| File name: | CCleaner_Setup.exe |
| Full analysis: | https://app.any.run/tasks/cbbae357-85a8-4df7-8b83-e1a6f2539cea |
| Verdict: | Malicious activity |
| Analysis date: | June 05, 2025, 00:34:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 11 sections |
| MD5: | 4BE1AE298B7174F13C9EF8DCE3B7D800 |
| SHA1: | 1EABC2ABF54E6905480D7ABD9C5B7314259293FB |
| SHA256: | 13A5C1A535C161FD2724423DAD1DFA6885C705713569D4ED4F2EBF900DF25ED7 |
| SSDEEP: | 98304:ucK14xyYUwBeWOvOTg+KuzmMEdzwwwbrz4kX/khT9ULsTBrJh8npLg832wok+nGm:K |
MALICIOUS
Bypass User Account Control (ComputerDefaults)
- ComputerDefaults.exe (PID: 2980)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- CCleaner_Setup.exe (PID: 1268)
Checks for external IP
- svchost.exe (PID: 2196)
- CCleaner_Setup.exe (PID: 1268)
There is functionality for taking screenshot (YARA)
- CCleaner_Setup.exe (PID: 1268)
Possibly patching Antimalware Scan Interface function (YARA)
- CCleaner_Setup.exe (PID: 1268)
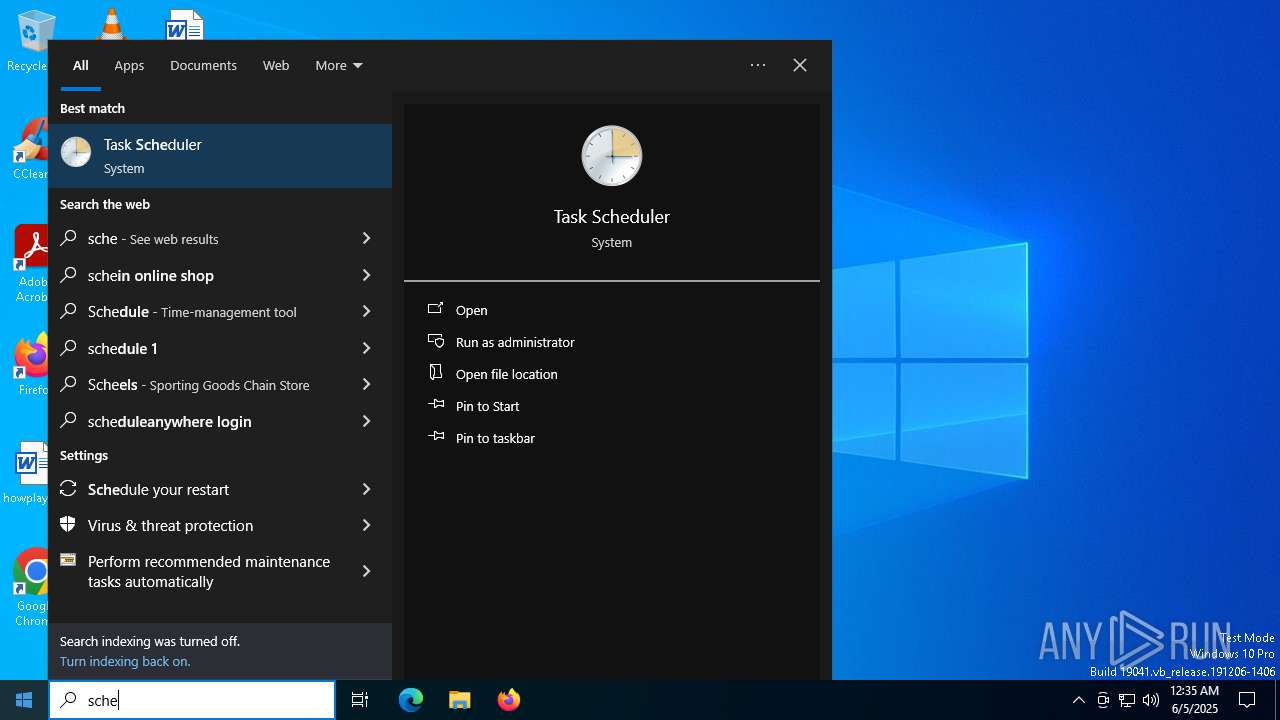
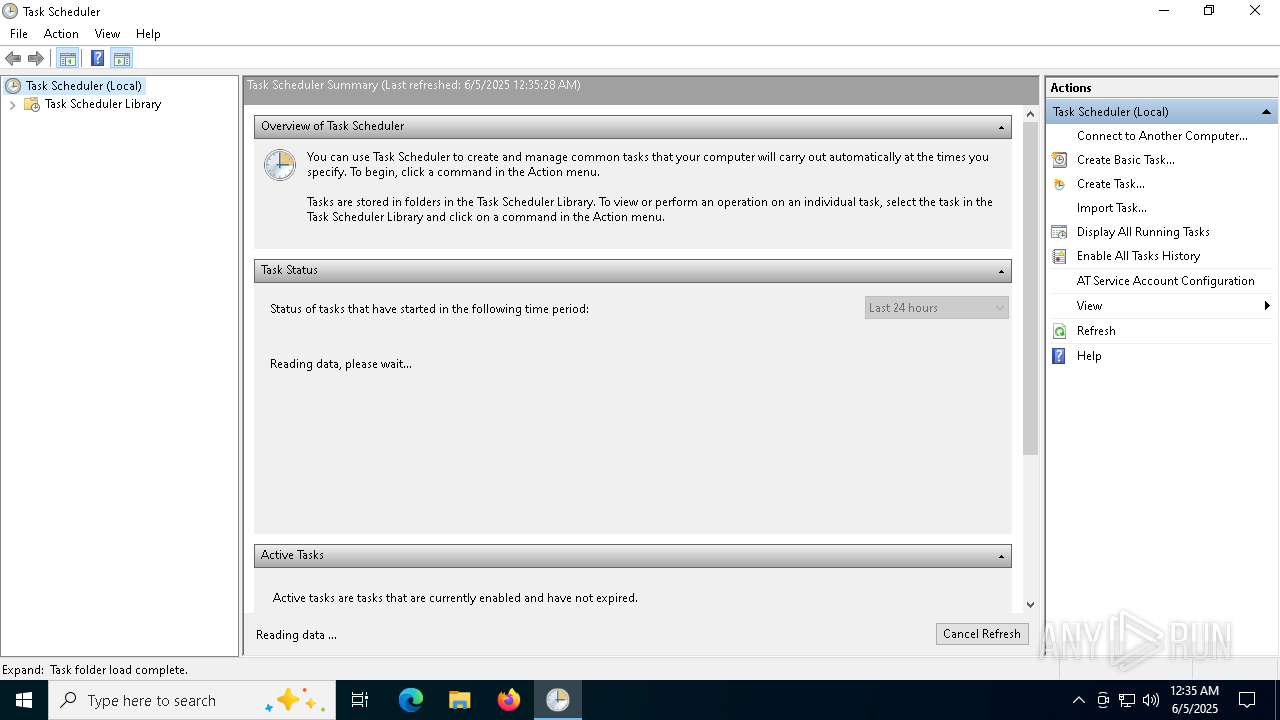
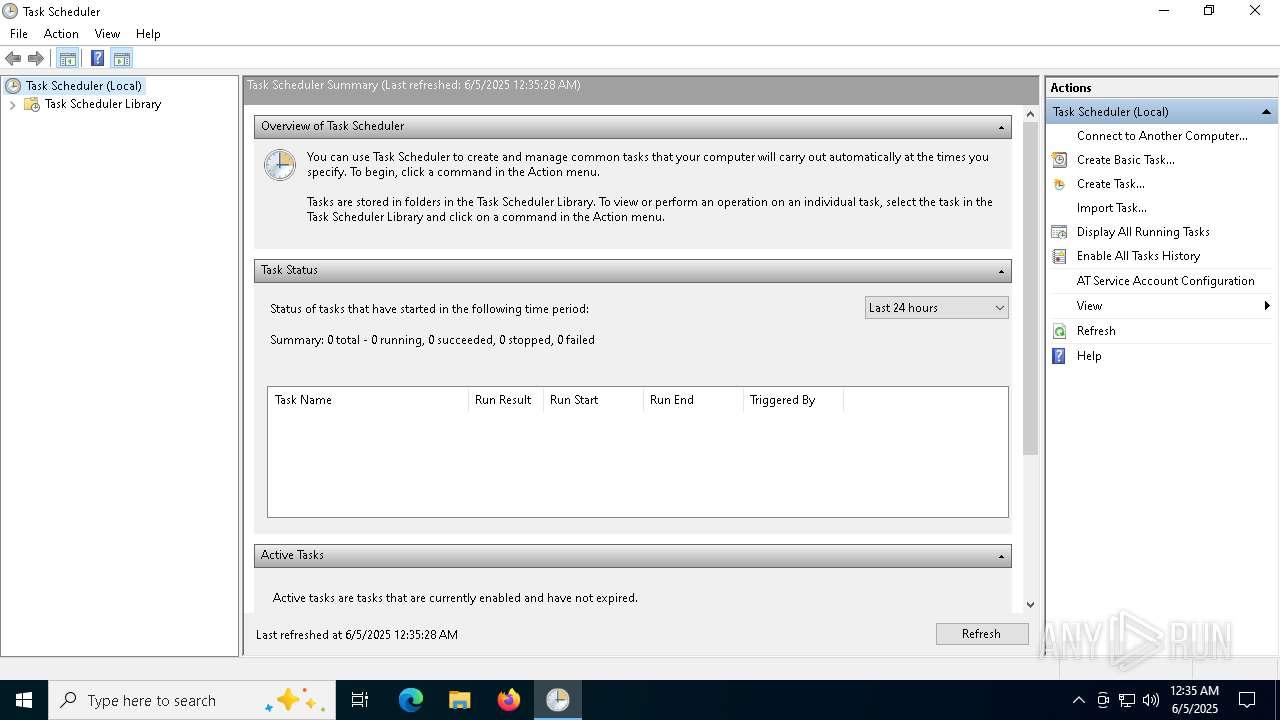
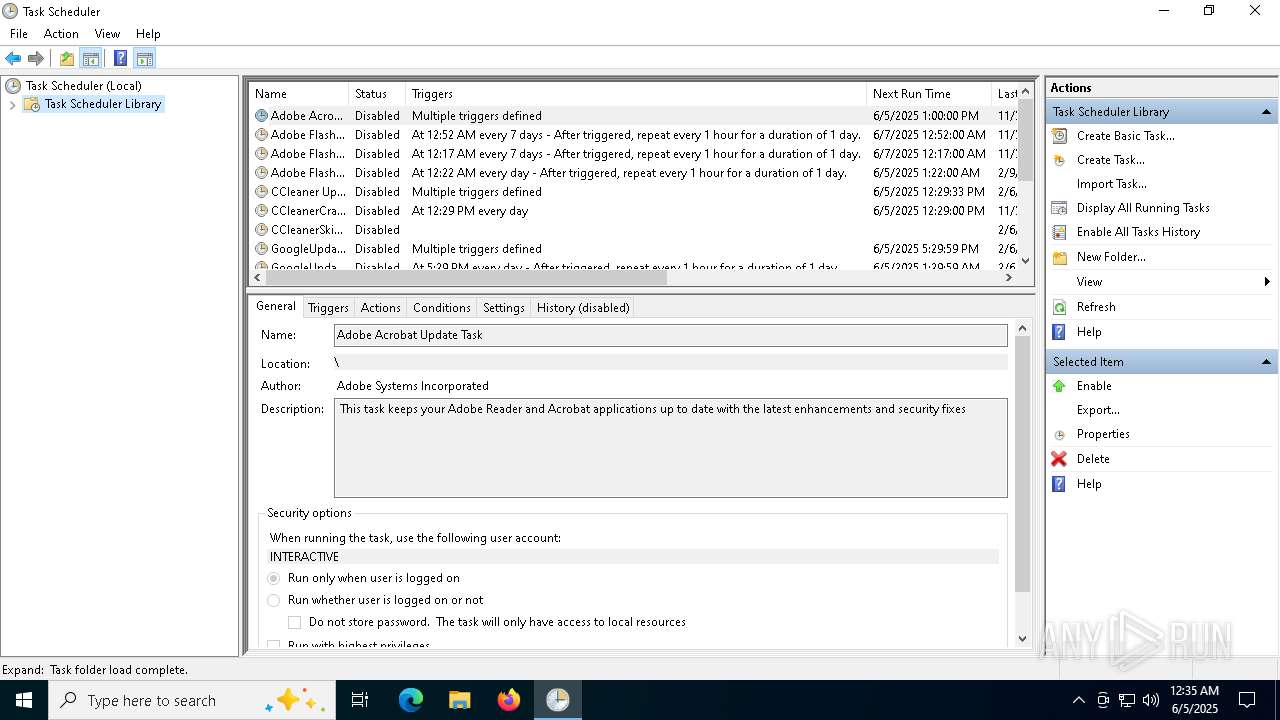
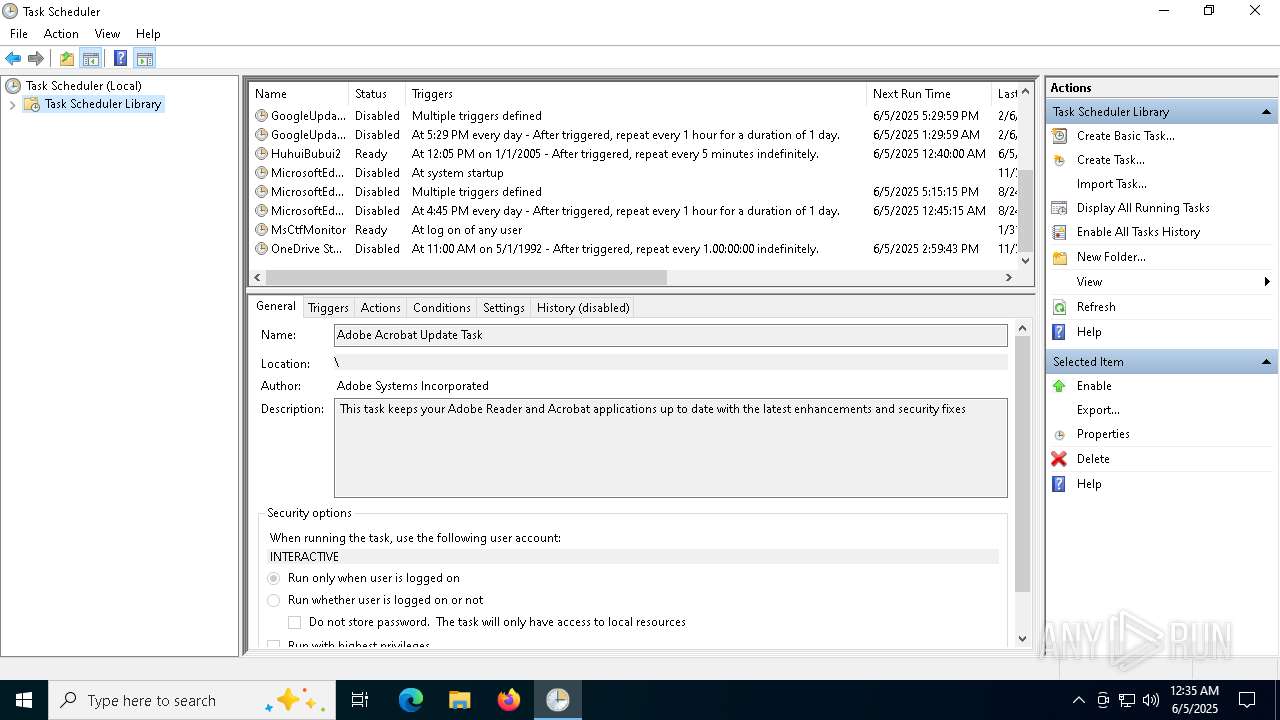
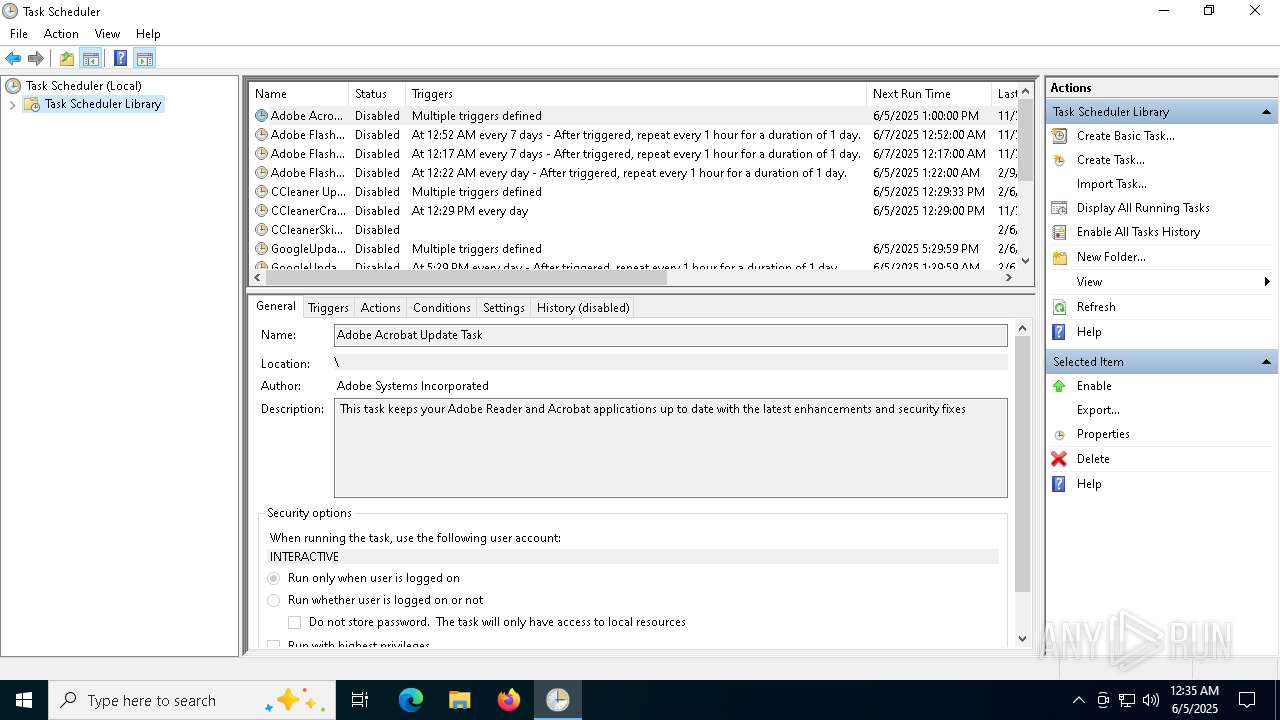
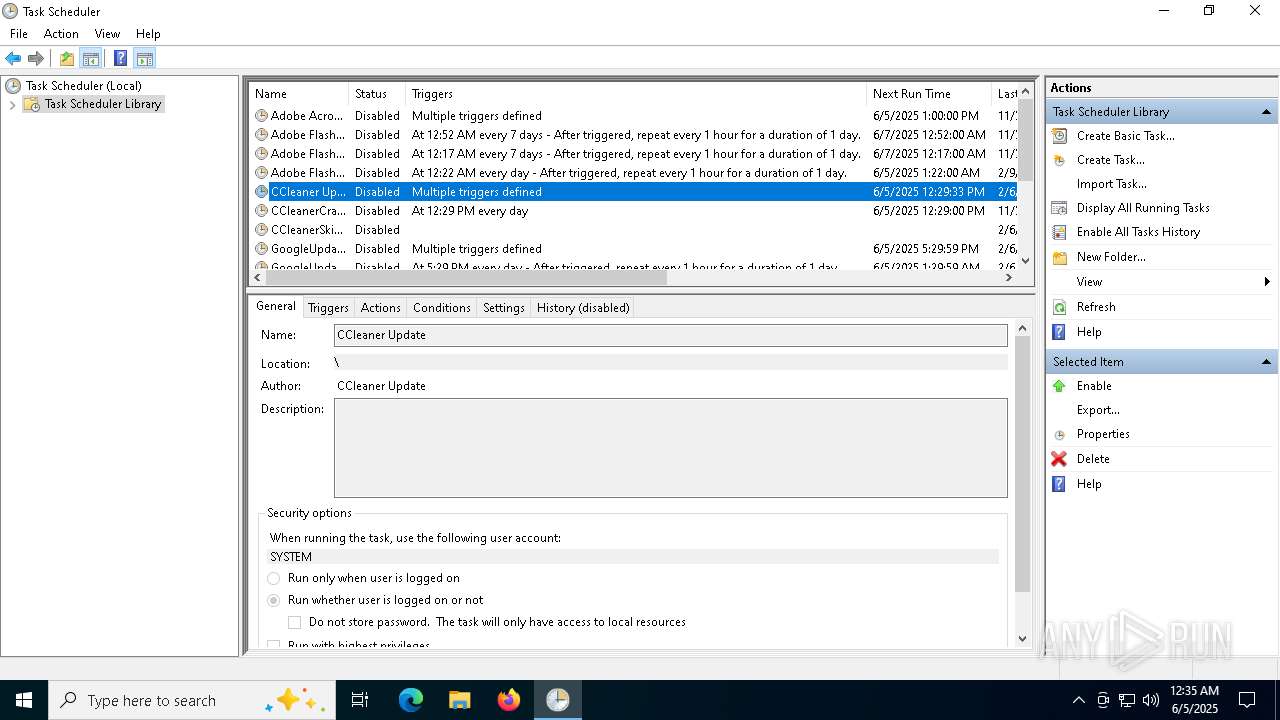
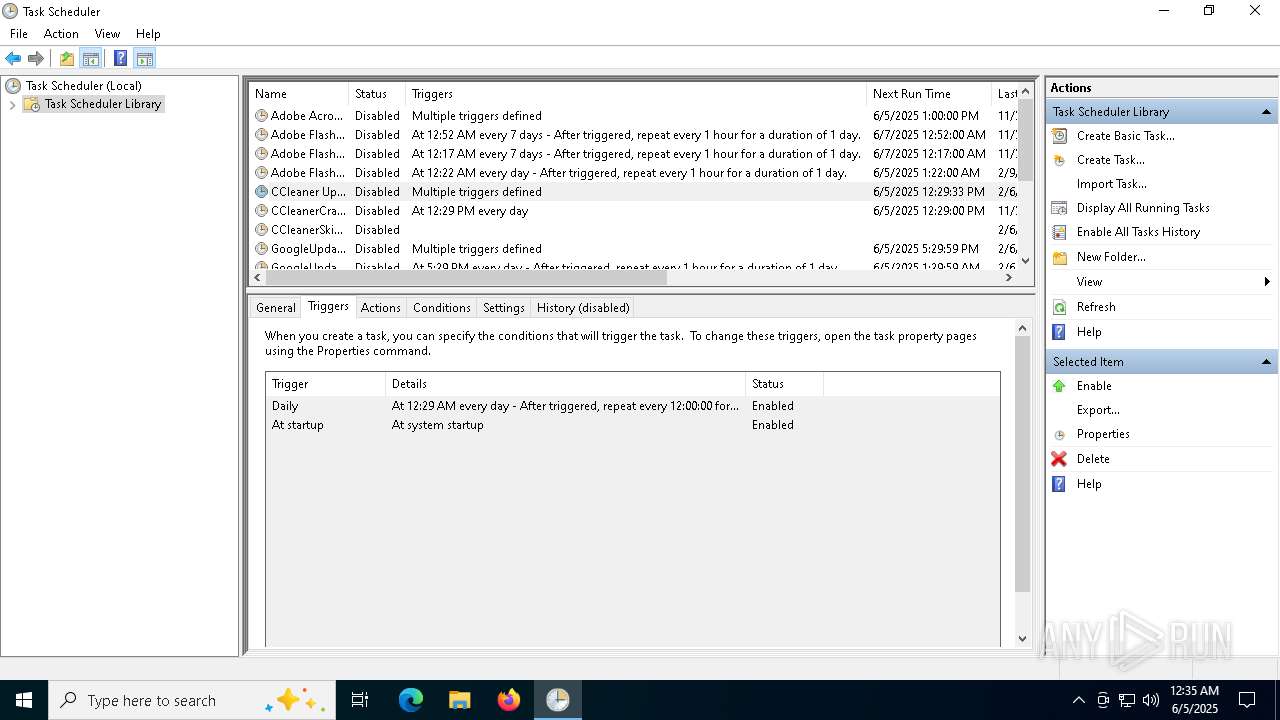
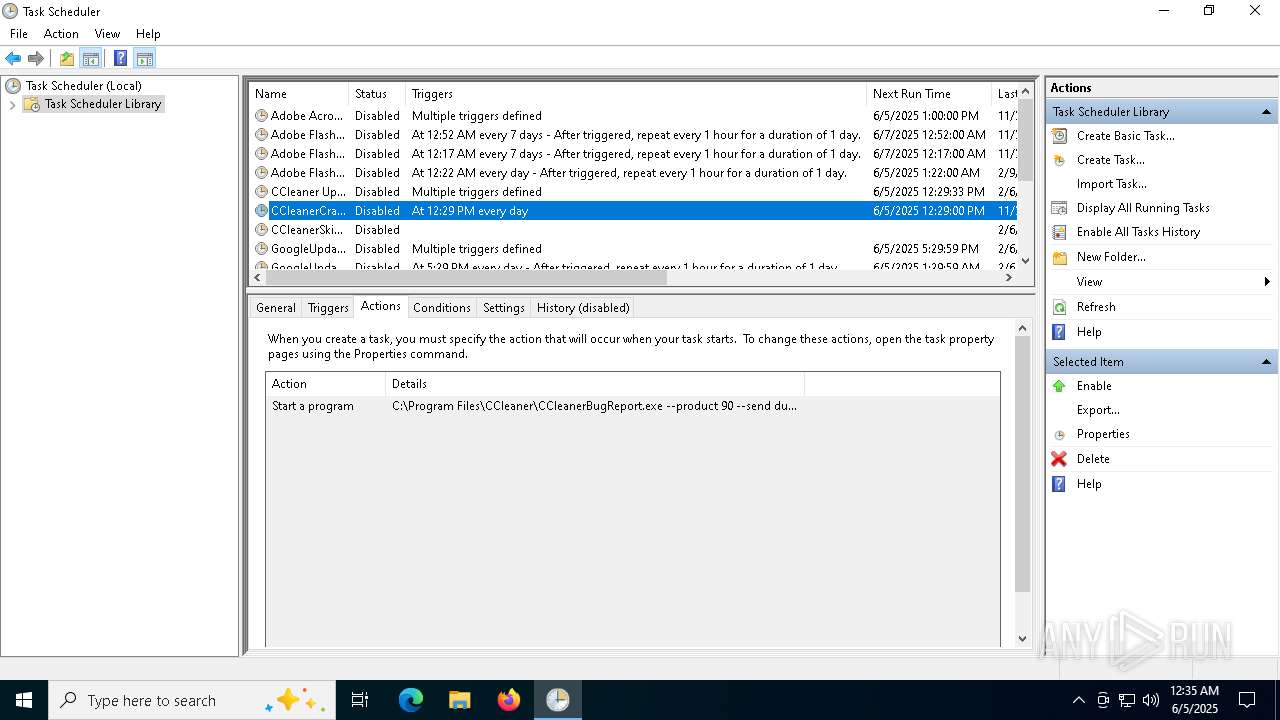
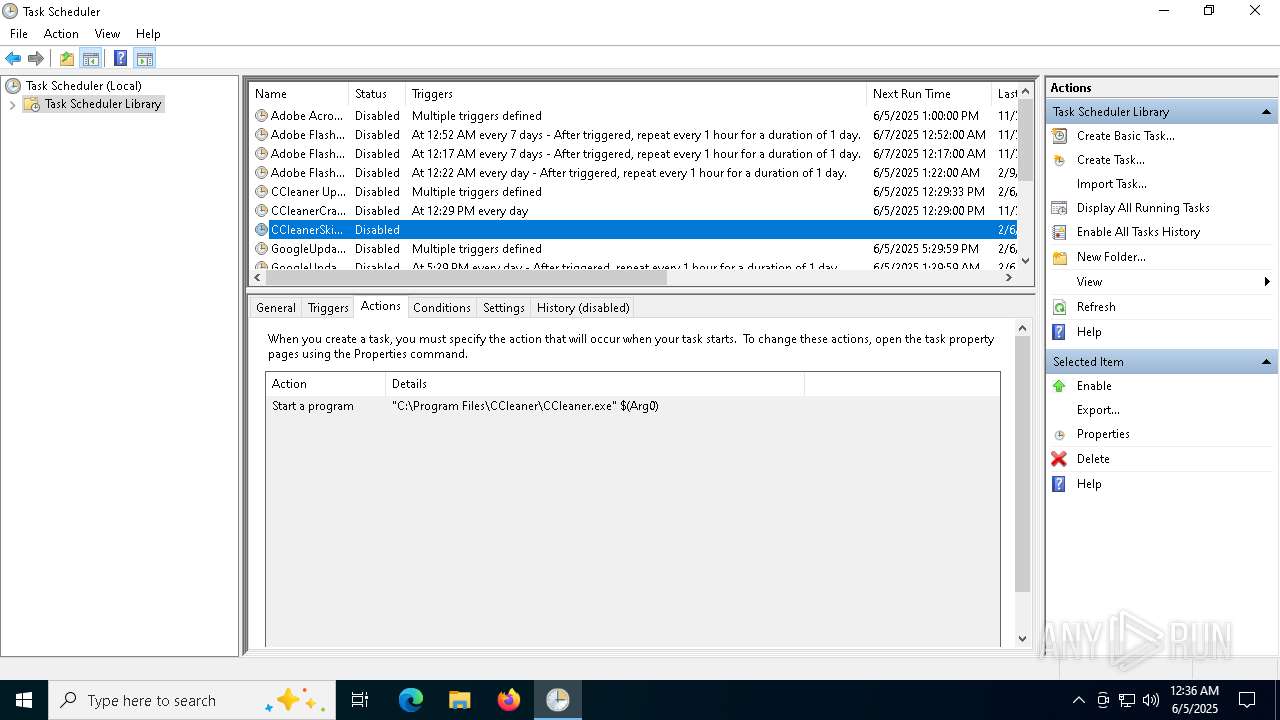
The process executes via Task Scheduler
- CCleaner_Setup.exe (PID: 8040)
INFO
Reads the computer name
- CCleaner_Setup.exe (PID: 1268)
- CCleaner_Setup.exe (PID: 7376)
- CCleaner_Setup.exe (PID: 8040)
Checks supported languages
- CCleaner_Setup.exe (PID: 7376)
- CCleaner_Setup.exe (PID: 1268)
- CCleaner_Setup.exe (PID: 8040)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 5588)
- powershell.exe (PID: 7508)
- powershell.exe (PID: 7200)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 7508)
- powershell.exe (PID: 5588)
- powershell.exe (PID: 7200)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7496)
- powershell.exe (PID: 5588)
- powershell.exe (PID: 7200)
- powershell.exe (PID: 7508)
Reads the machine GUID from the registry
- CCleaner_Setup.exe (PID: 1268)
Create files in a temporary directory
- CCleaner_Setup.exe (PID: 1268)
Compiled with Borland Delphi (YARA)
- CCleaner_Setup.exe (PID: 1268)
- mmc.exe (PID: 7712)
- slui.exe (PID: 7740)
Manual execution by a user
- mmc.exe (PID: 7712)
- mmc.exe (PID: 1804)
Reads security settings of Internet Explorer
- mmc.exe (PID: 7712)
Checks proxy server information
- slui.exe (PID: 7740)
Reads the software policy settings
- slui.exe (PID: 7740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (49.6) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.5) |
| .vxd | | | VXD Driver (0.7) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:06:04 19:25:59+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 8 |
| CodeSize: | 8861696 |
| InitializedDataSize: | 4178944 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8746f0 |
| OSVersion: | 5.2 |
| ImageVersion: | 5.2 |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.71.0.92 |
| ProductVersionNumber: | 5.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Unknown (0009) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | Glarysoft Ltd |
| FileDescription: | Glary Utilities 5 |
| FileVersion: | 5, 71, 0, 92 |
| InternalName: | Integrator.exe |
| LegalCopyright: | Copyright (c) 2003-2017 Glarysoft Ltd |
| OriginalFileName: | Integrator.exe |
| ProductName: | Glary Utilities |
| ProductVersion: | 5, 0, 0, 0 |
Total processes
146
Monitored processes
17
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1268 | "C:\Users\admin\AppData\Local\Temp\CCleaner_Setup.exe" | C:\Users\admin\AppData\Local\Temp\CCleaner_Setup.exe | ComputerDefaults.exe | ||||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: HIGH Description: Glary Utilities 5 Version: 5, 71, 0, 92 Modules
| |||||||||||||||
| 1804 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\taskschd.msc" /s | C:\Windows\System32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2980 | C:\Windows\System32\ComputerDefaults.exe | C:\Windows\System32\ComputerDefaults.exe | CCleaner_Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Set Program Access and Computer Defaults Control Panel Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5588 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | CCleaner_Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6036 | C:\Windows\System32\winver.exe | C:\Windows\System32\winver.exe | — | CCleaner_Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Version Reporter Applet Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7200 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | CCleaner_Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7220 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7376 | "C:\Users\admin\AppData\Local\Temp\CCleaner_Setup.exe" | C:\Users\admin\AppData\Local\Temp\CCleaner_Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Glarysoft Ltd Integrity Level: MEDIUM Description: Glary Utilities 5 Exit code: 0 Version: 5, 71, 0, 92 Modules
| |||||||||||||||
Total events
25 814
Read events
25 808
Write events
5
Delete events
1
Modification events
| (PID) Process: | (7712) mmc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MMC\SnapIns\FX:{c7b8fb06-bfe1-4c2e-9217-7a69a95bbac4} |
| Operation: | write | Name: | HelpTopic |
Value: C:\WINDOWS\Help\taskscheduler.chm | |||
| (PID) Process: | (7712) mmc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\MMC\SnapIns\FX:{c7b8fb06-bfe1-4c2e-9217-7a69a95bbac4} |
| Operation: | write | Name: | LinkedHelpTopics |
Value: C:\WINDOWS\Help\taskscheduler.chm | |||
| (PID) Process: | (7712) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7712) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File1 |
Value: C:\WINDOWS\system32\taskschd.msc | |||
| (PID) Process: | (7712) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File2 |
Value: C:\WINDOWS\system32\wf.msc | |||
| (PID) Process: | (7712) mmc.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Microsoft Management Console\Recent File List |
| Operation: | write | Name: | File3 |
Value: C:\WINDOWS\system32\services.msc | |||
Executable files
0
Suspicious files
1
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7496 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_j1aojao5.eqe.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5588 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_p0wfmgkr.a4z.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7508 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kynrl10o.qc4.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7508 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1tq2olkt.w42.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7496 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mvywwg5b.sq0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7200 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yui35e54.bvz.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5588 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pb4lxtv5.dcz.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7200 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tzrpnjq2.2qn.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7712 | mmc.exe | C:\Users\admin\AppData\Roaming\Microsoft\MMC\taskschd | xml | |
MD5:22C6C6B63CE92EE804133D20856D7EE6 | SHA256:F7984E9BE53B9C109338A5DB806D022B32F285F694CA510FD331D41E5FB0200F | |||
| 7496 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-Interactive | binary | |
MD5:CC9C21F2DF015566C36A0945FD895A26 | SHA256:B1CCB0729B79902C50C12C854BD0D67DA8AB7A76F726A8E97D88BB97724CAD16 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
47
DNS requests
25
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7172 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7172 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | CCleaner_Setup.exe | GET | 200 | 208.95.112.1:80 | http://www.ip-api.com/line/?fields=147505 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4616 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7212 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | CCleaner_Setup.exe | 208.95.112.1:80 | www.ip-api.com | TUT-AS | US | whitelisted |
1268 | CCleaner_Setup.exe | 77.238.241.203:443 | — | Tele.RU Ltd. | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.ip-api.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
1268 | CCleaner_Setup.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |