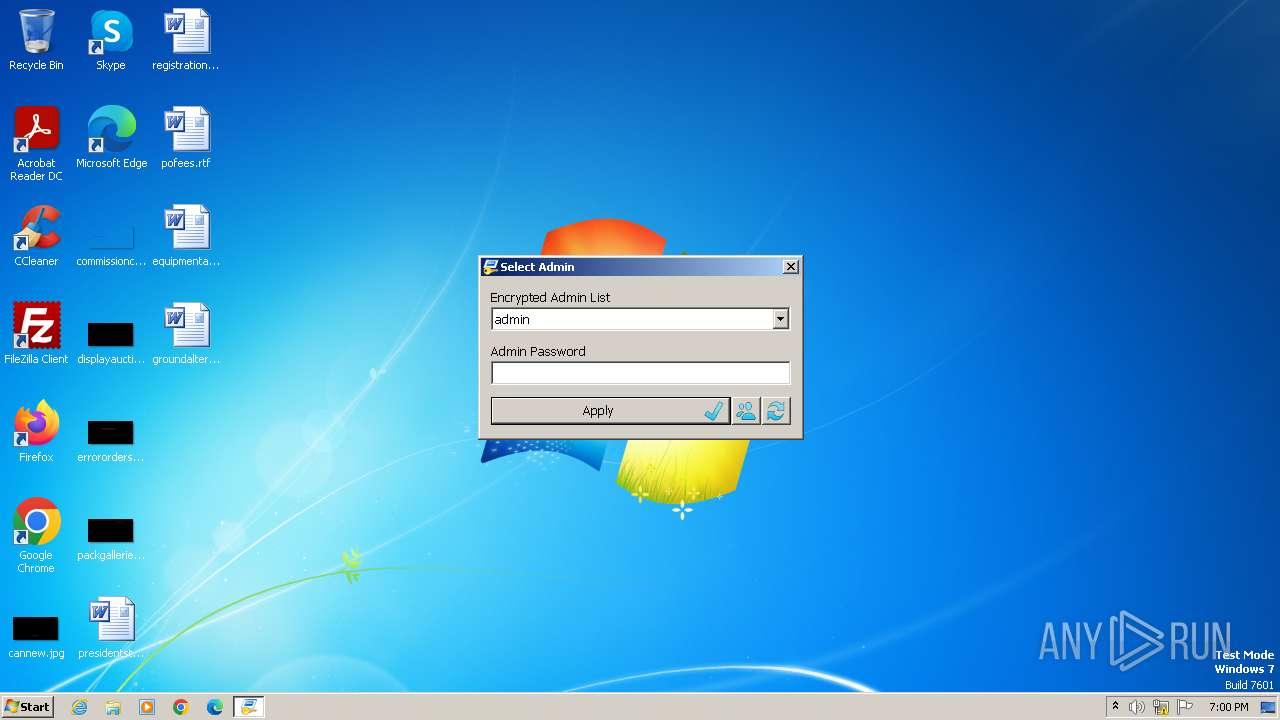
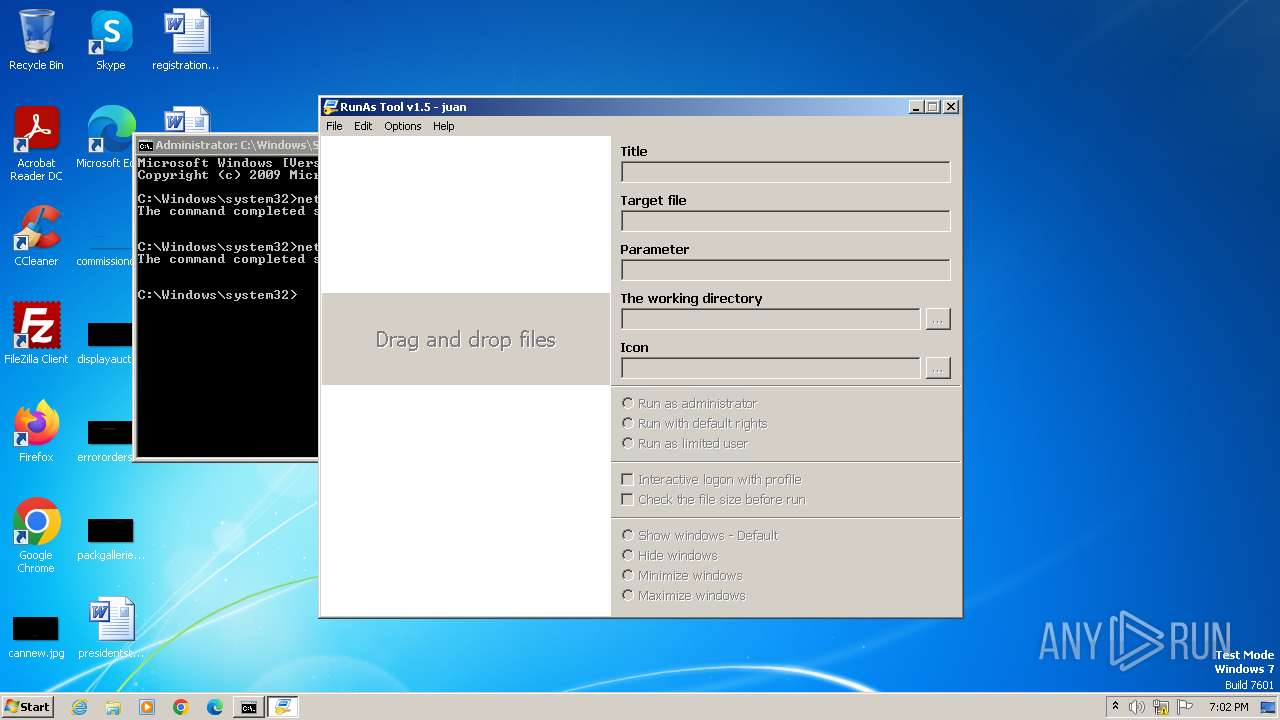
| File name: | RunAsTool.exe |
| Full analysis: | https://app.any.run/tasks/4ee5c450-e776-49a1-a7f2-7c46df5b9245 |
| Verdict: | Malicious activity |
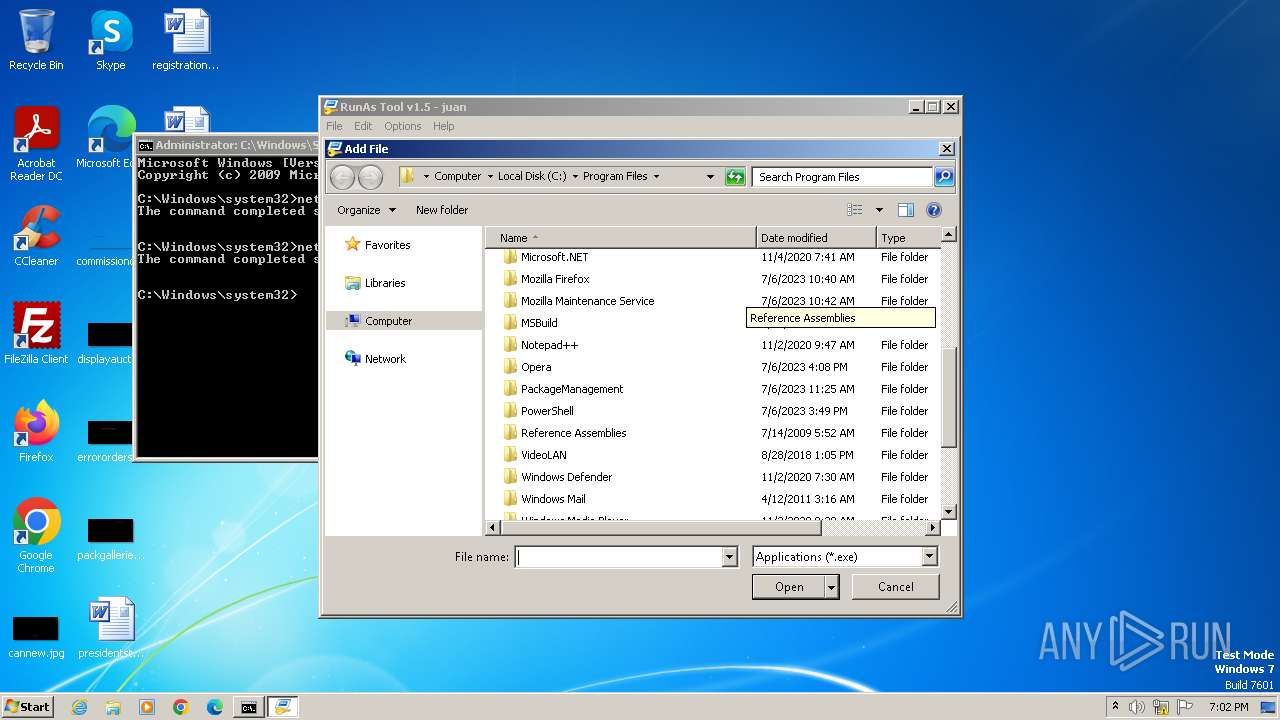
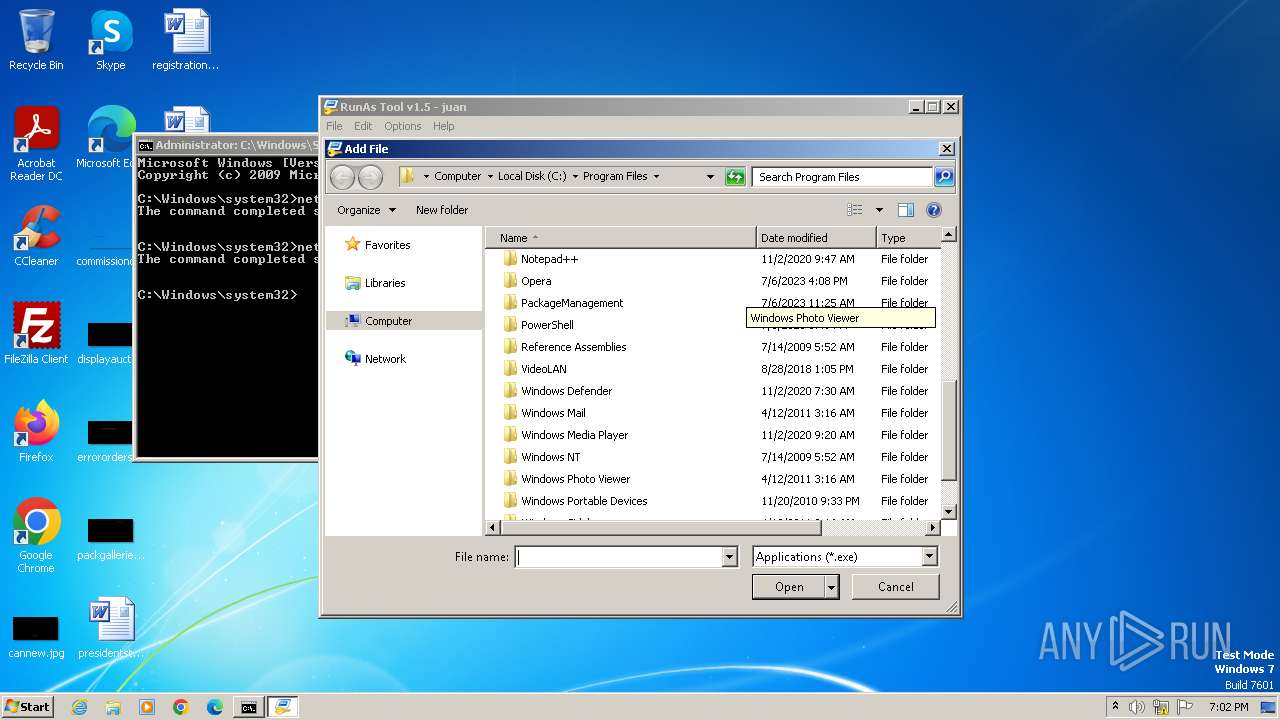
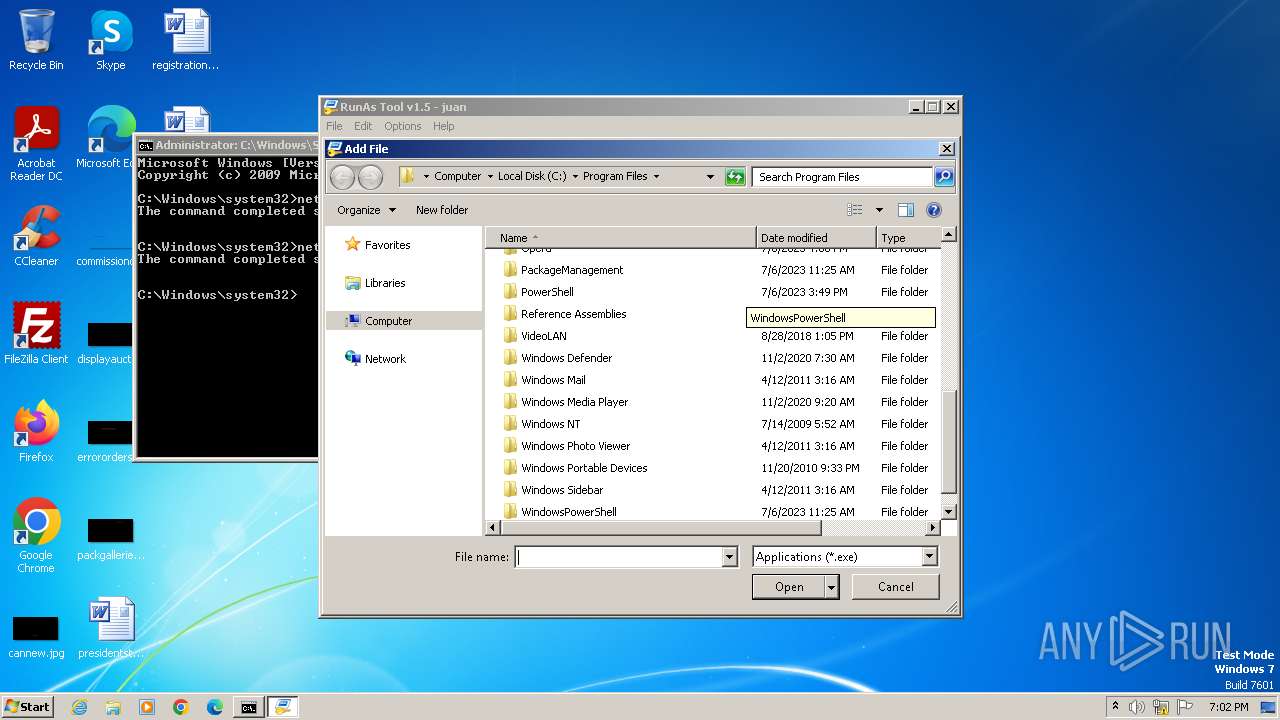
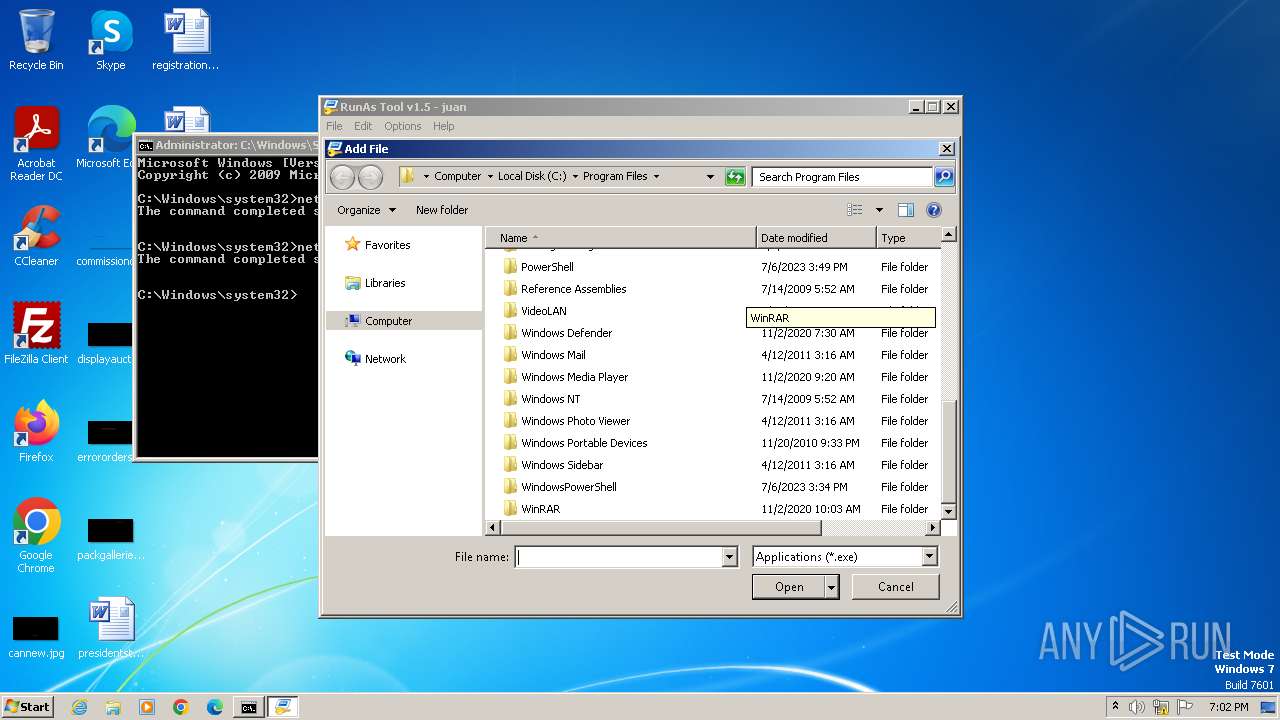
| Analysis date: | November 23, 2023, 19:00:11 |
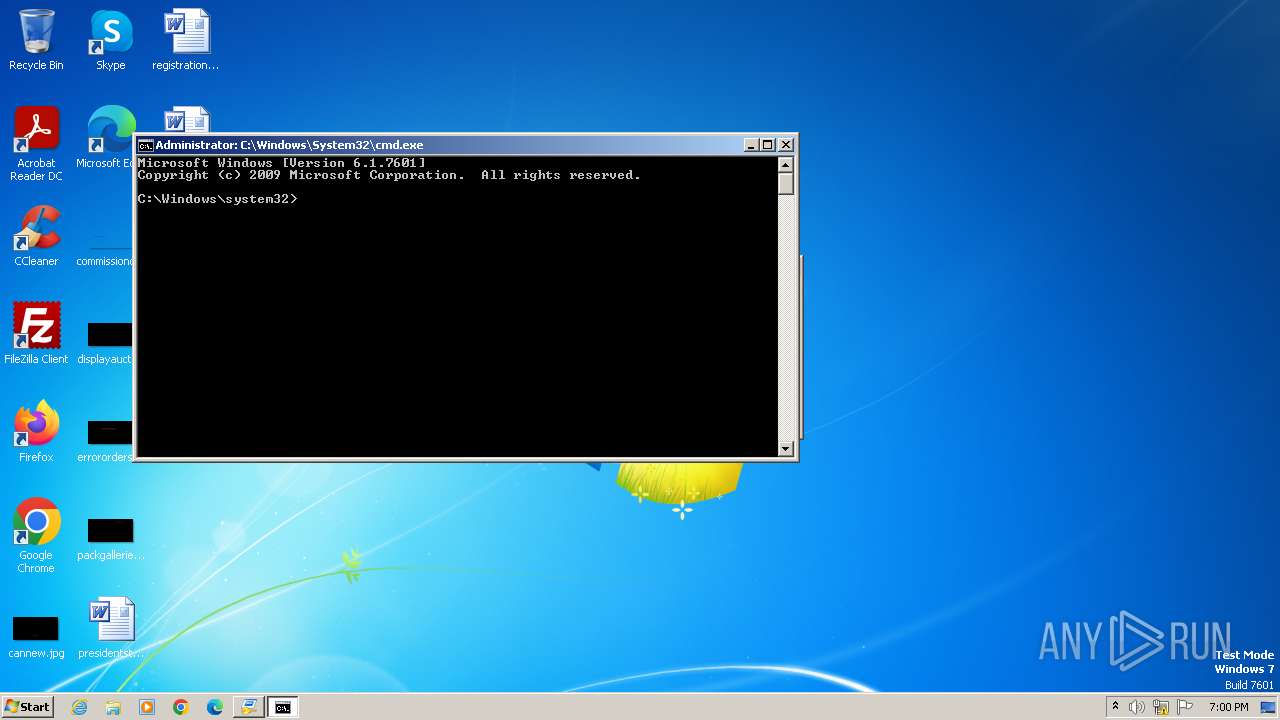
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 899198029F9ADC45094652DC9A629A99 |
| SHA1: | 60D5169C227500A56DD5555ABAF951D996D4203C |
| SHA256: | 13DE2EC4FB18CA9311443A8EB5495226311EE8FC58487973950A13C7E0CCCF40 |
| SSDEEP: | 12288:XaWzgMg7v3qnCiNErQohh0F4jCJ8lnyGQutkCoSMf3hUP9GAr:qaHMv6C1rjfnyGQAkwm32FG6 |
MALICIOUS
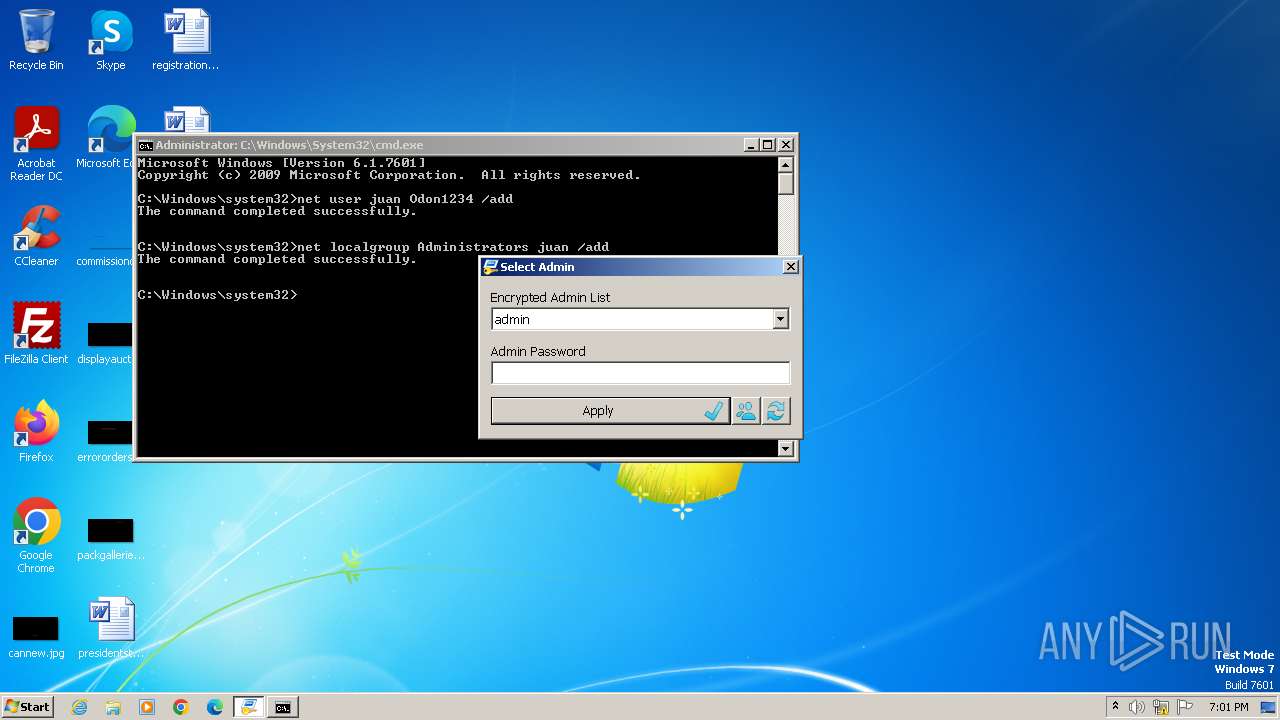
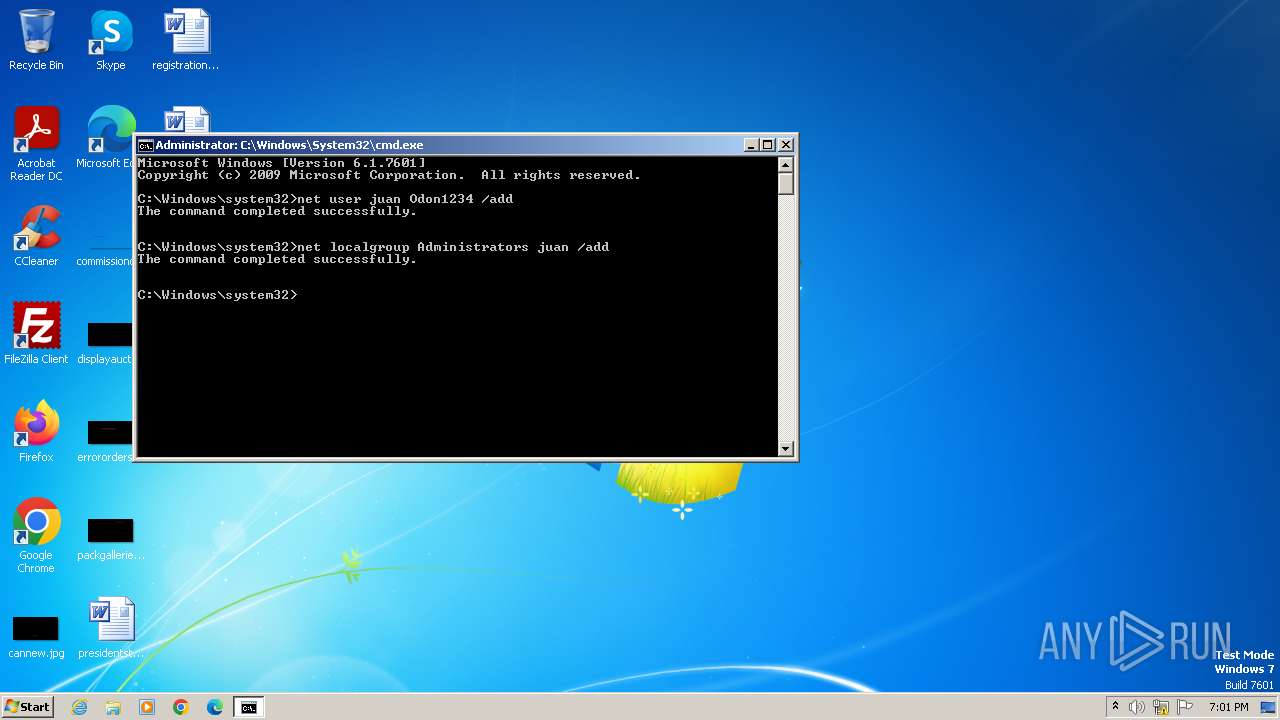
Starts NET.EXE to view/change users localgroup
- net.exe (PID: 1452)
- cmd.exe (PID: 2504)
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 2504)
- net.exe (PID: 2776)
Drops the executable file immediately after the start
- RunAsTool.exe (PID: 3108)
SUSPICIOUS
Application launched itself
- RunAsTool.exe (PID: 2876)
- RunAsTool.exe (PID: 3640)
INFO
Checks supported languages
- RunAsTool.exe (PID: 2876)
- RunAsTool.exe (PID: 3640)
- RunAsTool.exe (PID: 3108)
Reads mouse settings
- RunAsTool.exe (PID: 2876)
- RunAsTool.exe (PID: 3640)
- RunAsTool.exe (PID: 3108)
Reads the computer name
- RunAsTool.exe (PID: 2876)
- RunAsTool.exe (PID: 3640)
- RunAsTool.exe (PID: 3108)
Create files in a temporary directory
- RunAsTool.exe (PID: 2876)
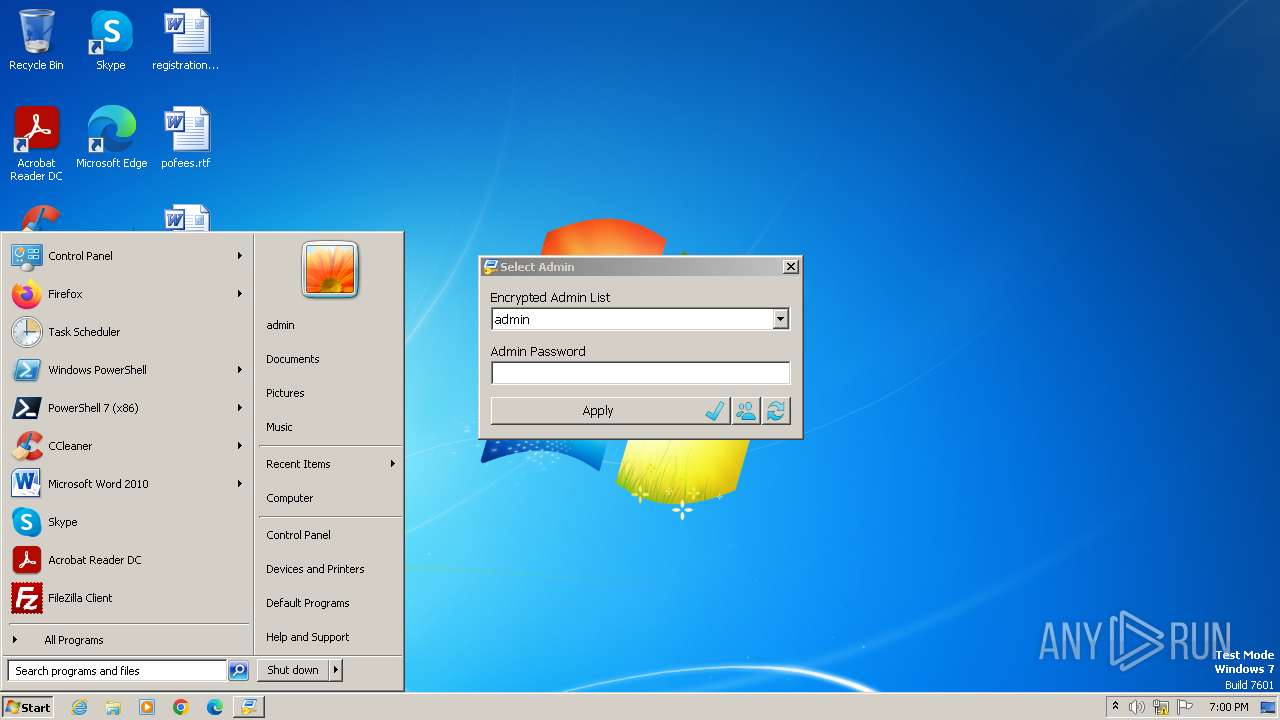
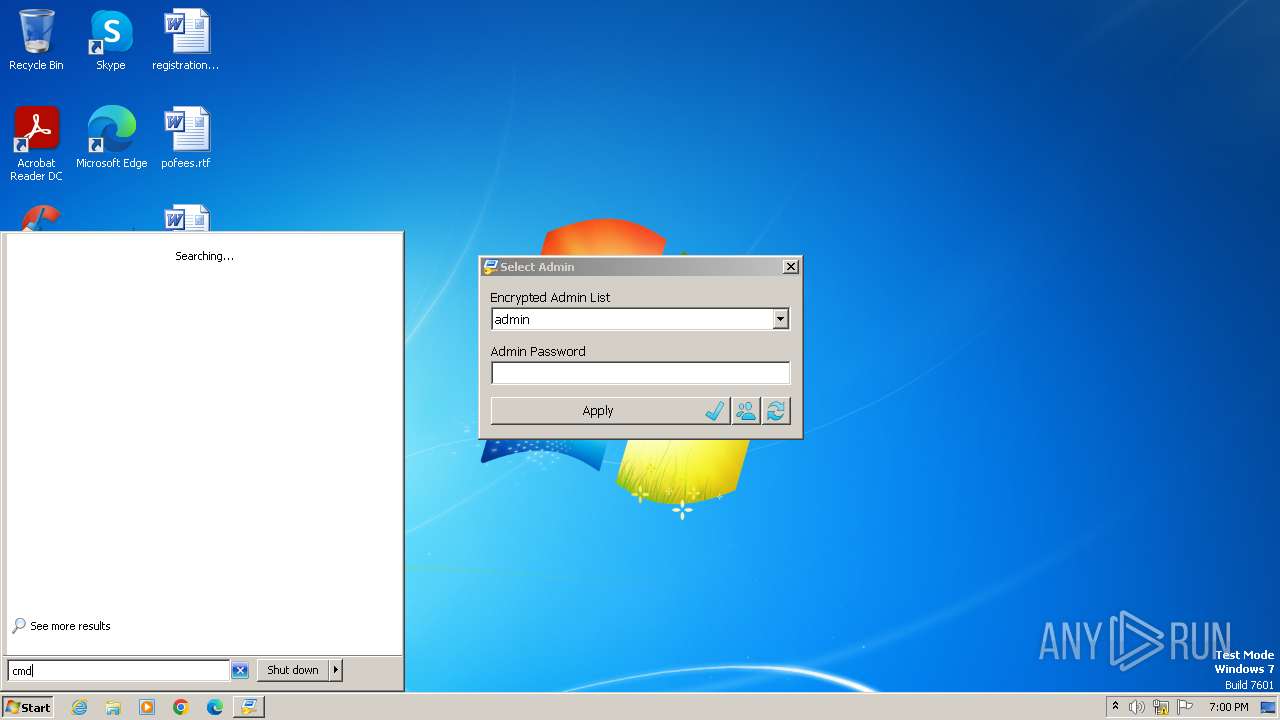
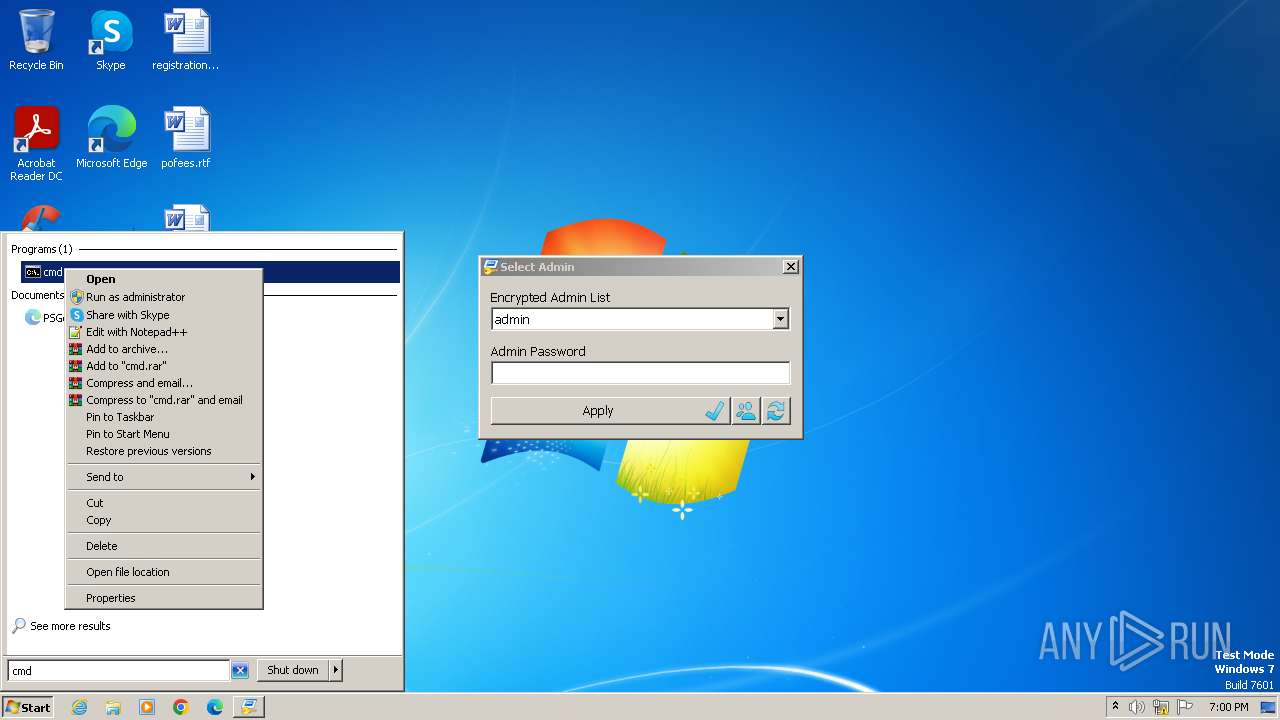
Manual execution by a user
- cmd.exe (PID: 2504)
Reads the machine GUID from the registry
- RunAsTool.exe (PID: 2876)
- RunAsTool.exe (PID: 3108)
Creates files in the program directory
- RunAsTool.exe (PID: 3108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:04:16 09:47:33+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 524800 |
| InitializedDataSize: | 177664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16310 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.0.0 |
| ProductVersionNumber: | 1.5.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| FileVersion: | 1.5.0.0 |
| Comments: | RunAs Tool |
| FileDescription: | RunAs Tool |
| LegalCopyright: | Copyright © 2015-2022 www.sordum.org All Rights Reserved. |
| Coder: | By BlueLife |
| CompanyName: | www.sordum.org |
| ProductVersion: | 1.5.0.0 |
| OriginalFileName: | RunAsTool.exe |
Total processes
53
Monitored processes
8
Malicious processes
0
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
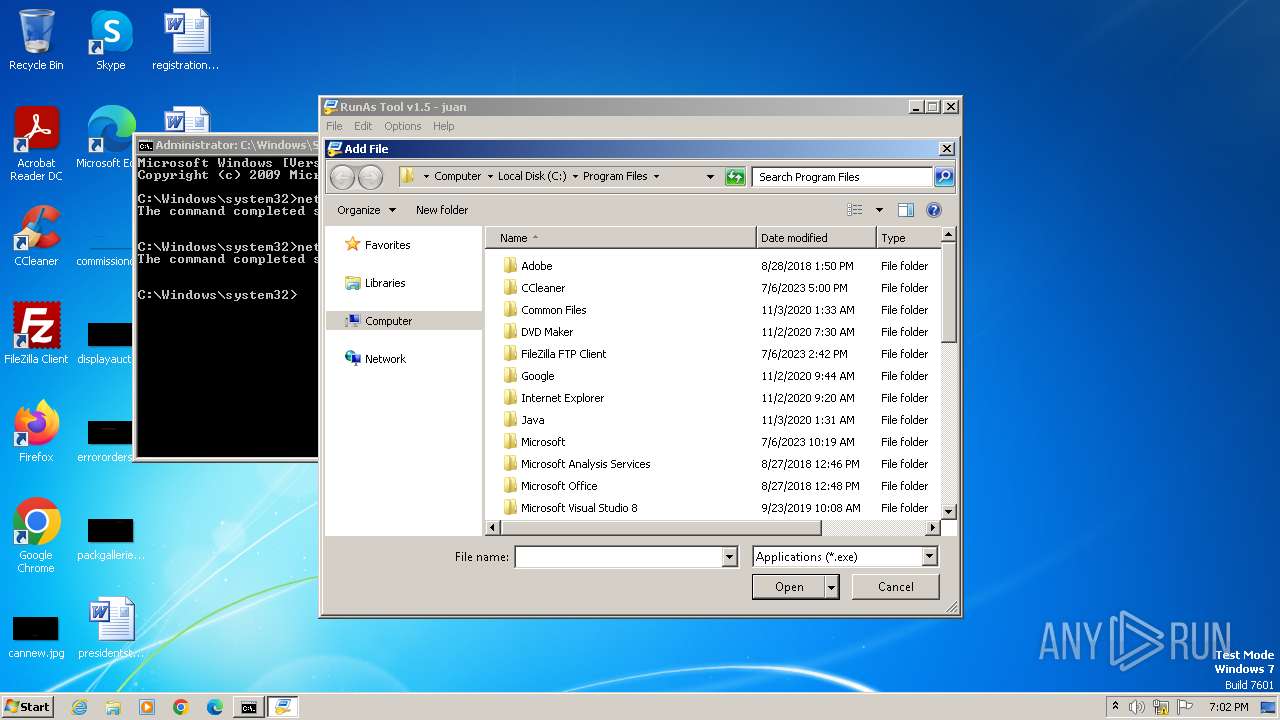
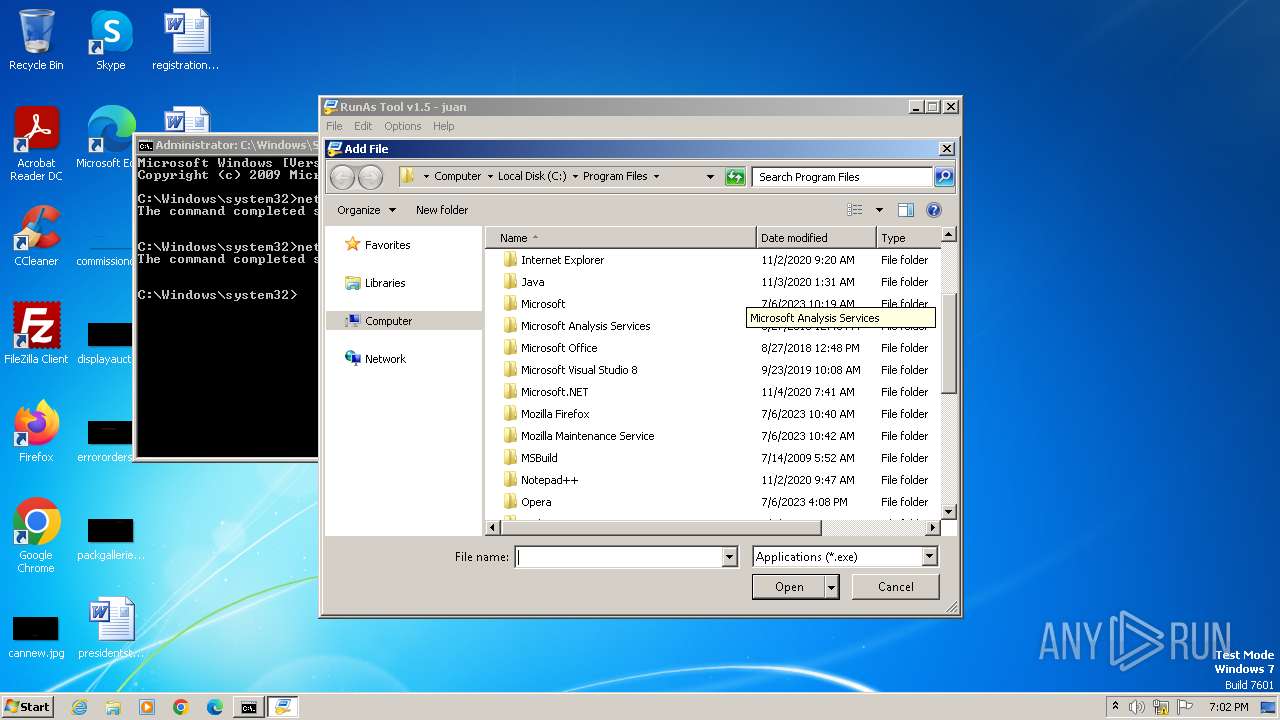
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1452 | net localgroup Administrators juan /add | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2504 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2776 | net user juan Odon1234 /add | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2840 | C:\Windows\system32\net1 user juan Odon1234 /add | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2876 | "C:\Users\admin\Downloads\RunAsTool.exe" | C:\Users\admin\Downloads\RunAsTool.exe | — | explorer.exe | |||||||||||
User: admin Company: www.sordum.org Integrity Level: MEDIUM Description: RunAs Tool Exit code: 2 Version: 1.5.0.0 Modules
| |||||||||||||||
| 3040 | C:\Windows\system32\net1 localgroup Administrators juan /add | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
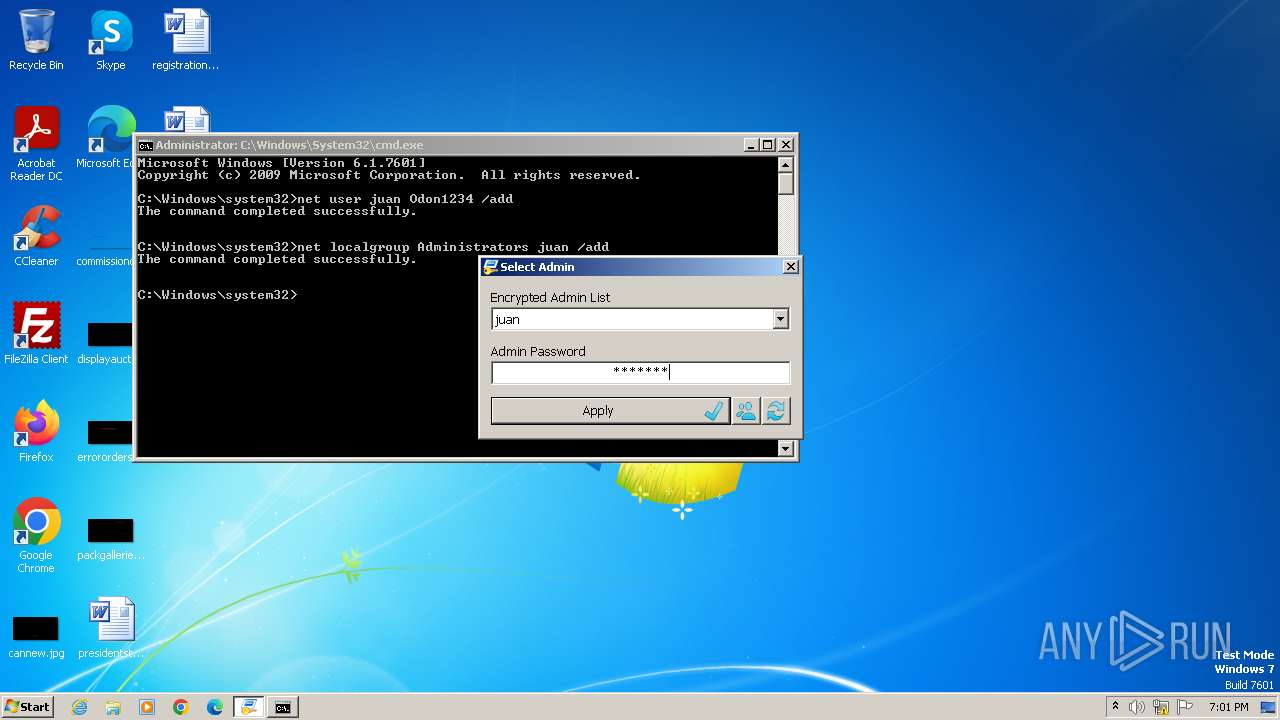
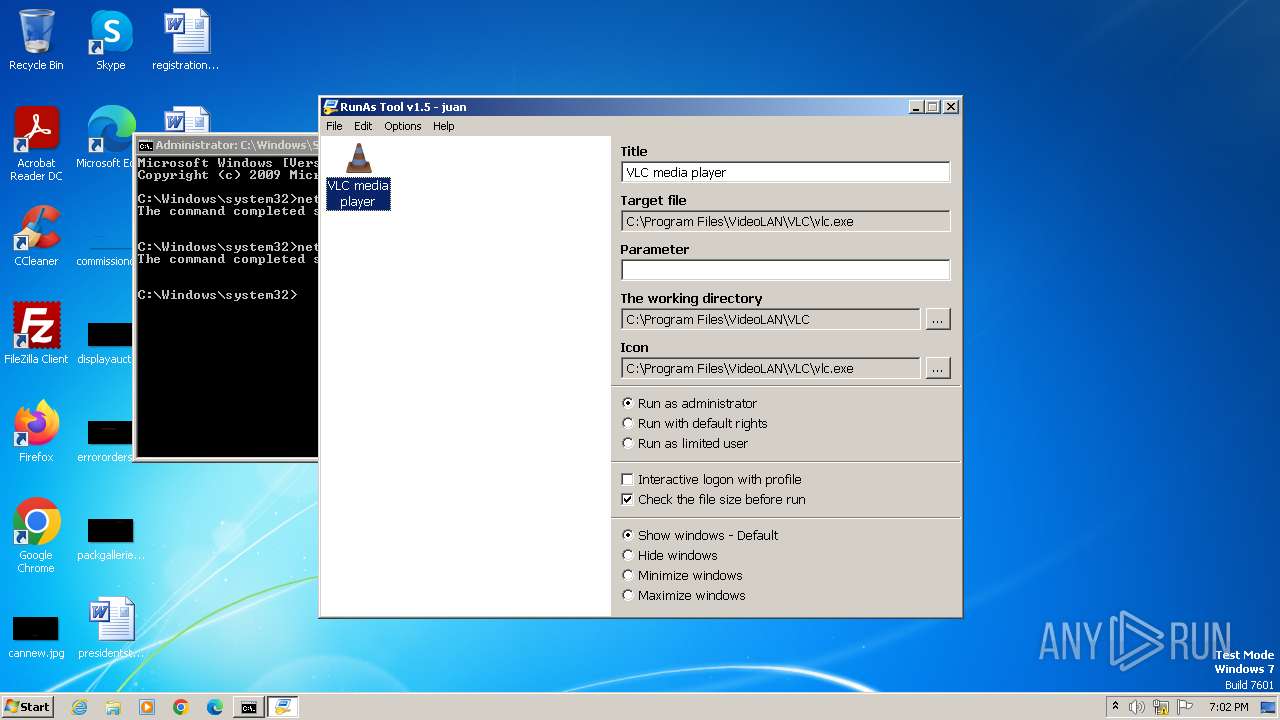
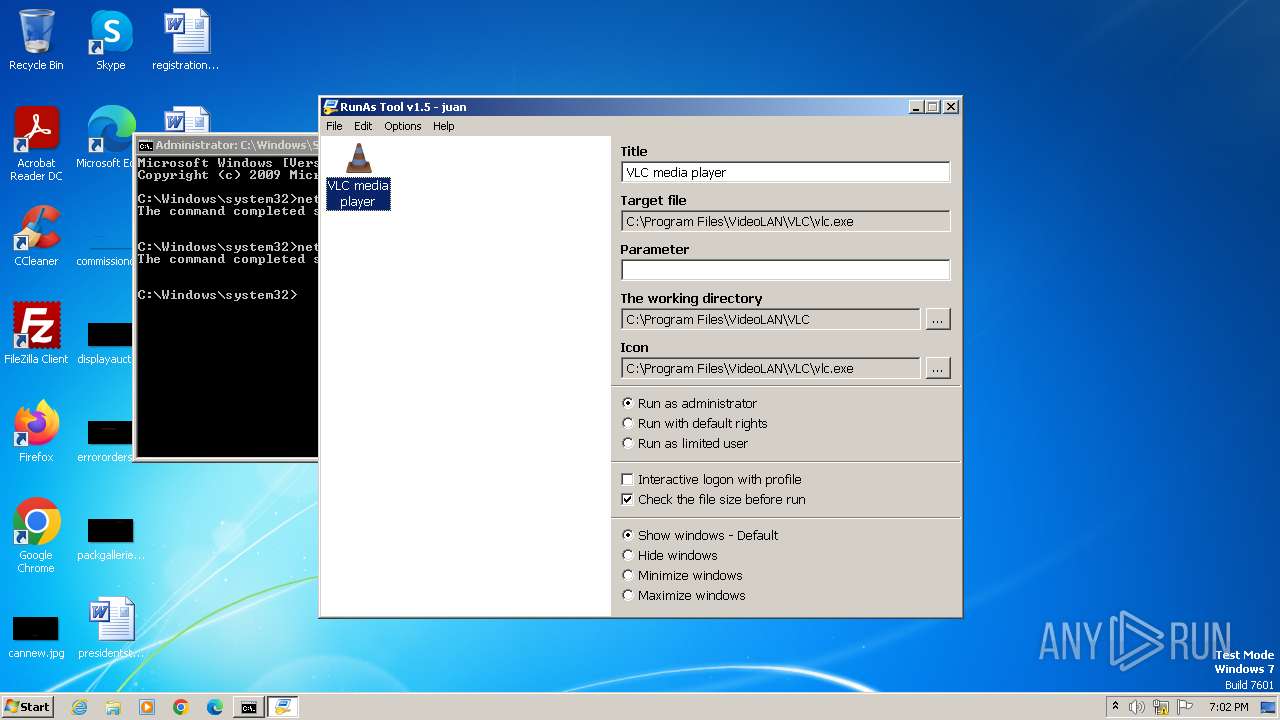
| 3108 | "C:\Users\admin\Downloads\RunAsTool.exe" /IsAdmin | C:\Users\admin\Downloads\RunAsTool.exe | RunAsTool.exe | ||||||||||||
User: juan Company: www.sordum.org Integrity Level: HIGH Description: RunAs Tool Exit code: 0 Version: 1.5.0.0 Modules
| |||||||||||||||
| 3640 | "C:\Users\admin\Downloads\RunAsTool.exe" /RunAdmin | C:\Users\admin\Downloads\RunAsTool.exe | — | RunAsTool.exe | |||||||||||
User: juan Company: www.sordum.org Integrity Level: MEDIUM Description: RunAs Tool Exit code: 0 Version: 1.5.0.0 Modules
| |||||||||||||||
Total events
2 691
Read events
2 628
Write events
60
Delete events
3
Modification events
| (PID) Process: | (3640) RunAsTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3640) RunAsTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3640) RunAsTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3640) RunAsTool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3108) RunAsTool.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\RunAsTool |
| Operation: | delete value | Name: | RunAsTool |
Value: 37A2777D647F01F8F314DC798F5905B24006779803549318225898612BB113 | |||
| (PID) Process: | (3108) RunAsTool.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\RunAsTool |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3108) RunAsTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: FFFFFFFF | |||
| (PID) Process: | (3108) RunAsTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02 | |||
| (PID) Process: | (3108) RunAsTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (3108) RunAsTool.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
15
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3640 | RunAsTool.exe | C:\Users\juan\AppData\Local\Temp\aut6748.tmp | binary | |
MD5:64E3579ED74175DE5C10EE8F27DBF2FA | SHA256:97DCFBCC84F34BF03D3EAE1F70CC1C91476836F4AEE8CB9C38FF4E19734240AB | |||
| 2876 | RunAsTool.exe | C:\Users\admin\Downloads\RunAsTool.ini | text | |
MD5:E74955C7E272D8CAAFD50E1385D055C2 | SHA256:BEB3B0A811C78509A9666DE8250CE2892ABD46175A74C477185DD87DCDE71EAA | |||
| 3108 | RunAsTool.exe | C:\Users\juan\AppData\Local\Microsoft\Windows\Explorer\thumbcache_96.db | binary | |
MD5:3E9C4EABA2C54DFE525197D54DC10532 | SHA256:05DA3DAA836DC6ED72144DFF35F8D90396B4D524DC35EF8D8CD01D86855BE858 | |||
| 2876 | RunAsTool.exe | C:\Users\admin\AppData\Local\Temp\autE00E.tmp | binary | |
MD5:FE971CFB8535AF5955F574609FD96D48 | SHA256:7D05ED3680FDE460C80A9E0DC0CD0DD814802C862B4CEB4AC20DABF9242EEABB | |||
| 3108 | RunAsTool.exe | C:\Users\juan\AppData\Local\Temp\aut68BF.tmp | binary | |
MD5:64E3579ED74175DE5C10EE8F27DBF2FA | SHA256:97DCFBCC84F34BF03D3EAE1F70CC1C91476836F4AEE8CB9C38FF4E19734240AB | |||
| 3108 | RunAsTool.exe | C:\Users\juan\AppData\Local\Microsoft\Windows\Explorer\thumbcache_idx.db | binary | |
MD5:D19D2DBCF116A4CB9F5FEDBCAD9C9F33 | SHA256:723FFBEE70BCCF84084457B6C1374F9B484A6A7282F8B12FCB2805751AB0FE59 | |||
| 3108 | RunAsTool.exe | C:\Program Files\RunAsTool\RunAsTool.ini | text | |
MD5:7DC25C1B9F204C1B8856775B69D21A7C | SHA256:5612B193179811AFC10CC5BB6EB72F3DF82CA244F30C762B70532BDBA7F74F3F | |||
| 3108 | RunAsTool.exe | C:\Users\juan\AppData\Local\Temp\aut68D0.tmp | binary | |
MD5:CC59A138FF3954A2D0888D71CB12B3A1 | SHA256:A4A0D9FA41467D3C5BCA1A33AAA1F75EE9FA62064B05B5023401F32523C1EE6D | |||
| 3640 | RunAsTool.exe | C:\Users\juan\AppData\Local\Temp\3o6m4v0p.tmp | text | |
MD5:603B9431AAC02883882DEC7A5A9F518D | SHA256:60734D71C7E8A3F4597CA9BCD2307668C65F71EE07C321A1A43A563BE48C47D5 | |||
| 3108 | RunAsTool.exe | C:\Users\juan\AppData\Local\Temp\3o1m0v8p.tmp | text | |
MD5:603B9431AAC02883882DEC7A5A9F518D | SHA256:60734D71C7E8A3F4597CA9BCD2307668C65F71EE07C321A1A43A563BE48C47D5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |