| File name: | 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA |
| Full analysis: | https://app.any.run/tasks/12bfe648-59c5-4fff-aa76-4bb461b62b5f |
| Verdict: | Malicious activity |
| Analysis date: | December 20, 2024, 21:32:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | D520D42E38E4147C9CD8123C1403271B |
| SHA1: | B4E05C8461CCFAD76D3D2761883108E02C61C201 |
| SHA256: | 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA |
| SSDEEP: | 24576:ihVLBu7lJaFy7CBCxJ+G3k/jnfZ9HD5s/uiCEnzgfLN7JM515CqB0Wpdxrn5:ihVtu7lky7CBCxJ+G3k/jnfZ9HNs/uiD |
MALICIOUS
Executing a file with an untrusted certificate
- 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe (PID: 6368)
SUSPICIOUS
Executable content was dropped or overwritten
- 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe (PID: 6368)
Process drops legitimate windows executable
- 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe (PID: 6368)
Reads security settings of Internet Explorer
- 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe (PID: 6368)
INFO
Checks supported languages
- 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe (PID: 6368)
Reads the computer name
- 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe (PID: 6368)
The sample compiled with english language support
- 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe (PID: 6368)
Create files in a temporary directory
- 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe (PID: 6368)
The process uses the downloaded file
- 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe (PID: 6368)
Reads the machine GUID from the registry
- 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe (PID: 6368)
Reads security settings of Internet Explorer
- splwow64.exe (PID: 6648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (47.7) |
|---|---|---|
| .scr | | | Windows screen saver (22.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (11.3) |
| .exe | | | Win32 Executable (generic) (7.7) |
| .exe | | | Win16/32 Executable Delphi generic (3.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2086:04:24 23:21:57+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 692224 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaae5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Bloomberg L.P. |
| FileDescription: | blpprint |
| FileVersion: | 1.0.0.0 |
| InternalName: | blpprint.exe |
| LegalCopyright: | Copyright © Bloomberg L.P. 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | blpprint.exe |
| ProductName: | blpprint |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
124
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6368 | "C:\Users\admin\AppData\Local\Temp\13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe" | C:\Users\admin\AppData\Local\Temp\13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe | explorer.exe | ||||||||||||
User: admin Company: Bloomberg L.P. Integrity Level: MEDIUM Description: blpprint Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6648 | C:\WINDOWS\splwow64.exe 8192 | C:\Windows\splwow64.exe | — | 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Print driver host for applications Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
673
Read events
671
Write events
2
Delete events
0
Modification events
| (PID) Process: | (6648) splwow64.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\splwow64.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 8E5E130000000000 | |||
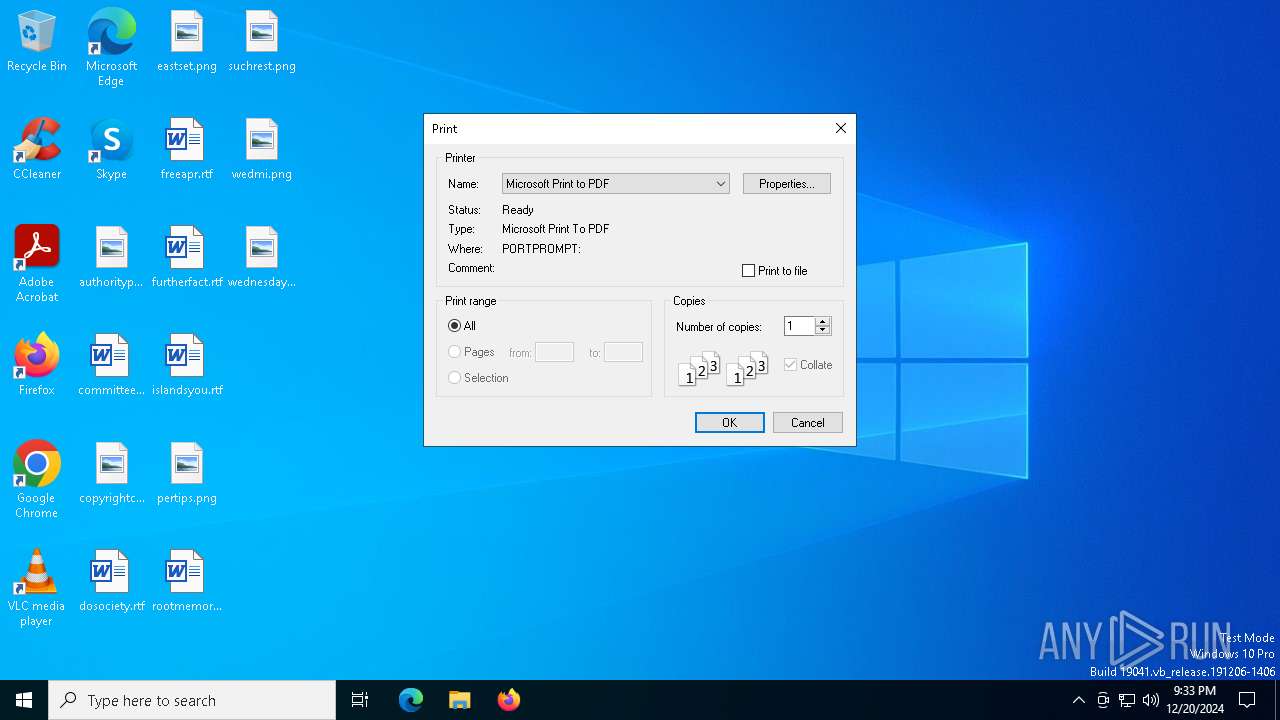
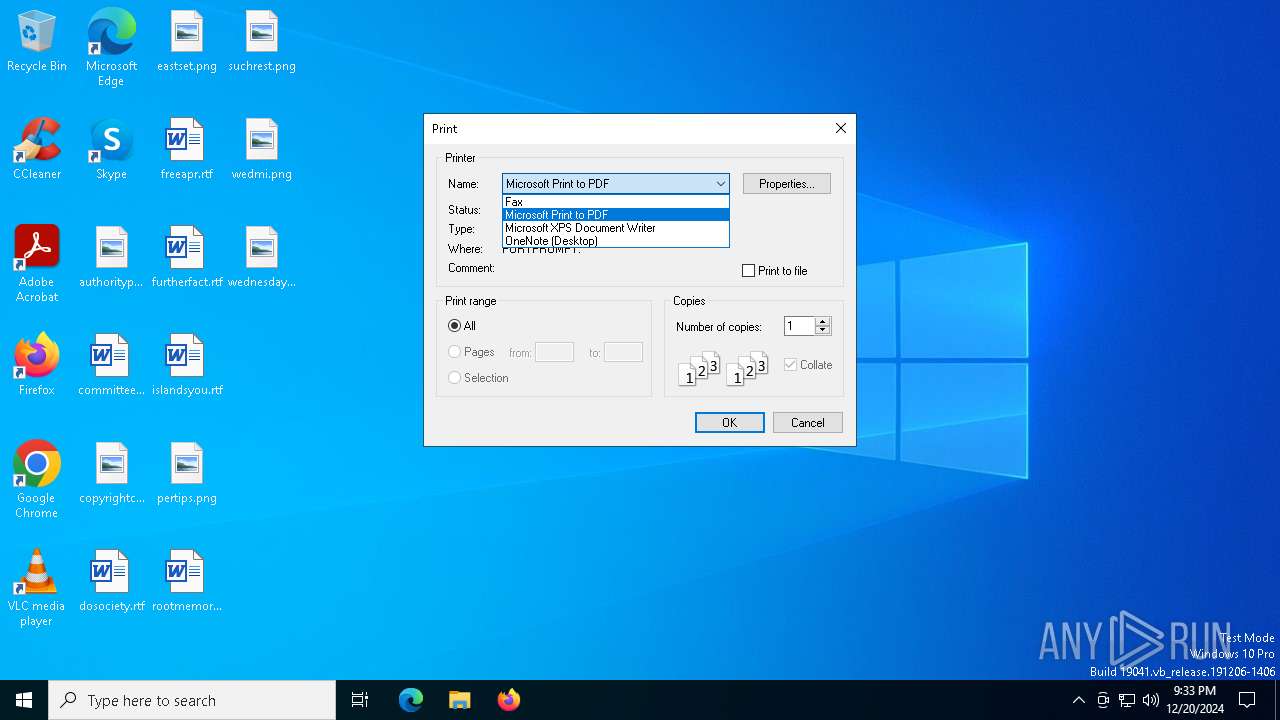
| (PID) Process: | (6368) 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Bloomberg L.P.\BlpPrint |
| Operation: | write | Name: | Default Printer |
Value: Microsoft Print to PDF | |||
Executable files
2
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6368 | 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe | C:\Users\admin\AppData\Local\Temp\Costura\2407F32B1C03D31B53213CF8B76C77D7\32\webview2loader.dll | executable | |
MD5:A362185B50F302563EF03EE1CBF68FD2 | SHA256:CD5BD9CF068C312ECC6CE09E1C413B68BA12393581AE3869DAEF6B22F70A0CD6 | |||
| 6368 | 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe | C:\Users\admin\AppData\Local\Temp\Costura\2407F32B1C03D31B53213CF8B76C77D7\32\microsoft.web.webview2.core.dll | executable | |
MD5:3D9465D5161AC2AB5A83265935514349 | SHA256:24D1F432632C971456E6DB676F609772B98D0CF3D3A5450C78D3DBB75744399E | |||
| 6368 | 13BF8B1CECCBB8FA418B61D20B28464AEA68B7F34DA01C4F8926C37E2A233FEA.exe | C:\Users\admin\AppData\Local\Temp\Bloomberg\Log\blpprint.20241220.log | text | |
MD5:8F236C0DEEB2AF994FD6C1C3C1CC293A | SHA256:6E43EFA9DF67BD5B9E1A6134C113041AF89F4F3490847C4637A7D49ABBEF84FD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
23
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.181:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.181:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.181:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 23.212.110.179:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| unknown |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| unknown |