)
- AVP68.exe (PID: 5936)
- JQX44.exe (PID: 5932)
- 49IS2.exe (PID: 4744)
- E3WGD.exe (PID: 3712)
- MNE8L.exe (PID: 1120)
- PJVCB.exe (PID: 3652)
- KU8HX.exe (PID: 4540)
- 0584N.exe (PID: 4140)
- MP9TW.exe (PID: 6560)
- 8W6R3.exe (PID: 5448)
- QM881.exe (PID: 4500)
- 2F2D3.exe (PID: 6424)
- TQ9J4.exe (PID: 6304)
- 42OLV.exe (PID: 6336)
- WEA53.exe (PID: 6732)
- Q2YBF.exe (PID: 6664)
- 92J0G.exe (PID: 6892)
- SKUOI.exe (PID: 6864)
- 6K4Q2.exe (PID: 7008)
- 5Z891.exe (PID: 6852)
- T78X0.exe (PID: 4312)
- 8G52R.exe (PID: 6496)
- YTYEA.exe (PID: 7020)
- V15ZZ.exe (PID: 7160)
- 2116Y.exe (PID: 6780)
- PK2F1.exe (PID: 7120)
- QI699.exe (PID: 5836)
- N0M02.exe (PID: 2796)
- S74IS.exe (PID: 4628)
- 276YT.exe (PID: 3052)
- V723N.exe (PID: 5920)
- W9609.exe (PID: 624)
- 378S4.exe (PID: 3500)
- 0F1R3.exe (PID: 5372)
- Y90VV.exe (PID: 4284)
- 8B952.exe (PID: 5148)
- D6W0N.exe (PID: 6316)
- 66LAL.exe (PID: 4492)
- 0I313.exe (PID: 5592)
- Q8W2L.exe (PID: 4072)
- YY598.exe (PID: 4140)
- 8F0F2.exe (PID: 5752)
- 9A9Q6.exe (PID: 6560)
- 8L8RH.exe (PID: 5448)
- 1IWE3.exe (PID: 5896)
- D6U26.exe (PID: 4500)
- D1297.exe (PID: 6364)
- D1BGI.exe (PID: 6828)
- 39YZ2.exe (PID: 6748)
- 3Y47A.exe (PID: 6928)
- TQBTR.exe (PID: 6532)
- 5COD3.exe (PID: 1512)
- MIA45.exe (PID: 2396)
- R3C14.exe (PID: 6272)
- 91U26.exe (PID: 7048)
- U8873.exe (PID: 6980)
- 78MU5.exe (PID: 3624)
- OY7FM.exe (PID: 1568)
- 5W26I.exe (PID: 5504)
- B581C.exe (PID: 6204)
- 911MO.exe (PID: 4920)
- VR6V2.exe (PID: 5064)
- 4JAG8.exe (PID: 5428)
- I4KI1.exe (PID: 2448)
- 1H060.exe (PID: 5904)
- 64VPY.exe (PID: 1724)
- DAB9M.exe (PID: 3688)
- 7UXSQ.exe (PID: 3956)
- 22W50.exe (PID: 6112)
- E8XAX.exe (PID: 4752)
- VV4I9.exe (PID: 6440)
- UUG01.exe (PID: 6308)
- J4Z28.exe (PID: 3808)
- 4SJ9O.exe (PID: 6148)
- P17LK.exe (PID: 6376)
- 9564H.exe (PID: 6640)
- A52HG.exe (PID: 4480)
- 3L0V2.exe (PID: 6356)
- 3OXE1.exe (PID: 6696)
- IUJ23.exe (PID: 6036)
- V4T76.exe (PID: 6756)
- UMI08.exe (PID: 6704)
- 578OY.exe (PID: 6800)
- 8UWQ3.exe (PID: 6900)
- 209JO.exe (PID: 7128)
- JF52M.exe (PID: 6956)
- K1582.exe (PID: 7024)
- 3C1Y2.exe (PID: 6964)
- 2OHZ2.exe (PID: 72)
- 4A165.exe (PID: 7112)
- EMUJU.exe (PID: 4056)
- BPD2E.exe (PID: 7152)
- 372V7.exe (PID: 920)
- IAL9T.exe (PID: 4916)
- M92AK.exe (PID: 5380)
- 57J9P.exe (PID: 2736)
- K5W7B.exe (PID: 1720)
- 2MITN.exe (PID: 4996)
- 79VU8.exe (PID: 3672)
- 2Y8G5.exe (PID: 2084)
- A1588.exe (PID: 372)
- 1NG25.exe (PID: 3956)
- MZ756.exe (PID: 4744)
- 28RHB.exe (PID: 2104)
- 8T5W7.exe (PID: 6168)
- 484O0.exe (PID: 1628)
- R71UH.exe (PID: 2336)
- 6734R.exe (PID: 7076)
- S77ZS.exe (PID: 6444)
- 6O2P1.exe (PID: 5960)
- C68Q1.exe (PID: 892)
- 0K35Y.exe (PID: 3732)
- D272S.exe (PID: 6376)
- QJ8Z3.exe (PID: 6512)
- E41LT.exe (PID: 4140)
- 2MZ2Q.exe (PID: 6556)
- HF969.exe (PID: 6352)
- 628E6.exe (PID: 5812)
- 9H4EX.exe (PID: 4612)
- 560K5.exe (PID: 4560)
- TJ7S5.exe (PID: 6368)
- Y1HQL.exe (PID: 6536)
- LTN7A.exe (PID: 6564)
- 152U6.exe (PID: 6464)
- 663MU.exe (PID: 6644)
- FSFC1.exe (PID: 6928)
- GII08.exe (PID: 4156)
- 8436V.exe (PID: 5208)
- A2EW5.exe (PID: 6776)
- ZKTPC.exe (PID: 1512)
- 9RM7K.exe (PID: 7000)
- 3N095.exe (PID: 7024)
- IY10Q.exe (PID: 4748)
- 67U4K.exe (PID: 7116)
- L9W60.exe (PID: 4020)
- E2KX5.exe (PID: 1016)
- 81GL1.exe (PID: 2252)
- FHSP4.exe (PID: 712)
- Z1RSM.exe (PID: 4952)
- 068DL.exe (PID: 6156)
- TKQ3J.exe (PID: 2620)
- 8480V.exe (PID: 5084)
- 089T7.exe (PID: 1508)
- B85MZ.exe (PID: 1648)
- 4S733.exe (PID: 6216)
- U9365.exe (PID: 6164)
- U8V9I.exe (PID: 1792)
- OJEV0.exe (PID: 2220)
- V8G6K.exe (PID: 6188)
- DBCMM.exe (PID: 6440)
- 68RFL.exe (PID: 6248)
- ZY185.exe (PID: 4540)
- K55BB.exe (PID: 3100)
- 5IVAU.exe (PID: 3412)
- S9M3S.exe (PID: 5656)
- 6305L.exe (PID: 6632)
- CVM16.exe (PID: 6592)
- 8XO1K.exe (PID: 6512)
- K5TT2.exe (PID: 4232)
- E2ZYL.exe (PID: 6344)
- G0OLR.exe (PID: 6296)
- 4ZD4X.exe (PID: 6084)
- 94704.exe (PID: 5304)
- EM8T0.exe (PID: 4560)
- K5299.exe (PID: 6304)
- 1O366.exe (PID: 6660)
- VPYHF.exe (PID: 6564)
- 941WE.exe (PID: 6644)
- 345DF.exe (PID: 6464)
- 4RWER.exe (PID: 5080)
- 39Q8V.exe (PID: 7132)
- TN94I.exe (PID: 6104)
- 69327.exe (PID: 4708)
- 26GP2.exe (PID: 3708)
- J4H9Z.exe (PID: 6760)
- F3P05.exe (PID: 4196)
- KH3F7.exe (PID: 7116)
- 6X74A.exe (PID: 4748)
- 2013B.exe (PID: 4020)
- 06MPS.exe (PID: 1016)
- X630B.exe (PID: 2252)
- 56795.exe (PID: 4952)
- LSVR6.exe (PID: 712)
- ODDV0.exe (PID: 32)
- 20GY4.exe (PID: 3688)
- 624BS.exe (PID: 5464)
- F96VK.exe (PID: 5444)
- 6922J.exe (PID: 3644)
- G331I.exe (PID: 6184)
- W833D.exe (PID: 5256)
- I378K.exe (PID: 2044)
- 2HF5B.exe (PID: 2308)
- Z7HM4.exe (PID: 3104)
- 0EWX4.exe (PID: 924)
- A7S01.exe (PID: 6440)
- AHNPY.exe (PID: 608)
- 97C14.exe (PID: 6148)
- 6YYWZ.exe (PID: 3756)
- 148Q3.exe (PID: 6816)
- 7444I.exe (PID: 2384)
- H49G5.exe (PID: 4036)
- 6M3A4.exe (PID: 4500)
- 8Q395.exe (PID: 6408)
- 015P1.exe (PID: 4152)
- 59CT2.exe (PID: 4532)
- O194N.exe (PID: 5896)
- 5FDRF.exe (PID: 5356)
- PQ42C.exe (PID: 6304)
- 4YKUD.exe (PID: 6708)
- L71O9.exe (PID: 6876)
- 2M418.exe (PID: 1492)
- P3GK8.exe (PID: 6956)
- 41263.exe (PID: 7028)
- I5FF3.exe (PID: 5072)
- 0K586.exe (PID: 4264)
- 8C0ZP.exe (PID: 7016)
- QL8WT.exe (PID: 5608)
- 8CUGN.exe (PID: 1488)
- 7N28X.exe (PID: 4488)
- 58X31.exe (PID: 1276)
- AOWJF.exe (PID: 5056)
- 2WOYO.exe (PID: 6548)
- P64A3.exe (PID: 4700)
- 98N83.exe (PID: 6108)
- KC51T.exe (PID: 6012)
- F0NQ8.exe (PID: 724)
- 26907.exe (PID: 5244)
- 31891.exe (PID: 6160)
- UJDI0.exe (PID: 1308)
- 48SB3.exe (PID: 368)
- 0M3WI.exe (PID: 5528)
- IW0KW.exe (PID: 4200)
- 4W23G.exe (PID: 5956)
- 931VD.exe (PID: 6208)
- R060H.exe (PID: 1808)
- V7776.exe (PID: 4160)
- YM6X3.exe (PID: 7076)
- 4W274.exe (PID: 532)
- 8O029.exe (PID: 4988)
- J042A.exe (PID: 4012)
- 18S8U.exe (PID: 3912)
- G0ANK.exe (PID: 1616)
- RFYJI.exe (PID: 6396)
- K3RP1.exe (PID: 2800)
- 11GI2.exe (PID: 2072)
- N7TA3.exe (PID: 6568)
- 34F17.exe (PID: 5448)
- 7W983.exe (PID: 4664)
- PRP6L.exe (PID: 5812)
- 517UZ.exe (PID: 6368)
- U42RD.exe (PID: 5304)
- UP1EQ.exe (PID: 6900)
- O81OI.exe (PID: 6856)
- 5CWSP.exe (PID: 928)
- E4GW8.exe (PID: 6916)
- 1PR86.exe (PID: 6852)
- GNC73.exe (PID: 5280)
- 907YG.exe (PID: 4288)
- 0562G.exe (PID: 7040)
- S09NQ.exe (PID: 5632)
- YA3ZA.exe (PID: 7052)
- Z7870.exe (PID: 3940)
- LVB60.exe (PID: 6744)
- C2QR9.exe (PID: 6764)
- UYQQ1.exe (PID: 6796)
- ZLS8S.exe (PID: 4384)
- 0JE0W.exe (PID: 5012)
- 1SLJB.exe (PID: 5920)
- 9GC6R.exe (PID: 3528)
- 092JI.exe (PID: 2536)
- 1511H.exe (PID: 1084)
- G94ZJ.exe (PID: 5716)
- ZK2DO.exe (PID: 3768)
- G9X52.exe (PID: 1748)
- 6PMI3.exe (PID: 4536)
- NT82L.exe (PID: 588)
- 68757.exe (PID: 3016)
- 7W3C2.exe (PID: 2744)
- C8Z9R.exe (PID: 2328)
- Z2752.exe (PID: 2932)
- 0FKRR.exe (PID: 3628)
- UVWWD.exe (PID: 6080)
- VT48N.exe (PID: 5960)
- 2R0EK.exe (PID: 6380)
- 3M9PJ.exe (PID: 3704)
- 26X40.exe (PID: 6780)
- XK1C3.exe (PID: 736)
- 38WPW.exe (PID: 6588)
- 96TZ2.exe (PID: 6484)
- 40S7S.exe (PID: 6556)
- H0DTU.exe (PID: 4668)
- 1Y8YQ.exe (PID: 6432)
- K6E5T.exe (PID: 6724)
- 0U8K3.exe (PID: 6840)
- 0W2Z8.exe (PID: 6948)
- C3OU8.exe (PID: 1492)
- 6BR15.exe (PID: 3648)
- W0MZX.exe (PID: 5088)
- 18YX1.exe (PID: 6788)
- 5XAYS.exe (PID: 7156)
- 22ELF.exe (PID: 7036)
- Z882J.exe (PID: 7020)
- 1D453.exe (PID: 5900)
- 5E8AY.exe (PID: 2920)
- C3KMH.exe (PID: 4920)
- LC22S.exe (PID: 6300)
- W3K13.exe (PID: 1360)
- JQH0B.exe (PID: 2252)
- I5E12.exe (PID: 1752)
- X1GXY.exe (PID: 2736)
- 27SJC.exe (PID: 4952)
- XWCT0.exe (PID: 3528)
- 7PR46.exe (PID: 1832)
- 58182.exe (PID: 5716)
- CB7Y4.exe (PID: 2536)
- 23NUQ.exe (PID: 3768)
- I1KNP.exe (PID: 1084)
- NQQR1.exe (PID: 6216)
- NFQ3K.exe (PID: 4536)
- P7EFE.exe (PID: 588)
- 3Y066.exe (PID: 3016)
- 273TK.exe (PID: 532)
- 39PMG.exe (PID: 2328)
- SBL81.exe (PID: 7076)
- 59OG9.exe (PID: 3628)
- V1YN9.exe (PID: 4012)
- 98R0N.exe (PID: 7120)
- 2GJ2G.exe (PID: 1616)
- 4KIX1.exe (PID: 6752)
- 3718U.exe (PID: 6520)
- ZJB54.exe (PID: 6088)
- CGSA2.exe (PID: 6340)
- 8FGC3.exe (PID: 5336)
- I4V63.exe (PID: 5360)
- J52RX.exe (PID: 6732)
- 057K9.exe (PID: 6692)
- 4SA2F.exe (PID: 6756)
- ZUY5E.exe (PID: 6708)
- K9QML.exe (PID: 6976)
- SAQM6.exe (PID: 5116)
- 2X000.exe (PID: 6992)
- 34J90.exe (PID: 7036)
- 0SXNW.exe (PID: 5900)
- USQL5.exe (PID: 5088)
- 68B13.exe (PID: 6788)
- 9671S.exe (PID: 7156)
- WZ7U2.exe (PID: 1100)
- 6GH45.exe (PID: 4196)
- 1C52V.exe (PID: 1744)
- 5DWMN.exe (PID: 1444)
- FP04U.exe (PID: 6548)
SUSPICIOUS
Reads the date of Windows installation
- 02b945d796fcd22a5d43896a9385f3d0.exe (PID: 6660)
- 8K04O.exe (PID: 6788)
- M724R.exe (PID: 6852)
- N35I5.exe (PID: 6916)
- S4888.exe (PID: 7160)
- MOWIB.exe (PID: 6976)
- VWL0Y.exe (PID: 7040)
- TG1RQ.exe (PID: 636)
- RUF25.exe (PID: 2524)
- 96X66.exe (PID: 1720)
- 7N829.exe (PID: 1752)
- 60CJD.exe (PID: 5620)
- 6E7J0.exe (PID: 3956)
- 9FWSN.exe (PID: 1712)
- 4149S.exe (PID: 6184)
- 22MS6.exe (PID: 6168)
- 4PPS8.exe (PID: 3712)
- RF642.exe (PID: 6460)
- C4GDM.exe (PID: 3652)
- 37W17.exe (PID: 1572)
- F1P8M.exe (PID: 6556)
- NY046.exe (PID: 6604)
- 0D3RZ.exe (PID: 6656)
- 7NO21.exe (PID: 6348)
- V5C9E.exe (PID: 6564)
- 0M637.exe (PID: 6432)
- L4KXM.exe (PID: 6544)
- FFTO4.exe (PID: 6800)
- J666T.exe (PID: 6876)
- AA73Y.exe (PID: 6932)
- 64J33.exe (PID: 4708)
- OVM3L.exe (PID: 6980)
- 4Z37G.exe (PID: 7116)
- U5511.exe (PID: 7052)
- N94X6.exe (PID: 1636)
- B6P0D.exe (PID: 5840)
- XE6NQ.exe (PID: 1012)
- 5D5H6.exe (PID: 920)
- UFH4K.exe (PID: 4548)
- R163X.exe (PID: 428)
- IZ7S7.exe (PID: 3500)
- 7K3Y8.exe (PID: 4360)
- G7ZB5.exe (PID: 1712)
- 54O67.exe (PID: 3956)
- 1U1UA.exe (PID: 6184)
- KHE50.exe (PID: 3712)
- 5X6M3.exe (PID: 6168)
- K7F8N.exe (PID: 3652)
- 1Y19C.exe (PID: 1572)
- QY355.exe (PID: 6460)
- 95K6H.exe (PID: 6620)
- PDK24.exe (PID: 6356)
- 96M0Q.exe (PID: 6568)
- 7863V.exe (PID: 6704)
- UP490.exe (PID: 6332)
- V1QEJ.exe (PID: 6544)
- 1OF85.exe (PID: 6680)
- 9DTLC.exe (PID: 6856)
- 3T82E.exe (PID: 5552)
- Y3227.exe (PID: 7016)
- 54Y7O.exe (PID: 7136)
- TJ2C4.exe (PID: 7112)
- CG2EB.exe (PID: 4232)
- V10Q0.exe (PID: 1016)
- 0N0W8.exe (PID: 3740)
- 5KS90.exe (PID: 5012)
- 5512W.exe (PID: 1412)
- Y301X.exe (PID: 1428)
- 0T21K.exe (PID: 624)
- 4X0SN.exe (PID: 2084)
- 984K3.exe (PID: 4752)
- TJ1QY.exe (PID: 4148)
- 1D62T.exe (PID: 3692)
- NB0TV.exe (PID: 6148)
- Y8U72.exe (PID: 4072)
- E5LC4.exe (PID: 1616)
- 5V5IZ.exe (PID: 4988)
- BZQD7.exe (PID: 6036)
- 025VG.exe (PID: 6512)
- G9V27.exe (PID: 1788)
- 6810I.exe (PID: 6364)
- EEO8S.exe (PID: 6408)
- O9WE2.exe (PID: 6344)
- 99ZL1.exe (PID: 6688)
- 77712.exe (PID: 6652)
- 711V7.exe (PID: 6888)
- 9V3PZ.exe (PID: 6968)
- QB88D.exe (PID: 6956)
- TX9MD.exe (PID: 7000)
- NHU4R.exe (PID: 7124)
- AEM4R.exe (PID: 7164)
- 4P82A.exe (PID: 7052)
- SFASV.exe (PID: 1444)
- T7LZ7.exe (PID: 2920)
- 986B7.exe (PID: 5924)
- X2726.exe (PID: 5196)
- KS0I5.exe (PID: 2084)
- NPS64.exe (PID: 2484)
- 4O9T8.exe (PID: 4960)
- HZR1Y.exe (PID: 4752)
- 6AE1C.exe (PID: 4148)
- 44WJS.exe (PID: 3724)
- N7R0N.exe (PID: 6220)
- 3BZAL.exe (PID: 5076)
- 87U7P.exe (PID: 6380)
- Z9Z56.exe (PID: 6036)
- 01V42.exe (PID: 324)
- 16LFW.exe (PID: 6508)
- WQ418.exe (PID: 6364)
- 3O9X3.exe (PID: 6404)
- ZM1H7.exe (PID: 6708)
- YM3X2.exe (PID: 6644)
- 42EZ1.exe (PID: 2600)
- CI071.exe (PID: 6832)
- 56SEV.exe (PID: 6960)
- K46TA.exe (PID: 5036)
- 4W0IT.exe (PID: 6996)
- 9954Z.exe (PID: 7016)
- 4WS91.exe (PID: 6740)
- ZM2KN.exe (PID: 6780)
- 18OM7.exe (PID: 4196)
- G1CB2.exe (PID: 5056)
- 04076.exe (PID: 4920)
- 6VN2K.exe (PID: 5904)
- AWJEF.exe (PID: 5196)
- 0NMLH.exe (PID: 1720)
- TOI8L.exe (PID: 3688)
- 22OGZ.exe (PID: 5092)
- 0654P.exe (PID: 5956)
- 4F4X6.exe (PID: 4160)
- 4B305.exe (PID: 3692)
- KL948.exe (PID: 6208)
- A5ZI9.exe (PID: 6244)
- 6T8NY.exe (PID: 5004)
- TOY05.exe (PID: 5076)
- 5EJSO.exe (PID: 6508)
- 5556W.exe (PID: 6036)
- 9IU9X.exe (PID: 6428)
- EV7AO.exe (PID: 6372)
- 8X41S.exe (PID: 6756)
- WE52B.exe (PID: 6348)
- XU9T1.exe (PID: 6716)
- J7661.exe (PID: 6544)
- 70O52.exe (PID: 6856)
- FGRMG.exe (PID: 4288)
- ICQ0E.exe (PID: 5036)
- HJB1G.exe (PID: 6984)
- LXSLE.exe (PID: 6980)
- 1I18S.exe (PID: 4024)
- DZB8M.exe (PID: 3740)
- 80EQ4.exe (PID: 4384)
- 3FFMR.exe (PID: 6740)
- 57D53.exe (PID: 4704)
- I7G22.exe (PID: 1944)
- 01CH8.exe (PID: 5196)
- 85007.exe (PID: 3820)
- 2E1Y3.exe (PID: 3956)
- 4VB81.exe (PID: 2084)
- C605X.exe (PID: 6188)
- D64AQ.exe (PID: 1120)
- IL366.exe (PID: 2480)
- N991U.exe (PID: 6288)
- 9031Q.exe (PID: 3104)
- HF7S5.exe (PID: 6448)
- K3VR8.exe (PID: 6560)
- 03553.exe (PID: 2916)
- K3YNW.exe (PID: 6396)
- 7UEBK.exe (PID: 364)
- 8OA0O.exe (PID: 1788)
- B30WC.exe (PID: 6364)
- DN635.exe (PID: 6528)
- R0OE4.exe (PID: 6660)
- 6IY2Z.exe (PID: 6788)
- SSN20.exe (PID: 2396)
- 927G1.exe (PID: 6860)
- U7JAA.exe (PID: 7020)
- 10W8W.exe (PID: 6996)
- OYH7Y.exe (PID: 7032)
- S9403.exe (PID: 7140)
- B4YQ1.exe (PID: 7120)
- R3G15.exe (PID: 7164)
- 56ISU.exe (PID: 6108)
- 74C91.exe (PID: 4928)
- DNFUA.exe (PID: 1100)
- H7221.exe (PID: 712)
- 907V7.exe (PID: 1428)
- AC1C4.exe (PID: 3500)
- 73875.exe (PID: 5372)
- O624I.exe (PID: 4484)
- 4T6WK.exe (PID: 6216)
- PQ12M.exe (PID: 4160)
- OA72T.exe (PID: 4416)
- S60O0.exe (PID: 7072)
- 365H2.exe (PID: 3960)
- LP845.exe (PID: 5396)
- PL6GL.exe (PID: 4500)
- 79476.exe (PID: 1604)
- 29X1Z.exe (PID: 6360)
- L4ZXZ.exe (PID: 6420)
- 58N6V.exe (PID: 6804)
- 04OHX.exe (PID: 6368)
- Q1BAQ.exe (PID: 6540)
- 9TMG1.exe (PID: 6908)
- H3VN5.exe (PID: 6880)
- WG1B7.exe (PID: 6972)
- H1062.exe (PID: 1684)
- 218P8.exe (PID: 1364)
- 657LD.exe (PID: 2684)
- 440KC.exe (PID: 6968)
- 4550G.exe (PID: 7000)
- 88OC4.exe (PID: 4024)
- Q0D99.exe (PID: 6784)
- X45W2.exe (PID: 5840)
- E28H6.exe (PID: 628)
- 54676.exe (PID: 1360)
- Z04H5.exe (PID: 1412)
- 900FK.exe (PID: 5720)
- 24N9H.exe (PID: 2524)
- D3Z0L.exe (PID: 6016)
- ITBP2.exe (PID: 5716)
- AVP68.exe (PID: 5936)
- JQX44.exe (PID: 5932)
- 49IS2.exe (PID: 4744)
- E3WGD.exe (PID: 3712)
- MNE8L.exe (PID: 1120)
- PJVCB.exe (PID: 3652)
- KU8HX.exe (PID: 4540)
- 0584N.exe (PID: 4140)
- MP9TW.exe (PID: 6560)
- 8W6R3.exe (PID: 5448)
- QM881.exe (PID: 4500)
- 2F2D3.exe (PID: 6424)
- TQ9J4.exe (PID: 6304)
- 42OLV.exe (PID: 6336)
- WEA53.exe (PID: 6732)
- Q2YBF.exe (PID: 6664)
- SKUOI.exe (PID: 6864)
- 92J0G.exe (PID: 6892)
- 5Z891.exe (PID: 6852)
- T78X0.exe (PID: 4312)
- 6K4Q2.exe (PID: 7008)
- 8G52R.exe (PID: 6496)
- YTYEA.exe (PID: 7020)
- 2116Y.exe (PID: 6780)
- PK2F1.exe (PID: 7120)
- V15ZZ.exe (PID: 7160)
- QI699.exe (PID: 5836)
- N0M02.exe (PID: 2796)
- 276YT.exe (PID: 3052)
- S74IS.exe (PID: 4628)
- V723N.exe (PID: 5920)
- W9609.exe (PID: 624)
- 0F1R3.exe (PID: 5372)
- 378S4.exe (PID: 3500)
- Y90VV.exe (PID: 4284)
- 8B952.exe (PID: 5148)
- D6W0N.exe (PID: 6316)
- 66LAL.exe (PID: 4492)
- 0I313.exe (PID: 5592)
- Q8W2L.exe (PID: 4072)
- 8F0F2.exe (PID: 5752)
- YY598.exe (PID: 4140)
- 9A9Q6.exe (PID: 6560)
- 8L8RH.exe (PID: 5448)
- D6U26.exe (PID: 4500)
- D1297.exe (PID: 6364)
- 1IWE3.exe (PID: 5896)
- D1BGI.exe (PID: 6828)
- 39YZ2.exe (PID: 6748)
- 3Y47A.exe (PID: 6928)
- TQBTR.exe (PID: 6532)
- 5COD3.exe (PID: 1512)
- MIA45.exe (PID: 2396)
- 91U26.exe (PID: 7048)
- R3C14.exe (PID: 6272)
- 78MU5.exe (PID: 3624)
- U8873.exe (PID: 6980)
- 5W26I.exe (PID: 5504)
- OY7FM.exe (PID: 1568)
- B581C.exe (PID: 6204)
- 911MO.exe (PID: 4920)
- 4JAG8.exe (PID: 5428)
- 1H060.exe (PID: 5904)
- VR6V2.exe (PID: 5064)
- 64VPY.exe (PID: 1724)
- I4KI1.exe (PID: 2448)
- 7UXSQ.exe (PID: 3956)
- DAB9M.exe (PID: 3688)
- 22W50.exe (PID: 6112)
- E8XAX.exe (PID: 4752)
- VV4I9.exe (PID: 6440)
- J4Z28.exe (PID: 3808)
- UUG01.exe (PID: 6308)
- 4SJ9O.exe (PID: 6148)
- A52HG.exe (PID: 4480)
- P17LK.exe (PID: 6376)
- 3L0V2.exe (PID: 6356)
- 9564H.exe (PID: 6640)
- IUJ23.exe (PID: 6036)
- 3OXE1.exe (PID: 6696)
- V4T76.exe (PID: 6756)
- UMI08.exe (PID: 6704)
- 8UWQ3.exe (PID: 6900)
- 578OY.exe (PID: 6800)
- JF52M.exe (PID: 6956)
- 209JO.exe (PID: 7128)
- K1582.exe (PID: 7024)
- 3C1Y2.exe (PID: 6964)
- 2OHZ2.exe (PID: 72)
- 4A165.exe (PID: 7112)
- EMUJU.exe (PID: 4056)
- BPD2E.exe (PID: 7152)
- 372V7.exe (PID: 920)
- IAL9T.exe (PID: 4916)
- M92AK.exe (PID: 5380)
- 57J9P.exe (PID: 2736)
- K5W7B.exe (PID: 1720)
- 2MITN.exe (PID: 4996)
- 79VU8.exe (PID: 3672)
- 2Y8G5.exe (PID: 2084)
- A1588.exe (PID: 372)
- 1NG25.exe (PID: 3956)
- 28RHB.exe (PID: 2104)
- 484O0.exe (PID: 1628)
- MZ756.exe (PID: 4744)
- R71UH.exe (PID: 2336)
- 8T5W7.exe (PID: 6168)
- S77ZS.exe (PID: 6444)
- 6734R.exe (PID: 7076)
- 6O2P1.exe (PID: 5960)
- C68Q1.exe (PID: 892)
- D272S.exe (PID: 6376)
- 0K35Y.exe (PID: 3732)
- E41LT.exe (PID: 4140)
- HF969.exe (PID: 6352)
- 2MZ2Q.exe (PID: 6556)
- QJ8Z3.exe (PID: 6512)
- 9H4EX.exe (PID: 4612)
- 560K5.exe (PID: 4560)
- 628E6.exe (PID: 5812)
- TJ7S5.exe (PID: 6368)
- Y1HQL.exe (PID: 6536)
- 663MU.exe (PID: 6644)
- LTN7A.exe (PID: 6564)
- FSFC1.exe (PID: 6928)
- 152U6.exe (PID: 6464)
- 8436V.exe (PID: 5208)
- GII08.exe (PID: 4156)
- A2EW5.exe (PID: 6776)
- ZKTPC.exe (PID: 1512)
- 3N095.exe (PID: 7024)
- 67U4K.exe (PID: 7116)
- L9W60.exe (PID: 4020)
- IY10Q.exe (PID: 4748)
- 81GL1.exe (PID: 2252)
- E2KX5.exe (PID: 1016)
- FHSP4.exe (PID: 712)
- Z1RSM.exe (PID: 4952)
- TKQ3J.exe (PID: 2620)
- 8480V.exe (PID: 5084)
- 068DL.exe (PID: 6156)
- B85MZ.exe (PID: 1648)
- 089T7.exe (PID: 1508)
- U9365.exe (PID: 6164)
- 4S733.exe (PID: 6216)
- OJEV0.exe (PID: 2220)
- V8G6K.exe (PID: 6188)
- U8V9I.exe (PID: 1792)
- DBCMM.exe (PID: 6440)
- 68RFL.exe (PID: 6248)
- K55BB.exe (PID: 3100)
- ZY185.exe (PID: 4540)
- 5IVAU.exe (PID: 3412)
- S9M3S.exe (PID: 5656)
- 6305L.exe (PID: 6632)
- CVM16.exe (PID: 6592)
- 8XO1K.exe (PID: 6512)
- K5TT2.exe (PID: 4232)
- E2ZYL.exe (PID: 6344)
- G0OLR.exe (PID: 6296)
- 4ZD4X.exe (PID: 6084)
- 94704.exe (PID: 5304)
- EM8T0.exe (PID: 4560)
- K5299.exe (PID: 6304)
- 1O366.exe (PID: 6660)
- VPYHF.exe (PID: 6564)
- 941WE.exe (PID: 6644)
- 345DF.exe (PID: 6464)
- 39Q8V.exe (PID: 7132)
- TN94I.exe (PID: 6104)
- 4RWER.exe (PID: 5080)
- 69327.exe (PID: 4708)
- J4H9Z.exe (PID: 6760)
- 26GP2.exe (PID: 3708)
- F3P05.exe (PID: 4196)
- 6X74A.exe (PID: 4748)
- KH3F7.exe (PID: 7116)
- 2013B.exe (PID: 4020)
- X630B.exe (PID: 2252)
- 06MPS.exe (PID: 1016)
- LSVR6.exe (PID: 712)
- 56795.exe (PID: 4952)
- 20GY4.exe (PID: 3688)
- 624BS.exe (PID: 5464)
- ODDV0.exe (PID: 32)
- 6922J.exe (PID: 3644)
- G331I.exe (PID: 6184)
- F96VK.exe (PID: 5444)
- I378K.exe (PID: 2044)
- 2HF5B.exe (PID: 2308)
- W833D.exe (PID: 5256)
- 0EWX4.exe (PID: 924)
- A7S01.exe (PID: 6440)
- Z7HM4.exe (PID: 3104)
- 97C14.exe (PID: 6148)
- 6YYWZ.exe (PID: 3756)
- AHNPY.exe (PID: 608)
- 7444I.exe (PID: 2384)
- 148Q3.exe (PID: 6816)
- H49G5.exe (PID: 4036)
- 8Q395.exe (PID: 6408)
- 6M3A4.exe (PID: 4500)
- 015P1.exe (PID: 4152)
- O194N.exe (PID: 5896)
- 59CT2.exe (PID: 4532)
- 5FDRF.exe (PID: 5356)
- PQ42C.exe (PID: 6304)
- 4YKUD.exe (PID: 6708)
- 2M418.exe (PID: 1492)
- P3GK8.exe (PID: 6956)
- L71O9.exe (PID: 6876)
- 41263.exe (PID: 7028)
- I5FF3.exe (PID: 5072)
- 8C0ZP.exe (PID: 7016)
- 0K586.exe (PID: 4264)
- QL8WT.exe (PID: 5608)
- 7N28X.exe (PID: 4488)
- 58X31.exe (PID: 1276)
- 8CUGN.exe (PID: 1488)
- AOWJF.exe (PID: 5056)
- 2WOYO.exe (PID: 6548)
- P64A3.exe (PID: 4700)
- 98N83.exe (PID: 6108)
- KC51T.exe (PID: 6012)
- F0NQ8.exe (PID: 724)
- 26907.exe (PID: 5244)
- 31891.exe (PID: 6160)
- 48SB3.exe (PID: 368)
- UJDI0.exe (PID: 1308)
- 0M3WI.exe (PID: 5528)
- IW0KW.exe (PID: 4200)
- 4W23G.exe (PID: 5956)
- R060H.exe (PID: 1808)
- V7776.exe (PID: 4160)
- 931VD.exe (PID: 6208)
- 4W274.exe (PID: 532)
- 8O029.exe (PID: 4988)
- YM6X3.exe (PID: 7076)
- J042A.exe (PID: 4012)
- G0ANK.exe (PID: 1616)
- 18S8U.exe (PID: 3912)
- RFYJI.exe (PID: 6396)
- K3RP1.exe (PID: 2800)
- 11GI2.exe (PID: 2072)
- 34F17.exe (PID: 5448)
- N7TA3.exe (PID: 6568)
- 7W983.exe (PID: 4664)
- PRP6L.exe (PID: 5812)
- U42RD.exe (PID: 5304)
- 517UZ.exe (PID: 6368)
- UP1EQ.exe (PID: 6900)
- 9RM7K.exe (PID: 7000)
- 5CWSP.exe (PID: 928)
- E4GW8.exe (PID: 6916)
- O81OI.exe (PID: 6856)
- 1PR86.exe (PID: 6852)
- 907YG.exe (PID: 4288)
- GNC73.exe (PID: 5280)
- S09NQ.exe (PID: 5632)
- YA3ZA.exe (PID: 7052)
- 0562G.exe (PID: 7040)
- LVB60.exe (PID: 6744)
- Z7870.exe (PID: 3940)
- UYQQ1.exe (PID: 6796)
- C2QR9.exe (PID: 6764)
- ZLS8S.exe (PID: 4384)
- 0JE0W.exe (PID: 5012)
- 1SLJB.exe (PID: 5920)
- 092JI.exe (PID: 2536)
- 9GC6R.exe (PID: 3528)
- G94ZJ.exe (PID: 5716)
- ZK2DO.exe (PID: 3768)
- 1511H.exe (PID: 1084)
- G9X52.exe (PID: 1748)
- 6PMI3.exe (PID: 4536)
- NT82L.exe (PID: 588)
- 68757.exe (PID: 3016)
- C8Z9R.exe (PID: 2328)
- Z2752.exe (PID: 2932)
- 7W3C2.exe (PID: 2744)
- UVWWD.exe (PID: 6080)
- 0FKRR.exe (PID: 3628)
- 2R0EK.exe (PID: 6380)
- 3M9PJ.exe (PID: 3704)
- VT48N.exe (PID: 5960)
- XK1C3.exe (PID: 736)
- 26X40.exe (PID: 6780)
- 38WPW.exe (PID: 6588)
- 96TZ2.exe (PID: 6484)
- 40S7S.exe (PID: 6556)
- H0DTU.exe (PID: 4668)
- 1Y8YQ.exe (PID: 6432)
- K6E5T.exe (PID: 6724)
- 0U8K3.exe (PID: 6840)
- 0W2Z8.exe (PID: 6948)
- 6BR15.exe (PID: 3648)
- C3OU8.exe (PID: 1492)
- 18YX1.exe (PID: 6788)
- W0MZX.exe (PID: 5088)
- 5XAYS.exe (PID: 7156)
- 22ELF.exe (PID: 7036)
- 1D453.exe (PID: 5900)
- Z882J.exe (PID: 7020)
- C3KMH.exe (PID: 4920)
- 5E8AY.exe (PID: 2920)
- W3K13.exe (PID: 1360)
- LC22S.exe (PID: 6300)
- I5E12.exe (PID: 1752)
- JQH0B.exe (PID: 2252)
- 27SJC.exe (PID: 4952)
- X1GXY.exe (PID: 2736)
- 7PR46.exe (PID: 1832)
- XWCT0.exe (PID: 3528)
- 58182.exe (PID: 5716)
- CB7Y4.exe (PID: 2536)
- I1KNP.exe (PID: 1084)
- 23NUQ.exe (PID: 3768)
- NFQ3K.exe (PID: 4536)
- NQQR1.exe (PID: 6216)
- P7EFE.exe (PID: 588)
- 3Y066.exe (PID: 3016)
- 39PMG.exe (PID: 2328)
- 273TK.exe (PID: 532)
- SBL81.exe (PID: 7076)
- V1YN9.exe (PID: 4012)
- 59OG9.exe (PID: 3628)
- 98R0N.exe (PID: 7120)
- 2GJ2G.exe (PID: 1616)
- 3718U.exe (PID: 6520)
- 4KIX1.exe (PID: 6752)
- ZJB54.exe (PID: 6088)
- CGSA2.exe (PID: 6340)
- I4V63.exe (PID: 5360)
- 8FGC3.exe (PID: 5336)
- 057K9.exe (PID: 6692)
- J52RX.exe (PID: 6732)
- 4SA2F.exe (PID: 6756)
- ZUY5E.exe (PID: 6708)
- 2X000.exe (PID: 6992)
Executable content was dropped or overwritten
- 02b945d796fcd22a5d43896a9385f3d0.exe (PID: 6660)
- 8K04O.exe (PID: 6788)
- M724R.exe (PID: 6852)
- N35I5.exe (PID: 6916)
- VWL0Y.exe (PID: 7040)
- S4888.exe (PID: 7160)
- MOWIB.exe (PID: 6976)
- TG1RQ.exe (PID: 636)
- 7N829.exe (PID: 1752)
- 96X66.exe (PID: 1720)
- RUF25.exe (PID: 2524)
- 6E7J0.exe (PID: 3956)
- 60CJD.exe (PID: 5620)
- 9FWSN.exe (PID: 1712)
- 4149S.exe (PID: 6184)
- 22MS6.exe (PID: 6168)
- 4PPS8.exe (PID: 3712)
- RF642.exe (PID: 6460)
- C4GDM.exe (PID: 3652)
- F1P8M.exe (PID: 6556)
- 37W17.exe (PID: 1572)
- 0D3RZ.exe (PID: 6656)
- 0M637.exe (PID: 6432)
- NY046.exe (PID: 6604)
- 7NO21.exe (PID: 6348)
- V5C9E.exe (PID: 6564)
- L4KXM.exe (PID: 6544)
- FFTO4.exe (PID: 6800)
- J666T.exe (PID: 6876)
- AA73Y.exe (PID: 6932)
- OVM3L.exe (PID: 6980)
- 64J33.exe (PID: 4708)
- 4Z37G.exe (PID: 7116)
- XE6NQ.exe (PID: 1012)
- U5511.exe (PID: 7052)
- N94X6.exe (PID: 1636)
- B6P0D.exe (PID: 5840)
- 5D5H6.exe (PID: 920)
- UFH4K.exe (PID: 4548)
- R163X.exe (PID: 428)
- 7K3Y8.exe (PID: 4360)
- IZ7S7.exe (PID: 3500)
- 54O67.exe (PID: 3956)
- G7ZB5.exe (PID: 1712)
- 1U1UA.exe (PID: 6184)
- KHE50.exe (PID: 3712)
- K7F8N.exe (PID: 3652)
- 5X6M3.exe (PID: 6168)
- 1Y19C.exe (PID: 1572)
- QY355.exe (PID: 6460)
- PDK24.exe (PID: 6356)
- 95K6H.exe (PID: 6620)
- UP490.exe (PID: 6332)
- 7863V.exe (PID: 6704)
- 96M0Q.exe (PID: 6568)
- 1OF85.exe (PID: 6680)
- V1QEJ.exe (PID: 6544)
- 9DTLC.exe (PID: 6856)
- 3T82E.exe (PID: 5552)
- 54Y7O.exe (PID: 7136)
- Y3227.exe (PID: 7016)
- CG2EB.exe (PID: 4232)
- 0N0W8.exe (PID: 3740)
- TJ2C4.exe (PID: 7112)
- V10Q0.exe (PID: 1016)
- 5KS90.exe (PID: 5012)
- 4X0SN.exe (PID: 2084)
- 5512W.exe (PID: 1412)
- Y301X.exe (PID: 1428)
- 0T21K.exe (PID: 624)
- 984K3.exe (PID: 4752)
- TJ1QY.exe (PID: 4148)
- 1D62T.exe (PID: 3692)
- NB0TV.exe (PID: 6148)
- 5V5IZ.exe (PID: 4988)
- Y8U72.exe (PID: 4072)
- E5LC4.exe (PID: 1616)
- BZQD7.exe (PID: 6036)
- 025VG.exe (PID: 6512)
- G9V27.exe (PID: 1788)
- 6810I.exe (PID: 6364)
- EEO8S.exe (PID: 6408)
- O9WE2.exe (PID: 6344)
- 99ZL1.exe (PID: 6688)
- 77712.exe (PID: 6652)
- 711V7.exe (PID: 6888)
- 9V3PZ.exe (PID: 6968)
- QB88D.exe (PID: 6956)
- NHU4R.exe (PID: 7124)
- TX9MD.exe (PID: 7000)
- AEM4R.exe (PID: 7164)
- SFASV.exe (PID: 1444)
- 4P82A.exe (PID: 7052)
- T7LZ7.exe (PID: 2920)
- 986B7.exe (PID: 5924)
- KS0I5.exe (PID: 2084)
- X2726.exe (PID: 5196)
- NPS64.exe (PID: 2484)
- 4O9T8.exe (PID: 4960)
- 6AE1C.exe (PID: 4148)
- HZR1Y.exe (PID: 4752)
- 44WJS.exe (PID: 3724)
- N7R0N.exe (PID: 6220)
- 87U7P.exe (PID: 6380)
- 3BZAL.exe (PID: 5076)
- 16LFW.exe (PID: 6508)
- Z9Z56.exe (PID: 6036)
- 01V42.exe (PID: 324)
- WQ418.exe (PID: 6364)
- 3O9X3.exe (PID: 6404)
- ZM1H7.exe (PID: 6708)
- YM3X2.exe (PID: 6644)
- CI071.exe (PID: 6832)
- 42EZ1.exe (PID: 2600)
- K46TA.exe (PID: 5036)
- 56SEV.exe (PID: 6960)
- 9954Z.exe (PID: 7016)
- ZM2KN.exe (PID: 6780)
- 4W0IT.exe (PID: 6996)
- 4WS91.exe (PID: 6740)
- 04076.exe (PID: 4920)
- 18OM7.exe (PID: 4196)
- G1CB2.exe (PID: 5056)
- 6VN2K.exe (PID: 5904)
- AWJEF.exe (PID: 5196)
- TOI8L.exe (PID: 3688)
- 22OGZ.exe (PID: 5092)
- 0NMLH.exe (PID: 1720)
- 0654P.exe (PID: 5956)
- KL948.exe (PID: 6208)
- 4F4X6.exe (PID: 4160)
- 4B305.exe (PID: 3692)
- 6T8NY.exe (PID: 5004)
- A5ZI9.exe (PID: 6244)
- 5EJSO.exe (PID: 6508)
- TOY05.exe (PID: 5076)
- 9IU9X.exe (PID: 6428)
- 5556W.exe (PID: 6036)
- EV7AO.exe (PID: 6372)
- 8X41S.exe (PID: 6756)
- WE52B.exe (PID: 6348)
- XU9T1.exe (PID: 6716)
- J7661.exe (PID: 6544)
- 70O52.exe (PID: 6856)
- FGRMG.exe (PID: 4288)
- ICQ0E.exe (PID: 5036)
- HJB1G.exe (PID: 6984)
- LXSLE.exe (PID: 6980)
- 1I18S.exe (PID: 4024)
- 3FFMR.exe (PID: 6740)
- 80EQ4.exe (PID: 4384)
- DZB8M.exe (PID: 3740)
- I7G22.exe (PID: 1944)
- 57D53.exe (PID: 4704)
- 85007.exe (PID: 3820)
- 01CH8.exe (PID: 5196)
- 2E1Y3.exe (PID: 3956)
- IL366.exe (PID: 2480)
- 4VB81.exe (PID: 2084)
- C605X.exe (PID: 6188)
- D64AQ.exe (PID: 1120)
- N991U.exe (PID: 6288)
- 9031Q.exe (PID: 3104)
- HF7S5.exe (PID: 6448)
- K3VR8.exe (PID: 6560)
- 03553.exe (PID: 2916)
- K3YNW.exe (PID: 6396)
- 7UEBK.exe (PID: 364)
- B30WC.exe (PID: 6364)
- R0OE4.exe (PID: 6660)
- 8OA0O.exe (PID: 1788)
- DN635.exe (PID: 6528)
- 927G1.exe (PID: 6860)
- SSN20.exe (PID: 2396)
- 6IY2Z.exe (PID: 6788)
- U7JAA.exe (PID: 7020)
- 10W8W.exe (PID: 6996)
- OYH7Y.exe (PID: 7032)
- S9403.exe (PID: 7140)
- R3G15.exe (PID: 7164)
- 74C91.exe (PID: 4928)
- B4YQ1.exe (PID: 7120)
- DNFUA.exe (PID: 1100)
- 56ISU.exe (PID: 6108)
- H7221.exe (PID: 712)
- 907V7.exe (PID: 1428)
- 73875.exe (PID: 5372)
- AC1C4.exe (PID: 3500)
- 4T6WK.exe (PID: 6216)
- OA72T.exe (PID: 4416)
- O624I.exe (PID: 4484)
- PQ12M.exe (PID: 4160)
- 365H2.exe (PID: 3960)
- 79476.exe (PID: 1604)
- S60O0.exe (PID: 7072)
- PL6GL.exe (PID: 4500)
- LP845.exe (PID: 5396)
- 04OHX.exe (PID: 6368)
- 29X1Z.exe (PID: 6360)
- L4ZXZ.exe (PID: 6420)
- 58N6V.exe (PID: 6804)
- Q1BAQ.exe (PID: 6540)
- 9TMG1.exe (PID: 6908)
- H3VN5.exe (PID: 6880)
- WG1B7.exe (PID: 6972)
- 218P8.exe (PID: 1364)
- H1062.exe (PID: 1684)
- 657LD.exe (PID: 2684)
- 440KC.exe (PID: 6968)
- 4550G.exe (PID: 7000)
- Q0D99.exe (PID: 6784)
- 88OC4.exe (PID: 4024)
- X45W2.exe (PID: 5840)
- E28H6.exe (PID: 628)
- 54676.exe (PID: 1360)
- Z04H5.exe (PID: 1412)
- D3Z0L.exe (PID: 6016)
- 24N9H.exe (PID: 2524)
- 900FK.exe (PID: 5720)
- ITBP2.exe (PID: 5716)
- AVP68.exe (PID: 5936)
- JQX44.exe (PID: 5932)
- 49IS2.exe (PID: 4744)
- E3WGD.exe (PID: 3712)
- MNE8L.exe (PID: 1120)
- PJVCB.exe (PID: 3652)
- KU8HX.exe (PID: 4540)
- 0584N.exe (PID: 4140)
- MP9TW.exe (PID: 6560)
- 8W6R3.exe (PID: 5448)
- QM881.exe (PID: 4500)
- 2F2D3.exe (PID: 6424)
- TQ9J4.exe (PID: 6304)
- 42OLV.exe (PID: 6336)
- WEA53.exe (PID: 6732)
- Q2YBF.exe (PID: 6664)
- SKUOI.exe (PID: 6864)
- 92J0G.exe (PID: 6892)
- 5Z891.exe (PID: 6852)
- 6K4Q2.exe (PID: 7008)
- T78X0.exe (PID: 4312)
- 8G52R.exe (PID: 6496)
- YTYEA.exe (PID: 7020)
- V15ZZ.exe (PID: 7160)
- 2116Y.exe (PID: 6780)
- QI699.exe (PID: 5836)
- PK2F1.exe (PID: 7120)
- N0M02.exe (PID: 2796)
- 276YT.exe (PID: 3052)
- V723N.exe (PID: 5920)
- S74IS.exe (PID: 4628)
- W9609.exe (PID: 624)
- 0F1R3.exe (PID: 5372)
- 378S4.exe (PID: 3500)
- Y90VV.exe (PID: 4284)
- 8B952.exe (PID: 5148)
- 66LAL.exe (PID: 4492)
- D6W0N.exe (PID: 6316)
- 0I313.exe (PID: 5592)
- Q8W2L.exe (PID: 4072)
- YY598.exe (PID: 4140)
- 8F0F2.exe (PID: 5752)
- 9A9Q6.exe (PID: 6560)
- 8L8RH.exe (PID: 5448)
- 1IWE3.exe (PID: 5896)
- D6U26.exe (PID: 4500)
- D1297.exe (PID: 6364)
- 39YZ2.exe (PID: 6748)
- D1BGI.exe (PID: 6828)
- 3Y47A.exe (PID: 6928)
- MIA45.exe (PID: 2396)
- TQBTR.exe (PID: 6532)
- 5COD3.exe (PID: 1512)
- 91U26.exe (PID: 7048)
- R3C14.exe (PID: 6272)
- U8873.exe (PID: 6980)
- 78MU5.exe (PID: 3624)
- OY7FM.exe (PID: 1568)
- 5W26I.exe (PID: 5504)
- B581C.exe (PID: 6204)
- 911MO.exe (PID: 4920)
- 4JAG8.exe (PID: 5428)
- VR6V2.exe (PID: 5064)
- 1H060.exe (PID: 5904)
- I4KI1.exe (PID: 2448)
- 64VPY.exe (PID: 1724)
- DAB9M.exe (PID: 3688)
- 7UXSQ.exe (PID: 3956)
- 22W50.exe (PID: 6112)
- E8XAX.exe (PID: 4752)
- VV4I9.exe (PID: 6440)
- UUG01.exe (PID: 6308)
- J4Z28.exe (PID: 3808)
- 4SJ9O.exe (PID: 6148)
- P17LK.exe (PID: 6376)
- A52HG.exe (PID: 4480)
- 9564H.exe (PID: 6640)
- IUJ23.exe (PID: 6036)
- 3L0V2.exe (PID: 6356)
- 3OXE1.exe (PID: 6696)
- V4T76.exe (PID: 6756)
- UMI08.exe (PID: 6704)
- 578OY.exe (PID: 6800)
- 8UWQ3.exe (PID: 6900)
- 209JO.exe (PID: 7128)
- JF52M.exe (PID: 6956)
- K1582.exe (PID: 7024)
- 3C1Y2.exe (PID: 6964)
- 2OHZ2.exe (PID: 72)
- 4A165.exe (PID: 7112)
- EMUJU.exe (PID: 4056)
- BPD2E.exe (PID: 7152)
- 372V7.exe (PID: 920)
- IAL9T.exe (PID: 4916)
- M92AK.exe (PID: 5380)
- 57J9P.exe (PID: 2736)
- 2MITN.exe (PID: 4996)
- K5W7B.exe (PID: 1720)
- 79VU8.exe (PID: 3672)
- 2Y8G5.exe (PID: 2084)
- A1588.exe (PID: 372)
- 1NG25.exe (PID: 3956)
- MZ756.exe (PID: 4744)
- 28RHB.exe (PID: 2104)
- 484O0.exe (PID: 1628)
- 8T5W7.exe (PID: 6168)
- 6734R.exe (PID: 7076)
- R71UH.exe (PID: 2336)
- S77ZS.exe (PID: 6444)
- 6O2P1.exe (PID: 5960)
- C68Q1.exe (PID: 892)
- D272S.exe (PID: 6376)
- 0K35Y.exe (PID: 3732)
- QJ8Z3.exe (PID: 6512)
- E41LT.exe (PID: 4140)
- 2MZ2Q.exe (PID: 6556)
- HF969.exe (PID: 6352)
- 9H4EX.exe (PID: 4612)
- 628E6.exe (PID: 5812)
- 560K5.exe (PID: 4560)
- TJ7S5.exe (PID: 6368)
- LTN7A.exe (PID: 6564)
- Y1HQL.exe (PID: 6536)
- 663MU.exe (PID: 6644)
- 152U6.exe (PID: 6464)
- GII08.exe (PID: 4156)
- FSFC1.exe (PID: 6928)
- 8436V.exe (PID: 5208)
- A2EW5.exe (PID: 6776)
- ZKTPC.exe (PID: 1512)
- 9RM7K.exe (PID: 7000)
- 3N095.exe (PID: 7024)
- IY10Q.exe (PID: 4748)
- 67U4K.exe (PID: 7116)
- L9W60.exe (PID: 4020)
- E2KX5.exe (PID: 1016)
- 81GL1.exe (PID: 2252)
- FHSP4.exe (PID: 712)
- Z1RSM.exe (PID: 4952)
- TKQ3J.exe (PID: 2620)
- 068DL.exe (PID: 6156)
- 8480V.exe (PID: 5084)
- B85MZ.exe (PID: 1648)
- 089T7.exe (PID: 1508)
- 4S733.exe (PID: 6216)
- U9365.exe (PID: 6164)
- U8V9I.exe (PID: 1792)
- OJEV0.exe (PID: 2220)
- 68RFL.exe (PID: 6248)
- V8G6K.exe (PID: 6188)
- ZY185.exe (PID: 4540)
- K55BB.exe (PID: 3100)
- 5IVAU.exe (PID: 3412)
- S9M3S.exe (PID: 5656)
- 6305L.exe (PID: 6632)
- K5TT2.exe (PID: 4232)
- CVM16.exe (PID: 6592)
- 8XO1K.exe (PID: 6512)
- E2ZYL.exe (PID: 6344)
- G0OLR.exe (PID: 6296)
- 4ZD4X.exe (PID: 6084)
- 94704.exe (PID: 5304)
- EM8T0.exe (PID: 4560)
- K5299.exe (PID: 6304)
- 1O366.exe (PID: 6660)
- VPYHF.exe (PID: 6564)
- 941WE.exe (PID: 6644)
- 345DF.exe (PID: 6464)
- 4RWER.exe (PID: 5080)
- 39Q8V.exe (PID: 7132)
- TN94I.exe (PID: 6104)
- 26GP2.exe (PID: 3708)
- 69327.exe (PID: 4708)
- J4H9Z.exe (PID: 6760)
- KH3F7.exe (PID: 7116)
- F3P05.exe (PID: 4196)
- 6X74A.exe (PID: 4748)
- 06MPS.exe (PID: 1016)
- 2013B.exe (PID: 4020)
- X630B.exe (PID: 2252)
- 56795.exe (PID: 4952)
- LSVR6.exe (PID: 712)
- 20GY4.exe (PID: 3688)
- 624BS.exe (PID: 5464)
- ODDV0.exe (PID: 32)
- 6922J.exe (PID: 3644)
- G331I.exe (PID: 6184)
- F96VK.exe (PID: 5444)
- W833D.exe (PID: 5256)
- I378K.exe (PID: 2044)
- 2HF5B.exe (PID: 2308)
- Z7HM4.exe (PID: 3104)
- 0EWX4.exe (PID: 924)
- A7S01.exe (PID: 6440)
- AHNPY.exe (PID: 608)
- 97C14.exe (PID: 6148)
- 6YYWZ.exe (PID: 3756)
- 148Q3.exe (PID: 6816)
- 7444I.exe (PID: 2384)
- H49G5.exe (PID: 4036)
- 6M3A4.exe (PID: 4500)
- 8Q395.exe (PID: 6408)
- 015P1.exe (PID: 4152)
- O194N.exe (PID: 5896)
- 59CT2.exe (PID: 4532)
- 5FDRF.exe (PID: 5356)
- PQ42C.exe (PID: 6304)
- 2M418.exe (PID: 1492)
- 4YKUD.exe (PID: 6708)
- L71O9.exe (PID: 6876)
- P3GK8.exe (PID: 6956)
- 41263.exe (PID: 7028)
- I5FF3.exe (PID: 5072)
- 0K586.exe (PID: 4264)
- 8C0ZP.exe (PID: 7016)
- QL8WT.exe (PID: 5608)
- 7N28X.exe (PID: 4488)
- 58X31.exe (PID: 1276)
- 8CUGN.exe (PID: 1488)
- AOWJF.exe (PID: 5056)
- 2WOYO.exe (PID: 6548)
- 98N83.exe (PID: 6108)
- P64A3.exe (PID: 4700)
- 26907.exe (PID: 5244)
- KC51T.exe (PID: 6012)
- F0NQ8.exe (PID: 724)
- 31891.exe (PID: 6160)
- 48SB3.exe (PID: 368)
- 0M3WI.exe (PID: 5528)
- UJDI0.exe (PID: 1308)
- IW0KW.exe (PID: 4200)
- 4W23G.exe (PID: 5956)
- 931VD.exe (PID: 6208)
- R060H.exe (PID: 1808)
- V7776.exe (PID: 4160)
- YM6X3.exe (PID: 7076)
- 4W274.exe (PID: 532)
- 8O029.exe (PID: 4988)
- J042A.exe (PID: 4012)
- 18S8U.exe (PID: 3912)
- G0ANK.exe (PID: 1616)
- 11GI2.exe (PID: 2072)
- RFYJI.exe (PID: 6396)
- K3RP1.exe (PID: 2800)
- 34F17.exe (PID: 5448)
- 7W983.exe (PID: 4664)
- N7TA3.exe (PID: 6568)
- PRP6L.exe (PID: 5812)
- U42RD.exe (PID: 5304)
- 517UZ.exe (PID: 6368)
- UP1EQ.exe (PID: 6900)
- O81OI.exe (PID: 6856)
- 5CWSP.exe (PID: 928)
- E4GW8.exe (PID: 6916)
- GNC73.exe (PID: 5280)
- 1PR86.exe (PID: 6852)
- 907YG.exe (PID: 4288)
- S09NQ.exe (PID: 5632)
- YA3ZA.exe (PID: 7052)
- 0562G.exe (PID: 7040)
- LVB60.exe (PID: 6744)
- C2QR9.exe (PID: 6764)
- Z7870.exe (PID: 3940)
- UYQQ1.exe (PID: 6796)
- ZLS8S.exe (PID: 4384)
- 0JE0W.exe (PID: 5012)
- 9GC6R.exe (PID: 3528)
- 1SLJB.exe (PID: 5920)
- DBCMM.exe (PID: 6440)
- 092JI.exe (PID: 2536)
- 1511H.exe (PID: 1084)
- G94ZJ.exe (PID: 5716)
- ZK2DO.exe (PID: 3768)
- 6PMI3.exe (PID: 4536)
- G9X52.exe (PID: 1748)
- NT82L.exe (PID: 588)
- 68757.exe (PID: 3016)
- 7W3C2.exe (PID: 2744)
- C8Z9R.exe (PID: 2328)
- Z2752.exe (PID: 2932)
- 0FKRR.exe (PID: 3628)
- UVWWD.exe (PID: 6080)
- VT48N.exe (PID: 5960)
- 2R0EK.exe (PID: 6380)
- 26X40.exe (PID: 6780)
- 3M9PJ.exe (PID: 3704)
- XK1C3.exe (PID: 736)
- 96TZ2.exe (PID: 6484)
- 38WPW.exe (PID: 6588)
- H0DTU.exe (PID: 4668)
- 40S7S.exe (PID: 6556)
- K6E5T.exe (PID: 6724)
- 1Y8YQ.exe (PID: 6432)
- 0U8K3.exe (PID: 6840)
- C3OU8.exe (PID: 1492)
- 0W2Z8.exe (PID: 6948)
- 6BR15.exe (PID: 3648)
- W0MZX.exe (PID: 5088)
- 18YX1.exe (PID: 6788)
- 22ELF.exe (PID: 7036)
- 5XAYS.exe (PID: 7156)
- Z882J.exe (PID: 7020)
- 1D453.exe (PID: 5900)
- C3KMH.exe (PID: 4920)
- 5E8AY.exe (PID: 2920)
- LC22S.exe (PID: 6300)
- W3K13.exe (PID: 1360)
- JQH0B.exe (PID: 2252)
- I5E12.exe (PID: 1752)
- 27SJC.exe (PID: 4952)
- X1GXY.exe (PID: 2736)
- 7PR46.exe (PID: 1832)
- XWCT0.exe (PID: 3528)
- 58182.exe (PID: 5716)
- CB7Y4.exe (PID: 2536)
- I1KNP.exe (PID: 1084)
- 23NUQ.exe (PID: 3768)
- NQQR1.exe (PID: 6216)
- NFQ3K.exe (PID: 4536)
- 3Y066.exe (PID: 3016)
- 273TK.exe (PID: 532)
- P7EFE.exe (PID: 588)
- 39PMG.exe (PID: 2328)
- V1YN9.exe (PID: 4012)
- SBL81.exe (PID: 7076)
- 59OG9.exe (PID: 3628)
- 98R0N.exe (PID: 7120)
- 2GJ2G.exe (PID: 1616)
- 4KIX1.exe (PID: 6752)
- 3718U.exe (PID: 6520)
- ZJB54.exe (PID: 6088)
- CGSA2.exe (PID: 6340)
- 8FGC3.exe (PID: 5336)
- I4V63.exe (PID: 5360)
- 057K9.exe (PID: 6692)
- J52RX.exe (PID: 6732)
- 4SA2F.exe (PID: 6756)
- ZUY5E.exe (PID: 6708)
- SAQM6.exe (PID: 5116)
- 2X000.exe (PID: 6992)
- 34J90.exe (PID: 7036)
- 9671S.exe (PID: 7156)
- K9QML.exe (PID: 6976)
- USQL5.exe (PID: 5088)
- 68B13.exe (PID: 6788)
- 6GH45.exe (PID: 4196)
- 0SXNW.exe (PID: 5900)
- 5DWMN.exe (PID: 1444)
- WZ7U2.exe (PID: 1100)
- 1C52V.exe (PID: 1744)
- FP04U.exe (PID: 6548)
Reads security settings of Internet Explorer
- 02b945d796fcd22a5d43896a9385f3d0.exe (PID: 6660)
- 8K04O.exe (PID: 6788)
- M724R.exe (PID: 6852)
- N35I5.exe (PID: 6916)
- S4888.exe (PID: 7160)
- MOWIB.exe (PID: 6976)
- VWL0Y.exe (PID: 7040)
- TG1RQ.exe (PID: 636)
- RUF25.exe (PID: 2524)
- 7N829.exe (PID: 1752)
- 96X66.exe (PID: 1720)
- 60CJD.exe (PID: 5620)
- 6E7J0.exe (PID: 3956)
- 9FWSN.exe (PID: 1712)
- 4149S.exe (PID: 6184)
- 22MS6.exe (PID: 6168)
- 4PPS8.exe (PID: 3712)
- C4GDM.exe (PID: 3652)
- RF642.exe (PID: 6460)
- 37W17.exe (PID: 1572)
- F1P8M.exe (PID: 6556)
- 0M637.exe (PID: 6432)
- NY046.exe (PID: 6604)
- 0D3RZ.exe (PID: 6656)
- 7NO21.exe (PID: 6348)
- V5C9E.exe (PID: 6564)
- FFTO4.exe (PID: 6800)
- L4KXM.exe (PID: 6544)
- J666T.exe (PID: 6876)
- AA73Y.exe (PID: 6932)
- OVM3L.exe (PID: 6980)
- 64J33.exe (PID: 4708)
- 4Z37G.exe (PID: 7116)
- U5511.exe (PID: 7052)
- N94X6.exe (PID: 1636)
- B6P0D.exe (PID: 5840)
- XE6NQ.exe (PID: 1012)
- 5D5H6.exe (PID: 920)
- UFH4K.exe (PID: 4548)
- R163X.exe (PID: 428)
- IZ7S7.exe (PID: 3500)
- 54O67.exe (PID: 3956)
- G7ZB5.exe (PID: 1712)
- 7K3Y8.exe (PID: 4360)
- 1U1UA.exe (PID: 6184)
- KHE50.exe (PID: 3712)
- 5X6M3.exe (PID: 6168)
- K7F8N.exe (PID: 3652)
- 1Y19C.exe (PID: 1572)
- QY355.exe (PID: 6460)
- PDK24.exe (PID: 6356)
- 95K6H.exe (PID: 6620)
- 7863V.exe (PID: 6704)
- 96M0Q.exe (PID: 6568)
- 1OF85.exe (PID: 6680)
- V1QEJ.exe (PID: 6544)
- UP490.exe (PID: 6332)
- 3T82E.exe (PID: 5552)
- 9DTLC.exe (PID: 6856)
- Y3227.exe (PID: 7016)
- 54Y7O.exe (PID: 7136)
- TJ2C4.exe (PID: 7112)
- CG2EB.exe (PID: 4232)
- V10Q0.exe (PID: 1016)
- 0N0W8.exe (PID: 3740)
- 5KS90.exe (PID: 5012)
- 4X0SN.exe (PID: 2084)
- 5512W.exe (PID: 1412)
- Y301X.exe (PID: 1428)
- 0T21K.exe (PID: 624)
- 984K3.exe (PID: 4752)
- TJ1QY.exe (PID: 4148)
- NB0TV.exe (PID: 6148)
- 5V5IZ.exe (PID: 4988)
- 1D62T.exe (PID: 3692)
- Y8U72.exe (PID: 4072)
- E5LC4.exe (PID: 1616)
- BZQD7.exe (PID: 6036)
- 025VG.exe (PID: 6512)
- G9V27.exe (PID: 1788)
- 6810I.exe (PID: 6364)
- O9WE2.exe (PID: 6344)
- 99ZL1.exe (PID: 6688)
- EEO8S.exe (PID: 6408)
- 77712.exe (PID: 6652)
- 711V7.exe (PID: 6888)
- QB88D.exe (PID: 6956)
- 9V3PZ.exe (PID: 6968)
- NHU4R.exe (PID: 7124)
- TX9MD.exe (PID: 7000)
- AEM4R.exe (PID: 7164)
- 4P82A.exe (PID: 7052)
- SFASV.exe (PID: 1444)
- T7LZ7.exe (PID: 2920)
- 986B7.exe (PID: 5924)
- X2726.exe (PID: 5196)
- NPS64.exe (PID: 2484)
- 4O9T8.exe (PID: 4960)
- KS0I5.exe (PID: 2084)
- HZR1Y.exe (PID: 4752)
- 6AE1C.exe (PID: 4148)
- 44WJS.exe (PID: 3724)
- N7R0N.exe (PID: 6220)
- 3BZAL.exe (PID: 5076)
- 16LFW.exe (PID: 6508)
- 87U7P.exe (PID: 6380)
- Z9Z56.exe (PID: 6036)
- 01V42.exe (PID: 324)
- 3O9X3.exe (PID: 6404)
- WQ418.exe (PID: 6364)
- ZM1H7.exe (PID: 6708)
- YM3X2.exe (PID: 6644)
- CI071.exe (PID: 6832)
- 42EZ1.exe (PID: 2600)
- 56SEV.exe (PID: 6960)
- K46TA.exe (PID: 5036)
- 4W0IT.exe (PID: 6996)
- 9954Z.exe (PID: 7016)
- 4WS91.exe (PID: 6740)
- 04076.exe (PID: 4920)
- ZM2KN.exe (PID: 6780)
- 18OM7.exe (PID: 4196)
- G1CB2.exe (PID: 5056)
- 6VN2K.exe (PID: 5904)
- AWJEF.exe (PID: 5196)
- 0NMLH.exe (PID: 1720)
- TOI8L.exe (PID: 3688)
- 0654P.exe (PID: 5956)
- KL948.exe (PID: 6208)
- 22OGZ.exe (PID: 5092)
- 4B305.exe (PID: 3692)
- 4F4X6.exe (PID: 4160)
- 6T8NY.exe (PID: 5004)
- A5ZI9.exe (PID: 6244)
- TOY05.exe (PID: 5076)
- 5EJSO.exe (PID: 6508)
- 5556W.exe (PID: 6036)
- 9IU9X.exe (PID: 6428)
- EV7AO.exe (PID: 6372)
- 8X41S.exe (PID: 6756)
- WE52B.exe (PID: 6348)
- XU9T1.exe (PID: 6716)
- J7661.exe (PID: 6544)
- 70O52.exe (PID: 6856)
- FGRMG.exe (PID: 4288)
- ICQ0E.exe (PID: 5036)
- HJB1G.exe (PID: 6984)
- 1I18S.exe (PID: 4024)
- 3FFMR.exe (PID: 6740)
- LXSLE.exe (PID: 6980)
- DZB8M.exe (PID: 3740)
- 80EQ4.exe (PID: 4384)
- 57D53.exe (PID: 4704)
- I7G22.exe (PID: 1944)
- 01CH8.exe (PID: 5196)
- 85007.exe (PID: 3820)
- 2E1Y3.exe (PID: 3956)
- IL366.exe (PID: 2480)
- 4VB81.exe (PID: 2084)
- C605X.exe (PID: 6188)
- D64AQ.exe (PID: 1120)
- N991U.exe (PID: 6288)
- 9031Q.exe (PID: 3104)
- K3VR8.exe (PID: 6560)
- 03553.exe (PID: 2916)
- HF7S5.exe (PID: 6448)
- K3YNW.exe (PID: 6396)
- 7UEBK.exe (PID: 364)
- 8OA0O.exe (PID: 1788)
- B30WC.exe (PID: 6364)
- R0OE4.exe (PID: 6660)
- DN635.exe (PID: 6528)
- SSN20.exe (PID: 2396)
- 6IY2Z.exe (PID: 6788)
- 927G1.exe (PID: 6860)
- U7JAA.exe (PID: 7020)
- 10W8W.exe (PID: 6996)
- OYH7Y.exe (PID: 7032)
- S9403.exe (PID: 7140)
- R3G15.exe (PID: 7164)
- 74C91.exe (PID: 4928)
- B4YQ1.exe (PID: 7120)
- DNFUA.exe (PID: 1100)
- 56ISU.exe (PID: 6108)
- H7221.exe (PID: 712)
- 907V7.exe (PID: 1428)
- 73875.exe (PID: 5372)
- AC1C4.exe (PID: 3500)
- 4T6WK.exe (PID: 6216)
- O624I.exe (PID: 4484)
- PQ12M.exe (PID: 4160)
- 365H2.exe (PID: 3960)
- OA72T.exe (PID: 4416)
- S60O0.exe (PID: 7072)
- 79476.exe (PID: 1604)
- LP845.exe (PID: 5396)
- PL6GL.exe (PID: 4500)
- 29X1Z.exe (PID: 6360)
- 04OHX.exe (PID: 6368)
- L4ZXZ.exe (PID: 6420)
- 58N6V.exe (PID: 6804)
- Q1BAQ.exe (PID: 6540)
- 9TMG1.exe (PID: 6908)
- H3VN5.exe (PID: 6880)
- WG1B7.exe (PID: 6972)
- 218P8.exe (PID: 1364)
- H1062.exe (PID: 1684)
- 657LD.exe (PID: 2684)
- 440KC.exe (PID: 6968)
- 4550G.exe (PID: 7000)
- Q0D99.exe (PID: 6784)
- 88OC4.exe (PID: 4024)
- X45W2.exe (PID: 5840)
- E28H6.exe (PID: 628)
- 54676.exe (PID: 1360)
- Z04H5.exe (PID: 1412)
- 900FK.exe (PID: 5720)
- D3Z0L.exe (PID: 6016)
- 24N9H.exe (PID: 2524)
- ITBP2.exe (PID: 5716)
- AVP68.exe (PID: 5936)
- JQX44.exe (PID: 5932)
- 49IS2.exe (PID: 4744)
- E3WGD.exe (PID: 3712)
- MNE8L.exe (PID: 1120)
- KU8HX.exe (PID: 4540)
- PJVCB.exe (PID: 3652)
- 0584N.exe (PID: 4140)
- MP9TW.exe (PID: 6560)
- 8W6R3.exe (PID: 5448)
- QM881.exe (PID: 4500)
- 2F2D3.exe (PID: 6424)
- TQ9J4.exe (PID: 6304)
- WEA53.exe (PID: 6732)
- 42OLV.exe (PID: 6336)
- Q2YBF.exe (PID: 6664)
- SKUOI.exe (PID: 6864)
- 92J0G.exe (PID: 6892)
- 6K4Q2.exe (PID: 7008)
- 5Z891.exe (PID: 6852)
- T78X0.exe (PID: 4312)
- 8G52R.exe (PID: 6496)
- YTYEA.exe (PID: 7020)
- 2116Y.exe (PID: 6780)
- PK2F1.exe (PID: 7120)
- QI699.exe (PID: 5836)
- V15ZZ.exe (PID: 7160)
- N0M02.exe (PID: 2796)
- 276YT.exe (PID: 3052)
- S74IS.exe (PID: 4628)
- W9609.exe (PID: 624)
- V723N.exe (PID: 5920)
- 0F1R3.exe (PID: 5372)
- 378S4.exe (PID: 3500)
- Y90VV.exe (PID: 4284)
- 8B952.exe (PID: 5148)
- D6W0N.exe (PID: 6316)
- 66LAL.exe (PID: 4492)
- 0I313.exe (PID: 5592)
- Q8W2L.exe (PID: 4072)
- 8F0F2.exe (PID: 5752)
- YY598.exe (PID: 4140)
- 9A9Q6.exe (PID: 6560)
- 8L8RH.exe (PID: 5448)
- D6U26.exe (PID: 4500)
- D1297.exe (PID: 6364)
- 1IWE3.exe (PID: 5896)
- D1BGI.exe (PID: 6828)
- 39YZ2.exe (PID: 6748)
- 3Y47A.exe (PID: 6928)
- TQBTR.exe (PID: 6532)
- MIA45.exe (PID: 2396)
- 5COD3.exe (PID: 1512)
- R3C14.exe (PID: 6272)
- 91U26.exe (PID: 7048)
- U8873.exe (PID: 6980)
- 78MU5.exe (PID: 3624)
- 5W26I.exe (PID: 5504)
- OY7FM.exe (PID: 1568)
- 911MO.exe (PID: 4920)
- B581C.exe (PID: 6204)
- VR6V2.exe (PID: 5064)
- 4JAG8.exe (PID: 5428)
- 1H060.exe (PID: 5904)
- 64VPY.exe (PID: 1724)
- I4KI1.exe (PID: 2448)
- 7UXSQ.exe (PID: 3956)
- DAB9M.exe (PID: 3688)
- 22W50.exe (PID: 6112)
- E8XAX.exe (PID: 4752)
- VV4I9.exe (PID: 6440)
- UUG01.exe (PID: 6308)
- J4Z28.exe (PID: 3808)
- P17LK.exe (PID: 6376)
- 4SJ9O.exe (PID: 6148)
- A52HG.exe (PID: 4480)
- 3L0V2.exe (PID: 6356)
- 9564H.exe (PID: 6640)
- 3OXE1.exe (PID: 6696)
- IUJ23.exe (PID: 6036)
- V4T76.exe (PID: 6756)
- UMI08.exe (PID: 6704)
- 578OY.exe (PID: 6800)
- 8UWQ3.exe (PID: 6900)
- 209JO.exe (PID: 7128)
- JF52M.exe (PID: 6956)
- 3C1Y2.exe (PID: 6964)
- K1582.exe (PID: 7024)
- 4A165.exe (PID: 7112)
- 2OHZ2.exe (PID: 72)
- BPD2E.exe (PID: 7152)
- EMUJU.exe (PID: 4056)
- 372V7.exe (PID: 920)
- IAL9T.exe (PID: 4916)
- 57J9P.exe (PID: 2736)
- M92AK.exe (PID: 5380)
- K5W7B.exe (PID: 1720)
- 2MITN.exe (PID: 4996)
- 2Y8G5.exe (PID: 2084)
- 79VU8.exe (PID: 3672)
- A1588.exe (PID: 372)
- 1NG25.exe (PID: 3956)
- MZ756.exe (PID: 4744)
- 28RHB.exe (PID: 2104)
- 484O0.exe (PID: 1628)
- 8T5W7.exe (PID: 6168)
- R71UH.exe (PID: 2336)
- S77ZS.exe (PID: 6444)
- 6734R.exe (PID: 7076)
- 6O2P1.exe (PID: 5960)
- C68Q1.exe (PID: 892)
- D272S.exe (PID: 6376)
- 0K35Y.exe (PID: 3732)
- QJ8Z3.exe (PID: 6512)
- E41LT.exe (PID: 4140)
- 2MZ2Q.exe (PID: 6556)
- HF969.exe (PID: 6352)
- 9H4EX.exe (PID: 4612)
- 628E6.exe (PID: 5812)
- TJ7S5.exe (PID: 6368)
- 560K5.exe (PID: 4560)
- Y1HQL.exe (PID: 6536)
- LTN7A.exe (PID: 6564)
- 663MU.exe (PID: 6644)
- FSFC1.exe (PID: 6928)
- 152U6.exe (PID: 6464)
- 8436V.exe (PID: 5208)
- GII08.exe (PID: 4156)
- A2EW5.exe (PID: 6776)
- ZKTPC.exe (PID: 1512)
- 9RM7K.exe (PID: 7000)
- 3N095.exe (PID: 7024)
- 67U4K.exe (PID: 7116)
- IY10Q.exe (PID: 4748)
- L9W60.exe (PID: 4020)
- 81GL1.exe (PID: 2252)
- E2KX5.exe (PID: 1016)
- FHSP4.exe (PID: 712)
- Z1RSM.exe (PID: 4952)
- TKQ3J.exe (PID: 2620)
- 068DL.exe (PID: 6156)
- 8480V.exe (PID: 5084)
- 089T7.exe (PID: 1508)
- B85MZ.exe (PID: 1648)
- 4S733.exe (PID: 6216)
- U9365.exe (PID: 6164)
- U8V9I.exe (PID: 1792)
- OJEV0.exe (PID: 2220)
- V8G6K.exe (PID: 6188)
- 68RFL.exe (PID: 6248)
- DBCMM.exe (PID: 6440)
- K55BB.exe (PID: 3100)
- 5IVAU.exe (PID: 3412)
- ZY185.exe (PID: 4540)
- S9M3S.exe (PID: 5656)
- 6305L.exe (PID: 6632)
- CVM16.exe (PID: 6592)
- 8XO1K.exe (PID: 6512)
- K5TT2.exe (PID: 4232)
- E2ZYL.exe (PID: 6344)
- G0OLR.exe (PID: 6296)
- 4ZD4X.exe (PID: 6084)
- 94704.exe (PID: 5304)
- EM8T0.exe (PID: 4560)
- K5299.exe (PID: 6304)
- 1O366.exe (PID: 6660)
- VPYHF.exe (PID: 6564)
- 941WE.exe (PID: 6644)
- 345DF.exe (PID: 6464)
- 39Q8V.exe (PID: 7132)
- TN94I.exe (PID: 6104)
- 4RWER.exe (PID: 5080)
- 26GP2.exe (PID: 3708)
- 69327.exe (PID: 4708)
- J4H9Z.exe (PID: 6760)
- F3P05.exe (PID: 4196)
- 6X74A.exe (PID: 4748)
- KH3F7.exe (PID: 7116)
- 2013B.exe (PID: 4020)
- 06MPS.exe (PID: 1016)
- X630B.exe (PID: 2252)
- 56795.exe (PID: 4952)
- LSVR6.exe (PID: 712)
- 20GY4.exe (PID: 3688)
- 624BS.exe (PID: 5464)
- ODDV0.exe (PID: 32)
- 6922J.exe (PID: 3644)
- G331I.exe (PID: 6184)
- F96VK.exe (PID: 5444)
- I378K.exe (PID: 2044)
- 2HF5B.exe (PID: 2308)
- W833D.exe (PID: 5256)
- 0EWX4.exe (PID: 924)
- A7S01.exe (PID: 6440)
- Z7HM4.exe (PID: 3104)
- 97C14.exe (PID: 6148)
- 6YYWZ.exe (PID: 3756)
- AHNPY.exe (PID: 608)
- 148Q3.exe (PID: 6816)
- 7444I.exe (PID: 2384)
- H49G5.exe (PID: 4036)
- 6M3A4.exe (PID: 4500)
- 8Q395.exe (PID: 6408)
- 015P1.exe (PID: 4152)
- O194N.exe (PID: 5896)
- 5FDRF.exe (PID: 5356)
- 59CT2.exe (PID: 4532)
- PQ42C.exe (PID: 6304)
- 4YKUD.exe (PID: 6708)
- 2M418.exe (PID: 1492)
- L71O9.exe (PID: 6876)
- P3GK8.exe (PID: 6956)
- 41263.exe (PID: 7028)
- 0K586.exe (PID: 4264)
- I5FF3.exe (PID: 5072)
- 8C0ZP.exe (PID: 7016)
- QL8WT.exe (PID: 5608)
- 7N28X.exe (PID: 4488)
- 8CUGN.exe (PID: 1488)
- 58X31.exe (PID: 1276)
- AOWJF.exe (PID: 5056)
- 2WOYO.exe (PID: 6548)
- 98N83.exe (PID: 6108)
- P64A3.exe (PID: 4700)
- KC51T.exe (PID: 6012)
- 26907.exe (PID: 5244)
- F0NQ8.exe (PID: 724)
- 31891.exe (PID: 6160)
- 48SB3.exe (PID: 368)
- UJDI0.exe (PID: 1308)
- IW0KW.exe (PID: 4200)
- 0M3WI.exe (PID: 5528)
- 4W23G.exe (PID: 5956)
- 931VD.exe (PID: 6208)
- R060H.exe (PID: 1808)
- V7776.exe (PID: 4160)
- 4W274.exe (PID: 532)
- 8O029.exe (PID: 4988)
- YM6X3.exe (PID: 7076)
- J042A.exe (PID: 4012)
- 18S8U.exe (PID: 3912)
- G0ANK.exe (PID: 1616)
- RFYJI.exe (PID: 6396)
- K3RP1.exe (PID: 2800)
- 11GI2.exe (PID: 2072)
- 34F17.exe (PID: 5448)
- N7TA3.exe (PID: 6568)
- 7W983.exe (PID: 4664)
- PRP6L.exe (PID: 5812)
- 517UZ.exe (PID: 6368)
- UP1EQ.exe (PID: 6900)
- U42RD.exe (PID: 5304)
- 5CWSP.exe (PID: 928)
- E4GW8.exe (PID: 6916)
- O81OI.exe (PID: 6856)
- 1PR86.exe (PID: 6852)
- 907YG.exe (PID: 4288)
- GNC73.exe (PID: 5280)
- S09NQ.exe (PID: 5632)
- YA3ZA.exe (PID: 7052)
- 0562G.exe (PID: 7040)
- LVB60.exe (PID: 6744)
- C2QR9.exe (PID: 6764)
- Z7870.exe (PID: 3940)
- UYQQ1.exe (PID: 6796)
- ZLS8S.exe (PID: 4384)
- 0JE0W.exe (PID: 5012)
- 1SLJB.exe (PID: 5920)
- 092JI.exe (PID: 2536)
- 9GC6R.exe (PID: 3528)
- G94ZJ.exe (PID: 5716)
- 1511H.exe (PID: 1084)
- ZK2DO.exe (PID: 3768)
- 6PMI3.exe (PID: 4536)
- G9X52.exe (PID: 1748)
- NT82L.exe (PID: 588)
- 68757.exe (PID: 3016)
- C8Z9R.exe (PID: 2328)
- 7W3C2.exe (PID: 2744)
- Z2752.exe (PID: 2932)
- 0FKRR.exe (PID: 3628)
- UVWWD.exe (PID: 6080)
- 2R0EK.exe (PID: 6380)
- VT48N.exe (PID: 5960)
- 3M9PJ.exe (PID: 3704)
- XK1C3.exe (PID: 736)
- 26X40.exe (PID: 6780)
- 38WPW.exe (PID: 6588)
- 96TZ2.exe (PID: 6484)
- H0DTU.exe (PID: 4668)
- 40S7S.exe (PID: 6556)
- 1Y8YQ.exe (PID: 6432)
- K6E5T.exe (PID: 6724)
- 0U8K3.exe (PID: 6840)
- C3OU8.exe (PID: 1492)
- 0W2Z8.exe (PID: 6948)
- 6BR15.exe (PID: 3648)
- W0MZX.exe (PID: 5088)
- 18YX1.exe (PID: 6788)
- 5XAYS.exe (PID: 7156)
- 22ELF.exe (PID: 7036)
- Z882J.exe (PID: 7020)
- 1D453.exe (PID: 5900)
- 5E8AY.exe (PID: 2920)
- C3KMH.exe (PID: 4920)
- LC22S.exe (PID: 6300)
- W3K13.exe (PID: 1360)
- I5E12.exe (PID: 1752)
- JQH0B.exe (PID: 2252)
- X1GXY.exe (PID: 2736)
- 27SJC.exe (PID: 4952)
- 7PR46.exe (PID: 1832)
- XWCT0.exe (PID: 3528)
- 58182.exe (PID: 5716)
- CB7Y4.exe (PID: 2536)
- I1KNP.exe (PID: 1084)
- 23NUQ.exe (PID: 3768)
- NQQR1.exe (PID: 6216)
- NFQ3K.exe (PID: 4536)
- 3Y066.exe (PID: 3016)
- P7EFE.exe (PID: 588)
- 39PMG.exe (PID: 2328)
- 273TK.exe (PID: 532)
- V1YN9.exe (PID: 4012)
- SBL81.exe (PID: 7076)
- 59OG9.exe (PID: 3628)
- 2GJ2G.exe (PID: 1616)
- 98R0N.exe (PID: 7120)
- 3718U.exe (PID: 6520)
- 4KIX1.exe (PID: 6752)
- CGSA2.exe (PID: 6340)
- ZJB54.exe (PID: 6088)
- 8FGC3.exe (PID: 5336)
- I4V63.exe (PID: 5360)
- J52RX.exe (PID: 6732)
- 057K9.exe (PID: 6692)
- 4SA2F.exe (PID: 6756)
- ZUY5E.exe (PID: 6708)
- 2X000.exe (PID: 6992)
Starts itself from another location
- 02b945d796fcd22a5d43896a9385f3d0.exe (PID: 6660)
- 8K04O.exe (PID: 6788)
- M724R.exe (PID: 6852)
- N35I5.exe (PID: 6916)
- VWL0Y.exe (PID: 7040)
- MOWIB.exe (PID: 6976)
- TG1RQ.exe (PID: 636)
- S4888.exe (PID: 7160)
- 96X66.exe (PID: 1720)
- 7N829.exe (PID: 1752)
- 60CJD.exe (PID: 5620)
- RUF25.exe (PID: 2524)
- 6E7J0.exe (PID: 3956)
- 9FWSN.exe (PID: 1712)
- 4149S.exe (PID: 6184)
- 4PPS8.exe (PID: 3712)
- C4GDM.exe (PID: 3652)
- RF642.exe (PID: 6460)
- 22MS6.exe (PID: 6168)
- 37W17.exe (PID: 1572)
- F1P8M.exe (PID: 6556)
- 0D3RZ.exe (PID: 6656)
- NY046.exe (PID: 6604)
- 7NO21.exe (PID: 6348)
- 0M637.exe (PID: 6432)
- L4KXM.exe (PID: 6544)
- V5C9E.exe (PID: 6564)
- AA73Y.exe (PID: 6932)
- FFTO4.exe (PID: 6800)
- J666T.exe (PID: 6876)
- 64J33.exe (PID: 4708)
- OVM3L.exe (PID: 6980)
- U5511.exe (PID: 7052)
- 4Z37G.exe (PID: 7116)
- XE6NQ.exe (PID: 1012)
- N94X6.exe (PID: 1636)
- UFH4K.exe (PID: 4548)
- B6P0D.exe (PID: 5840)
- 5D5H6.exe (PID: 920)
- R163X.exe (PID: 428)
- IZ7S7.exe (PID: 3500)
- 7K3Y8.exe (PID: 4360)
- 54O67.exe (PID: 3956)
- 1U1UA.exe (PID: 6184)
- KHE50.exe (PID: 3712)
- G7ZB5.exe (PID: 1712)
- K7F8N.exe (PID: 3652)
- 5X6M3.exe (PID: 6168)
- QY355.exe (PID: 6460)
- 1Y19C.exe (PID: 1572)
- 95K6H.exe (PID: 6620)
- PDK24.exe (PID: 6356)
- 96M0Q.exe (PID: 6568)
- 7863V.exe (PID: 6704)
- UP490.exe (PID: 6332)
- 1OF85.exe (PID: 6680)
- V1QEJ.exe (PID: 6544)
- 9DTLC.exe (PID: 6856)
- Y3227.exe (PID: 7016)
- 54Y7O.exe (PID: 7136)
- 3T82E.exe (PID: 5552)
- TJ2C4.exe (PID: 7112)
- CG2EB.exe (PID: 4232)
- V10Q0.exe (PID: 1016)
- 0N0W8.exe (PID: 3740)
- 5KS90.exe (PID: 5012)
- 5512W.exe (PID: 1412)
- 4X0SN.exe (PID: 2084)
- Y301X.exe (PID: 1428)
- 984K3.exe (PID: 4752)
- TJ1QY.exe (PID: 4148)
- 0T21K.exe (PID: 624)
- NB0TV.exe (PID: 6148)
- 1D62T.exe (PID: 3692)
- Y8U72.exe (PID: 4072)
- 5V5IZ.exe (PID: 4988)
- BZQD7.exe (PID: 6036)
- 025VG.exe (PID: 6512)
- E5LC4.exe (PID: 1616)
- G9V27.exe (PID: 1788)
- 6810I.exe (PID: 6364)
- EEO8S.exe (PID: 6408)
- O9WE2.exe (PID: 6344)
- 711V7.exe (PID: 6888)
- 99ZL1.exe (PID: 6688)
- 77712.exe (PID: 6652)
- QB88D.exe (PID: 6956)
- 9V3PZ.exe (PID: 6968)
- NHU4R.exe (PID: 7124)
- TX9MD.exe (PID: 7000)
- 4P82A.exe (PID: 7052)
- AEM4R.exe (PID: 7164)
- SFASV.exe (PID: 1444)
- T7LZ7.exe (PID: 2920)
- X2726.exe (PID: 5196)
- 986B7.exe (PID: 5924)
- KS0I5.exe (PID: 2084)
- NPS64.exe (PID: 2484)
- HZR1Y.exe (PID: 4752)
- 6AE1C.exe (PID: 4148)
- 4O9T8.exe (PID: 4960)
- 44WJS.exe (PID: 3724)
- N7R0N.exe (PID: 6220)
- 87U7P.exe (PID: 6380)
- 3BZAL.exe (PID: 5076)
- 16LFW.exe (PID: 6508)
- Z9Z56.exe (PID: 6036)
- 3O9X3.exe (PID: 6404)
- 01V42.exe (PID: 324)
- ZM1H7.exe (PID: 6708)
- WQ418.exe (PID: 6364)
- CI071.exe (PID: 6832)
- 42EZ1.exe (PID: 2600)
- YM3X2.exe (PID: 6644)
- 56SEV.exe (PID: 6960)
- K46TA.exe (PID: 5036)
- 4W0IT.exe (PID: 6996)
- 9954Z.exe (PID: 7016)
- ZM2KN.exe (PID: 6780)
- 4WS91.exe (PID: 6740)
- 04076.exe (PID: 4920)
- 18OM7.exe (PID: 4196)
- G1CB2.exe (PID: 5056)
- 6VN2K.exe (PID: 5904)
- AWJEF.exe (PID: 5196)
- TOI8L.exe (PID: 3688)
- 0NMLH.exe (PID: 1720)
- 22OGZ.exe (PID: 5092)
- 0654P.exe (PID: 5956)
- KL948.exe (PID: 6208)
- 4F4X6.exe (PID: 4160)
- 4B305.exe (PID: 3692)
- A5ZI9.exe (PID: 6244)
- 6T8NY.exe (PID: 5004)
- TOY05.exe (PID: 5076)
- 5EJSO.exe (PID: 6508)
- 5556W.exe (PID: 6036)
- 9IU9X.exe (PID: 6428)
- EV7AO.exe (PID: 6372)
- 8X41S.exe (PID: 6756)
- WE52B.exe (PID: 6348)
- XU9T1.exe (PID: 6716)
- J7661.exe (PID: 6544)
- 70O52.exe (PID: 6856)
- FGRMG.exe (PID: 4288)
- ICQ0E.exe (PID: 5036)
- HJB1G.exe (PID: 6984)
- LXSLE.exe (PID: 6980)
- 1I18S.exe (PID: 4024)
- 3FFMR.exe (PID: 6740)
- DZB8M.exe (PID: 3740)
- 80EQ4.exe (PID: 4384)
- I7G22.exe (PID: 1944)
- 57D53.exe (PID: 4704)
- 01CH8.exe (PID: 5196)
- 85007.exe (PID: 3820)
- 2E1Y3.exe (PID: 3956)
- 4VB81.exe (PID: 2084)
- C605X.exe (PID: 6188)
- D64AQ.exe (PID: 1120)
- IL366.exe (PID: 2480)
- 9031Q.exe (PID: 3104)
- N991U.exe (PID: 6288)
- HF7S5.exe (PID: 6448)
- K3VR8.exe (PID: 6560)
- K3YNW.exe (PID: 6396)
- 7UEBK.exe (PID: 364)
- 03553.exe (PID: 2916)
- 8OA0O.exe (PID: 1788)
- B30WC.exe (PID: 6364)
- R0OE4.exe (PID: 6660)
- DN635.exe (PID: 6528)
- 927G1.exe (PID: 6860)
- SSN20.exe (PID: 2396)
- U7JAA.exe (PID: 7020)
- 10W8W.exe (PID: 6996)
- 6IY2Z.exe (PID: 6788)
- S9403.exe (PID: 7140)
- OYH7Y.exe (PID: 7032)
- B4YQ1.exe (PID: 7120)
- R3G15.exe (PID: 7164)
- DNFUA.exe (PID: 1100)
- 56ISU.exe (PID: 6108)
- 74C91.exe (PID: 4928)
- H7221.exe (PID: 712)
- 907V7.exe (PID: 1428)
- AC1C4.exe (PID: 3500)
- 73875.exe (PID: 5372)
- O624I.exe (PID: 4484)
- 4T6WK.exe (PID: 6216)
- OA72T.exe (PID: 4416)
- PQ12M.exe (PID: 4160)
- S60O0.exe (PID: 7072)
- LP845.exe (PID: 5396)
- 79476.exe (PID: 1604)
- 29X1Z.exe (PID: 6360)
- PL6GL.exe (PID: 4500)
- L4ZXZ.exe (PID: 6420)
- 04OHX.exe (PID: 6368)
- Q1BAQ.exe (PID: 6540)
- 58N6V.exe (PID: 6804)
- 9TMG1.exe (PID: 6908)
- H3VN5.exe (PID: 6880)
- WG1B7.exe (PID: 6972)
- H1062.exe (PID: 1684)
- 218P8.exe (PID: 1364)
- 657LD.exe (PID: 2684)
- 440KC.exe (PID: 6968)
- 4550G.exe (PID: 7000)
- 88OC4.exe (PID: 4024)
- Q0D99.exe (PID: 6784)
- E28H6.exe (PID: 628)
- X45W2.exe (PID: 5840)
- 54676.exe (PID: 1360)
- Z04H5.exe (PID: 1412)
- D3Z0L.exe (PID: 6016)
- 900FK.exe (PID: 5720)
- 24N9H.exe (PID: 2524)
- ITBP2.exe (PID: 5716)
- AVP68.exe (PID: 5936)
- JQX44.exe (PID: 5932)
- 49IS2.exe (PID: 4744)
- E3WGD.exe (PID: 3712)
- MNE8L.exe (PID: 1120)
- KU8HX.exe (PID: 4540)
- PJVCB.exe (PID: 3652)
- 0584N.exe (PID: 4140)
- MP9TW.exe (PID: 6560)
- 8W6R3.exe (PID: 5448)
- QM881.exe (PID: 4500)
- 2F2D3.exe (PID: 6424)
- TQ9J4.exe (PID: 6304)
- WEA53.exe (PID: 6732)
- Q2YBF.exe (PID: 6664)
- 42OLV.exe (PID: 6336)
- SKUOI.exe (PID: 6864)
- 92J0G.exe (PID: 6892)
- 5Z891.exe (PID: 6852)
- 6K4Q2.exe (PID: 7008)
- T78X0.exe (PID: 4312)
- YTYEA.exe (PID: 7020)
- 2116Y.exe (PID: 6780)
- 8G52R.exe (PID: 6496)
- PK2F1.exe (PID: 7120)
- V15ZZ.exe (PID: 7160)
- N0M02.exe (PID: 2796)
- QI699.exe (PID: 5836)
- 276YT.exe (PID: 3052)
- S74IS.exe (PID: 4628)
- V723N.exe (PID: 5920)
- W9609.exe (PID: 624)
- 365H2.exe (PID: 3960)
- 0F1R3.exe (PID: 5372)
- 378S4.exe (PID: 3500)
- 8B952.exe (PID: 5148)
- Y90VV.exe (PID: 4284)
- 66LAL.exe (PID: 4492)
- D6W0N.exe (PID: 6316)
- Q8W2L.exe (PID: 4072)
- 0I313.exe (PID: 5592)
- 8F0F2.exe (PID: 5752)
- YY598.exe (PID: 4140)
- 9A9Q6.exe (PID: 6560)
- 8L8RH.exe (PID: 5448)
- D6U26.exe (PID: 4500)
- D1297.exe (PID: 6364)
- 1IWE3.exe (PID: 5896)
- D1BGI.exe (PID: 6828)
- 39YZ2.exe (PID: 6748)
- TQBTR.exe (PID: 6532)
- 3Y47A.exe (PID: 6928)
- MIA45.exe (PID: 2396)
- 5COD3.exe (PID: 1512)
- 91U26.exe (PID: 7048)
- R3C14.exe (PID: 6272)
- 78MU5.exe (PID: 3624)
- U8873.exe (PID: 6980)
- 5W26I.exe (PID: 5504)
- OY7FM.exe (PID: 1568)
- 911MO.exe (PID: 4920)
- 4JAG8.exe (PID: 5428)
- B581C.exe (PID: 6204)
- 1H060.exe (PID: 5904)
- VR6V2.exe (PID: 5064)
- 64VPY.exe (PID: 1724)
- I4KI1.exe (PID: 2448)
- 7UXSQ.exe (PID: 3956)
- DAB9M.exe (PID: 3688)
- 22W50.exe (PID: 6112)
- E8XAX.exe (PID: 4752)
- VV4I9.exe (PID: 6440)
- J4Z28.exe (PID: 3808)
- UUG01.exe (PID: 6308)
- 4SJ9O.exe (PID: 6148)
- A52HG.exe (PID: 4480)
- P17LK.exe (PID: 6376)
- 3L0V2.exe (PID: 6356)
- 9564H.exe (PID: 6640)
- 3OXE1.exe (PID: 6696)
- IUJ23.exe (PID: 6036)
- V4T76.exe (PID: 6756)
- UMI08.exe (PID: 6704)
- 578OY.exe (PID: 6800)
- 8UWQ3.exe (PID: 6900)
- JF52M.exe (PID: 6956)
- K1582.exe (PID: 7024)
- 209JO.exe (PID: 7128)
- 3C1Y2.exe (PID: 6964)
- 4A165.exe (PID: 7112)
- EMUJU.exe (PID: 4056)
- 2OHZ2.exe (PID: 72)
- BPD2E.exe (PID: 7152)
- IAL9T.exe (PID: 4916)
- 372V7.exe (PID: 920)
- 57J9P.exe (PID: 2736)
- M92AK.exe (PID: 5380)
- K5W7B.exe (PID: 1720)
- 2MITN.exe (PID: 4996)
- 2Y8G5.exe (PID: 2084)
- 79VU8.exe (PID: 3672)
- 1NG25.exe (PID: 3956)
- A1588.exe (PID: 372)
- 28RHB.exe (PID: 2104)
- 484O0.exe (PID: 1628)
- MZ756.exe (PID: 4744)
- R71UH.exe (PID: 2336)
- 8T5W7.exe (PID: 6168)
- 6734R.exe (PID: 7076)
- S77ZS.exe (PID: 6444)
- 6O2P1.exe (PID: 5960)
- C68Q1.exe (PID: 892)
- 0K35Y.exe (PID: 3732)
- D272S.exe (PID: 6376)
- E41LT.exe (PID: 4140)
- HF969.exe (PID: 6352)
- QJ8Z3.exe (PID: 6512)
- 9H4EX.exe (PID: 4612)
- 2MZ2Q.exe (PID: 6556)
- TJ7S5.exe (PID: 6368)
- 628E6.exe (PID: 5812)
- Y1HQL.exe (PID: 6536)
- 560K5.exe (PID: 4560)
- 663MU.exe (PID: 6644)
- LTN7A.exe (PID: 6564)
- FSFC1.exe (PID: 6928)
- 152U6.exe (PID: 6464)
- 8436V.exe (PID: 5208)
- GII08.exe (PID: 4156)
- ZKTPC.exe (PID: 1512)
- A2EW5.exe (PID: 6776)
- 3N095.exe (PID: 7024)
- 9RM7K.exe (PID: 7000)
- 67U4K.exe (PID: 7116)
- L9W60.exe (PID: 4020)
- IY10Q.exe (PID: 4748)
- 81GL1.exe (PID: 2252)
- E2KX5.exe (PID: 1016)
- Z1RSM.exe (PID: 4952)
- TKQ3J.exe (PID: 2620)
- FHSP4.exe (PID: 712)
- 8480V.exe (PID: 5084)
- 068DL.exe (PID: 6156)
- 089T7.exe (PID: 1508)
- B85MZ.exe (PID: 1648)
- U9365.exe (PID: 6164)
- 4S733.exe (PID: 6216)
- OJEV0.exe (PID: 2220)
- V8G6K.exe (PID: 6188)
- U8V9I.exe (PID: 1792)
- DBCMM.exe (PID: 6440)
- 68RFL.exe (PID: 6248)
- K55BB.exe (PID: 3100)
- 5IVAU.exe (PID: 3412)
- 6305L.exe (PID: 6632)
- S9M3S.exe (PID: 5656)
- CVM16.exe (PID: 6592)
- K5TT2.exe (PID: 4232)
- E2ZYL.exe (PID: 6344)
- 8XO1K.exe (PID: 6512)
- 4ZD4X.exe (PID: 6084)
- 94704.exe (PID: 5304)
- G0OLR.exe (PID: 6296)
- K5299.exe (PID: 6304)
- 1O366.exe (PID: 6660)
- EM8T0.exe (PID: 4560)
- VPYHF.exe (PID: 6564)
- 941WE.exe (PID: 6644)
- 345DF.exe (PID: 6464)
- 39Q8V.exe (PID: 7132)
- TN94I.exe (PID: 6104)
- 4RWER.exe (PID: 5080)
- 69327.exe (PID: 4708)
- J4H9Z.exe (PID: 6760)
- 26GP2.exe (PID: 3708)
- F3P05.exe (PID: 4196)
- 6X74A.exe (PID: 4748)
- KH3F7.exe (PID: 7116)
- 2013B.exe (PID: 4020)
- X630B.exe (PID: 2252)
- 06MPS.exe (PID: 1016)
- LSVR6.exe (PID: 712)
- 56795.exe (PID: 4952)
- 20GY4.exe (PID: 3688)
- ODDV0.exe (PID: 32)
- 624BS.exe (PID: 5464)
- 6922J.exe (PID: 3644)
- F96VK.exe (PID: 5444)
- I378K.exe (PID: 2044)
- G331I.exe (PID: 6184)
- W833D.exe (PID: 5256)
- 2HF5B.exe (PID: 2308)
- 0EWX4.exe (PID: 924)
- A7S01.exe (PID: 6440)
- Z7HM4.exe (PID: 3104)
- 97C14.exe (PID: 6148)
- 6YYWZ.exe (PID: 3756)
- AHNPY.exe (PID: 608)
- 7444I.exe (PID: 2384)
- H49G5.exe (PID: 4036)
- 8Q395.exe (PID: 6408)
- 015P1.exe (PID: 4152)
- 6M3A4.exe (PID: 4500)
- O194N.exe (PID: 5896)
- 59CT2.exe (PID: 4532)
- PQ42C.exe (PID: 6304)
- 5FDRF.exe (PID: 5356)
- 4YKUD.exe (PID: 6708)
- 2M418.exe (PID: 1492)
- P3GK8.exe (PID: 6956)
- L71O9.exe (PID: 6876)
- 41263.exe (PID: 7028)
- I5FF3.exe (PID: 5072)
- 8C0ZP.exe (PID: 7016)
- 0K586.exe (PID: 4264)
- QL8WT.exe (PID: 5608)
- 7N28X.exe (PID: 4488)
- 8CUGN.exe (PID: 1488)
- 58X31.exe (PID: 1276)
- AOWJF.exe (PID: 5056)
- 2WOYO.exe (PID: 6548)
- P64A3.exe (PID: 4700)
- 98N83.exe (PID: 6108)
- KC51T.exe (PID: 6012)
- 26907.exe (PID: 5244)
- 31891.exe (PID: 6160)
- F0NQ8.exe (PID: 724)
- 48SB3.exe (PID: 368)
- UJDI0.exe (PID: 1308)
- 0M3WI.exe (PID: 5528)
- 4W23G.exe (PID: 5956)
- IW0KW.exe (PID: 4200)
- R060H.exe (PID: 1808)
- V7776.exe (PID: 4160)
- 931VD.exe (PID: 6208)
- 4W274.exe (PID: 532)
- YM6X3.exe (PID: 7076)
- J042A.exe (PID: 4012)
- 8O029.exe (PID: 4988)
- G0ANK.exe (PID: 1616)
- 18S8U.exe (PID: 3912)
- RFYJI.exe (PID: 6396)
- 11GI2.exe (PID: 2072)
- K3RP1.exe (PID: 2800)
- 34F17.exe (PID: 5448)
- N7TA3.exe (PID: 6568)
- PRP6L.exe (PID: 5812)
- 7W983.exe (PID: 4664)
- 517UZ.exe (PID: 6368)
- U42RD.exe (PID: 5304)
- UP1EQ.exe (PID: 6900)
- 5CWSP.exe (PID: 928)
- O81OI.exe (PID: 6856)
- 1PR86.exe (PID: 6852)
- E4GW8.exe (PID: 6916)
- GNC73.exe (PID: 5280)
- S09NQ.exe (PID: 5632)
- 907YG.exe (PID: 4288)
- 0562G.exe (PID: 7040)
- LVB60.exe (PID: 6744)
- YA3ZA.exe (PID: 7052)
- Z7870.exe (PID: 3940)
- UYQQ1.exe (PID: 6796)
- C2QR9.exe (PID: 6764)
- 0JE0W.exe (PID: 5012)
- 1SLJB.exe (PID: 5920)
- ZLS8S.exe (PID: 4384)
- 092JI.exe (PID: 2536)
- 9GC6R.exe (PID: 3528)
- G94ZJ.exe (PID: 5716)
- ZY185.exe (PID: 4540)
- ZK2DO.exe (PID: 3768)
- 1511H.exe (PID: 1084)
- G9X52.exe (PID: 1748)
- 6PMI3.exe (PID: 4536)
- 68757.exe (PID: 3016)
- C8Z9R.exe (PID: 2328)
- NT82L.exe (PID: 588)
- Z2752.exe (PID: 2932)
- 7W3C2.exe (PID: 2744)
- UVWWD.exe (PID: 6080)
- 0FKRR.exe (PID: 3628)
- 2R0EK.exe (PID: 6380)
- 3M9PJ.exe (PID: 3704)
- VT48N.exe (PID: 5960)
- XK1C3.exe (PID: 736)
- 26X40.exe (PID: 6780)
- 96TZ2.exe (PID: 6484)
- 38WPW.exe (PID: 6588)
- 40S7S.exe (PID: 6556)
- H0DTU.exe (PID: 4668)
- 1Y8YQ.exe (PID: 6432)
- K6E5T.exe (PID: 6724)
- 0W2Z8.exe (PID: 6948)
- 0U8K3.exe (PID: 6840)
- 6BR15.exe (PID: 3648)
- C3OU8.exe (PID: 1492)
- W0MZX.exe (PID: 5088)
- 18YX1.exe (PID: 6788)
- 5XAYS.exe (PID: 7156)
- 22ELF.exe (PID: 7036)
- Z882J.exe (PID: 7020)
- 1D453.exe (PID: 5900)
- C3KMH.exe (PID: 4920)
- 5E8AY.exe (PID: 2920)
- W3K13.exe (PID: 1360)
- I5E12.exe (PID: 1752)
- LC22S.exe (PID: 6300)
- 27SJC.exe (PID: 4952)
- X1GXY.exe (PID: 2736)
- JQH0B.exe (PID: 2252)
- 7PR46.exe (PID: 1832)
- XWCT0.exe (PID: 3528)
- 148Q3.exe (PID: 6816)
- 58182.exe (PID: 5716)
- CB7Y4.exe (PID: 2536)
- I1KNP.exe (PID: 1084)
- NFQ3K.exe (PID: 4536)
- 23NUQ.exe (PID: 3768)
- 3Y066.exe (PID: 3016)
- NQQR1.exe (PID: 6216)
- 39PMG.exe (PID: 2328)
- P7EFE.exe (PID: 588)
- SBL81.exe (PID: 7076)
- 59OG9.exe (PID: 3628)
- 273TK.exe (PID: 532)
- 2GJ2G.exe (PID: 1616)
- V1YN9.exe (PID: 4012)
- 98R0N.exe (PID: 7120)
- 3718U.exe (PID: 6520)
- CGSA2.exe (PID: 6340)
- 4KIX1.exe (PID: 6752)
- ZJB54.exe (PID: 6088)
- I4V63.exe (PID: 5360)
- 8FGC3.exe (PID: 5336)
- 057K9.exe (PID: 6692)
- J52RX.exe (PID: 6732)
- ZUY5E.exe (PID: 6708)
- 4SA2F.exe (PID: 6756)
- 2X000.exe (PID: 6992)
- SAQM6.exe (PID: 5116)
- 68B13.exe (PID: 6788)
- 34J90.exe (PID: 7036)
- 9671S.exe (PID: 7156)
- K9QML.exe (PID: 6976)
- USQL5.exe (PID: 5088)
- WZ7U2.exe (PID: 1100)
- 6GH45.exe (PID: 4196)
- 0SXNW.exe (PID: 5900)
- 5DWMN.exe (PID: 1444)
- 1C52V.exe (PID: 1744)
INFO
Checks supported languages
- 02b945d796fcd22a5d43896a9385f3d0.exe (PID: 6660)
- 8K04O.exe (PID: 6788)
- M724R.exe (PID: 6852)
- MOWIB.exe (PID: 6976)
- N35I5.exe (PID: 6916)
- VWL0Y.exe (PID: 7040)
- S4888.exe (PID: 7160)
- 7N829.exe (PID: 1752)
- TG1RQ.exe (PID: 636)
- RUF25.exe (PID: 2524)
- 96X66.exe (PID: 1720)
- 60CJD.exe (PID: 5620)
- 6E7J0.exe (PID: 3956)
- 9FWSN.exe (PID: 1712)
- 4149S.exe (PID: 6184)
- 4PPS8.exe (PID: 3712)
- 22MS6.exe (PID: 6168)
- RF642.exe (PID: 6460)
- 37W17.exe (PID: 1572)
- C4GDM.exe (PID: 3652)
- F1P8M.exe (PID: 6556)
- NY046.exe (PID: 6604)
- 0D3RZ.exe (PID: 6656)
- 0M637.exe (PID: 6432)
- 7NO21.exe (PID: 6348)
- V5C9E.exe (PID: 6564)
- J666T.exe (PID: 6876)
- FFTO4.exe (PID: 6800)
- L4KXM.exe (PID: 6544)
- AA73Y.exe (PID: 6932)
- 64J33.exe (PID: 4708)
- U5511.exe (PID: 7052)
- OVM3L.exe (PID: 6980)
- 4Z37G.exe (PID: 7116)
- XE6NQ.exe (PID: 1012)
- N94X6.exe (PID: 1636)
- B6P0D.exe (PID: 5840)
- UFH4K.exe (PID: 4548)
- R163X.exe (PID: 428)
- 5D5H6.exe (PID: 920)
- IZ7S7.exe (PID: 3500)
- 7K3Y8.exe (PID: 4360)
- 54O67.exe (PID: 3956)
- G7ZB5.exe (PID: 1712)
- KHE50.exe (PID: 3712)
- 1U1UA.exe (PID: 6184)
- 5X6M3.exe (PID: 6168)
- K7F8N.exe (PID: 3652)
- QY355.exe (PID: 6460)
- 1Y19C.exe (PID: 1572)
- 96M0Q.exe (PID: 6568)
- 95K6H.exe (PID: 6620)
- PDK24.exe (PID: 6356)
- 7863V.exe (PID: 6704)
- UP490.exe (PID: 6332)
- 1OF85.exe (PID: 6680)
- V1QEJ.exe (PID: 6544)
- 3T82E.exe (PID: 5552)
- Y3227.exe (PID: 7016)
- 9DTLC.exe (PID: 6856)
- TJ2C4.exe (PID: 7112)
- 54Y7O.exe (PID: 7136)
- 0N0W8.exe (PID: 3740)
- CG2EB.exe (PID: 4232)
- V10Q0.exe (PID: 1016)
- 5512W.exe (PID: 1412)
- 5KS90.exe (PID: 5012)
- 4X0SN.exe (PID: 2084)
- Y301X.exe (PID: 1428)
- 0T21K.exe (PID: 624)
- 984K3.exe (PID: 4752)
- TJ1QY.exe (PID: 4148)
- 1D62T.exe (PID: 3692)
- NB0TV.exe (PID: 6148)
- 5V5IZ.exe (PID: 4988)
- Y8U72.exe (PID: 4072)
- E5LC4.exe (PID: 1616)
- G9V27.exe (PID: 1788)
- 025VG.exe (PID: 6512)
- BZQD7.exe (PID: 6036)
- EEO8S.exe (PID: 6408)
- 6810I.exe (PID: 6364)
- 99ZL1.exe (PID: 6688)
- O9WE2.exe (PID: 6344)
- 711V7.exe (PID: 6888)
- QB88D.exe (PID: 6956)
- 77712.exe (PID: 6652)
- 9V3PZ.exe (PID: 6968)
- TX9MD.exe (PID: 7000)
- NHU4R.exe (PID: 7124)
- 4P82A.exe (PID: 7052)
- AEM4R.exe (PID: 7164)
- SFASV.exe (PID: 1444)
- T7LZ7.exe (PID: 2920)
- X2726.exe (PID: 5196)
- KS0I5.exe (PID: 2084)
- 986B7.exe (PID: 5924)
- NPS64.exe (PID: 2484)
- 4O9T8.exe (PID: 4960)
- HZR1Y.exe (PID: 4752)
- 6AE1C.exe (PID: 4148)
- 44WJS.exe (PID: 3724)
- N7R0N.exe (PID: 6220)
- 87U7P.exe (PID: 6380)
- 3BZAL.exe (PID: 5076)
- 16LFW.exe (PID: 6508)
- Z9Z56.exe (PID: 6036)
- 01V42.exe (PID: 324)
- WQ418.exe (PID: 6364)
- 3O9X3.exe (PID: 6404)
- YM3X2.exe (PID: 6644)
- ZM1H7.exe (PID: 6708)
- 42EZ1.exe (PID: 2600)
- CI071.exe (PID: 6832)
- 4W0IT.exe (PID: 6996)
- 56SEV.exe (PID: 6960)
- K46TA.exe (PID: 5036)
- 9954Z.exe (PID: 7016)
- ZM2KN.exe (PID: 6780)
- 4WS91.exe (PID: 6740)
- 04076.exe (PID: 4920)
- 18OM7.exe (PID: 4196)
- G1CB2.exe (PID: 5056)
- AWJEF.exe (PID: 5196)
- 0NMLH.exe (PID: 1720)
- 6VN2K.exe (PID: 5904)
- 22OGZ.exe (PID: 5092)
- TOI8L.exe (PID: 3688)
- 0654P.exe (PID: 5956)
- KL948.exe (PID: 6208)
- 4B305.exe (PID: 3692)
- 4F4X6.exe (PID: 4160)
- 6T8NY.exe (PID: 5004)
- TOY05.exe (PID: 5076)
- A5ZI9.exe (PID: 6244)
- 5EJSO.exe (PID: 6508)
- 5556W.exe (PID: 6036)
- 9IU9X.exe (PID: 6428)
- EV7AO.exe (PID: 6372)
- 8X41S.exe (PID: 6756)
- XU9T1.exe (PID: 6716)
- J7661.exe (PID: 6544)
- WE52B.exe (PID: 6348)
- 70O52.exe (PID: 6856)
- FGRMG.exe (PID: 4288)
- ICQ0E.exe (PID: 5036)
- HJB1G.exe (PID: 6984)
- LXSLE.exe (PID: 6980)
- 1I18S.exe (PID: 4024)
- 3FFMR.exe (PID: 6740)
- 80EQ4.exe (PID: 4384)
- DZB8M.exe (PID: 3740)
- I7G22.exe (PID: 1944)
- 01CH8.exe (PID: 5196)
- 57D53.exe (PID: 4704)
- 85007.exe (PID: 3820)
- 4VB81.exe (PID: 2084)
- 2E1Y3.exe (PID: 3956)
- IL366.exe (PID: 2480)
- C605X.exe (PID: 6188)
- D64AQ.exe (PID: 1120)
- N991U.exe (PID: 6288)
- 9031Q.exe (PID: 3104)
- HF7S5.exe (PID: 6448)
- K3VR8.exe (PID: 6560)
- 03553.exe (PID: 2916)
- K3YNW.exe (PID: 6396)
- 7UEBK.exe (PID: 364)
- B30WC.exe (PID: 6364)
- R0OE4.exe (PID: 6660)
- 8OA0O.exe (PID: 1788)
- 927G1.exe (PID: 6860)
- DN635.exe (PID: 6528)
- SSN20.exe (PID: 2396)
- 6IY2Z.exe (PID: 6788)
- 10W8W.exe (PID: 6996)
- OYH7Y.exe (PID: 7032)
- U7JAA.exe (PID: 7020)
- S9403.exe (PID: 7140)
- B4YQ1.exe (PID: 7120)
- R3G15.exe (PID: 7164)
- 74C91.exe (PID: 4928)
- DNFUA.exe (PID: 1100)
- 56ISU.exe (PID: 6108)
- 907V7.exe (PID: 1428)
- AC1C4.exe (PID: 3500)
- H7221.exe (PID: 712)
- 73875.exe (PID: 5372)
- O624I.exe (PID: 4484)
- 4T6WK.exe (PID: 6216)
- OA72T.exe (PID: 4416)
- PQ12M.exe (PID: 4160)
- 365H2.exe (PID: 3960)
- S60O0.exe (PID: 7072)
- 79476.exe (PID: 1604)
- PL6GL.exe (PID: 4500)
- LP845.exe (PID: 5396)
- 04OHX.exe (PID: 6368)
- 29X1Z.exe (PID: 6360)
- 58N6V.exe (PID: 6804)
- L4ZXZ.exe (PID: 6420)
- 9TMG1.exe (PID: 6908)
- Q1BAQ.exe (PID: 6540)
- H3VN5.exe (PID: 6880)
- 218P8.exe (PID: 1364)
- H1062.exe (PID: 1684)
- 440KC.exe (PID: 6968)
- 657LD.exe (PID: 2684)
- 4550G.exe (PID: 7000)
- Q0D99.exe (PID: 6784)
- E28H6.exe (PID: 628)
- 88OC4.exe (PID: 4024)
- X45W2.exe (PID: 5840)
- Z04H5.exe (PID: 1412)
- 54676.exe (PID: 1360)
- 900FK.exe (PID: 5720)
- D3Z0L.exe (PID: 6016)
- 24N9H.exe (PID: 2524)
- ITBP2.exe (PID: 5716)
- AVP68.exe (PID: 5936)
- JQX44.exe (PID: 5932)
- 49IS2.exe (PID: 4744)
- E3WGD.exe (PID: 3712)
- MNE8L.exe (PID: 1120)
- PJVCB.exe (PID: 3652)
- KU8HX.exe (PID: 4540)
- 0584N.exe (PID: 4140)
- MP9TW.exe (PID: 6560)
- 8W6R3.exe (PID: 5448)
- QM881.exe (PID: 4500)
- 2F2D3.exe (PID: 6424)
- TQ9J4.exe (PID: 6304)
- WEA53.exe (PID: 6732)
- 42OLV.exe (PID: 6336)
- Q2YBF.exe (PID: 6664)
- 92J0G.exe (PID: 6892)
- SKUOI.exe (PID: 6864)
- 6K4Q2.exe (PID: 7008)
- 5Z891.exe (PID: 6852)
- YTYEA.exe (PID: 7020)
- T78X0.exe (PID: 4312)
- 8G52R.exe (PID: 6496)
- V15ZZ.exe (PID: 7160)
- 2116Y.exe (PID: 6780)
- QI699.exe (PID: 5836)
- PK2F1.exe (PID: 7120)
- N0M02.exe (PID: 2796)
- S74IS.exe (PID: 4628)
- 276YT.exe (PID: 3052)
- V723N.exe (PID: 5920)
- W9609.exe (PID: 624)
- 378S4.exe (PID: 3500)
- WG1B7.exe (PID: 6972)
- 0F1R3.exe (PID: 5372)
- 8B952.exe (PID: 5148)
- Y90VV.exe (PID: 4284)
- 66LAL.exe (PID: 4492)
- D6W0N.exe (PID: 6316)
- Q8W2L.exe (PID: 4072)
- 0I313.exe (PID: 5592)
- 8F0F2.exe (PID: 5752)
- YY598.exe (PID: 4140)
- 9A9Q6.exe (PID: 6560)
- 8L8RH.exe (PID: 5448)
- 1IWE3.exe (PID: 5896)
- D6U26.exe (PID: 4500)
- 39YZ2.exe (PID: 6748)
- D1297.exe (PID: 6364)
- D1BGI.exe (PID: 6828)
- MIA45.exe (PID: 2396)
- TQBTR.exe (PID: 6532)
- 3Y47A.exe (PID: 6928)
- 5COD3.exe (PID: 1512)
- R3C14.exe (PID: 6272)
- 91U26.exe (PID: 7048)
- 78MU5.exe (PID: 3624)
- U8873.exe (PID: 6980)
- OY7FM.exe (PID: 1568)
- 5W26I.exe (PID: 5504)
- B581C.exe (PID: 6204)
- 911MO.exe (PID: 4920)
- VR6V2.exe (PID: 5064)
- 4JAG8.exe (PID: 5428)
- I4KI1.exe (PID: 2448)
- 1H060.exe (PID: 5904)
- DAB9M.exe (PID: 3688)
- 64VPY.exe (PID: 1724)
- E8XAX.exe (PID: 4752)
- 7UXSQ.exe (PID: 3956)
- J4Z28.exe (PID: 3808)
- 22W50.exe (PID: 6112)
- VV4I9.exe (PID: 6440)
- UUG01.exe (PID: 6308)
- 4SJ9O.exe (PID: 6148)
- P17LK.exe (PID: 6376)
- A52HG.exe (PID: 4480)
- 9564H.exe (PID: 6640)
- IUJ23.exe (PID: 6036)
- 3L0V2.exe (PID: 6356)
- UMI08.exe (PID: 6704)
- 3OXE1.exe (PID: 6696)
- 8UWQ3.exe (PID: 6900)
- V4T76.exe (PID: 6756)
- 578OY.exe (PID: 6800)
- 209JO.exe (PID: 7128)
- 3C1Y2.exe (PID: 6964)
- JF52M.exe (PID: 6956)
- K1582.exe (PID: 7024)
- 2OHZ2.exe (PID: 72)
- BPD2E.exe (PID: 7152)
- 4A165.exe (PID: 7112)
- EMUJU.exe (PID: 4056)
- M92AK.exe (PID: 5380)
- IAL9T.exe (PID: 4916)
- 372V7.exe (PID: 920)
- 2MITN.exe (PID: 4996)
- 57J9P.exe (PID: 2736)
- K5W7B.exe (PID: 1720)
- 2Y8G5.exe (PID: 2084)
- 1NG25.exe (PID: 3956)
- 79VU8.exe (PID: 3672)
- A1588.exe (PID: 372)
- MZ756.exe (PID: 4744)
- 28RHB.exe (PID: 2104)
- 484O0.exe (PID: 1628)
- 8T5W7.exe (PID: 6168)
- 6734R.exe (PID: 7076)
- R71UH.exe (PID: 2336)
- C68Q1.exe (PID: 892)
- S77ZS.exe (PID: 6444)
- 0K35Y.exe (PID: 3732)
- 6O2P1.exe (PID: 5960)
- D272S.exe (PID: 6376)
- E41LT.exe (PID: 4140)
- QJ8Z3.exe (PID: 6512)
- HF969.exe (PID: 6352)
- 2MZ2Q.exe (PID: 6556)
- 628E6.exe (PID: 5812)
- 9H4EX.exe (PID: 4612)
- 560K5.exe (PID: 4560)
- TJ7S5.exe (PID: 6368)
- LTN7A.exe (PID: 6564)
- Y1HQL.exe (PID: 6536)
- 152U6.exe (PID: 6464)
- 663MU.exe (PID: 6644)
- GII08.exe (PID: 4156)
- FSFC1.exe (PID: 6928)
- ZKTPC.exe (PID: 1512)
- 8436V.exe (PID: 5208)
- A2EW5.exe (PID: 6776)
- 3N095.exe (PID: 7024)
- 9RM7K.exe (PID: 7000)
- IY10Q.exe (PID: 4748)
- 67U4K.exe (PID: 7116)
- E2KX5.exe (PID: 1016)
- L9W60.exe (PID: 4020)
- 81GL1.exe (PID: 2252)
- Z1RSM.exe (PID: 4952)
- FHSP4.exe (PID: 712)
- 068DL.exe (PID: 6156)
- TKQ3J.exe (PID: 2620)
- B85MZ.exe (PID: 1648)
- 8480V.exe (PID: 5084)
- 089T7.exe (PID: 1508)
- U9365.exe (PID: 6164)
- 4S733.exe (PID: 6216)
- U8V9I.exe (PID: 1792)
- OJEV0.exe (PID: 2220)
- V8G6K.exe (PID: 6188)
- 68RFL.exe (PID: 6248)
- DBCMM.exe (PID: 6440)
- K55BB.exe (PID: 3100)
- ZY185.exe (PID: 4540)
- 6305L.exe (PID: 6632)
- 5IVAU.exe (PID: 3412)
- S9M3S.exe (PID: 5656)
- K5TT2.exe (PID: 4232)
- CVM16.exe (PID: 6592)
- 8XO1K.exe (PID: 6512)
- E2ZYL.exe (PID: 6344)
- 4ZD4X.exe (PID: 6084)
- G0OLR.exe (PID: 6296)
- K5299.exe (PID: 6304)
- 94704.exe (PID: 5304)
- EM8T0.exe (PID: 4560)
- VPYHF.exe (PID: 6564)
- 1O366.exe (PID: 6660)
- 941WE.exe (PID: 6644)
- 345DF.exe (PID: 6464)
- 4RWER.exe (PID: 5080)
- 39Q8V.exe (PID: 7132)
- 69327.exe (PID: 4708)
- TN94I.exe (PID: 6104)
- 26GP2.exe (PID: 3708)
- J4H9Z.exe (PID: 6760)
- F3P05.exe (PID: 4196)
- KH3F7.exe (PID: 7116)
- 6X74A.exe (PID: 4748)
- 06MPS.exe (PID: 1016)
- 2013B.exe (PID: 4020)
- 56795.exe (PID: 4952)
- X630B.exe (PID: 2252)
- LSVR6.exe (PID: 712)
- 20GY4.exe (PID: 3688)
- ODDV0.exe (PID: 32)
- 624BS.exe (PID: 5464)
- F96VK.exe (PID: 5444)
- 6922J.exe (PID: 3644)
- G331I.exe (PID: 6184)
- W833D.exe (PID: 5256)
- I378K.exe (PID: 2044)
- 2HF5B.exe (PID: 2308)
- 0EWX4.exe (PID: 924)
- Z7HM4.exe (PID: 3104)
- A7S01.exe (PID: 6440)
- AHNPY.exe (PID: 608)
- 97C14.exe (PID: 6148)
- 7444I.exe (PID: 2384)
- 6YYWZ.exe (PID: 3756)
- 148Q3.exe (PID: 6816)
- 8Q395.exe (PID: 6408)
- H49G5.exe (PID: 4036)
- 6M3A4.exe (PID: 4500)
- O194N.exe (PID: 5896)
- 015P1.exe (PID: 4152)
- 59CT2.exe (PID: 4532)
- 5FDRF.exe (PID: 5356)
- PQ42C.exe (PID: 6304)
- 2M418.exe (PID: 1492)
- 4YKUD.exe (PID: 6708)
- L71O9.exe (PID: 6876)
- 41263.exe (PID: 7028)
- P3GK8.exe (PID: 6956)
- I5FF3.exe (PID: 5072)
- 0K586.exe (PID: 4264)
- 8C0ZP.exe (PID: 7016)
- QL8WT.exe (PID: 5608)
- 7N28X.exe (PID: 4488)
- 8CUGN.exe (PID: 1488)
- 58X31.exe (PID: 1276)
- 2WOYO.exe (PID: 6548)
- AOWJF.exe (PID: 5056)
- 98N83.exe (PID: 6108)
- P64A3.exe (PID: 4700)
- 26907.exe (PID: 5244)
- KC51T.exe (PID: 6012)
- F0NQ8.exe (PID: 724)
- 48SB3.exe (PID: 368)
- 31891.exe (PID: 6160)
- UJDI0.exe (PID: 1308)
- 0M3WI.exe (PID: 5528)
- IW0KW.exe (PID: 4200)
- 4W23G.exe (PID: 5956)
- R060H.exe (PID: 1808)
- 931VD.exe (PID: 6208)
- V7776.exe (PID: 4160)
- 4W274.exe (PID: 532)
- YM6X3.exe (PID: 7076)
- 8O029.exe (PID: 4988)
- G0ANK.exe (PID: 1616)
- J042A.exe (PID: 4012)
- 18S8U.exe (PID: 3912)
- 11GI2.exe (PID: 2072)
- RFYJI.exe (PID: 6396)
- 34F17.exe (PID: 5448)
- K3RP1.exe (PID: 2800)
- N7TA3.exe (PID: 6568)
- 7W983.exe (PID: 4664)
- 517UZ.exe (PID: 6368)
- PRP6L.exe (PID: 5812)
- U42RD.exe (PID: 5304)
- 5CWSP.exe (PID: 928)
- UP1EQ.exe (PID: 6900)
- O81OI.exe (PID: 6856)
- E4GW8.exe (PID: 6916)
- GNC73.exe (PID: 5280)
- 1PR86.exe (PID: 6852)
- 907YG.exe (PID: 4288)
- 0562G.exe (PID: 7040)
- S09NQ.exe (PID: 5632)
- YA3ZA.exe (PID: 7052)
- Z7870.exe (PID: 3940)
- LVB60.exe (PID: 6744)
- C2QR9.exe (PID: 6764)
- 0JE0W.exe (PID: 5012)
- UYQQ1.exe (PID: 6796)
- ZLS8S.exe (PID: 4384)
- 9GC6R.exe (PID: 3528)
- 1SLJB.exe (PID: 5920)
- 092JI.exe (PID: 2536)
- G94ZJ.exe (PID: 5716)
- 1511H.exe (PID: 1084)
- 6PMI3.exe (PID: 4536)
- ZK2DO.exe (PID: 3768)
- G9X52.exe (PID: 1748)
- 68757.exe (PID: 3016)
- NT82L.exe (PID: 588)
- 7W3C2.exe (PID: 2744)
- C8Z9R.exe (PID: 2328)
- Z2752.exe (PID: 2932)
- 0FKRR.exe (PID: 3628)
- UVWWD.exe (PID: 6080)
- 2R0EK.exe (PID: 6380)
- VT48N.exe (PID: 5960)
- 26X40.exe (PID: 6780)
- 3M9PJ.exe (PID: 3704)
- XK1C3.exe (PID: 736)
- 96TZ2.exe (PID: 6484)
- 38WPW.exe (PID: 6588)
- 40S7S.exe (PID: 6556)
- H0DTU.exe (PID: 4668)
- 1Y8YQ.exe (PID: 6432)
- K6E5T.exe (PID: 6724)
- 0U8K3.exe (PID: 6840)
- 0W2Z8.exe (PID: 6948)
- C3OU8.exe (PID: 1492)
- W0MZX.exe (PID: 5088)
- 6BR15.exe (PID: 3648)
- 22ELF.exe (PID: 7036)
- 18YX1.exe (PID: 6788)
- 1D453.exe (PID: 5900)
- 5XAYS.exe (PID: 7156)
- Z882J.exe (PID: 7020)
- C3KMH.exe (PID: 4920)
- W3K13.exe (PID: 1360)
- 5E8AY.exe (PID: 2920)
- LC22S.exe (PID: 6300)
- I5E12.exe (PID: 1752)
- JQH0B.exe (PID: 2252)
- X1GXY.exe (PID: 2736)
- 7PR46.exe (PID: 1832)
- 27SJC.exe (PID: 4952)
- XWCT0.exe (PID: 3528)
- 58182.exe (PID: 5716)
- CB7Y4.exe (PID: 2536)
- 23NUQ.exe (PID: 3768)
- I1KNP.exe (PID: 1084)
- NFQ3K.exe (PID: 4536)
- NQQR1.exe (PID: 6216)
- P7EFE.exe (PID: 588)
- 3Y066.exe (PID: 3016)
- 273TK.exe (PID: 532)
- 39PMG.exe (PID: 2328)
- 59OG9.exe (PID: 3628)
- SBL81.exe (PID: 7076)
- V1YN9.exe (PID: 4012)
- 98R0N.exe (PID: 7120)
- 2GJ2G.exe (PID: 1616)
- 3718U.exe (PID: 6520)
- 4KIX1.exe (PID: 6752)
- CGSA2.exe (PID: 6340)
- I4V63.exe (PID: 5360)
- ZJB54.exe (PID: 6088)
- 057K9.exe (PID: 6692)
- 8FGC3.exe (PID: 5336)
- J52RX.exe (PID: 6732)
- ZUY5E.exe (PID: 6708)
- 4SA2F.exe (PID: 6756)
- SAQM6.exe (PID: 5116)
- 2X000.exe (PID: 6992)
Reads the computer name
- 02b945d796fcd22a5d43896a9385f3d0.exe (PID: 6660)
- 8K04O.exe (PID: 6788)
- M724R.exe (PID: 6852)
- N35I5.exe (PID: 6916)
- MOWIB.exe (PID: 6976)
- VWL0Y.exe (PID: 7040)
- S4888.exe (PID: 7160)
- TG1RQ.exe (PID: 636)
- 7N829.exe (PID: 1752)
- RUF25.exe (PID: 2524)
- 96X66.exe (PID: 1720)
- 60CJD.exe (PID: 5620)
- 6E7J0.exe (PID: 3956)
- 9FWSN.exe (PID: 1712)
- 4149S.exe (PID: 6184)
- 22MS6.exe (PID: 6168)
- 4PPS8.exe (PID: 3712)
- RF642.exe (PID: 6460)
- 37W17.exe (PID: 1572)
- C4GDM.exe (PID: 3652)
- F1P8M.exe (PID: 6556)
- NY046.exe (PID: 6604)
- 0D3RZ.exe (PID: 6656)
- 0M637.exe (PID: 6432)
- V5C9E.exe (PID: 6564)
- 7NO21.exe (PID: 6348)
- FFTO4.exe (PID: 6800)
- L4KXM.exe (PID: 6544)
- AA73Y.exe (PID: 6932)
- J666T.exe (PID: 6876)
- OVM3L.exe (PID: 6980)
- U5511.exe (PID: 7052)
- 64J33.exe (PID: 4708)
- 4Z37G.exe (PID: 7116)
- XE6NQ.exe (PID: 1012)
- N94X6.exe (PID: 1636)
- B6P0D.exe (PID: 5840)
- 5D5H6.exe (PID: 920)
- UFH4K.exe (PID: 4548)
- IZ7S7.exe (PID: 3500)
- 7K3Y8.exe (PID: 4360)
- R163X.exe (PID: 428)
- 54O67.exe (PID: 3956)
- G7ZB5.exe (PID: 1712)
- 1U1UA.exe (PID: 6184)
- KHE50.exe (PID: 3712)
- K7F8N.exe (PID: 3652)
- 5X6M3.exe (PID: 6168)
- 1Y19C.exe (PID: 1572)
- QY355.exe (PID: 6460)
- PDK24.exe (PID: 6356)
- 96M0Q.exe (PID: 6568)
- 95K6H.exe (PID: 6620)
- 7863V.exe (PID: 6704)
- UP490.exe (PID: 6332)
- 1OF85.exe (PID: 6680)
- V1QEJ.exe (PID: 6544)
- 3T82E.exe (PID: 5552)
- 9DTLC.exe (PID: 6856)
- 54Y7O.exe (PID: 7136)
- Y3227.exe (PID: 7016)
- CG2EB.exe (PID: 4232)
- 0N0W8.exe (PID: 3740)
- TJ2C4.exe (PID: 7112)
- V10Q0.exe (PID: 1016)
- 5512W.exe (PID: 1412)
- 4X0SN.exe (PID: 2084)
- 5KS90.exe (PID: 5012)
- Y301X.exe (PID: 1428)
- 0T21K.exe (PID: 624)
- TJ1QY.exe (PID: 4148)
- 1D62T.exe (PID: 3692)
- 984K3.exe (PID: 4752)
- NB0TV.exe (PID: 6148)
- 5V5IZ.exe (PID: 4988)
- Y8U72.exe (PID: 4072)
- E5LC4.exe (PID: 1616)
- 025VG.exe (PID: 6512)
- G9V27.exe (PID: 1788)
- BZQD7.exe (PID: 6036)
- EEO8S.exe (PID: 6408)
- 6810I.exe (PID: 6364)
- O9WE2.exe (PID: 6344)
- 99ZL1.exe (PID: 6688)
- 711V7.exe (PID: 6888)
- 77712.exe (PID: 6652)
- TX9MD.exe (PID: 7000)
- QB88D.exe (PID: 6956)
- 9V3PZ.exe (PID: 6968)
- NHU4R.exe (PID: 7124)
- 4P82A.exe (PID: 7052)
- AEM4R.exe (PID: 7164)
- SFASV.exe (PID: 1444)
- T7LZ7.exe (PID: 2920)
- 986B7.exe (PID: 5924)
- KS0I5.exe (PID: 2084)
- X2726.exe (PID: 5196)
- NPS64.exe (PID: 2484)
- 4O9T8.exe (PID: 4960)
- HZR1Y.exe (PID: 4752)
- 6AE1C.exe (PID: 4148)
- N7R0N.exe (PID: 6220)
- 87U7P.exe (PID: 6380)
- 44WJS.exe (PID: 3724)
- 3BZAL.exe (PID: 5076)
- 16LFW.exe (PID: 6508)
- 01V42.exe (PID: 324)
- Z9Z56.exe (PID: 6036)
- WQ418.exe (PID: 6364)
- 3O9X3.exe (PID: 6404)
- YM3X2.exe (PID: 6644)
- ZM1H7.exe (PID: 6708)
- 42EZ1.exe (PID: 2600)
- CI071.exe (PID: 6832)
- K46TA.exe (PID: 5036)
- 56SEV.exe (PID: 6960)
- 9954Z.exe (PID: 7016)
- ZM2KN.exe (PID: 6780)
- 4W0IT.exe (PID: 6996)
- 4WS91.exe (PID: 6740)
- 04076.exe (PID: 4920)
- 18OM7.exe (PID: 4196)
- G1CB2.exe (PID: 5056)
- AWJEF.exe (PID: 5196)
- 6VN2K.exe (PID: 5904)
- TOI8L.exe (PID: 3688)
- 22OGZ.exe (PID: 5092)
- 0NMLH.exe (PID: 1720)
- 0654P.exe (PID: 5956)
- KL948.exe (PID: 6208)
- 4F4X6.exe (PID: 4160)
- 4B305.exe (PID: 3692)
- 6T8NY.exe (PID: 5004)
- A5ZI9.exe (PID: 6244)
- 5EJSO.exe (PID: 6508)
- 5556W.exe (PID: 6036)
- TOY05.exe (PID: 5076)
- 9IU9X.exe (PID: 6428)
- EV7AO.exe (PID: 6372)
- 8X41S.exe (PID: 6756)
- WE52B.exe (PID: 6348)
- XU9T1.exe (PID: 6716)
- J7661.exe (PID: 6544)
- 70O52.exe (PID: 6856)
- FGRMG.exe (PID: 4288)
- ICQ0E.exe (PID: 5036)
- HJB1G.exe (PID: 6984)
- LXSLE.exe (PID: 6980)
- 1I18S.exe (PID: 4024)
- 3FFMR.exe (PID: 6740)
- 80EQ4.exe (PID: 4384)
- DZB8M.exe (PID: 3740)
- I7G22.exe (PID: 1944)
- 01CH8.exe (PID: 5196)
- 57D53.exe (PID: 4704)
- 85007.exe (PID: 3820)
- 4VB81.exe (PID: 2084)
- 2E1Y3.exe (PID: 3956)
- IL366.exe (PID: 2480)
- D64AQ.exe (PID: 1120)
- N991U.exe (PID: 6288)
- C605X.exe (PID: 6188)
- 9031Q.exe (PID: 3104)
- HF7S5.exe (PID: 6448)
- 03553.exe (PID: 2916)
- K3VR8.exe (PID: 6560)
- K3YNW.exe (PID: 6396)
- 7UEBK.exe (PID: 364)
- B30WC.exe (PID: 6364)
- R0OE4.exe (PID: 6660)
- 8OA0O.exe (PID: 1788)
- DN635.exe (PID: 6528)
- 927G1.exe (PID: 6860)
- 6IY2Z.exe (PID: 6788)
- SSN20.exe (PID: 2396)
- U7JAA.exe (PID: 7020)
- 10W8W.exe (PID: 6996)
- S9403.exe (PID: 7140)
- B4YQ1.exe (PID: 7120)
- OYH7Y.exe (PID: 7032)
- R3G15.exe (PID: 7164)
- 74C91.exe (PID: 4928)
- DNFUA.exe (PID: 1100)
- 56ISU.exe (PID: 6108)
- 907V7.exe (PID: 1428)
- H7221.exe (PID: 712)
- 73875.exe (PID: 5372)
- O624I.exe (PID: 4484)
- AC1C4.exe (PID: 3500)
- 4T6WK.exe (PID: 6216)
- OA72T.exe (PID: 4416)
- PQ12M.exe (PID: 4160)
- 365H2.exe (PID: 3960)
- S60O0.exe (PID: 7072)
- 79476.exe (PID: 1604)
- PL6GL.exe (PID: 4500)
- LP845.exe (PID: 5396)
- 04OHX.exe (PID: 6368)
- 29X1Z.exe (PID: 6360)
- 58N6V.exe (PID: 6804)
- L4ZXZ.exe (PID: 6420)
- Q1BAQ.exe (PID: 6540)
- 9TMG1.exe (PID: 6908)
- H3VN5.exe (PID: 6880)
- WG1B7.exe (PID: 6972)
- 218P8.exe (PID: 1364)
- H1062.exe (PID: 1684)
- 657LD.exe (PID: 2684)
- 440KC.exe (PID: 6968)
- 4550G.exe (PID: 7000)
- Q0D99.exe (PID: 6784)
- 88OC4.exe (PID: 4024)
- E28H6.exe (PID: 628)
- X45W2.exe (PID: 5840)
- 54676.exe (PID: 1360)
- Z04H5.exe (PID: 1412)
- 900FK.exe (PID: 5720)
- D3Z0L.exe (PID: 6016)
- 24N9H.exe (PID: 2524)
- ITBP2.exe (PID: 5716)
- AVP68.exe (PID: 5936)
- JQX44.exe (PID: 5932)
- 49IS2.exe (PID: 4744)
- E3WGD.exe (PID: 3712)
- MNE8L.exe (PID: 1120)
- PJVCB.exe (PID: 3652)
- KU8HX.exe (PID: 4540)
- 0584N.exe (PID: 4140)
- MP9TW.exe (PID: 6560)
- 8W6R3.exe (PID: 5448)
- QM881.exe (PID: 4500)
- 2F2D3.exe (PID: 6424)
- TQ9J4.exe (PID: 6304)
- WEA53.exe (PID: 6732)
- 42OLV.exe (PID: 6336)
- 92J0G.exe (PID: 6892)
- Q2YBF.exe (PID: 6664)
- SKUOI.exe (PID: 6864)
- 6K4Q2.exe (PID: 7008)
- 5Z891.exe (PID: 6852)
- YTYEA.exe (PID: 7020)
- T78X0.exe (PID: 4312)
- 8G52R.exe (PID: 6496)
- V15ZZ.exe (PID: 7160)
- 2116Y.exe (PID: 6780)
- PK2F1.exe (PID: 7120)
- QI699.exe (PID: 5836)
- N0M02.exe (PID: 2796)
- S74IS.exe (PID: 4628)
- V723N.exe (PID: 5920)
- 276YT.exe (PID: 3052)
- W9609.exe (PID: 624)
- 0F1R3.exe (PID: 5372)
- 8B952.exe (PID: 5148)
- 378S4.exe (PID: 3500)
- Y90VV.exe (PID: 4284)
- 66LAL.exe (PID: 4492)
- D6W0N.exe (PID: 6316)
- Q8W2L.exe (PID: 4072)
- 0I313.exe (PID: 5592)
- YY598.exe (PID: 4140)
- 8F0F2.exe (PID: 5752)
- 9A9Q6.exe (PID: 6560)
- 1IWE3.exe (PID: 5896)
- 8L8RH.exe (PID: 5448)
- D6U26.exe (PID: 4500)
- 39YZ2.exe (PID: 6748)
- D1297.exe (PID: 6364)
- TQBTR.exe (PID: 6532)
- D1BGI.exe (PID: 6828)
- 3Y47A.exe (PID: 6928)
- MIA45.exe (PID: 2396)
- 5COD3.exe (PID: 1512)
- R3C14.exe (PID: 6272)
- 91U26.exe (PID: 7048)
- 78MU5.exe (PID: 3624)
- U8873.exe (PID: 6980)
- OY7FM.exe (PID: 1568)
- 5W26I.exe (PID: 5504)
- B581C.exe (PID: 6204)
- 911MO.exe (PID: 4920)
- VR6V2.exe (PID: 5064)
- 4JAG8.exe (PID: 5428)
- 1H060.exe (PID: 5904)
- I4KI1.exe (PID: 2448)
- 64VPY.exe (PID: 1724)
- DAB9M.exe (PID: 3688)
- 7UXSQ.exe (PID: 3956)
- E8XAX.exe (PID: 4752)
- 22W50.exe (PID: 6112)
- VV4I9.exe (PID: 6440)
- UUG01.exe (PID: 6308)
- J4Z28.exe (PID: 3808)
- 4SJ9O.exe (PID: 6148)
- P17LK.exe (PID: 6376)
- 9564H.exe (PID: 6640)
- A52HG.exe (PID: 4480)
- IUJ23.exe (PID: 6036)
- 3L0V2.exe (PID: 6356)
- 3OXE1.exe (PID: 6696)
- UMI08.exe (PID: 6704)
- V4T76.exe (PID: 6756)
- 8UWQ3.exe (PID: 6900)
- 578OY.exe (PID: 6800)
- JF52M.exe (PID: 6956)
- 209JO.exe (PID: 7128)
- K1582.exe (PID: 7024)
- 3C1Y2.exe (PID: 6964)
- 2OHZ2.exe (PID: 72)
- 4A165.exe (PID: 7112)
- EMUJU.exe (PID: 4056)
- BPD2E.exe (PID: 7152)
- 372V7.exe (PID: 920)
- M92AK.exe (PID: 5380)
- IAL9T.exe (PID: 4916)
- 57J9P.exe (PID: 2736)
- 2MITN.exe (PID: 4996)
- K5W7B.exe (PID: 1720)
- 2Y8G5.exe (PID: 2084)
- 79VU8.exe (PID: 3672)
- A1588.exe (PID: 372)
- 1NG25.exe (PID: 3956)
- MZ756.exe (PID: 4744)
- 28RHB.exe (PID: 2104)
- 8T5W7.exe (PID: 6168)
- 484O0.exe (PID: 1628)
- 6734R.exe (PID: 7076)
- R71UH.exe (PID: 2336)
- S77ZS.exe (PID: 6444)
- C68Q1.exe (PID: 892)
- 6O2P1.exe (PID: 5960)
- D272S.exe (PID: 6376)
- 0K35Y.exe (PID: 3732)
- QJ8Z3.exe (PID: 6512)
- E41LT.exe (PID: 4140)
- 2MZ2Q.exe (PID: 6556)
- HF969.exe (PID: 6352)
- 628E6.exe (PID: 5812)
- 9H4EX.exe (PID: 4612)
- 560K5.exe (PID: 4560)
- TJ7S5.exe (PID: 6368)
- LTN7A.exe (PID: 6564)
- Y1HQL.exe (PID: 6536)
- 152U6.exe (PID: 6464)
- 663MU.exe (PID: 6644)
- FSFC1.exe (PID: 6928)
- GII08.exe (PID: 4156)
- 8436V.exe (PID: 5208)
- ZKTPC.exe (PID: 1512)
- A2EW5.exe (PID: 6776)
- 9RM7K.exe (PID: 7000)
- 3N095.exe (PID: 7024)
- IY10Q.exe (PID: 4748)
- 67U4K.exe (PID: 7116)
- E2KX5.exe (PID: 1016)
- L9W60.exe (PID: 4020)
- 81GL1.exe (PID: 2252)
- FHSP4.exe (PID: 712)
- Z1RSM.exe (PID: 4952)
- TKQ3J.exe (PID: 2620)
- 068DL.exe (PID: 6156)
- B85MZ.exe (PID: 1648)
- 8480V.exe (PID: 5084)
- 089T7.exe (PID: 1508)
- 4S733.exe (PID: 6216)
- U9365.exe (PID: 6164)
- U8V9I.exe (PID: 1792)
- OJEV0.exe (PID: 2220)
- 68RFL.exe (PID: 6248)
- V8G6K.exe (PID: 6188)
- DBCMM.exe (PID: 6440)
- ZY185.exe (PID: 4540)
- K55BB.exe (PID: 3100)
- 6305L.exe (PID: 6632)
- 5IVAU.exe (PID: 3412)
- S9M3S.exe (PID: 5656)
- K5TT2.exe (PID: 4232)
- CVM16.exe (PID: 6592)
- 8XO1K.exe (PID: 6512)
- 4ZD4X.exe (PID: 6084)
- E2ZYL.exe (PID: 6344)
- G0OLR.exe (PID: 6296)
- K5299.exe (PID: 6304)
- 94704.exe (PID: 5304)
- EM8T0.exe (PID: 4560)
- VPYHF.exe (PID: 6564)
- 1O366.exe (PID: 6660)
- 941WE.exe (PID: 6644)
- 345DF.exe (PID: 6464)
- 4RWER.exe (PID: 5080)
- 39Q8V.exe (PID: 7132)
- TN94I.exe (PID: 6104)
- 69327.exe (PID: 4708)
- 26GP2.exe (PID: 3708)
- J4H9Z.exe (PID: 6760)
- F3P05.exe (PID: 4196)
- KH3F7.exe (PID: 7116)
- 6X74A.exe (PID: 4748)
- 06MPS.exe (PID: 1016)
- 2013B.exe (PID: 4020)
- X630B.exe (PID: 2252)
- 56795.exe (PID: 4952)
- LSVR6.exe (PID: 712)
- ODDV0.exe (PID: 32)
- 20GY4.exe (PID: 3688)
- 624BS.exe (PID: 5464)
- F96VK.exe (PID: 5444)
- 6922J.exe (PID: 3644)
- G331I.exe (PID: 6184)
- W833D.exe (PID: 5256)
- I378K.exe (PID: 2044)
- 2HF5B.exe (PID: 2308)
- Z7HM4.exe (PID: 3104)
- 0EWX4.exe (PID: 924)
- A7S01.exe (PID: 6440)
- AHNPY.exe (PID: 608)
- 97C14.exe (PID: 6148)
- 6YYWZ.exe (PID: 3756)
- 7444I.exe (PID: 2384)
- 148Q3.exe (PID: 6816)
- H49G5.exe (PID: 4036)
- 6M3A4.exe (PID: 4500)
- 8Q395.exe (PID: 6408)
- 015P1.exe (PID: 4152)
- O194N.exe (PID: 5896)
- 59CT2.exe (PID: 4532)
- 5FDRF.exe (PID: 5356)
- PQ42C.exe (PID: 6304)
- 4YKUD.exe (PID: 6708)
- 2M418.exe (PID: 1492)
- L71O9.exe (PID: 6876)
- P3GK8.exe (PID: 6956)
- 41263.exe (PID: 7028)
- I5FF3.exe (PID: 5072)
- 0K586.exe (PID: 4264)
- 8C0ZP.exe (PID: 7016)
- QL8WT.exe (PID: 5608)
- 7N28X.exe (PID: 4488)
- 8CUGN.exe (PID: 1488)
- 58X31.exe (PID: 1276)
- AOWJF.exe (PID: 5056)
- 98N83.exe (PID: 6108)
- 2WOYO.exe (PID: 6548)
- P64A3.exe (PID: 4700)
- KC51T.exe (PID: 6012)
- 26907.exe (PID: 5244)
- F0NQ8.exe (PID: 724)
- 31891.exe (PID: 6160)
- UJDI0.exe (PID: 1308)
- 48SB3.exe (PID: 368)
- 0M3WI.exe (PID: 5528)
- IW0KW.exe (PID: 4200)
- R060H.exe (PID: 1808)
- 4W23G.exe (PID: 5956)
- 931VD.exe (PID: 6208)
- V7776.exe (PID: 4160)
- YM6X3.exe (PID: 7076)
- 4W274.exe (PID: 532)
- 8O029.exe (PID: 4988)
- J042A.exe (PID: 4012)
- G0ANK.exe (PID: 1616)
- 18S8U.exe (PID: 3912)
- 11GI2.exe (PID: 2072)
- RFYJI.exe (PID: 6396)
- 34F17.exe (PID: 5448)
- K3RP1.exe (PID: 2800)
- N7TA3.exe (PID: 6568)
- 7W983.exe (PID: 4664)
- 517UZ.exe (PID: 6368)
- PRP6L.exe (PID: 5812)
- U42RD.exe (PID: 5304)
- UP1EQ.exe (PID: 6900)
- O81OI.exe (PID: 6856)
- 5CWSP.exe (PID: 928)
- E4GW8.exe (PID: 6916)
- GNC73.exe (PID: 5280)
- 1PR86.exe (PID: 6852)
- 907YG.exe (PID: 4288)
- 0562G.exe (PID: 7040)
- S09NQ.exe (PID: 5632)
- YA3ZA.exe (PID: 7052)
- Z7870.exe (PID: 3940)
- LVB60.exe (PID: 6744)
- C2QR9.exe (PID: 6764)
- UYQQ1.exe (PID: 6796)
- ZLS8S.exe (PID: 4384)
- 0JE0W.exe (PID: 5012)
- 9GC6R.exe (PID: 3528)
- 1SLJB.exe (PID: 5920)
- 092JI.exe (PID: 2536)
- 1511H.exe (PID: 1084)
- G94ZJ.exe (PID: 5716)
- 6PMI3.exe (PID: 4536)
- ZK2DO.exe (PID: 3768)
- G9X52.exe (PID: 1748)
- NT82L.exe (PID: 588)
- 68757.exe (PID: 3016)
- 7W3C2.exe (PID: 2744)
- C8Z9R.exe (PID: 2328)
- 0FKRR.exe (PID: 3628)
- Z2752.exe (PID: 2932)
- UVWWD.exe (PID: 6080)
- VT48N.exe (PID: 5960)
- 2R0EK.exe (PID: 6380)
- 26X40.exe (PID: 6780)
- 3M9PJ.exe (PID: 3704)
- XK1C3.exe (PID: 736)
- 96TZ2.exe (PID: 6484)
- 40S7S.exe (PID: 6556)
- 38WPW.exe (PID: 6588)
- H0DTU.exe (PID: 4668)
- 1Y8YQ.exe (PID: 6432)
- K6E5T.exe (PID: 6724)
- 0U8K3.exe (PID: 6840)
- C3OU8.exe (PID: 1492)
- 0W2Z8.exe (PID: 6948)
- W0MZX.exe (PID: 5088)
- 6BR15.exe (PID: 3648)
- 18YX1.exe (PID: 6788)
- 22ELF.exe (PID: 7036)
- 5XAYS.exe (PID: 7156)
- 1D453.exe (PID: 5900)
- Z882J.exe (PID: 7020)
- C3KMH.exe (PID: 4920)
- 5E8AY.exe (PID: 2920)
- LC22S.exe (PID: 6300)
- W3K13.exe (PID: 1360)
- JQH0B.exe (PID: 2252)
- I5E12.exe (PID: 1752)
- X1GXY.exe (PID: 2736)
- 27SJC.exe (PID: 4952)
- XWCT0.exe (PID: 3528)
- 7PR46.exe (PID: 1832)
- 58182.exe (PID: 5716)
- CB7Y4.exe (PID: 2536)
- 23NUQ.exe (PID: 3768)
- I1KNP.exe (PID: 1084)
- NQQR1.exe (PID: 6216)
- NFQ3K.exe (PID: 4536)
- P7EFE.exe (PID: 588)
- 3Y066.exe (PID: 3016)
- 273TK.exe (PID: 532)
- 39PMG.exe (PID: 2328)
- 59OG9.exe (PID: 3628)
- SBL81.exe (PID: 7076)
- V1YN9.exe (PID: 4012)
- 98R0N.exe (PID: 7120)
- 2GJ2G.exe (PID: 1616)
- 4KIX1.exe (PID: 6752)
- 3718U.exe (PID: 6520)
- I4V63.exe (PID: 5360)
- CGSA2.exe (PID: 6340)
- ZJB54.exe (PID: 6088)
- 057K9.exe (PID: 6692)
- 8FGC3.exe (PID: 5336)
- ZUY5E.exe (PID: 6708)
- J52RX.exe (PID: 6732)
- 4SA2F.exe (PID: 6756)
- SAQM6.exe (PID: 5116)
- 2X000.exe (PID: 6992)
Process checks computer location settings
- 02b945d796fcd22a5d43896a9385f3d0.exe (PID: 6660)
- 8K04O.exe (PID: 6788)
- M724R.exe (PID: 6852)
- N35I5.exe (PID: 6916)
- VWL0Y.exe (PID: 7040)
- MOWIB.exe (PID: 6976)
- S4888.exe (PID: 7160)
- TG1RQ.exe (PID: 636)
- 96X66.exe (PID: 1720)
- RUF25.exe (PID: 2524)
- 7N829.exe (PID: 1752)
- 60CJD.exe (PID: 5620)
- 6E7J0.exe (PID: 3956)
- 9FWSN.exe (PID: 1712)
- 4149S.exe (PID: 6184)
- 22MS6.exe (PID: 6168)
- 4PPS8.exe (PID: 3712)
- C4GDM.exe (PID: 3652)
- RF642.exe (PID: 6460)
- F1P8M.exe (PID: 6556)
- 37W17.exe (PID: 1572)
- NY046.exe (PID: 6604)
- 0D3RZ.exe (PID: 6656)
- 7NO21.exe (PID: 6348)
- 0M637.exe (PID: 6432)
- L4KXM.exe (PID: 6544)
- V5C9E.exe (PID: 6564)
- FFTO4.exe (PID: 6800)
- J666T.exe (PID: 6876)
- AA73Y.exe (PID: 6932)
- 64J33.exe (PID: 4708)
- OVM3L.exe (PID: 6980)
- 4Z37G.exe (PID: 7116)
- U5511.exe (PID: 7052)
- XE6NQ.exe (PID: 1012)
- N94X6.exe (PID: 1636)
- 5D5H6.exe (PID: 920)
- UFH4K.exe (PID: 4548)
- B6P0D.exe (PID: 5840)
- R163X.exe (PID: 428)
- IZ7S7.exe (PID: 3500)
- 7K3Y8.exe (PID: 4360)
- 54O67.exe (PID: 3956)
- 1U1UA.exe (PID: 6184)
- KHE50.exe (PID: 3712)
- G7ZB5.exe (PID: 1712)
- 5X6M3.exe (PID: 6168)
- K7F8N.exe (PID: 3652)
- QY355.exe (PID: 6460)
- 1Y19C.exe (PID: 1572)
- 95K6H.exe (PID: 6620)
- PDK24.exe (PID: 6356)
- 96M0Q.exe (PID: 6568)
- 7863V.exe (PID: 6704)
- 1OF85.exe (PID: 6680)
- V1QEJ.exe (PID: 6544)
- UP490.exe (PID: 6332)
- 9DTLC.exe (PID: 6856)
- 3T82E.exe (PID: 5552)
- Y3227.exe (PID: 7016)
- 54Y7O.exe (PID: 7136)
- TJ2C4.exe (PID: 7112)
- CG2EB.exe (PID: 4232)
- 0N0W8.exe (PID: 3740)
- V10Q0.exe (PID: 1016)
- 5KS90.exe (PID: 5012)
- 4X0SN.exe (PID: 2084)
- 5512W.exe (PID: 1412)
- Y301X.exe (PID: 1428)
- 0T21K.exe (PID: 624)
- 984K3.exe (PID: 4752)
- TJ1QY.exe (PID: 4148)
- 1D62T.exe (PID: 3692)
- NB0TV.exe (PID: 6148)
- 5V5IZ.exe (PID: 4988)
- Y8U72.exe (PID: 4072)
- E5LC4.exe (PID: 1616)
- BZQD7.exe (PID: 6036)
- 025VG.exe (PID: 6512)
- 6810I.exe (PID: 6364)
- EEO8S.exe (PID: 6408)
- G9V27.exe (PID: 1788)
- O9WE2.exe (PID: 6344)
- 99ZL1.exe (PID: 6688)
- 77712.exe (PID: 6652)
- 711V7.exe (PID: 6888)
- QB88D.exe (PID: 6956)
- 9V3PZ.exe (PID: 6968)
- NHU4R.exe (PID: 7124)
- TX9MD.exe (PID: 7000)
- 4P82A.exe (PID: 7052)
- AEM4R.exe (PID: 7164)
- T7LZ7.exe (PID: 2920)
- SFASV.exe (PID: 1444)
- 986B7.exe (PID: 5924)
- X2726.exe (PID: 5196)
- KS0I5.exe (PID: 2084)
- NPS64.exe (PID: 2484)
- HZR1Y.exe (PID: 4752)
- 6AE1C.exe (PID: 4148)
- 4O9T8.exe (PID: 4960)
- N7R0N.exe (PID: 6220)
- 44WJS.exe (PID: 3724)
- 87U7P.exe (PID: 6380)
- 16LFW.exe (PID: 6508)
- 3BZAL.exe (PID: 5076)
- Z9Z56.exe (PID: 6036)
- 3O9X3.exe (PID: 6404)
- 01V42.exe (PID: 324)
- ZM1H7.exe (PID: 6708)
- YM3X2.exe (PID: 6644)
- WQ418.exe (PID: 6364)
- CI071.exe (PID: 6832)
- 42EZ1.exe (PID: 2600)
- 56SEV.exe (PID: 6960)
- K46TA.exe (PID: 5036)
- 9954Z.exe (PID: 7016)
- 4W0IT.exe (PID: 6996)
- ZM2KN.exe (PID: 6780)
- 4WS91.exe (PID: 6740)
- 04076.exe (PID: 4920)
- 18OM7.exe (PID: 4196)
- G1CB2.exe (PID: 5056)
- 6VN2K.exe (PID: 5904)
- AWJEF.exe (PID: 5196)
- 0NMLH.exe (PID: 1720)
- TOI8L.exe (PID: 3688)
- 22OGZ.exe (PID: 5092)
- KL948.exe (PID: 6208)
- 0654P.exe (PID: 5956)
- 4F4X6.exe (PID: 4160)
- 4B305.exe (PID: 3692)
- A5ZI9.exe (PID: 6244)
- 6T8NY.exe (PID: 5004)
- TOY05.exe (PID: 5076)
- 5EJSO.exe (PID: 6508)
- 5556W.exe (PID: 6036)
- 9IU9X.exe (PID: 6428)
- EV7AO.exe (PID: 6372)
- 8X41S.exe (PID: 6756)
- WE52B.exe (PID: 6348)
- XU9T1.exe (PID: 6716)
- J7661.exe (PID: 6544)
- 70O52.exe (PID: 6856)
- ICQ0E.exe (PID: 5036)
- HJB1G.exe (PID: 6984)
- FGRMG.exe (PID: 4288)
- LXSLE.exe (PID: 6980)
- 1I18S.exe (PID: 4024)
- 3FFMR.exe (PID: 6740)
- DZB8M.exe (PID: 3740)
- 80EQ4.exe (PID: 4384)
- 57D53.exe (PID: 4704)
- I7G22.exe (PID: 1944)
- 01CH8.exe (PID: 5196)
- 85007.exe (PID: 3820)
- 2E1Y3.exe (PID: 3956)
- IL366.exe (PID: 2480)
- 4VB81.exe (PID: 2084)
- C605X.exe (PID: 6188)
- D64AQ.exe (PID: 1120)
- N991U.exe (PID: 6288)
- 9031Q.exe (PID: 3104)
- K3VR8.exe (PID: 6560)
- 03553.exe (PID: 2916)
- HF7S5.exe (PID: 6448)
- K3YNW.exe (PID: 6396)
- 7UEBK.exe (PID: 364)
- 8OA0O.exe (PID: 1788)
- B30WC.exe (PID: 6364)
- R0OE4.exe (PID: 6660)
- DN635.exe (PID: 6528)
- SSN20.exe (PID: 2396)
- 927G1.exe (PID: 6860)
- U7JAA.exe (PID: 7020)
- 10W8W.exe (PID: 6996)
- 6IY2Z.exe (PID: 6788)
- OYH7Y.exe (PID: 7032)
- S9403.exe (PID: 7140)
- R3G15.exe (PID: 7164)
- B4YQ1.exe (PID: 7120)
- DNFUA.exe (PID: 1100)
- 56ISU.exe (PID: 6108)
- 74C91.exe (PID: 4928)
- H7221.exe (PID: 712)
- 907V7.exe (PID: 1428)
- AC1C4.exe (PID: 3500)
- 73875.exe (PID: 5372)
- O624I.exe (PID: 4484)
- 4T6WK.exe (PID: 6216)
- PQ12M.exe (PID: 4160)
- 365H2.exe (PID: 3960)
- OA72T.exe (PID: 4416)
- S60O0.exe (PID: 7072)
- 79476.exe (PID: 1604)
- LP845.exe (PID: 5396)
- PL6GL.exe (PID: 4500)
- 29X1Z.exe (PID: 6360)
- 04OHX.exe (PID: 6368)
- 58N6V.exe (PID: 6804)
- L4ZXZ.exe (PID: 6420)
- Q1BAQ.exe (PID: 6540)
- 9TMG1.exe (PID: 6908)
- H3VN5.exe (PID: 6880)
- WG1B7.exe (PID: 6972)
- 218P8.exe (PID: 1364)
- H1062.exe (PID: 1684)
- 657LD.exe (PID: 2684)
- 440KC.exe (PID: 6968)
- 4550G.exe (PID: 7000)
- Q0D99.exe (PID: 6784)
- 88OC4.exe (PID: 4024)
- X45W2.exe (PID: 5840)
- E28H6.exe (PID: 628)
- 54676.exe (PID: 1360)
- Z04H5.exe (PID: 1412)
- 900FK.exe (PID: 5720)
- D3Z0L.exe (PID: 6016)
- 24N9H.exe (PID: 2524)
- ITBP2.exe (PID: 5716)
- AVP68.exe (PID: 5936)
- JQX44.exe (PID: 5932)
- 49IS2.exe (PID: 4744)
- E3WGD.exe (PID: 3712)
- MNE8L.exe (PID: 1120)
- PJVCB.exe (PID: 3652)
- KU8HX.exe (PID: 4540)
