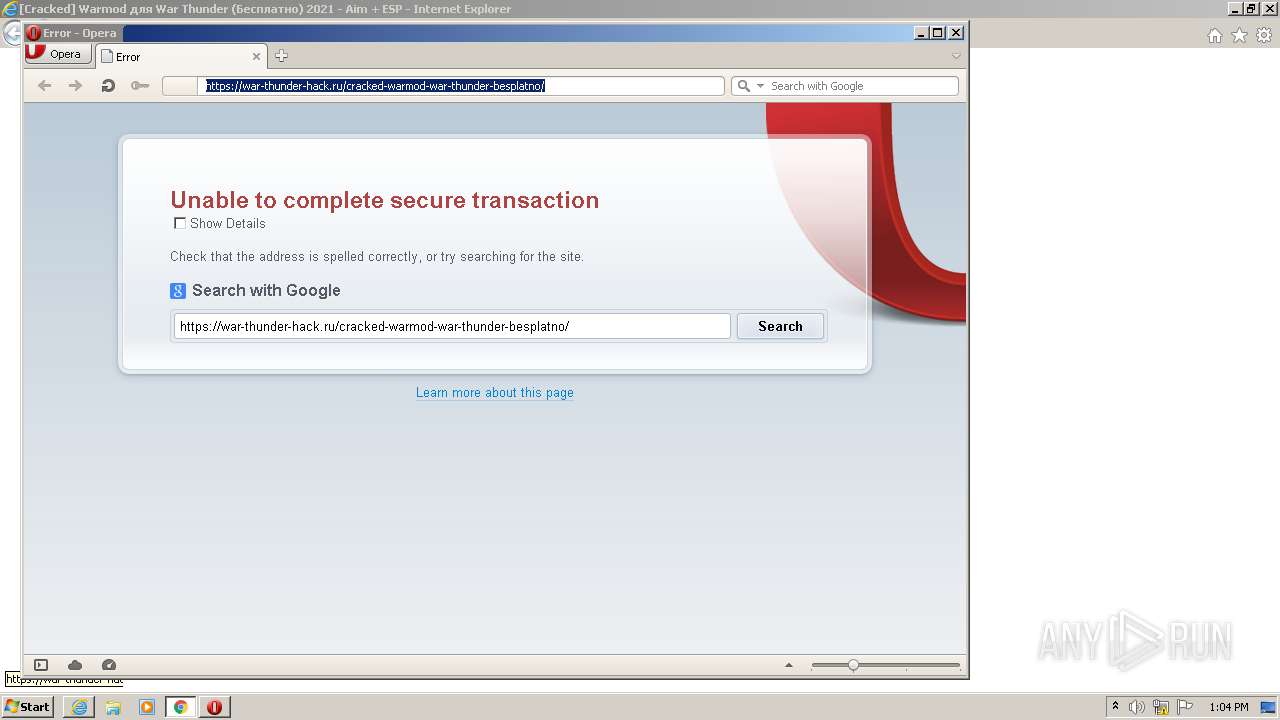
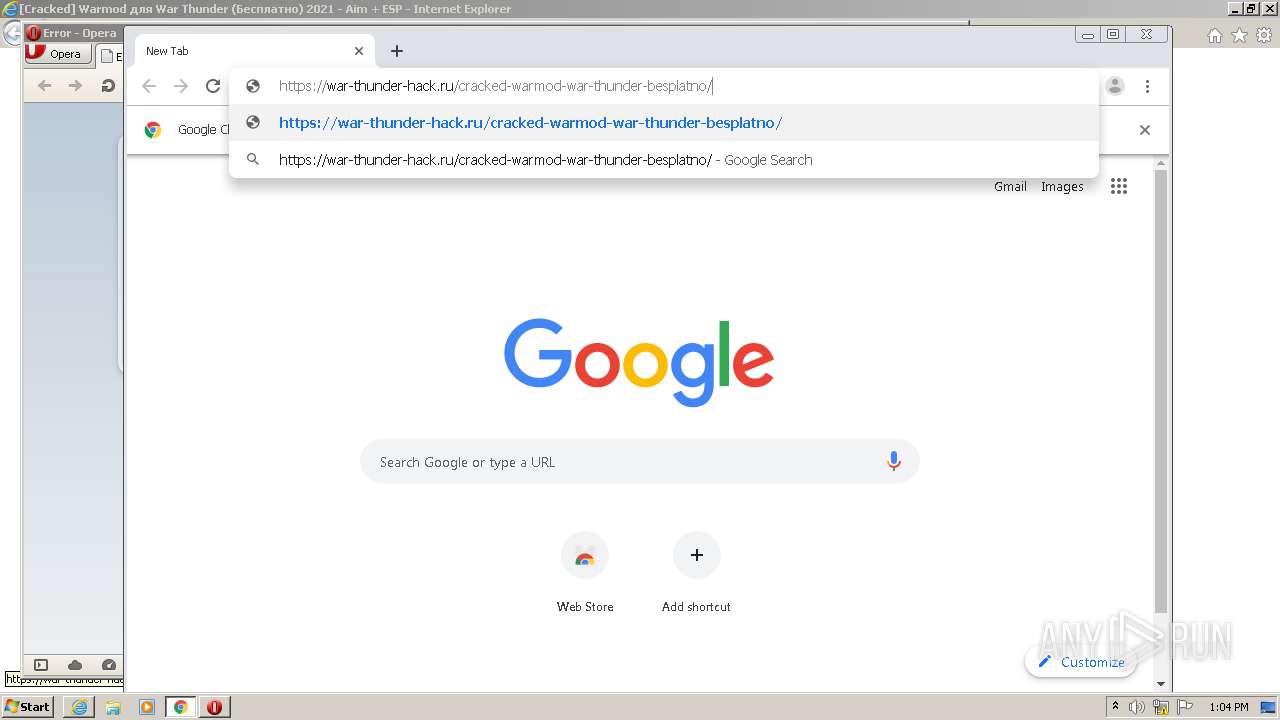
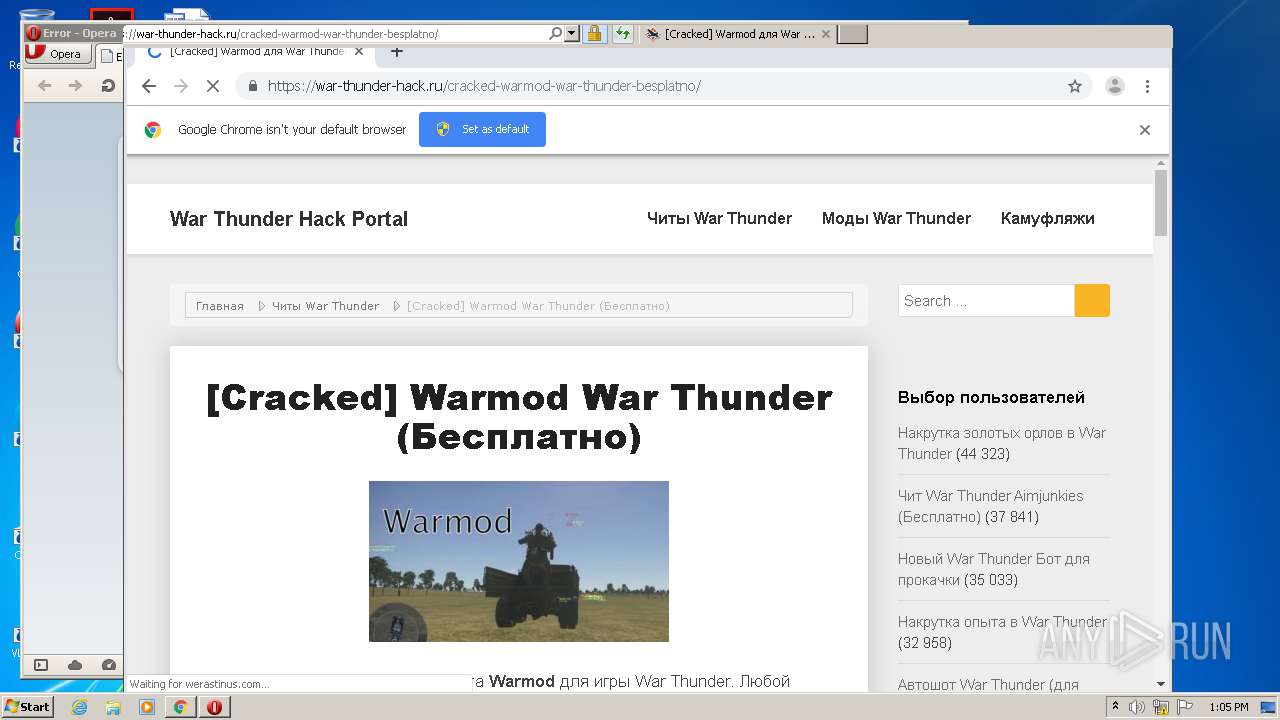
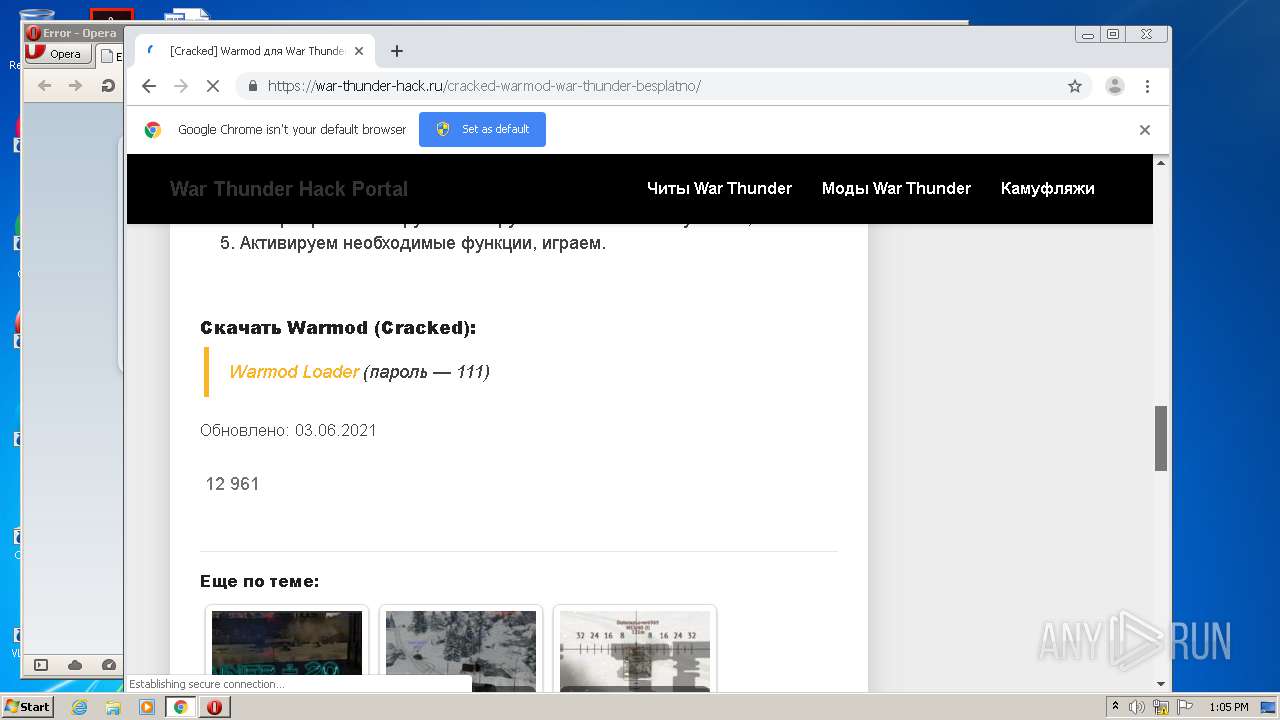
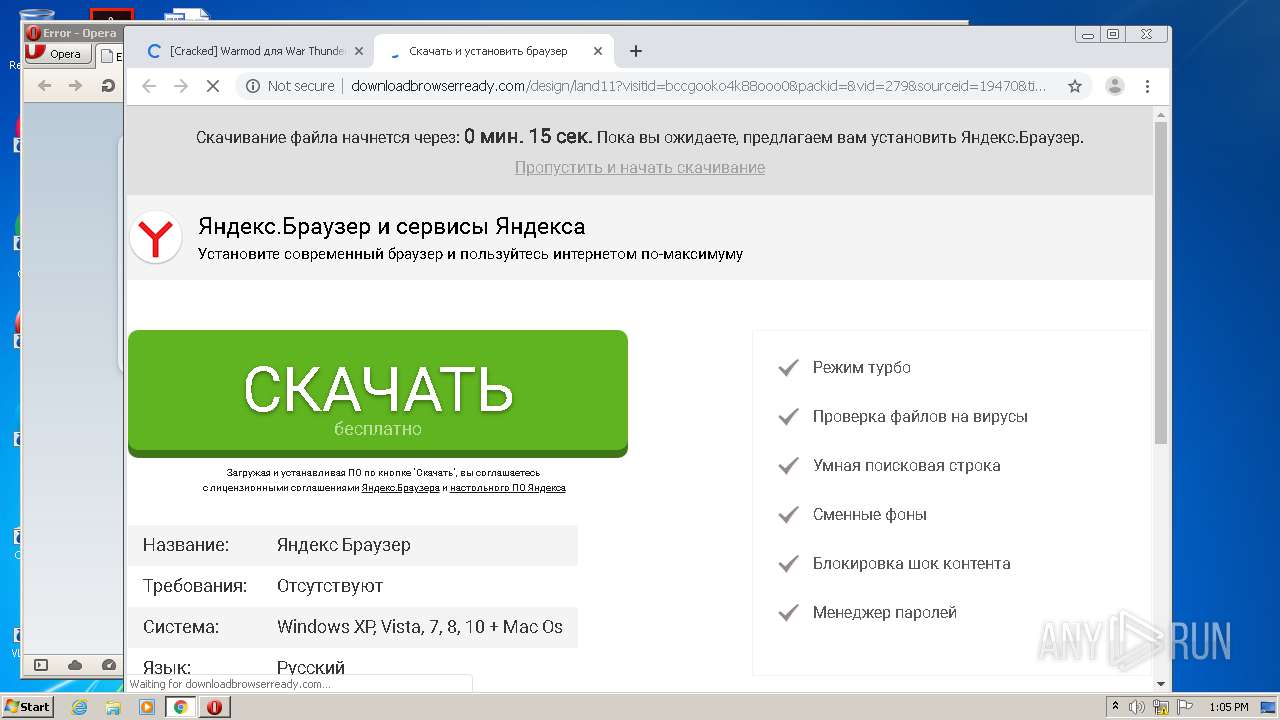
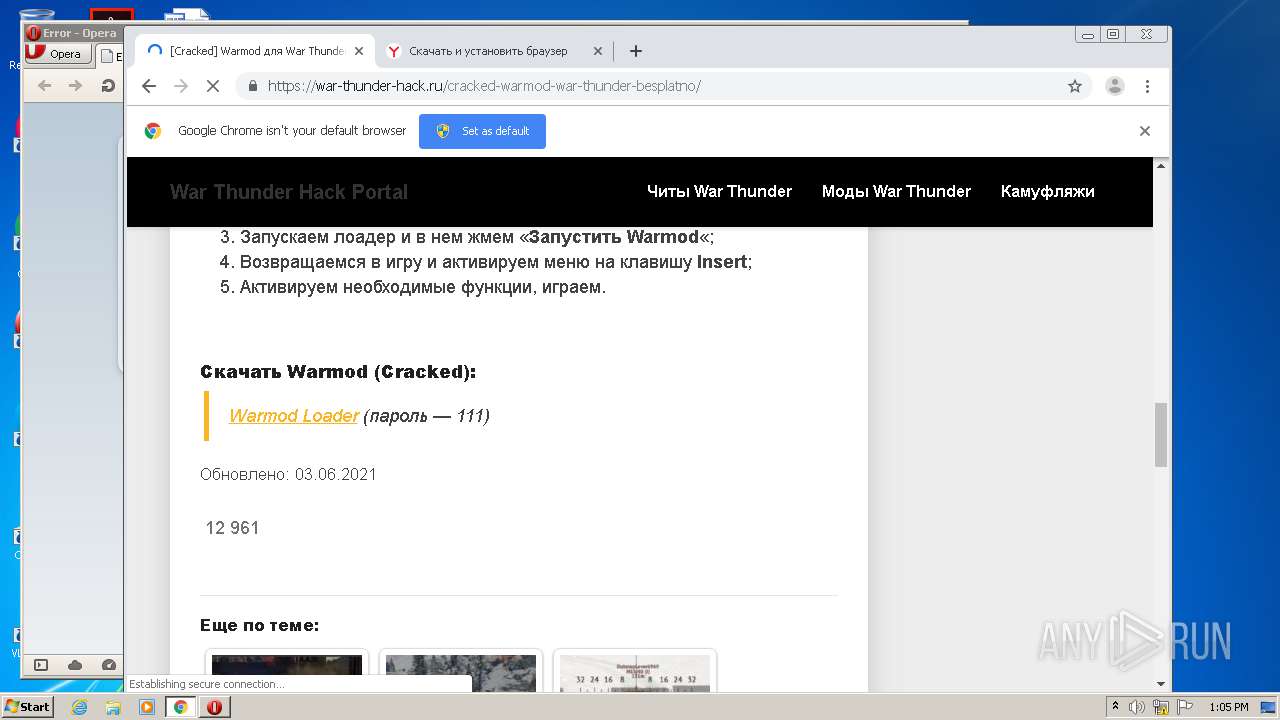
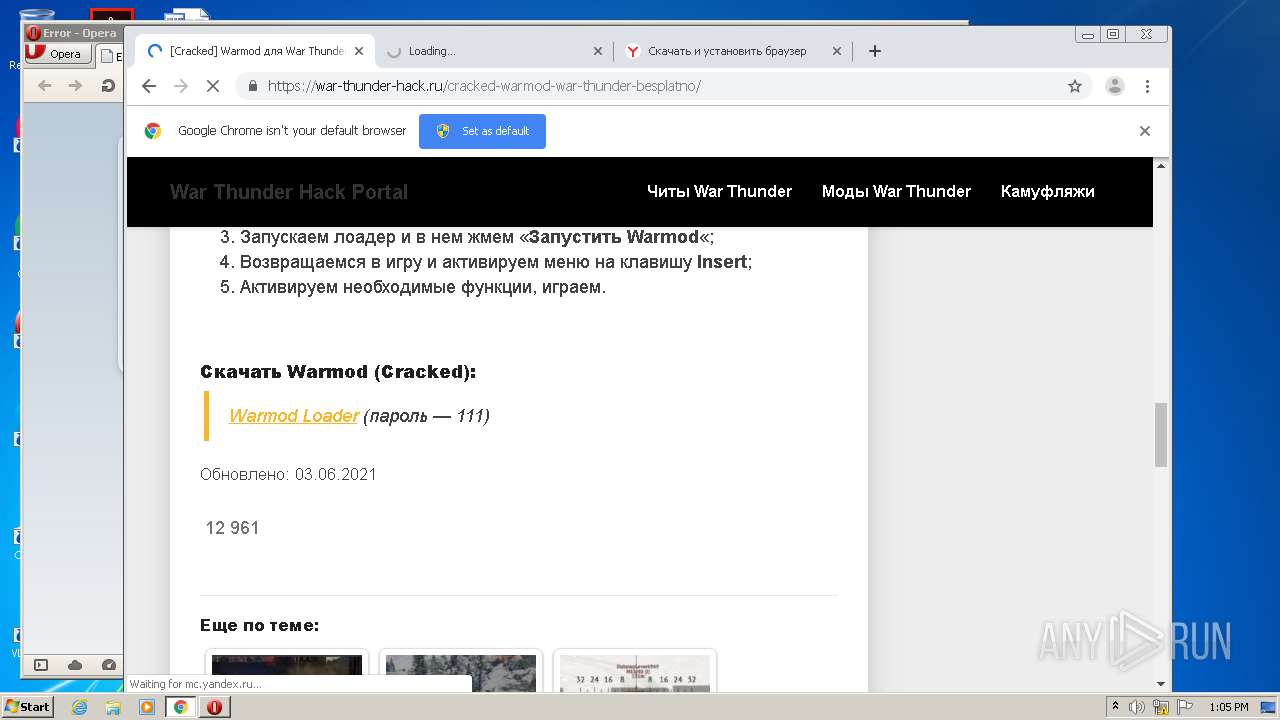
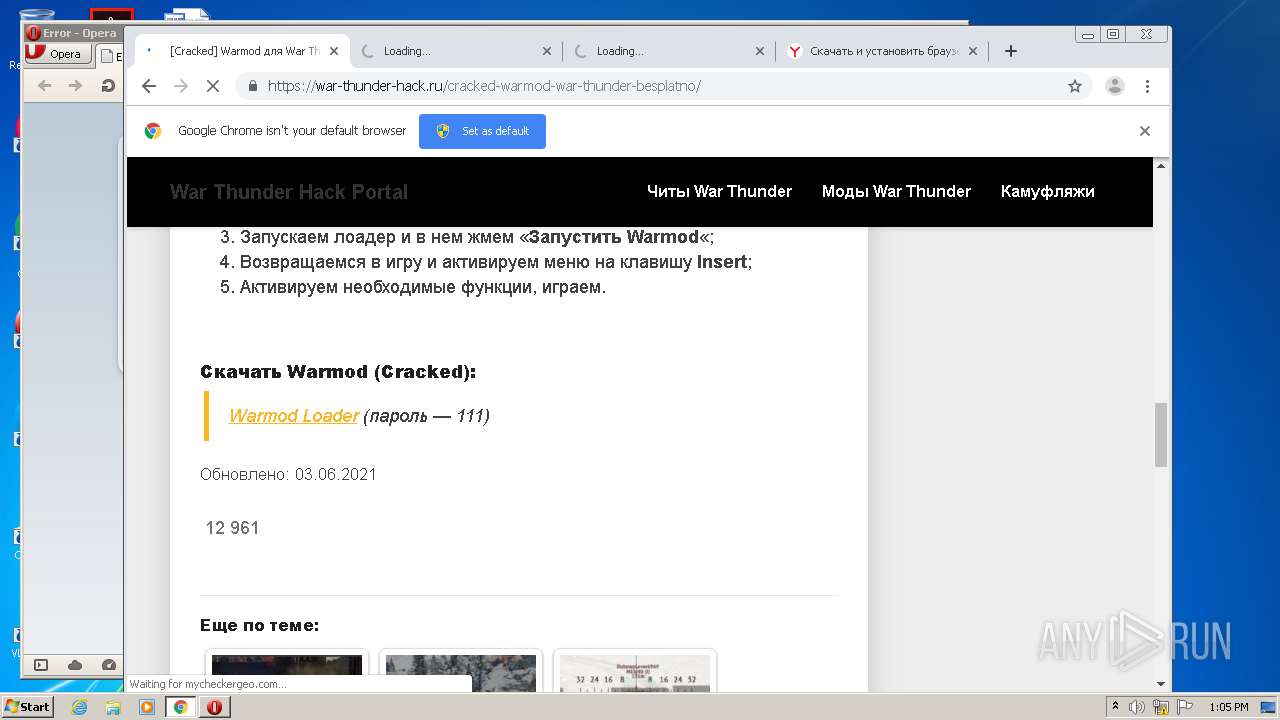
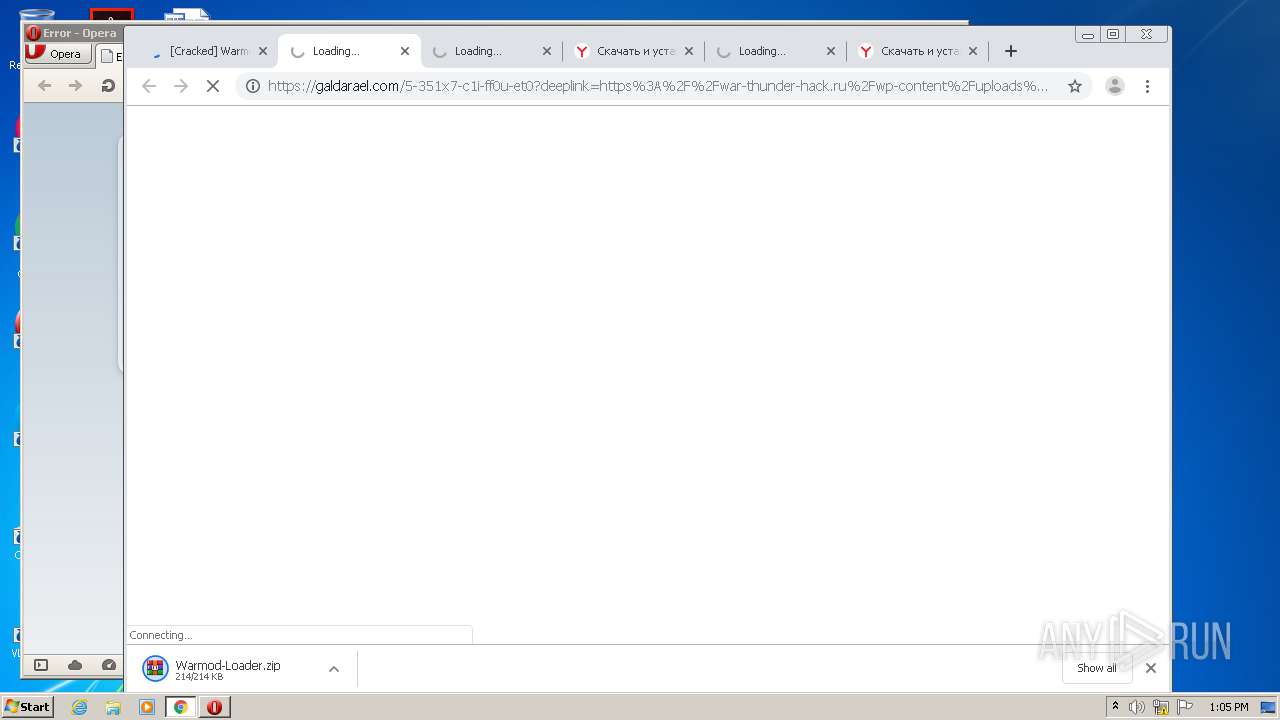
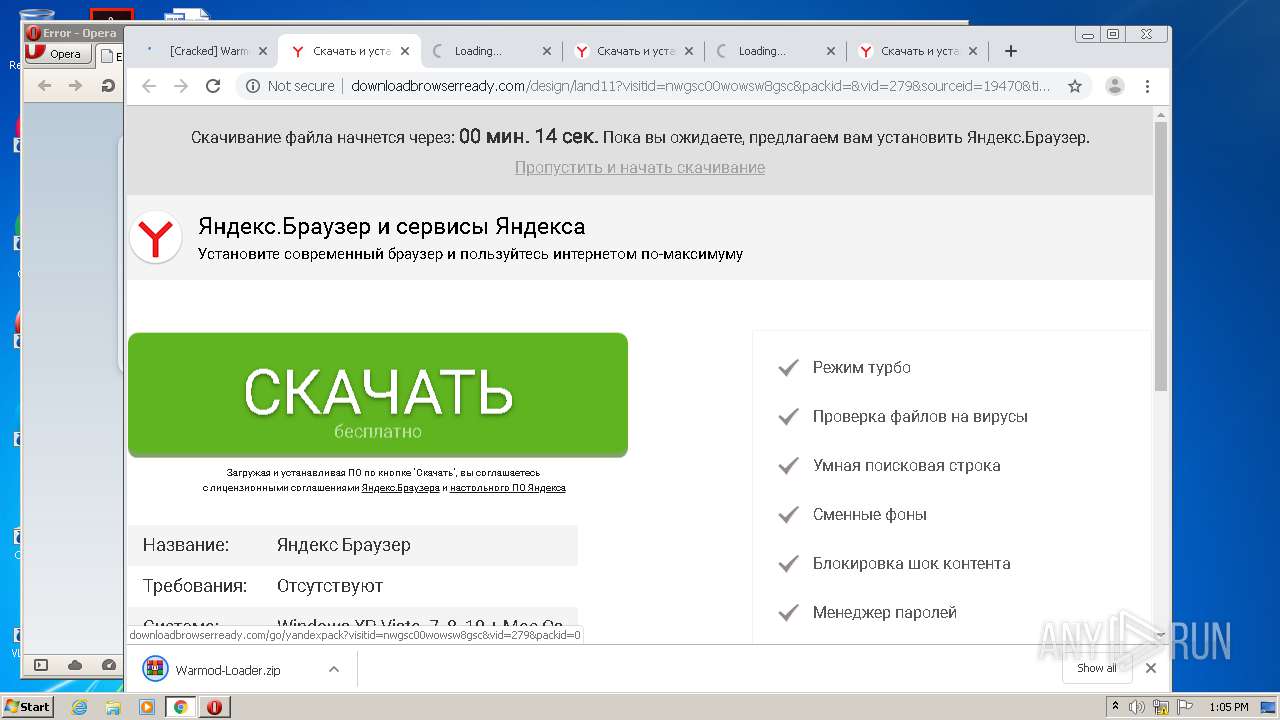
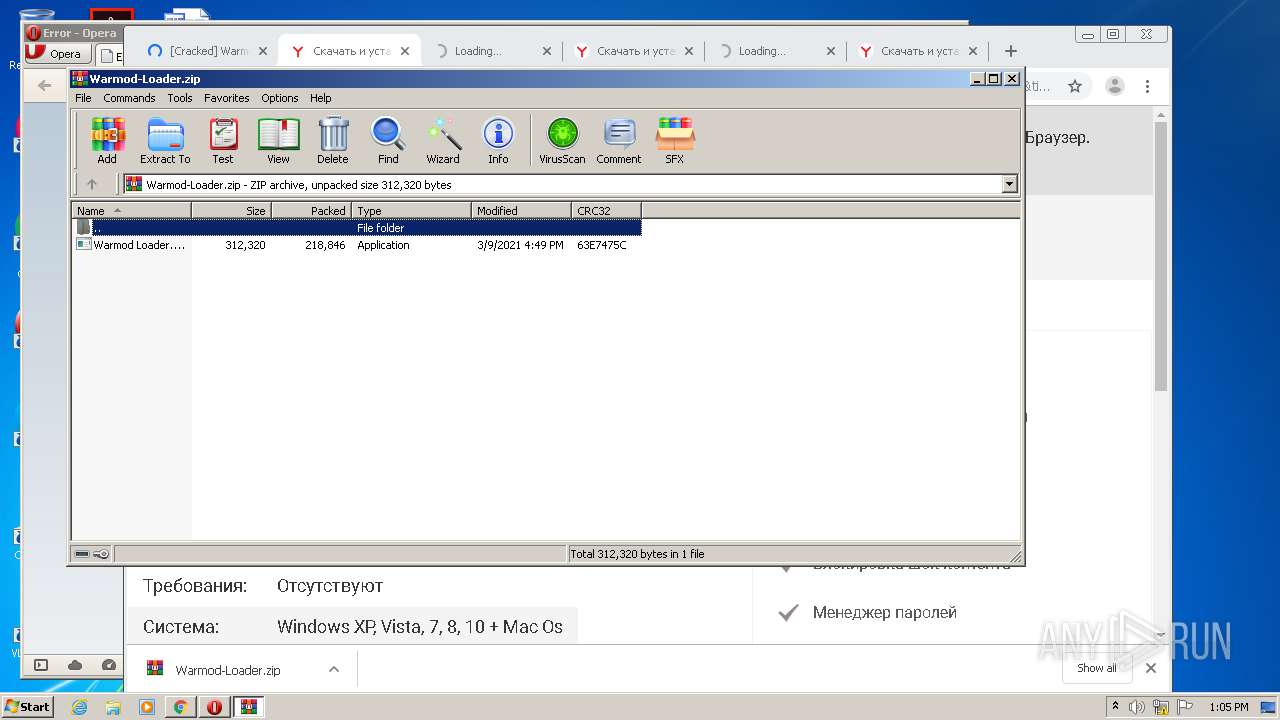
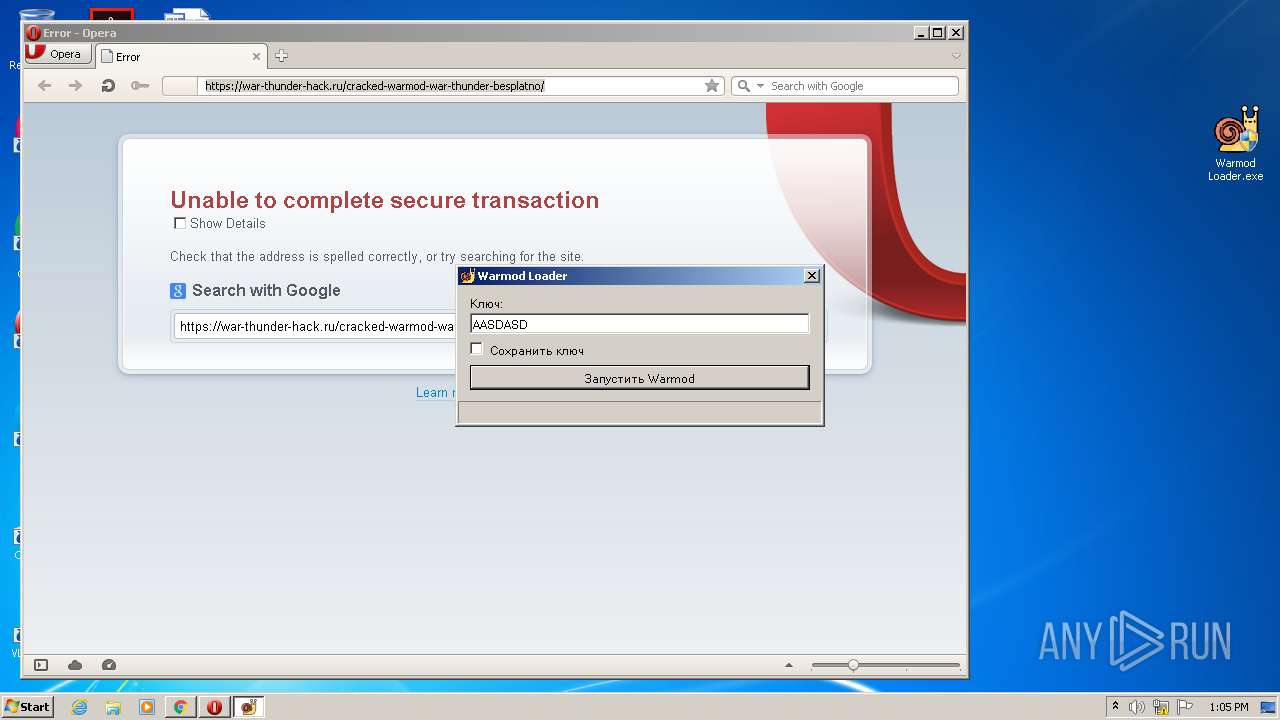
| URL: | https://war-thunder-hack.ru/cracked-warmod-war-thunder-besplatno/ |
| Full analysis: | https://app.any.run/tasks/f413d387-d0ac-4955-90c5-8beda4c93b69 |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2021, 12:03:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4112BC3F4369D681C3D39A6D35462C3B |
| SHA1: | A1B6CCCFEEC574350C6873D7D4A96C6C137BC225 |
| SHA256: | 14133078B52757B94DF93FF3E13EEB56EB17CD0A72BB6B22BD264EB9A70E832E |
| SSDEEP: | 3:N8Vd3OkEGZcYOyavH:27Atya/ |
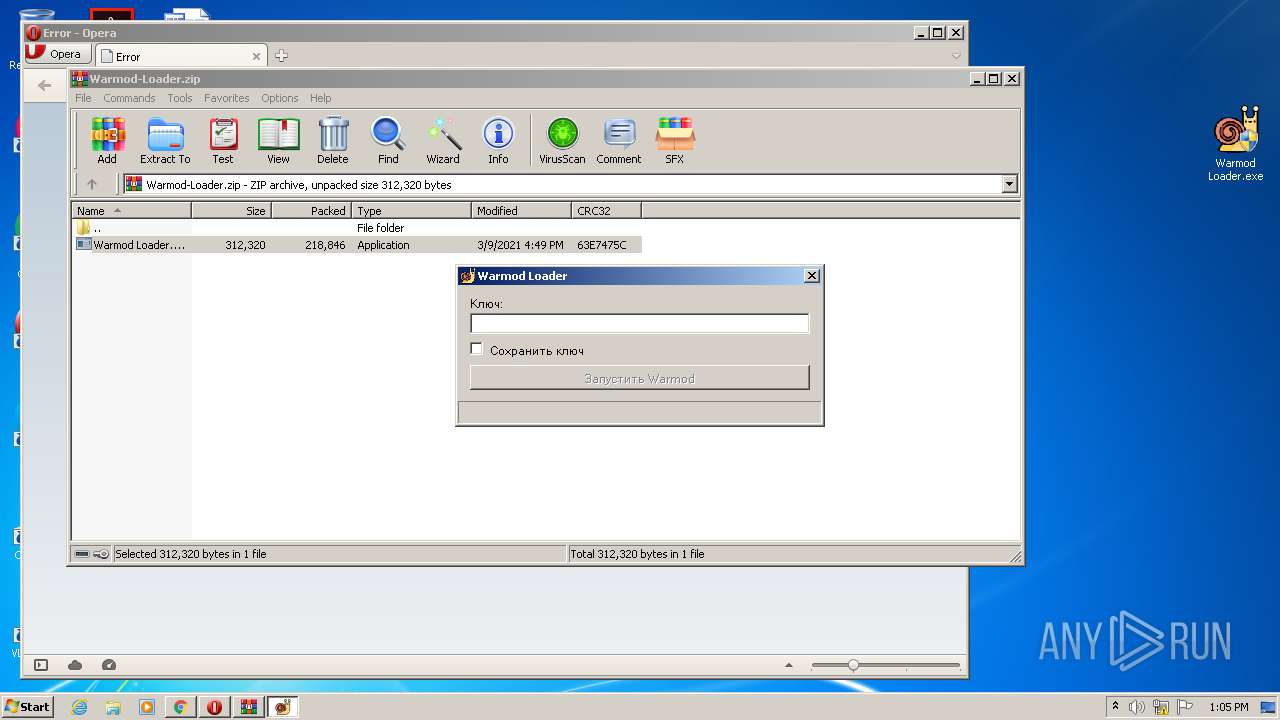
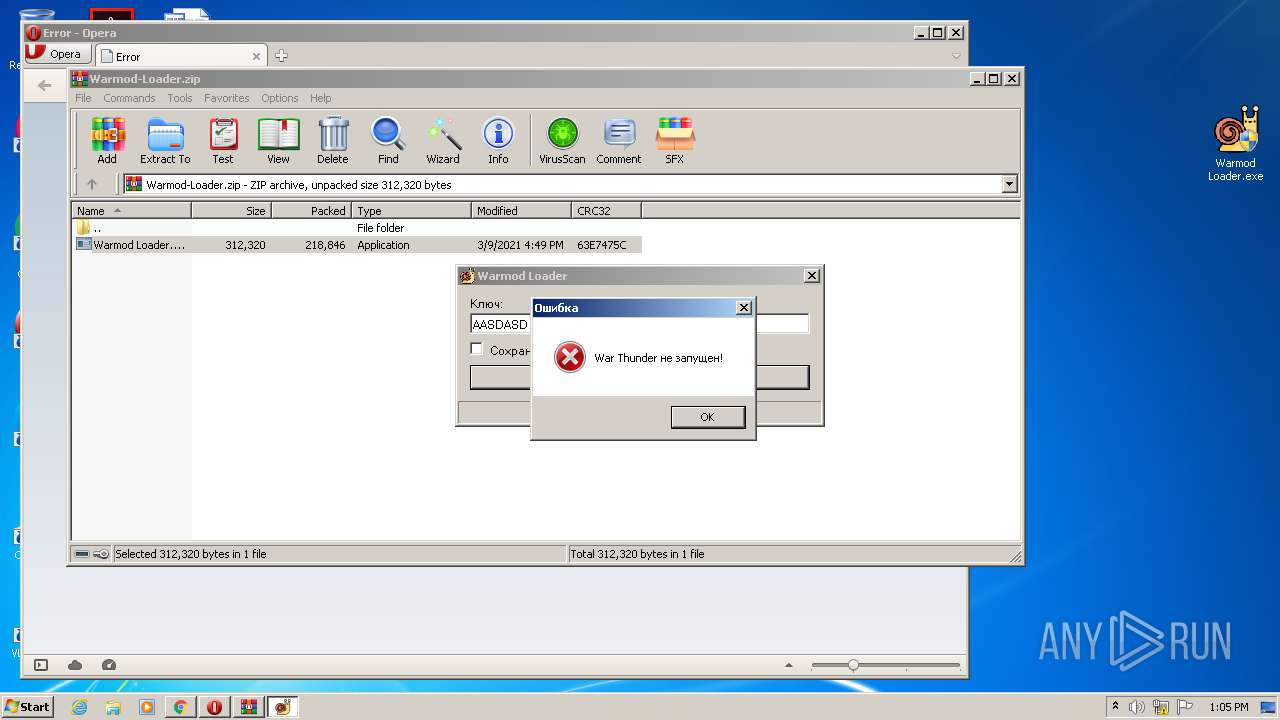
MALICIOUS
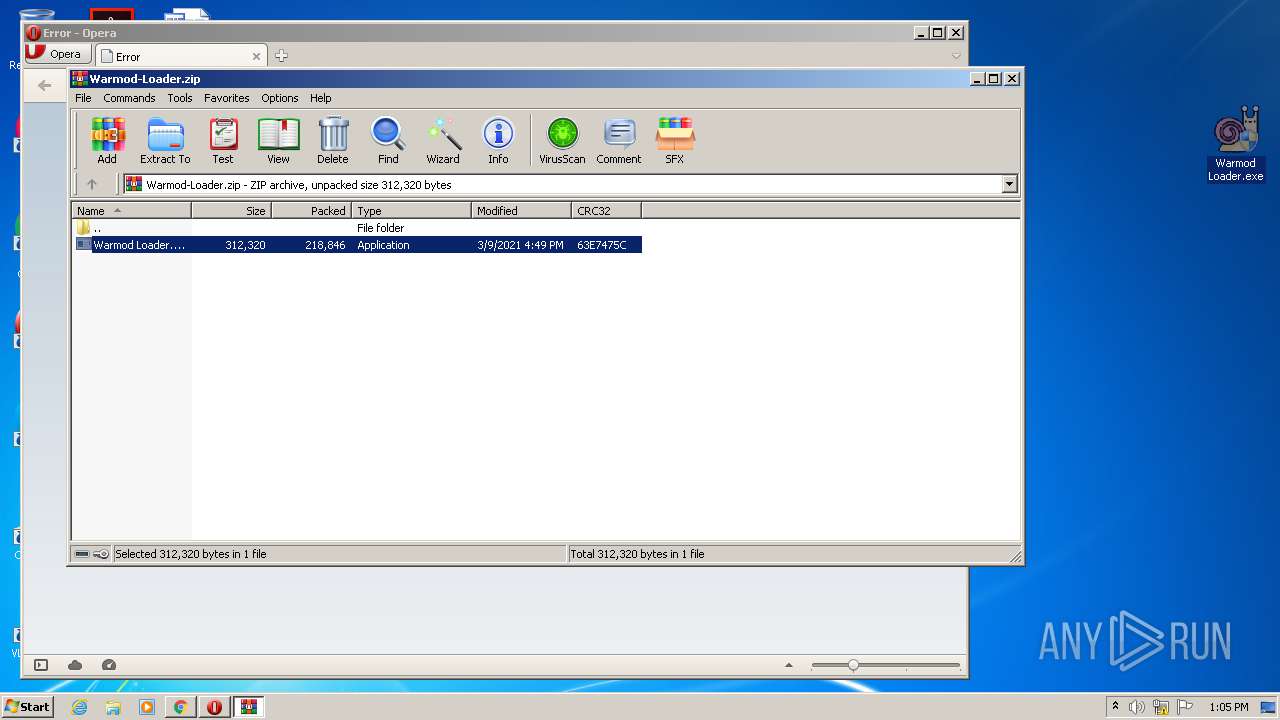
Application was dropped or rewritten from another process
- Warmod Loader.exe (PID: 3128)
- Warmod Loader.exe (PID: 3960)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2028)
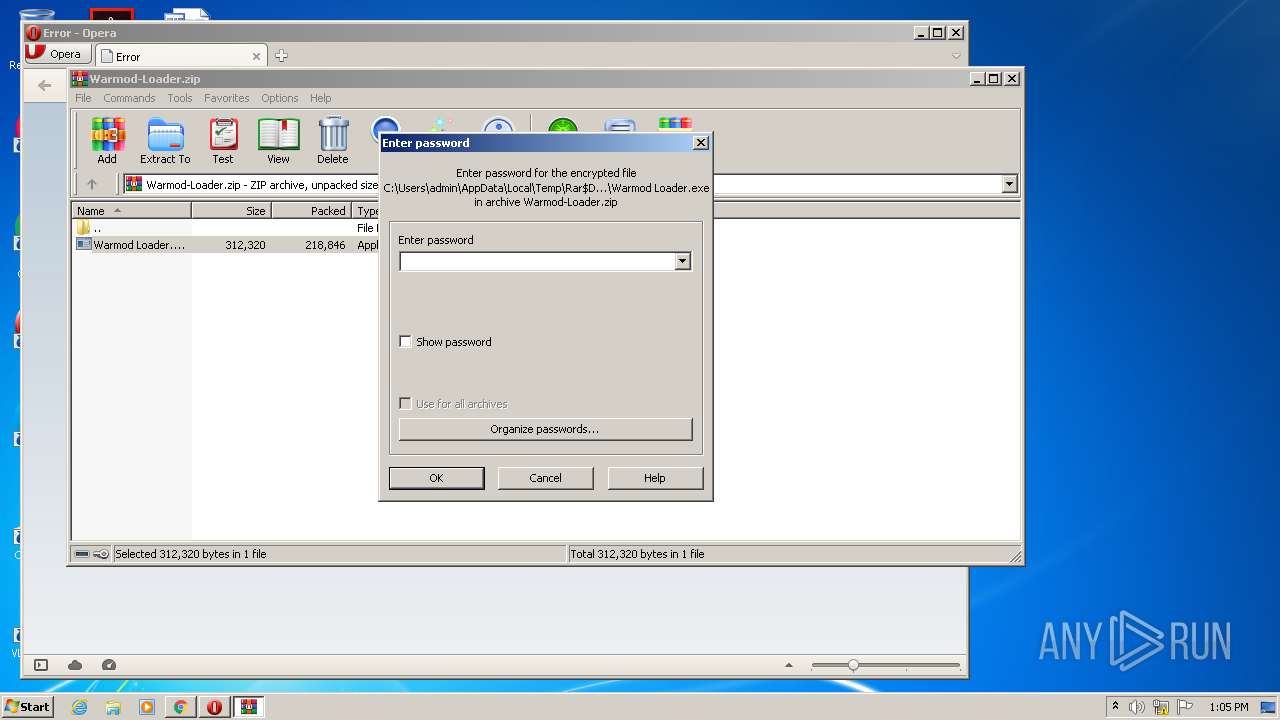
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2852)
Drops a file with too old compile date
- WinRAR.exe (PID: 2852)
INFO
Application launched itself
- iexplore.exe (PID: 2100)
- chrome.exe (PID: 2028)
Changes internet zones settings
- iexplore.exe (PID: 2100)
Creates files in the user directory
- iexplore.exe (PID: 768)
- opera.exe (PID: 2104)
- iexplore.exe (PID: 2100)
Reads settings of System Certificates
- iexplore.exe (PID: 768)
- iexplore.exe (PID: 2100)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2100)
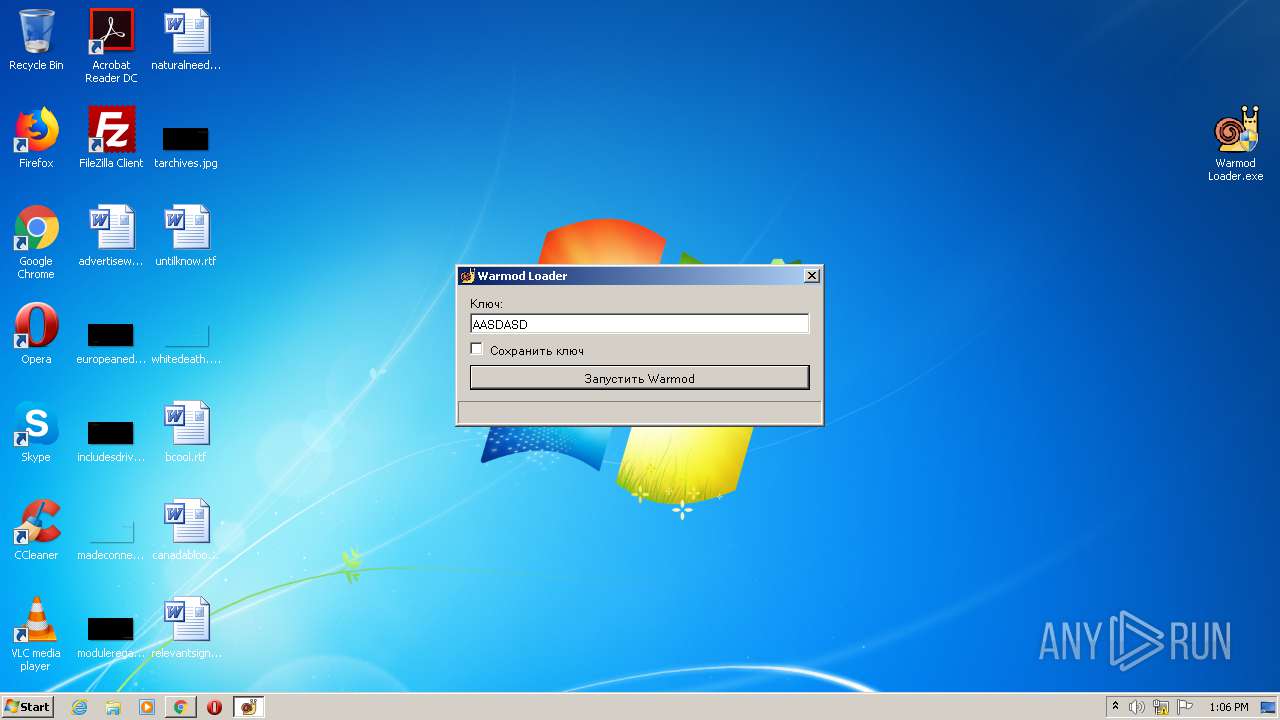
Manual execution by user
- opera.exe (PID: 2104)
- chrome.exe (PID: 2028)
- Warmod Loader.exe (PID: 3128)
- Warmod Loader.exe (PID: 3960)
Reads internet explorer settings
- iexplore.exe (PID: 768)
Changes settings of System certificates
- iexplore.exe (PID: 2100)
Reads the hosts file
- chrome.exe (PID: 2096)
- chrome.exe (PID: 2028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
51
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,12622658673511766928,11143429356798059891,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3340031572792368725 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2100 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,12622658673511766928,11143429356798059891,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16083689567579768816 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,12622658673511766928,11143429356798059891,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6764628608175215850 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4064 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,12622658673511766928,11143429356798059891,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8965974479721486552 --mojo-platform-channel-handle=4688 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,12622658673511766928,11143429356798059891,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9493739101645152754 --mojo-platform-channel-handle=4976 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,12622658673511766928,11143429356798059891,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18187704185118493307 --mojo-platform-channel-handle=4924 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,12622658673511766928,11143429356798059891,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9686380991632495835 --mojo-platform-channel-handle=3328 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,12622658673511766928,11143429356798059891,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11953130111375883726 --mojo-platform-channel-handle=4556 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 409
Read events
2 063
Write events
336
Delete events
10
Modification events
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 400004006 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30893114 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2100) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
172
Text files
338
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 768 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab2DD.tmp | — | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar2DE.tmp | — | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\644B8874112055B5E195ECB0E8F243A4 | der | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\644B8874112055B5E195ECB0E8F243A4 | binary | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\cracked-warmod-war-thunder-besplatno[1].htm | html | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\065D9D41BB246285EA9CA50F063EF02A | der | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\B6A2V8VT.txt | text | |
MD5:— | SHA256:— | |||
| 768 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Trainer-War-Thunder-min-150x150[1].jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
131
DNS requests
85
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
768 | iexplore.exe | GET | 200 | 104.125.75.233:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
768 | iexplore.exe | GET | 200 | 216.58.214.195:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDIWwoCq3x8%2FAoAAAAA1XGc | US | der | 472 b | whitelisted |
768 | iexplore.exe | GET | 200 | 2.22.118.163:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | GB | der | 1.16 Kb | whitelisted |
768 | iexplore.exe | GET | 200 | 216.58.214.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
768 | iexplore.exe | GET | 200 | 88.221.223.48:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgQDgOKwyRzoGwrxa%2BJwai21Yw%3D%3D | unknown | der | 503 b | shared |
768 | iexplore.exe | GET | 200 | 216.58.214.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
768 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
768 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
768 | iexplore.exe | GET | 200 | 184.86.103.212:80 | http://crl.certum.pl/ca.crl | US | der | 845 b | whitelisted |
768 | iexplore.exe | GET | 200 | 216.58.214.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
768 | iexplore.exe | 87.236.16.46:443 | war-thunder-hack.ru | Beget Ltd | RU | malicious |
768 | iexplore.exe | 2.22.118.163:80 | crl.identrust.com | Akamai International B.V. | GB | suspicious |
768 | iexplore.exe | 104.125.75.233:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
768 | iexplore.exe | 88.221.223.48:80 | r3.o.lencr.org | Akamai International B.V. | — | unknown |
768 | iexplore.exe | 216.58.214.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
768 | iexplore.exe | 142.250.185.196:443 | www.google.com | Google Inc. | US | whitelisted |
2100 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
768 | iexplore.exe | 142.250.74.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
768 | iexplore.exe | 172.67.160.231:443 | werastinus.com | — | US | unknown |
768 | iexplore.exe | 88.208.46.61:443 | gentlemenius.com | DataWeb Global Group B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
war-thunder-hack.ru |
| suspicious |
crl.identrust.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
r3.o.lencr.org |
| shared |
www.google.com |
| malicious |
gentlemenius.com |
| unknown |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2104 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2104 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2104 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2104 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2104 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2104 | opera.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |