| URL: | https://bit.ly/3KHk3yQ |
| Full analysis: | https://app.any.run/tasks/67058a9e-2285-4413-afa1-395f78bc937b |
| Verdict: | Malicious activity |
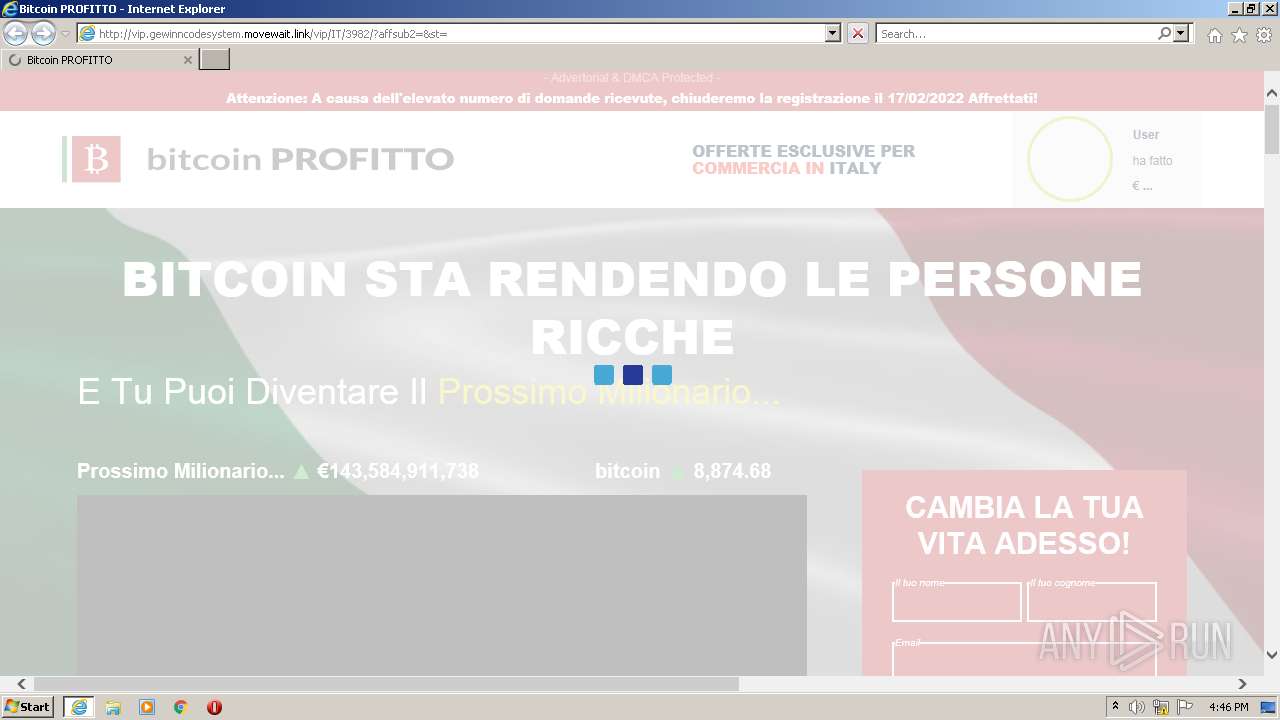
| Analysis date: | February 17, 2022, 16:45:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D710257860A52B4C6BD128C33E201A27 |
| SHA1: | 9186C6902DBA410A20DB3D2F715DA5B6EB58B6AD |
| SHA256: | 13D3277CBA729AF693CBF93867E3E6605BF3A482F0C86D74246C63D439F3FC89 |
| SSDEEP: | 3:N8kSu80:2i80 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1004)
- iexplore.exe (PID: 3752)
- iexplore.exe (PID: 1428)
INFO
Checks supported languages
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 1004)
- iexplore.exe (PID: 3752)
- iexplore.exe (PID: 1428)
Reads the computer name
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 3752)
- iexplore.exe (PID: 1428)
- iexplore.exe (PID: 1004)
Application launched itself
- iexplore.exe (PID: 2956)
Reads internet explorer settings
- iexplore.exe (PID: 3752)
- iexplore.exe (PID: 1428)
- iexplore.exe (PID: 1004)
Reads settings of System Certificates
- iexplore.exe (PID: 3752)
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 1428)
Creates files in the user directory
- iexplore.exe (PID: 3752)
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 1428)
Changes internet zones settings
- iexplore.exe (PID: 2956)
Checks Windows Trust Settings
- iexplore.exe (PID: 3752)
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 1428)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2956)
Changes settings of System certificates
- iexplore.exe (PID: 2956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
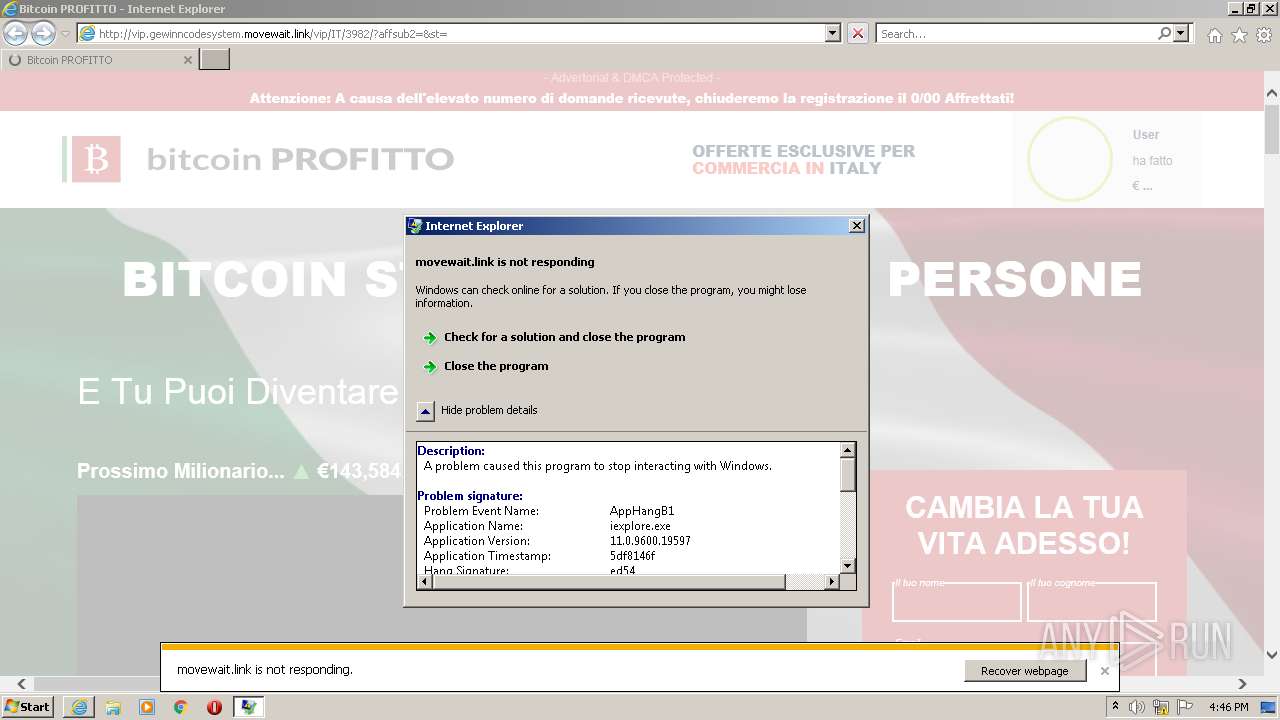
| 1004 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2956 CREDAT:3544335 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2956 CREDAT:4003086 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://bit.ly/3KHk3yQ" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3752 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2956 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3489660927 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
21 548
Read events
21 369
Write events
177
Delete events
2
Modification events
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30942237 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30942237 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
22
Text files
78
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3752 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0270780F846F08BEFE0DD8112D932FEF | der | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 3752 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\3KHk3yQ[1].htm | html | |
MD5:— | SHA256:— | |||
| 3752 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\4D1ED785E3365DE6C966A82E99CCE8EA_216A6C169356295AB09C26D4D7D32E06 | der | |
MD5:— | SHA256:— | |||
| 3752 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\4D1ED785E3365DE6C966A82E99CCE8EA_216A6C169356295AB09C26D4D7D32E06 | binary | |
MD5:— | SHA256:— | |||
| 3752 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0270780F846F08BEFE0DD8112D932FEF | binary | |
MD5:— | SHA256:— | |||
| 3752 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 3752 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\JCQB5LSV.txt | text | |
MD5:— | SHA256:— | |||
| 3752 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\L0HXUD8L.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
117
DNS requests
33
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
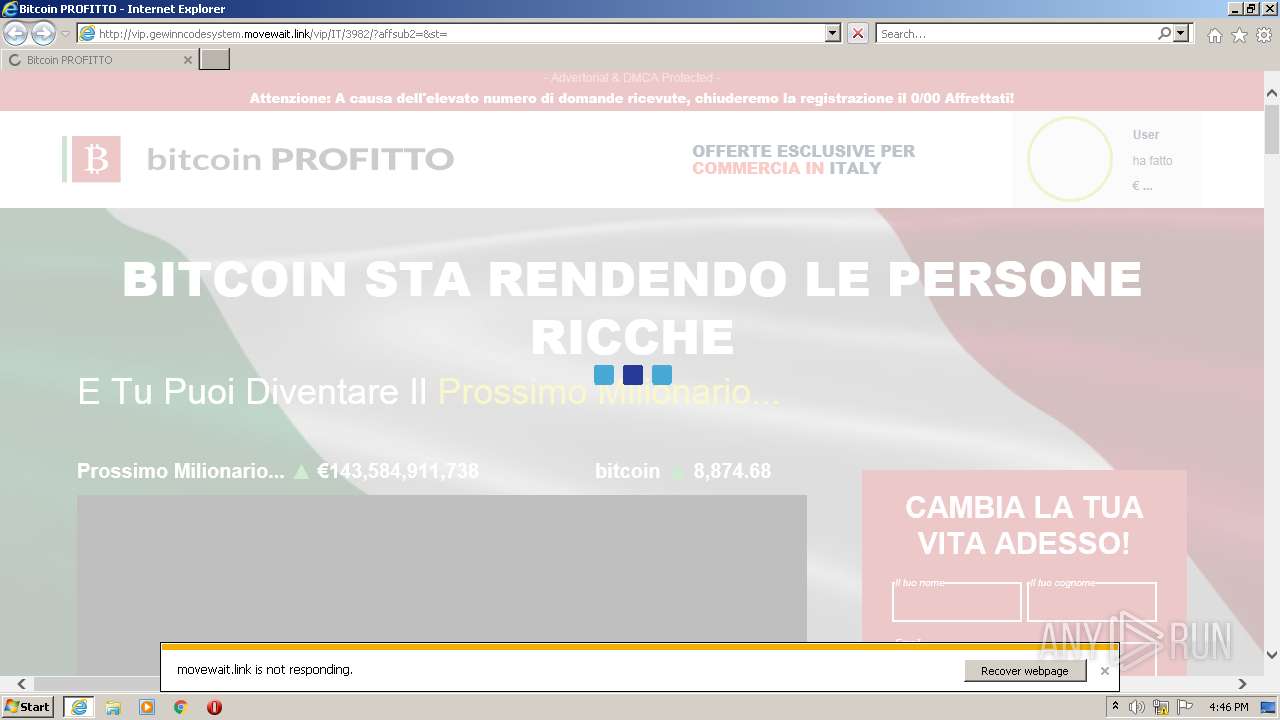
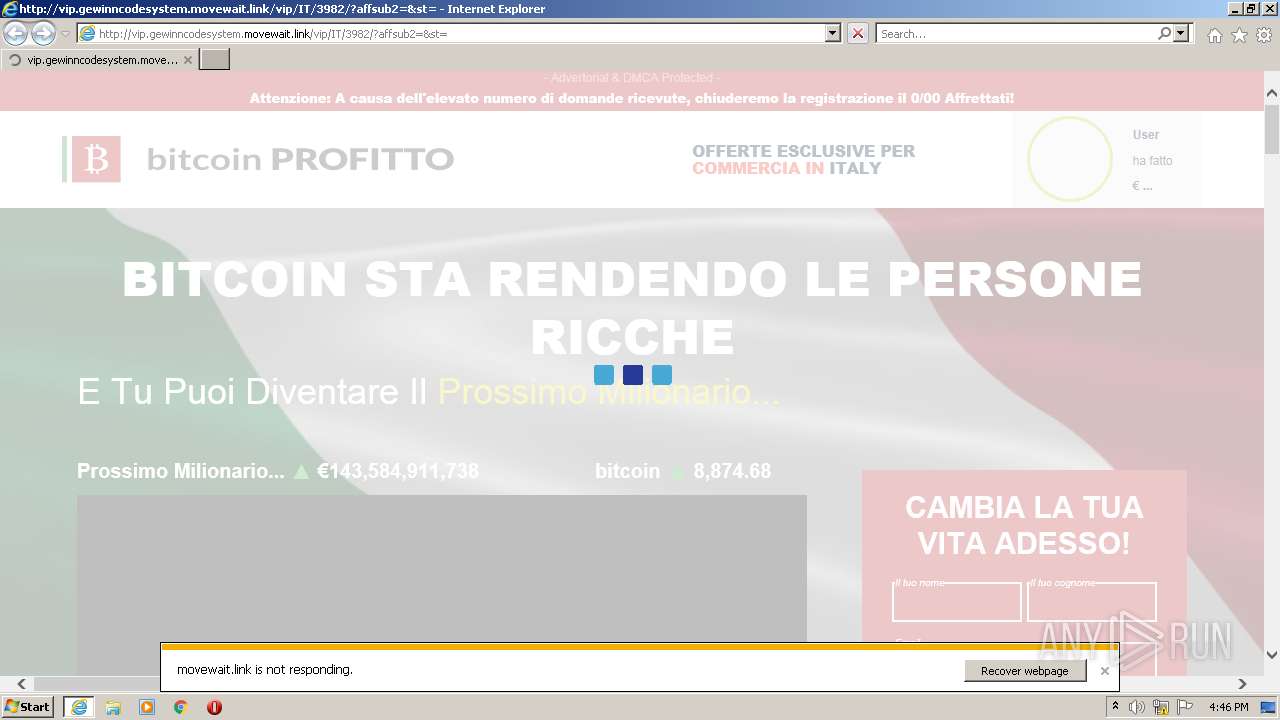
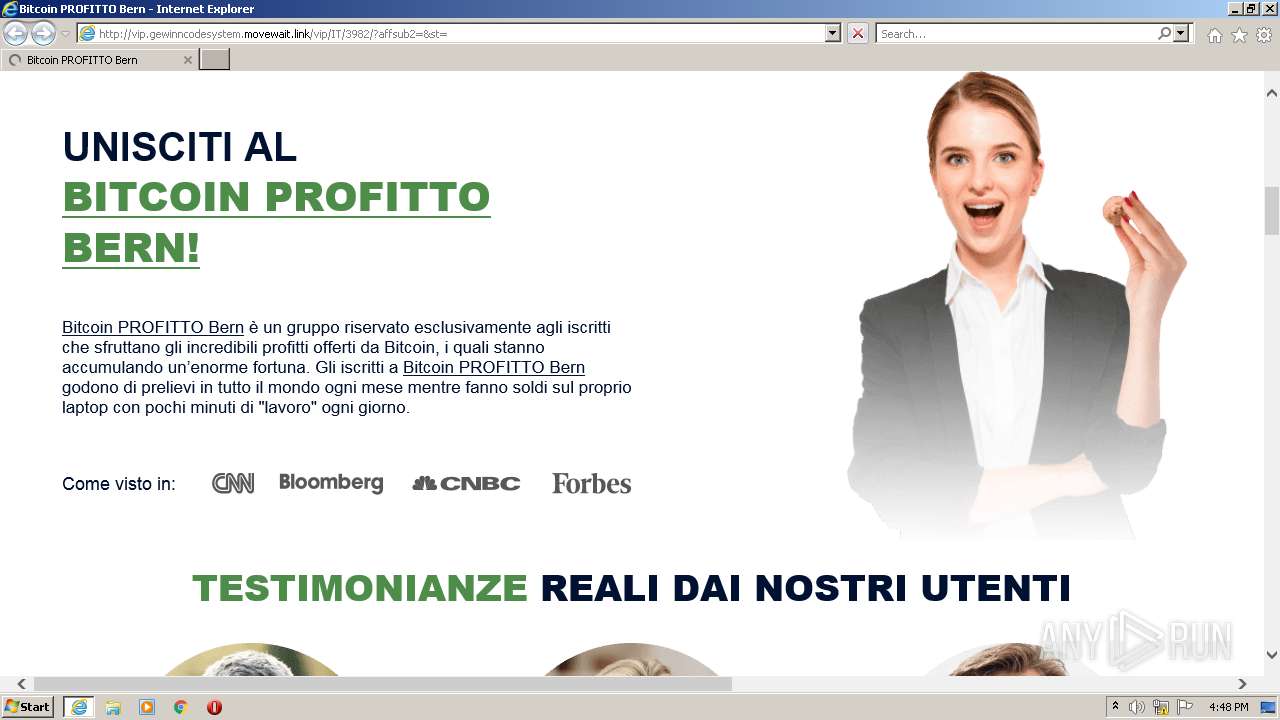
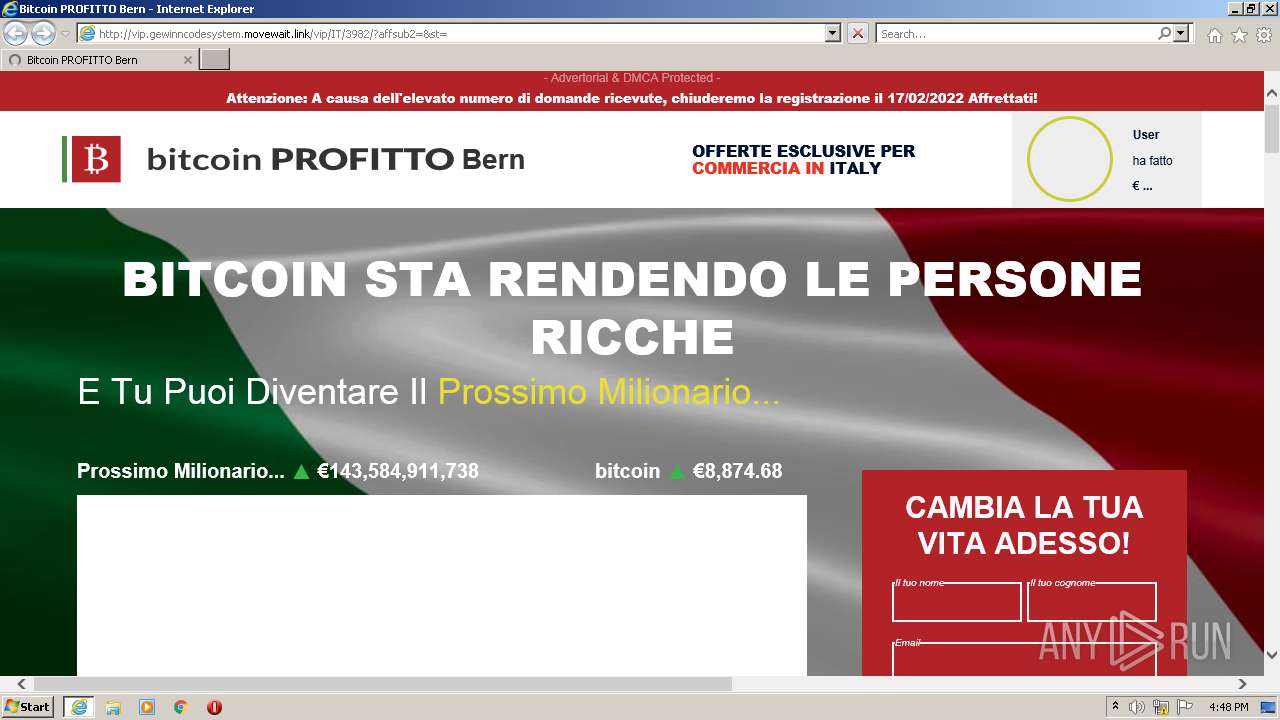
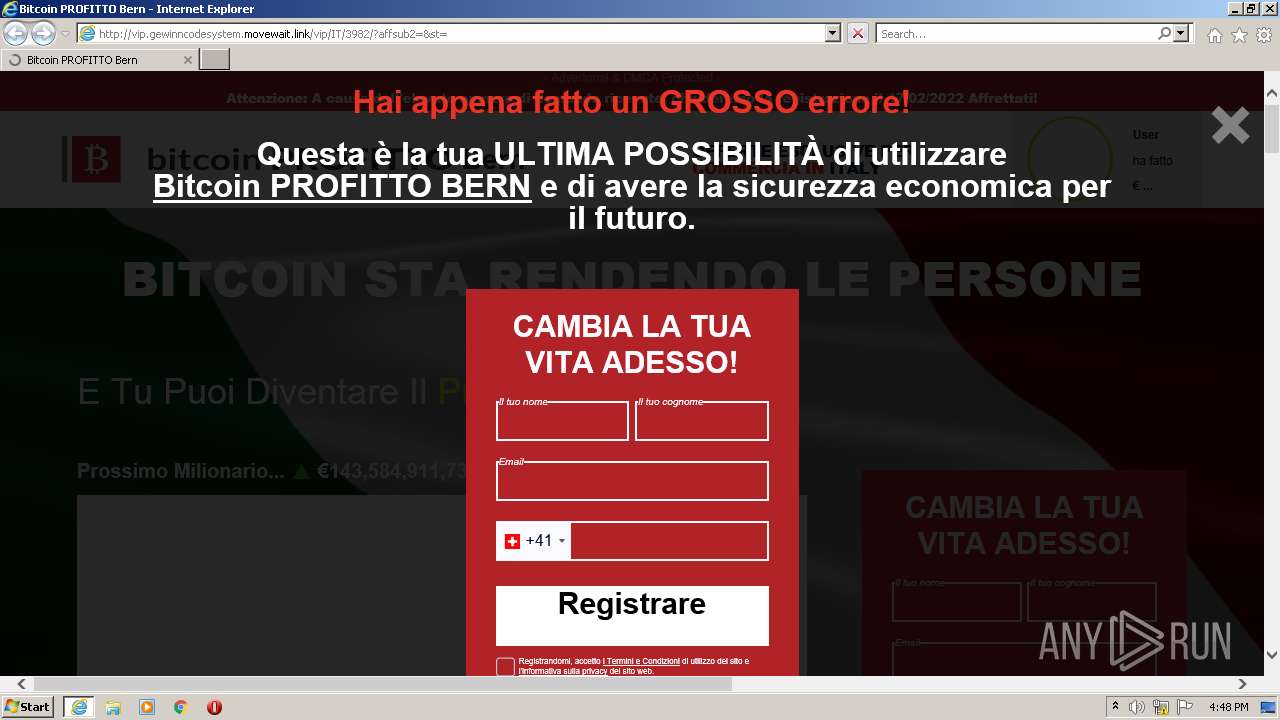
3752 | iexplore.exe | GET | 302 | 34.88.171.120:80 | http://nd7ad.imaginehair.link/athwt2 | US | — | — | suspicious |
3752 | iexplore.exe | GET | 200 | 34.88.171.120:80 | http://vip.gewinncodesystem.movewait.link/vip/IT/3982/css/index.css | US | text | 34.3 Kb | suspicious |
3752 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 592 b | whitelisted |
3752 | iexplore.exe | GET | 200 | 34.88.171.120:80 | http://vip.gewinncodesystem.movewait.link/vip/IT/3982/css/ion.rangeSlider.min.css | US | text | 10.8 Kb | suspicious |
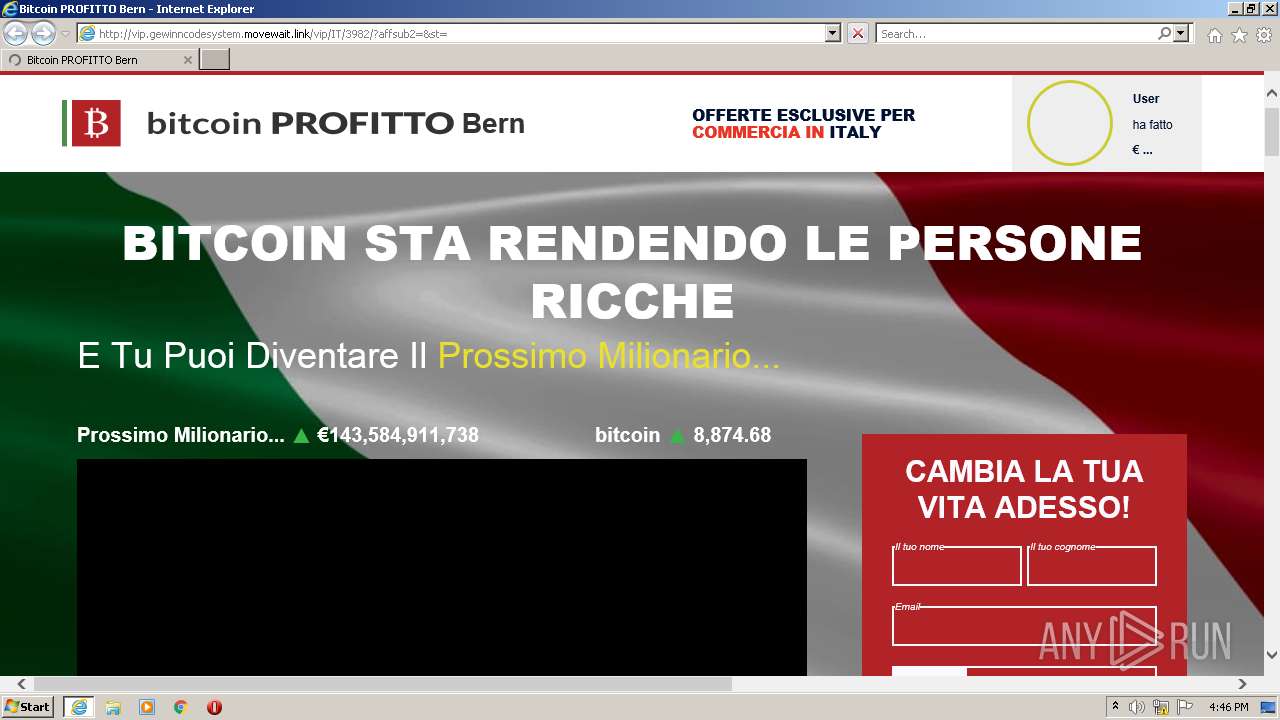
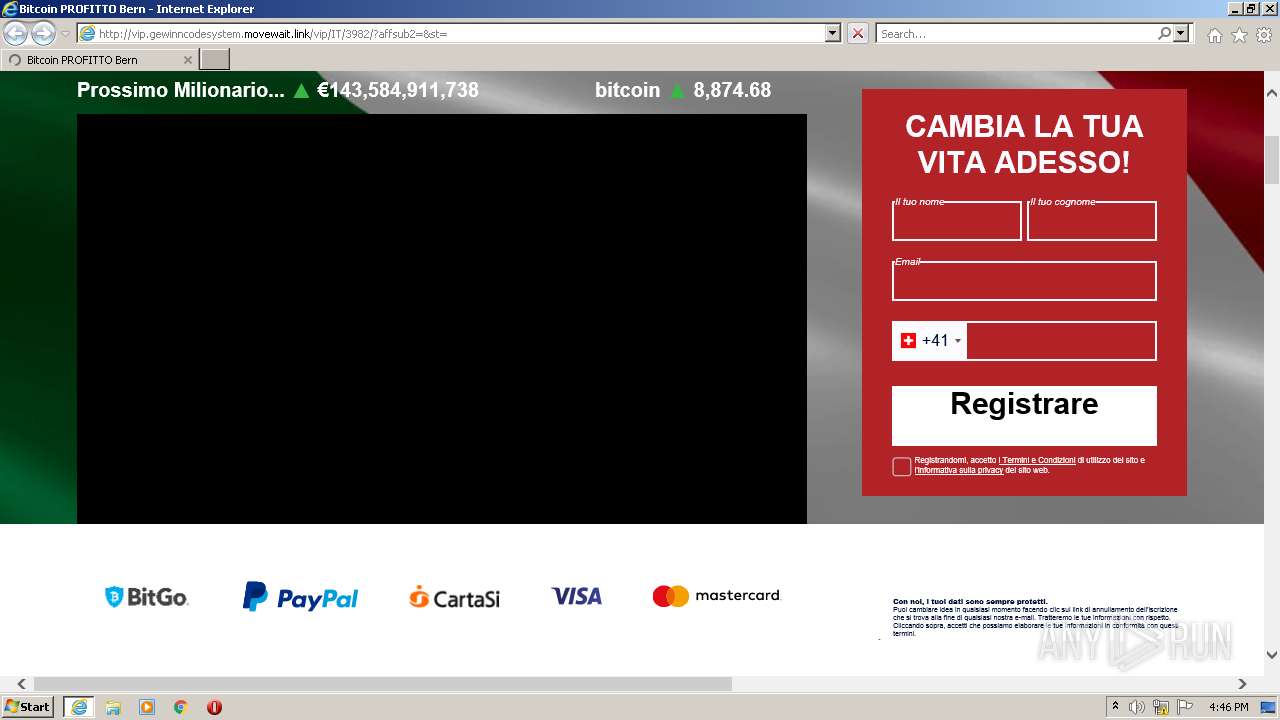
3752 | iexplore.exe | GET | 200 | 34.88.171.120:80 | http://vip.gewinncodesystem.movewait.link/vip/IT/3982/?affsub2=&st= | US | html | 11.4 Kb | suspicious |
3752 | iexplore.exe | GET | 200 | 34.88.171.120:80 | http://vip.gewinncodesystem.movewait.link/vip/IT/3982/css/popup-final.css | US | text | 2.57 Kb | suspicious |
3752 | iexplore.exe | GET | 200 | 34.88.171.120:80 | http://vip.gewinncodesystem.movewait.link/vip/IT/3982/css/bootstrap-grid.min.css | US | text | 28.0 Kb | suspicious |
3752 | iexplore.exe | GET | 301 | 34.88.171.120:80 | http://vip.gewinncodesystem.movewait.link/vip/IT/3982?affsub2=&st= | US | html | 185 b | suspicious |
3752 | iexplore.exe | GET | 200 | 34.88.171.120:80 | http://vip.gewinncodesystem.movewait.link/vip/IT/3982/css/index-fonts.css | US | text | 7.65 Kb | suspicious |
3752 | iexplore.exe | GET | 200 | 34.88.171.120:80 | http://vip.gewinncodesystem.movewait.link/vip/IT/3982/images/volume.png | US | image | 875 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2956 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3752 | iexplore.exe | 8.248.133.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
— | — | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2956 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3752 | iexplore.exe | 67.199.248.11:443 | bit.ly | Bitly Inc | US | shared |
2956 | iexplore.exe | 104.111.242.51:443 | go.microsoft.com | Akamai International B.V. | NL | unknown |
3752 | iexplore.exe | 67.199.248.10:443 | bit.ly | Bitly Inc | US | shared |
2956 | iexplore.exe | 13.92.246.37:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
1428 | iexplore.exe | 142.250.186.142:443 | s.ytimg.com | Google Inc. | US | whitelisted |
3752 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bit.ly |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
nd7ad.imaginehair.link |
| suspicious |
vip.gewinncodesystem.movewait.link |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
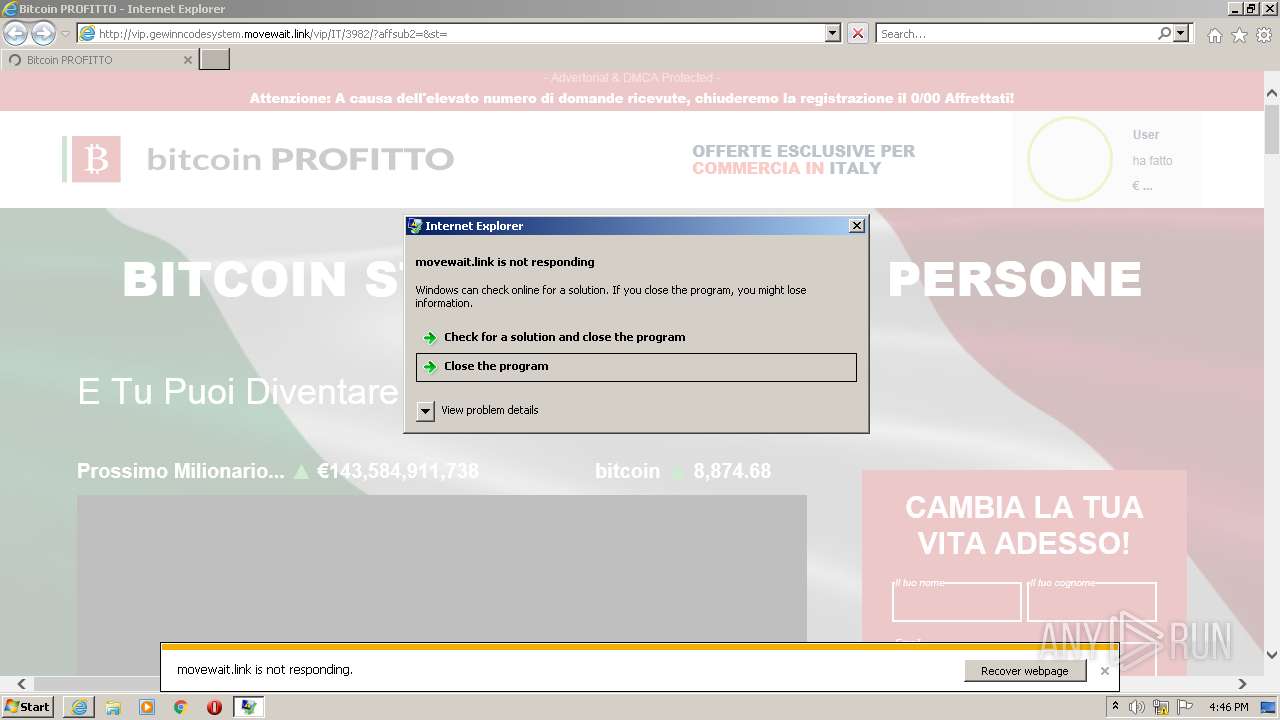
3752 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3752 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3752 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3752 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |