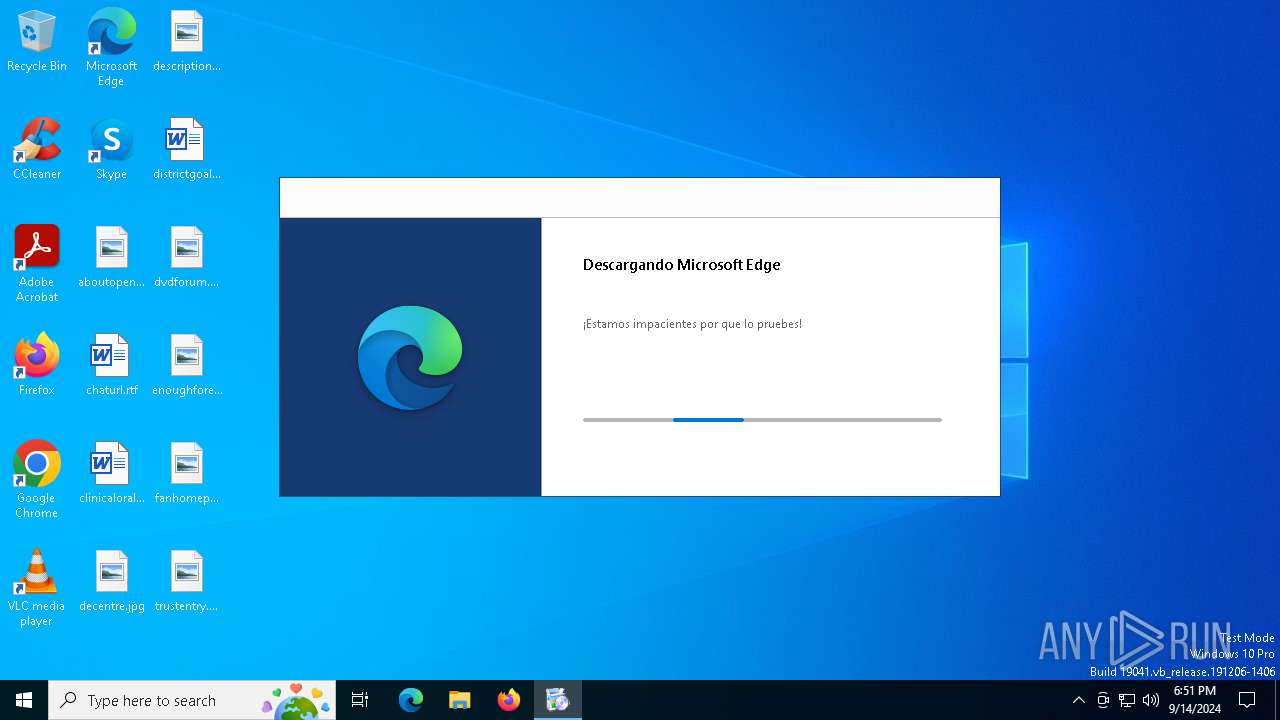
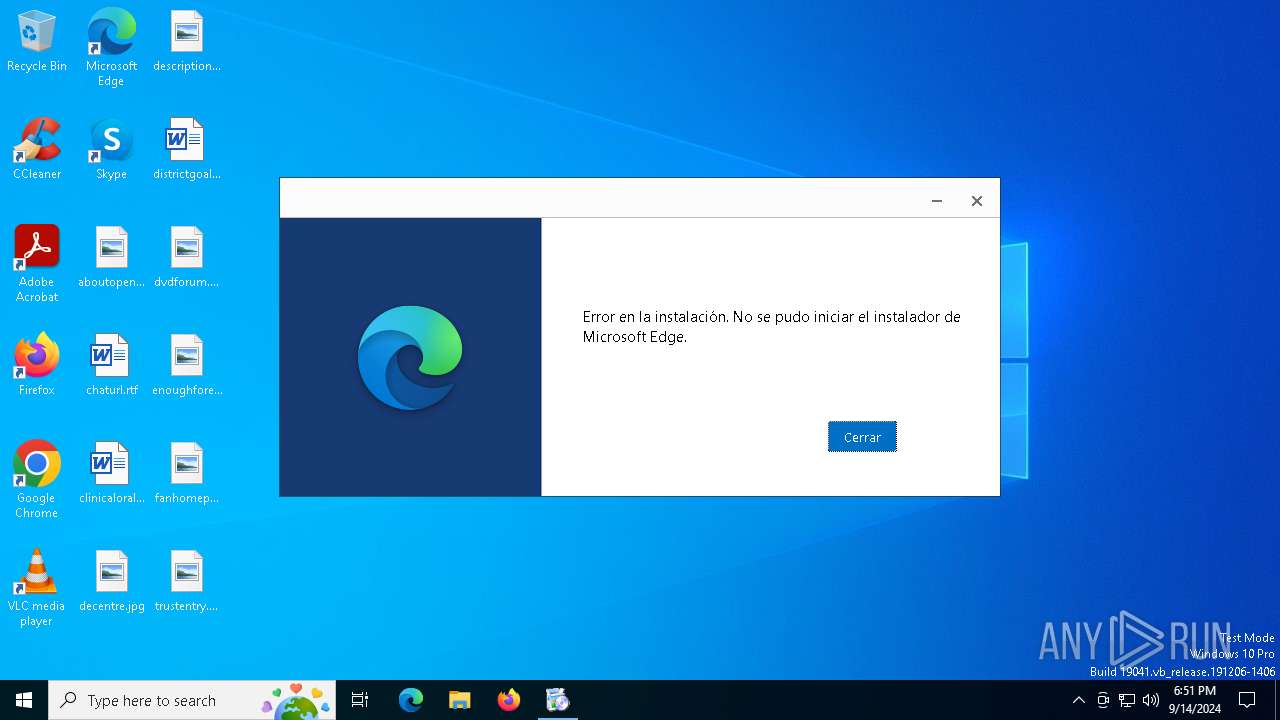
| File name: | MicrosoftEdgeSetup.exe |
| Full analysis: | https://app.any.run/tasks/d3d1035a-9a12-4a0a-9d8a-f6557e715243 |
| Verdict: | Malicious activity |
| Analysis date: | September 14, 2024, 18:50:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6FF133CA319EE4A8D350B130FACF9A8B |
| SHA1: | 685BC1715C814E4B68B4B7A4ADFCA50B982A500A |
| SHA256: | 13C7236C900455B05ED4E066C175361F76D1AEEAC0E0592FAA8D4DE020254F6A |
| SSDEEP: | 49152:RTwFJC8q0b7NALZ0aKJUb41o2M7nmB+181WHm0ZHjQsfSnAMveSC+1b7hGtPCPDH:RqnnNSDN1mS81WHm0ljj1MJr1b9pDsCr |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- MicrosoftEdgeSetup.exe (PID: 4980)
- MicrosoftEdgeUpdateSetup.exe (PID: 6248)
Starts a Microsoft application from unusual location
- MicrosoftEdgeSetup.exe (PID: 4980)
- MicrosoftEdgeUpdate.exe (PID: 3236)
- MicrosoftEdgeUpdate.exe (PID: 1156)
- MicrosoftEdgeUpdateSetup.exe (PID: 6248)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 3236)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 3236)
- MicrosoftEdgeUpdate.exe (PID: 1156)
INFO
Create files in a temporary directory
- MicrosoftEdgeUpdate.exe (PID: 1156)
- MicrosoftEdgeSetup.exe (PID: 4980)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 1156)
- MicrosoftEdgeUpdate.exe (PID: 3236)
Reads the computer name
- MicrosoftEdgeUpdate.exe (PID: 1156)
- MicrosoftEdgeUpdate.exe (PID: 3236)
Checks supported languages
- MicrosoftEdgeUpdate.exe (PID: 1156)
- MicrosoftEdgeSetup.exe (PID: 4980)
- MicrosoftEdgeUpdateSetup.exe (PID: 6248)
- MicrosoftEdgeUpdate.exe (PID: 3236)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 3236)
- MicrosoftEdgeUpdate.exe (PID: 1156)
Creates files in the program directory
- MicrosoftEdgeUpdateSetup.exe (PID: 6248)
- MicrosoftEdgeUpdate.exe (PID: 1156)
Checks proxy server information
- MicrosoftEdgeUpdate.exe (PID: 3236)
- wermgr.exe (PID: 1076)
- wermgr.exe (PID: 7028)
Reads the software policy settings
- MicrosoftEdgeUpdate.exe (PID: 3236)
- wermgr.exe (PID: 1076)
- wermgr.exe (PID: 7028)
Reads the machine GUID from the registry
- MicrosoftEdgeUpdate.exe (PID: 1156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:09:04 15:33:37+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.31 |
| CodeSize: | 110592 |
| InitializedDataSize: | 1512960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x83f0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.195.19 |
| ProductVersionNumber: | 1.3.195.19 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Edge Update Setup |
| FileVersion: | 1.3.195.19 |
| InternalName: | Microsoft Edge Update Setup |
| LegalCopyright: | Copyright Microsoft Corporation |
| OriginalFileName: | MicrosoftEdgeUpdateSetup.exe |
| ProductName: | Microsoft Edge Update |
| ProductVersion: | 1.3.195.19 |
| UpstreamVersion: | 1.3.99.0 |
| LanguageId: | en |
Total processes
126
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1076 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "3236" "2200" "972" "2196" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\SysWOW64\wermgr.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\MicrosoftEdgeUpdate.exe /installsource taggedmi /install "appguid={56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}&appname=Microsoft%20Edge&needsadmin=prefers&lang=es-419&brand=M100" | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 2147747592 Version: 1.3.195.19 Modules
| |||||||||||||||
| 3236 | "C:\Program Files (x86)\Microsoft\Temp\EUB09B.tmp\MicrosoftEdgeUpdate.exe" /installsource taggedmi /install "appguid={56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}&appname=Microsoft%20Edge&needsadmin=prefers&lang=es-419&brand=M100" /installelevated | C:\Program Files (x86)\Microsoft\Temp\EUB09B.tmp\MicrosoftEdgeUpdate.exe | MicrosoftEdgeUpdateSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Update Exit code: 2147747592 Version: 1.3.195.19 Modules
| |||||||||||||||
| 4980 | "C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeSetup.exe" | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeSetup.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Setup Exit code: 2147747592 Version: 1.3.195.19 Modules
| |||||||||||||||
| 6248 | "C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\MicrosoftEdgeUpdateSetup.exe" /installsource taggedmi /install "appguid={56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}&appname=Microsoft%20Edge&needsadmin=prefers&lang=es-419&brand=M100" /installelevated /nomitag | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\MicrosoftEdgeUpdateSetup.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Update Setup Exit code: 2147747592 Version: 1.3.195.19 Modules
| |||||||||||||||
| 7028 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "1156" "1588" "1564" "1592" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\SysWOW64\wermgr.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 870
Read events
6 835
Write events
33
Delete events
2
Modification events
| (PID) Process: | (3236) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MicrosoftEdgeUpdate.exe |
| Operation: | write | Name: | DisableExceptionChainValidation |
Value: 0 | |||
| (PID) Process: | (3236) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{176E3885-BF20-4882-8138-2BB412DAD4AB} |
| Operation: | write | Name: | PersistedPingString |
Value: <?xml version="1.0" encoding="UTF-8"?><request protocol="3.0" updater="Omaha" updaterversion="1.3.195.19" shell_version="1.3.147.37" ismachine="1" sessionid="{B836D1D9-00D1-41FD-8AC7-5A04428B4EBA}" userid="{FD984739-A122-4DB0-BE5B-46E3E09D84E4}" installsource="taggedmi" requestid="{176E3885-BF20-4882-8138-2BB412DAD4AB}" dedup="cr" domainjoined="0"><hw logical_cpus="4" physmemory="4" disk_type="2" sse="1" sse2="1" sse3="1" ssse3="1" sse41="1" sse42="1" avx="1"/><os platform="win" version="10.0.19045.4046" sp="" arch="x64" product_type="48" is_wip="0" is_in_lockdown_mode="0"/><oem product_manufacturer="DELL" product_name="DELL"/><exp etag=""r452t1+k2Tgq/HXzjvFNBRhopBWR9sbjXxqeUDH9uX0=""/><app appid="{F3C4FE00-EFD5-403B-9569-398A20F1BA4A}" version="1.3.185.17" nextversion="1.3.195.19" lang="es-419" brand="M100" client=""><event eventtype="2" eventresult="1" errorcode="0" extracode1="0" system_uptime_ticks="12278282823" install_time_ms="500"/></app></request> | |||
| (PID) Process: | (3236) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{176E3885-BF20-4882-8138-2BB412DAD4AB} |
| Operation: | write | Name: | PersistedPingTime |
Value: 133708134649860097 | |||
| (PID) Process: | (3236) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\proxy |
| Operation: | write | Name: | source |
Value: auto | |||
| (PID) Process: | (3236) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{176E3885-BF20-4882-8138-2BB412DAD4AB} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3236) MicrosoftEdgeUpdate.exe | Key: | \REGISTRY\A\{7a5b022b-7423-e0ed-5bf8-e16ed0631dc3}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (3236) MicrosoftEdgeUpdate.exe | Key: | \REGISTRY\A\{7a5b022b-7423-e0ed-5bf8-e16ed0631dc3}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1076) wermgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\IdentityCRL\ClockData |
| Operation: | write | Name: | ClockTimeSeconds |
Value: 22DBE56600000000 | |||
| (PID) Process: | (1076) wermgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\IdentityCRL\ClockData |
| Operation: | write | Name: | TickCount |
Value: 56E0120000000000 | |||
| (PID) Process: | (3236) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\UsageStats\Daily\Counts |
| Operation: | write | Name: | setup_uac_succeeded |
Value: 0300000000000000 | |||
Executable files
300
Suspicious files
5
Text files
9
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4980 | MicrosoftEdgeSetup.exe | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\psuser_64.dll | executable | |
MD5:72AA2974228D0D4E62A8E3C670DB1204 | SHA256:632762238CDB97D88C6527AD5D2AAD7A84C61550545458F69CE5EDB504E659C0 | |||
| 4980 | MicrosoftEdgeSetup.exe | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\MicrosoftEdgeUpdateOnDemand.exe | executable | |
MD5:B24A7473192E02CA5A8EF0A6CDF5A7FA | SHA256:2FB732A43AF16159B58EEA7950EE63FF6ED21EE78303C584FCC580F92D997BF5 | |||
| 4980 | MicrosoftEdgeSetup.exe | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\psmachine_64.dll | executable | |
MD5:AE6E84289F0264374BA3B54634FD1864 | SHA256:198FAF3C4107737679C6A057F1E661B5B8A15CFD39C1BECFE2EF9062A7F2F24B | |||
| 4980 | MicrosoftEdgeSetup.exe | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\MicrosoftEdgeUpdateComRegisterShell64.exe | executable | |
MD5:1D35F02C24D817CD9AE2B9BD75A4C135 | SHA256:0ABF4F0FE0033A56EBDAFF875B63CC083FD9C8628D2FB2AB5826D3C0C687B262 | |||
| 4980 | MicrosoftEdgeSetup.exe | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\psmachine_arm64.dll | executable | |
MD5:26A613B3E85F99F277C72E089BA55A96 | SHA256:81078F06FAE5DC44257EEFC39675449A4E8D9CEB4910750BABF0914F5361017D | |||
| 4980 | MicrosoftEdgeSetup.exe | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\psuser.dll | executable | |
MD5:33BF134B69D77316BD814D8904F27B35 | SHA256:55C9EB7C7FD62B2173F2203421E85DFAD845C169B1225FF4CA1A9E0CFFEA2B0D | |||
| 4980 | MicrosoftEdgeSetup.exe | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\MicrosoftEdgeUpdateCore.exe | executable | |
MD5:E468FE744CBAEBC00B08578F6C71FBC0 | SHA256:7C75C35F4222E83088DE98BA25595EB76013450FC959D7FEEFCAB592D1C9839F | |||
| 4980 | MicrosoftEdgeSetup.exe | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\psuser_arm64.dll | executable | |
MD5:2558A7A1D81BBF04E634BC07F89EE1AB | SHA256:72176E9B1DF519C63658E98BB4984CF93E5306C3EE221A2CF28FA0141D8DAB7D | |||
| 4980 | MicrosoftEdgeSetup.exe | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\MicrosoftEdgeComRegisterShellARM64.exe | executable | |
MD5:3A6B04122205EC351F8FBEF3E20F65C4 | SHA256:7BA65317643FBC0D03195BDEEBA318732823A91EF27F62483D5FC0ED3FEA4912 | |||
| 4980 | MicrosoftEdgeSetup.exe | C:\Users\admin\AppData\Local\Temp\EUA66A.tmp\psmachine.dll | executable | |
MD5:440CC4D0CE247CA6F5B9A3D30192B844 | SHA256:C5EC4633F80C54FE8D77BDE05A952B11B4B647A2FFC10E43D0370154780D21F7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
29
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1076 | wermgr.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6516 | svchost.exe | 20.44.239.154:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | SG | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.44.239.154:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | SG | unknown |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.44.239.154:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | SG | unknown |
4324 | svchost.exe | 20.44.239.154:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | SG | unknown |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3424 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3424 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |