analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| File name: | IDM 32bit Patch.exe |
| Full analysis: | https://app.any.run/tasks/46878400-b532-44aa-8d1a-ebd335d43ee6 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 13:45:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 926FF1E2FB06D214F46B521464BB990A |
| SHA1: | C59EFADF531DB4FAFBB892FA668A7E9D8F8E5D81 |
| SHA256: | 1391ED251CF4D50DC7358C525F8B2C6DBF55AF715F6090CEAF90DAEF23B1DD72 |
| SSDEEP: | 49152:OAI+lUND3tWW9adCe/k/zgq/jex3Zjzyn8YmIF7Czl:OAI+QTEmaVcESIdWn8YjF7Kl |
MALICIOUS
Drops executable file immediately after starts
- IDM 32bit Patch.exe (PID: 3252)
Executes PowerShell scripts
- cmd.exe (PID: 4032)
SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 4032)
- IDM 32bit Patch.exe (PID: 3252)
- cmd.exe (PID: 1612)
- powershell.exe (PID: 3068)
Creates files in the program directory
- IDM 32bit Patch.exe (PID: 3252)
- cmd.exe (PID: 4032)
Creates a directory in Program Files
- IDM 32bit Patch.exe (PID: 3252)
Starts CMD.EXE for commands execution
- IDM 32bit Patch.exe (PID: 3252)
- cmd.exe (PID: 4032)
Reads the computer name
- IDM 32bit Patch.exe (PID: 3252)
- powershell.exe (PID: 3068)
Drops a file with a compile date too recent
- IDM 32bit Patch.exe (PID: 3252)
Executable content was dropped or overwritten
- IDM 32bit Patch.exe (PID: 3252)
Creates a software uninstall entry
- IDM 32bit Patch.exe (PID: 3252)
Application launched itself
- cmd.exe (PID: 4032)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 4032)
Uses WHOAMI.EXE to obtaining logged on user information
- cmd.exe (PID: 1612)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 4032)
INFO
Checks supported languages
- whoami.exe (PID: 3772)
- reg.exe (PID: 464)
- taskkill.exe (PID: 2836)
- taskkill.exe (PID: 1392)
- taskkill.exe (PID: 3136)
- taskkill.exe (PID: 896)
- taskkill.exe (PID: 2984)
- reg.exe (PID: 2008)
- taskkill.exe (PID: 3848)
- reg.exe (PID: 4084)
- reg.exe (PID: 2120)
- taskkill.exe (PID: 3568)
- reg.exe (PID: 3652)
- reg.exe (PID: 3796)
- reg.exe (PID: 2432)
- reg.exe (PID: 2592)
- reg.exe (PID: 3108)
- reg.exe (PID: 1392)
- reg.exe (PID: 336)
- reg.exe (PID: 3532)
- reg.exe (PID: 3148)
- reg.exe (PID: 3608)
- reg.exe (PID: 2672)
- reg.exe (PID: 2840)
- reg.exe (PID: 3216)
- reg.exe (PID: 1940)
- reg.exe (PID: 2972)
- reg.exe (PID: 3836)
- reg.exe (PID: 3480)
- reg.exe (PID: 4072)
- reg.exe (PID: 3484)
- reg.exe (PID: 2124)
- reg.exe (PID: 1032)
- reg.exe (PID: 3176)
- reg.exe (PID: 3744)
- reg.exe (PID: 3932)
- reg.exe (PID: 3620)
- reg.exe (PID: 2464)
- reg.exe (PID: 2260)
- reg.exe (PID: 2556)
- reg.exe (PID: 2308)
- reg.exe (PID: 656)
- reg.exe (PID: 1960)
- reg.exe (PID: 3316)
- reg.exe (PID: 3084)
- reg.exe (PID: 3556)
- reg.exe (PID: 780)
- reg.exe (PID: 1240)
- reg.exe (PID: 1360)
- reg.exe (PID: 2220)
- reg.exe (PID: 3984)
- reg.exe (PID: 3036)
- reg.exe (PID: 2712)
- reg.exe (PID: 652)
- reg.exe (PID: 3896)
- reg.exe (PID: 2604)
- reg.exe (PID: 4056)
- reg.exe (PID: 2104)
- reg.exe (PID: 2340)
- reg.exe (PID: 416)
- reg.exe (PID: 3948)
- reg.exe (PID: 2008)
- reg.exe (PID: 1600)
- reg.exe (PID: 440)
- reg.exe (PID: 3168)
- reg.exe (PID: 1996)
- reg.exe (PID: 280)
- reg.exe (PID: 2720)
- reg.exe (PID: 3544)
- reg.exe (PID: 3956)
- reg.exe (PID: 1872)
- reg.exe (PID: 2580)
- reg.exe (PID: 2744)
- reg.exe (PID: 3364)
- reg.exe (PID: 2140)
- reg.exe (PID: 2248)
- reg.exe (PID: 1552)
- reg.exe (PID: 3852)
- reg.exe (PID: 4092)
- reg.exe (PID: 1276)
- reg.exe (PID: 2400)
- reg.exe (PID: 2516)
- reg.exe (PID: 1572)
- reg.exe (PID: 2652)
- reg.exe (PID: 1792)
- reg.exe (PID: 3576)
- reg.exe (PID: 3556)
- reg.exe (PID: 852)
- reg.exe (PID: 2788)
- reg.exe (PID: 3120)
- reg.exe (PID: 3316)
- reg.exe (PID: 3816)
- reg.exe (PID: 2552)
- reg.exe (PID: 3932)
- reg.exe (PID: 472)
- reg.exe (PID: 3084)
- reg.exe (PID: 2168)
- reg.exe (PID: 3936)
- reg.exe (PID: 240)
- reg.exe (PID: 3848)
- reg.exe (PID: 2192)
- reg.exe (PID: 3772)
- reg.exe (PID: 2124)
- reg.exe (PID: 1264)
- reg.exe (PID: 1960)
- reg.exe (PID: 2472)
- reg.exe (PID: 1484)
- reg.exe (PID: 3400)
- reg.exe (PID: 2260)
- reg.exe (PID: 3524)
- reg.exe (PID: 3324)
- reg.exe (PID: 2332)
- reg.exe (PID: 828)
- reg.exe (PID: 2448)
- reg.exe (PID: 2784)
- reg.exe (PID: 2840)
- reg.exe (PID: 3264)
- reg.exe (PID: 1996)
- reg.exe (PID: 1296)
- reg.exe (PID: 3920)
- reg.exe (PID: 1480)
- reg.exe (PID: 2180)
- reg.exe (PID: 3956)
- reg.exe (PID: 1560)
- reg.exe (PID: 2392)
- reg.exe (PID: 2632)
- reg.exe (PID: 1164)
- reg.exe (PID: 4028)
- reg.exe (PID: 2400)
- reg.exe (PID: 2856)
- reg.exe (PID: 2652)
- reg.exe (PID: 2224)
- reg.exe (PID: 3620)
- reg.exe (PID: 2516)
- reg.exe (PID: 3428)
- reg.exe (PID: 3196)
- reg.exe (PID: 1436)
- reg.exe (PID: 3536)
- reg.exe (PID: 2076)
- reg.exe (PID: 1012)
- reg.exe (PID: 1376)
- reg.exe (PID: 2572)
- reg.exe (PID: 2108)
- reg.exe (PID: 2044)
- reg.exe (PID: 2728)
- reg.exe (PID: 416)
- reg.exe (PID: 1108)
- reg.exe (PID: 2612)
- reg.exe (PID: 2972)
- reg.exe (PID: 3704)
- reg.exe (PID: 2428)
- reg.exe (PID: 2892)
- reg.exe (PID: 2716)
- reg.exe (PID: 2500)
- reg.exe (PID: 3400)
- reg.exe (PID: 3380)
- reg.exe (PID: 1960)
- reg.exe (PID: 576)
- reg.exe (PID: 3524)
- reg.exe (PID: 2268)
- reg.exe (PID: 3832)
- reg.exe (PID: 3280)
- reg.exe (PID: 2764)
- reg.exe (PID: 3968)
- reg.exe (PID: 1296)
- reg.exe (PID: 2176)
- reg.exe (PID: 2088)
- reg.exe (PID: 4072)
- reg.exe (PID: 3636)
- reg.exe (PID: 4084)
- reg.exe (PID: 2408)
- reg.exe (PID: 1720)
- reg.exe (PID: 2656)
- reg.exe (PID: 376)
- reg.exe (PID: 2596)
- reg.exe (PID: 4024)
- reg.exe (PID: 492)
- reg.exe (PID: 3048)
- reg.exe (PID: 1872)
- reg.exe (PID: 2540)
- reg.exe (PID: 1544)
- reg.exe (PID: 2200)
- reg.exe (PID: 2732)
- reg.exe (PID: 3792)
- reg.exe (PID: 696)
- reg.exe (PID: 1988)
- reg.exe (PID: 2584)
- reg.exe (PID: 876)
- reg.exe (PID: 2184)
- reg.exe (PID: 356)
- reg.exe (PID: 2400)
- reg.exe (PID: 2096)
- reg.exe (PID: 3964)
- reg.exe (PID: 2848)
- reg.exe (PID: 2948)
- reg.exe (PID: 1360)
- reg.exe (PID: 3116)
- reg.exe (PID: 3664)
- reg.exe (PID: 956)
- reg.exe (PID: 2576)
- reg.exe (PID: 3752)
- reg.exe (PID: 3380)
- reg.exe (PID: 1072)
- reg.exe (PID: 3604)
- reg.exe (PID: 3248)
- reg.exe (PID: 3396)
- reg.exe (PID: 3856)
- reg.exe (PID: 3916)
- reg.exe (PID: 128)
- reg.exe (PID: 2396)
- reg.exe (PID: 656)
- reg.exe (PID: 2520)
- reg.exe (PID: 4048)
- reg.exe (PID: 3744)
- reg.exe (PID: 952)
- reg.exe (PID: 3260)
- reg.exe (PID: 600)
- reg.exe (PID: 2780)
- reg.exe (PID: 2500)
- reg.exe (PID: 3024)
- reg.exe (PID: 3364)
- reg.exe (PID: 3120)
- reg.exe (PID: 1868)
- reg.exe (PID: 3188)
- reg.exe (PID: 3308)
- reg.exe (PID: 2220)
- reg.exe (PID: 3868)
- reg.exe (PID: 3244)
- reg.exe (PID: 3860)
- reg.exe (PID: 1316)
- reg.exe (PID: 3148)
- reg.exe (PID: 3844)
- reg.exe (PID: 2192)
- reg.exe (PID: 1276)
- reg.exe (PID: 2068)
Reads the computer name
- whoami.exe (PID: 3772)
- taskkill.exe (PID: 1392)
- taskkill.exe (PID: 2836)
- taskkill.exe (PID: 3136)
- taskkill.exe (PID: 2984)
- taskkill.exe (PID: 896)
- taskkill.exe (PID: 3848)
- taskkill.exe (PID: 3568)
Checks Windows Trust Settings
- powershell.exe (PID: 3068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 148992 |
| InitializedDataSize: | 314880 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25468 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.41.2.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
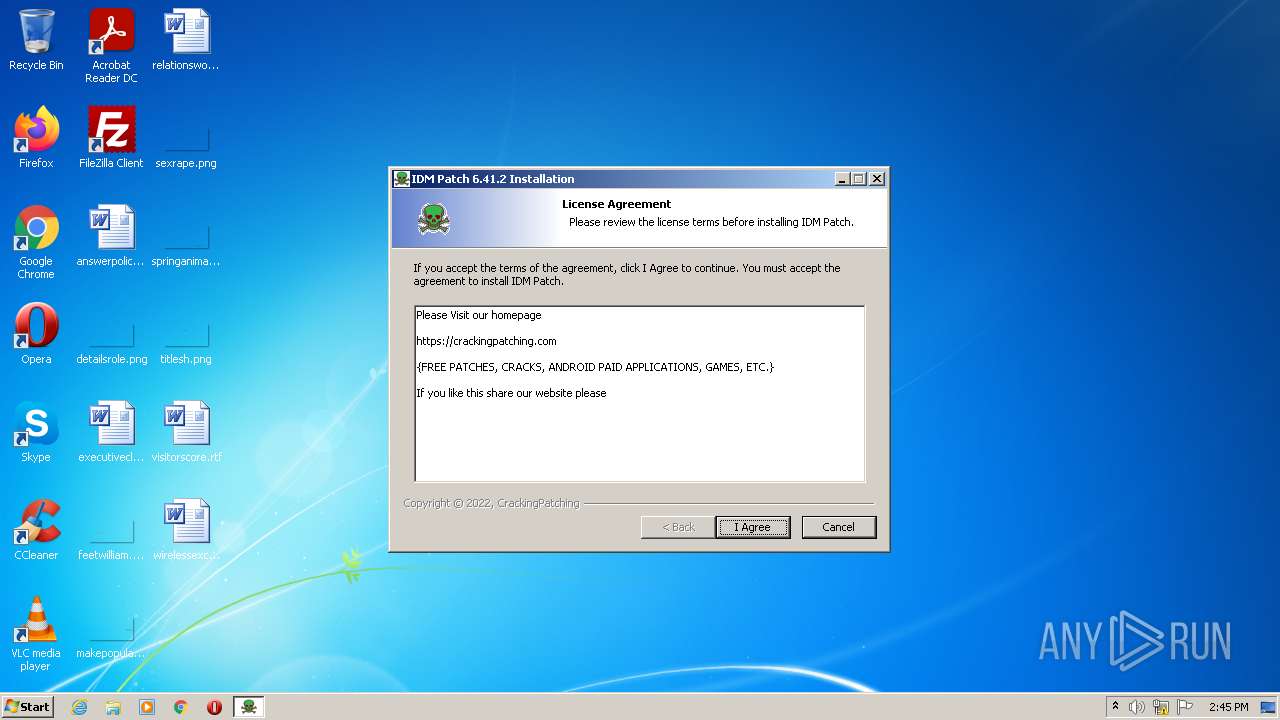
| CompanyName: | CrackingPatching |
| FileDescription: | IDM Patch 6.41.2 Installation |
| FileVersion: | 6.41.2 |
| LegalCopyright: | CrackingPatching |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | CrackingPatching |
| FileDescription: | IDM Patch 6.41.2 Installation |
| FileVersion: | 6.41.2 |
| LegalCopyright: | CrackingPatching |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000244CC | 0x00024600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59443 |
DATA | 0x00026000 | 0x00002894 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 0x00029000 | 0x000010F5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002B000 | 0x00001798 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88555 |
.tls | 0x0002D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0002F000 | 0x00001884 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 0x00031000 | 0x00046F60 | 0x00047000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.14034 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 5.24025 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 4.94231 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 4.73718 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 4.51902 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
54 | 4.05378 | 270376 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.75922 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
278
Monitored processes
240
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2564 | "C:\Users\admin\AppData\Local\Temp\IDM 32bit Patch.exe" | C:\Users\admin\AppData\Local\Temp\IDM 32bit Patch.exe | — | Explorer.EXE |
User: admin Company: CrackingPatching Integrity Level: MEDIUM Description: IDM Patch 6.41.2 Installation Exit code: 3221226540 Version: 6.41.2 | ||||
| 3252 | "C:\Users\admin\AppData\Local\Temp\IDM 32bit Patch.exe" | C:\Users\admin\AppData\Local\Temp\IDM 32bit Patch.exe | Explorer.EXE | |
User: admin Company: CrackingPatching Integrity Level: HIGH Description: IDM Patch 6.41.2 Installation Version: 6.41.2 | ||||
| 4032 | C:\Windows\system32\cmd.exe /c ""C:\Program Files\Internet Download Manager\IDM_Cleaner.bat" " | C:\Windows\system32\cmd.exe | — | IDM 32bit Patch.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 1612 | C:\Windows\system32\cmd.exe /c whoami /user /fo list | C:\Windows\system32\cmd.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 3772 | whoami /user /fo list | C:\Windows\system32\whoami.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: whoami - displays logged on user information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 464 | reg query HKU\S-1-5-19 | C:\Windows\system32\reg.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 1392 | taskkill /IM "IDMan.exe" /F | C:\Windows\system32\taskkill.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 2836 | taskkill /IM "IEMonitor.exe" /F | C:\Windows\system32\taskkill.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3136 | taskkill /IM "IDMGrHlp.exe" /F | C:\Windows\system32\taskkill.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3568 | taskkill /IM "idmBroker.exe" /F | C:\Windows\system32\taskkill.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
Total events
2 566
Read events
2 517
Write events
44
Delete events
5
Modification events
| (PID) Process: | (3252) IDM 32bit Patch.exe | Key: | HKEY_CURRENT_USER\Software\DownloadManager |
| Operation: | write | Name: | AdvIntDriverEnabled2 |
Value: 1 | |||
| (PID) Process: | (3252) IDM 32bit Patch.exe | Key: | HKEY_CURRENT_USER\Software\DownloadManager |
| Operation: | write | Name: | FName |
Value: CrackingPatching | |||
| (PID) Process: | (3252) IDM 32bit Patch.exe | Key: | HKEY_CURRENT_USER\Software\DownloadManager |
| Operation: | write | Name: | LName |
Value: .com | |||
| (PID) Process: | (3252) IDM 32bit Patch.exe | Key: | HKEY_CURRENT_USER\Software\DownloadManager |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (3252) IDM 32bit Patch.exe | Key: | HKEY_CURRENT_USER\Software\DownloadManager |
| Operation: | write | Name: | Serial |
Value: U2CFH-WQFY5-2HUVW-C6I8O | |||
| (PID) Process: | (3252) IDM 32bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Internet Download Manager |
| Operation: | write | Name: | AdvIntDriverEnabled2 |
Value: 1 | |||
| (PID) Process: | (3252) IDM 32bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Internet Download Manager |
| Operation: | write | Name: | FName |
Value: CrackingPatching | |||
| (PID) Process: | (3252) IDM 32bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Internet Download Manager |
| Operation: | write | Name: | LName |
Value: .com | |||
| (PID) Process: | (3252) IDM 32bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Internet Download Manager |
| Operation: | write | Name: | |
Value: | |||
| (PID) Process: | (3252) IDM 32bit Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Internet Download Manager |
| Operation: | write | Name: | Serial |
Value: U2CFH-WQFY5-2HUVW-C6I8O | |||
Executable files
3
Suspicious files
4
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3252 | IDM 32bit Patch.exe | C:\Program Files\Internet Download Manager\Uninstall.ini | ini | |
MD5:D55D2C54C0263A4FE585CA9B1AAE0C4D | SHA256:49B0EDCAD91325299DFC3DFF66CB216B8F131F9430C0A1FB9732DE974A8992E5 | |||
| 3252 | IDM 32bit Patch.exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:48FC4F88A77C82D5EDC9FF8BA119FB0C | SHA256:C3886AAC37762BA30A24CBAA391B01443A9DC26BC5984F6122092BD03174DF27 | |||
| 3252 | IDM 32bit Patch.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | compressed | |
MD5:86A830C9C942156F38A3201CD2C6FE13 | SHA256:0251545402C5FCCEF33DC1A6953A48620B2F616CEAE3512294E961779329D00C | |||
| 3252 | IDM 32bit Patch.exe | C:\Program Files\Internet Download Manager\IDMan.exe | executable | |
MD5:CC32561933F5231F11F8FB29307766AF | SHA256:3BBEA44CA36AAE8D25E385528BCEA36AE3EE838153C534A36B0D9EDC2F027B57 | |||
| 3252 | IDM 32bit Patch.exe | C:\Users\admin\AppData\Local\Temp\$inst\5.tmp | image | |
MD5:AB2021E67E0E08657288D880ABFBAA72 | SHA256:331D997E586CBA40D4DA0587887FC4CAA4CC44E53421737DAFA67E67445E6753 | |||
| 4032 | cmd.exe | C:\Program Files\Internet Download Manager\none.reg | text | |
MD5:9DD5EAB7B66B1A00126831115BF27761 | SHA256:46A0185B1DBEF55EE03601853E5CAD81B1F268D9BEA05F4F55F21426972181A3 | |||
| 3068 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ufgteyui.kem.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:6B86B273FF34FCE19D6B804EFF5A3F5747ADA4EAA22F1D49C01E52DDB7875B4B | |||
| 3252 | IDM 32bit Patch.exe | C:\Users\admin\AppData\Local\Temp\$inst\15.tmp | text | |
MD5:E098B42C30CA4A246BE7B344DD6E7B0C | SHA256:F2B3CF26A633E9F1DDCC2E30D81D6A1729767879E3E560A613BD4506EAD6A1DC | |||
| 3252 | IDM 32bit Patch.exe | C:\Program Files\Internet Download Manager\IDM_Cleaner.bat | text | |
MD5:4AC126BEB60194AE5E20E833C2585532 | SHA256:D7B326983D4A533A0B6D1E596327FD1A662A75207F09A64DEDF72E724CEBEFF0 | |||
| 3252 | IDM 32bit Patch.exe | C:\Users\admin\AppData\Local\Temp\$inst\7.tmp | image | |
MD5:696641D2325E8B142B6C16D1183ACA43 | SHA256:4A56FFCE0E414F3495F70E9C2960837DF25423B0DBAFD21A073DBDBAA461BC90 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report