- 0584N.exe (PID: 4140)
- MP9TW.exe (PID: 6560)
- 8W6R3.exe (PID: 5448)
- QM881.exe (PID: 4500)
- 2F2D3.exe (PID: 6424)
- TQ9J4.exe (PID: 6304)
- WEA53.exe (PID: 6732)
- Q2YBF.exe (PID: 6664)
- 42OLV.exe (PID: 6336)
- SKUOI.exe (PID: 6864)
- 92J0G.exe (PID: 6892)
- 5Z891.exe (PID: 6852)
- T78X0.exe (PID: 4312)
- 6K4Q2.exe (PID: 7008)
- 8G52R.exe (PID: 6496)
- YTYEA.exe (PID: 7020)
- 2116Y.exe (PID: 6780)
- PK2F1.exe (PID: 7120)
- QI699.exe (PID: 5836)
- V15ZZ.exe (PID: 7160)
- N0M02.exe (PID: 2796)
- 276YT.exe (PID: 3052)
- S74IS.exe (PID: 4628)
- W9609.exe (PID: 624)
- V723N.exe (PID: 5920)
- 0F1R3.exe (PID: 5372)
- 378S4.exe (PID: 3500)
- 8B952.exe (PID: 5148)
- Y90VV.exe (PID: 4284)
- D6W0N.exe (PID: 6316)
- 66LAL.exe (PID: 4492)
- 0I313.exe (PID: 5592)
- Q8W2L.exe (PID: 4072)
- YY598.exe (PID: 4140)
- 8F0F2.exe (PID: 5752)
- 9A9Q6.exe (PID: 6560)
- 8L8RH.exe (PID: 5448)
- D6U26.exe (PID: 4500)
- D1297.exe (PID: 6364)
- 1IWE3.exe (PID: 5896)
- D1BGI.exe (PID: 6828)
- 39YZ2.exe (PID: 6748)
- 3Y47A.exe (PID: 6928)
- TQBTR.exe (PID: 6532)
- 5COD3.exe (PID: 1512)
- MIA45.exe (PID: 2396)
- 91U26.exe (PID: 7048)
- R3C14.exe (PID: 6272)
- U8873.exe (PID: 6980)
- 78MU5.exe (PID: 3624)
- 5W26I.exe (PID: 5504)
- OY7FM.exe (PID: 1568)
- B581C.exe (PID: 6204)
- 911MO.exe (PID: 4920)
- 4JAG8.exe (PID: 5428)
- 1H060.exe (PID: 5904)
- VR6V2.exe (PID: 5064)
- 64VPY.exe (PID: 1724)
- I4KI1.exe (PID: 2448)
- DAB9M.exe (PID: 3688)
- 7UXSQ.exe (PID: 3956)
- 22W50.exe (PID: 6112)
- E8XAX.exe (PID: 4752)
- VV4I9.exe (PID: 6440)
- J4Z28.exe (PID: 3808)
- UUG01.exe (PID: 6308)
- 4SJ9O.exe (PID: 6148)
- A52HG.exe (PID: 4480)
- P17LK.exe (PID: 6376)
- 3L0V2.exe (PID: 6356)
- 9564H.exe (PID: 6640)
- 3OXE1.exe (PID: 6696)
- IUJ23.exe (PID: 6036)
- V4T76.exe (PID: 6756)
- UMI08.exe (PID: 6704)
- 578OY.exe (PID: 6800)
- 8UWQ3.exe (PID: 6900)
- JF52M.exe (PID: 6956)
- 209JO.exe (PID: 7128)
- 3C1Y2.exe (PID: 6964)
- K1582.exe (PID: 7024)
- 4A165.exe (PID: 7112)
- 2OHZ2.exe (PID: 72)
- EMUJU.exe (PID: 4056)
- BPD2E.exe (PID: 7152)
- IAL9T.exe (PID: 4916)
- 372V7.exe (PID: 920)
- 57J9P.exe (PID: 2736)
- M92AK.exe (PID: 5380)
- 2MITN.exe (PID: 4996)
- K5W7B.exe (PID: 1720)
- 79VU8.exe (PID: 3672)
- 2Y8G5.exe (PID: 2084)
- 1NG25.exe (PID: 3956)
- 28RHB.exe (PID: 2104)
- A1588.exe (PID: 372)
- MZ756.exe (PID: 4744)
- 484O0.exe (PID: 1628)
- 8T5W7.exe (PID: 6168)
- R71UH.exe (PID: 2336)
- 6734R.exe (PID: 7076)
- S77ZS.exe (PID: 6444)
- 6O2P1.exe (PID: 5960)
- C68Q1.exe (PID: 892)
- D272S.exe (PID: 6376)
- 0K35Y.exe (PID: 3732)
- QJ8Z3.exe (PID: 6512)
- E41LT.exe (PID: 4140)
- HF969.exe (PID: 6352)
- 2MZ2Q.exe (PID: 6556)
- 9H4EX.exe (PID: 4612)
- 628E6.exe (PID: 5812)
- TJ7S5.exe (PID: 6368)
- 560K5.exe (PID: 4560)
- Y1HQL.exe (PID: 6536)
- LTN7A.exe (PID: 6564)
- 663MU.exe (PID: 6644)
- FSFC1.exe (PID: 6928)
- 152U6.exe (PID: 6464)
- 8436V.exe (PID: 5208)
- GII08.exe (PID: 4156)
- A2EW5.exe (PID: 6776)
- ZKTPC.exe (PID: 1512)
- 9RM7K.exe (PID: 7000)
- 3N095.exe (PID: 7024)
- 67U4K.exe (PID: 7116)
- L9W60.exe (PID: 4020)
- IY10Q.exe (PID: 4748)
- 81GL1.exe (PID: 2252)
- E2KX5.exe (PID: 1016)
- Z1RSM.exe (PID: 4952)
- FHSP4.exe (PID: 712)
- TKQ3J.exe (PID: 2620)
- 8480V.exe (PID: 5084)
- 068DL.exe (PID: 6156)
- 089T7.exe (PID: 1508)
- B85MZ.exe (PID: 1648)
- 4S733.exe (PID: 6216)
- U9365.exe (PID: 6164)
- OJEV0.exe (PID: 2220)
- V8G6K.exe (PID: 6188)
- U8V9I.exe (PID: 1792)
- DBCMM.exe (PID: 6440)
- 68RFL.exe (PID: 6248)
- K55BB.exe (PID: 3100)
- ZY185.exe (PID: 4540)
- 5IVAU.exe (PID: 3412)
- S9M3S.exe (PID: 5656)
- 6305L.exe (PID: 6632)
- CVM16.exe (PID: 6592)
- K5TT2.exe (PID: 4232)
- 8XO1K.exe (PID: 6512)
- E2ZYL.exe (PID: 6344)
- 4ZD4X.exe (PID: 6084)
- 94704.exe (PID: 5304)
- G0OLR.exe (PID: 6296)
- K5299.exe (PID: 6304)
- EM8T0.exe (PID: 4560)
- 1O366.exe (PID: 6660)
- VPYHF.exe (PID: 6564)
- 941WE.exe (PID: 6644)
- 345DF.exe (PID: 6464)
- 39Q8V.exe (PID: 7132)
- TN94I.exe (PID: 6104)
- 4RWER.exe (PID: 5080)
- 69327.exe (PID: 4708)
- J4H9Z.exe (PID: 6760)
- 26GP2.exe (PID: 3708)
- F3P05.exe (PID: 4196)
- 6X74A.exe (PID: 4748)
- KH3F7.exe (PID: 7116)
- 2013B.exe (PID: 4020)
- X630B.exe (PID: 2252)
- 06MPS.exe (PID: 1016)
- 56795.exe (PID: 4952)
- LSVR6.exe (PID: 712)
- 20GY4.exe (PID: 3688)
- ODDV0.exe (PID: 32)
- 624BS.exe (PID: 5464)
- 6922J.exe (PID: 3644)
- G331I.exe (PID: 6184)
- F96VK.exe (PID: 5444)
- I378K.exe (PID: 2044)
- W833D.exe (PID: 5256)
- 2HF5B.exe (PID: 2308)
- 0EWX4.exe (PID: 924)
- A7S01.exe (PID: 6440)
- Z7HM4.exe (PID: 3104)
- 97C14.exe (PID: 6148)
- 6YYWZ.exe (PID: 3756)
- AHNPY.exe (PID: 608)
- 7444I.exe (PID: 2384)
- H49G5.exe (PID: 4036)
- 148Q3.exe (PID: 6816)
- 6M3A4.exe (PID: 4500)
- 8Q395.exe (PID: 6408)
- 015P1.exe (PID: 4152)
- O194N.exe (PID: 5896)
- 59CT2.exe (PID: 4532)
- PQ42C.exe (PID: 6304)
- 5FDRF.exe (PID: 5356)
- 4YKUD.exe (PID: 6708)
- L71O9.exe (PID: 6876)
- 2M418.exe (PID: 1492)
- P3GK8.exe (PID: 6956)
- 41263.exe (PID: 7028)
- 0K586.exe (PID: 4264)
- I5FF3.exe (PID: 5072)
- 8C0ZP.exe (PID: 7016)
- QL8WT.exe (PID: 5608)
- 7N28X.exe (PID: 4488)
- 8CUGN.exe (PID: 1488)
- AOWJF.exe (PID: 5056)
- 58X31.exe (PID: 1276)
- 2WOYO.exe (PID: 6548)
- P64A3.exe (PID: 4700)
- 98N83.exe (PID: 6108)
- KC51T.exe (PID: 6012)
- 26907.exe (PID: 5244)
- 31891.exe (PID: 6160)
- F0NQ8.exe (PID: 724)
- 48SB3.exe (PID: 368)
- UJDI0.exe (PID: 1308)
- IW0KW.exe (PID: 4200)
- 0M3WI.exe (PID: 5528)
- 4W23G.exe (PID: 5956)
- R060H.exe (PID: 1808)
- V7776.exe (PID: 4160)
- 931VD.exe (PID: 6208)
- 4W274.exe (PID: 532)
- 8O029.exe (PID: 4988)
- YM6X3.exe (PID: 7076)
- J042A.exe (PID: 4012)
- 18S8U.exe (PID: 3912)
- G0ANK.exe (PID: 1616)
- RFYJI.exe (PID: 6396)
- K3RP1.exe (PID: 2800)
- 11GI2.exe (PID: 2072)
- 34F17.exe (PID: 5448)
- 7W983.exe (PID: 4664)
- N7TA3.exe (PID: 6568)
- PRP6L.exe (PID: 5812)
- U42RD.exe (PID: 5304)
- 517UZ.exe (PID: 6368)
- UP1EQ.exe (PID: 6900)
- 5CWSP.exe (PID: 928)
- E4GW8.exe (PID: 6916)
- O81OI.exe (PID: 6856)
- 1PR86.exe (PID: 6852)
- 907YG.exe (PID: 4288)
- GNC73.exe (PID: 5280)
- S09NQ.exe (PID: 5632)
- YA3ZA.exe (PID: 7052)
- 0562G.exe (PID: 7040)
- LVB60.exe (PID: 6744)
- C2QR9.exe (PID: 6764)
- Z7870.exe (PID: 3940)
- UYQQ1.exe (PID: 6796)
- ZLS8S.exe (PID: 4384)
- 0JE0W.exe (PID: 5012)
- 1SLJB.exe (PID: 5920)
- 092JI.exe (PID: 2536)
- 9GC6R.exe (PID: 3528)
- G94ZJ.exe (PID: 5716)
- ZK2DO.exe (PID: 3768)
- 1511H.exe (PID: 1084)
- G9X52.exe (PID: 1748)
- 6PMI3.exe (PID: 4536)
- 68757.exe (PID: 3016)
- C8Z9R.exe (PID: 2328)
- NT82L.exe (PID: 588)
- Z2752.exe (PID: 2932)
- 7W3C2.exe (PID: 2744)
- UVWWD.exe (PID: 6080)
- 0FKRR.exe (PID: 3628)
- 2R0EK.exe (PID: 6380)
- 3M9PJ.exe (PID: 3704)
- VT48N.exe (PID: 5960)
- 26X40.exe (PID: 6780)
- XK1C3.exe (PID: 736)
- 38WPW.exe (PID: 6588)
- 96TZ2.exe (PID: 6484)
- 40S7S.exe (PID: 6556)
- H0DTU.exe (PID: 4668)
- 1Y8YQ.exe (PID: 6432)
- 0U8K3.exe (PID: 6840)
- K6E5T.exe (PID: 6724)
- 0W2Z8.exe (PID: 6948)
- C3OU8.exe (PID: 1492)
- 6BR15.exe (PID: 3648)
- 18YX1.exe (PID: 6788)
- W0MZX.exe (PID: 5088)
- 5XAYS.exe (PID: 7156)
- 22ELF.exe (PID: 7036)
- Z882J.exe (PID: 7020)
- 1D453.exe (PID: 5900)
- 5E8AY.exe (PID: 2920)
- C3KMH.exe (PID: 4920)
- W3K13.exe (PID: 1360)
- LC22S.exe (PID: 6300)
- I5E12.exe (PID: 1752)
- JQH0B.exe (PID: 2252)
- 27SJC.exe (PID: 4952)
- X1GXY.exe (PID: 2736)
- 7PR46.exe (PID: 1832)
- XWCT0.exe (PID: 3528)
- CB7Y4.exe (PID: 2536)
- 58182.exe (PID: 5716)
- I1KNP.exe (PID: 1084)
- 23NUQ.exe (PID: 3768)
- NQQR1.exe (PID: 6216)
- NFQ3K.exe (PID: 4536)
- 3Y066.exe (PID: 3016)
- P7EFE.exe (PID: 588)
- 273TK.exe (PID: 532)
- SBL81.exe (PID: 7076)
- 39PMG.exe (PID: 2328)
- V1YN9.exe (PID: 4012)
- 59OG9.exe (PID: 3628)
- 2GJ2G.exe (PID: 1616)
- 98R0N.exe (PID: 7120)
- 3718U.exe (PID: 6520)
- ZJB54.exe (PID: 6088)
- CGSA2.exe (PID: 6340)
- 4KIX1.exe (PID: 6752)
- 8FGC3.exe (PID: 5336)
- I4V63.exe (PID: 5360)
- J52RX.exe (PID: 6732)
- 057K9.exe (PID: 6692)
- ZUY5E.exe (PID: 6708)
- 4SA2F.exe (PID: 6756)
- 2X000.exe (PID: 6992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (27.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (24.2) |
| .exe | | | UPX compressed Win32 Executable (23.7) |
| .scr | | | Windows screen saver (11.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:04:10 17:28:39+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 389120 |
| InitializedDataSize: | 24576 |
| UninitializedDataSize: | 864256 |
| EntryPoint: | 0x9add5 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
689
Monitored processes
574
Malicious processes
358
Suspicious processes
214
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Users\admin\Desktop\ODDV0.exe" | C:\Users\admin\Desktop\ODDV0.exe | 20GY4.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 72 | "C:\Users\admin\Desktop\2OHZ2.exe" | C:\Users\admin\Desktop\2OHZ2.exe | 4A165.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 324 | "C:\Users\admin\Desktop\01V42.exe" | C:\Users\admin\Desktop\01V42.exe | Z9Z56.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 364 | "C:\Users\admin\Desktop\7UEBK.exe" | C:\Users\admin\Desktop\7UEBK.exe | K3YNW.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 368 | "C:\Users\admin\Desktop\48SB3.exe" | C:\Users\admin\Desktop\48SB3.exe | 31891.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 372 | "C:\Users\admin\Desktop\A1588.exe" | C:\Users\admin\Desktop\A1588.exe | 1NG25.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 428 | "C:\Users\admin\Desktop\R163X.exe" | C:\Users\admin\Desktop\R163X.exe | UFH4K.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 532 | "C:\Users\admin\Desktop\4W274.exe" | C:\Users\admin\Desktop\4W274.exe | V7776.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 532 | "C:\Users\admin\Desktop\273TK.exe" | C:\Users\admin\Desktop\273TK.exe | 39PMG.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 588 | "C:\Users\admin\Desktop\NT82L.exe" | C:\Users\admin\Desktop\NT82L.exe | 68757.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
395 838
Read events
391 358
Write events
4 480
Delete events
0
Modification events
| (PID) Process: | (6292) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6292) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6292) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6292) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6660) 02b945d796fcd22a5d43896a9385f3d0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6660) 02b945d796fcd22a5d43896a9385f3d0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6660) 02b945d796fcd22a5d43896a9385f3d0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6660) 02b945d796fcd22a5d43896a9385f3d0.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6788) 8K04O.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6788) 8K04O.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
571
Suspicious files
5
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LDR27GF3CK0H1FEST7J1.temp | — | |
MD5:— | SHA256:— | |||
| 6660 | 02b945d796fcd22a5d43896a9385f3d0.exe | C:\Users\admin\Desktop\8K04O.exe | executable | |
MD5:757A86A80E78846CCF2FB72D766BB8E6 | SHA256:3971AE23092ECCCF4B81E71C8D50B6DF5D624B624B95CB9C737A21D65E50F7C2 | |||
| 6292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF113b02.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6788 | 8K04O.exe | C:\Users\admin\Desktop\M724R.exe | executable | |
MD5:3A658351B4E707DBD6C3F344F314073B | SHA256:4F8E6034FCF8FC09C52BBF9548C2E39262E3E6FAD62BB852A65BB8ED8F154EF2 | |||
| 6292 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:6D8A6C824498E0AA554FC665BF0F7C49 | SHA256:B499C9F3F447B72E23B38A64E5C9D7582A9671EFA4805867D23BE93B7AC1F1C6 | |||
| 6852 | M724R.exe | C:\Users\admin\Desktop\N35I5.exe | executable | |
MD5:5A0A68E77801F06DF109C2CE363BFE20 | SHA256:19A29C17387A84E31065D6AC3499400BBB25B9C30B6A4D8B47B77F17C1455B53 | |||
| 6976 | MOWIB.exe | C:\Users\admin\Desktop\VWL0Y.exe | executable | |
MD5:BD149ED9D1939C647146301367A35213 | SHA256:3B4B3DDC535D7C8476A61E3CC51AF2867D19249267290E8677AA30375DEBE739 | |||
| 7160 | S4888.exe | C:\Users\admin\Desktop\TG1RQ.exe | executable | |
MD5:36284232C0618A950BF6DB7F9F86B30D | SHA256:6A9BAA1042AD24D277CC51C81FA22560F5752DD27781D2EADC7DD69783455CDD | |||
| 7040 | VWL0Y.exe | C:\Users\admin\Desktop\S4888.exe | executable | |
MD5:EA8E5E5348CD7E151DB5FE0089ED2BC6 | SHA256:FCBFE7D49633CBE5B339F4314D886DC546DB8BCCE13F2C9748E012E1823C4F1C | |||
| 6292 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0vt54kxb.5na.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
22
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5612 | svchost.exe | GET | 200 | 2.21.20.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
2308 | RUXIMICS.exe | GET | 200 | 2.21.20.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 2.21.20.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5612 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
2308 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
— | — | POST | 200 | 20.189.173.2:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
5612 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2308 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5140 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5612 | svchost.exe | 2.21.20.133:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4364 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
2308 | RUXIMICS.exe | 2.21.20.133:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5140 | MoUsoCoreWorker.exe | 2.21.20.133:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
5612 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
2308 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |