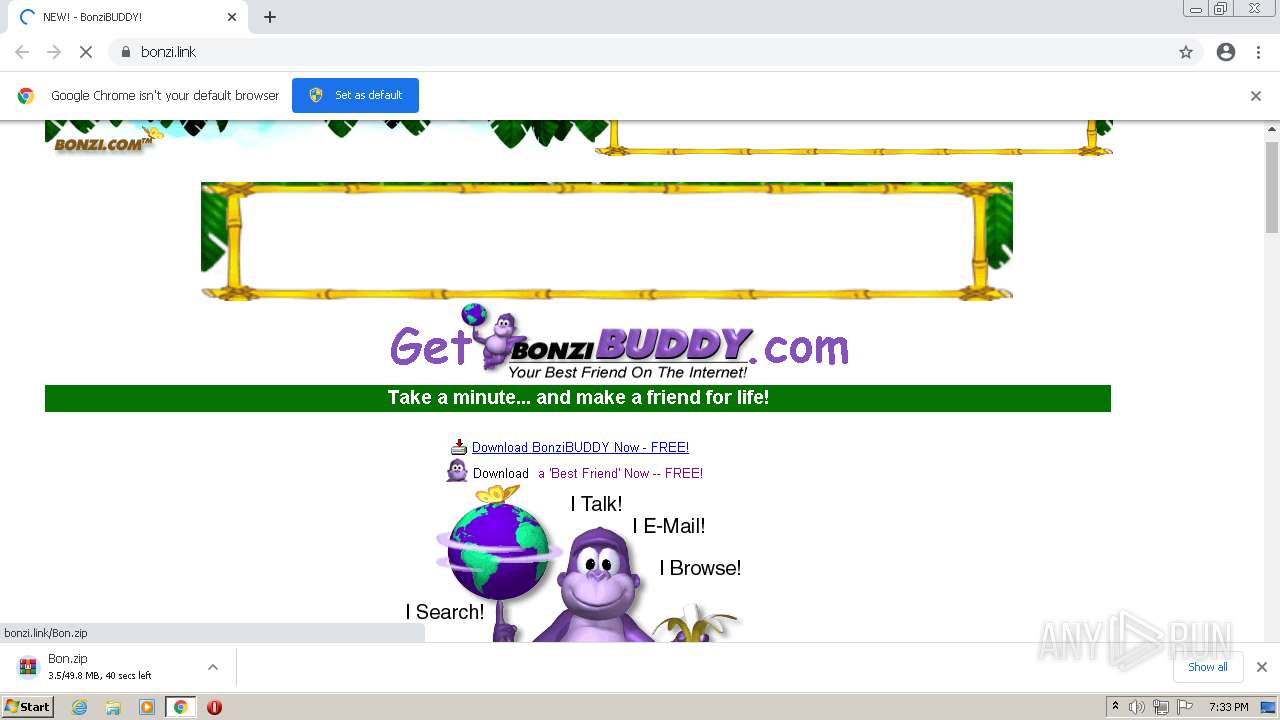
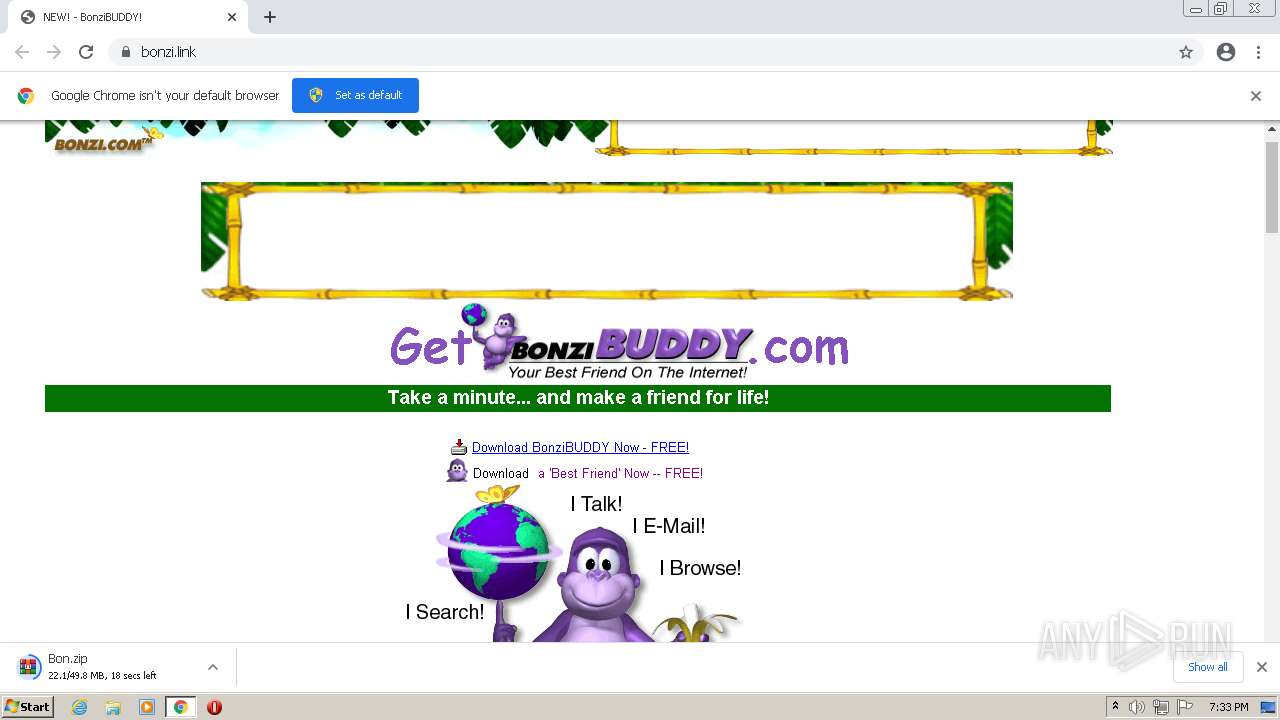
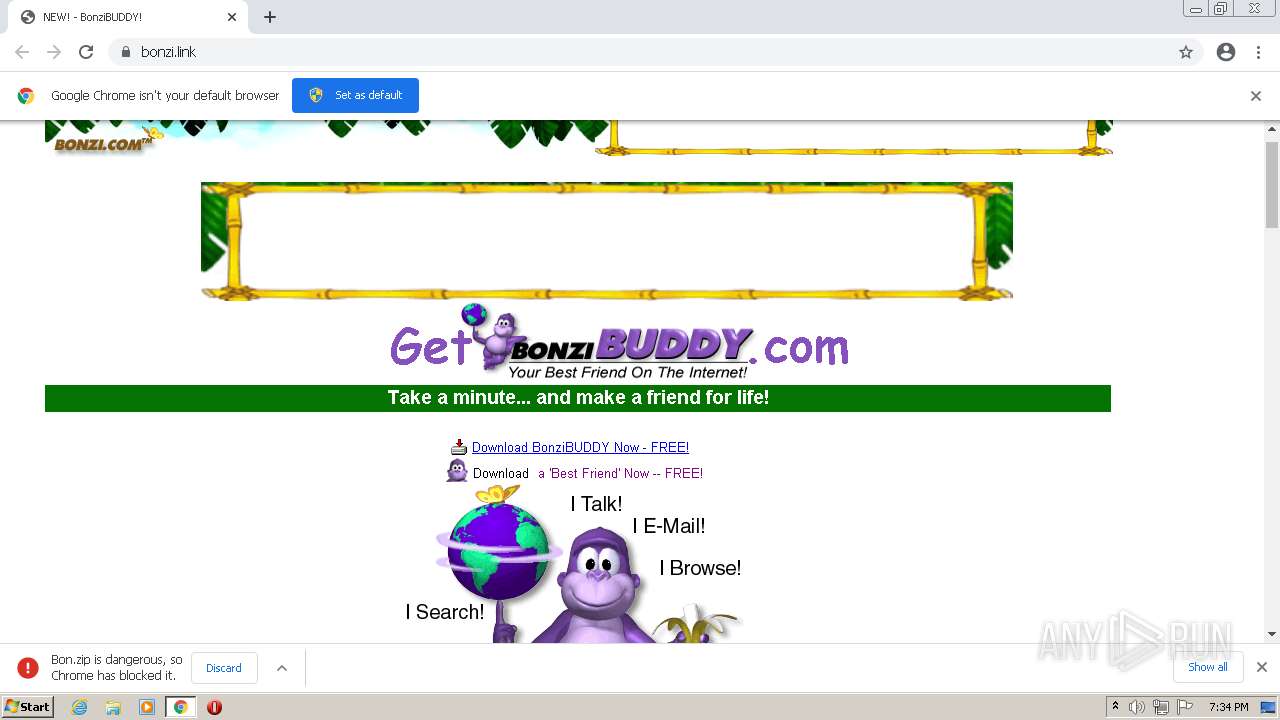
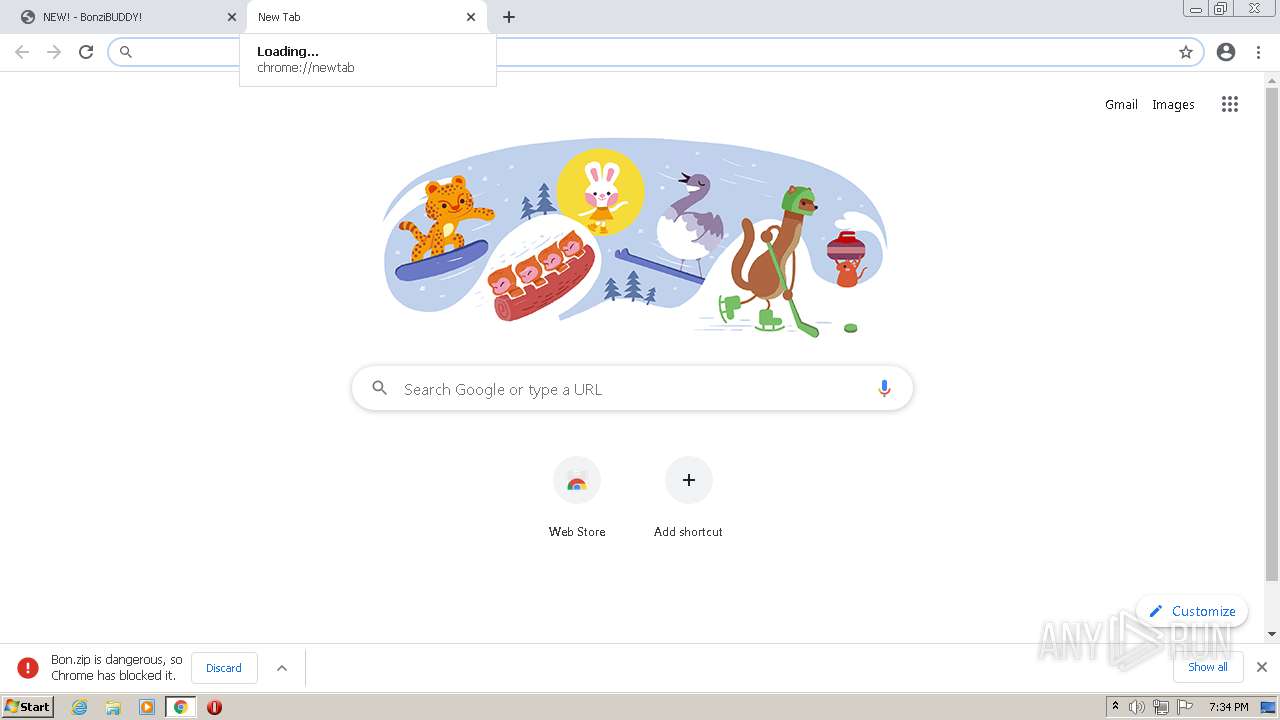
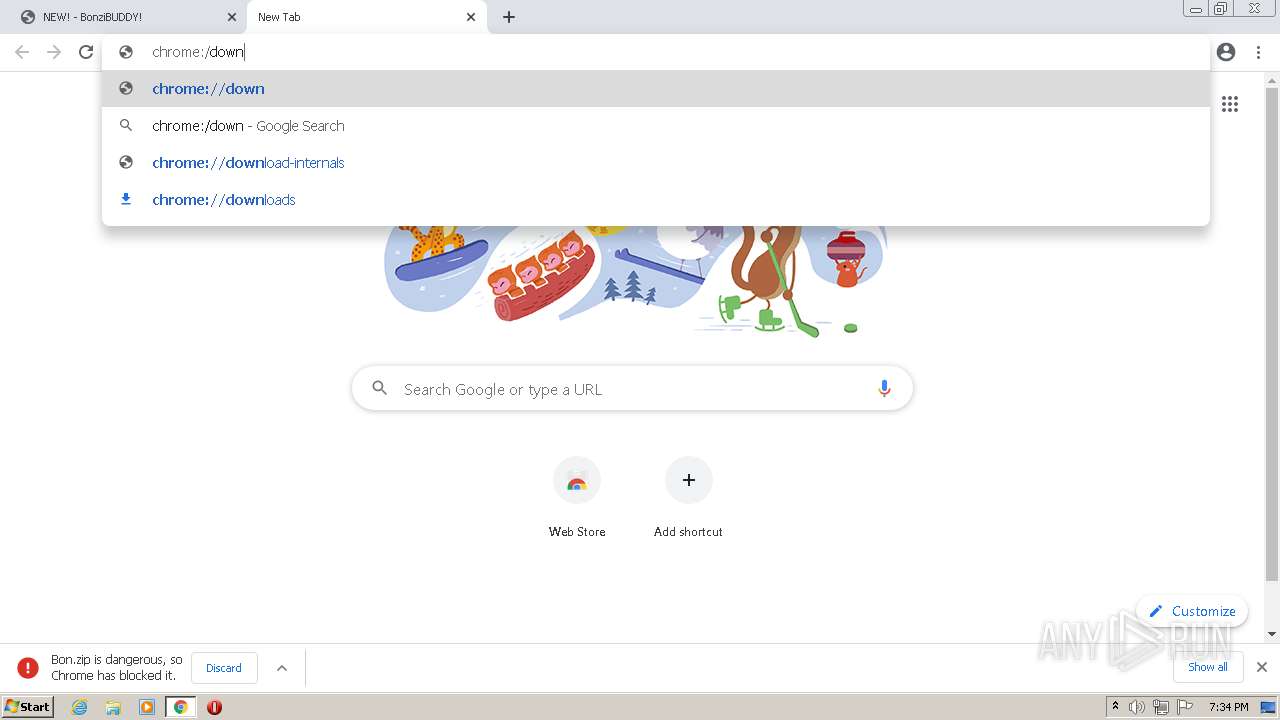
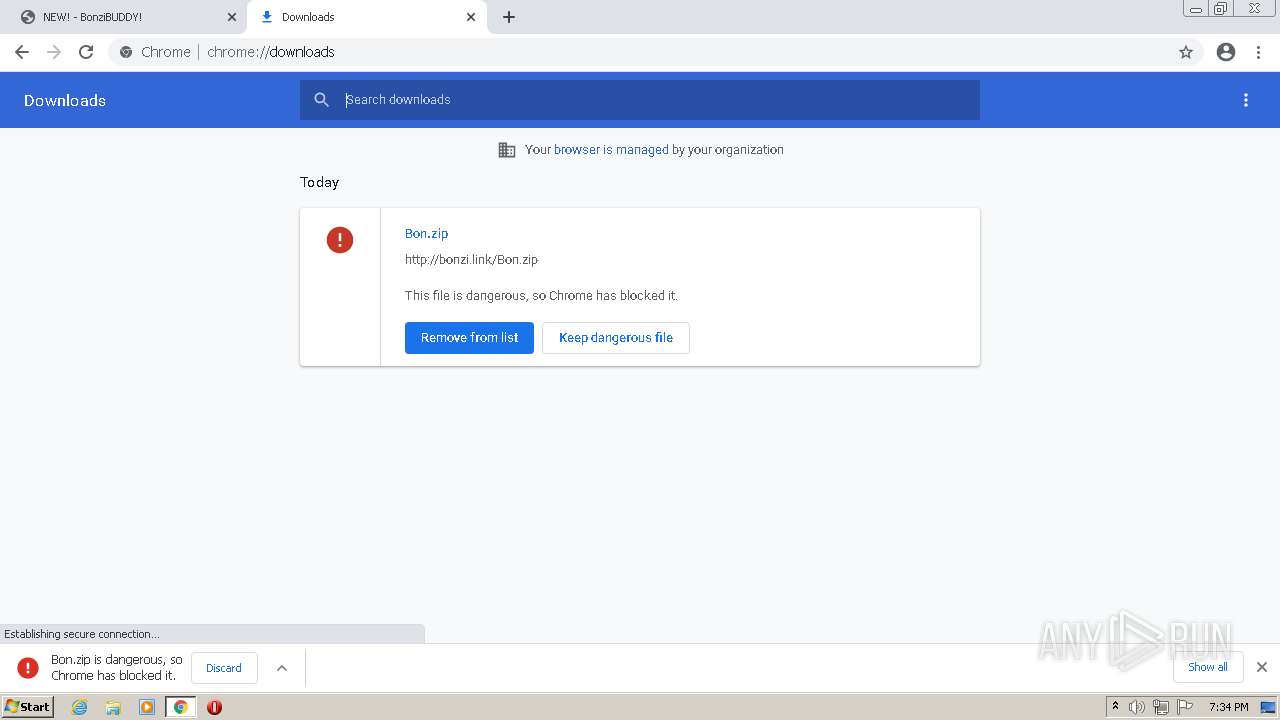
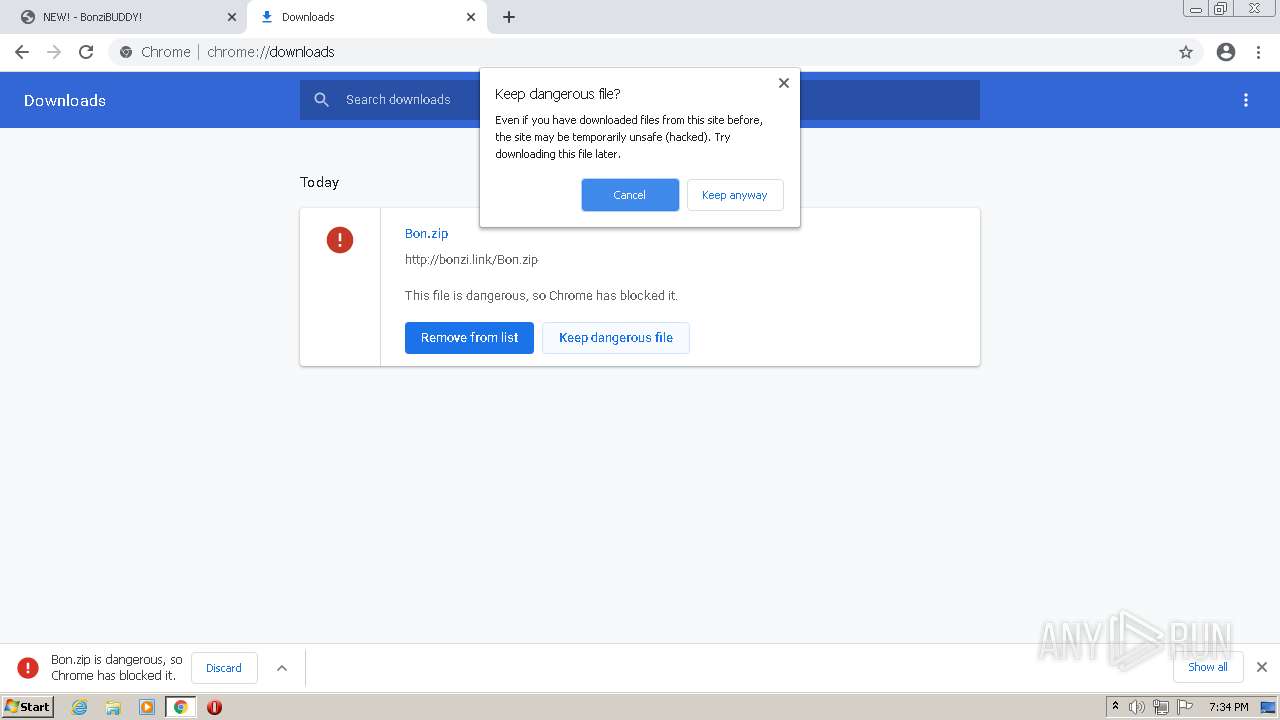
| URL: | https://bonzi.link |
| Full analysis: | https://app.any.run/tasks/508dff9a-03ab-443b-a05d-54a5e3550dc6 |
| Verdict: | Malicious activity |
| Analysis date: | February 04, 2022, 19:33:19 |
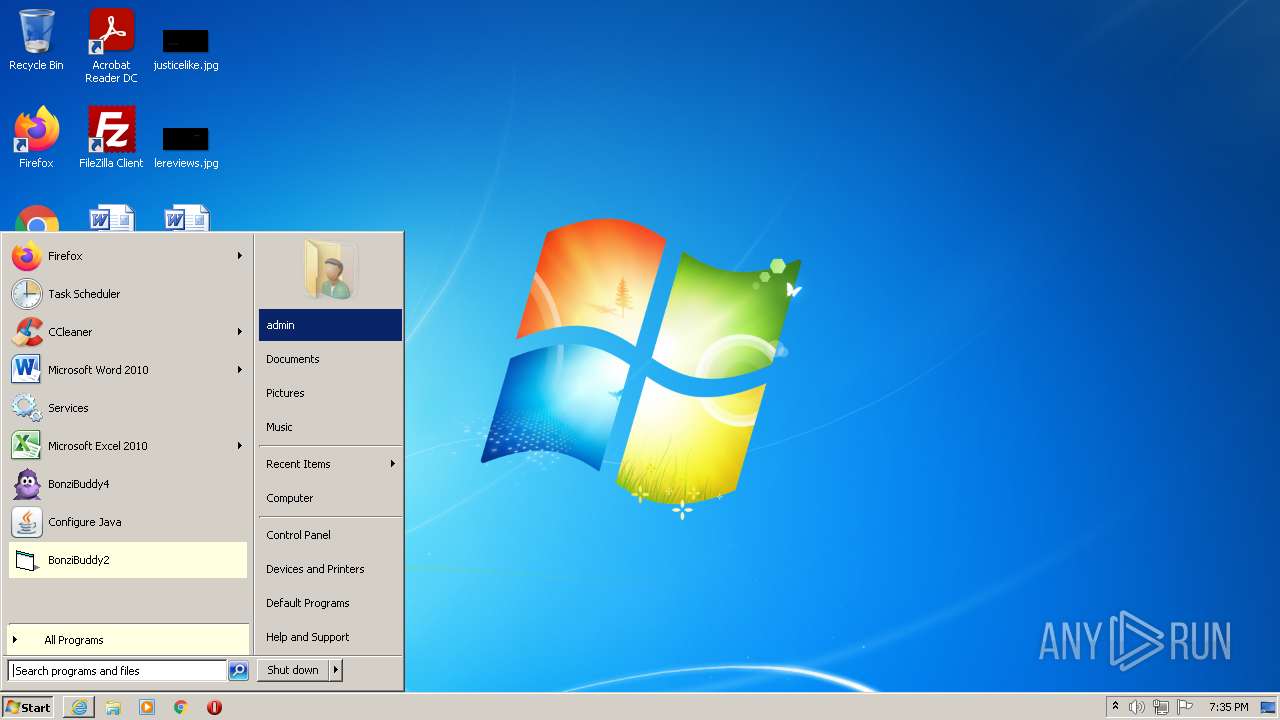
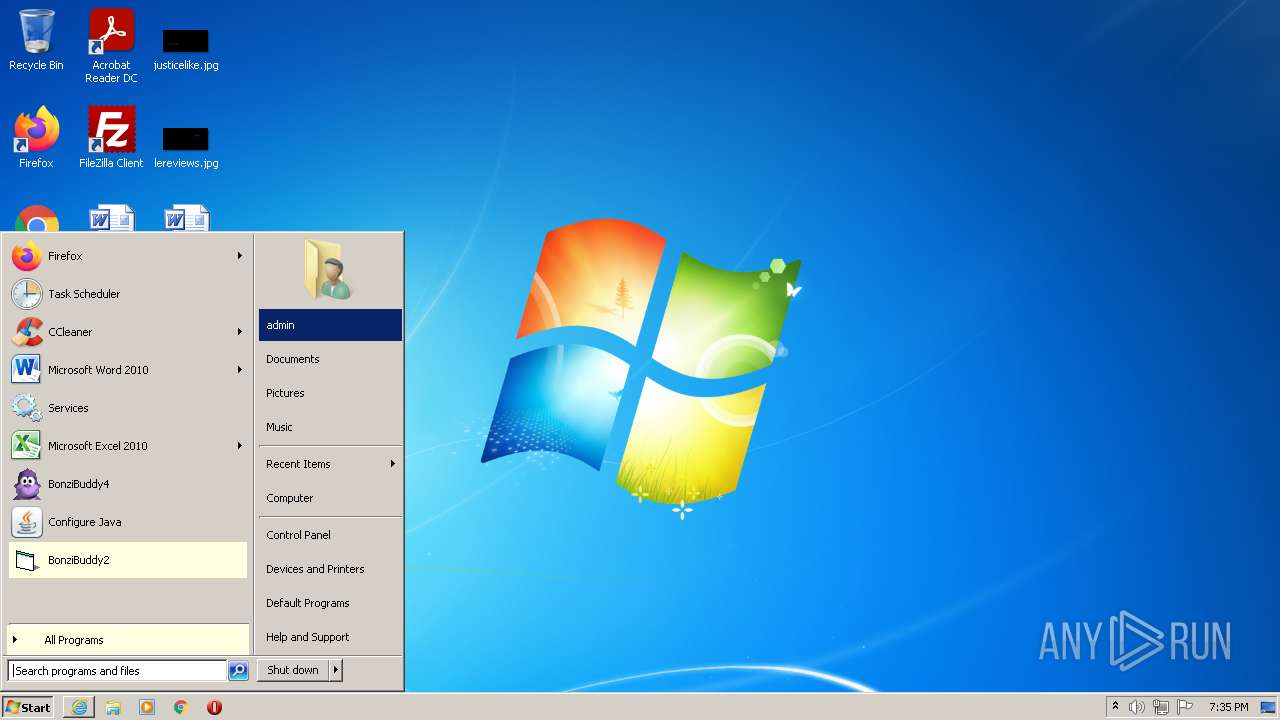
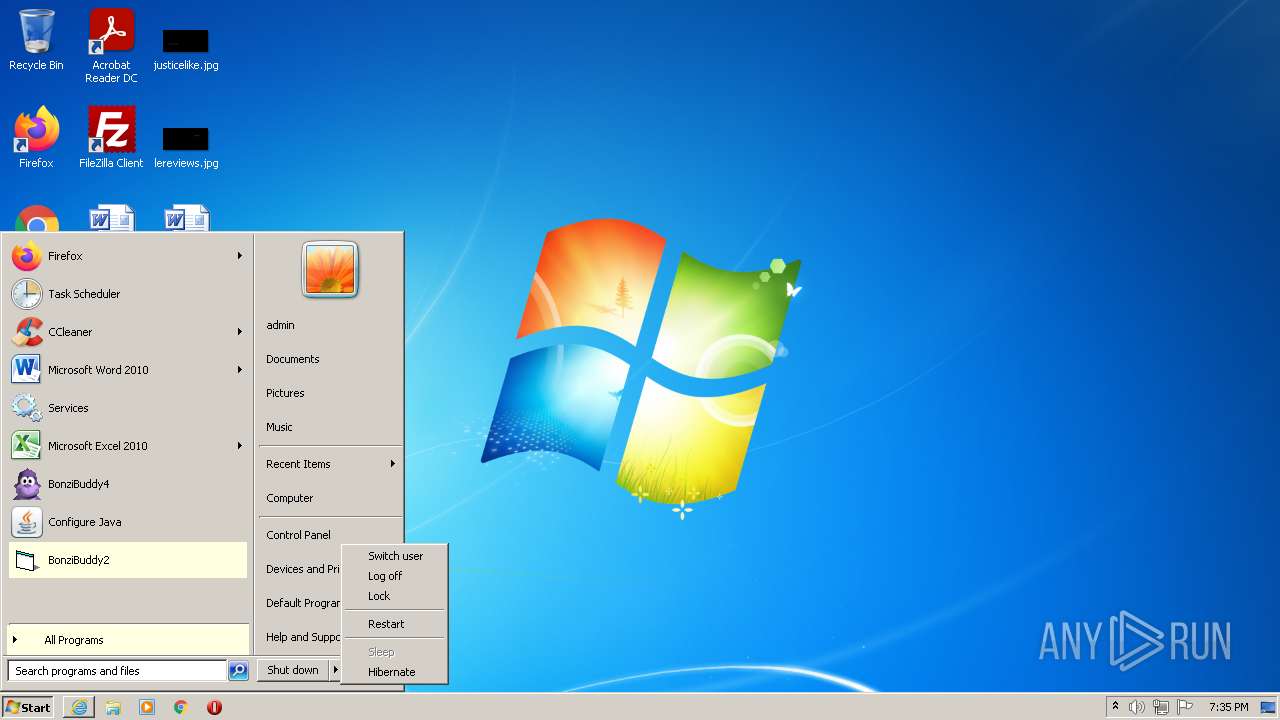
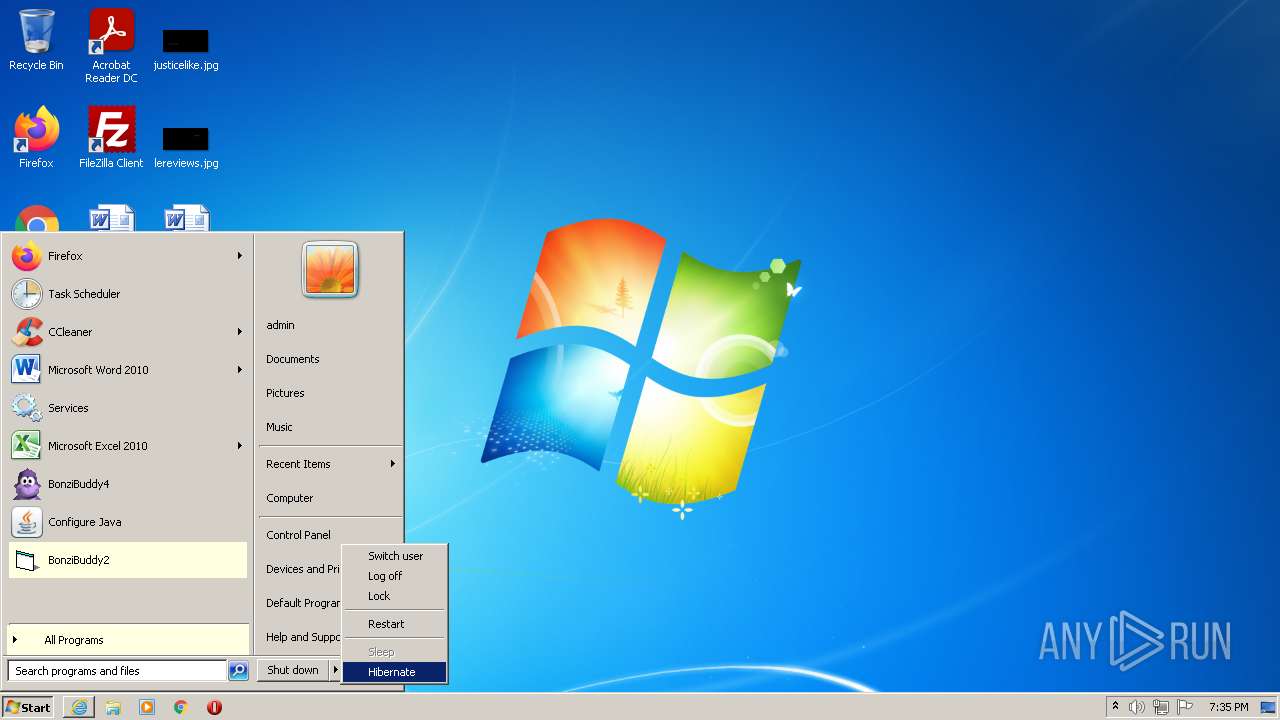
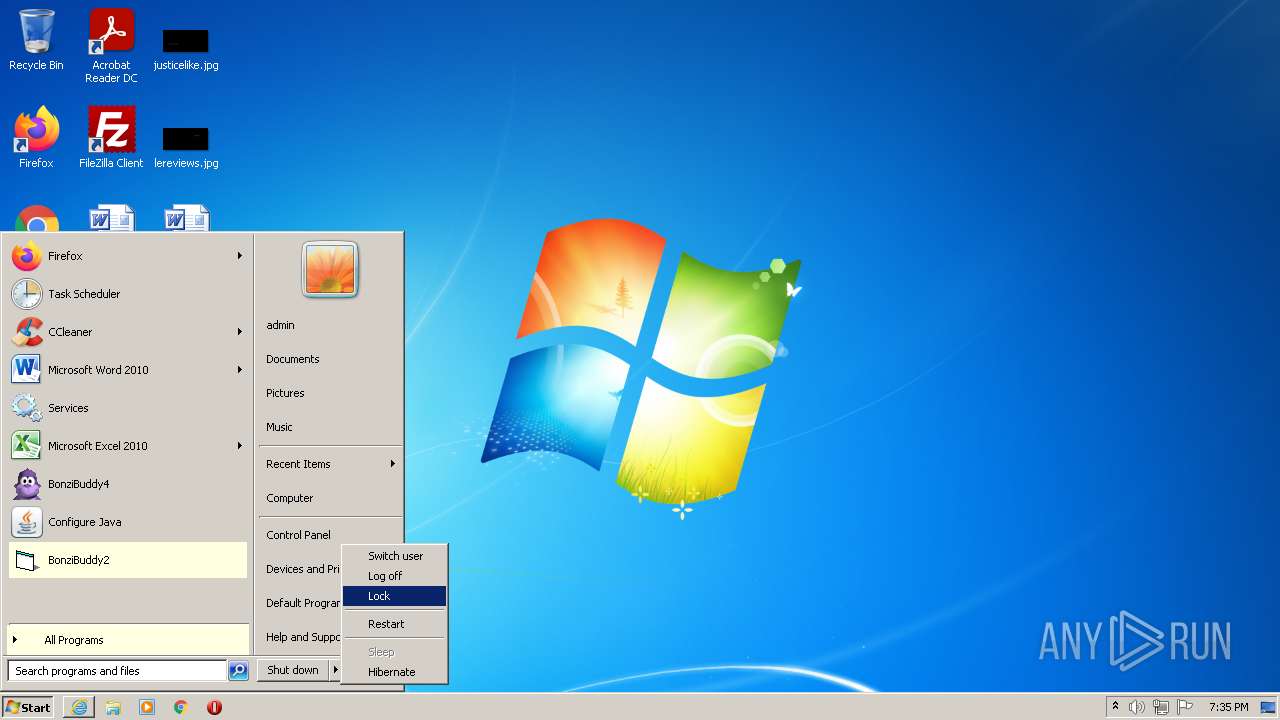
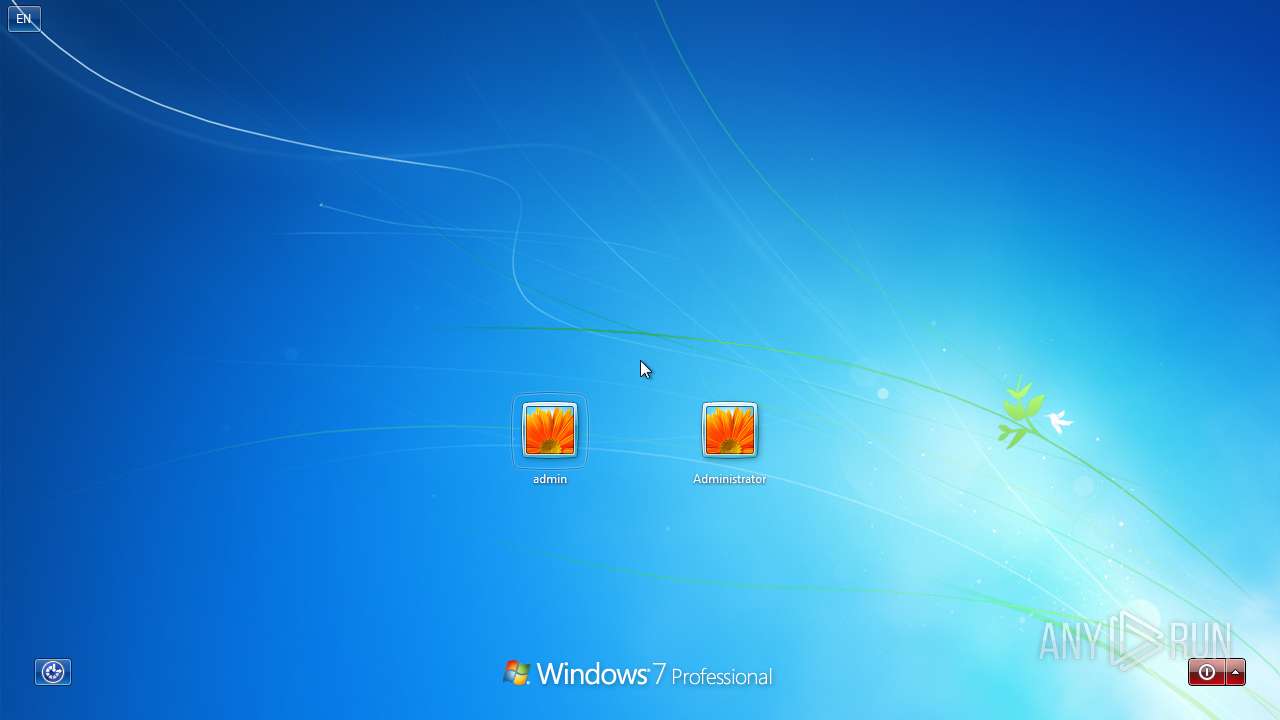
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4CDA4F278683F4F1DCD4069994C83FED |
| SHA1: | D2C5036C2F349D54A02A5E2BE51C77353914D9E0 |
| SHA256: | 13E504A9B415D995F6F6D270E14F010D204965050CA10C6E63813F520B89FB19 |
| SSDEEP: | 3:N89n:29n |
MALICIOUS
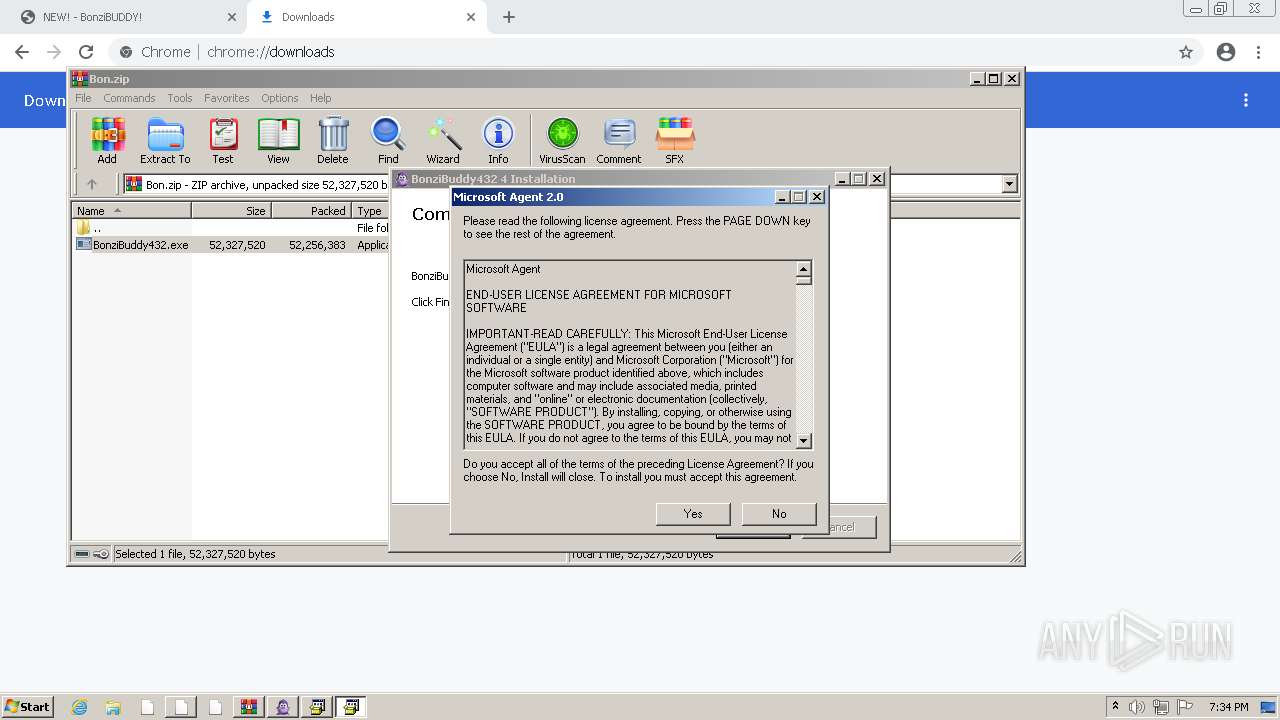
Application was dropped or rewritten from another process
- MSAGENT.EXE (PID: 1808)
- tv_enua.exe (PID: 3604)
- BonziBDY_4.EXE (PID: 2096)
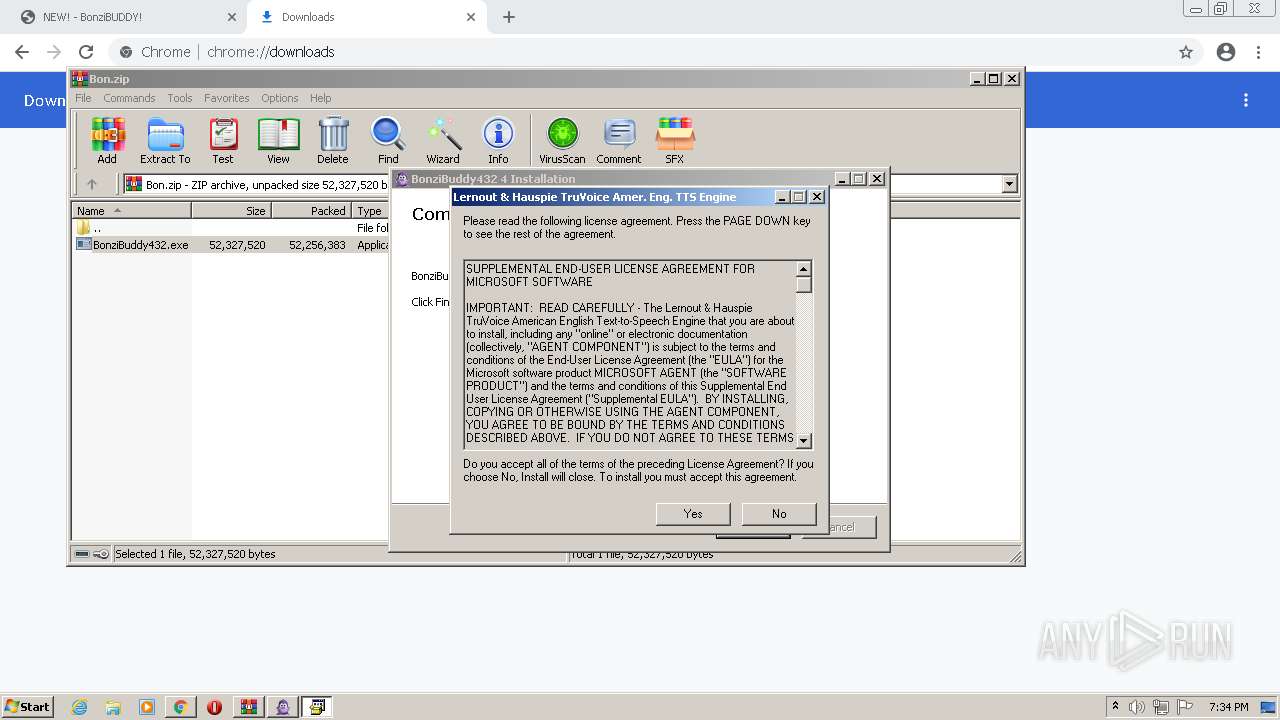
Registers / Runs the DLL via REGSVR32.EXE
- tv_enua.exe (PID: 3604)
Changes the autorun value in the registry
- tv_enua.exe (PID: 3604)
Loads dropped or rewritten executable
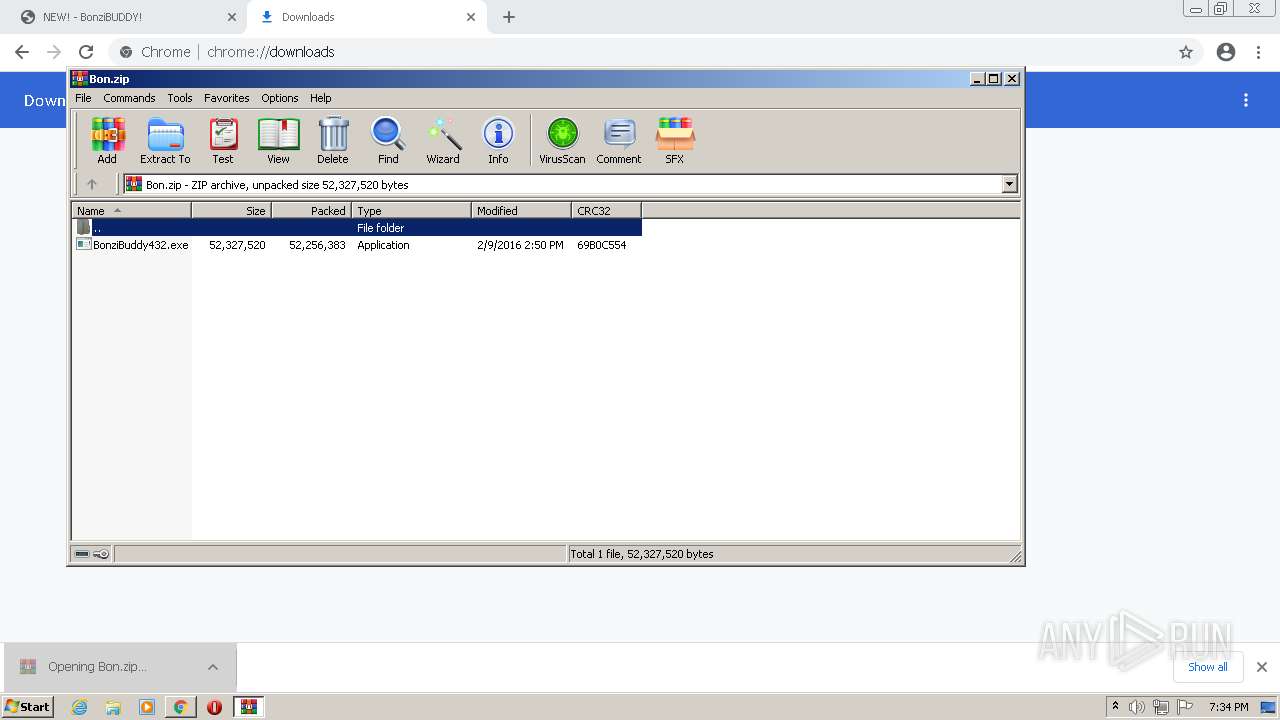
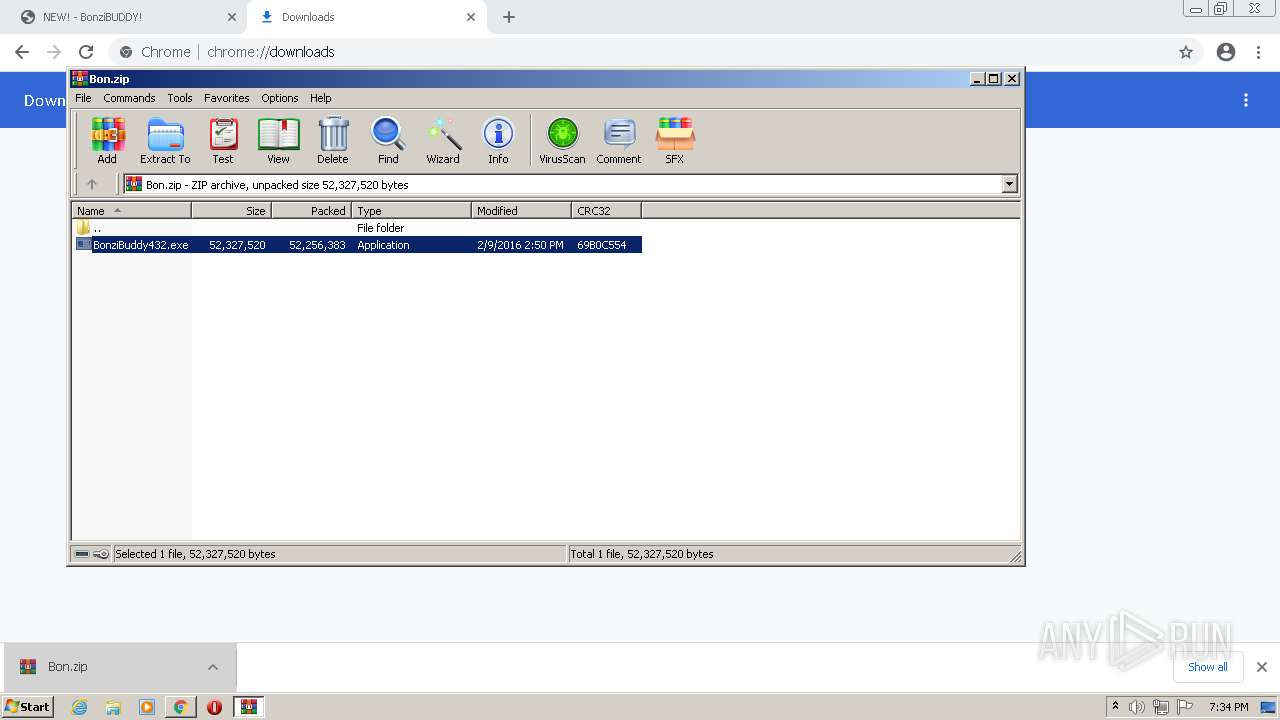
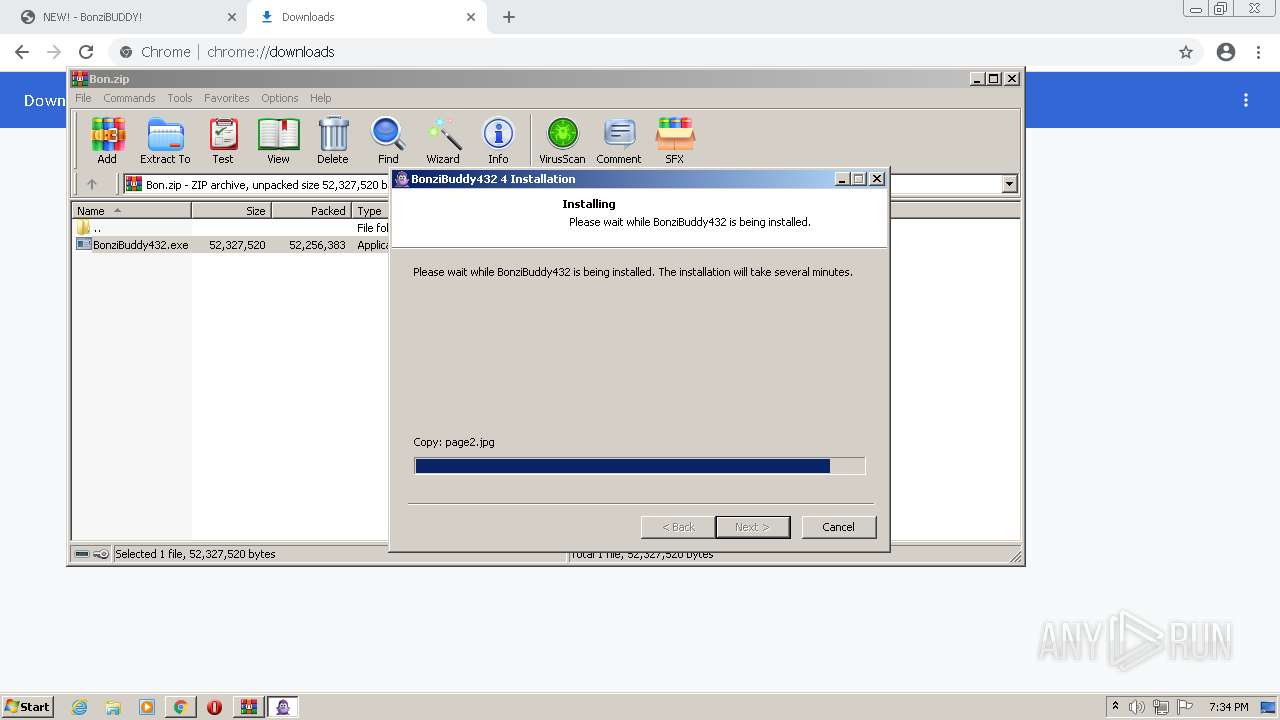
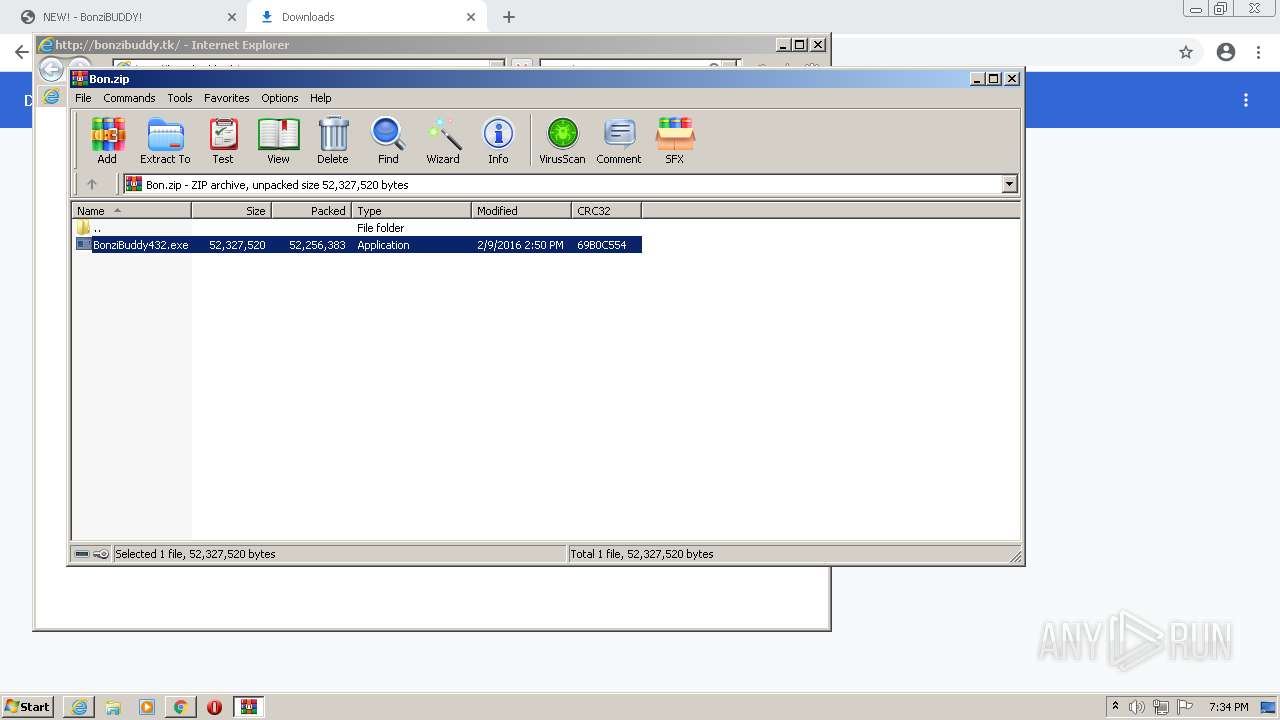
- BonziBuddy432.exe (PID: 2924)
- regsvr32.exe (PID: 2652)
- tv_enua.exe (PID: 3604)
- regsvr32.exe (PID: 660)
- BonziBDY_4.EXE (PID: 2096)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 1504)
- BonziBuddy432.exe (PID: 2924)
- MSAGENT.EXE (PID: 1808)
- cmd.exe (PID: 3172)
- tv_enua.exe (PID: 3604)
- BonziBDY_4.EXE (PID: 2096)
Reads the computer name
- WinRAR.exe (PID: 1504)
- BonziBuddy432.exe (PID: 2924)
- tv_enua.exe (PID: 3604)
Executable content was dropped or overwritten
- BonziBuddy432.exe (PID: 2924)
- tv_enua.exe (PID: 3604)
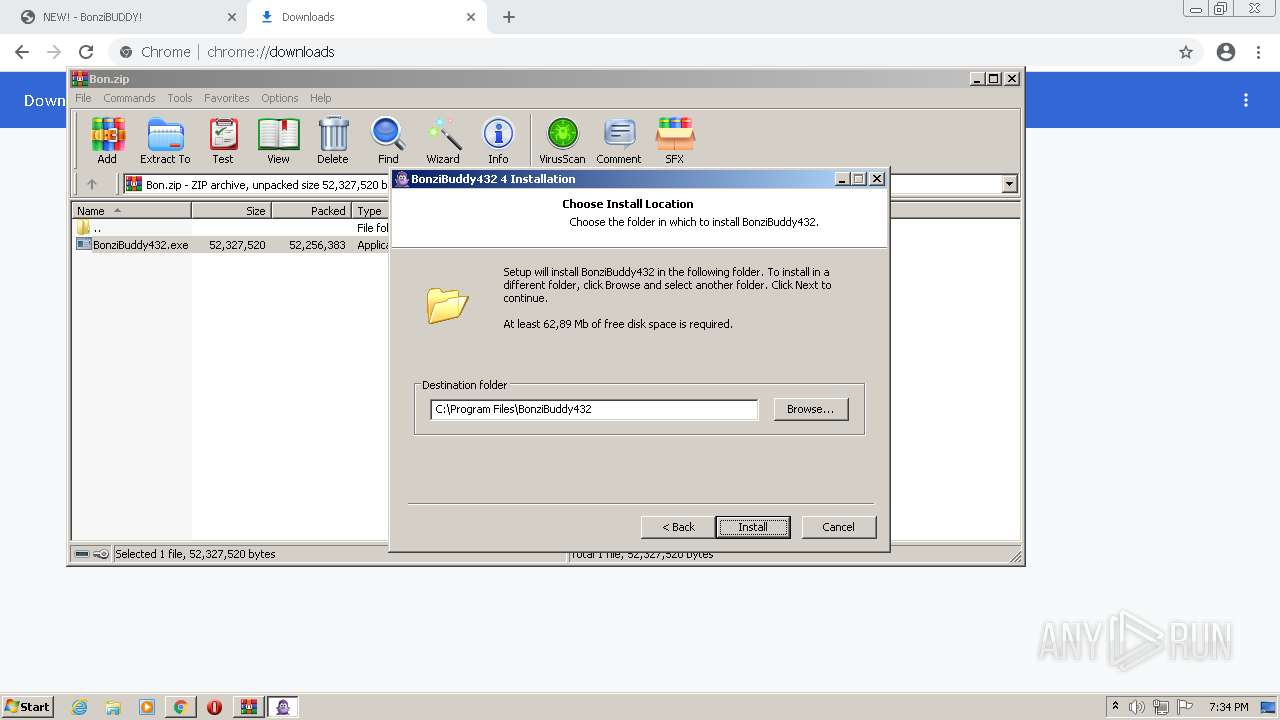
Creates a directory in Program Files
- BonziBuddy432.exe (PID: 2924)
Drops a file with too old compile date
- BonziBuddy432.exe (PID: 2924)
- tv_enua.exe (PID: 3604)
Drops a file that was compiled in debug mode
- BonziBuddy432.exe (PID: 2924)
- tv_enua.exe (PID: 3604)
Creates a software uninstall entry
- BonziBuddy432.exe (PID: 2924)
- tv_enua.exe (PID: 3604)
Creates files in the Windows directory
- BonziBuddy432.exe (PID: 2924)
- tv_enua.exe (PID: 3604)
Creates files in the user directory
- BonziBuddy432.exe (PID: 2924)
Drops a file with a compile date too recent
- tv_enua.exe (PID: 3604)
Removes files from Windows directory
- tv_enua.exe (PID: 3604)
Reads mouse settings
- BonziBuddy432.exe (PID: 2924)
Starts CMD.EXE for commands execution
- BonziBuddy432.exe (PID: 2924)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 660)
- regsvr32.exe (PID: 2652)
Starts Internet Explorer
- BonziBuddy432.exe (PID: 2924)
Creates files in the program directory
- BonziBuddy432.exe (PID: 2924)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2604)
INFO
Checks supported languages
- chrome.exe (PID: 3336)
- chrome.exe (PID: 2748)
- chrome.exe (PID: 1192)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 120)
- chrome.exe (PID: 1032)
- chrome.exe (PID: 2072)
- chrome.exe (PID: 2496)
- chrome.exe (PID: 1292)
- chrome.exe (PID: 1268)
- chrome.exe (PID: 400)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 384)
- chrome.exe (PID: 4044)
- chrome.exe (PID: 836)
- chrome.exe (PID: 660)
- chrome.exe (PID: 1100)
- chrome.exe (PID: 1380)
- chrome.exe (PID: 3400)
- chrome.exe (PID: 3200)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 3868)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3504)
- regsvr32.exe (PID: 660)
- regsvr32.exe (PID: 2652)
- grpconv.exe (PID: 1548)
- iexplore.exe (PID: 440)
- iexplore.exe (PID: 2604)
- chrome.exe (PID: 3108)
Reads the hosts file
- chrome.exe (PID: 3336)
- chrome.exe (PID: 1192)
Reads the computer name
- chrome.exe (PID: 1268)
- chrome.exe (PID: 3384)
- chrome.exe (PID: 1292)
- chrome.exe (PID: 3336)
- chrome.exe (PID: 1192)
- chrome.exe (PID: 400)
- chrome.exe (PID: 836)
- chrome.exe (PID: 2560)
- chrome.exe (PID: 3504)
- iexplore.exe (PID: 440)
- iexplore.exe (PID: 2604)
- chrome.exe (PID: 3108)
Application launched itself
- chrome.exe (PID: 3336)
- iexplore.exe (PID: 440)
Reads settings of System Certificates
- chrome.exe (PID: 1192)
- iexplore.exe (PID: 2604)
- iexplore.exe (PID: 440)
Reads the date of Windows installation
- chrome.exe (PID: 836)
Reads internet explorer settings
- iexplore.exe (PID: 2604)
Changes internet zones settings
- iexplore.exe (PID: 440)
Checks Windows Trust Settings
- iexplore.exe (PID: 2604)
- iexplore.exe (PID: 440)
Changes settings of System certificates
- iexplore.exe (PID: 2604)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2604)
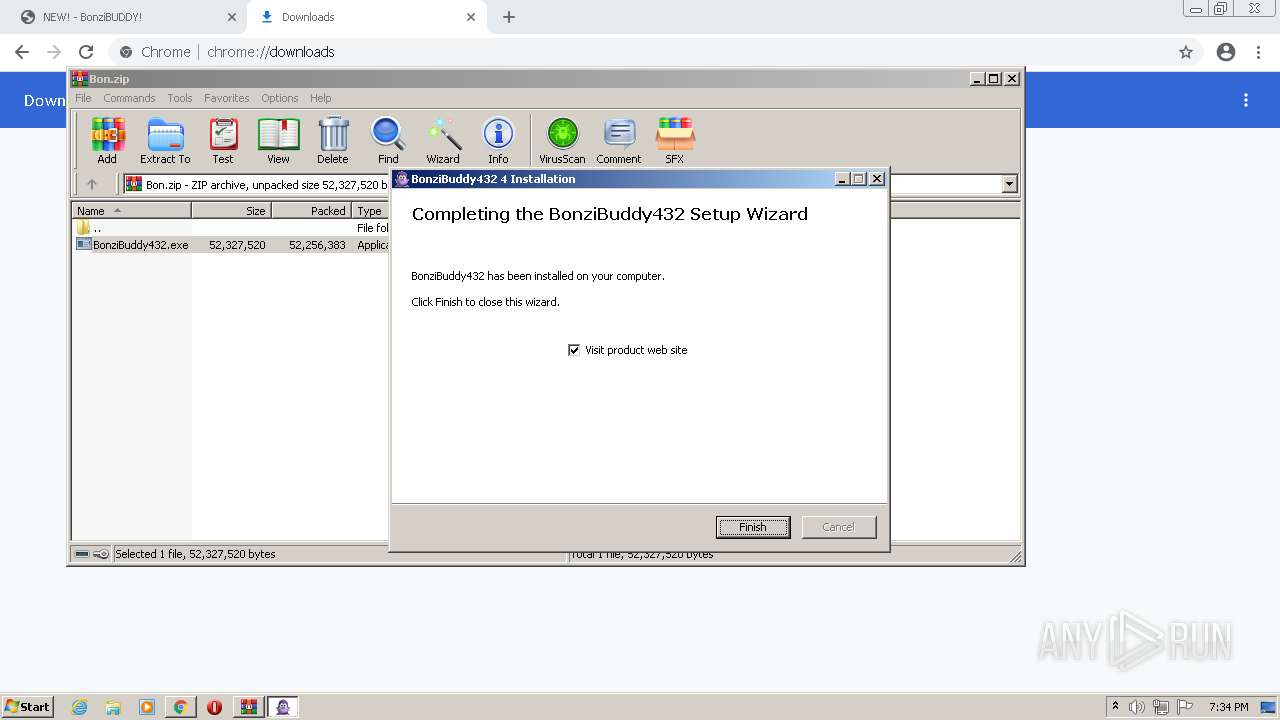
Manual execution by user
- BonziBDY_4.EXE (PID: 2096)
Creates files in the user directory
- iexplore.exe (PID: 2604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
40
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4306269051922255115,14264345994921082308,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,4306269051922255115,14264345994921082308,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3156 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,4306269051922255115,14264345994921082308,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=584 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
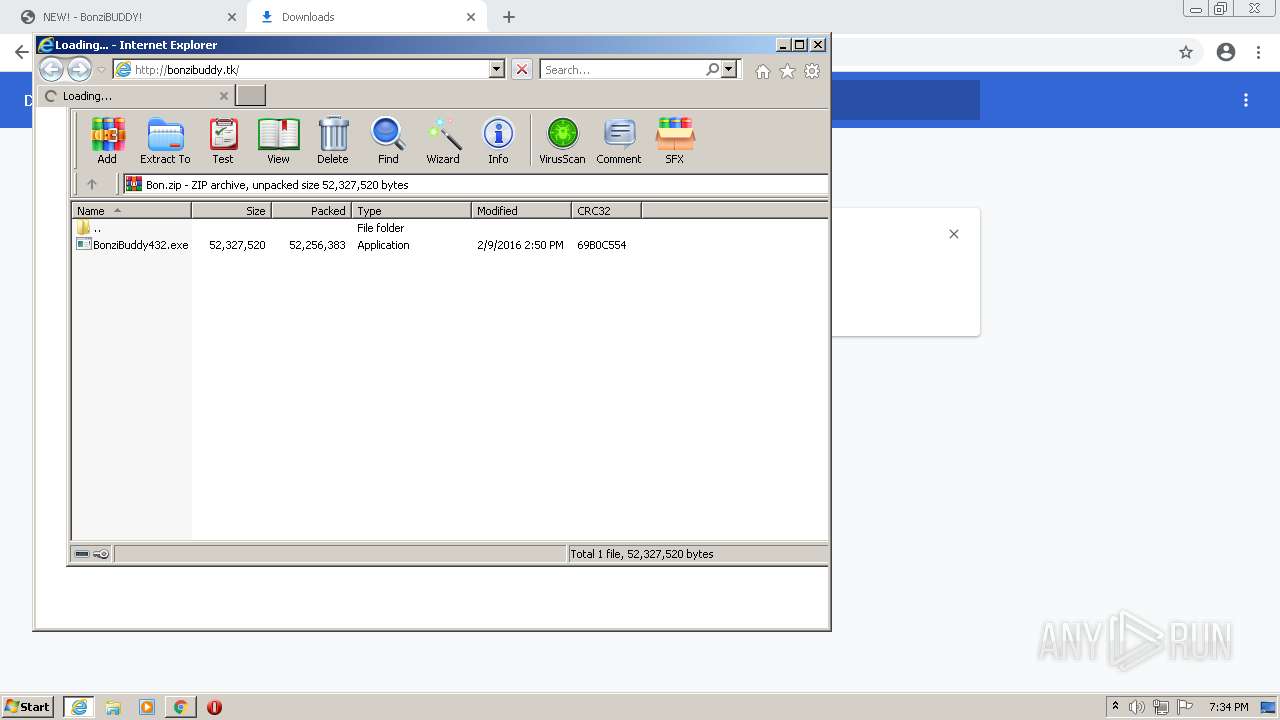
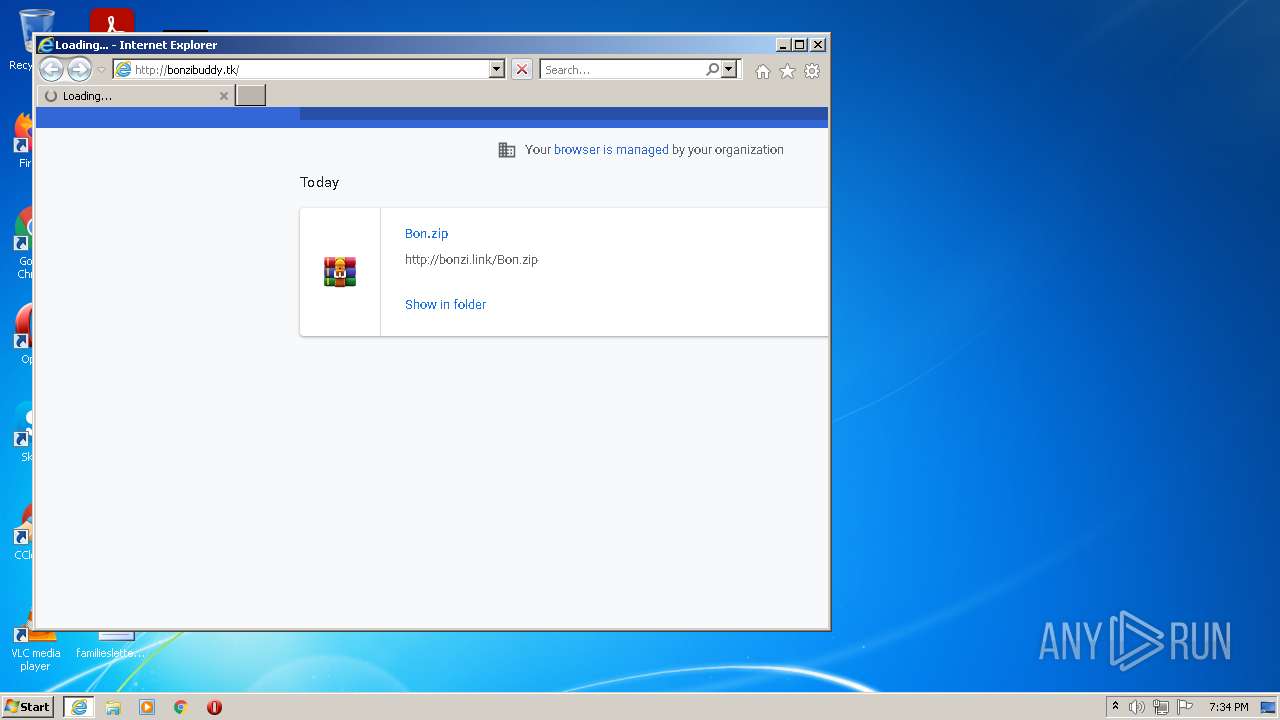
| 440 | "C:\Program Files\Internet Explorer\iexplore.exe" http://bonzibuddy.tk/ | C:\Program Files\Internet Explorer\iexplore.exe | BonziBuddy432.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
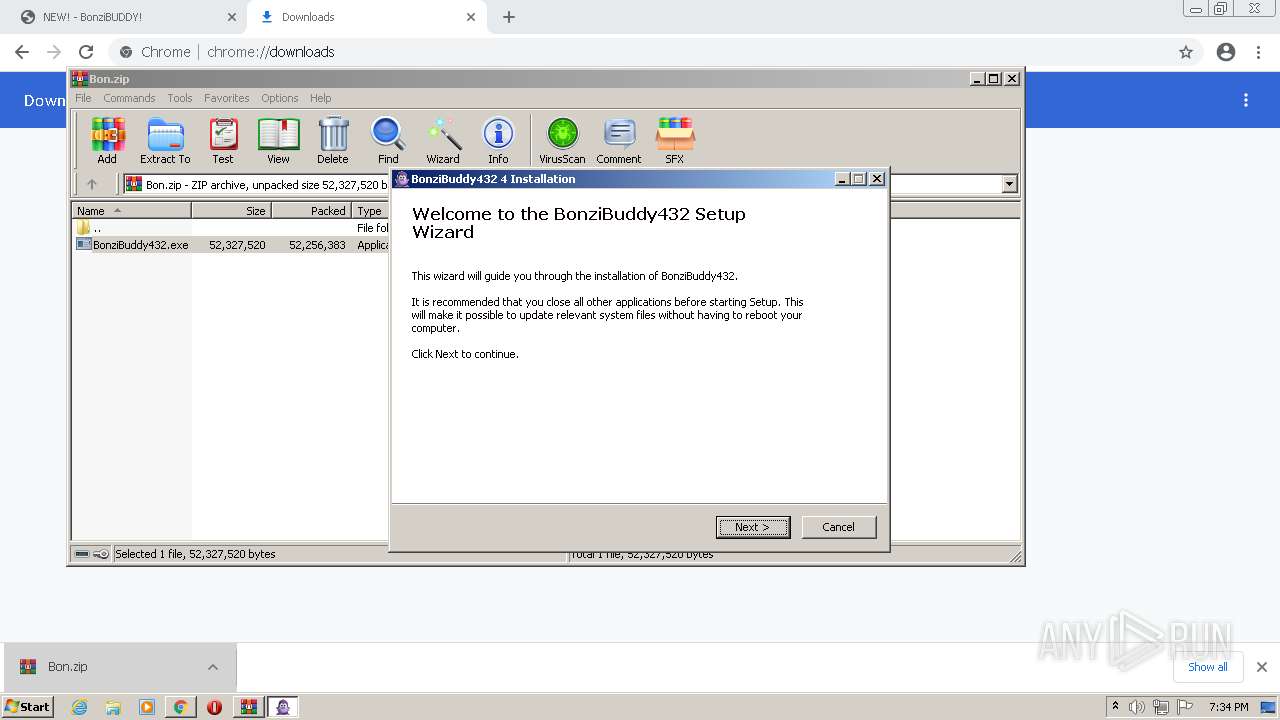
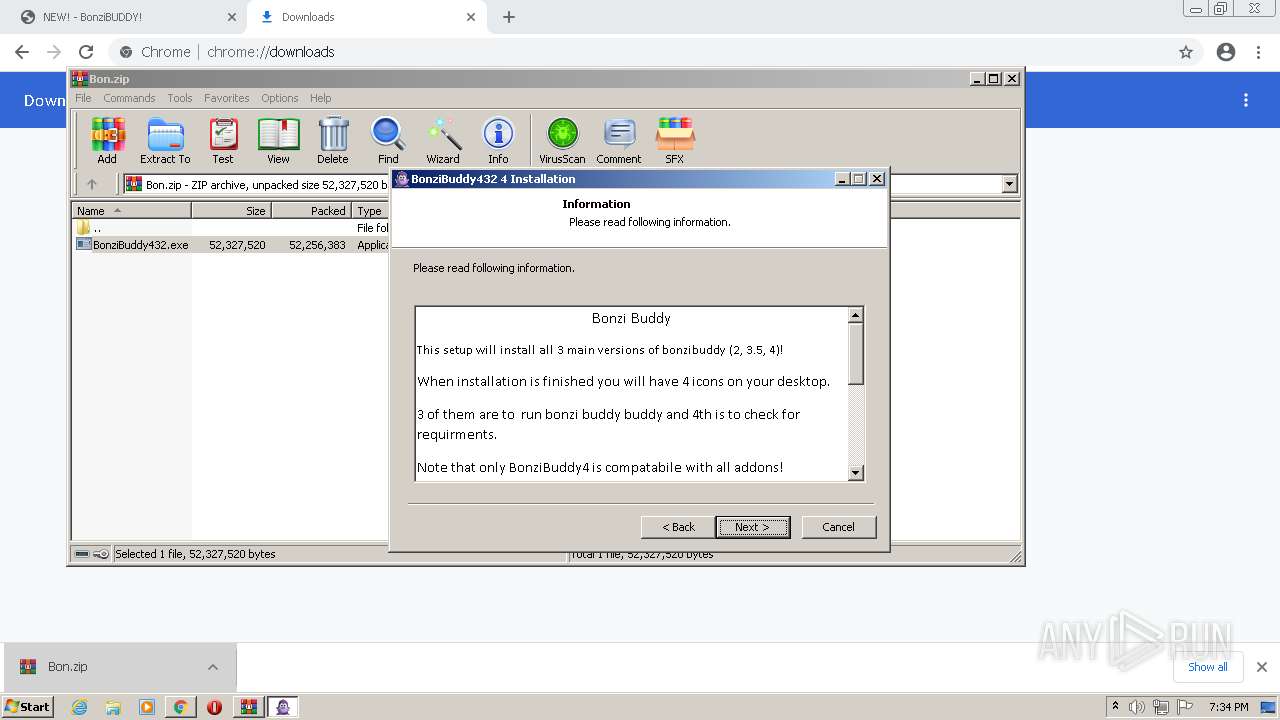
| 556 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1504.41841\BonziBuddy432.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1504.41841\BonziBuddy432.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Bonzi Software Integrity Level: MEDIUM Description: BonziBuddy432 4 Installation Exit code: 3221226540 Version: 4 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,4306269051922255115,14264345994921082308,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3188 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 660 | regsvr32 /s C:\Windows\lhsp\tv\tv_enua.dll | C:\Windows\system32\regsvr32.exe | — | tv_enua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,4306269051922255115,14264345994921082308,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,4306269051922255115,14264345994921082308,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,4306269051922255115,14264345994921082308,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3120 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
37 400
Read events
35 772
Write events
1 579
Delete events
49
Modification events
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
47
Suspicious files
80
Text files
260
Unknown types
42
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61FD7F82-D08.pma | — | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b5a7afb5-c9ec-498a-b98f-7edb26210f95.tmp | text | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFe2a28.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe2a38.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3336 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1525c1d8-9f3b-4a59-8642-57b84e875b59.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
66
DNS requests
32
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2604 | iexplore.exe | GET | — | 185.199.220.34:80 | http://bonzibuddy.tk/survive.mp3 | GB | — | — | malicious |
2604 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2604 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCLHtDCfO2bBwoAAAABLgJa | US | der | 472 b | whitelisted |
2604 | iexplore.exe | GET | 200 | 185.199.220.34:80 | http://bonzibuddy.tk/ | GB | compressed | 762 b | malicious |
2604 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2604 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDKa002niAMOQoAAAABLgV0 | US | der | 472 b | whitelisted |
2604 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDgBTRQd6qpTgoAAAABLgJY | US | der | 472 b | whitelisted |
2604 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
2604 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2604 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDIRy5Lqyj5dAoAAAABLgV%2F | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1192 | chrome.exe | 216.58.212.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1192 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
1192 | chrome.exe | 142.250.186.173:443 | accounts.google.com | Google Inc. | US | suspicious |
1192 | chrome.exe | 149.56.78.29:443 | bonzi.link | OVH SAS | CA | suspicious |
1192 | chrome.exe | 172.217.18.98:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
1192 | chrome.exe | 149.56.78.29:80 | bonzi.link | OVH SAS | CA | suspicious |
1192 | chrome.exe | 142.250.186.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1192 | chrome.exe | 142.250.185.206:443 | apis.google.com | Google Inc. | US | whitelisted |
1192 | chrome.exe | 172.217.16.131:443 | update.googleapis.com | Google Inc. | US | whitelisted |
2604 | iexplore.exe | 142.250.185.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
bonzi.link |
| suspicious |
accounts.google.com |
| shared |
pagead2.googlesyndication.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
2604 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2604 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2604 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2604 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2604 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |
2604 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to a *.tk domain |