| File name: | rdpHelper.exe_ |
| Full analysis: | https://app.any.run/tasks/a3b783e8-fb00-4765-87da-73847ffe1e5f |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
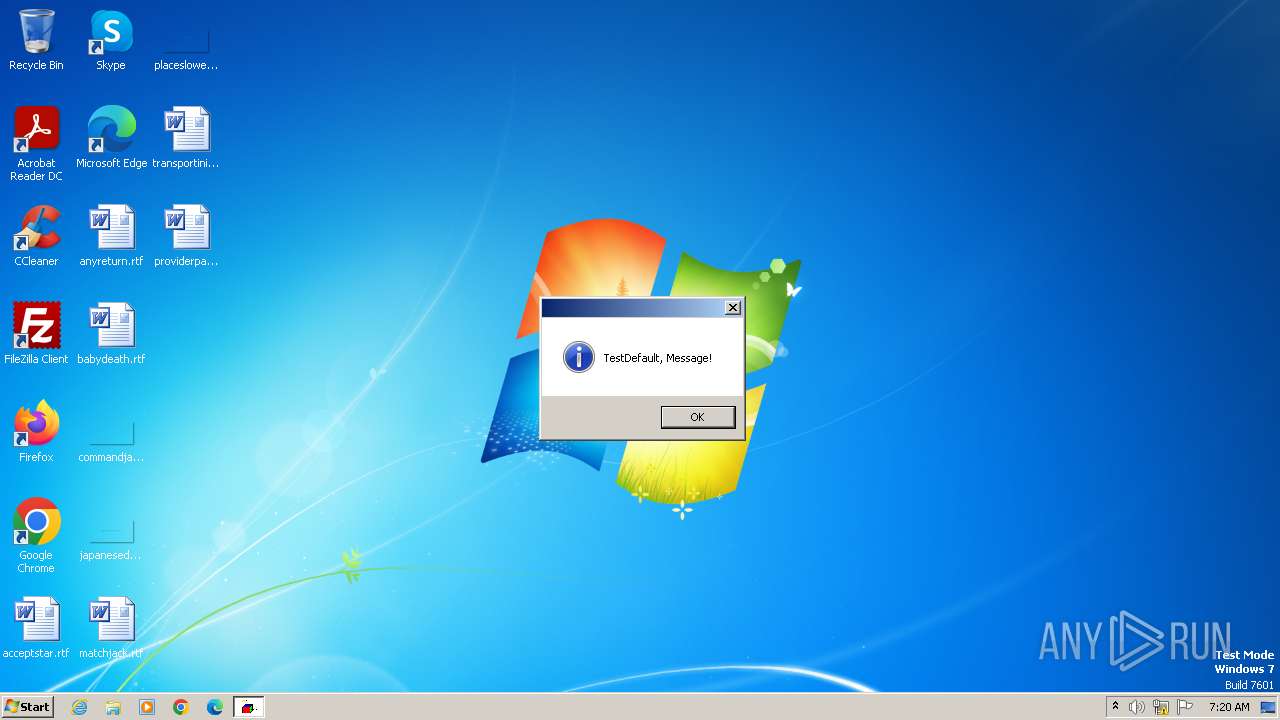
| Analysis date: | November 02, 2023, 07:20:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1E8B35B160FEB419CB6F58B915C11307 |
| SHA1: | 818CF033DE3B72E18B70CA832653E27E54A22302 |
| SHA256: | 13F25202CD0885DFDEB0C24E856A66A920E1FEB0FD87468F928768131C84AB8C |
| SSDEEP: | 49152:RbA3lgViq4EdTp49JkoIoAAeM4hSIW4hxSVkhl0FiHA9nIWAz/FiKJ86RSQMJ3lk:RbfV7dTpholAfhFByien5W8KJ5HMJ3g9 |
MALICIOUS
Drops the executable file immediately after the start
- rdpHelper.exe_.exe (PID: 3512)
- chainportruntime.exe (PID: 3756)
- taskeng.exe (PID: 2316)
UAC/LUA settings modification
- chainportruntime.exe (PID: 3756)
- taskeng.exe (PID: 2316)
- taskeng.exe (PID: 3416)
- cmd.exe (PID: 2528)
Adds path to the Windows Defender exclusion list
- chainportruntime.exe (PID: 3756)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2944)
- wscript.exe (PID: 2972)
- wscript.exe (PID: 3412)
DCRAT has been detected (YARA)
- taskeng.exe (PID: 2316)
SUSPICIOUS
Executing commands from a ".bat" file
- wscript.exe (PID: 3412)
Runs shell command (SCRIPT)
- wscript.exe (PID: 3412)
- wscript.exe (PID: 2944)
Executed via WMI
- schtasks.exe (PID: 3744)
- schtasks.exe (PID: 3988)
- schtasks.exe (PID: 4004)
- schtasks.exe (PID: 3960)
- schtasks.exe (PID: 4044)
- schtasks.exe (PID: 3792)
- schtasks.exe (PID: 3536)
- schtasks.exe (PID: 3992)
- schtasks.exe (PID: 4080)
- schtasks.exe (PID: 3628)
- schtasks.exe (PID: 3788)
- schtasks.exe (PID: 4068)
- schtasks.exe (PID: 2380)
- schtasks.exe (PID: 1756)
- schtasks.exe (PID: 528)
- schtasks.exe (PID: 1604)
- schtasks.exe (PID: 1616)
- schtasks.exe (PID: 556)
- schtasks.exe (PID: 3672)
- schtasks.exe (PID: 916)
- schtasks.exe (PID: 3820)
The process creates files with name similar to system file names
- chainportruntime.exe (PID: 3756)
Starts itself from another location
- chainportruntime.exe (PID: 3756)
Script adds exclusion path to Windows Defender
- chainportruntime.exe (PID: 3756)
Reads the Internet Settings
- chainportruntime.exe (PID: 3756)
- taskeng.exe (PID: 2316)
- rdpHelper.exe_.exe (PID: 3512)
- wscript.exe (PID: 3412)
Starts POWERSHELL.EXE for commands execution
- chainportruntime.exe (PID: 3756)
Powershell version downgrade attack
- powershell.exe (PID: 148)
- powershell.exe (PID: 2164)
- powershell.exe (PID: 1612)
- powershell.exe (PID: 2000)
- powershell.exe (PID: 1232)
- powershell.exe (PID: 712)
- powershell.exe (PID: 2088)
- powershell.exe (PID: 1880)
The process executes VB scripts
- taskeng.exe (PID: 2316)
- rdpHelper.exe_.exe (PID: 3512)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 2944)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 2944)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 2972)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 2972)
- wscript.exe (PID: 2944)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 2944)
The process executes via Task Scheduler
- cmd.exe (PID: 2528)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3412)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 3436)
- chainportruntime.exe (PID: 3756)
- rdpHelper.exe_.exe (PID: 3512)
- taskeng.exe (PID: 2316)
- taskeng.exe (PID: 3416)
- wmpnscfg.exe (PID: 3368)
- cmd.exe (PID: 2528)
Reads the computer name
- wmpnscfg.exe (PID: 3436)
- rdpHelper.exe_.exe (PID: 3512)
- taskeng.exe (PID: 2316)
- wmpnscfg.exe (PID: 3368)
- taskeng.exe (PID: 3416)
- chainportruntime.exe (PID: 3756)
- cmd.exe (PID: 2528)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3436)
- chainportruntime.exe (PID: 3756)
- taskeng.exe (PID: 2316)
- wmpnscfg.exe (PID: 3368)
- taskeng.exe (PID: 3416)
- cmd.exe (PID: 2528)
Reads Environment values
- chainportruntime.exe (PID: 3756)
- taskeng.exe (PID: 2316)
- taskeng.exe (PID: 3416)
- cmd.exe (PID: 2528)
Reads product name
- chainportruntime.exe (PID: 3756)
- taskeng.exe (PID: 2316)
- taskeng.exe (PID: 3416)
- cmd.exe (PID: 2528)
Process checks are UAC notifies on
- chainportruntime.exe (PID: 3756)
- taskeng.exe (PID: 2316)
- taskeng.exe (PID: 3416)
- cmd.exe (PID: 2528)
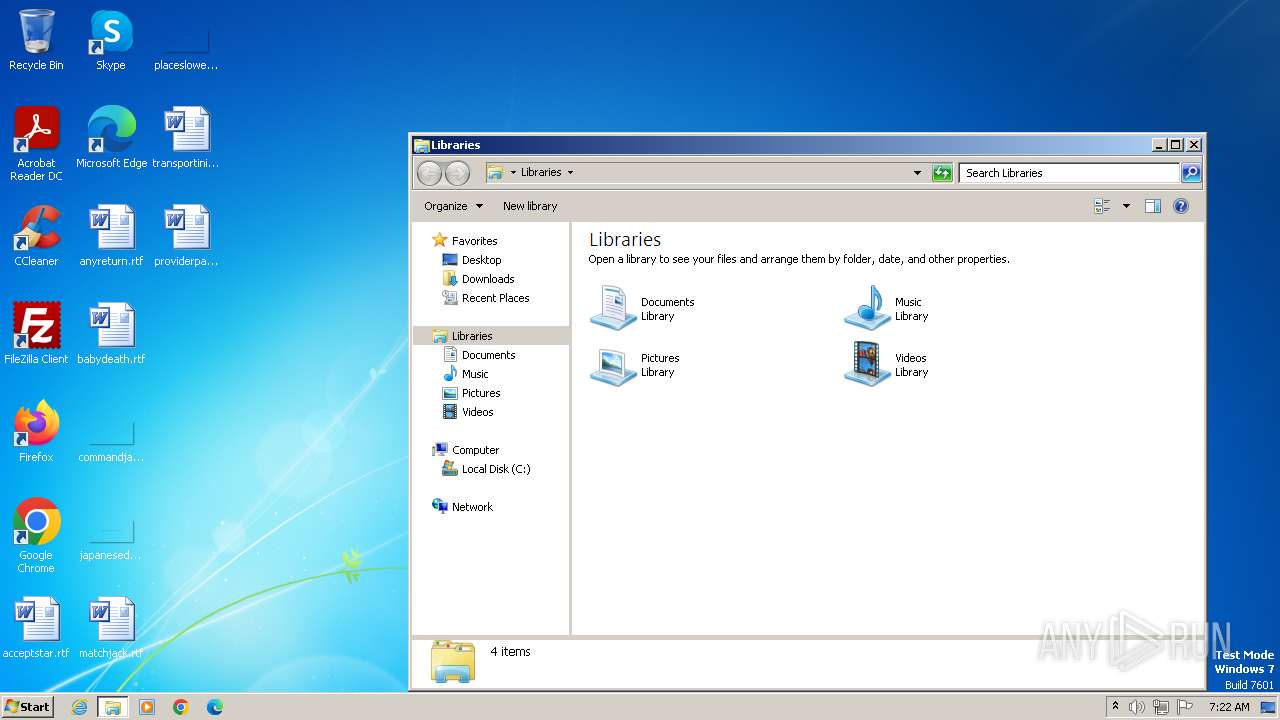
Creates files in the program directory
- chainportruntime.exe (PID: 3756)
Create files in a temporary directory
- taskeng.exe (PID: 2316)
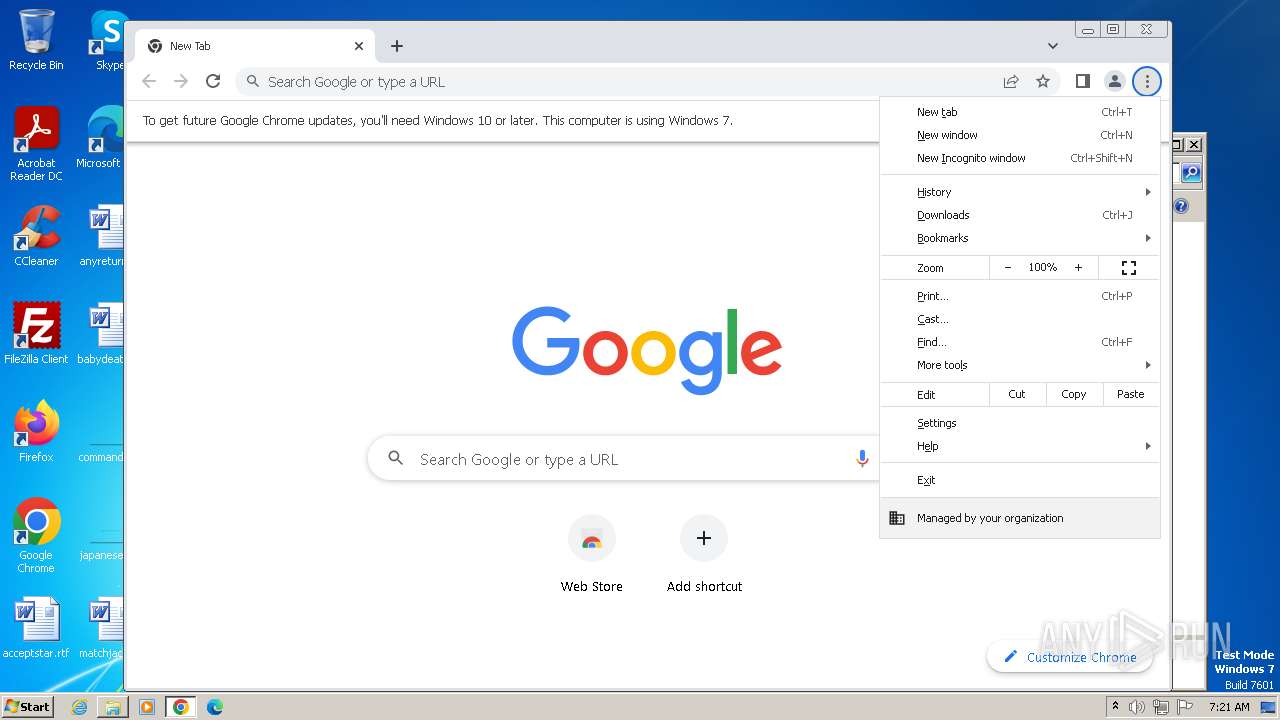
Manual execution by a user
- wmpnscfg.exe (PID: 3368)
- explorer.exe (PID: 3664)
- chrome.exe (PID: 3732)
Application launched itself
- chrome.exe (PID: 3732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
DcRat
(PID) Process(2316) taskeng.exe
C2 (1)http://80.78.247.7/base0/2CpuDle/BigloaddefaultJavascript/privatePipeGeosecure/7/@zd3bk5WaXlGchN3clN2byBXZ0FGZwV3X
Options
MutexDCR_MUTEX-rQQ7lJpc0sUXEdH002uJ
savebrowsersdatatosinglefilefalse
ignorepartiallyemptydatafalse
cookiestrue
passwordstrue
formstrue
cctrue
historytrue
telegramtrue
steamtrue
discordtrue
filezillatrue
screenshottrue
clipboardtrue
sysinfotrue
searchpath{SYSTEMDRIVE}/Users/{USERNAME}/AppData/;{SYSTEMDRIVE}/Users/{USERNAME}/Desktop/;{SYSTEMDRIVE}/Users/{USERNAME}/Downloads/;{SYSTEMDRIVE}/Users/{USERNAME}/OpenVPN/config/;D:/;
Targetru
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:12:01 19:00:55+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 201216 |
| InitializedDataSize: | 137728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ec40 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
101
Monitored processes
53
Malicious processes
15
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:\Windows\ModemLogs\SearchIndexer.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | chainportruntime.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 528 | schtasks.exe /create /tn "cmdc" /sc MINUTE /mo 5 /tr "'C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\cmd.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 556 | schtasks.exe /create /tn "IMEDICTUPDATEI" /sc MINUTE /mo 11 /tr "'C:\MsagentIntoPerfCommon\IMEDICTUPDATE.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 712 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\cmd.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | chainportruntime.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | schtasks.exe /create /tn "wininitw" /sc MINUTE /mo 13 /tr "'C:\Program Files\Microsoft Office\CLIPART\PUB60COR\wininit.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2112 --field-trial-handle=1160,i,15269091311998428159,17485035996280840098,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1232 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:\Windows\Panther\setup.exe\IMEDICTUPDATE.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | chainportruntime.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2144 --field-trial-handle=1160,i,15269091311998428159,17485035996280840098,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1604 | schtasks.exe /create /tn "IMEDICTUPDATEI" /sc MINUTE /mo 9 /tr "'C:\MsagentIntoPerfCommon\IMEDICTUPDATE.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1612 | "powershell" -Command Add-MpPreference -ExclusionPath 'C:\Program Files\Microsoft Office\CLIPART\PUB60COR\wininit.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | chainportruntime.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
15 123
Read events
14 608
Write events
509
Delete events
6
Modification events
| (PID) Process: | (3436) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{A0B066CE-F2EF-45EA-8FF7-26F391F5C737}\{857FCC3A-07A0-40BD-B781-EBA324CC6E41} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3436) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{A0B066CE-F2EF-45EA-8FF7-26F391F5C737} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3436) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{622543A4-75A1-49AC-B1EB-13369586EEDA} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3512) rdpHelper.exe_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3512) rdpHelper.exe_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3512) rdpHelper.exe_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3512) rdpHelper.exe_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3412) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3412) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3412) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
9
Suspicious files
72
Text files
39
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3512 | rdpHelper.exe_.exe | C:\MsagentIntoPerfCommon\gq1DoNGewQk1eSwuMtaNCess40r.bat | text | |
MD5:E3C9CBF2BC8B86B784E1263625CCC058 | SHA256:9611227D74D195C8814595A48213FEFDE2B15286A93B61175CCEC2DC0BFE1D0B | |||
| 3512 | rdpHelper.exe_.exe | C:\MsagentIntoPerfCommon\sPWugGHEh.vbe | binary | |
MD5:3DB9E950B0D9A5DDA15BD27437EF9932 | SHA256:B055E2B1DD6B4C79DB2239504463AC86E8BAF0CD79951E642D765779A9B8B112 | |||
| 3756 | chainportruntime.exe | C:\Windows\Panther\setup.exe\IMEDICTUPDATE.exe | executable | |
MD5:05B000A3F0E4A4370EFD644162D3685A | SHA256:50F5F76724C901E9A7A8688DCD9ACD00E5E8726C1DEDAF839B67E6E133CC0E12 | |||
| 3756 | chainportruntime.exe | C:\MSOCache\All Users\{90140000-001A-040C-0000-0000000FF1CE}-C\96094160f8fe35 | text | |
MD5:499F463ED5342A892912BDFFB87F828F | SHA256:D98F0466F0E28CD6E3D2C16AB13752CA28A0ADB796D36B793ECA92A1A7038FFC | |||
| 3512 | rdpHelper.exe_.exe | C:\MsagentIntoPerfCommon\chainportruntime.exe | executable | |
MD5:05B000A3F0E4A4370EFD644162D3685A | SHA256:50F5F76724C901E9A7A8688DCD9ACD00E5E8726C1DEDAF839B67E6E133CC0E12 | |||
| 3756 | chainportruntime.exe | C:\MSOCache\All Users\{90140000-001A-040C-0000-0000000FF1CE}-C\taskeng.exe | executable | |
MD5:05B000A3F0E4A4370EFD644162D3685A | SHA256:50F5F76724C901E9A7A8688DCD9ACD00E5E8726C1DEDAF839B67E6E133CC0E12 | |||
| 3512 | rdpHelper.exe_.exe | C:\MsagentIntoPerfCommon\file.vbs | text | |
MD5:677CC4360477C72CB0CE00406A949C61 | SHA256:F1CCCB5AE4AA51D293BD3C7D2A1A04CB7847D22C5DB8E05AC64E9A6D7455AA0B | |||
| 3756 | chainportruntime.exe | C:\Program Files\Microsoft Office\CLIPART\PUB60COR\56085415360792 | text | |
MD5:CA37EFDB2F77E7DB97CD9F6851ACFCF0 | SHA256:307567FF934C02EF66A005C936E7B3D9DCDB956213C9102CD7699EB3000F9850 | |||
| 3756 | chainportruntime.exe | C:\Program Files\Microsoft Office\CLIPART\PUB60COR\wininit.exe | executable | |
MD5:05B000A3F0E4A4370EFD644162D3685A | SHA256:50F5F76724C901E9A7A8688DCD9ACD00E5E8726C1DEDAF839B67E6E133CC0E12 | |||
| 3756 | chainportruntime.exe | C:\Windows\Panther\setup.exe\5940a34987c991 | text | |
MD5:892A58FBAC1E4B28724071FCFF4F1331 | SHA256:66A6E18874FB92604288F60C7FB789A0BB369A0F92A82BB30CE79DD6A629591F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
17
DNS requests
22
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2316 | taskeng.exe | 80.78.247.7:80 | — | Domain names registrar REG.RU, Ltd | RU | unknown |
3732 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3932 | chrome.exe | 142.250.186.109:443 | accounts.google.com | GOOGLE | US | whitelisted |
3932 | chrome.exe | 142.250.185.227:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
3932 | chrome.exe | 142.250.186.68:443 | www.google.com | GOOGLE | US | whitelisted |
3932 | chrome.exe | 172.217.18.3:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
dns.msftncsi.com |
| shared |