| File name: | 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe |
| Full analysis: | https://app.any.run/tasks/3eba0bf1-6353-41af-b636-97890f54f0f8 |
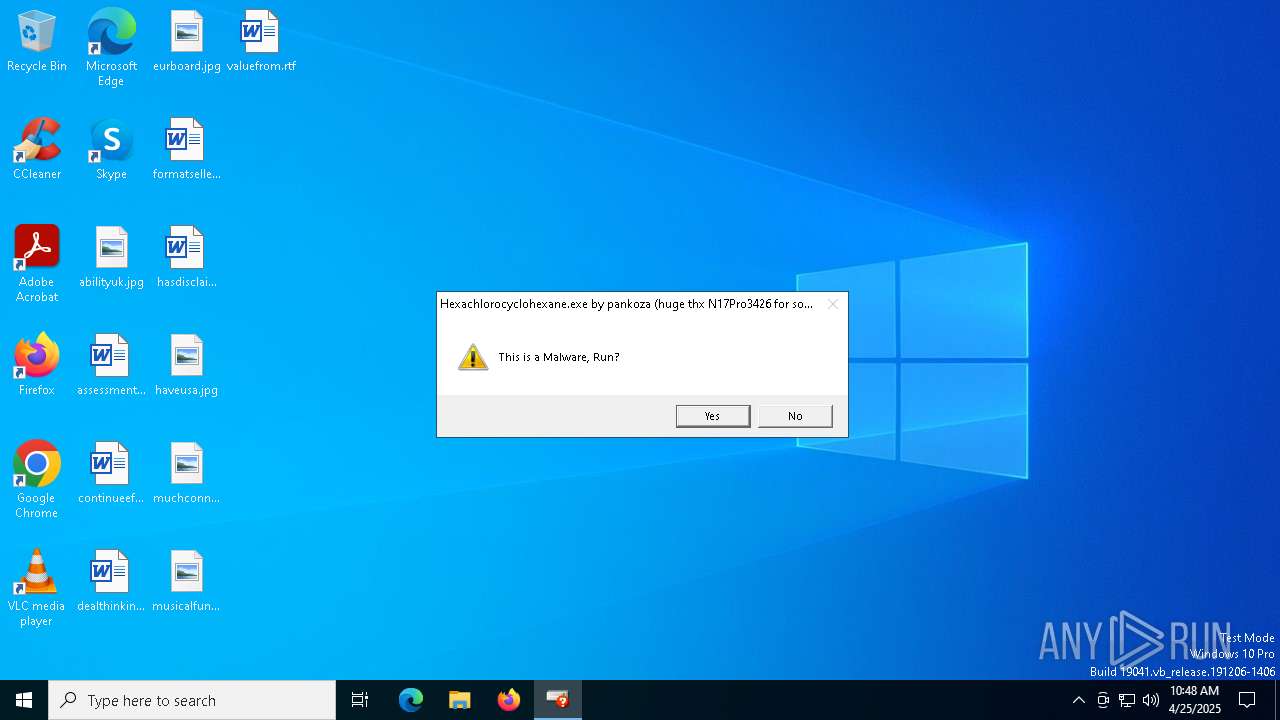
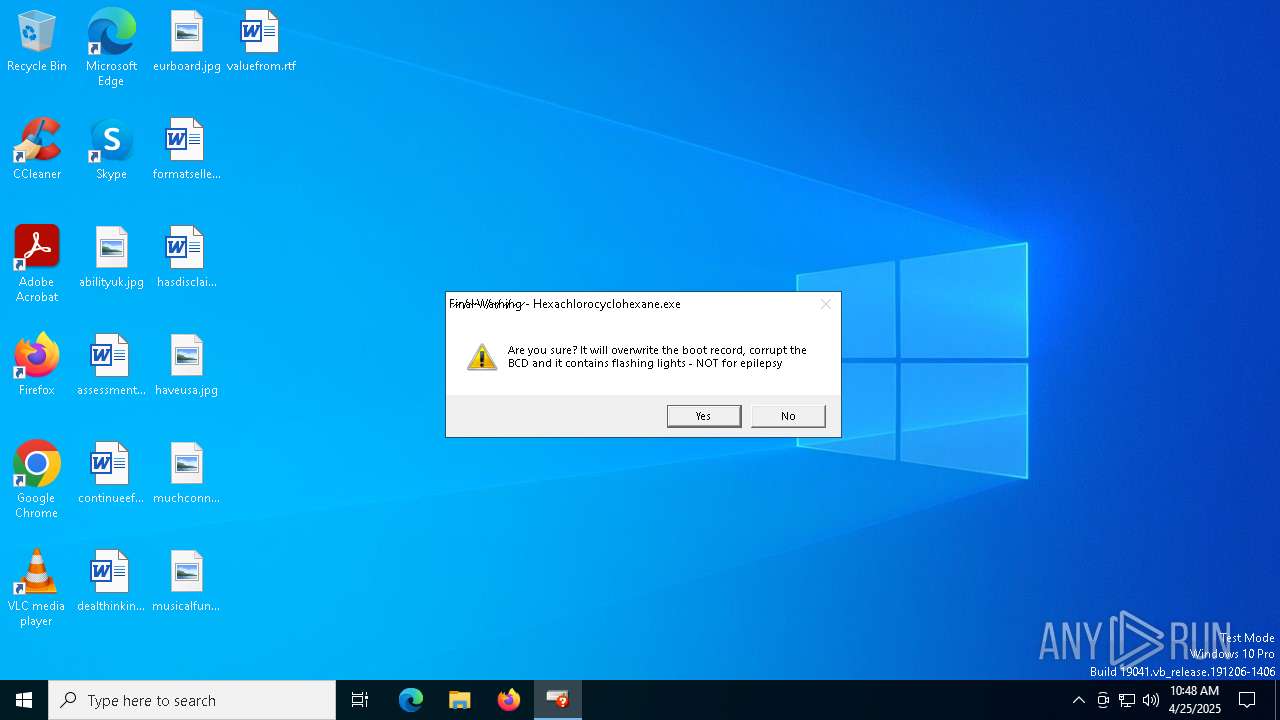
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2025, 10:48:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 0A3C93F6A1501F3D857894AE4022B69B |
| SHA1: | EC2FA5D07AB4D39F4F36C5AE0699BE5F79C57165 |
| SHA256: | 13A76F0D261E6D8B4A2887557BBBBE8A1E8A5EA97B8D827AB3774ABEB3CA58F4 |
| SSDEEP: | 3072:SEwwyUFfHoEs+3DcR1TXBheyUXk7NytFfShOxaMS94e71eEy93aQKARjCj:SEwwyU5gODcbTXBhUGytIb4e5i1kj |
MALICIOUS
Disables the LogOff the Start menu
- reg.exe (PID: 4380)
Disables task manager
- reg.exe (PID: 6744)
Disables the Run the Start menu
- reg.exe (PID: 6300)
SUSPICIOUS
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 728)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 4724)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 2244)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 5864)
Starts CMD.EXE for commands execution
- 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe (PID: 744)
There is functionality for taking screenshot (YARA)
- 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe (PID: 744)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 664)
Reads security settings of Internet Explorer
- 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe (PID: 744)
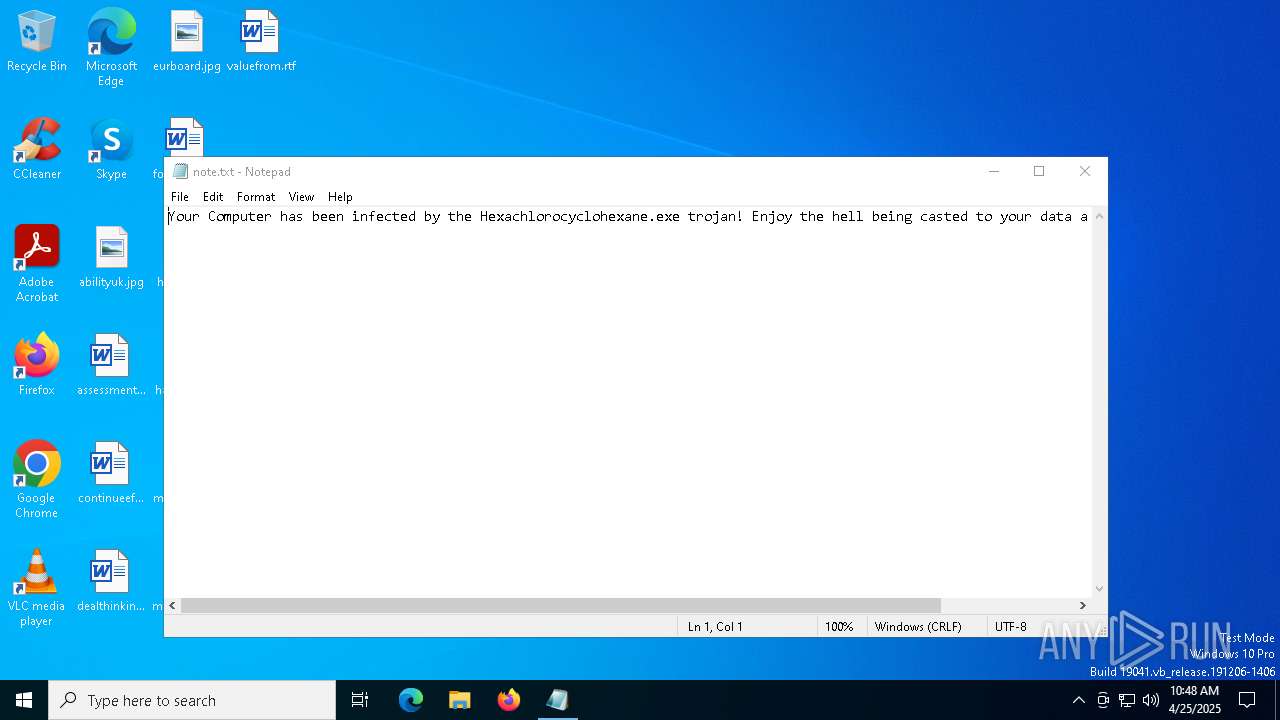
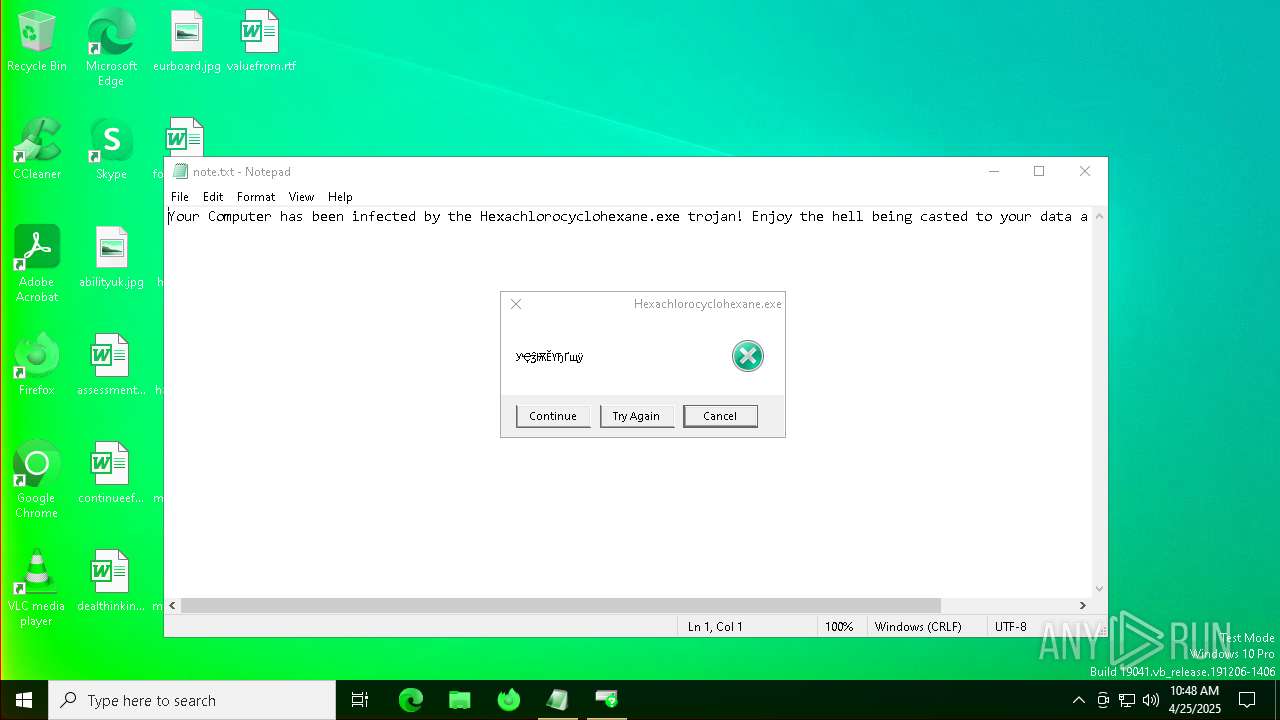
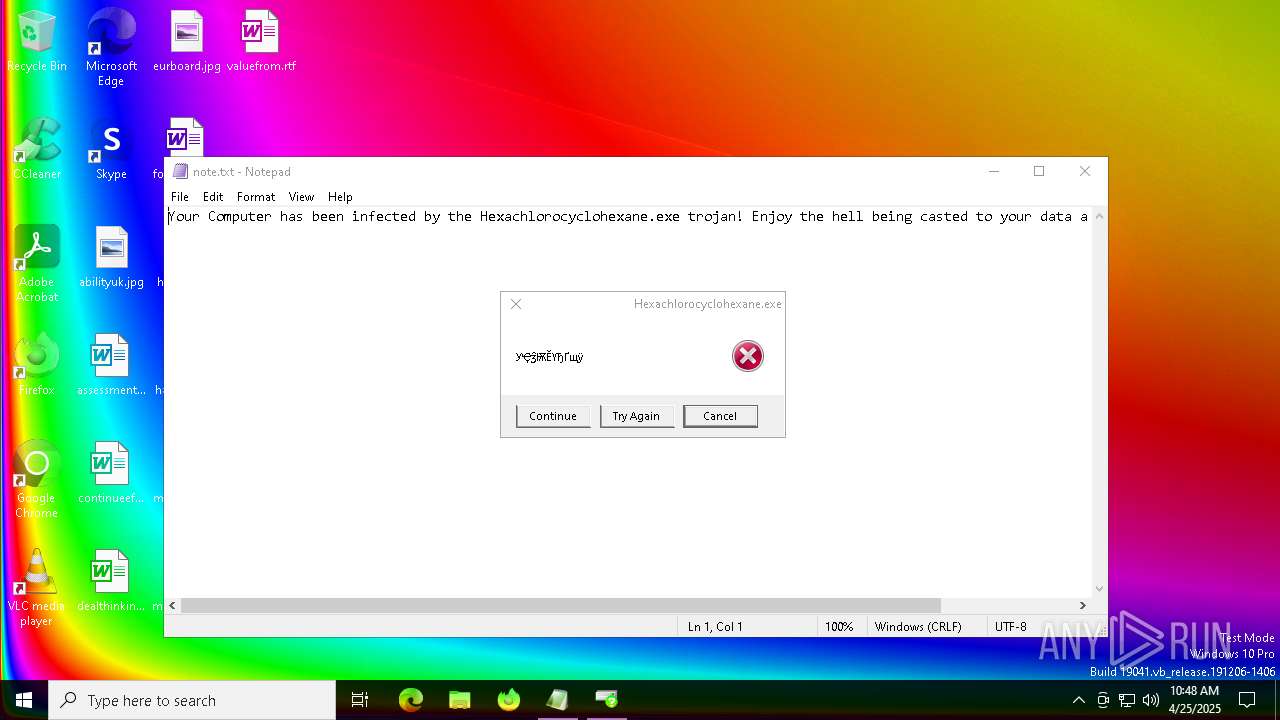
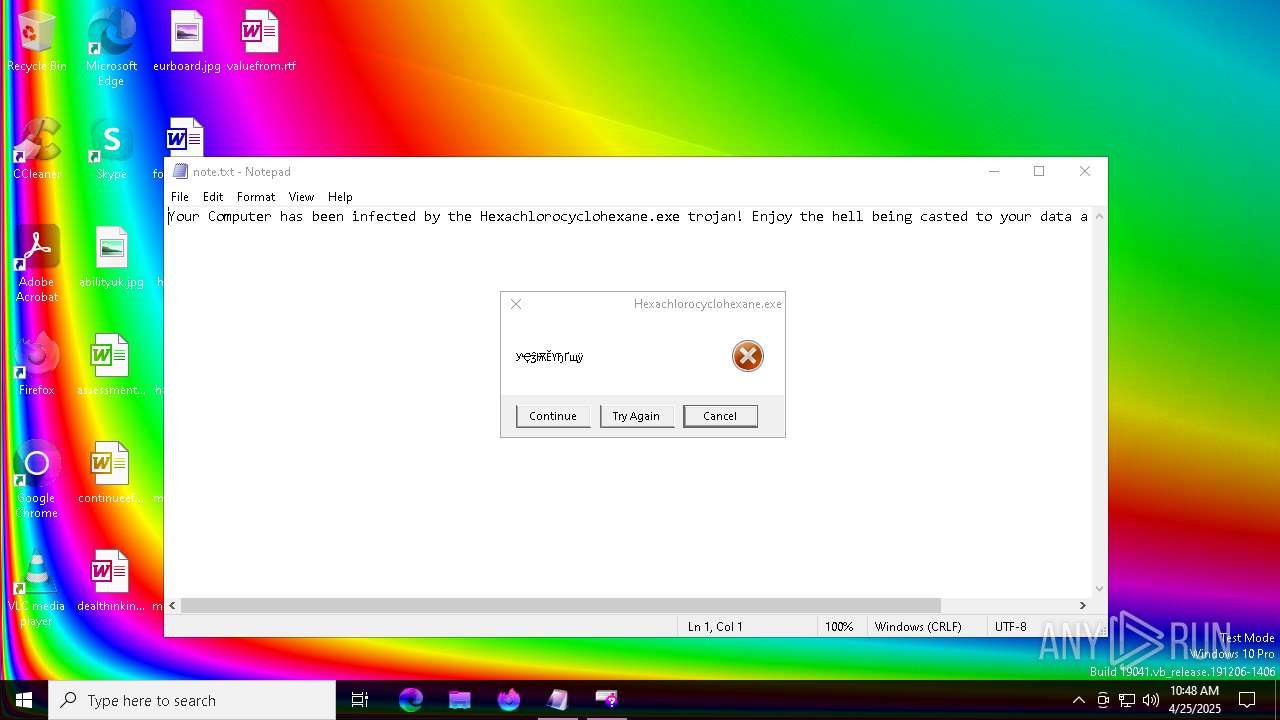
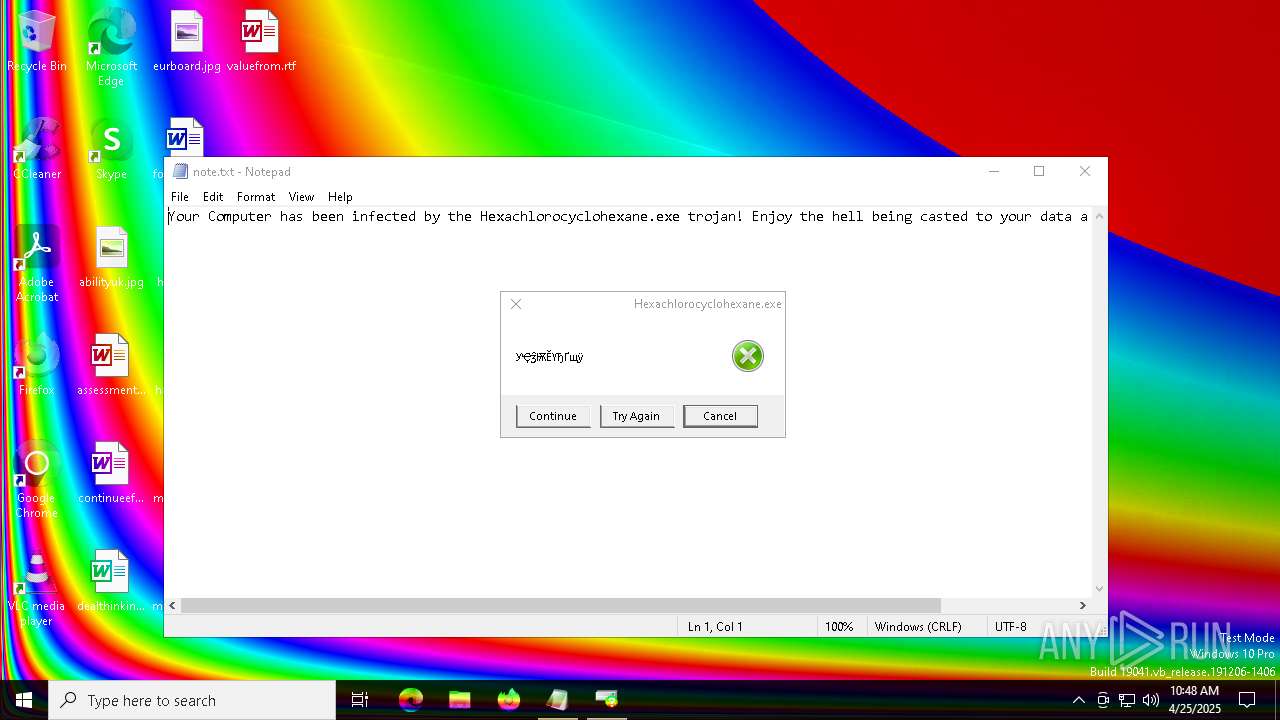
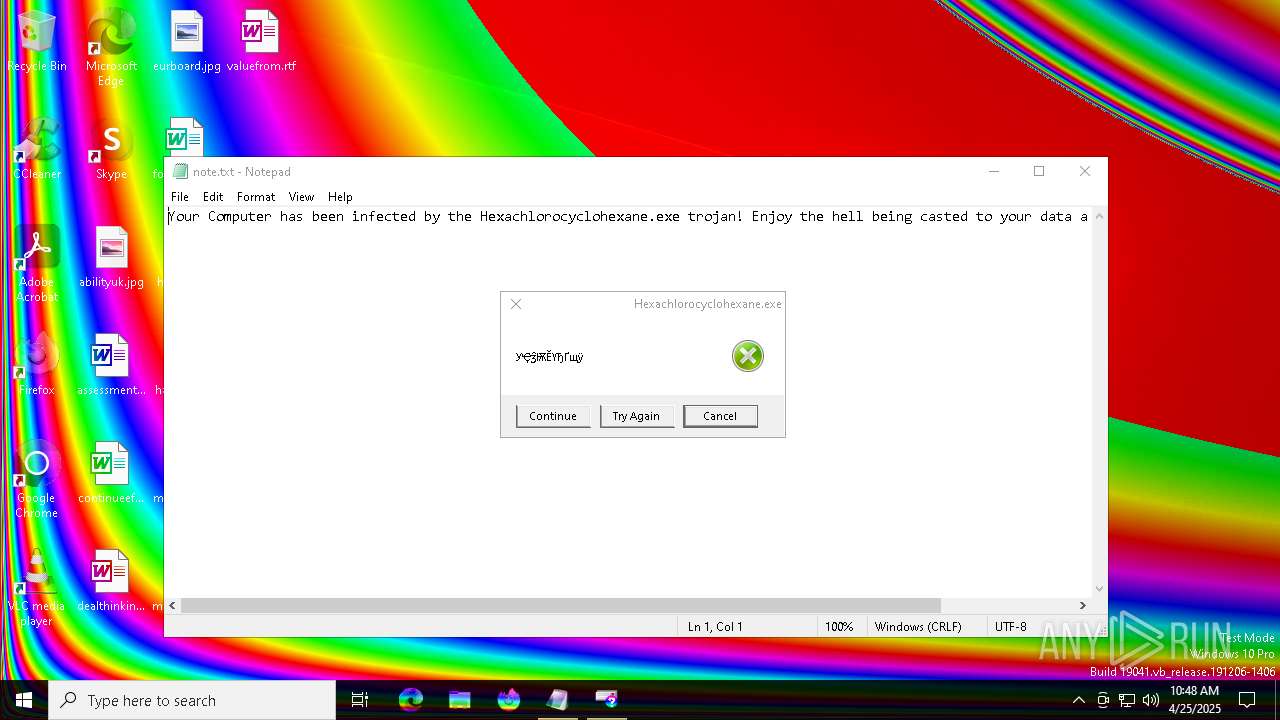
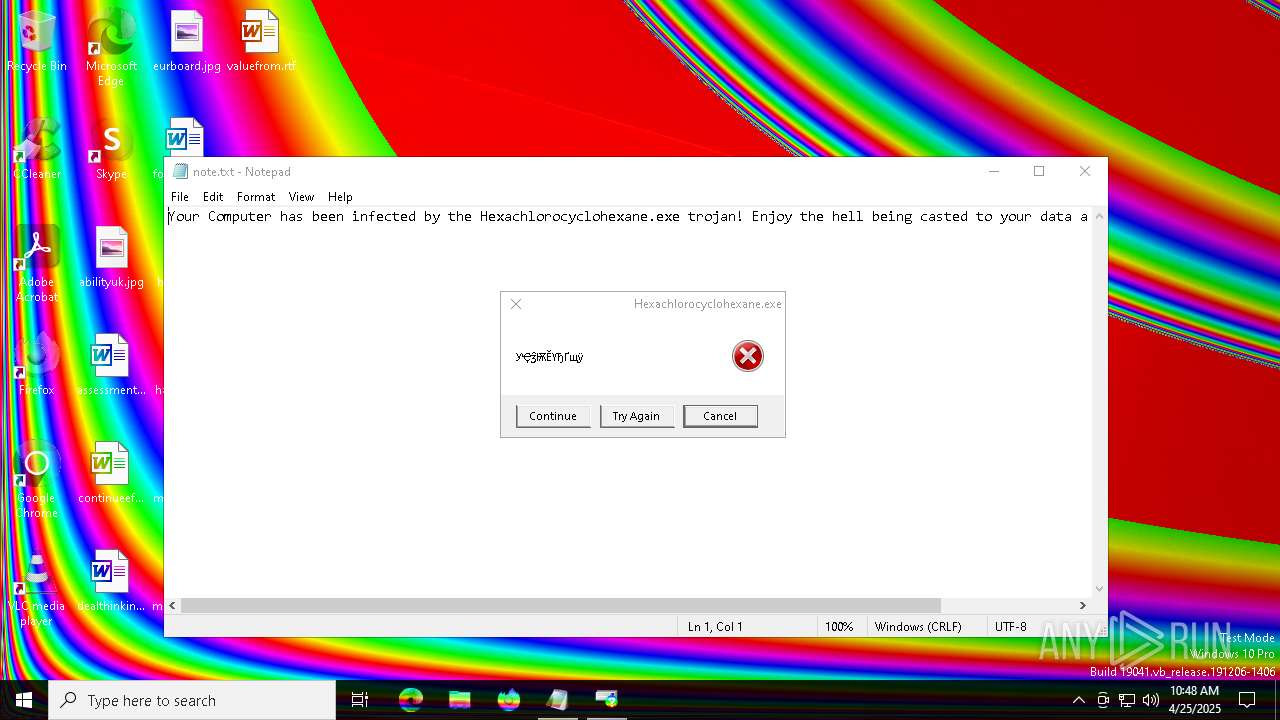
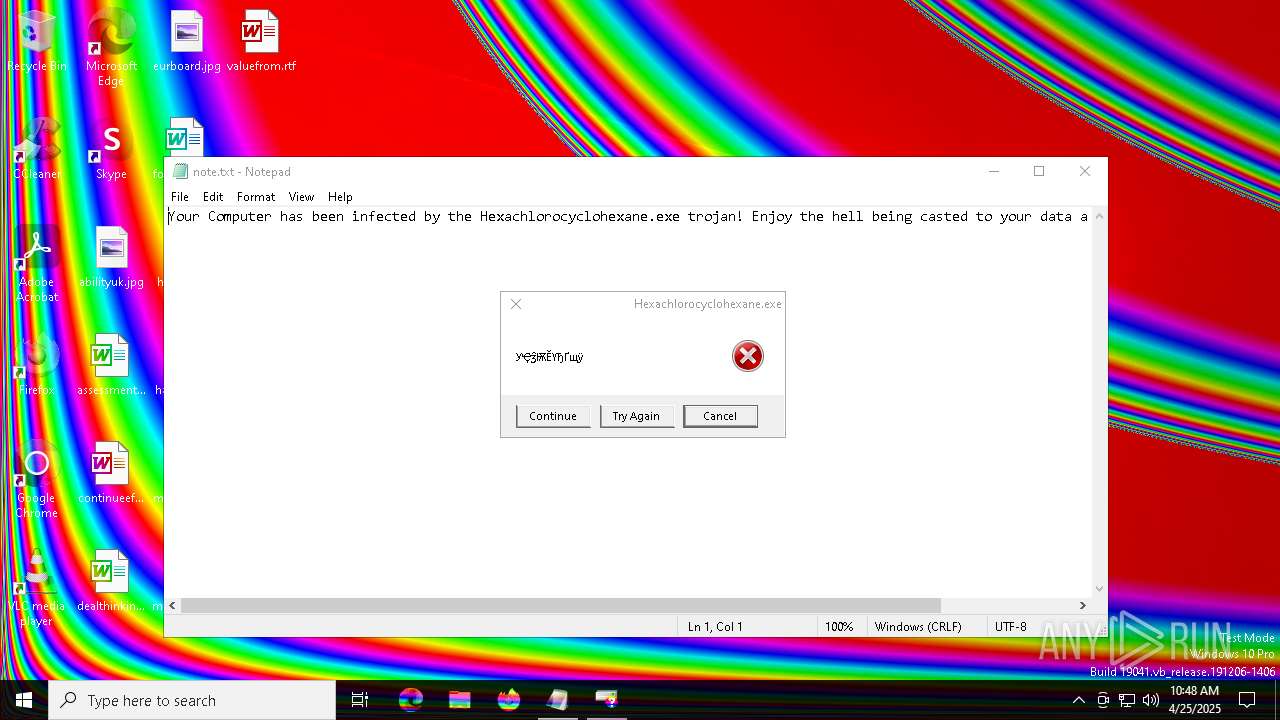
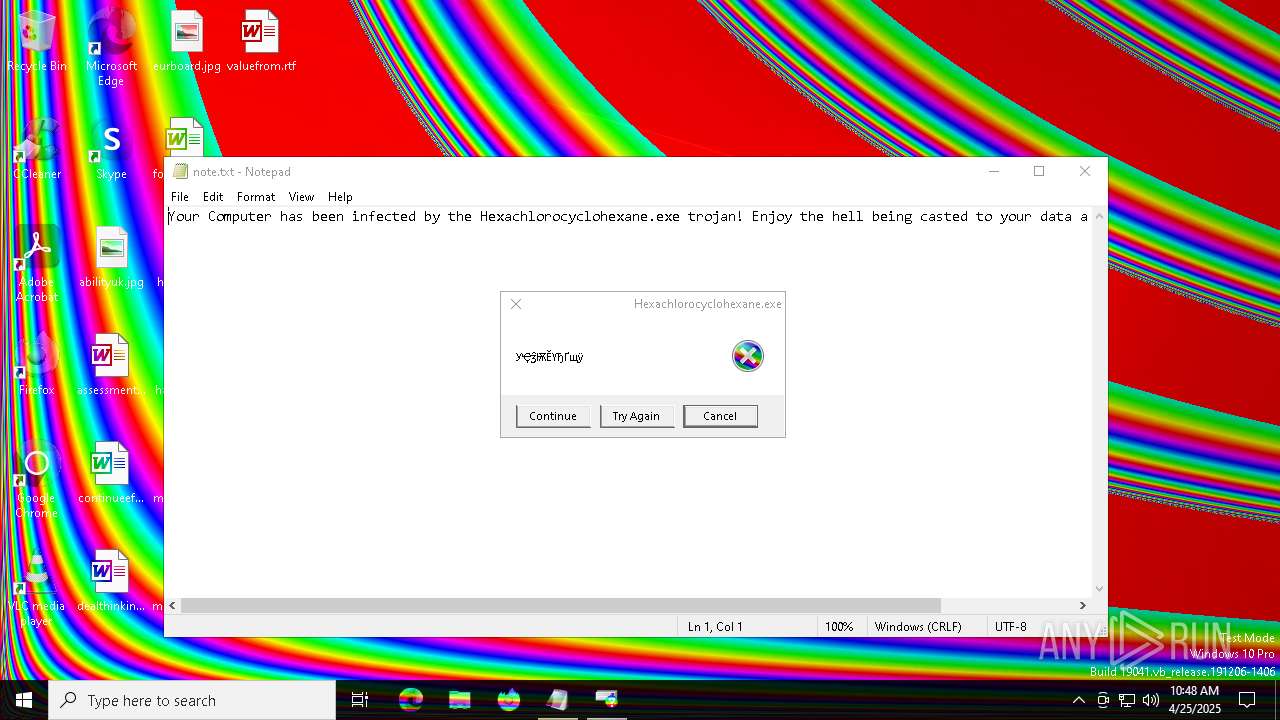
Start notepad (likely ransomware note)
- 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe (PID: 744)
INFO
Checks supported languages
- 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe (PID: 744)
Reads the computer name
- 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe (PID: 744)
Process checks computer location settings
- 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe (PID: 744)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:09:29 19:45:59+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 81920 |
| InitializedDataSize: | 57344 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6925 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.6.6.6 |
| ProductVersionNumber: | 6.6.6.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Process default |
| CharacterSet: | Unicode |
| CompanyName: | hell |
| FileDescription: | Free Netflix Account Generator 2023 |
| FileVersion: | 6.6.6.6 |
| InternalName: | Hexachlorocyclohexane.exe |
| LegalCopyright: | Copyright (C) 2023 |
| OriginalFileName: | Hexachlorocyclohexane.exe |
| ProductName: | Hexachlorocyclohexane.exe GDI Trojan |
| ProductVersion: | 6.6.6.6 |
Total processes
159
Monitored processes
31
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | C:\WINDOWS\system32\cmd.exe /c taskkill /f /im taskmgr.exe | C:\Windows\SysWOW64\cmd.exe | — | 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | C:\WINDOWS\system32\cmd.exe /c reg add HKLM\Software\Microsoft\Windows\CurrentVersion\Policies\System /v HideFastUserSwitching /t REG_DWORD /d 1 /f | C:\Windows\SysWOW64\cmd.exe | — | 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | "C:\Users\admin\AppData\Local\Temp\13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe" | C:\Users\admin\AppData\Local\Temp\13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe | explorer.exe | ||||||||||||
User: admin Company: hell Integrity Level: HIGH Description: Free Netflix Account Generator 2023 Version: 6.6.6.6 Modules
| |||||||||||||||
| 920 | reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableChangePassword /t REG_DWORD /d 1 /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | C:\WINDOWS\system32\cmd.exe /c REG ADD hkcu\Software\Microsoft\Windows\CurrentVersion\policies\Explorer /v NoControlPanel /t reg_dword /d 1 /f | C:\Windows\SysWOW64\cmd.exe | — | 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | C:\WINDOWS\system32\cmd.exe /c REG ADD hkcu\Software\Microsoft\Windows\CurrentVersion\policies\Explorer /v NoRun /t reg_dword /d 1 /f | C:\Windows\SysWOW64\cmd.exe | — | 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | C:\WINDOWS\system32\cmd.exe /c reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Policies\System /v DisableLockWorkstation /t REG_DWORD /d 1 /f | C:\Windows\SysWOW64\cmd.exe | — | 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
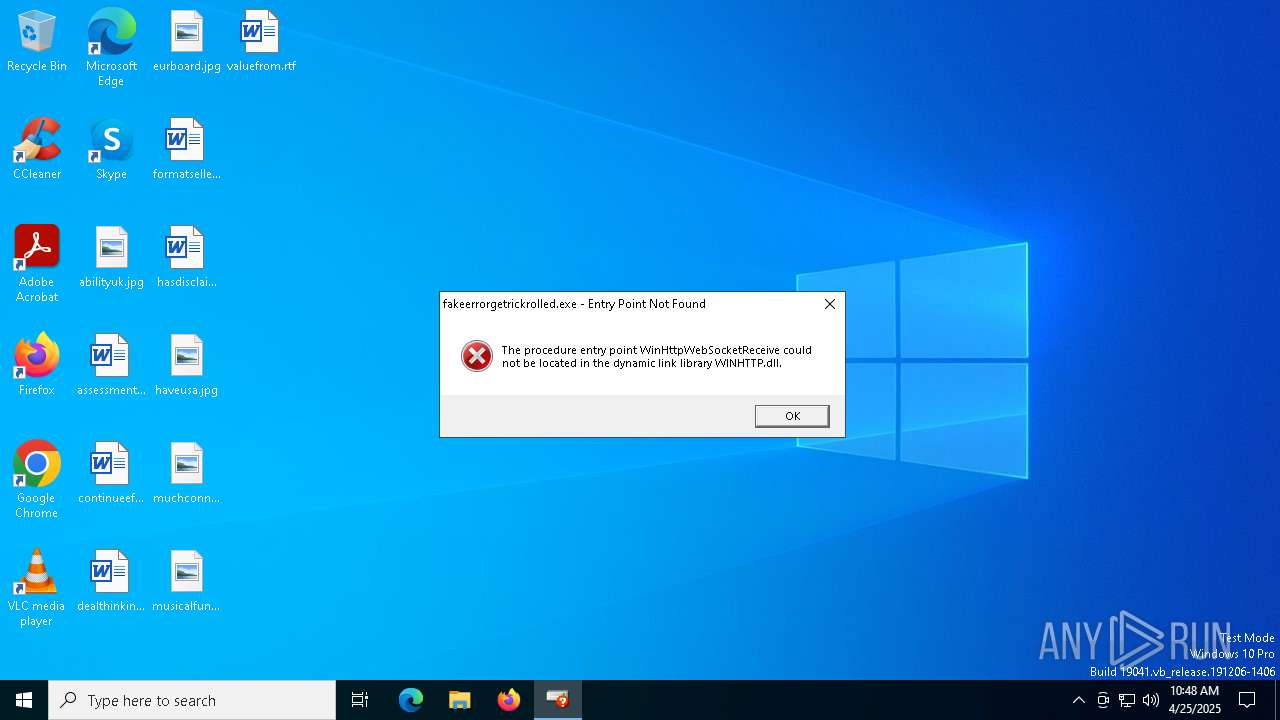
| 2568 | "C:\Users\admin\AppData\Local\Temp\13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe" | C:\Users\admin\AppData\Local\Temp\13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe | — | explorer.exe | |||||||||||
User: admin Company: hell Integrity Level: MEDIUM Description: Free Netflix Account Generator 2023 Exit code: 3221226540 Version: 6.6.6.6 Modules
| |||||||||||||||
Total events
1 414
Read events
1 407
Write events
7
Delete events
0
Modification events
| (PID) Process: | (6744) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\system |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (6300) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoRun |
Value: 1 | |||
| (PID) Process: | (5528) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoControlPanel |
Value: 1 | |||
| (PID) Process: | (6540) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | HideFastUserSwitching |
Value: 1 | |||
| (PID) Process: | (5892) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\system |
| Operation: | write | Name: | DisableLockWorkstation |
Value: 1 | |||
| (PID) Process: | (920) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\system |
| Operation: | write | Name: | DisableChangePassword |
Value: 1 | |||
| (PID) Process: | (4380) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | NoLogoff |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 744 | 13a76f0d261e6d8b4a2887557bbbbe8a1e8a5ea97b8d827ab3774abeb3ca58f4.exe | C:\Hexachlorocyclohexane\note.txt | text | |
MD5:EA548AB9C32EF92AFC59651FD2A5EE90 | SHA256:7E29CC704A0DD5E22CB9F09310DBC255DD3B432C9F7B57255647BE8692E122E6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6712 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6712 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6712 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |