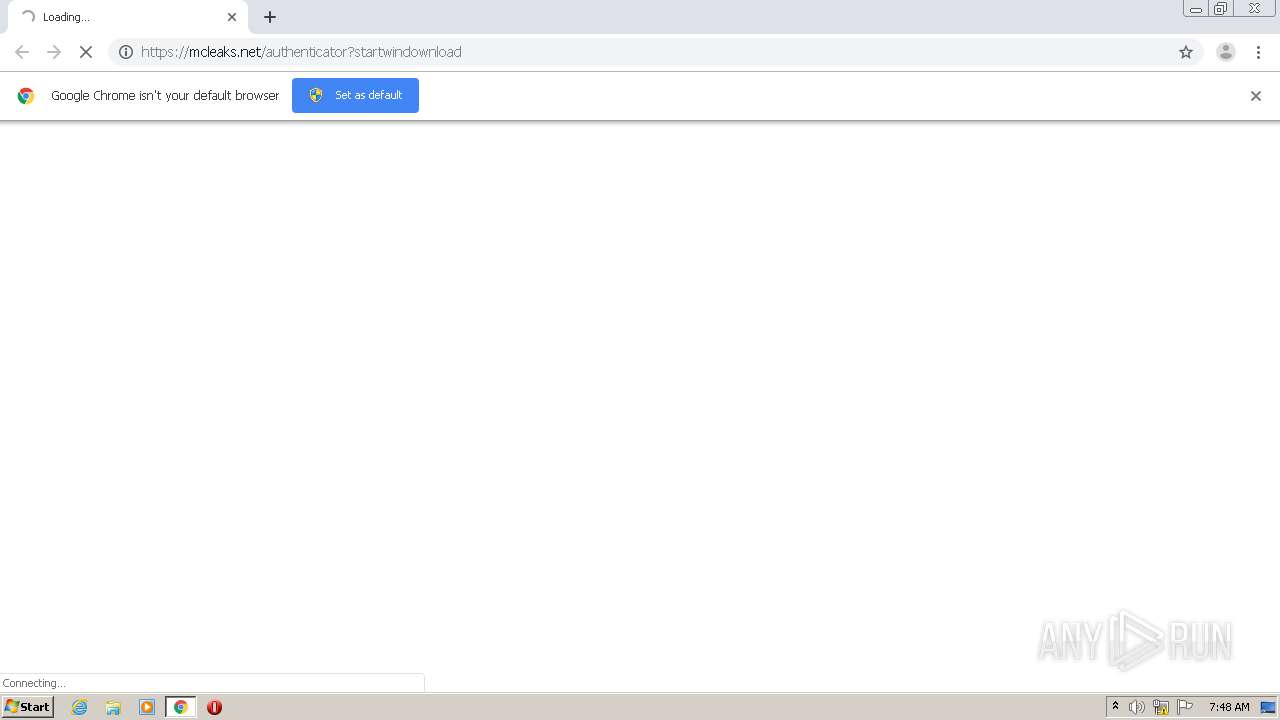
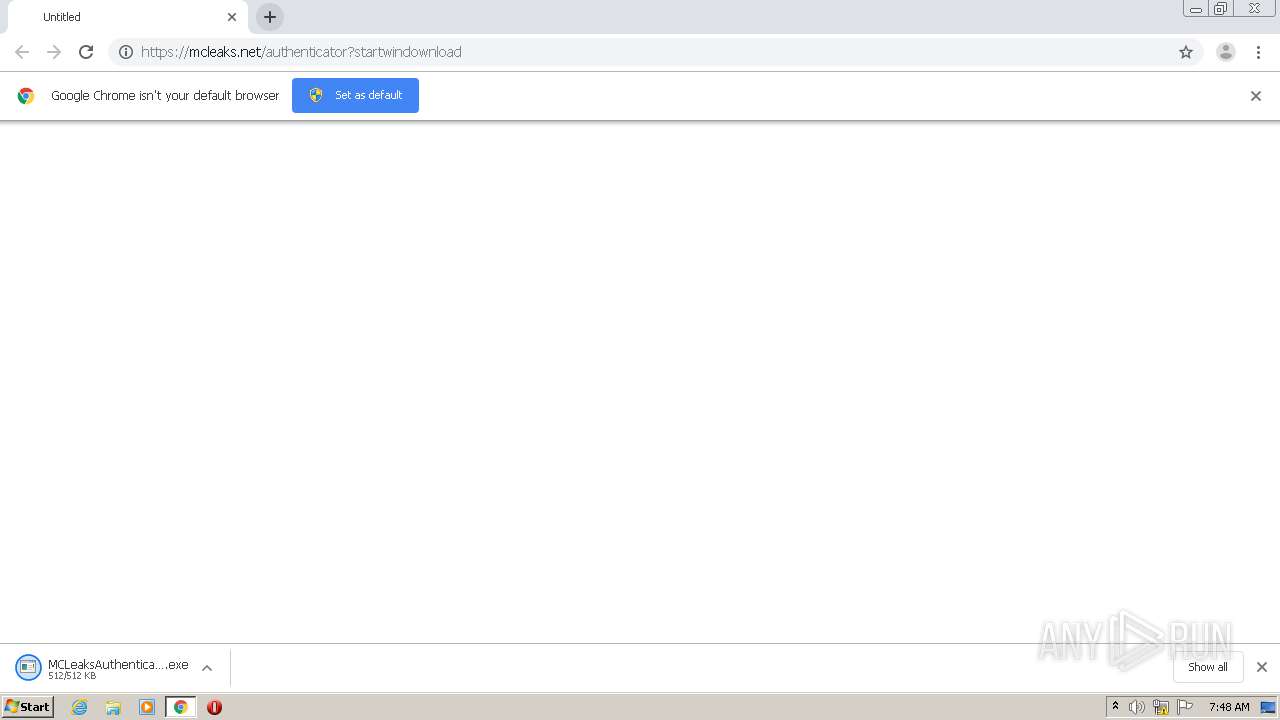
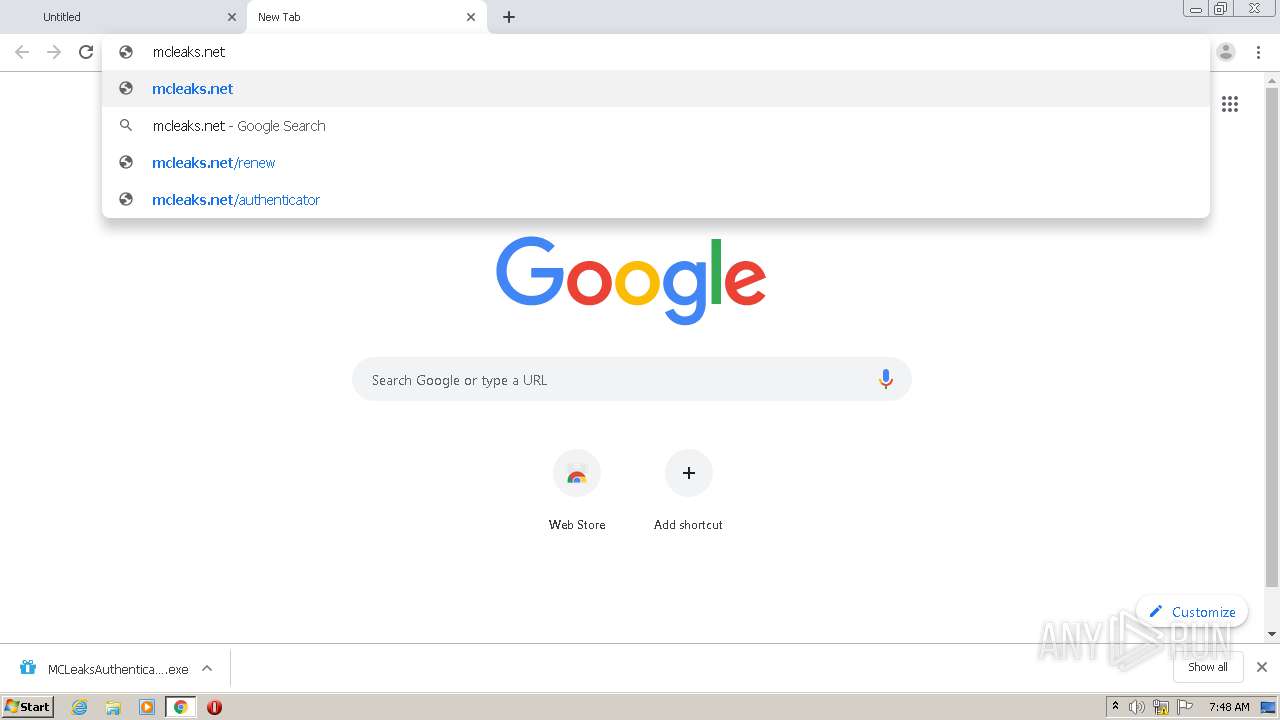
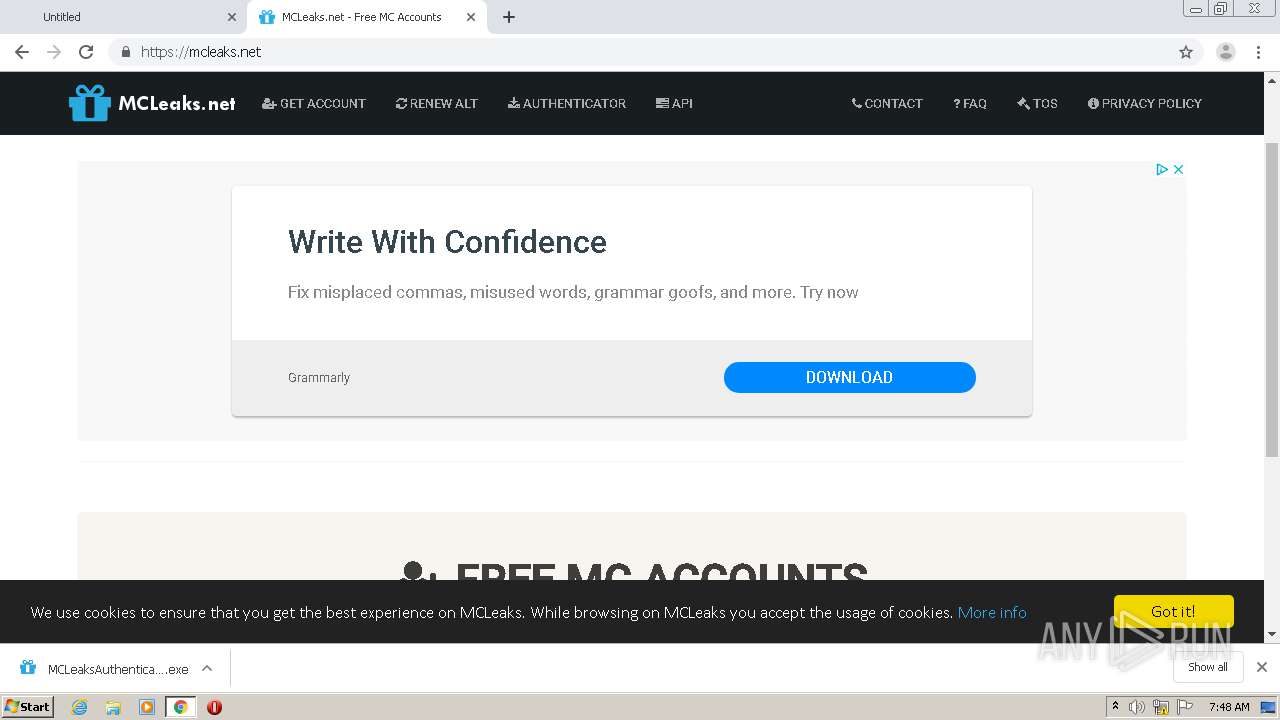
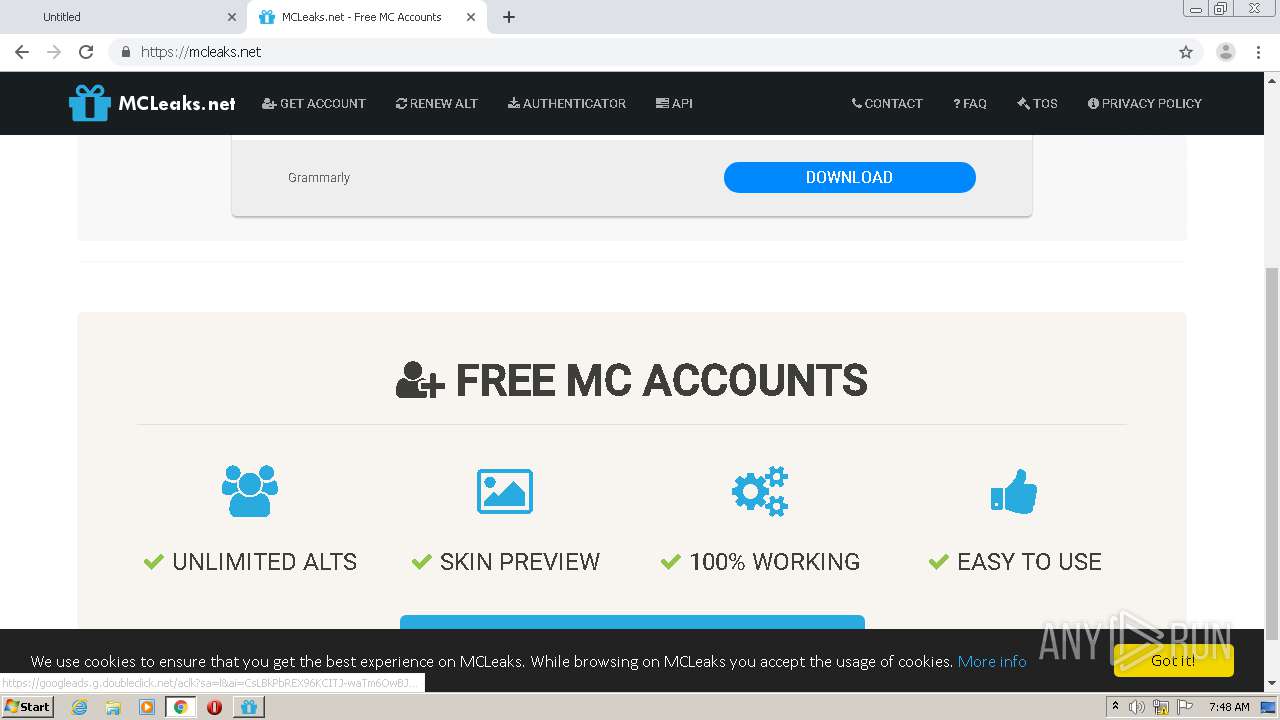
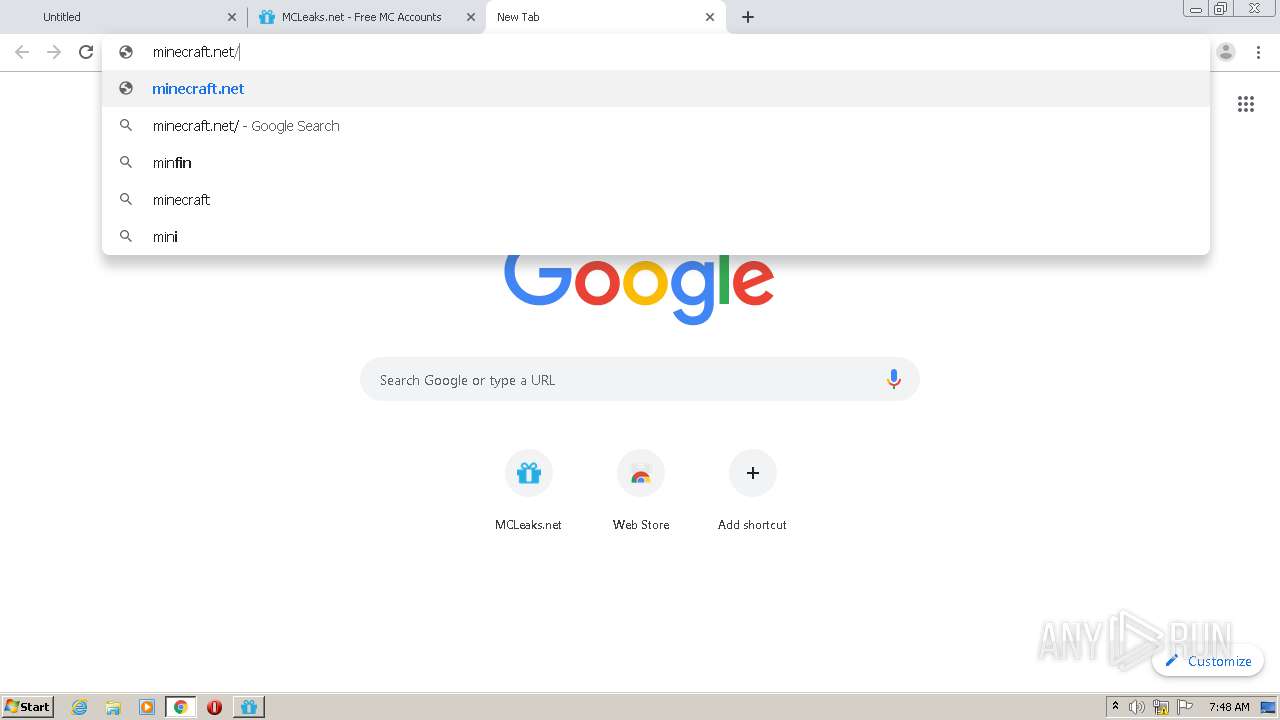
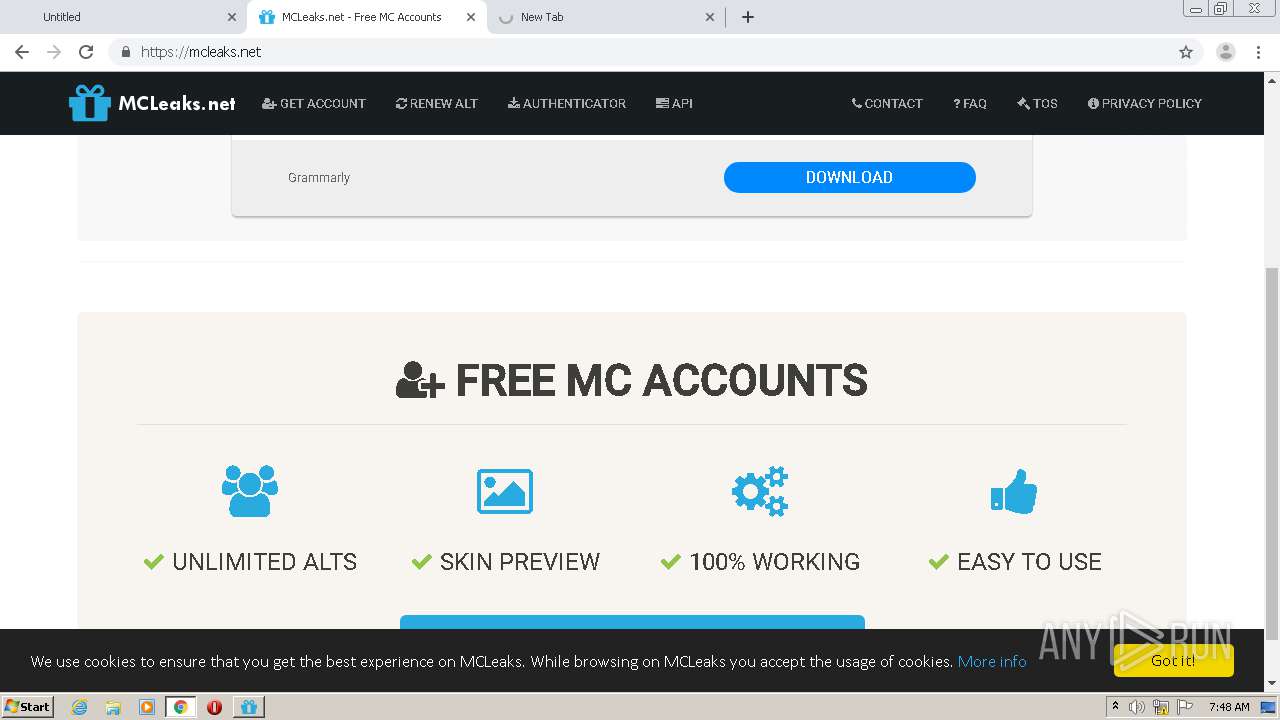
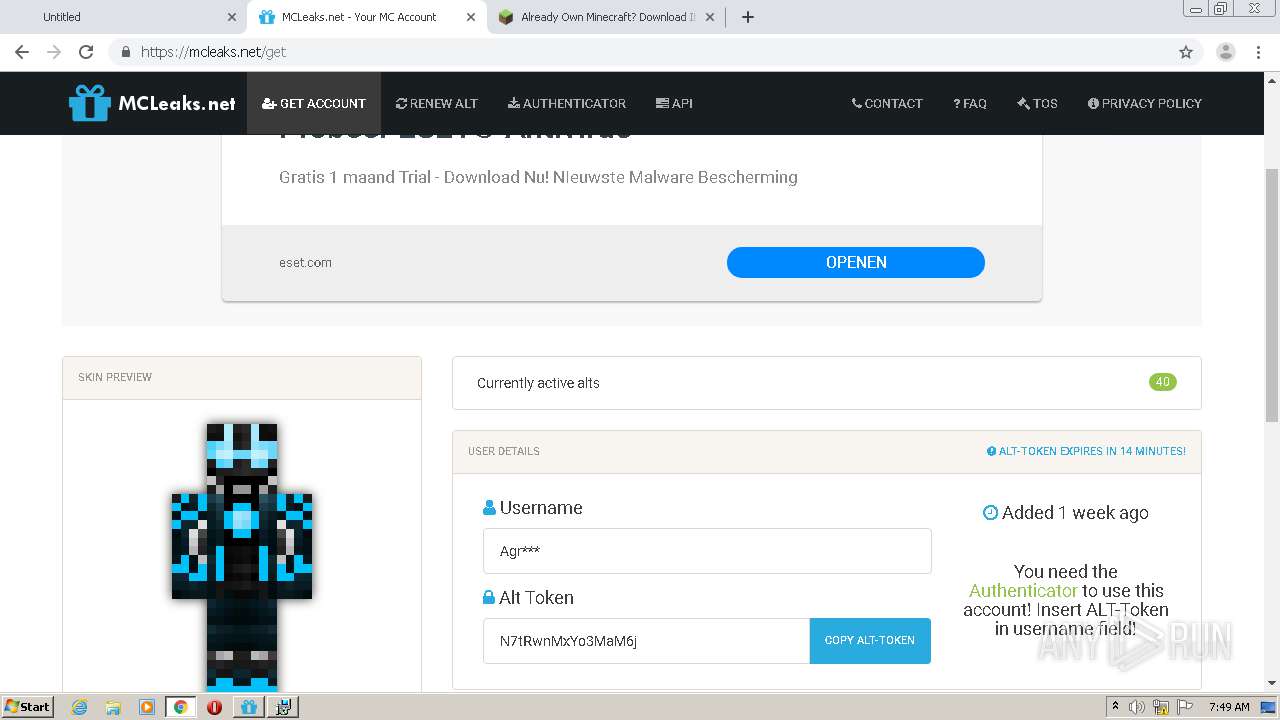
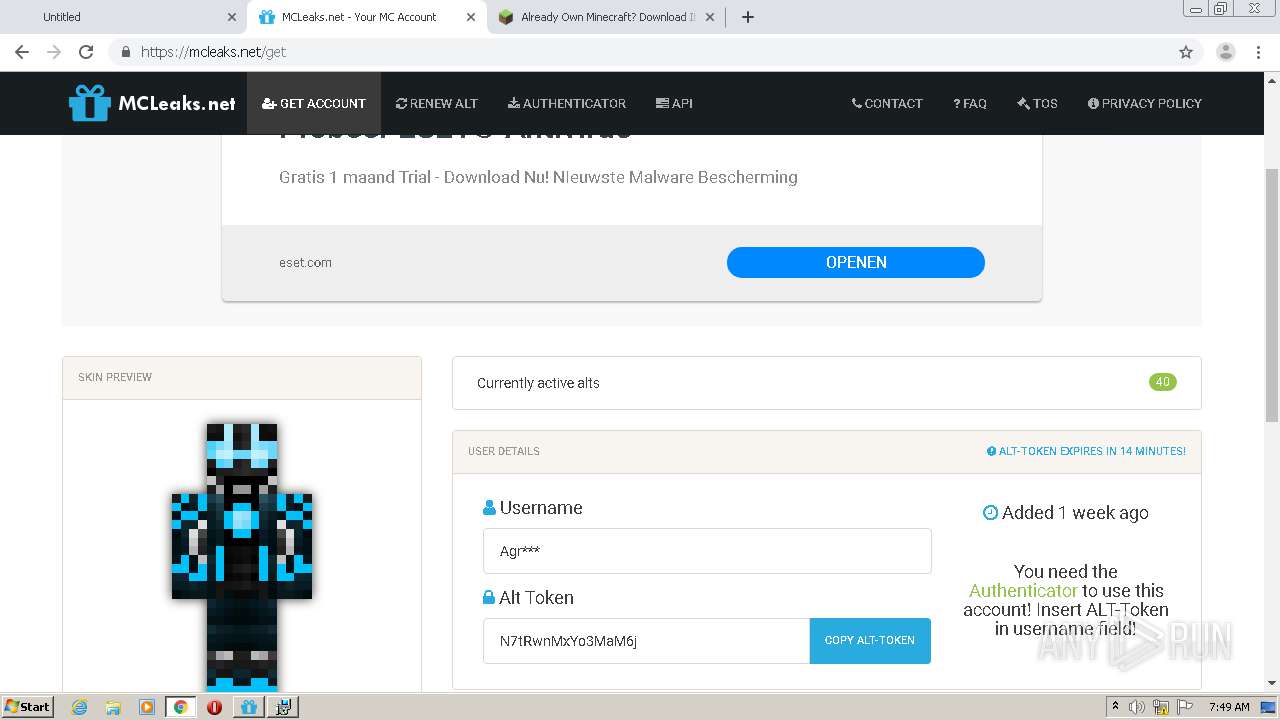
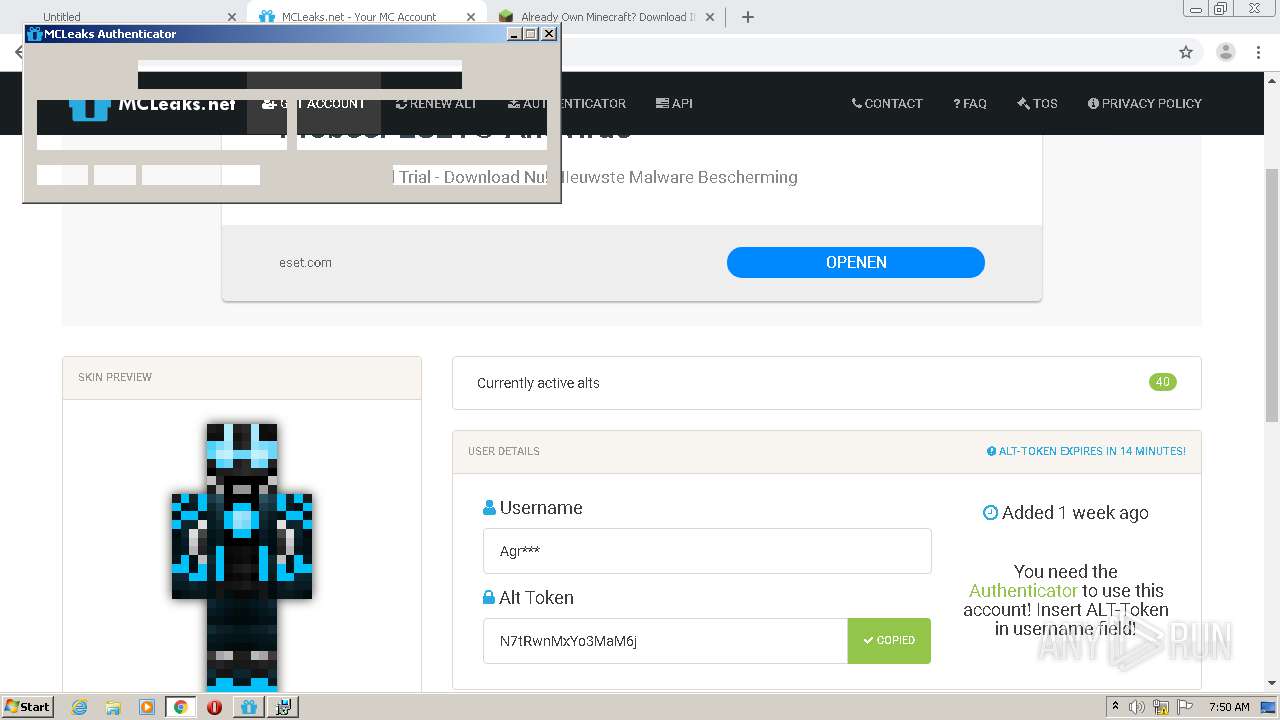
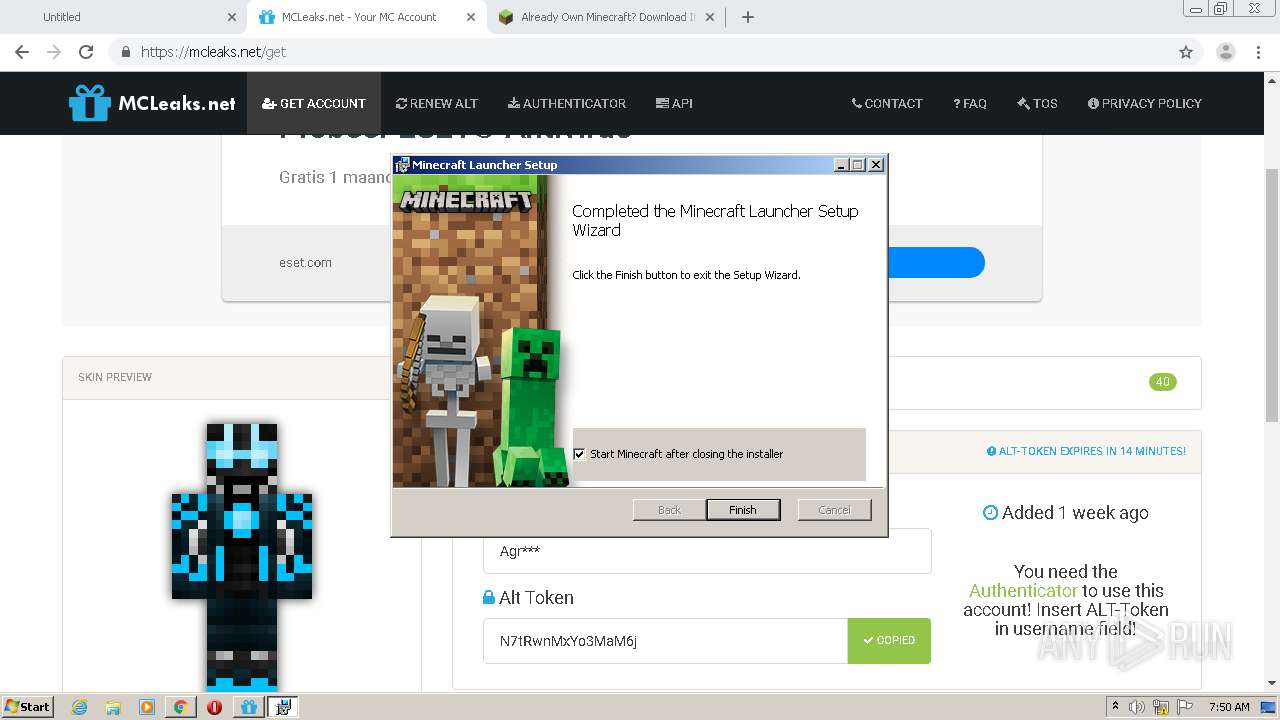
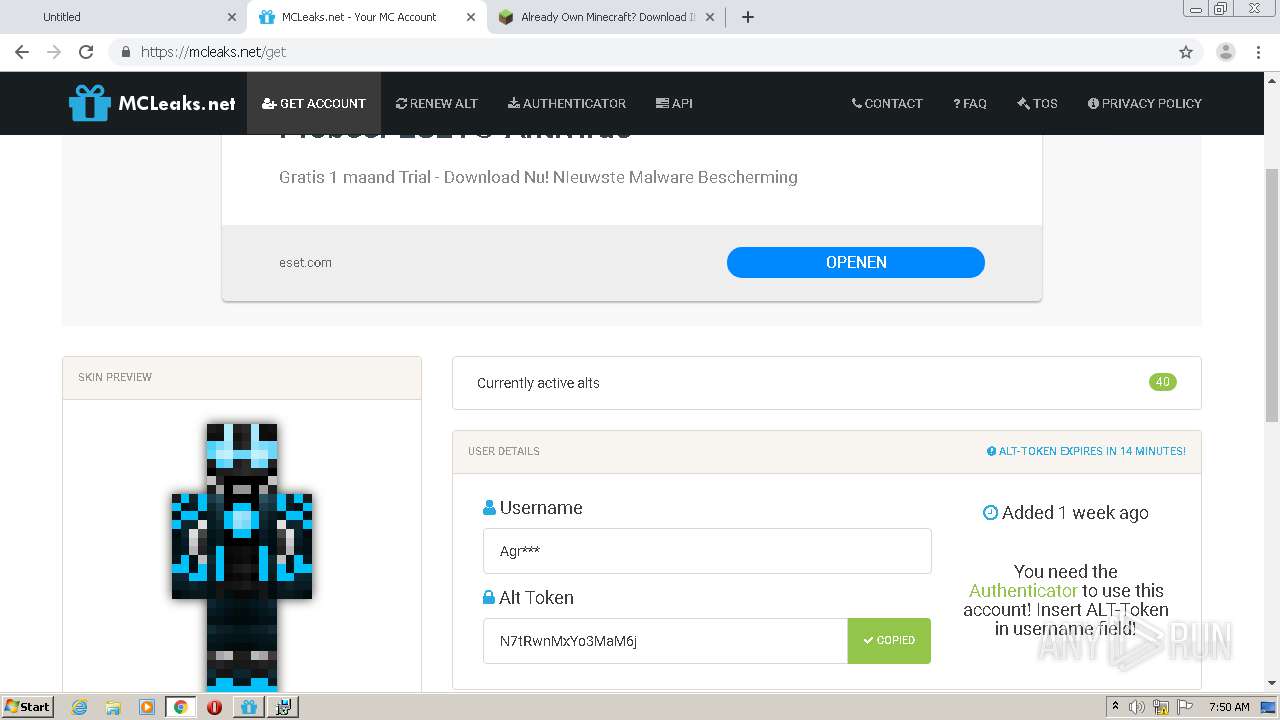
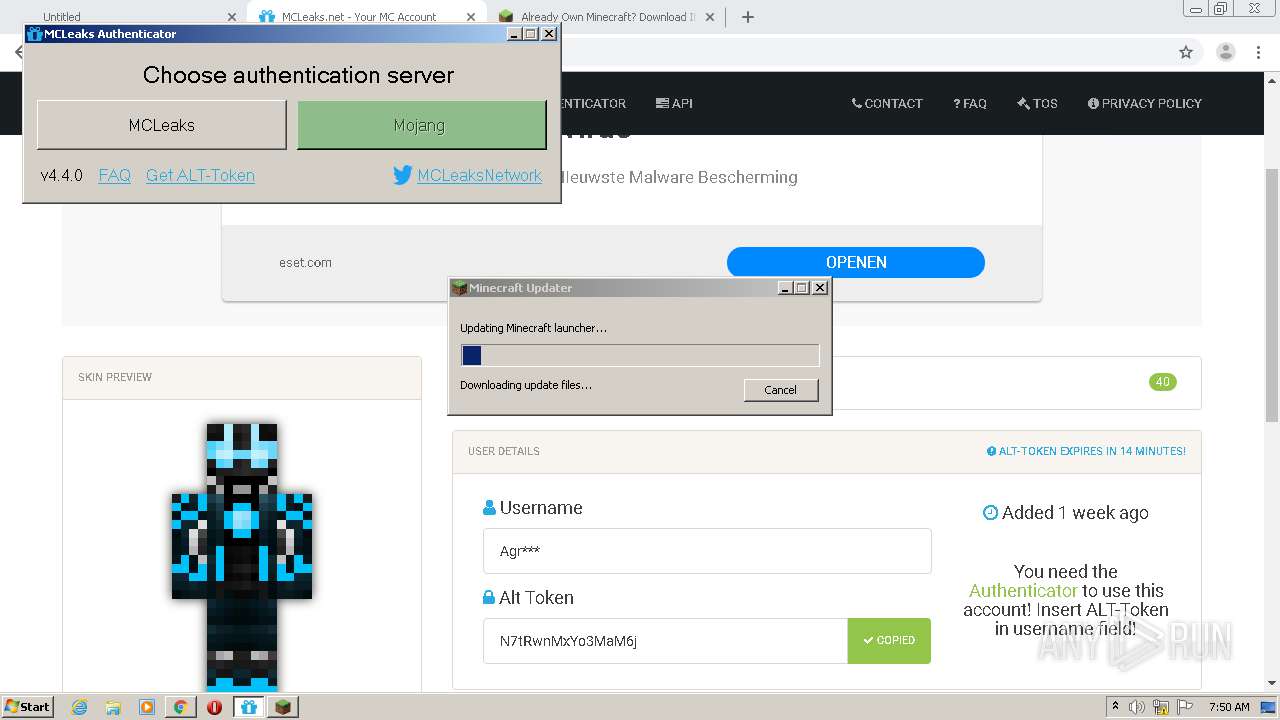
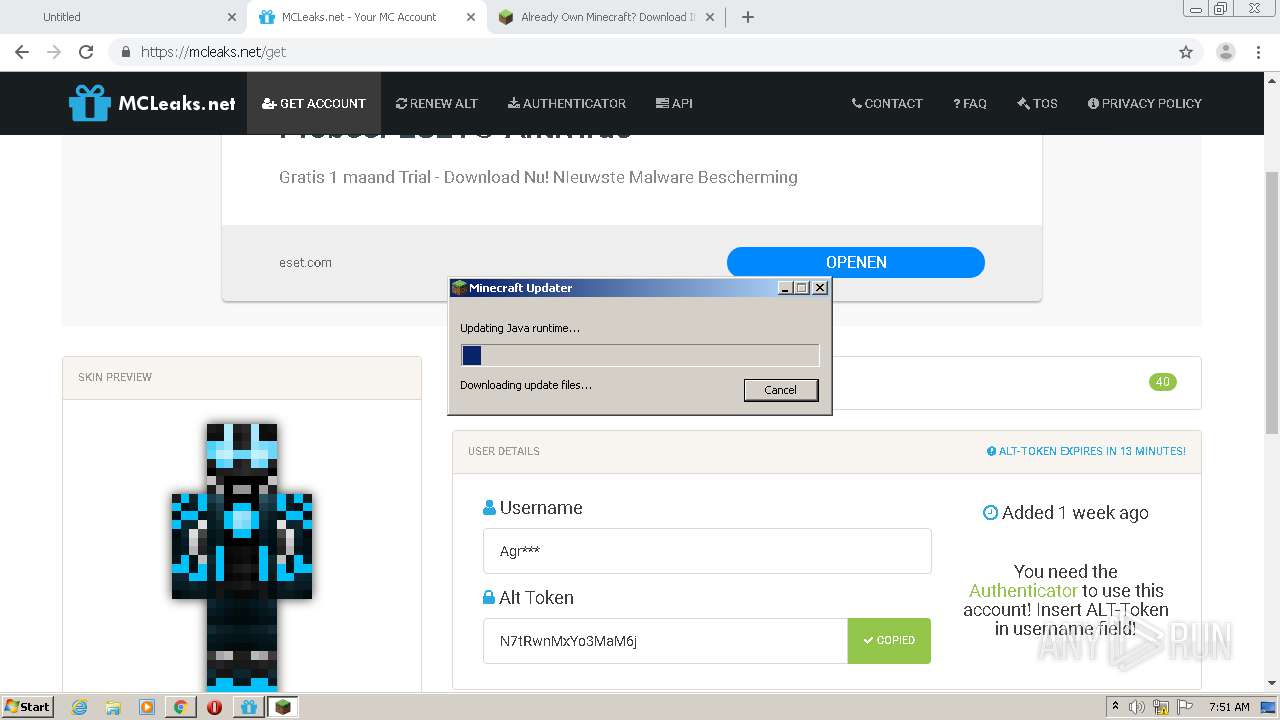
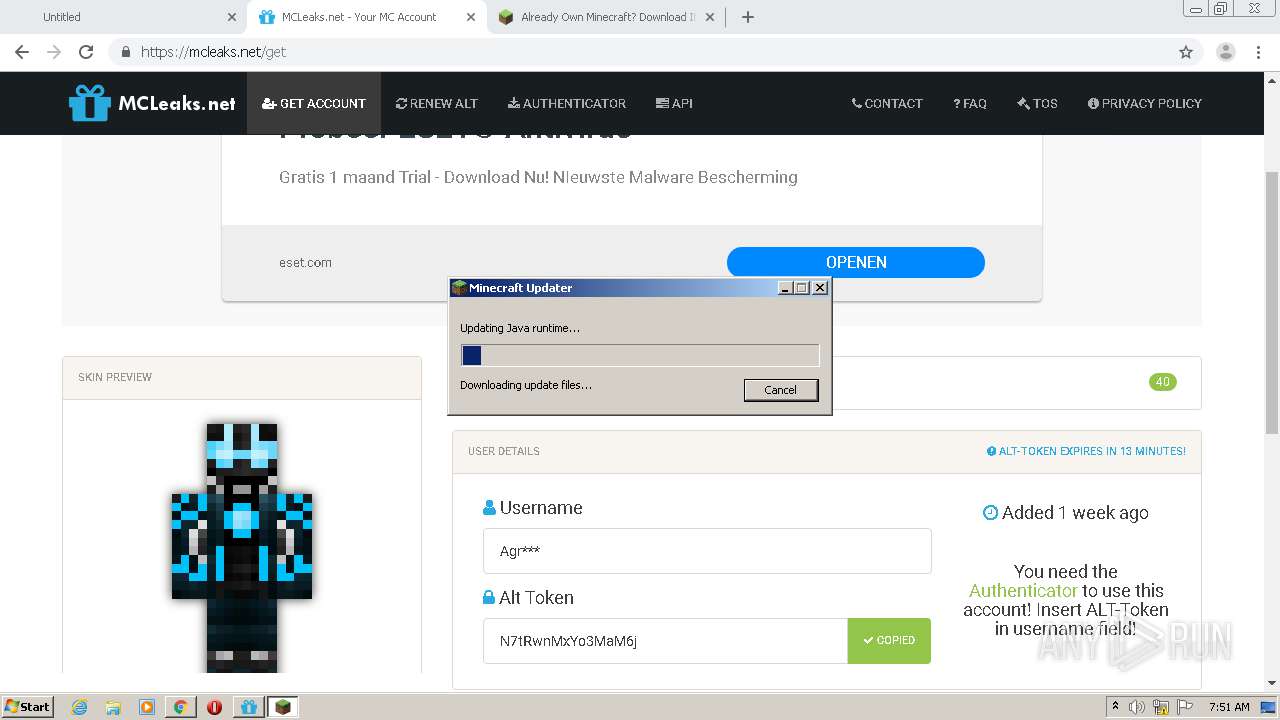
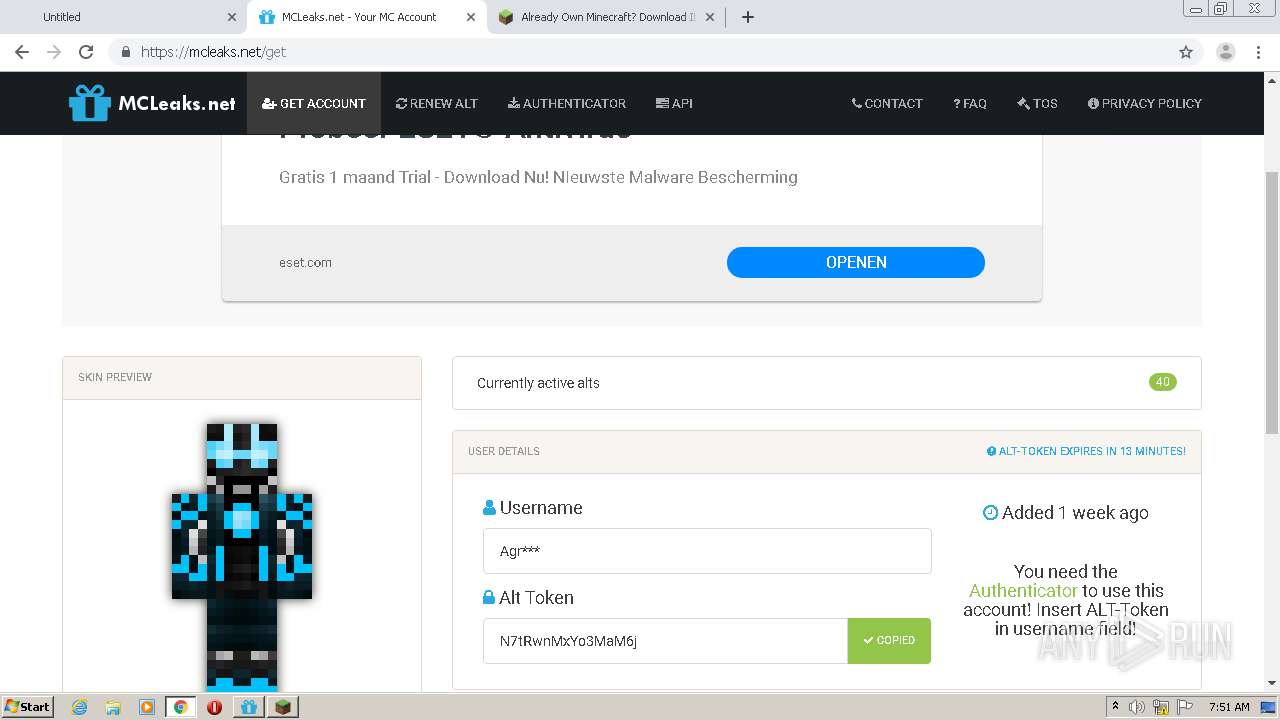
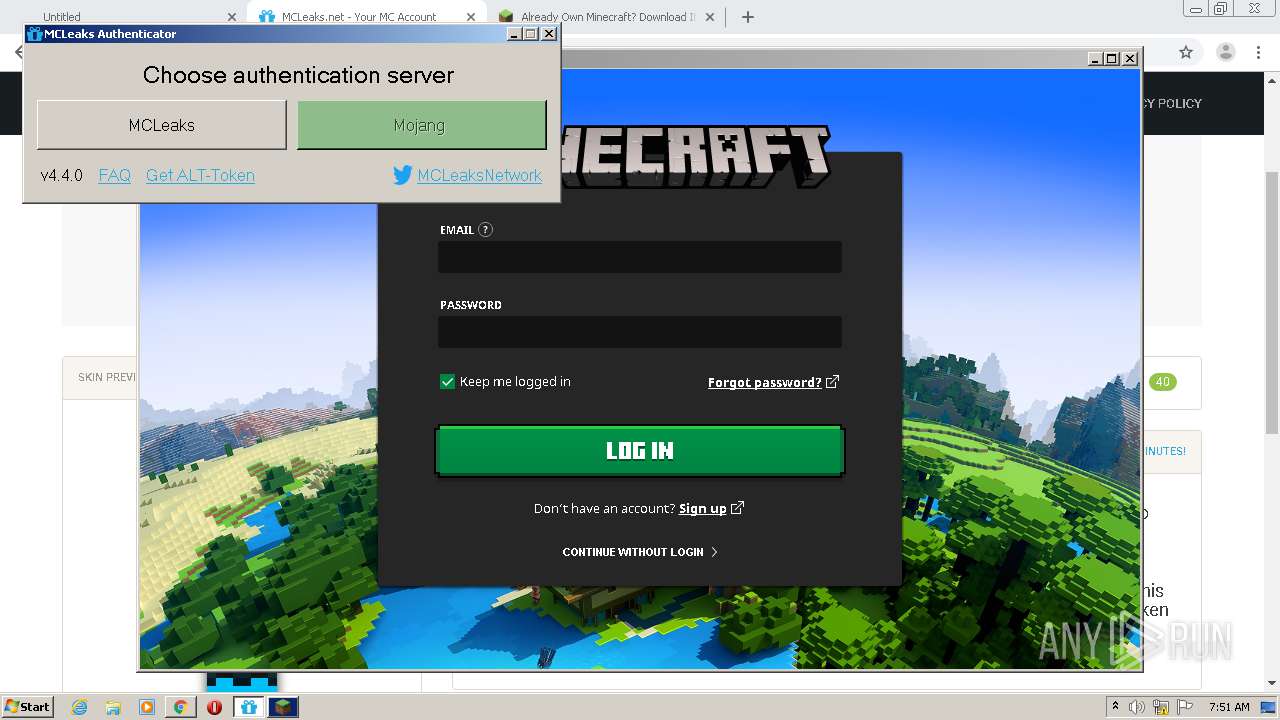
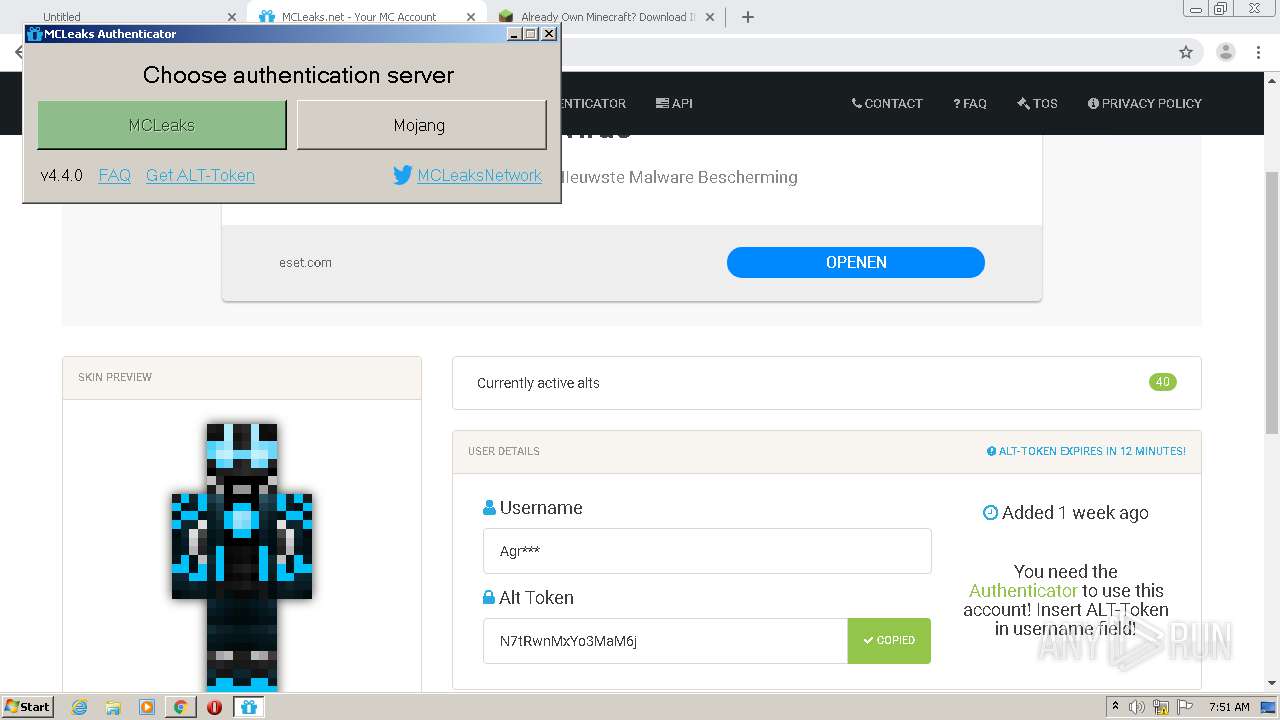
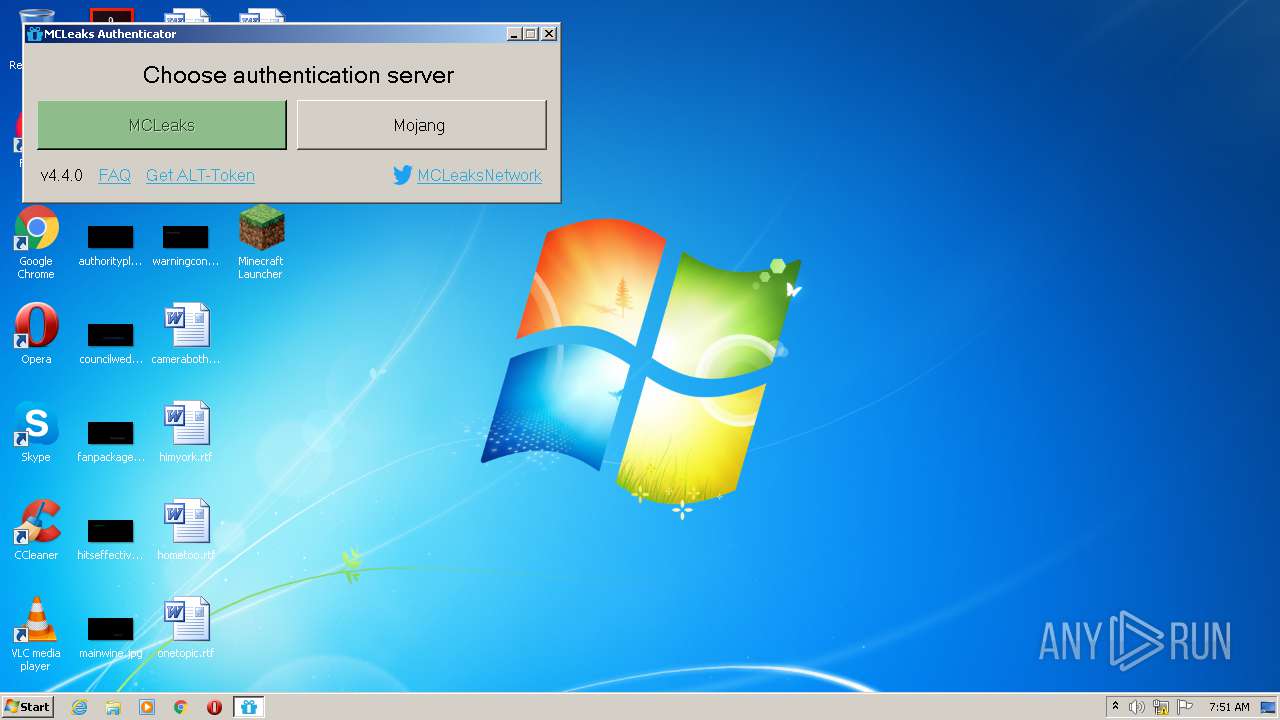
| URL: | https://mcleaks.net/authenticator?startwindownload |
| Full analysis: | https://app.any.run/tasks/a69fe475-3431-4bab-a4a3-363636fb5620 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2020, 06:47:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 282E71D31594785AA4CB7827CCF127CD |
| SHA1: | ED43928341B16B62692B980CA92FB3008E4835B3 |
| SHA256: | 140DBE668A0D5DD2B0675834101516A28C299289DBCFAFD2B323EAD5325E92FA |
| SSDEEP: | 3:N8PAEho3dREX0i:249TEki |
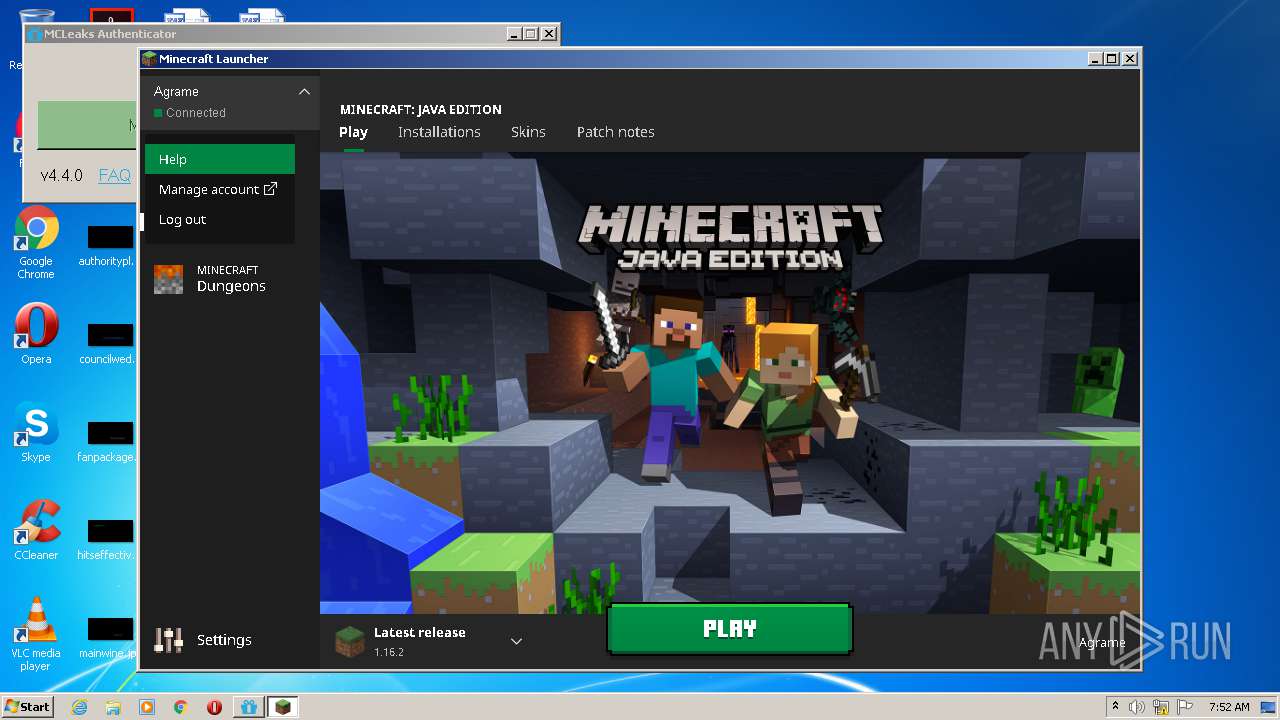
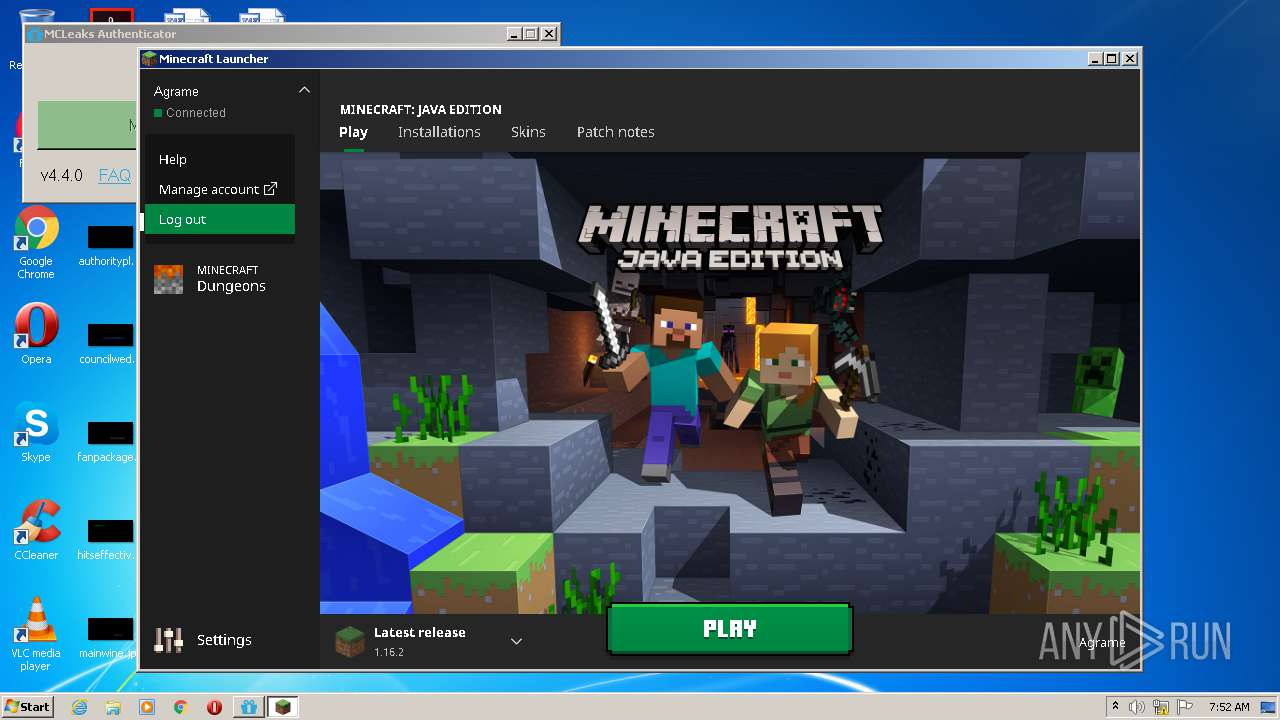
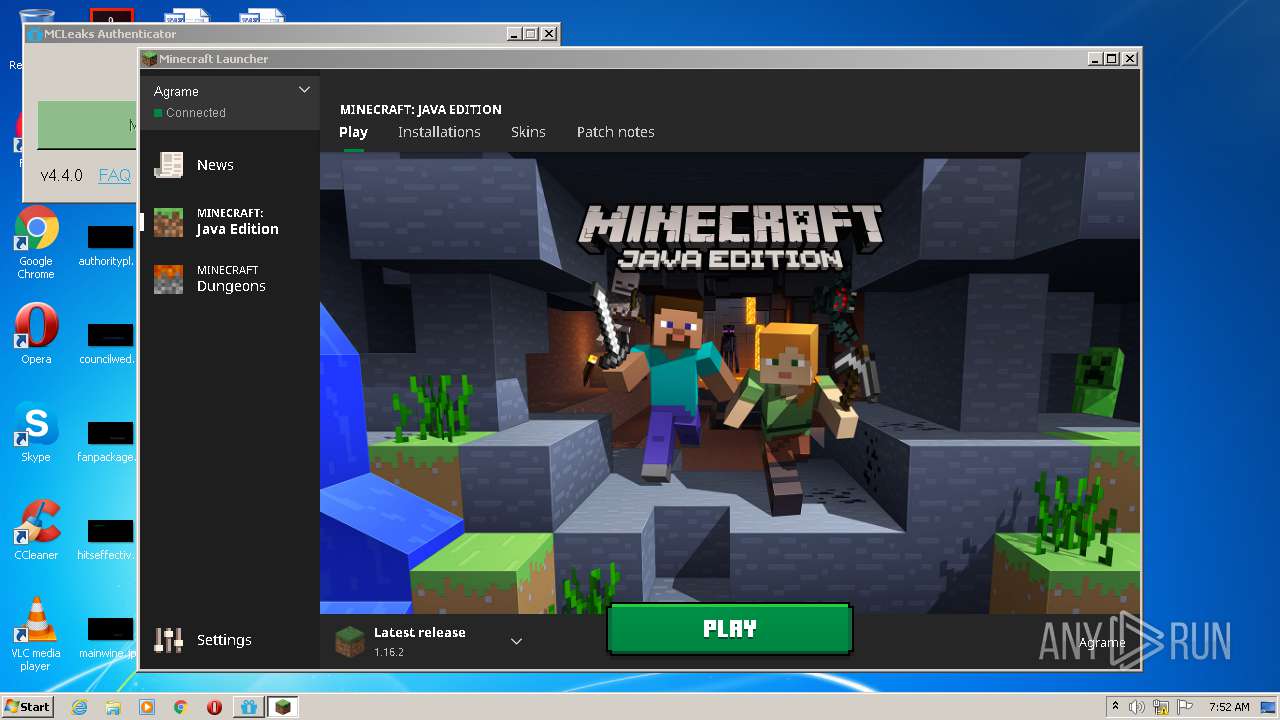
MALICIOUS
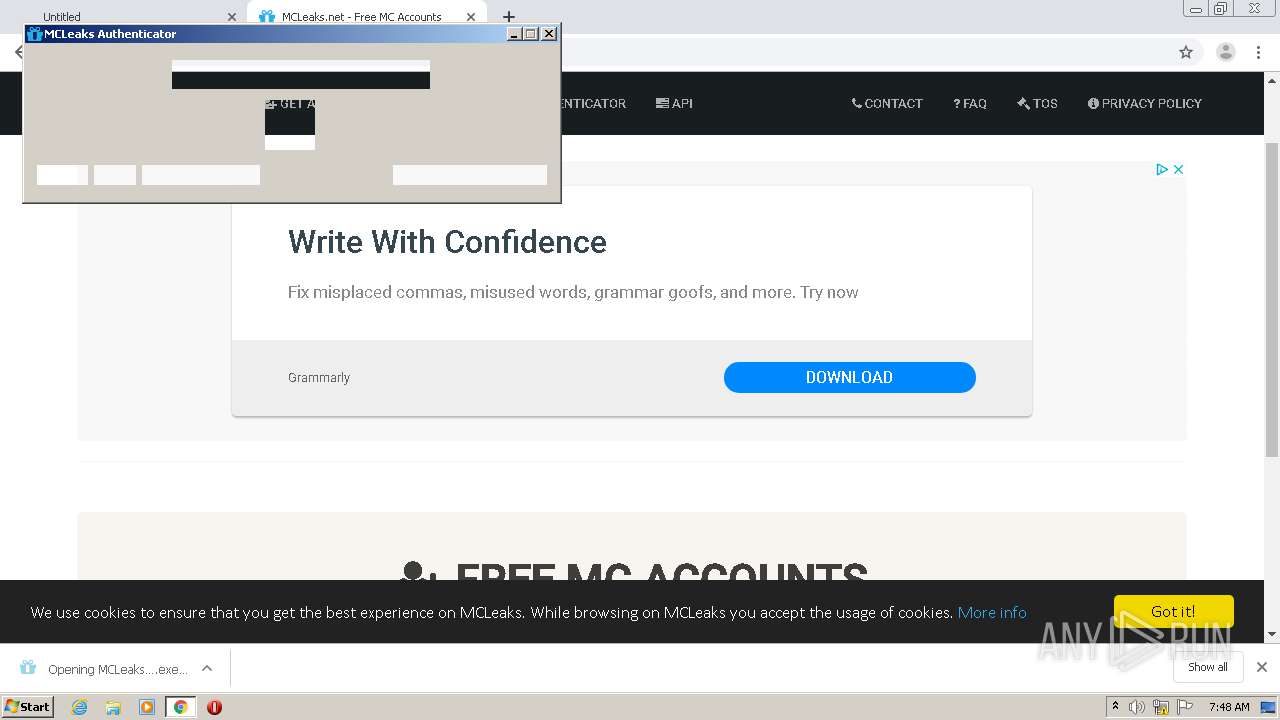
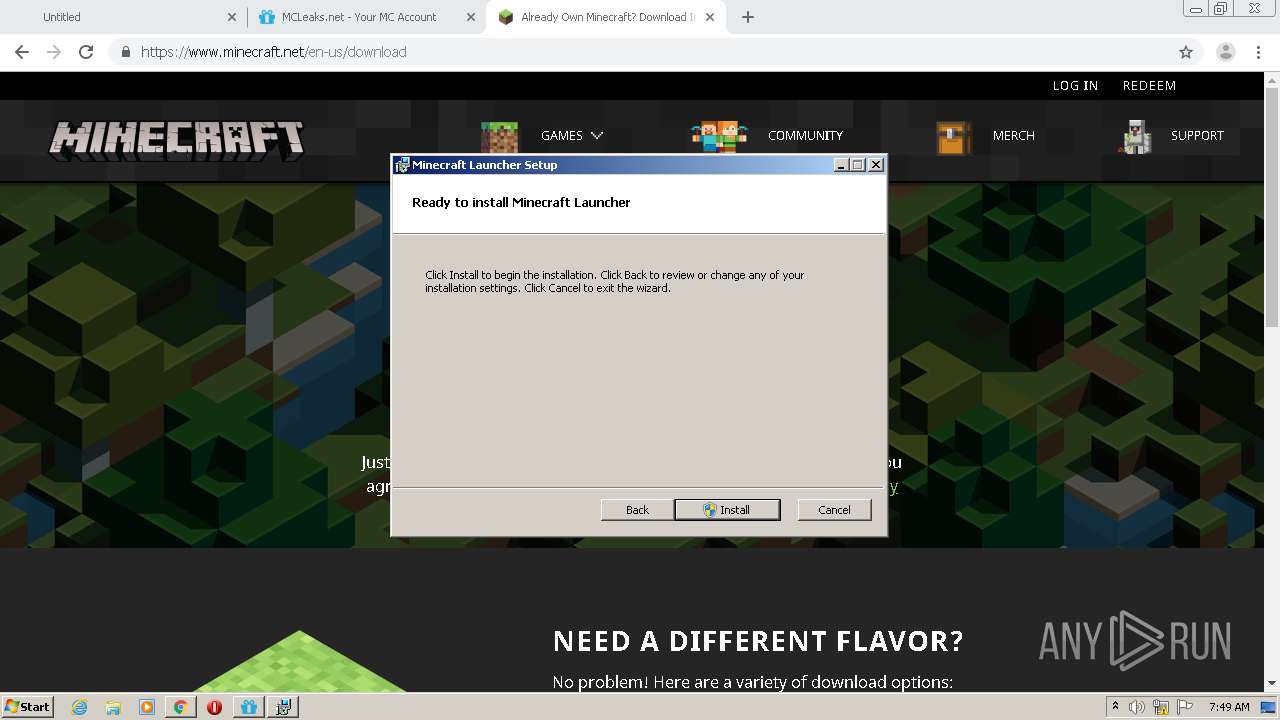
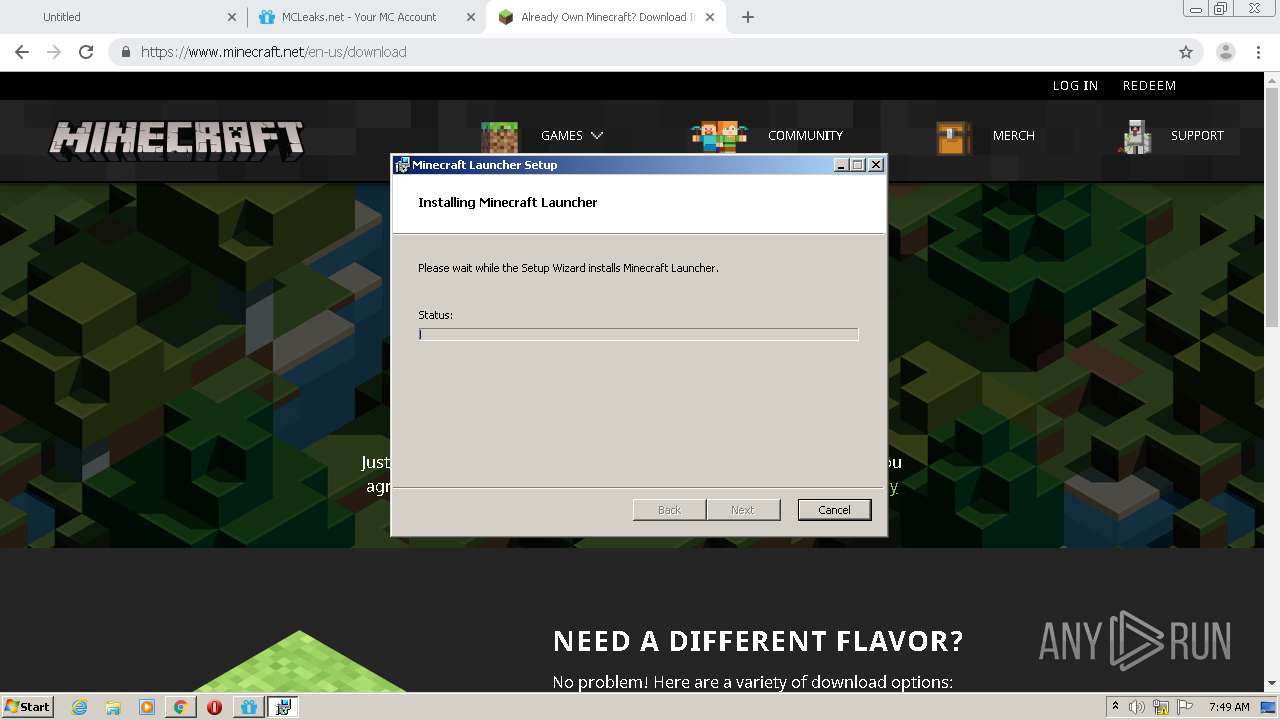
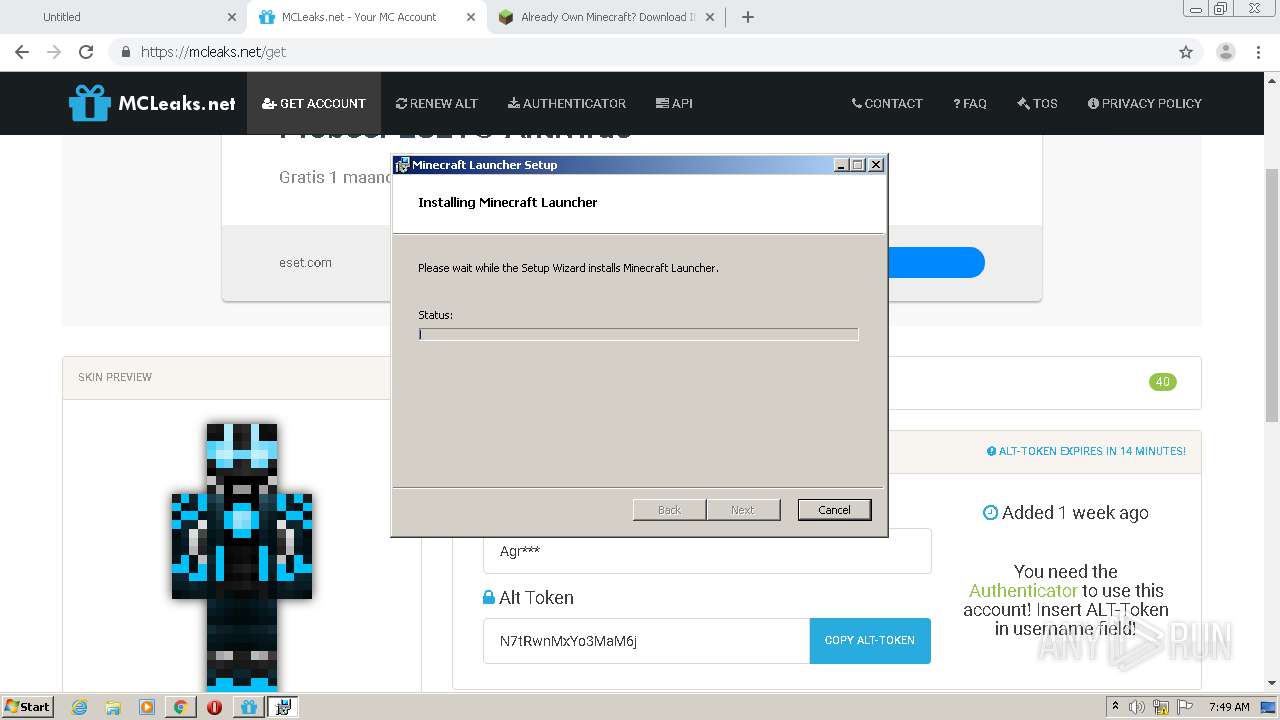
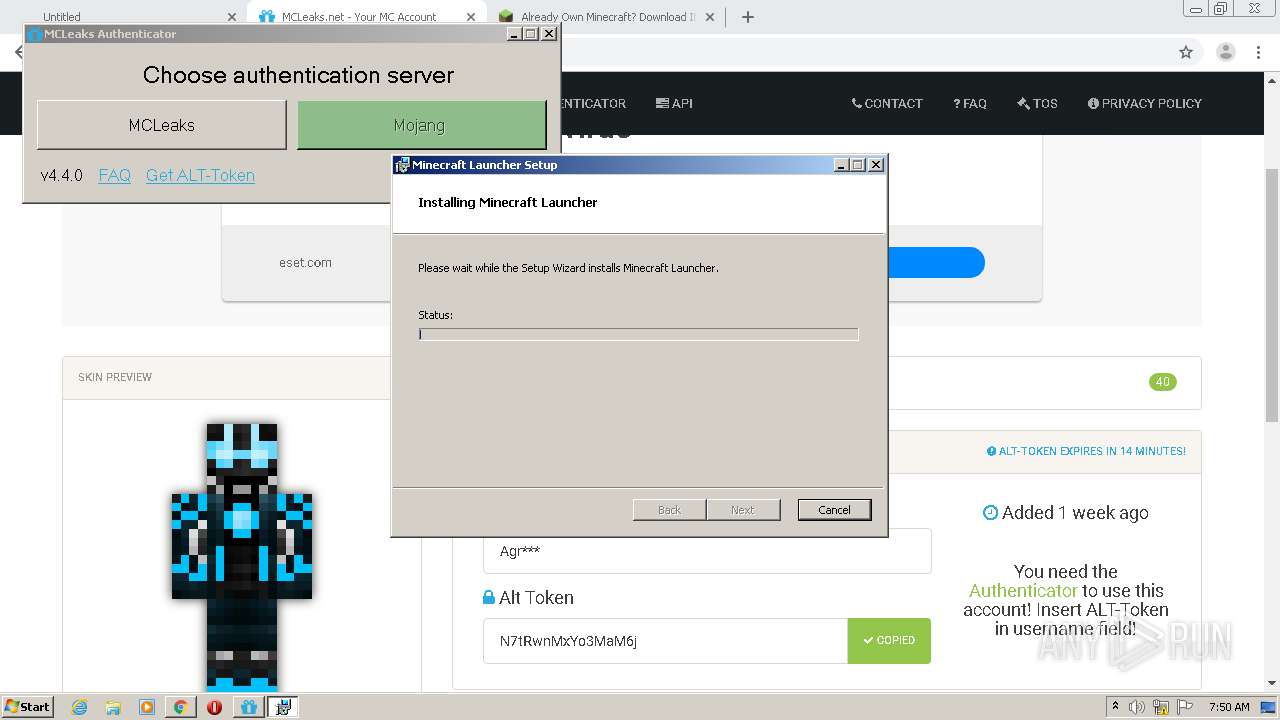
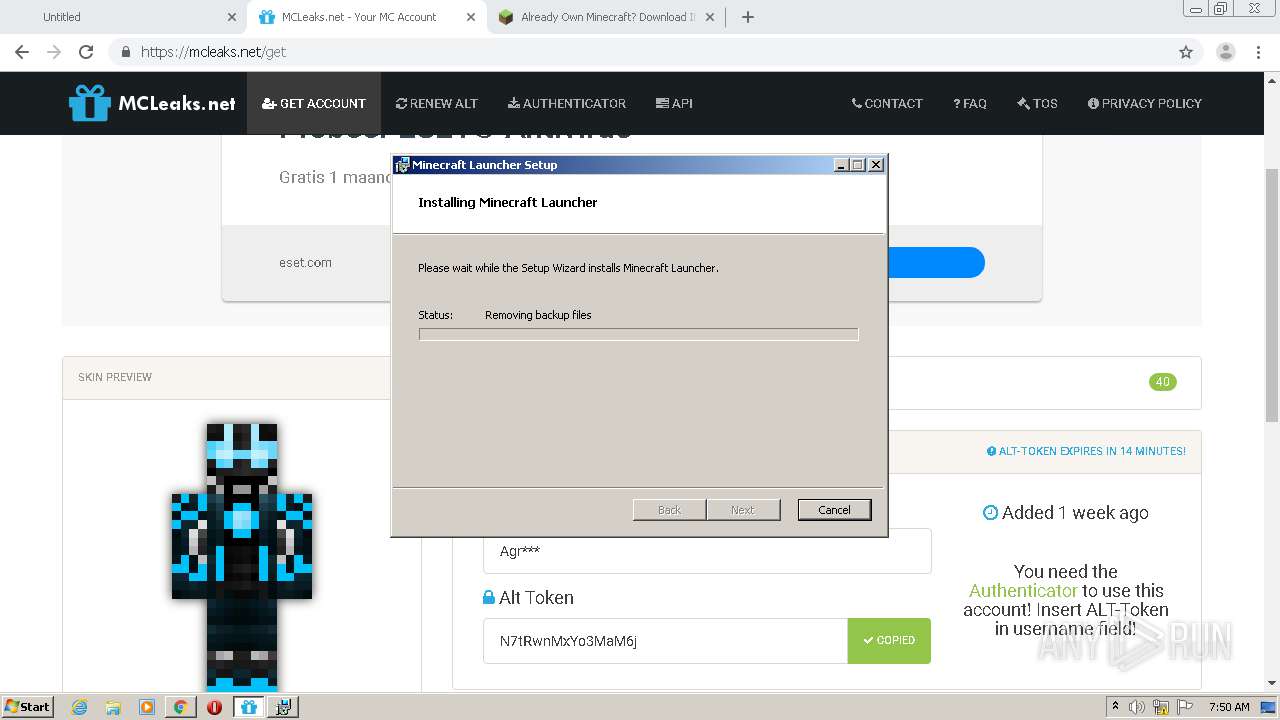
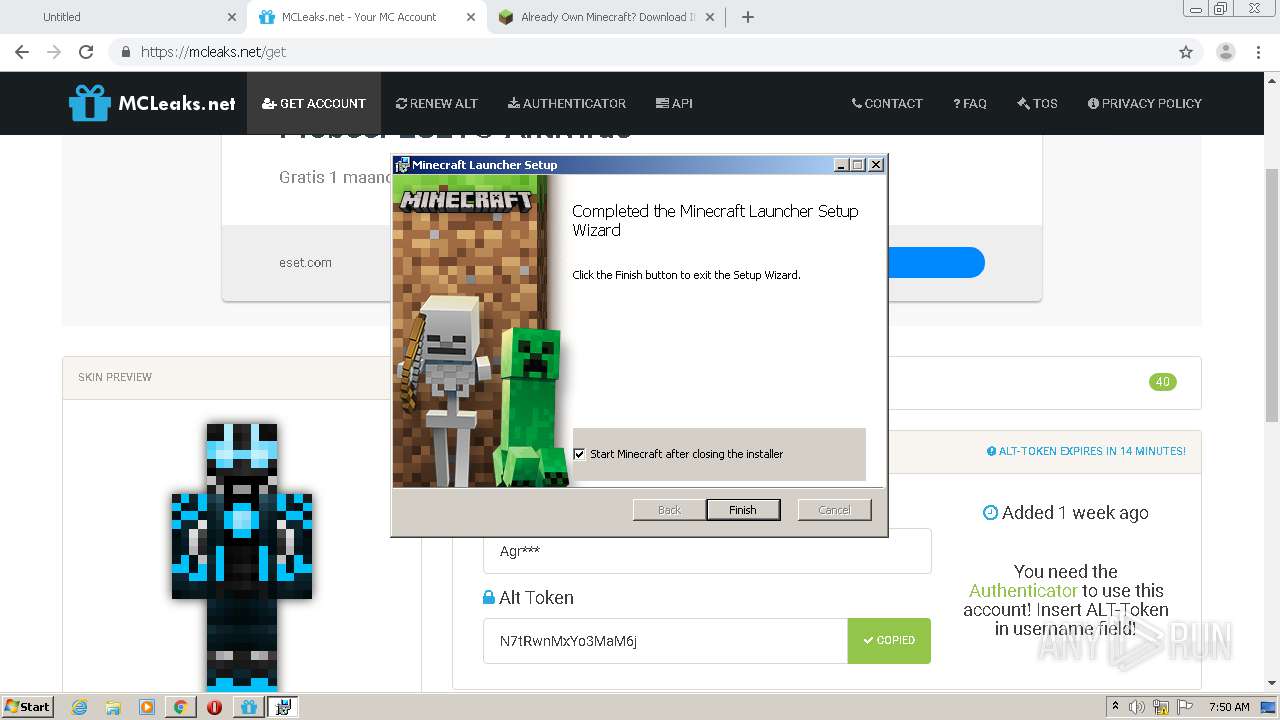
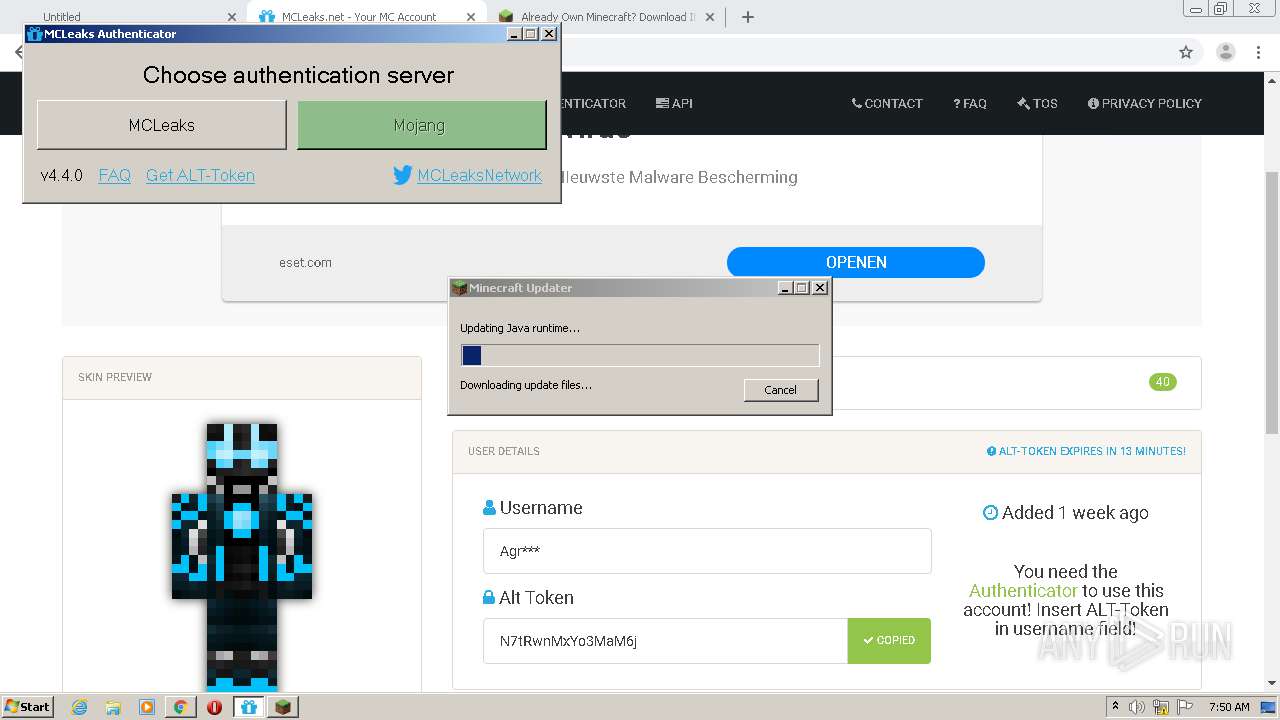
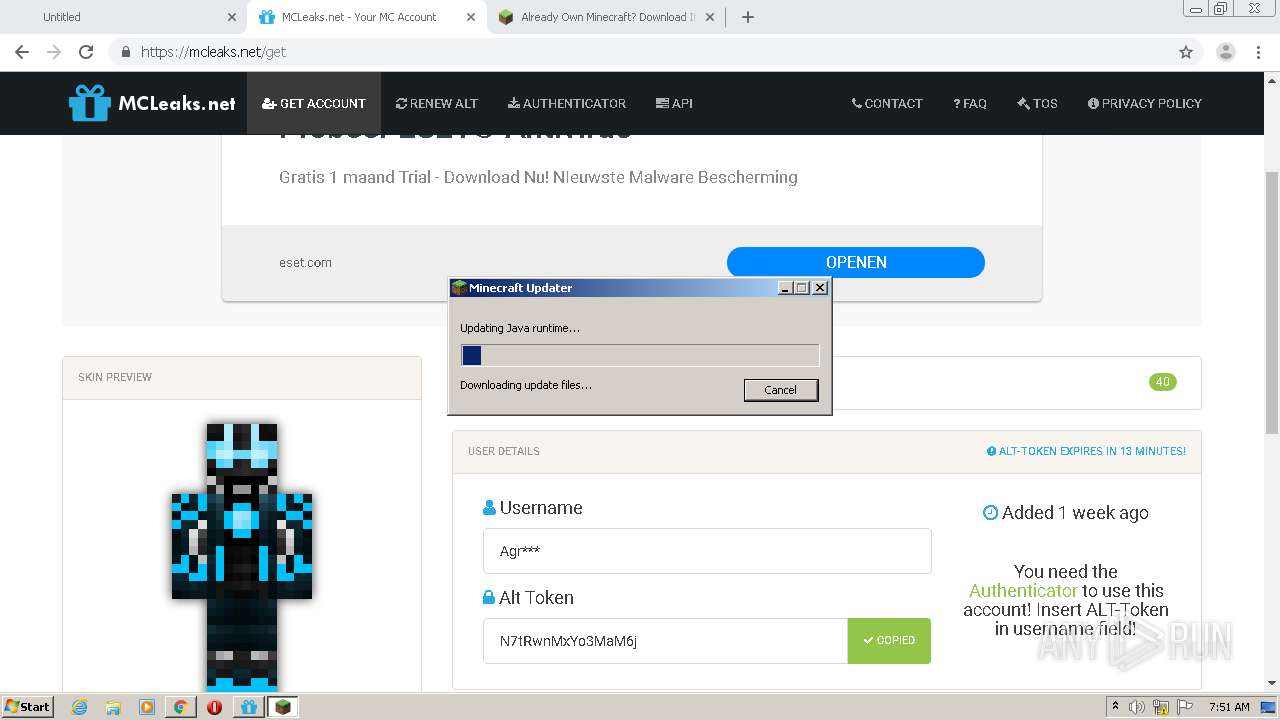
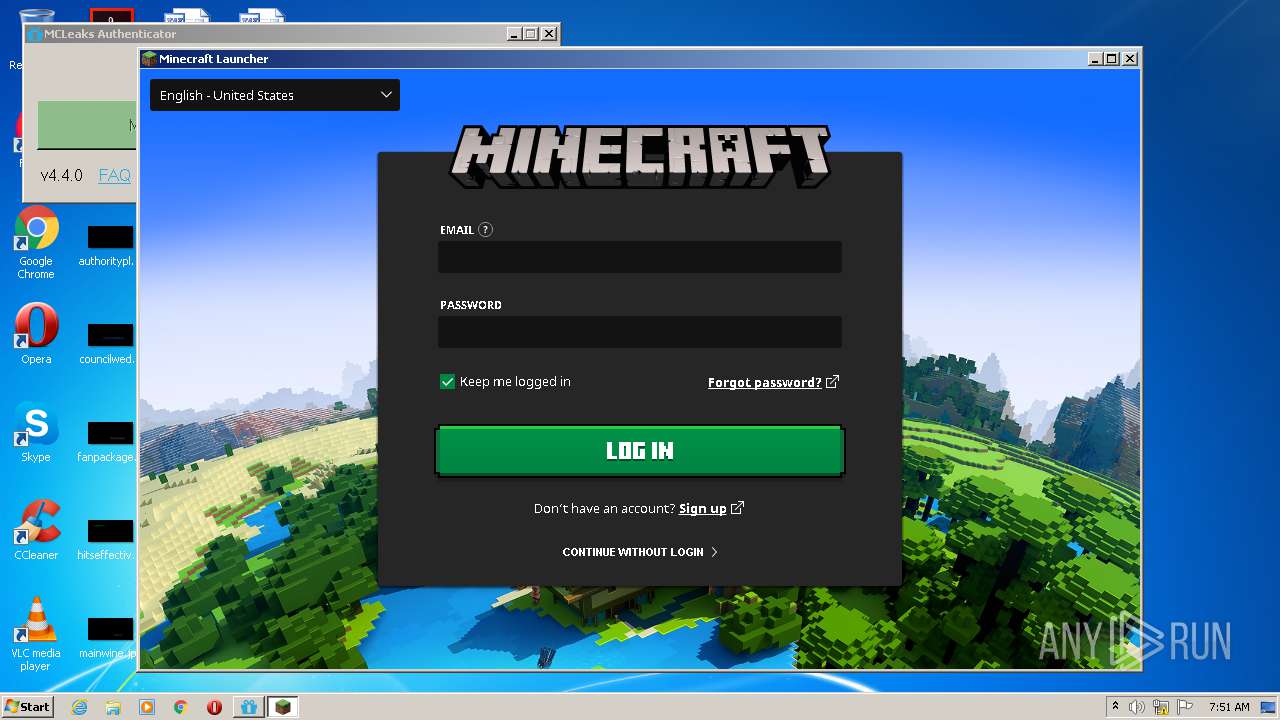
Application was dropped or rewritten from another process
- MCLeaksAuthenticator_4.4.0.exe (PID: 3736)
- MCLeaksAuthenticator_4.4.0.exe (PID: 2496)
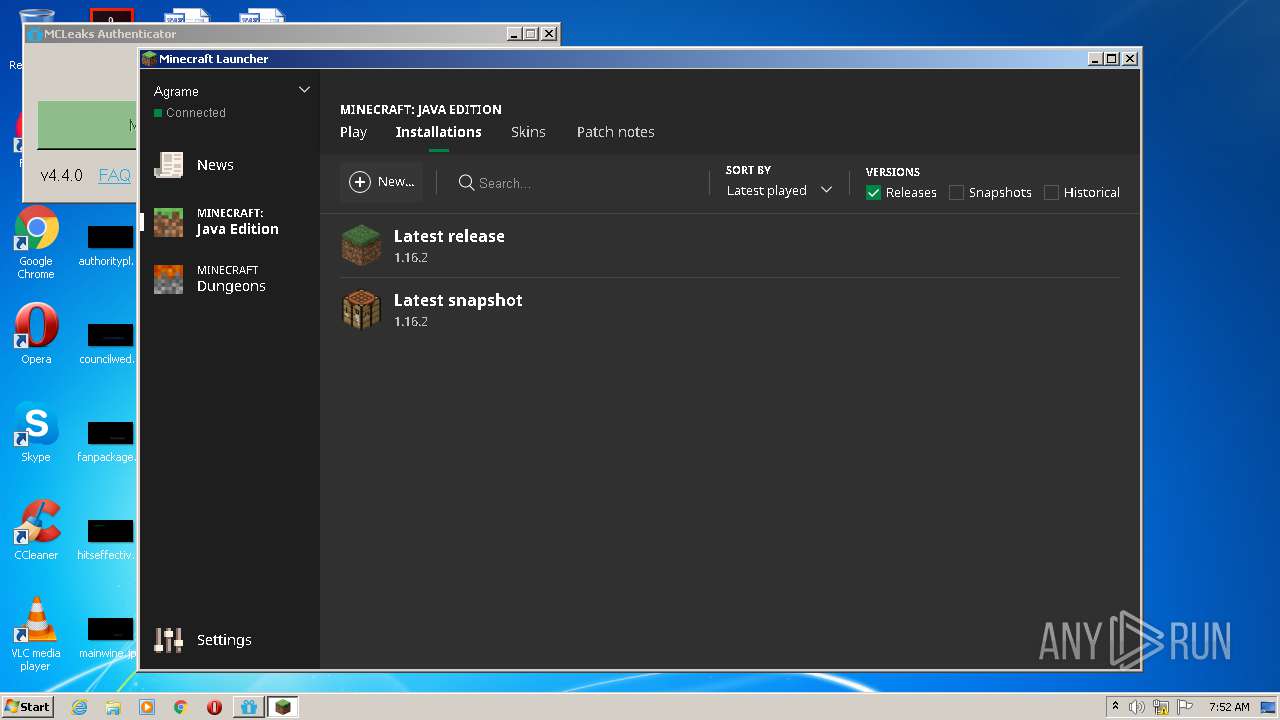
- MinecraftLauncher.exe (PID: 3896)
- MinecraftLauncher.exe (PID: 1748)
- keytool.exe (PID: 3564)
- keytool.exe (PID: 1828)
- MinecraftLauncher.exe (PID: 2776)
- MinecraftLauncher.exe (PID: 3380)
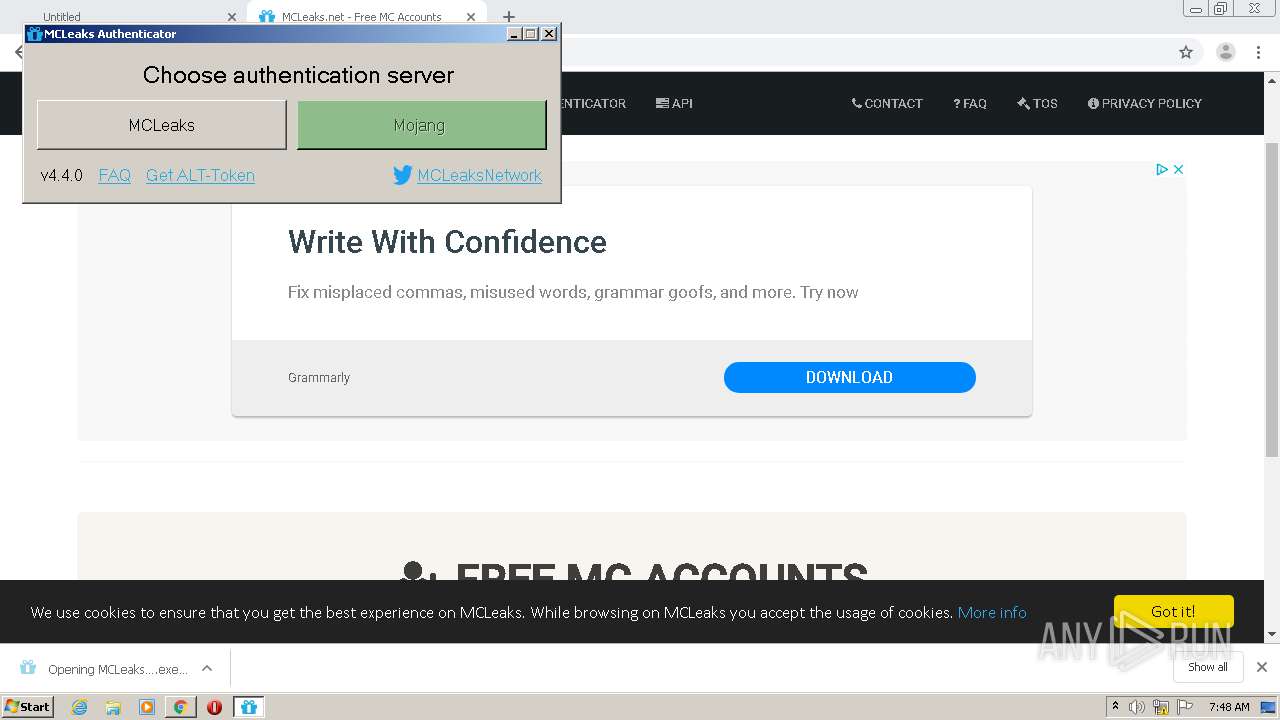
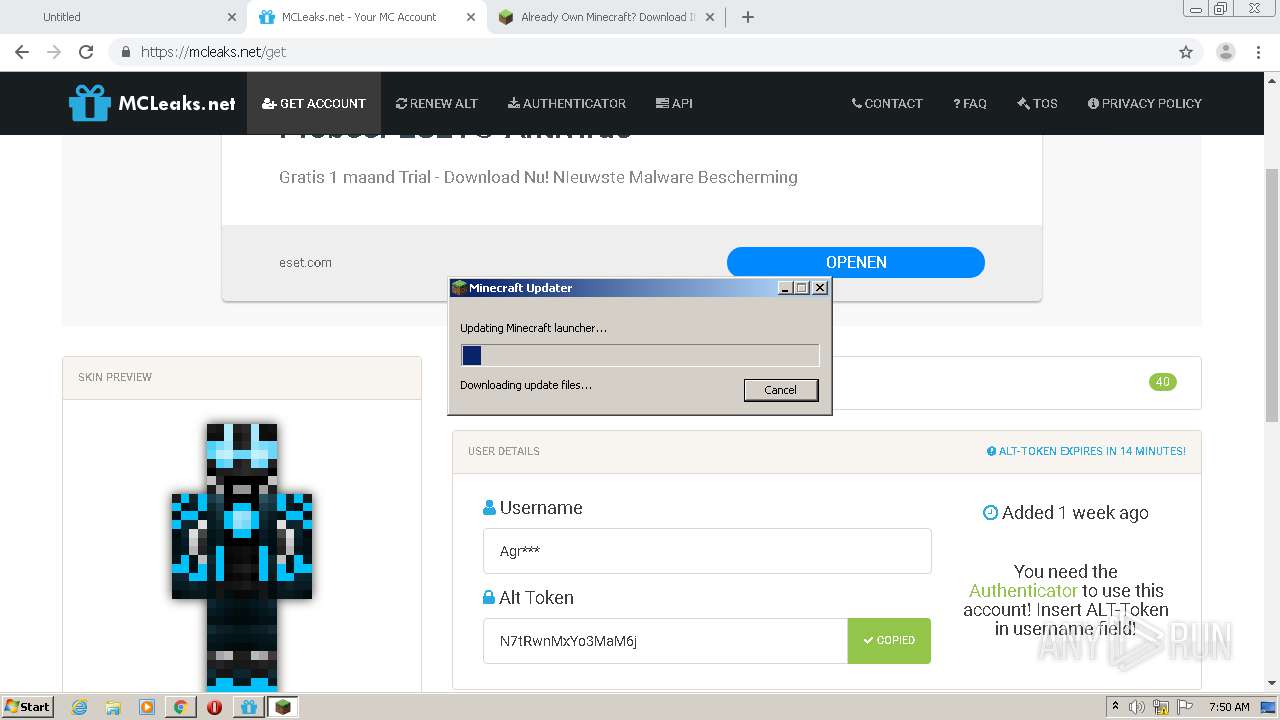
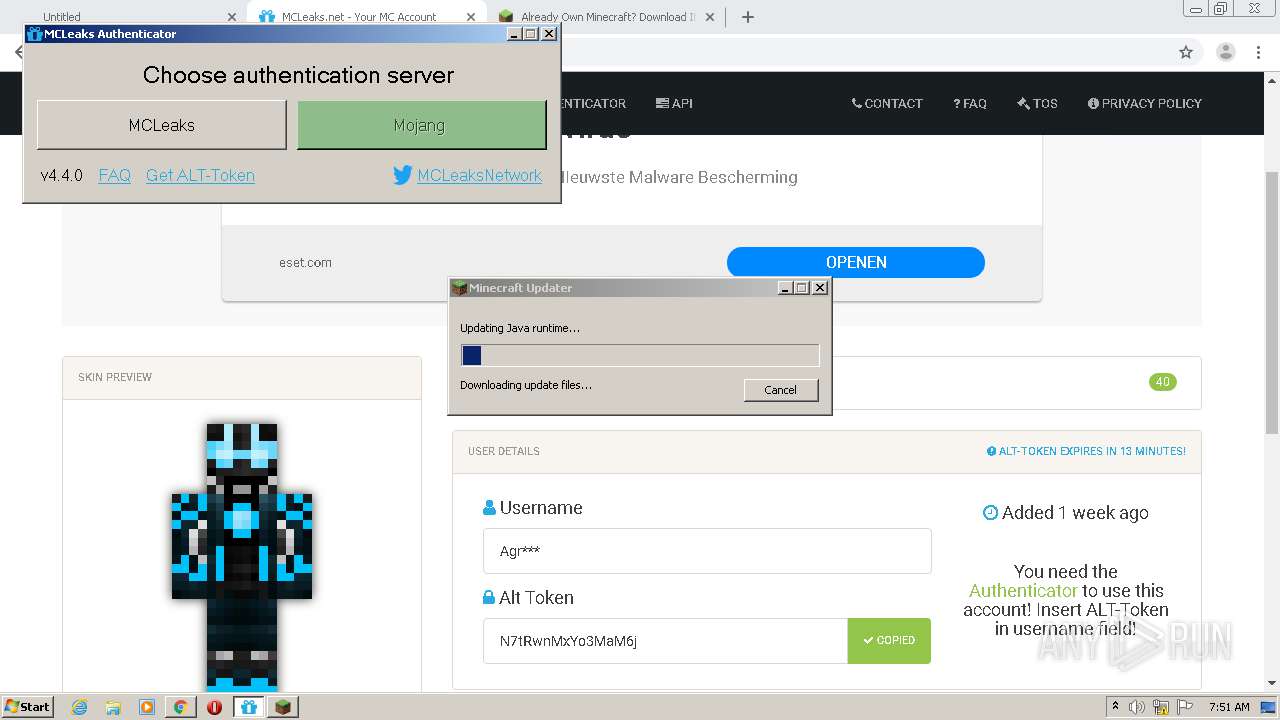
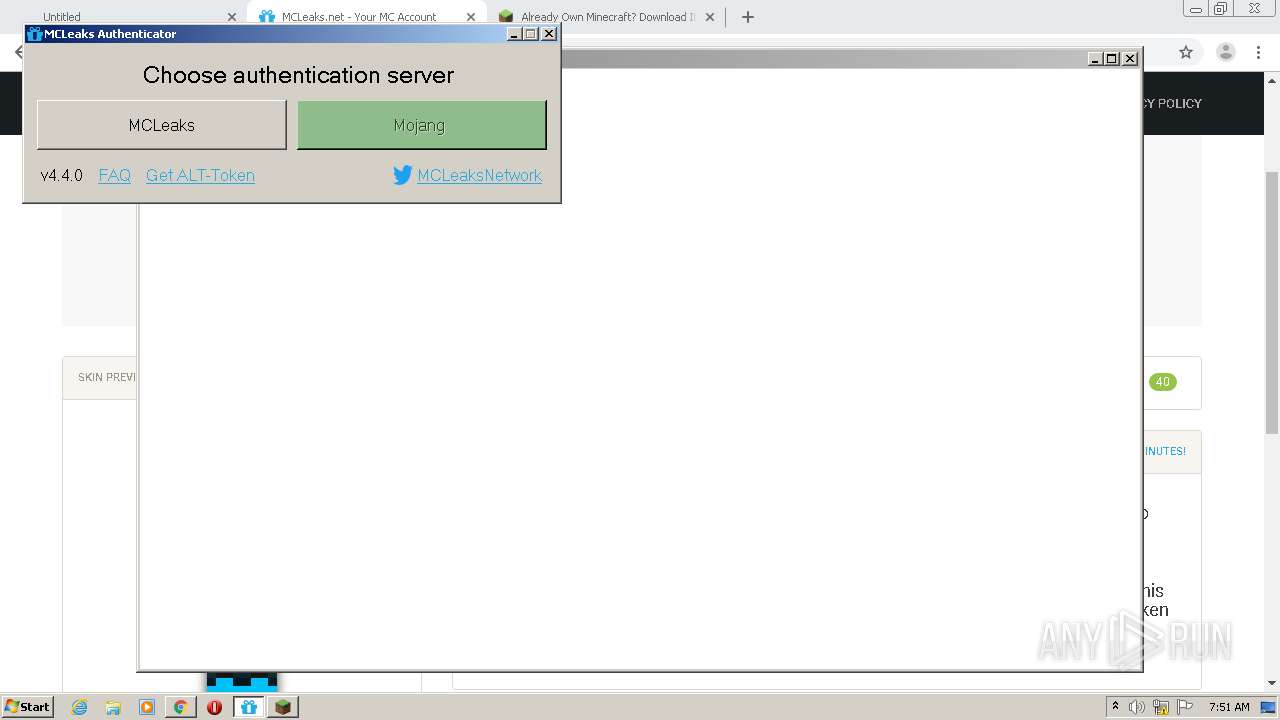
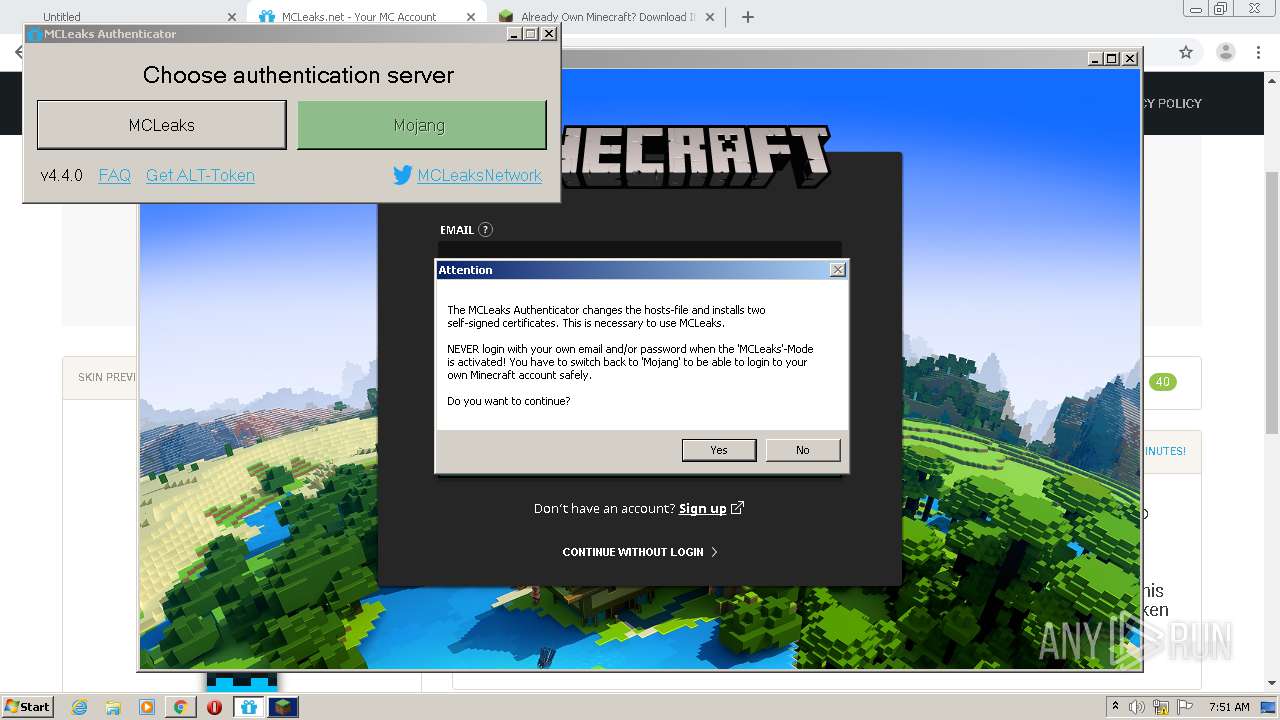
Changes settings of System certificates
- MCLeaksAuthenticator_4.4.0.exe (PID: 2496)
- certutil.exe (PID: 3876)
Loads dropped or rewritten executable
- MinecraftLauncher.exe (PID: 3896)
- MinecraftLauncher.exe (PID: 1748)
- keytool.exe (PID: 3564)
- keytool.exe (PID: 1828)
- MinecraftLauncher.exe (PID: 2776)
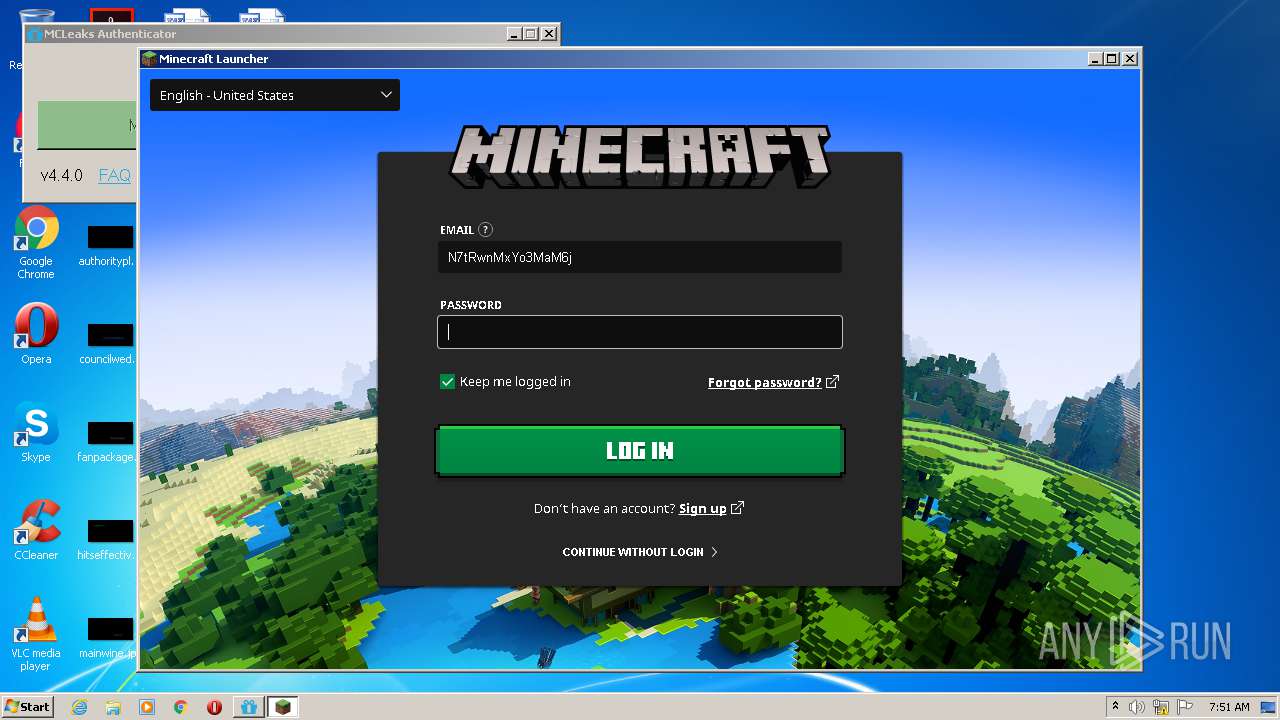
Writes to the hosts file
- MCLeaksAuthenticator_4.4.0.exe (PID: 2496)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2816)
- chrome.exe (PID: 2644)
- msiexec.exe (PID: 4072)
- MinecraftLauncher.exe (PID: 3896)
Starts Microsoft Installer
- chrome.exe (PID: 2816)
Adds / modifies Windows certificates
- MCLeaksAuthenticator_4.4.0.exe (PID: 2496)
Creates files in the user directory
- MinecraftLauncher.exe (PID: 3896)
- MCLeaksAuthenticator_4.4.0.exe (PID: 2496)
Removes files from Windows directory
- certutil.exe (PID: 3876)
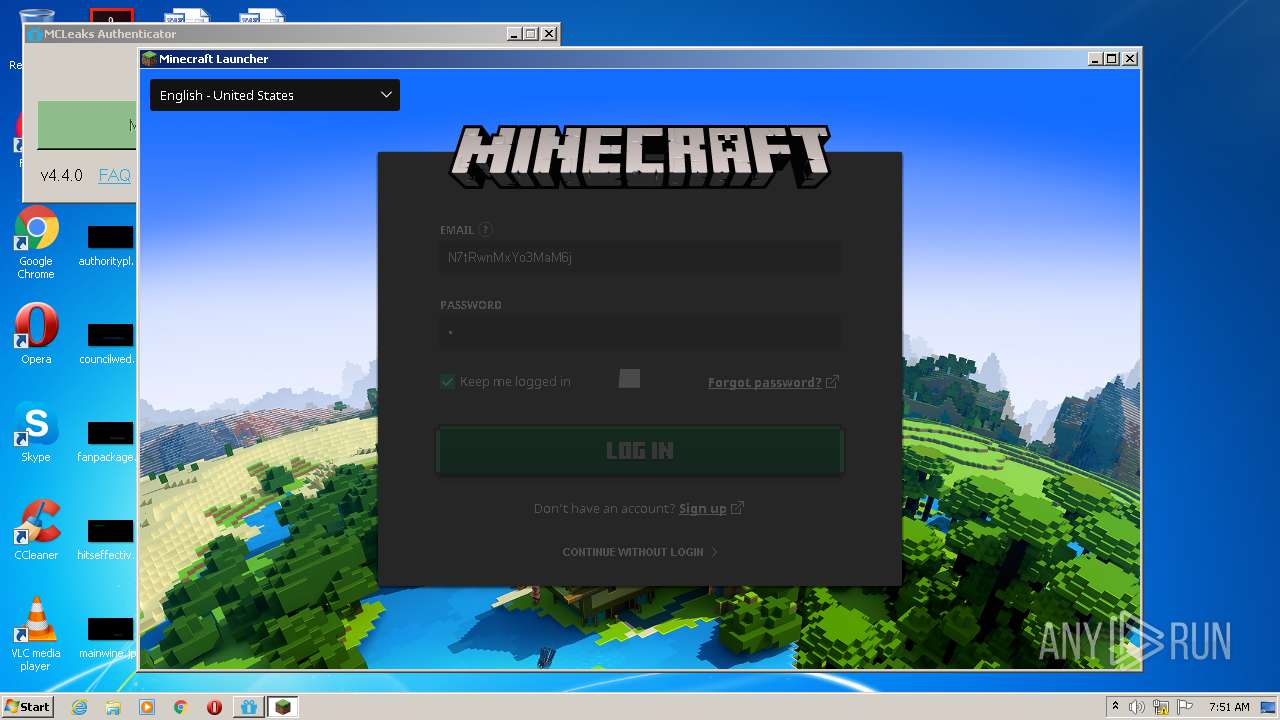
Application launched itself
- MinecraftLauncher.exe (PID: 3896)
- MinecraftLauncher.exe (PID: 2776)
Creates files in the Windows directory
- certutil.exe (PID: 3876)
Creates files in the program directory
- MinecraftLauncher.exe (PID: 3896)
Starts Internet Explorer
- MinecraftLauncher.exe (PID: 2776)
INFO
Application launched itself
- chrome.exe (PID: 2816)
- iexplore.exe (PID: 2252)
Reads the hosts file
- chrome.exe (PID: 2816)
- chrome.exe (PID: 2644)
- MCLeaksAuthenticator_4.4.0.exe (PID: 2496)
- MinecraftLauncher.exe (PID: 3896)
- MinecraftLauncher.exe (PID: 2776)
Reads settings of System Certificates
- chrome.exe (PID: 2644)
- MinecraftLauncher.exe (PID: 3896)
- MinecraftLauncher.exe (PID: 2776)
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 2252)
Reads Internet Cache Settings
- chrome.exe (PID: 2816)
- iexplore.exe (PID: 2252)
- iexplore.exe (PID: 4076)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1840)
- MsiExec.exe (PID: 3440)
- MsiExec.exe (PID: 2548)
Dropped object may contain Bitcoin addresses
- MinecraftLauncher.exe (PID: 3896)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 2644)
- iexplore.exe (PID: 4076)
Manual execution by user
- MinecraftLauncher.exe (PID: 2776)
Changes internet zones settings
- iexplore.exe (PID: 2252)
Creates files in the user directory
- iexplore.exe (PID: 4076)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2252)
Reads internet explorer settings
- iexplore.exe (PID: 4076)
Changes settings of System certificates
- iexplore.exe (PID: 2252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
95
Monitored processes
45
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12402589341762561296,11912508459725493961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=876140722192819465 --mojo-platform-channel-handle=912 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12402589341762561296,11912508459725493961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=678373434669096601 --mojo-platform-channel-handle=4416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,12402589341762561296,11912508459725493961,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=629222414153162982 --mojo-platform-channel-handle=4228 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,12402589341762561296,11912508459725493961,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11998677973984133268 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3740 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,12402589341762561296,11912508459725493961,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12577368541486309101 --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Minecraft Launcher\MinecraftLauncher.exe" --type=renderer --no-sandbox --service-pipe-token=0CF8F6911923BE34F09145B3991AEA87 --lang=en-US --lang=en-US --log-file="C:\Program Files\Minecraft Launcher\debug.log" --launcherui --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=0CF8F6911923BE34F09145B3991AEA87 --renderer-client-id=2 --mojo-platform-channel-handle=1580 /prefetch:1 | C:\Program Files\Minecraft Launcher\MinecraftLauncher.exe | — | MinecraftLauncher.exe | |||||||||||
User: admin Company: Mojang Integrity Level: MEDIUM Description: Minecraft launcher Exit code: 0 Version: 1.0.1.0 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Minecraft Launcher\runtime\jre-x86\bin\keytool.exe" -storepass "changeit" -noprompt -import -alias authserver.mojang.com -file "C:\Users\admin\AppData\Roaming\mcleaks\authserver.mojang.com.crt" -keystore "C:\Program Files\Minecraft Launcher\runtime\jre-x86\lib\security\cacerts" | C:\Program Files\Minecraft Launcher\runtime\jre-x86\bin\keytool.exe | — | MCLeaksAuthenticator_4.4.0.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.51.16 Modules
| |||||||||||||||
| 1840 | C:\Windows\system32\MsiExec.exe -Embedding 00818E7132DF52A5DCB722F12712B69E | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,12402589341762561296,11912508459725493961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=571042865825260837 --mojo-platform-channel-handle=4080 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2252 | "C:\Program Files\Internet Explorer\iexplore.exe" https://my.minecraft.net/profile/ | C:\Program Files\Internet Explorer\iexplore.exe | MinecraftLauncher.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 492
Read events
2 225
Write events
258
Delete events
9
Modification events
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2816-13242811683568125 |
Value: 259 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2816) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
135
Suspicious files
512
Text files
294
Unknown types
65
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\69fb9914-4ce9-42f1-8c5d-a4db18992765.tmp | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RF191265.TMP | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:1B8E44CB8872BF26BC5219E37A700F8A | SHA256:FD3D4BC8A7D28A05D1321F1D175FB59FC2BCC3532B92274A50133C22F0A0480A | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:D11C35B3D5258F594933332C11C6F0F2 | SHA256:DC2EB16E16FA3FB258AC31A481F817208CF0C917AF4224F2832588D3A64ADD05 | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:988975E56D776333B46F1BCAE6967C0E | SHA256:22186F0422A02BE70860975EF688A895EEA653C3A7259FFBA9114138A544E05A | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF19138e.TMP | — | |
MD5:— | SHA256:— | |||
| 2816 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF19117b.TMP | text | |
MD5:1B8E44CB8872BF26BC5219E37A700F8A | SHA256:FD3D4BC8A7D28A05D1321F1D175FB59FC2BCC3532B92274A50133C22F0A0480A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
174
DNS requests
92
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4076 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAiIzVJfGSRETRSlgpHeuVI%3D | US | der | 1.47 Kb | whitelisted |
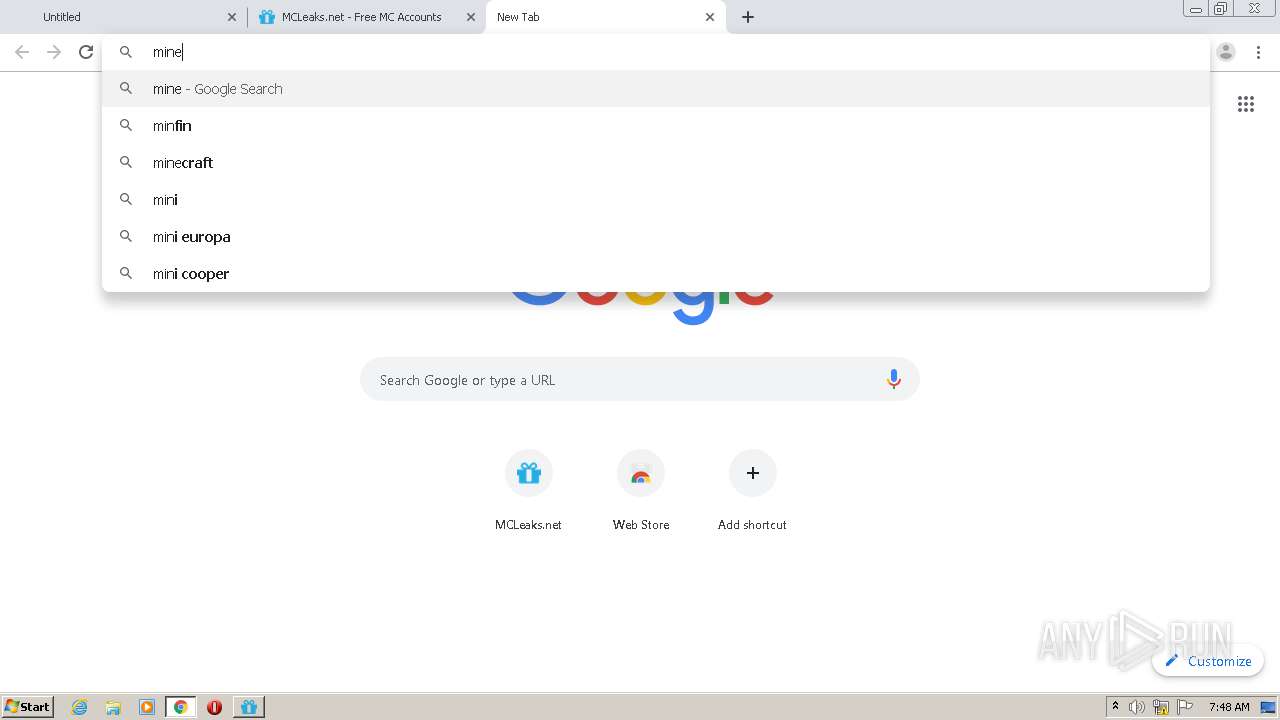
2644 | chrome.exe | GET | 301 | 172.67.190.251:80 | http://mcleaks.net/get | US | — | — | whitelisted |
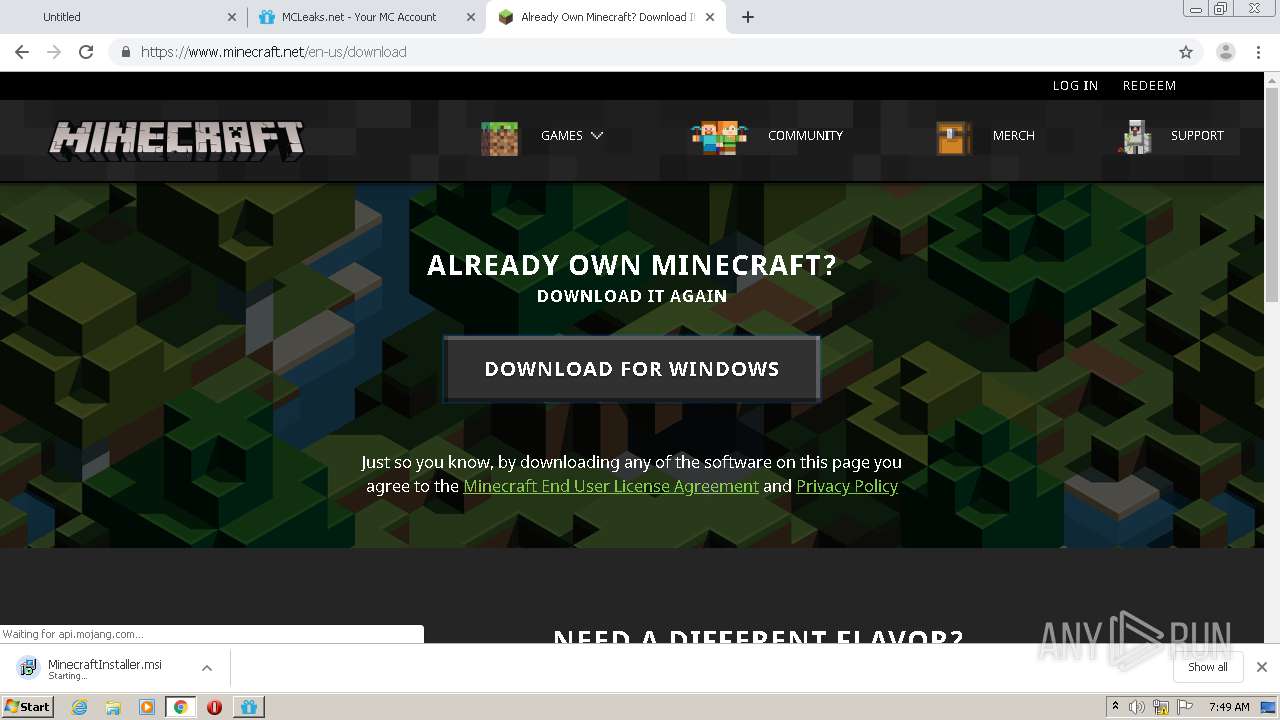
2644 | chrome.exe | GET | 301 | 13.226.135.57:80 | http://minecraft.net/en-us/download | US | html | 183 b | whitelisted |
4076 | iexplore.exe | GET | 200 | 13.226.156.74:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
4076 | iexplore.exe | GET | 200 | 13.226.156.74:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
4076 | iexplore.exe | GET | 200 | 13.226.156.74:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
4076 | iexplore.exe | GET | 200 | 13.226.156.67:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
4076 | iexplore.exe | GET | 200 | 13.226.156.125:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
4076 | iexplore.exe | GET | 200 | 13.226.156.15:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEA8zewPfKIhZJxIOrEQxmFI%3D | US | der | 471 b | whitelisted |
4076 | iexplore.exe | GET | 200 | 13.226.156.125:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2644 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
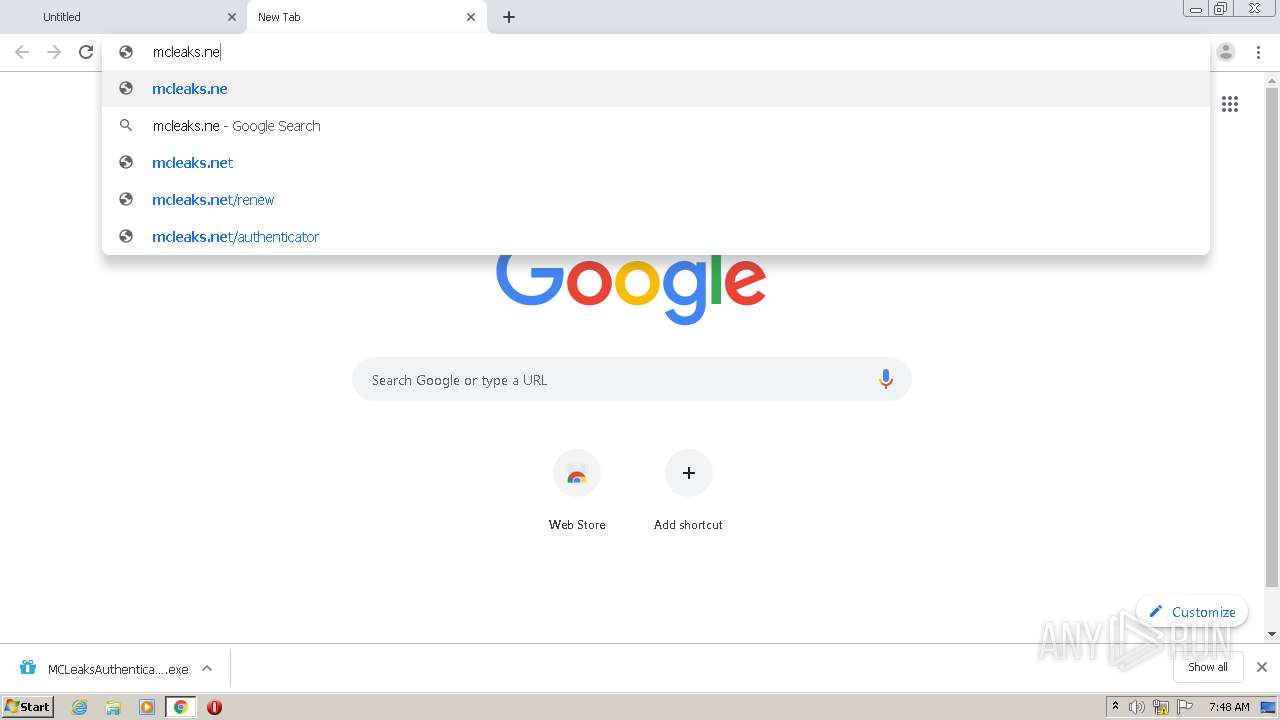
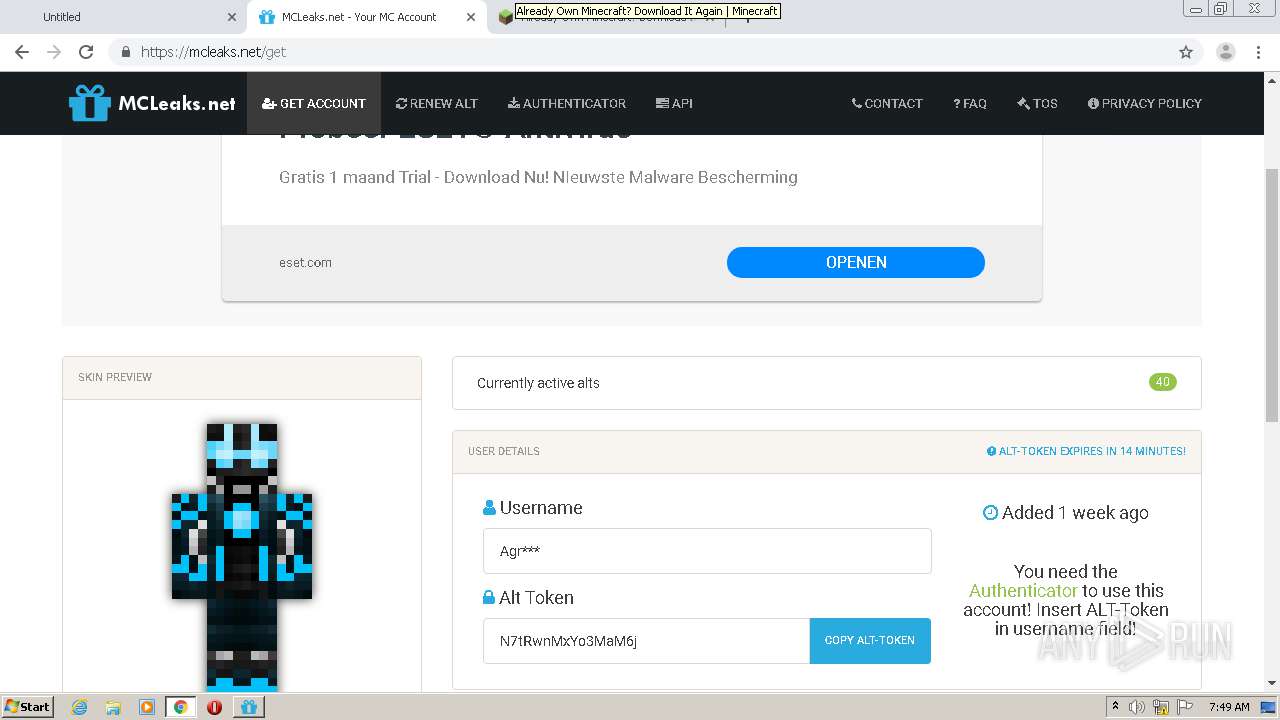
2644 | chrome.exe | 172.67.190.251:443 | mcleaks.net | — | US | unknown |
2644 | chrome.exe | 172.217.18.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2644 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
2644 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2644 | chrome.exe | 172.217.23.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2644 | chrome.exe | 172.217.18.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2644 | chrome.exe | 216.58.212.174:443 | ogs.google.be | Google Inc. | US | whitelisted |
2644 | chrome.exe | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2644 | chrome.exe | 172.67.190.251:80 | mcleaks.net | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
mcleaks.net |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.be |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |