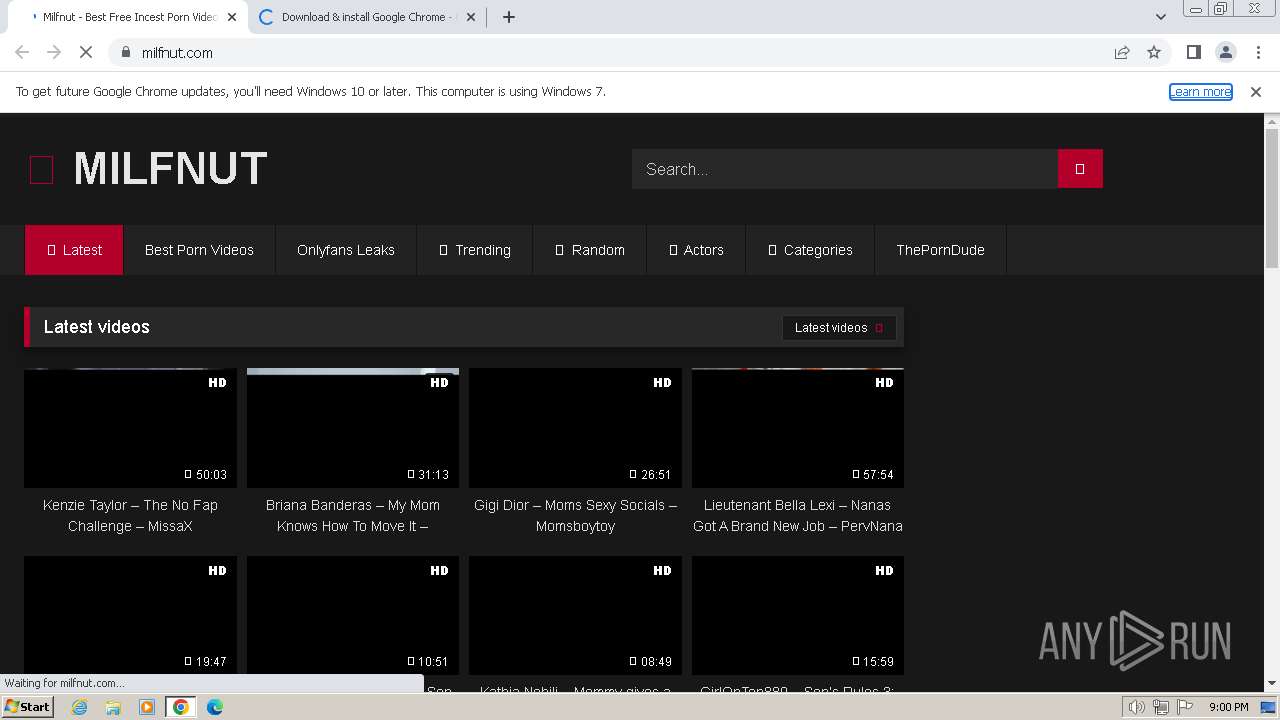
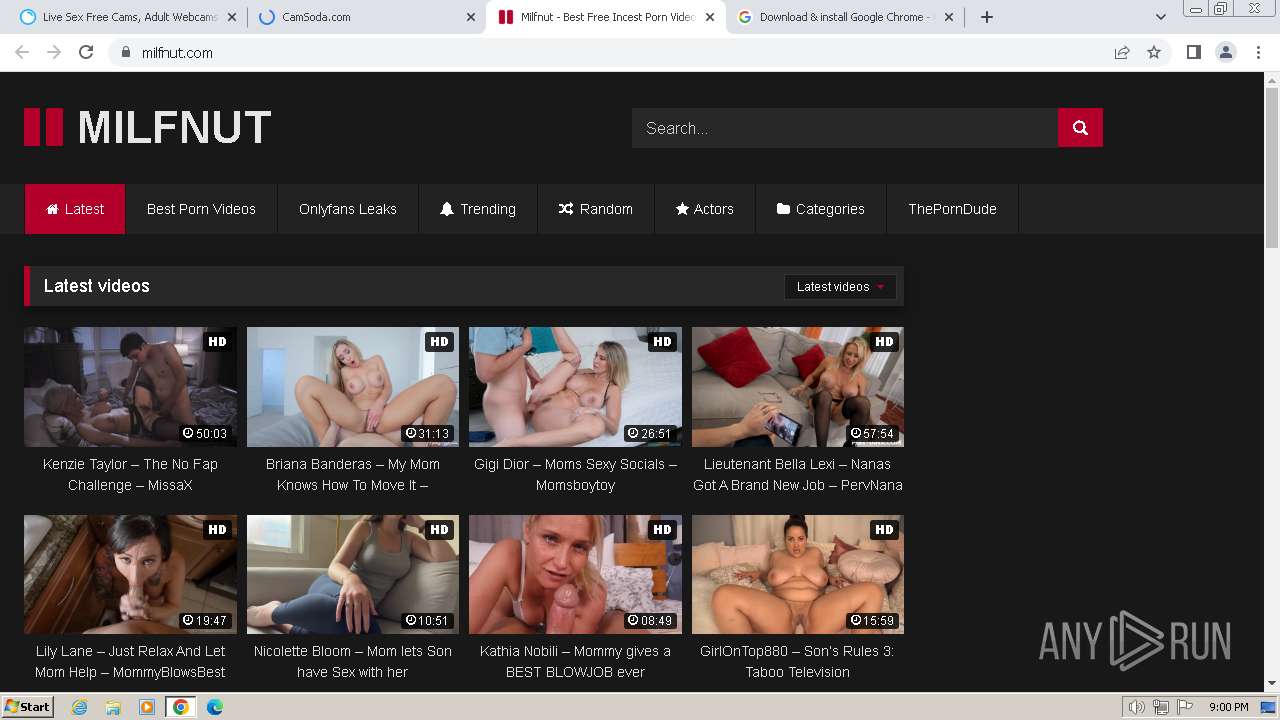
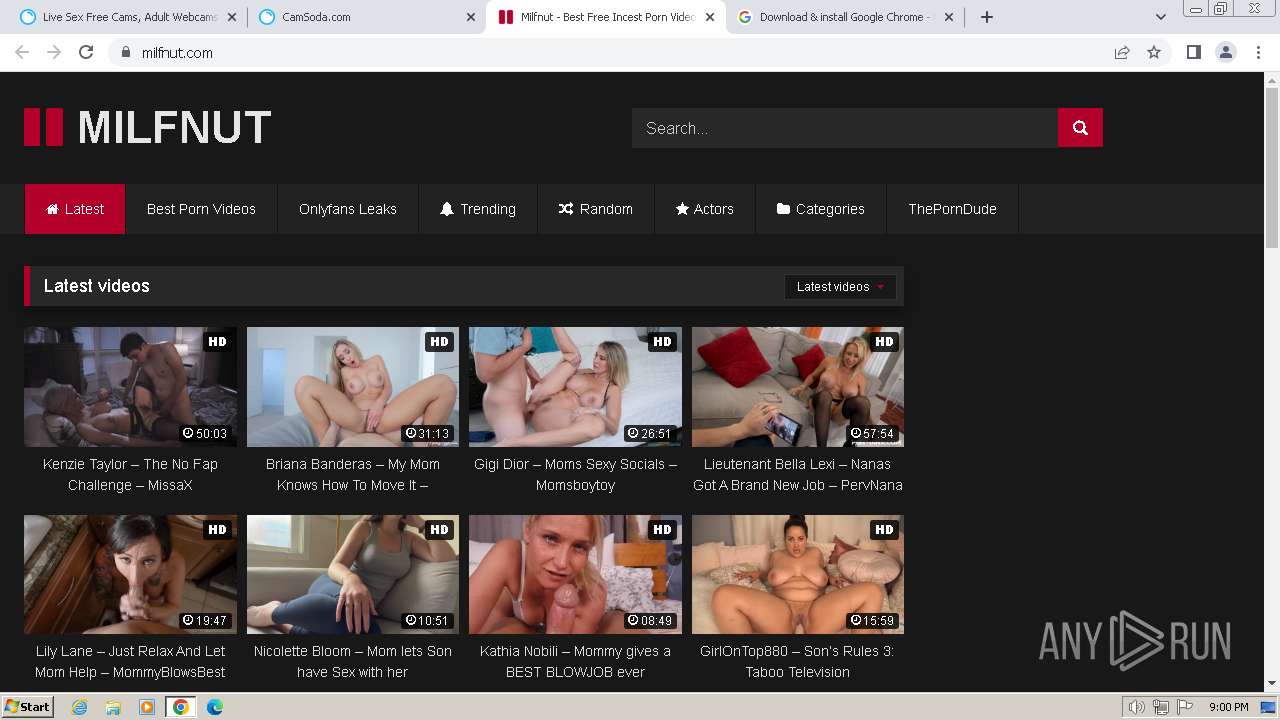
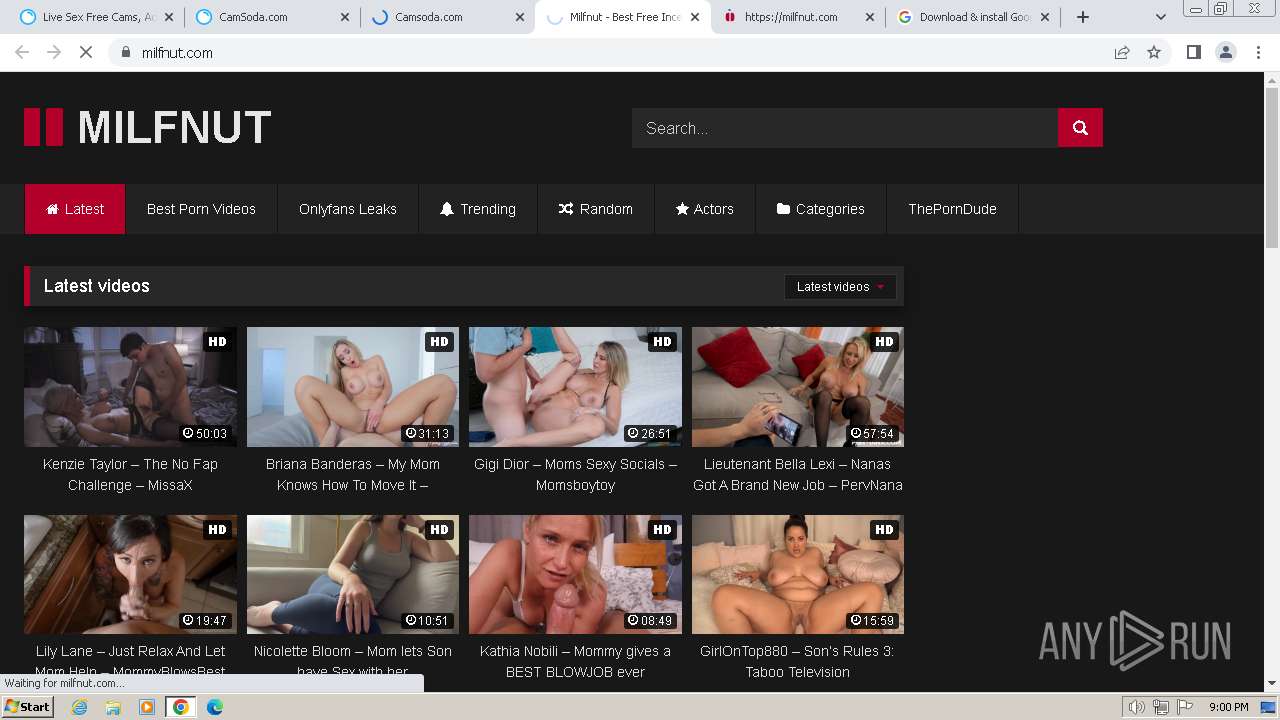
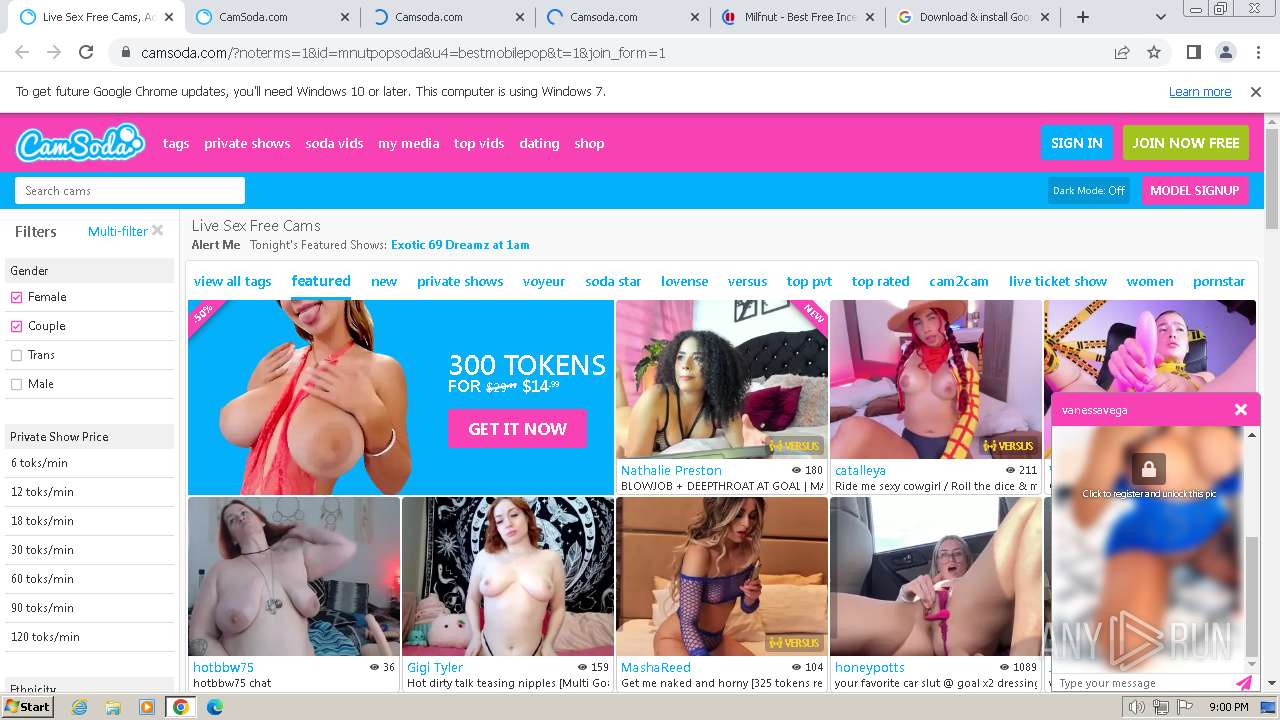
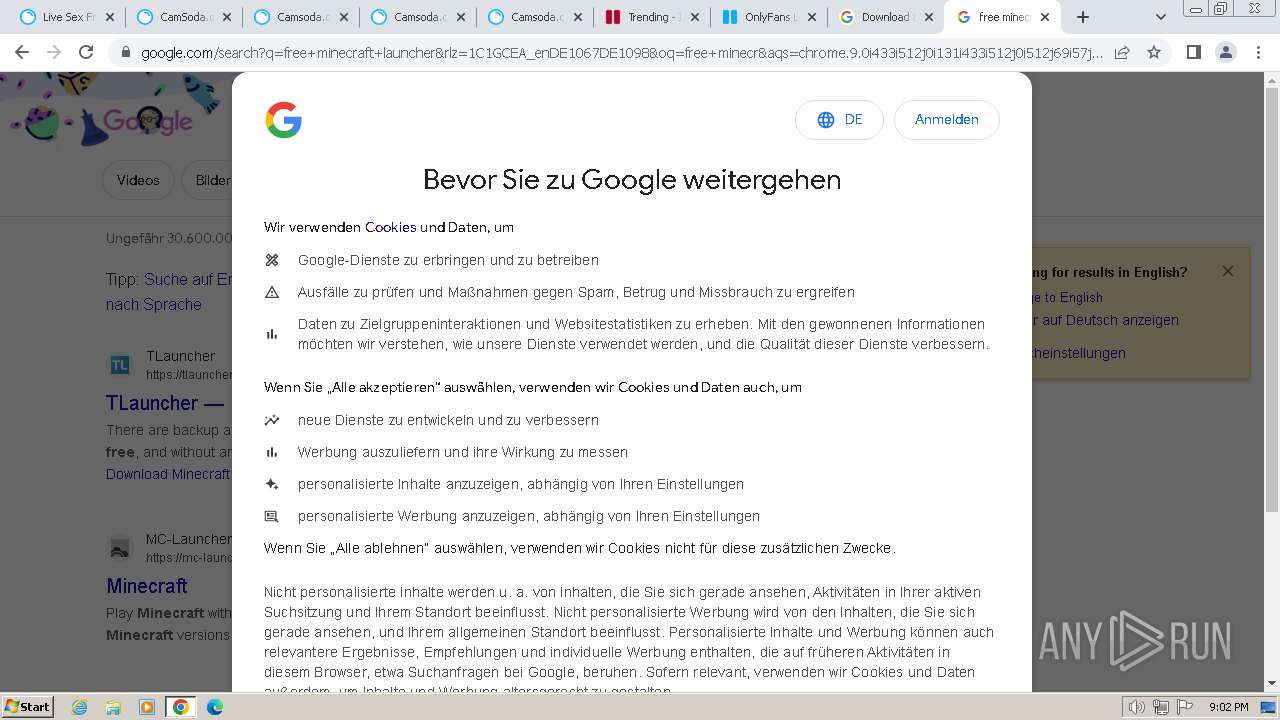
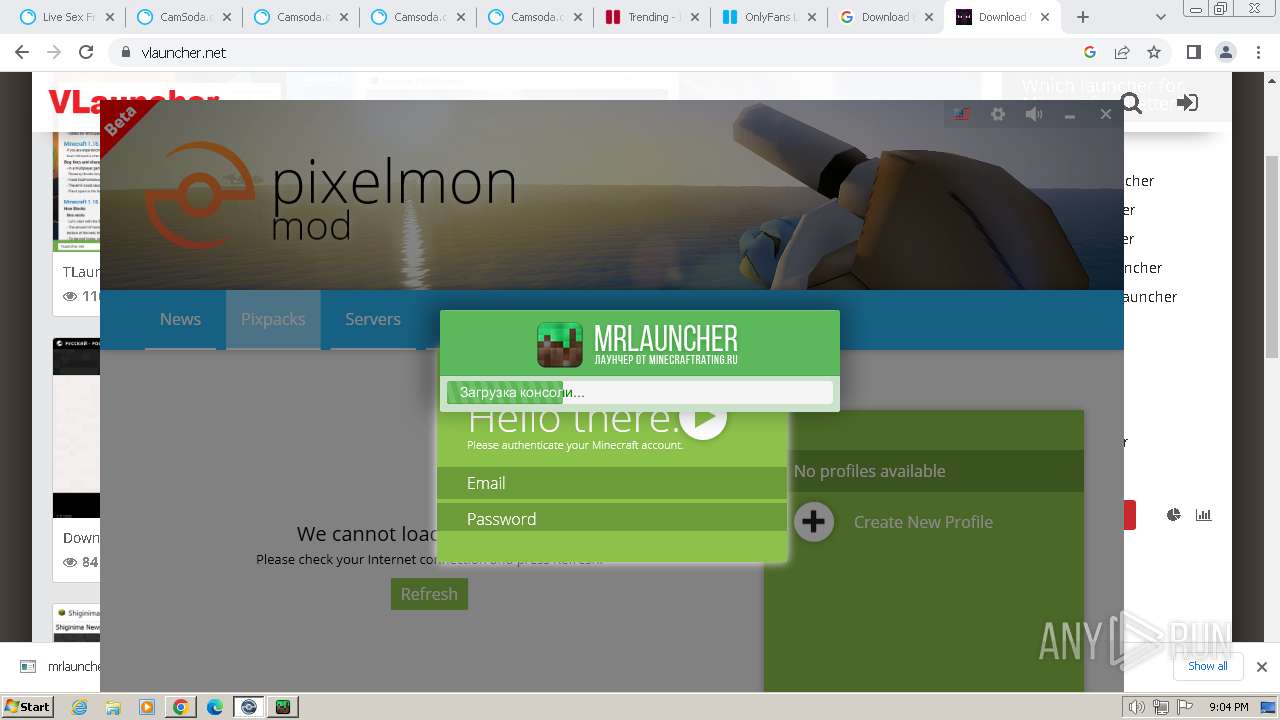
| URL: | https://milfnut.com/ |
| Full analysis: | https://app.any.run/tasks/dbce76eb-223b-45bd-9479-e6903317188a |
| Verdict: | Malicious activity |
| Analysis date: | February 23, 2024, 20:59:51 |
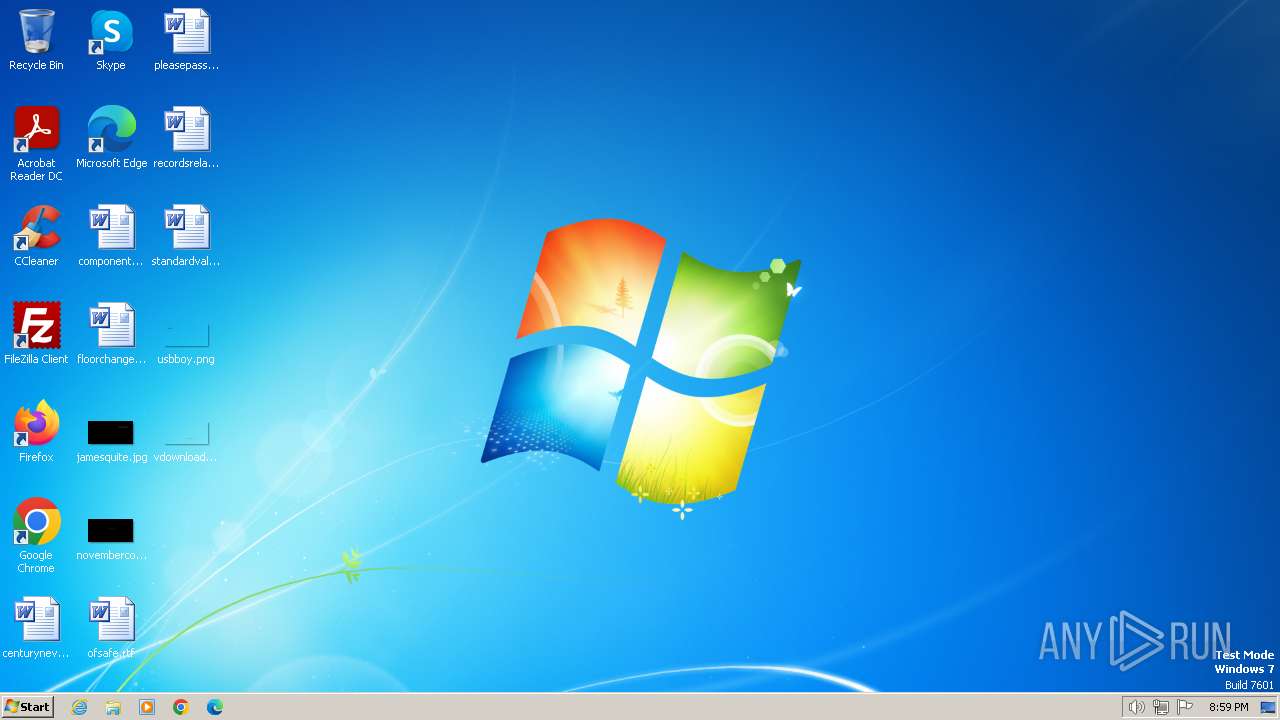
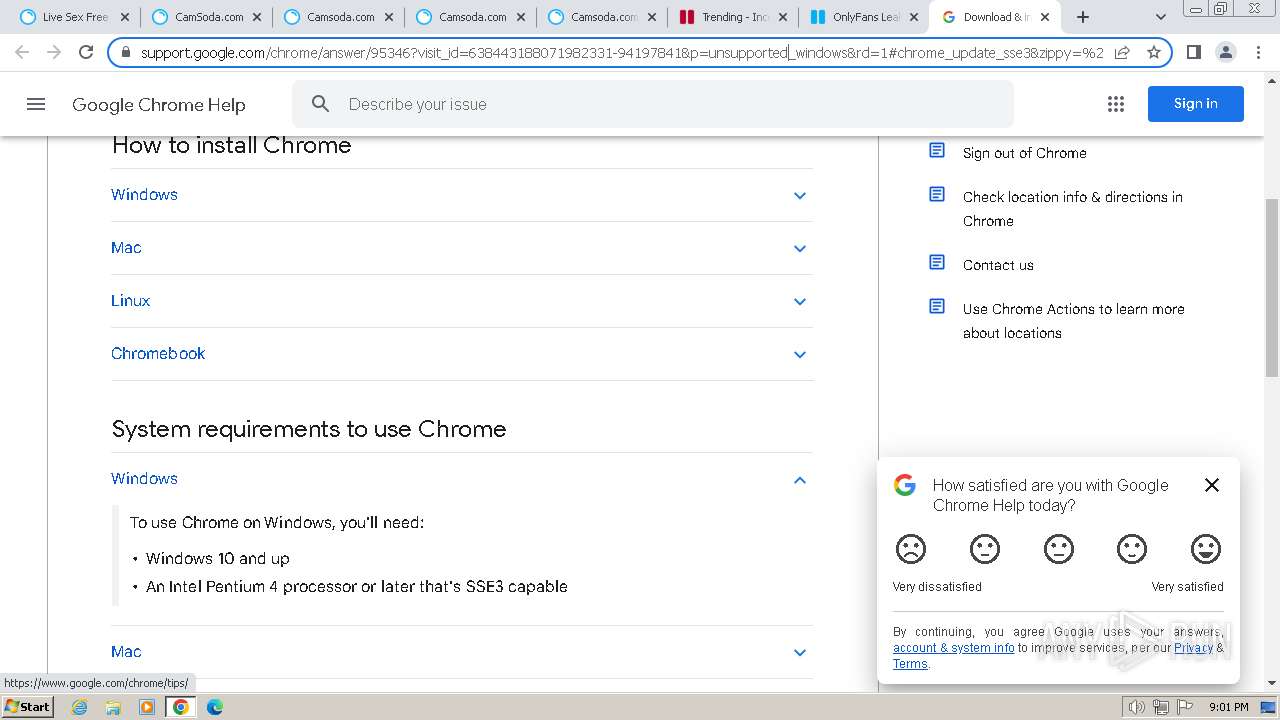
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A87587ACEEEDC8679B701F36294867D8 |
| SHA1: | 9396641655A5CAB491F9D85515CFBB427BAF31F0 |
| SHA256: | 13BB61069B45C47116900C87B3C211F0522163E60CEDDB4EED9014106D670F26 |
| SSDEEP: | 3:N8YR:2a |
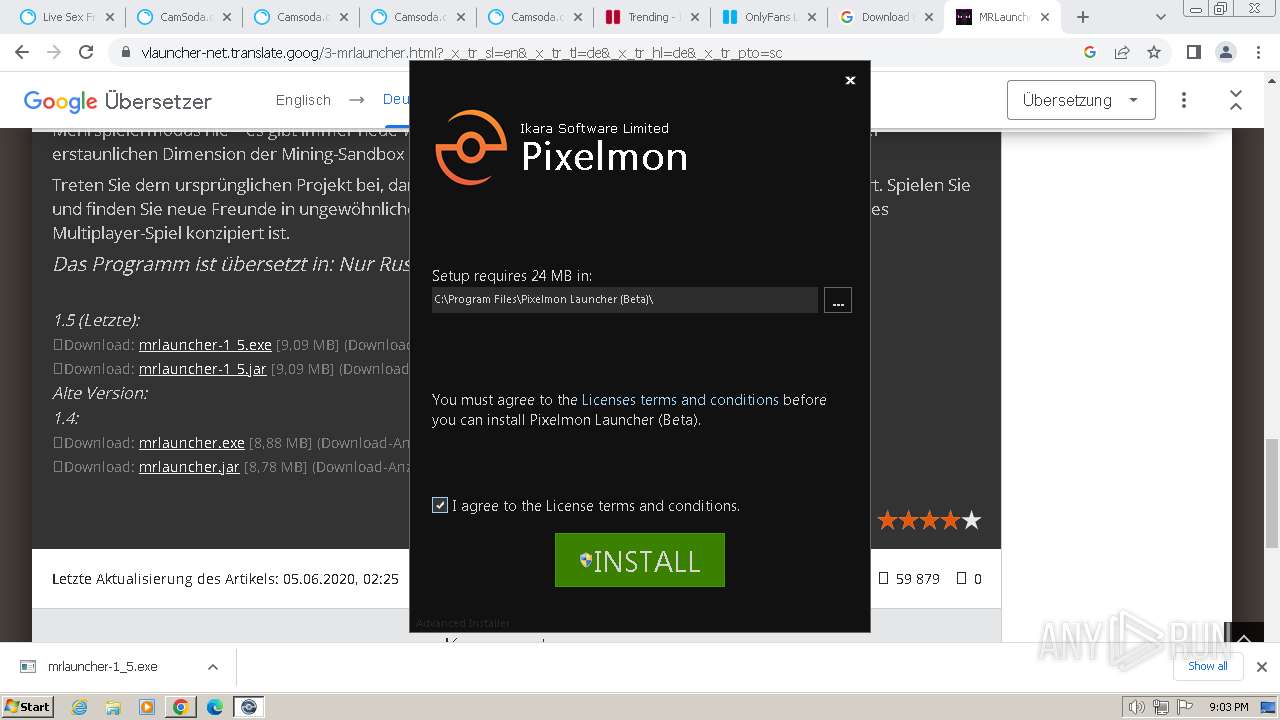
MALICIOUS
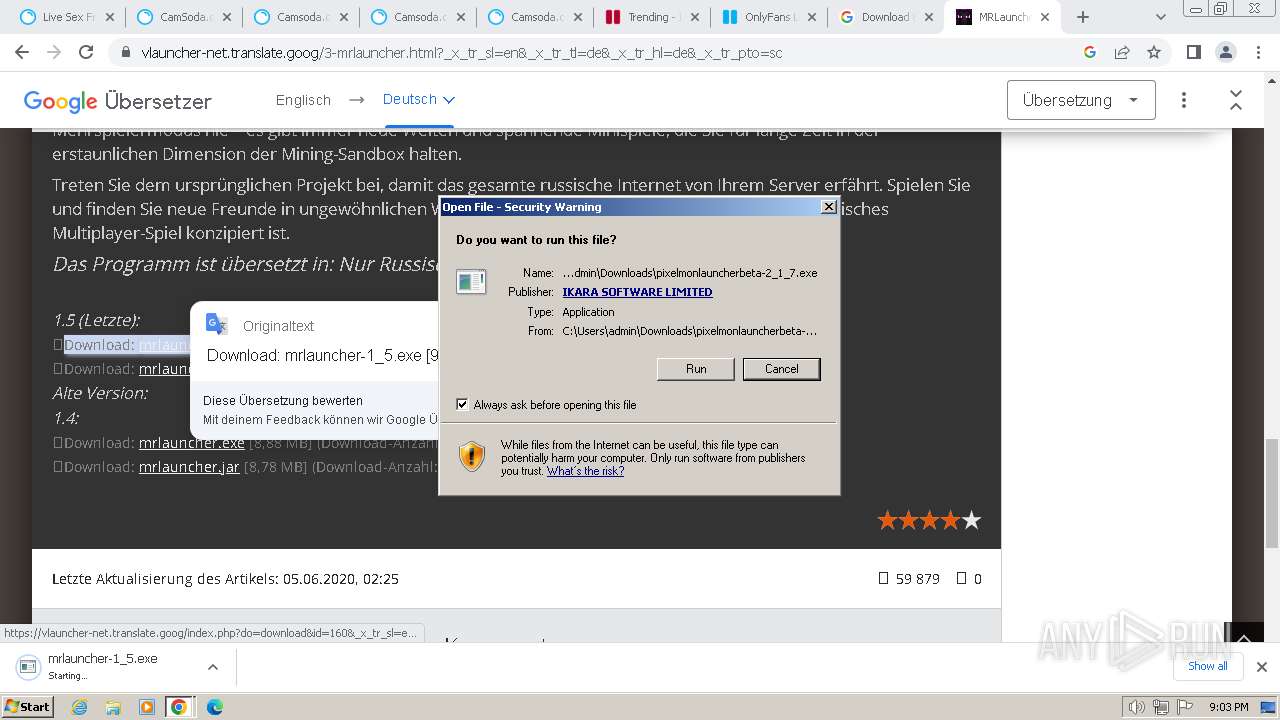
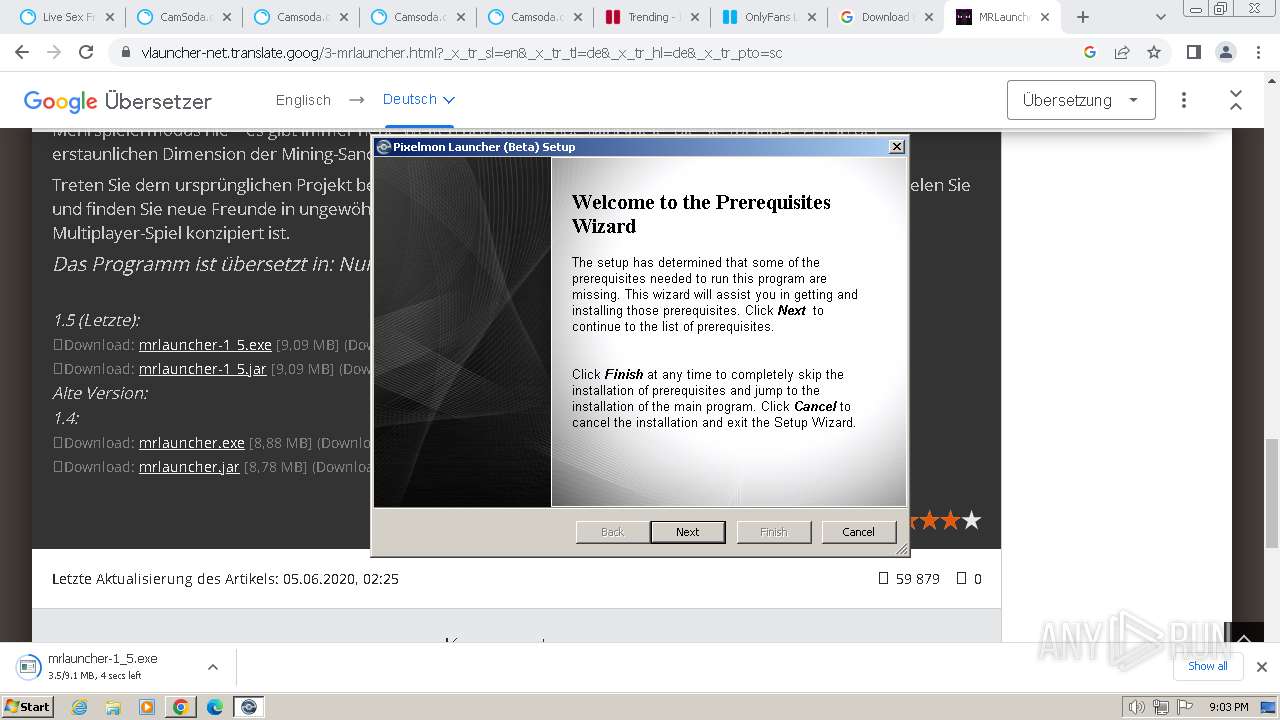
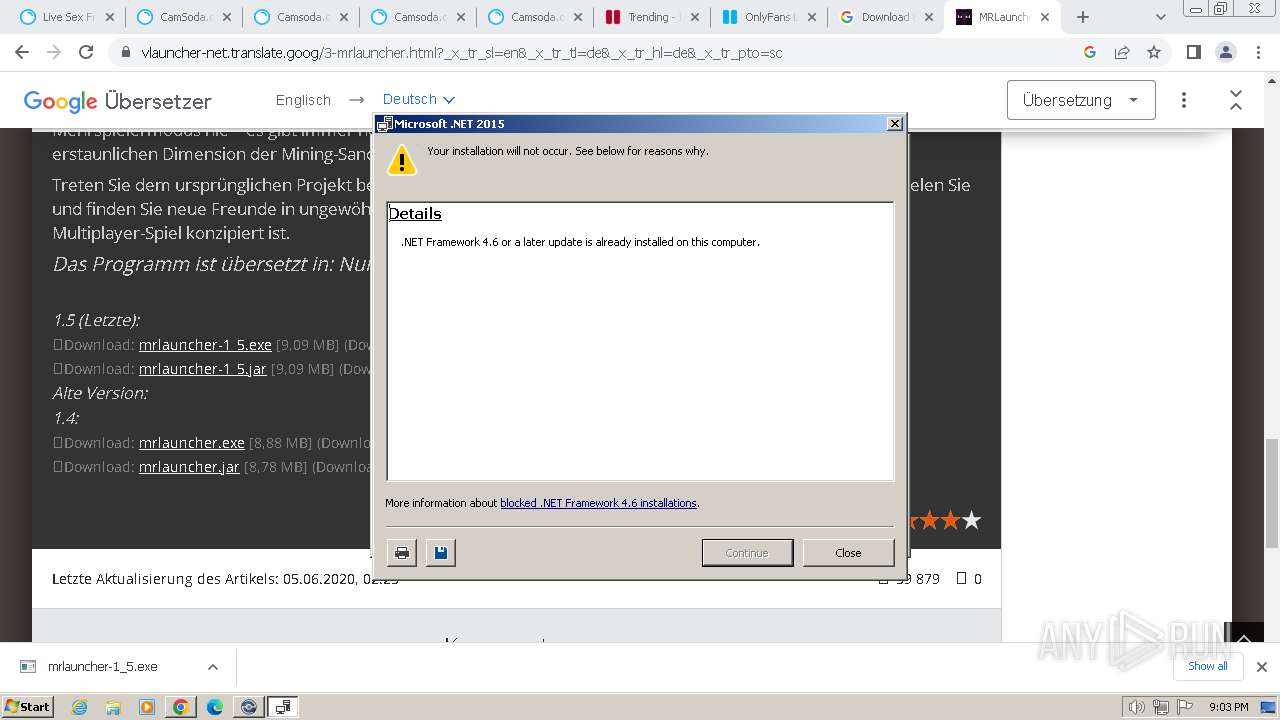
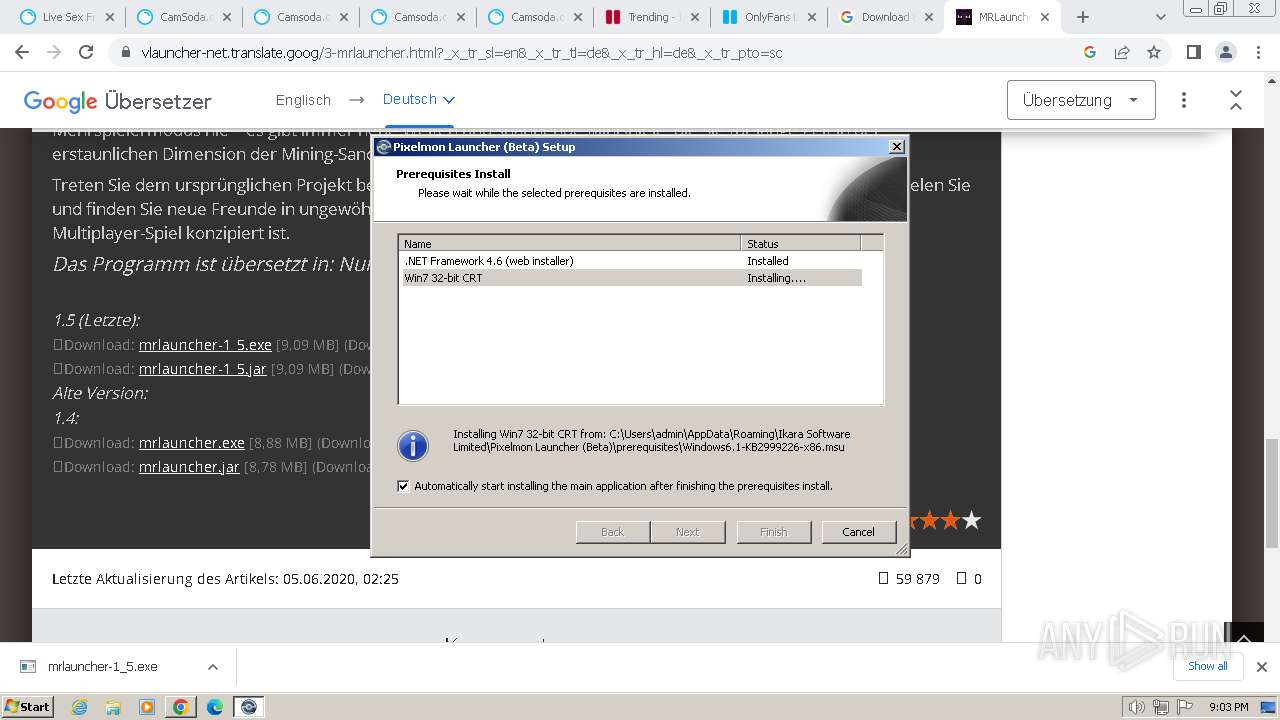
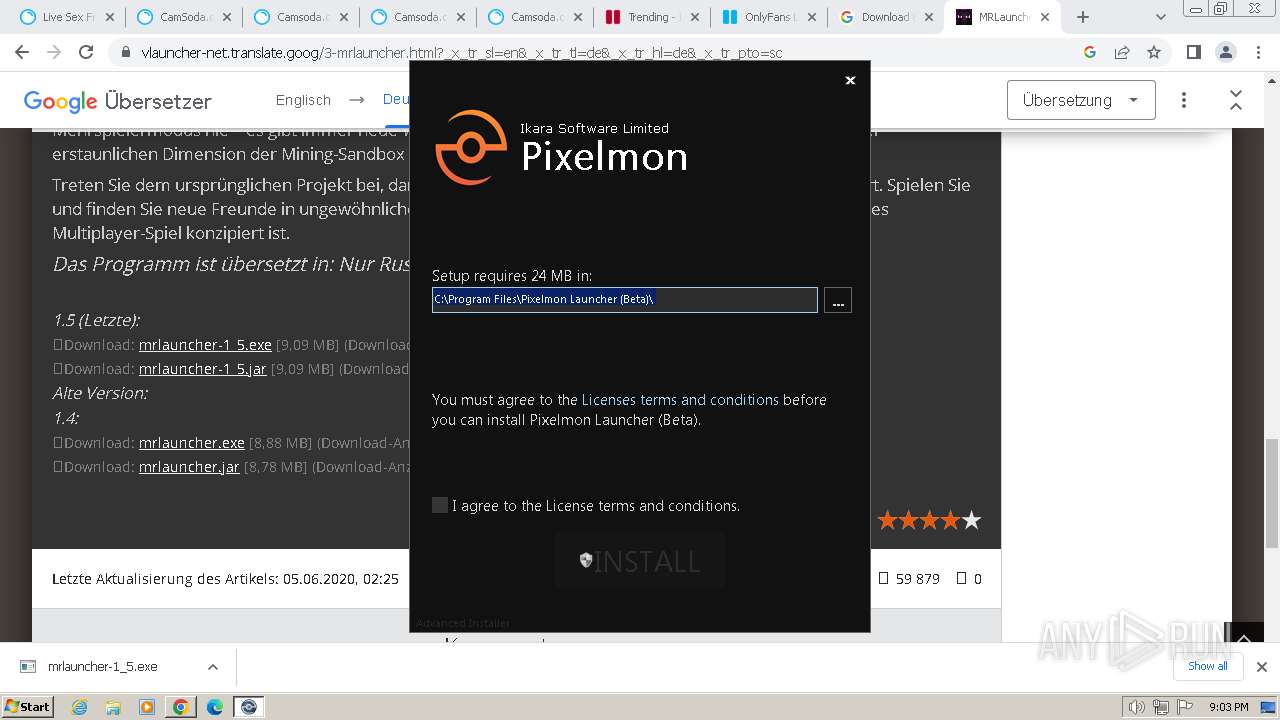
Drops the executable file immediately after the start
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
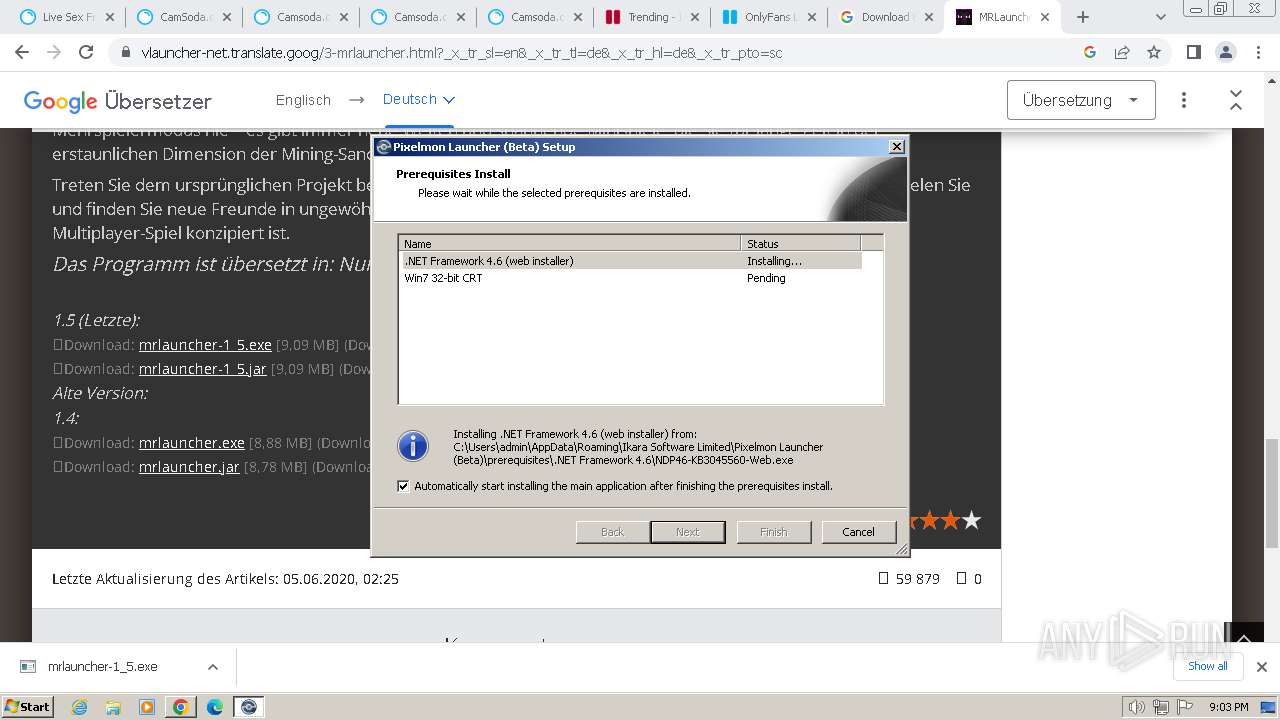
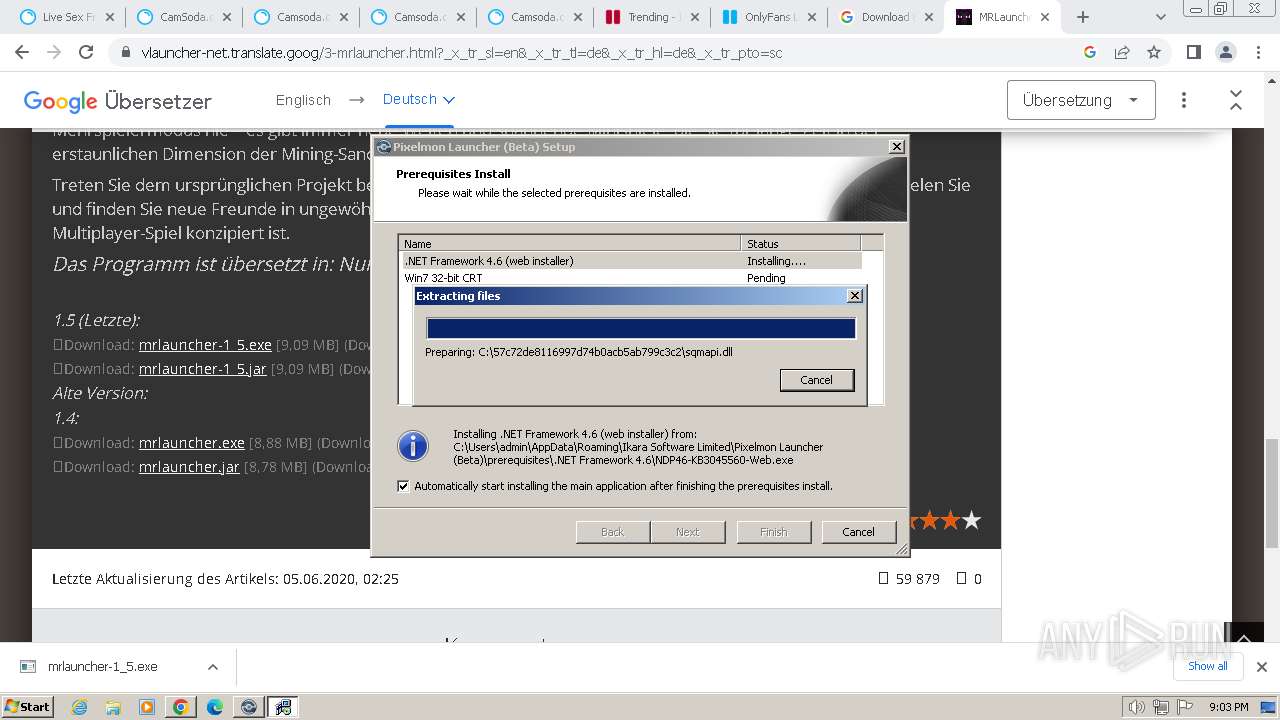
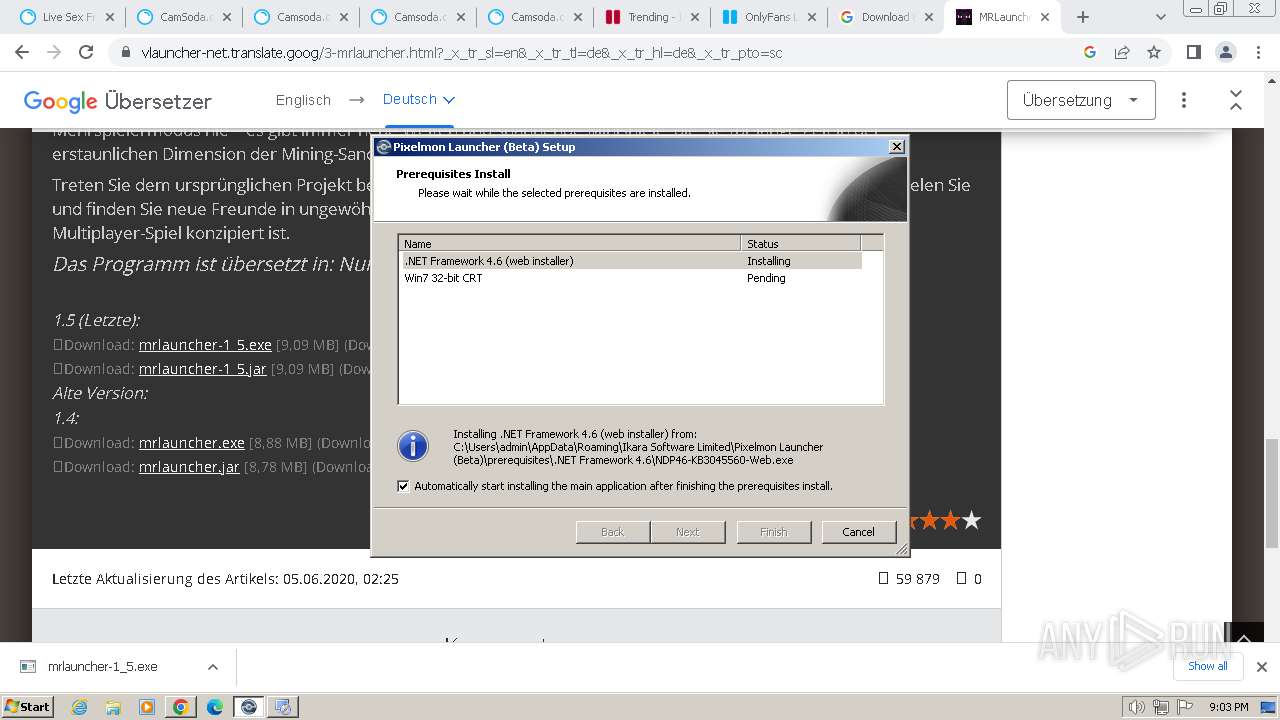
- NDP46-KB3045560-Web.exe (PID: 2204)
- pixelmonlauncherbeta-2_1_7.exe (PID: 1844)
- javaw.exe (PID: 268)
Changes the autorun value in the registry
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
SUSPICIOUS
Process drops legitimate windows executable
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- NDP46-KB3045560-Web.exe (PID: 2204)
Executable content was dropped or overwritten
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- NDP46-KB3045560-Web.exe (PID: 2204)
- pixelmonlauncherbeta-2_1_7.exe (PID: 1844)
- javaw.exe (PID: 268)
Reads the Internet Settings
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- PixelmonLauncherUpdater.exe (PID: 2804)
- WMIC.exe (PID: 2760)
Reads security settings of Internet Explorer
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- pixelmonlauncherbeta-2_1_7.exe (PID: 1844)
- PixelmonLauncherUpdater.exe (PID: 2804)
Checks Windows Trust Settings
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- pixelmonlauncherbeta-2_1_7.exe (PID: 1844)
- PixelmonLauncherUpdater.exe (PID: 2804)
Reads settings of System Certificates
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- pixelmonlauncherbeta-2_1_7.exe (PID: 1844)
- PixelmonLauncherUpdater.exe (PID: 2804)
Reads the Windows owner or organization settings
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- pixelmonlauncherbeta-2_1_7.exe (PID: 1844)
Reads Internet Explorer settings
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
Executes as Windows Service
- VSSVC.exe (PID: 1336)
Starts CMD.EXE for commands execution
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- cmd.exe (PID: 2660)
- cmd.exe (PID: 1608)
Executing commands from a ".bat" file
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- cmd.exe (PID: 1608)
- cmd.exe (PID: 2660)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 2660)
- cmd.exe (PID: 1608)
Application launched itself
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- cmd.exe (PID: 1608)
- cmd.exe (PID: 2660)
Process requests binary or script from the Internet
- javaw.exe (PID: 268)
Uses WMIC.EXE to obtain BIOS management information
- javaw.exe (PID: 268)
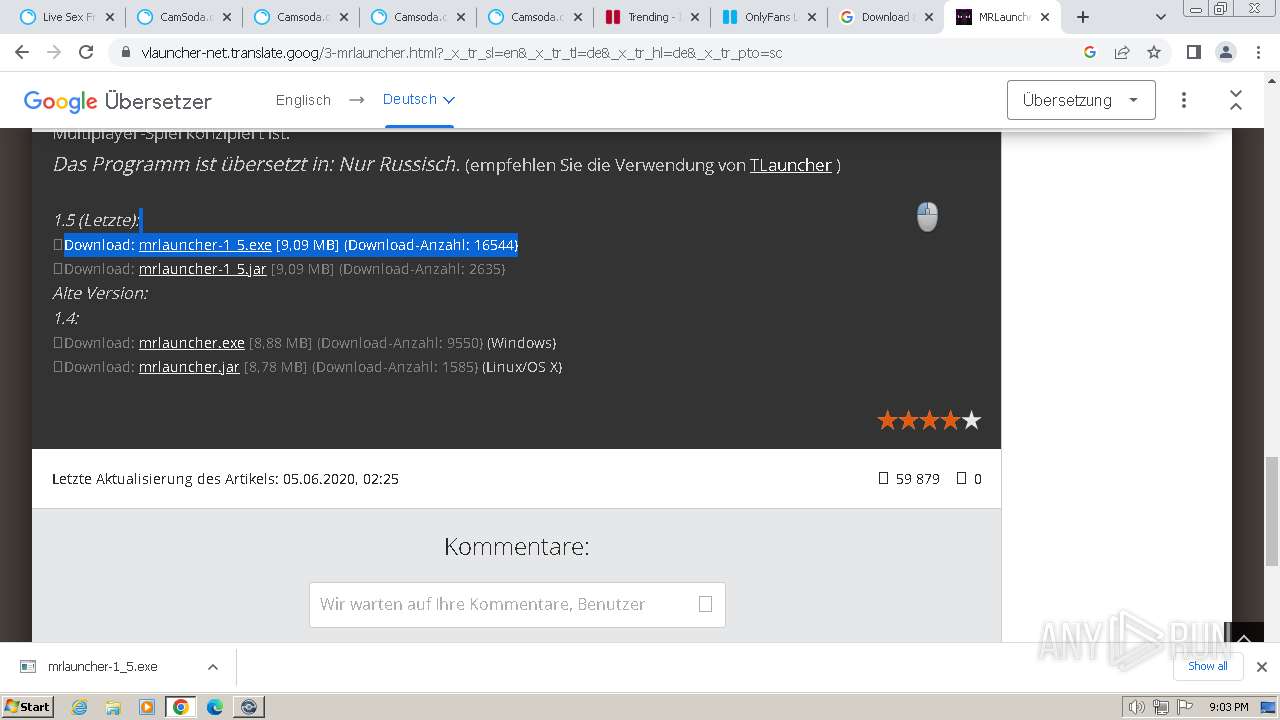
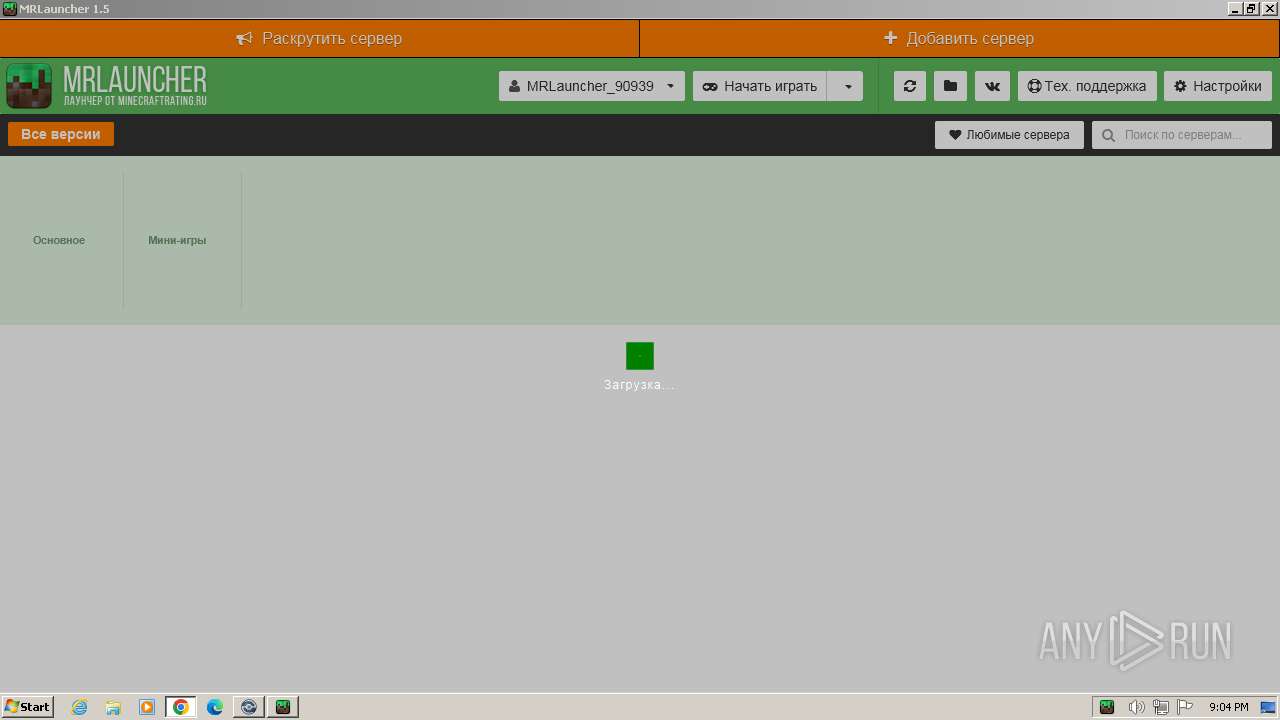
Checks for Java to be installed
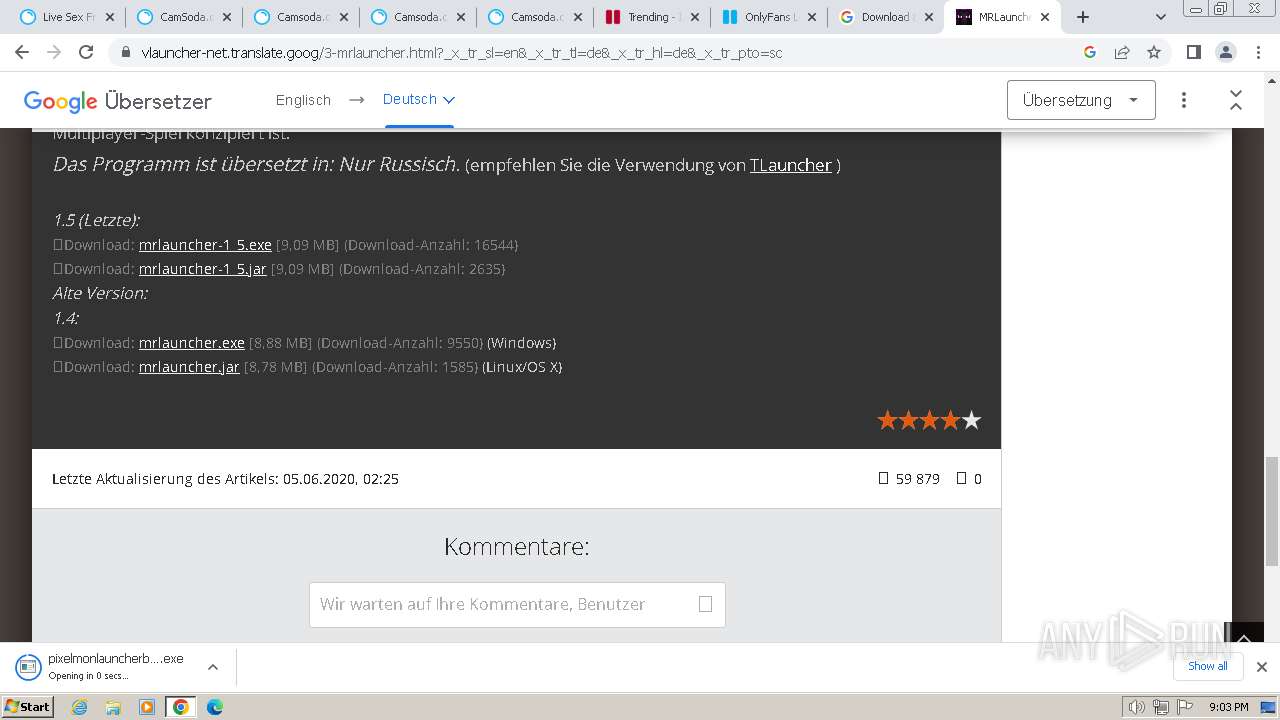
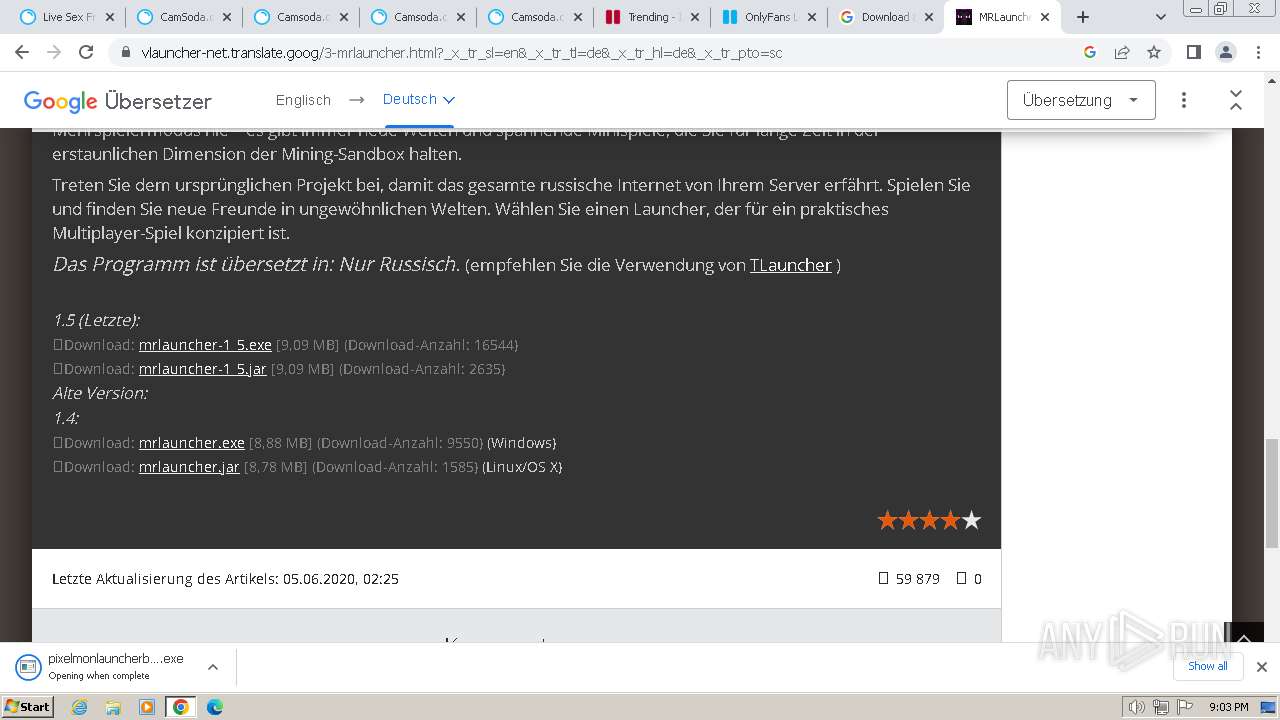
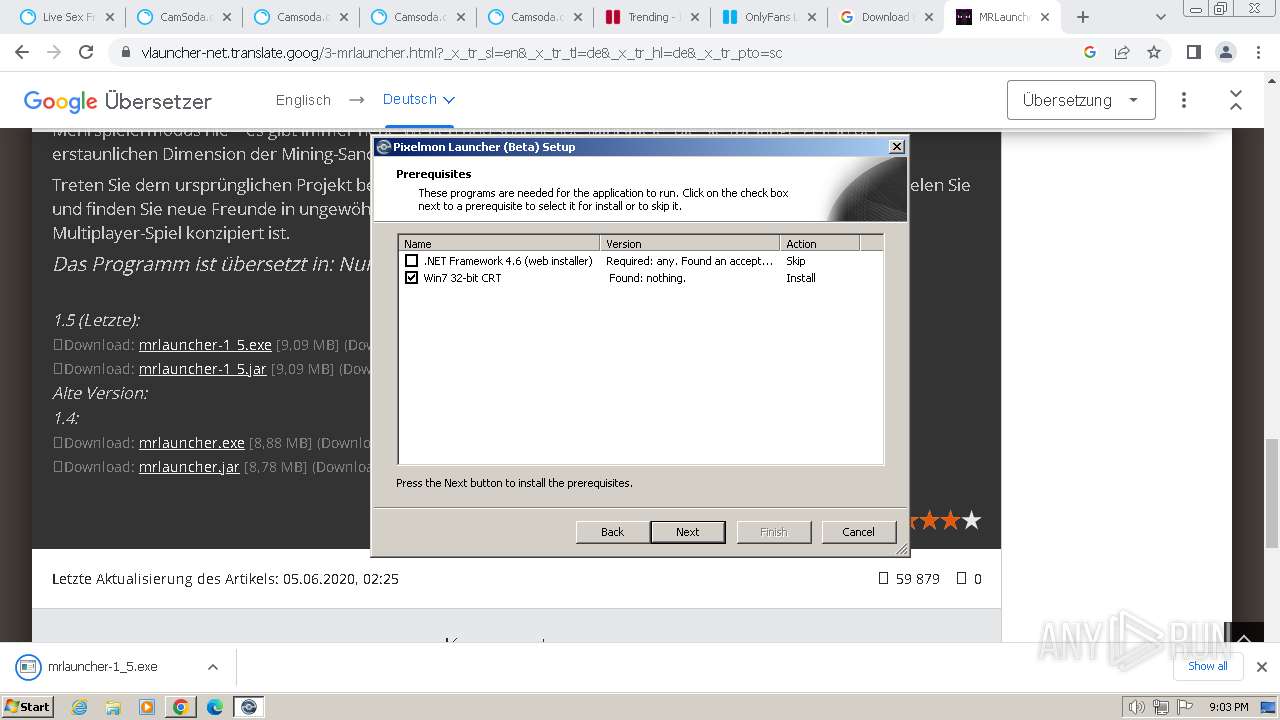
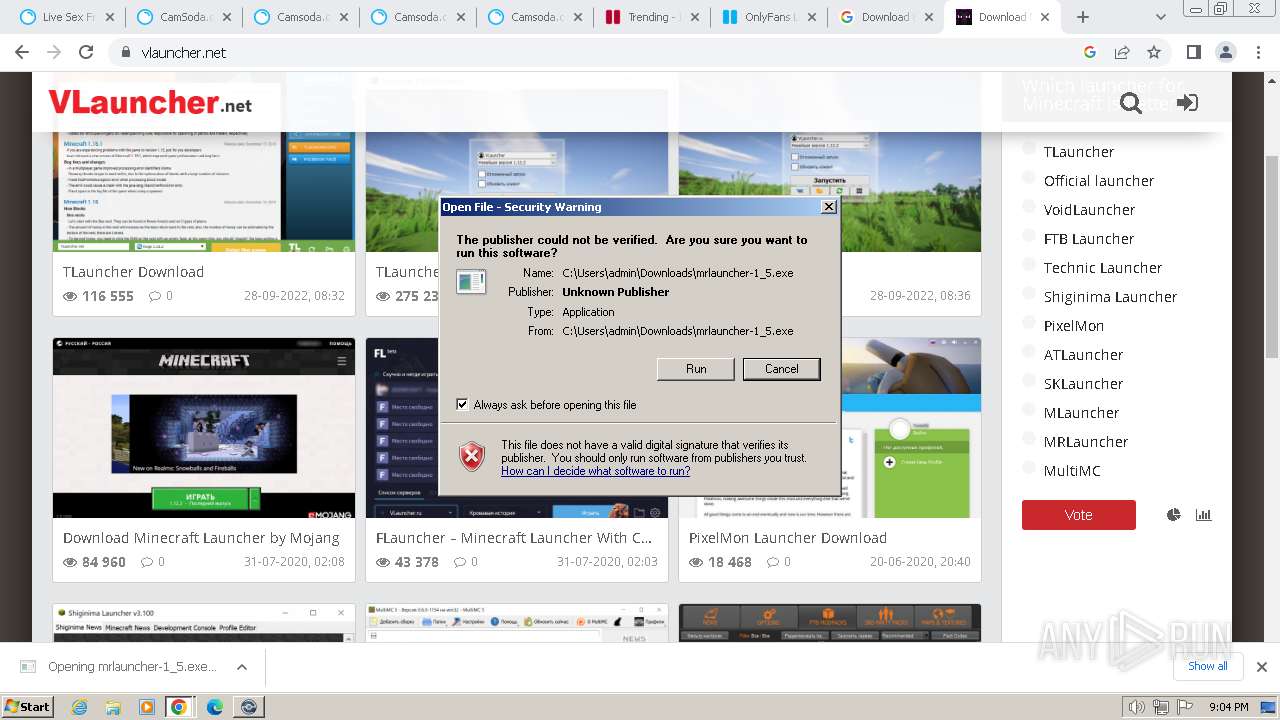
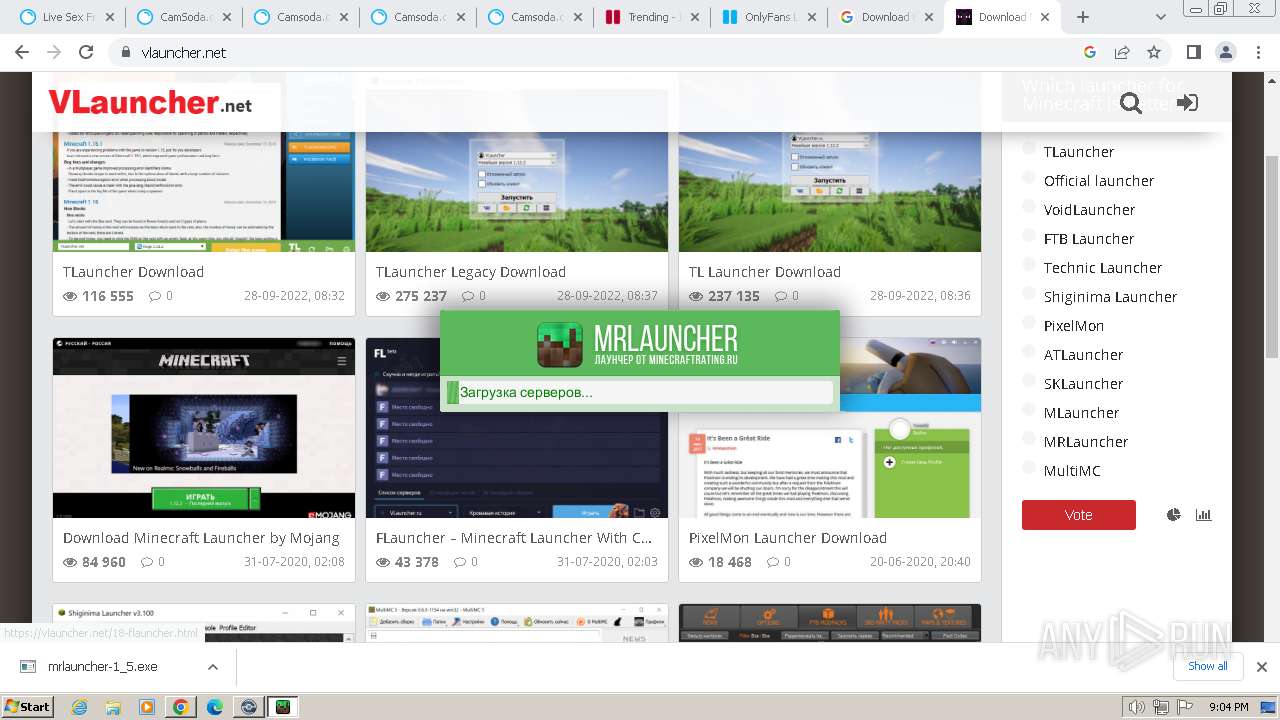
- mrlauncher-1_5.exe (PID: 2572)
INFO
Checks supported languages
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- NDP46-KB3045560-Web.exe (PID: 2204)
- Setup.exe (PID: 3616)
- pixelmonlauncherbeta-2_1_7.exe (PID: 1844)
- PixelmonLauncherUpdater.exe (PID: 2804)
- javaw.exe (PID: 268)
- mrlauncher-1_5.exe (PID: 2572)
Reads the computer name
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- NDP46-KB3045560-Web.exe (PID: 2204)
- Setup.exe (PID: 3616)
- pixelmonlauncherbeta-2_1_7.exe (PID: 1844)
- PixelmonLauncherUpdater.exe (PID: 2804)
- javaw.exe (PID: 268)
The process uses the downloaded file
- chrome.exe (PID: 2836)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 2296)
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
Connects to unusual port
- chrome.exe (PID: 3228)
Reads the machine GUID from the registry
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- NDP46-KB3045560-Web.exe (PID: 2204)
- pixelmonlauncherbeta-2_1_7.exe (PID: 1844)
- PixelmonLauncherUpdater.exe (PID: 2804)
- javaw.exe (PID: 268)
Create files in a temporary directory
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- NDP46-KB3045560-Web.exe (PID: 2204)
- Setup.exe (PID: 3616)
- javaw.exe (PID: 268)
Executable content was dropped or overwritten
- chrome.exe (PID: 3672)
Drops the executable file immediately after the start
- chrome.exe (PID: 3672)
Creates files or folders in the user directory
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- PixelmonLauncherUpdater.exe (PID: 2804)
- javaw.exe (PID: 268)
Reads Environment values
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- pixelmonlauncherbeta-2_1_7.exe (PID: 1844)
- PixelmonLauncherUpdater.exe (PID: 2804)
Application launched itself
- chrome.exe (PID: 3672)
Reads CPU info
- Setup.exe (PID: 3616)
Reads the software policy settings
- pixelmonlauncherbeta-2_1_7.exe (PID: 128)
- pixelmonlauncherbeta-2_1_7.exe (PID: 1844)
- PixelmonLauncherUpdater.exe (PID: 2804)
Creates files in the program directory
- pixelmonlauncherbeta-2_1_7.exe (PID: 1844)
- PixelmonLauncherUpdater.exe (PID: 2804)
- javaw.exe (PID: 268)
Checks proxy server information
- PixelmonLauncherUpdater.exe (PID: 2804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
134
Monitored processes
76
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Users\admin\Downloads\pixelmonlauncherbeta-2_1_7.exe" | C:\Users\admin\Downloads\pixelmonlauncherbeta-2_1_7.exe | chrome.exe | ||||||||||||
User: admin Company: Ikara Software Limited Integrity Level: MEDIUM Description: This installer database contains the logic and data required to install Pixelmon Launcher (Beta). Exit code: 0 Version: 2.1.7 Modules
| |||||||||||||||
| 268 | ATTRIB -r "\\?\C:\Users\admin\AppData\Roaming\IKARAS~1\PIXELM~1.7\install\PIXELM~1.MSI" | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 268 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -Xms368m -Xmx368m -jar "C:\Users\admin\Downloads\mrlauncher-1_5.exe" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | mrlauncher-1_5.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=51 --mojo-platform-channel-handle=5596 --field-trial-handle=1160,i,4918540821898735775,1574969296272029837,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=4264 --field-trial-handle=1160,i,4918540821898735775,1574969296272029837,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=1948 --field-trial-handle=1160,i,4918540821898735775,1574969296272029837,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --mojo-platform-channel-handle=4108 --field-trial-handle=1160,i,4918540821898735775,1574969296272029837,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=5320 --field-trial-handle=1160,i,4918540821898735775,1574969296272029837,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=5572 --field-trial-handle=1160,i,4918540821898735775,1574969296272029837,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=3412 --field-trial-handle=1160,i,4918540821898735775,1574969296272029837,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
33 741
Read events
33 355
Write events
362
Delete events
24
Modification events
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3672) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
53
Suspicious files
51
Text files
366
Unknown types
72
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17f6a4.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF17f78f.TMP | text | |
MD5:C383FD120B14BB0E98E99C1BCC9B43F6 | SHA256:56A3A5EACBD28BEE1CF8C1D0052321A5C27EE858BEF7B2FA1DE20806A0823CC1 | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF17f869.TMP | text | |
MD5:B36B68CE4A71A5BFAF89A4D1CC07893F | SHA256:6422CC04455EF100D67FD9F299AACFEF3BA4F77D0FA1D2440D89E7D1CF65EBBC | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF180867.TMP | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF17f6b4.TMP | text | |
MD5:05CF4C3C5148DA6355D3561A9EAA5E8A | SHA256:8D720243F6876898E4F197C8867C4CEE69F1C7335C55B8A29C120B1028D93E41 | |||
| 3672 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF17f6b4.TMP | text | |
MD5:ADB669AB4CD1C63883C64FB0DBA2C7DA | SHA256:18BFF89047EC5B122573D089B3DC7A7DD14A5A7A515B2D8141584B41E723253F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
251
DNS requests
376
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | unknown |
2804 | PixelmonLauncherUpdater.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9ae4df6a91664ea6 | GB | — | — | unknown |
2804 | PixelmonLauncherUpdater.exe | GET | 302 | 104.22.68.118:80 | http://download.nodecdn.net/containers/pixelmon/launcher/updatesbeta.txt | unknown | html | 145 b | unknown |
1584 | PixelmonLauncher.exe | GET | 403 | 172.67.82.228:80 | http://pixelmonmod.com/api/launcher/news/launcher_feed.min.php | US | html | 5.85 Kb | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 3.07 Kb | unknown |
2804 | PixelmonLauncherUpdater.exe | GET | 301 | 172.67.82.228:80 | http://pixelmonmod.com/ | US | — | — | unknown |
2804 | PixelmonLauncherUpdater.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | binary | 1.47 Kb | unknown |
268 | javaw.exe | GET | 403 | 172.67.70.194:80 | http://minecraftrating.ru/mrlauncher_api/database_mrlauncher.s3db | US | text | 16 b | unknown |
268 | javaw.exe | GET | 403 | 172.67.70.194:80 | http://minecraftrating.ru/mrlauncher_api/database_mrlauncher_multi.s3db | US | text | 16 b | unknown |
268 | javaw.exe | GET | 404 | 104.20.64.88:80 | http://repo.tlauncher.org/update/downloads/versions/new3/versions/versions.json | unknown | html | 1.57 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3228 | chrome.exe | 142.251.173.84:443 | accounts.google.com | GOOGLE | US | unknown |
3672 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
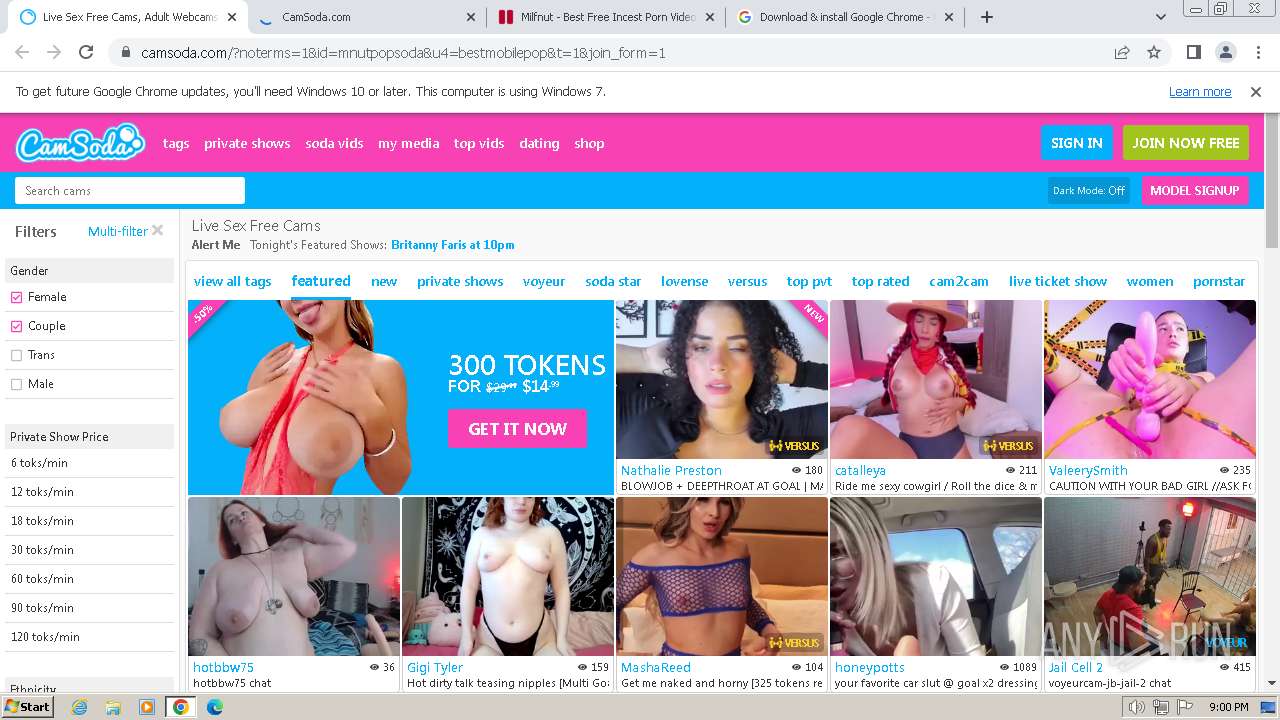
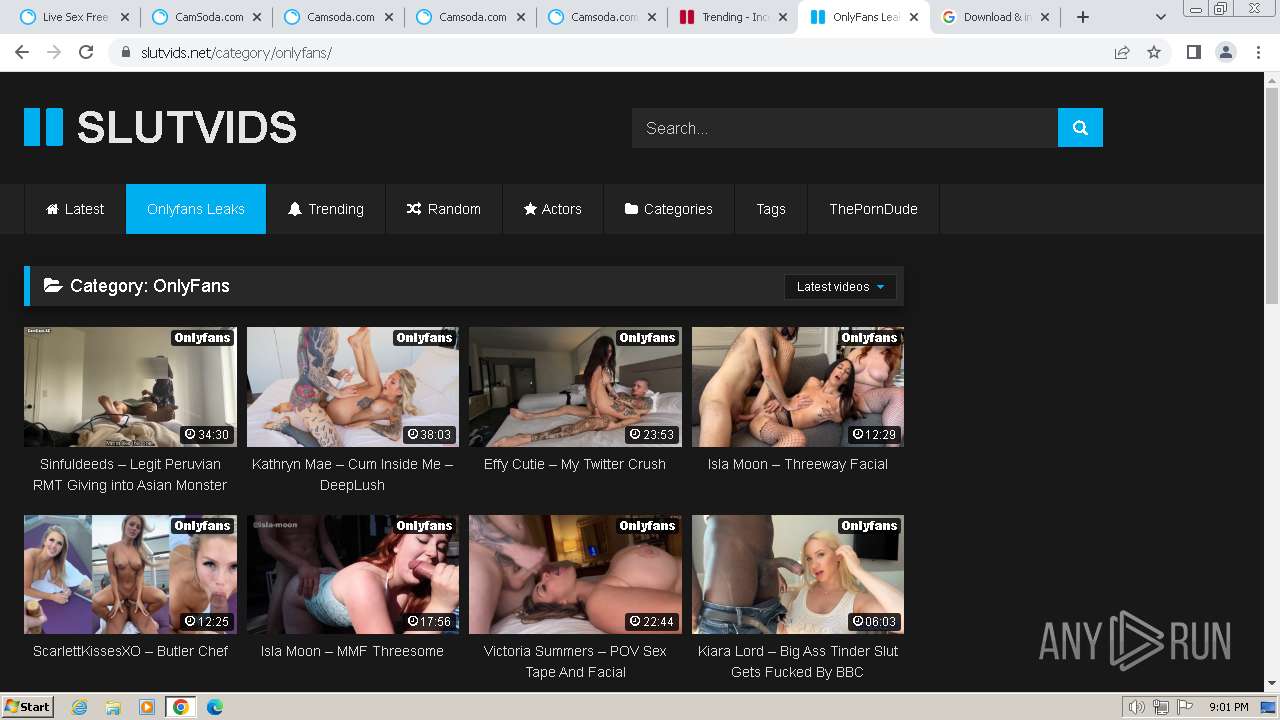
3228 | chrome.exe | 185.178.208.182:443 | milfnut.com | Ddos-guard Ltd | RU | unknown |
3228 | chrome.exe | 142.250.184.228:443 | www.google.com | GOOGLE | US | whitelisted |
3228 | chrome.exe | 142.250.184.238:443 | support.google.com | GOOGLE | US | whitelisted |
3228 | chrome.exe | 142.250.186.42:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
3228 | chrome.exe | 142.250.185.202:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
milfnut.com |
| unknown |
www.google.com |
| whitelisted |
support.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
storage.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3228 | chrome.exe | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3228 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
3228 | chrome.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
3228 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
3228 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
268 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
268 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
Setup.exe | The operation completed successfully.
|