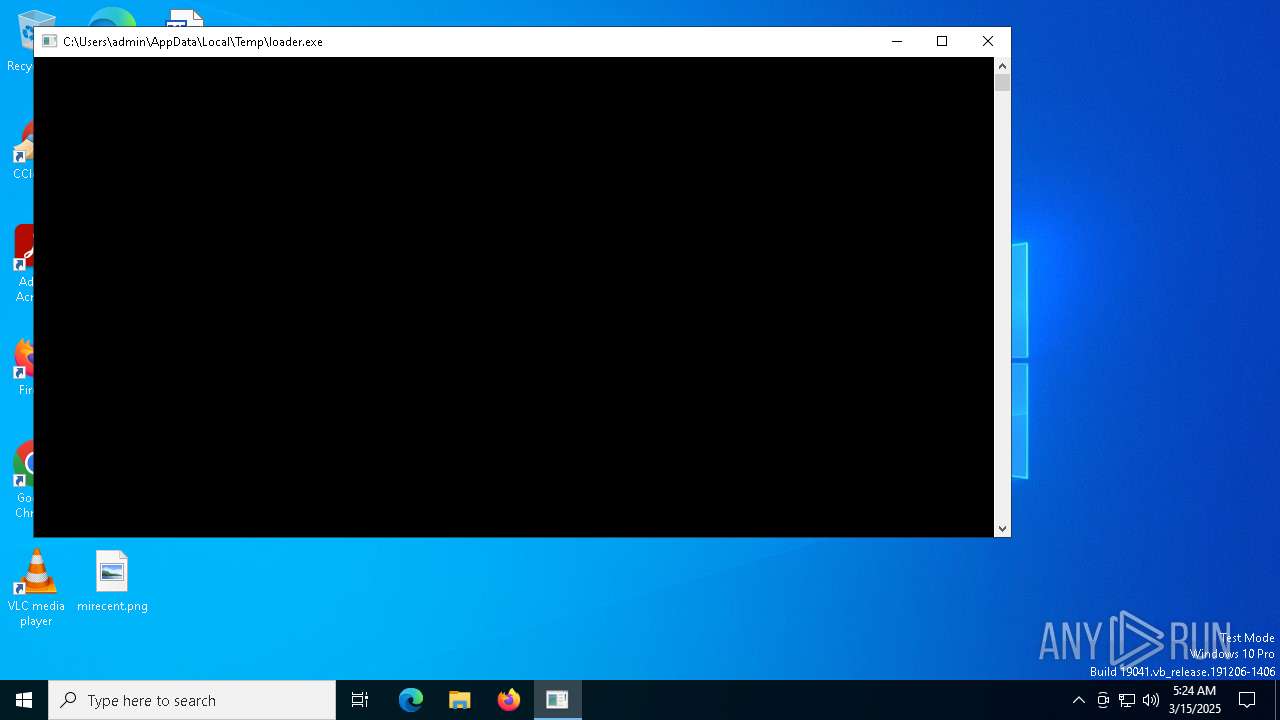
| File name: | loader.exe |
| Full analysis: | https://app.any.run/tasks/dc581409-f05f-4bb3-b1b6-a9447b3fc291 |
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2025, 05:23:59 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 13 sections |
| MD5: | 7CF56182CDA09ED6541EB04CEB428B90 |
| SHA1: | D441D9D23687A2BF445718238758707CE2E5B62C |
| SHA256: | 13D20912ED3F46C358F0A7C79C5B13F85CC81D0296CDB8582C2EF6F8E7879BA4 |
| SSDEEP: | 98304:JsTo8ilKPLm60WmQ9yQC4NDozzhs4eoV29zecm9GBw0xWZ5vB0rNI2/WTM9xzfwM:2TNj+8li1Y5 |
MALICIOUS
Uses TASKKILL.EXE to kill security tools
- cmd.exe (PID: 5200)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 7588)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 8164)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 7744)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 728)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 7948)
- cmd.exe (PID: 4024)
- cmd.exe (PID: 7272)
- cmd.exe (PID: 7372)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 8144)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 4892)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 856)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 1196)
- cmd.exe (PID: 7912)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 7852)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 1388)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 5404)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 7512)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 7268)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 4000)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 7520)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 4560)
- cmd.exe (PID: 616)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 7832)
- cmd.exe (PID: 7948)
- cmd.exe (PID: 8116)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 5204)
- cmd.exe (PID: 632)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 5512)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 5376)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 4560)
- cmd.exe (PID: 2108)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 7428)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 4112)
- cmd.exe (PID: 5164)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 7592)
- cmd.exe (PID: 7300)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 2240)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 4988)
- cmd.exe (PID: 5200)
- cmd.exe (PID: 5956)
- cmd.exe (PID: 7940)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 6964)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 7172)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 4756)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 2240)
- cmd.exe (PID: 5260)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 7860)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 4488)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 864)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 6632)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 7364)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 4040)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 5008)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 7940)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 5552)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 4268)
- cmd.exe (PID: 7452)
SUSPICIOUS
Reads the BIOS version
- loader.exe (PID: 1812)
Hides command output
- cmd.exe (PID: 4380)
- cmd.exe (PID: 1180)
- cmd.exe (PID: 5200)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 7448)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7588)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 7864)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 8044)
- cmd.exe (PID: 8100)
- cmd.exe (PID: 7396)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 4024)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 8164)
- cmd.exe (PID: 7744)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 6640)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 7500)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 7516)
- cmd.exe (PID: 728)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 6080)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 7948)
- cmd.exe (PID: 6964)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 7996)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 8112)
- cmd.exe (PID: 8172)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 7272)
- cmd.exe (PID: 7372)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 4024)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 728)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 6080)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 1240)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 8152)
- cmd.exe (PID: 8144)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 8076)
- cmd.exe (PID: 7460)
- cmd.exe (PID: 4892)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 7276)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 856)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 632)
- cmd.exe (PID: 7640)
- cmd.exe (PID: 1196)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 8108)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 7196)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 1348)
- cmd.exe (PID: 7912)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 7584)
- cmd.exe (PID: 7488)
- cmd.exe (PID: 7300)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 1388)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 7852)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 7252)
- cmd.exe (PID: 7380)
- cmd.exe (PID: 7340)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 5404)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 7512)
- cmd.exe (PID: 7744)
- cmd.exe (PID: 7412)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 7268)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 7484)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 8188)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 4988)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 7732)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 7864)
- cmd.exe (PID: 8004)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 4000)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 7832)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 5416)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 7520)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 4560)
- cmd.exe (PID: 616)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 7832)
- cmd.exe (PID: 5332)
- cmd.exe (PID: 1188)
- cmd.exe (PID: 7524)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 7716)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 7520)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 7572)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 7948)
- cmd.exe (PID: 5576)
- cmd.exe (PID: 8004)
- cmd.exe (PID: 8116)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 7244)
- cmd.exe (PID: 7448)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 4620)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 5204)
- cmd.exe (PID: 7844)
- cmd.exe (PID: 5512)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 632)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 4424)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 7420)
- cmd.exe (PID: 8176)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 7540)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 4560)
- cmd.exe (PID: 7620)
- cmd.exe (PID: 5376)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 7404)
- cmd.exe (PID: 2420)
- cmd.exe (PID: 2108)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 4896)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 7864)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 7904)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 7620)
- cmd.exe (PID: 4560)
- cmd.exe (PID: 5376)
- cmd.exe (PID: 7364)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 1180)
- cmd.exe (PID: 7408)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 7428)
- cmd.exe (PID: 6960)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 7276)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 4112)
- cmd.exe (PID: 5164)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 8152)
- cmd.exe (PID: 1760)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 536)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 7592)
- cmd.exe (PID: 7300)
- cmd.exe (PID: 2240)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 5176)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 2092)
- cmd.exe (PID: 8132)
- cmd.exe (PID: 8176)
- cmd.exe (PID: 5200)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 7716)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 4988)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 5956)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 7276)
- cmd.exe (PID: 4200)
- cmd.exe (PID: 7916)
- cmd.exe (PID: 7940)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 6964)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 4756)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 8084)
- cmd.exe (PID: 7196)
- cmd.exe (PID: 7172)
- cmd.exe (PID: 2984)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 4424)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 4892)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 4620)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 7860)
- cmd.exe (PID: 5260)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 2240)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 684)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 7944)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 8184)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 720)
- cmd.exe (PID: 4944)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 864)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 4488)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 7364)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 2908)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 7912)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 6632)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 8180)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 5404)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 7500)
- cmd.exe (PID: 7740)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 7364)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 2140)
- cmd.exe (PID: 7884)
- cmd.exe (PID: 5588)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 7344)
- cmd.exe (PID: 7872)
- cmd.exe (PID: 5008)
- cmd.exe (PID: 1184)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 4040)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 7244)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 6584)
- cmd.exe (PID: 4436)
- cmd.exe (PID: 5436)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 7940)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 8068)
- cmd.exe (PID: 5556)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 1136)
- cmd.exe (PID: 7552)
- cmd.exe (PID: 8132)
- cmd.exe (PID: 6852)
- cmd.exe (PID: 5008)
- cmd.exe (PID: 4040)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 7244)
- cmd.exe (PID: 1188)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 684)
- cmd.exe (PID: 5552)
- cmd.exe (PID: 4268)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 5036)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 7364)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 3332)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 1180)
- cmd.exe (PID: 7988)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 1132)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 4380)
- cmd.exe (PID: 1180)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 7448)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7864)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 7248)
- cmd.exe (PID: 7396)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 4024)
- cmd.exe (PID: 6044)
- cmd.exe (PID: 7564)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 8100)
- cmd.exe (PID: 7976)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 4408)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 7500)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 7516)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 6080)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 6964)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 7996)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 8172)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 8112)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 728)
- cmd.exe (PID: 1240)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 6080)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 3100)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 8000)
- cmd.exe (PID: 8076)
- cmd.exe (PID: 8152)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 7236)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 632)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 7276)
- cmd.exe (PID: 7696)
- cmd.exe (PID: 8108)
- cmd.exe (PID: 7196)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 8072)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 7584)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 7488)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 7300)
- cmd.exe (PID: 1348)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 7776)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 7880)
- cmd.exe (PID: 8096)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 7252)
- cmd.exe (PID: 7380)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 6040)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 7744)
- cmd.exe (PID: 7412)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 6668)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 7484)
- cmd.exe (PID: 7556)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 4988)
- cmd.exe (PID: 7452)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 8004)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 7864)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 2392)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 7832)
- cmd.exe (PID: 5416)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 7376)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 5228)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 7876)
- cmd.exe (PID: 1188)
- cmd.exe (PID: 5332)
- cmd.exe (PID: 7572)
- cmd.exe (PID: 7716)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 7520)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 7524)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 8004)
- cmd.exe (PID: 1096)
- cmd.exe (PID: 5084)
- cmd.exe (PID: 7244)
- cmd.exe (PID: 7448)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 4620)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 7420)
- cmd.exe (PID: 8176)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 7968)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 4424)
- cmd.exe (PID: 7320)
- cmd.exe (PID: 7620)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 7540)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 2420)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 4896)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 2644)
- cmd.exe (PID: 7864)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 7528)
- cmd.exe (PID: 7620)
- cmd.exe (PID: 5376)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 4560)
- cmd.exe (PID: 7276)
- cmd.exe (PID: 7408)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 1180)
- cmd.exe (PID: 7364)
- cmd.exe (PID: 2268)
- cmd.exe (PID: 536)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 8152)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 2320)
- cmd.exe (PID: 4688)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 1760)
- cmd.exe (PID: 5176)
- cmd.exe (PID: 4188)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 8040)
- cmd.exe (PID: 8156)
- cmd.exe (PID: 8132)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 2092)
- cmd.exe (PID: 8176)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 7820)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 1072)
- cmd.exe (PID: 7716)
- cmd.exe (PID: 7800)
- cmd.exe (PID: 4200)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 7276)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 5680)
- cmd.exe (PID: 8084)
- cmd.exe (PID: 4424)
- cmd.exe (PID: 7312)
- cmd.exe (PID: 7464)
- cmd.exe (PID: 4892)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 4620)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 7196)
- cmd.exe (PID: 7188)
- cmd.exe (PID: 7560)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 7700)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 7944)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 684)
- cmd.exe (PID: 8080)
- cmd.exe (PID: 2340)
- cmd.exe (PID: 720)
- cmd.exe (PID: 7364)
- cmd.exe (PID: 2980)
- cmd.exe (PID: 5304)
- cmd.exe (PID: 7576)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 2908)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 5640)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 4464)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 7912)
- cmd.exe (PID: 4068)
- cmd.exe (PID: 8136)
- cmd.exe (PID: 7544)
- cmd.exe (PID: 1616)
- cmd.exe (PID: 8180)
- cmd.exe (PID: 7740)
- cmd.exe (PID: 7476)
- cmd.exe (PID: 5404)
- cmd.exe (PID: 6156)
- cmd.exe (PID: 7500)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 7884)
- cmd.exe (PID: 7828)
- cmd.exe (PID: 2140)
- cmd.exe (PID: 7892)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 8120)
- cmd.exe (PID: 7872)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 7344)
- cmd.exe (PID: 2096)
- cmd.exe (PID: 5588)
- cmd.exe (PID: 1184)
- cmd.exe (PID: 7244)
- cmd.exe (PID: 7324)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7788)
- cmd.exe (PID: 7288)
- cmd.exe (PID: 6584)
- cmd.exe (PID: 4436)
- cmd.exe (PID: 7468)
- cmd.exe (PID: 7568)
- cmd.exe (PID: 1136)
- cmd.exe (PID: 7552)
- cmd.exe (PID: 8132)
- cmd.exe (PID: 5008)
- cmd.exe (PID: 6852)
- cmd.exe (PID: 4040)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 7244)
- cmd.exe (PID: 5508)
- cmd.exe (PID: 1188)
- cmd.exe (PID: 7908)
- cmd.exe (PID: 684)
- cmd.exe (PID: 5036)
- cmd.exe (PID: 7688)
- cmd.exe (PID: 7364)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 3332)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 1180)
- cmd.exe (PID: 7988)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 1132)
Starts CMD.EXE for commands execution
- loader.exe (PID: 1812)
INFO
Checks supported languages
- loader.exe (PID: 1812)
Process checks whether UAC notifications are on
- loader.exe (PID: 1812)
Gets the hash of the file via CERTUTIL.EXE
- certutil.exe (PID: 1228)
Reads the computer name
- loader.exe (PID: 1812)
Themida protector has been detected
- loader.exe (PID: 1812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:03:13 19:27:11+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 1143296 |
| InitializedDataSize: | 390144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x75a058 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
1 153
Monitored processes
1 022
Malicious processes
1
Suspicious processes
191
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | C:\WINDOWS\system32\cmd.exe /c taskkill /FI "IMAGENAME eq httpdebugger*" /IM * /F /T >nul 2>&1 | C:\Windows\System32\cmd.exe | — | loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\cmd.exe /c taskkill /f /im x64dbg.exe >nul 2>&1 | C:\Windows\System32\cmd.exe | — | loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | taskkill /f /im HTTPDebuggerUI.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | taskkill /f /im Ida64.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | C:\WINDOWS\system32\cmd.exe /c taskkill /FI "IMAGENAME eq processhacker*" /IM * /F /T >nul 2>&1 | C:\Windows\System32\cmd.exe | — | loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | taskkill /f /im HTTPDebuggerUI.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | C:\WINDOWS\system32\cmd.exe /c taskkill /f /im HTTPDebuggerUI.exe >nul 2>&1 | C:\Windows\System32\cmd.exe | — | loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | taskkill /f /im cheatengine-x86_64-SSE4-AVX2.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | taskkill /f /im idaq64.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | taskkill /f /im HTTPDebuggerUI.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
49 847
Read events
49 844
Write events
3
Delete events
0
Modification events
| (PID) Process: | (1228) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.1!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_AUTO_UPDATE_CA_REVOCATION | |||
| (PID) Process: | (1228) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.2!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_AUTO_UPDATE_END_REVOCATION | |||
| (PID) Process: | (1228) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.3!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_NO_OCSP_FAILOVER_TO_CRL | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
15
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
756 | lsass.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
8164 | SIHClient.exe | GET | 200 | 23.222.10.99:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
— | — | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
6240 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | unknown |
8164 | SIHClient.exe | GET | 200 | 23.222.10.99:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
1812 | loader.exe | 172.67.72.57:443 | keyauth.win | CLOUDFLARENET | US | unknown |
3216 | svchost.exe | 20.198.162.76:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | unknown |
756 | lsass.exe | 2.23.197.184:80 | x1.c.lencr.org | CW Vodafone Group PLC | GB | unknown |
— | — | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
— | — | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | unknown |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6544 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| unknown |
google.com |
| unknown |
crl.microsoft.com |
| whitelisted |
keyauth.win |
| unknown |
client.wns.windows.com |
| unknown |
x1.c.lencr.org |
| unknown |
login.live.com |
| unknown |
ocsp.digicert.com |
| unknown |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1812 | loader.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |